Xage Security is an AI security platform that delivers zero trust for AI, LLMs, and agentic AI at the protocol layer, enforcing identity-based access controls below the AI stack where prompts cannot bypass them.
This protocol-layer approach is fundamentally different from application-level tools like Lakera Guard or Noma Security — even a successfully jailbroken AI agent cannot circumvent Xage’s enforcement because it operates at a layer the AI cannot reach.
The company was founded by Duncan Greatwood (CEO), a former Apple executive who previously served as CEO of Topsy — the social media search and analytics pioneer acquired by Apple in 2013. Susanto Irwan serves as Co-Founder, President, and CTO.
Xage originally built its zero trust platform for IT, operational technology (OT), and cloud environments, securing critical infrastructure including 60%+ of U.S. midstream energy infrastructure.
In 2025, the company expanded to AI security with the launch of Zero Trust for AI, signing its first customer within days and securing a strategic partnership with NVIDIA within weeks.
The company reported 81% year-over-year revenue growth, 102% customer growth, and raised an additional $15M in equity funding in December 2025 led by Piva Capital.
What is Xage Security?
Xage’s approach to AI security is fundamentally different from prompt-level filtering or application-layer monitoring. The platform enforces identity and policy at the network data protocol layer — below the AI stack.
This means that even if an AI prompt is manipulated through jailbreak techniques, unauthorized access is blocked because enforcement happens at a layer the AI cannot reach.
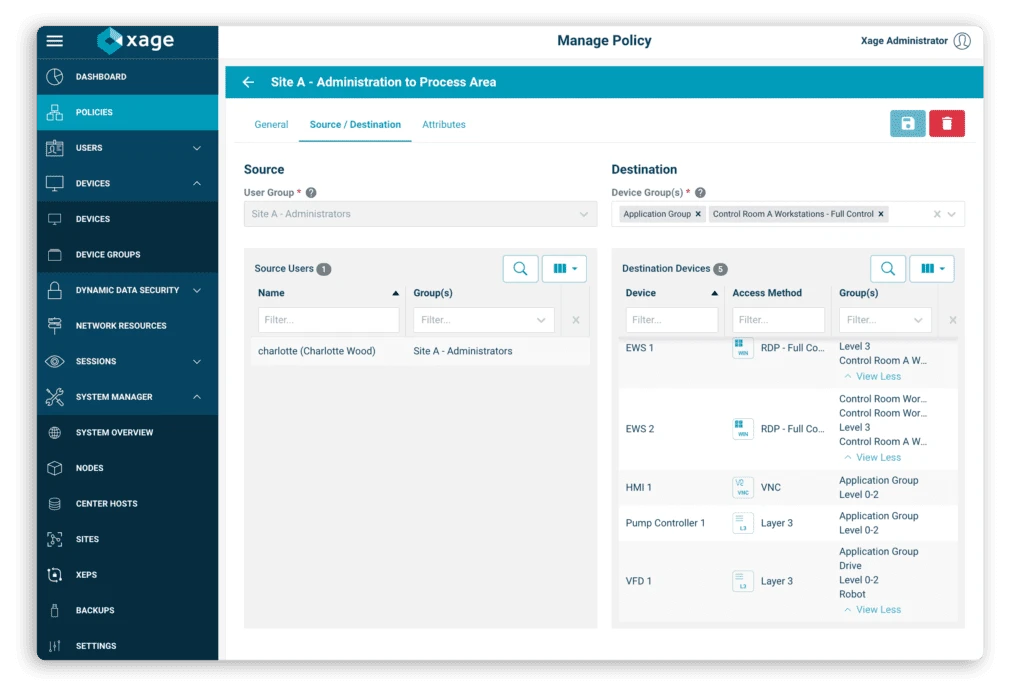
Each AI agent is treated as a non-human identity with cryptographic credentials, scoped entitlements, and automated rotation. The Xage Fabric wraps each agent with access control shielding based on its identity and entitlements, handling credential issuance, rotation, and revocation automatically.
Key Features
| Feature | Details |
|---|---|
| Enforcement Layer | Network data protocol layer (below AI stack) |
| Jailbreak Protection | Prompt manipulation cannot bypass protocol-layer enforcement |
| Identity Model | Cryptographic credentials per agent with scoped entitlements |
| Credential Management | Automated issuance, rotation, and revocation |
| NVIDIA Integration | Runs on BlueField DPUs for hardware-accelerated enforcement |
| Scale | 10M assets, 50M simultaneous AI-to-AI and AI-to-resource interactions |
| Throughput | 400 Gbps (100x faster than software-only) |
| Unified Platform | Secures IT, OT, cloud, and AI in a single architecture |
| XPAM | Extended Privileged Access Management for vendor and admin access |
| MCP Security | Protects Model Context Protocol pipelines |
| A2A Security | Controls agent-to-agent interactions |
How protocol-layer zero trust works
Most AI security tools operate at the application layer — filtering prompts, scanning outputs, or monitoring agent behavior. Xage takes a different approach by enforcing at the network protocol layer:
Identity assignment — Each AI agent receives a cryptographic identity with defined entitlements. The identity specifies exactly which resources the agent can access, what operations it can perform, and under what conditions.
Protocol-layer interception — When an agent attempts to access a resource (database, API, service, or another agent), the Xage Fabric intercepts the request at the network protocol layer. This happens before the request reaches the target system.
Policy enforcement — The request is evaluated against identity-based policies. Because enforcement happens at the protocol layer, a compromised or jailbroken AI agent cannot bypass these controls through prompt manipulation.
The AI model simply does not have access to the enforcement mechanism.
Credential lifecycle — The Fabric automatically manages credential lifecycle: issuing temporary credentials, rotating them on schedule, and revoking them when no longer needed. No persistent credentials exist that could be leaked or misused.
NVIDIA partnership
Xage’s integration with NVIDIA runs the zero trust enforcement engine natively on NVIDIA BlueField DPUs (Data Processing Units). This hardware-accelerated approach delivers performance that software-only solutions cannot match:
- 10 million assets supported simultaneously
- 50 million concurrent AI-to-AI and AI-to-resource interactions
- 400 Gbps throughput for security enforcement
- 100x faster than software-only enforcement
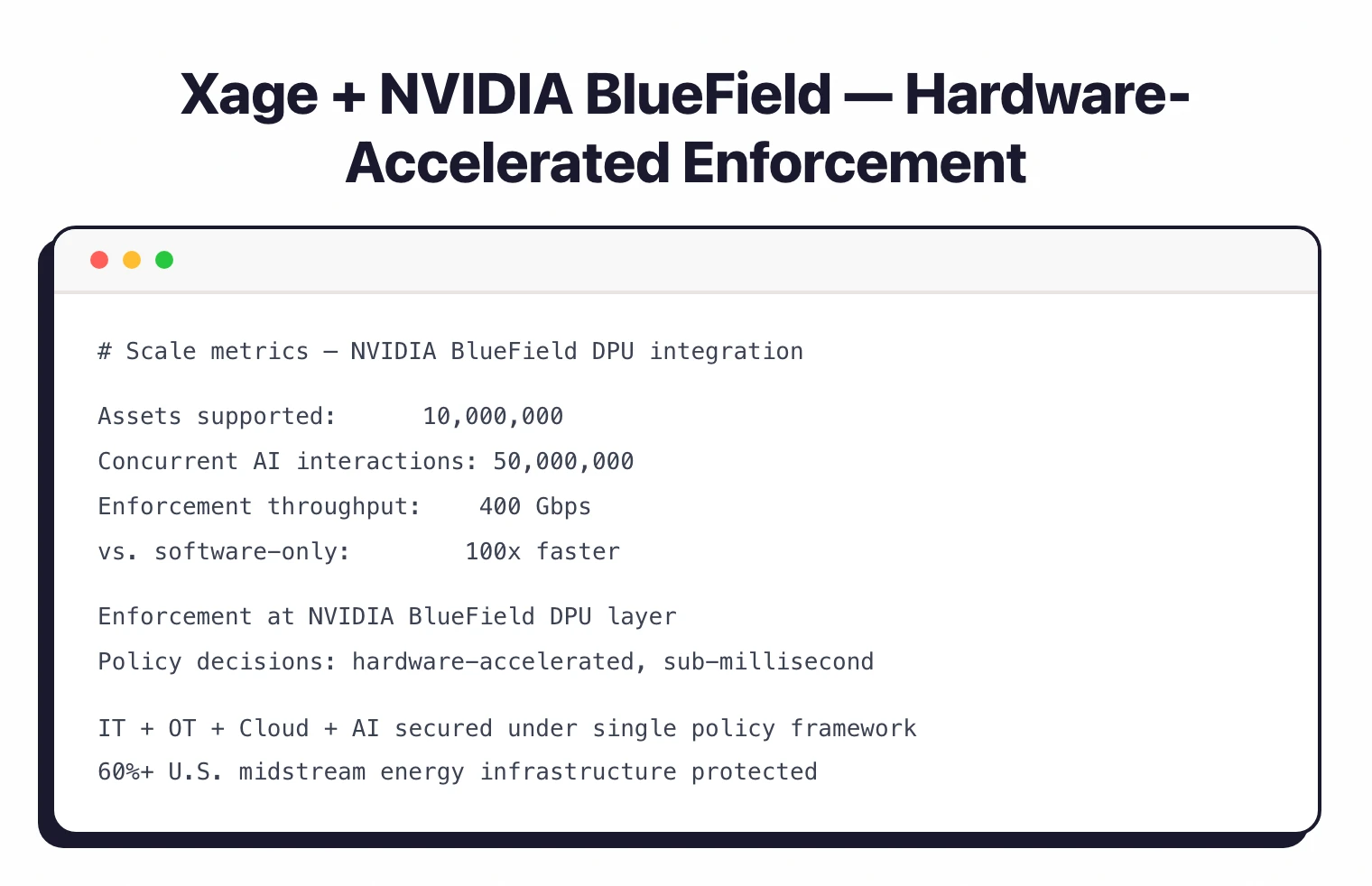
This scale targets AI factories and hyperscale environments where millions of agents and models interact continuously. The NVIDIA partnership was announced in 2025 alongside Xage’s Zero Trust for AI launch.
Beyond AI: unified zero trust
Xage’s platform is not AI-only. The same architecture secures IT, OT, cloud, and AI environments under a single policy framework. This matters most for organizations in critical infrastructure sectors — energy, manufacturing, federal agencies — where AI systems interact with operational technology and physical infrastructure.
The platform includes Extended Privileged Access Management (XPAM) for vendor and administrative access, VPN replacement capabilities, and zero trust segmentation across the full technology stack.
Getting Started
When to use Xage Security
Ideal for organizations that need AI security enforcement that cannot be bypassed through prompt manipulation. The protocol-layer approach provides a fundamentally different security guarantee than application-layer tools.
The platform shines in critical infrastructure sectors — energy, manufacturing, federal — where AI systems interact with operational technology and physical infrastructure.
The NVIDIA integration makes it viable at hyperscale, supporting AI factories with millions of concurrent interactions.
Organizations already using Xage for IT/OT zero trust can extend the same platform to cover AI workloads without deploying a separate AI security tool.
For more AI security tools and guidance, see the AI security tools category page. For application-layer AI security, see Noma Security or Onyx Security.
For runtime prompt protection, consider Lakera Guard or LLM Guard. For agent-level access control, check Alter. For LLM vulnerability scanning, look at Garak or Promptfoo.