Wiz is an IaC security and CNAPP platform that scans cloud environments without installing agents. The platform connects to AWS, Azure, GCP, OCI, and Alibaba Cloud via API and maps relationships between resources, identities, and vulnerabilities through what it calls the Security Graph.
More than 50% of Fortune 100 companies use Wiz, including Morgan Stanley, Salesforce, BMW, Siemens, Snowflake, and Slack. The company was the fastest SaaS product to reach $100M and $200M ARR.
Google announced a $32B acquisition of Wiz in March 2025. As of Google Cloud Next ‘26, Wiz has officially joined the Google Cloud Security family, with the deal closing during 2026.
The platform integrates with 200+ security tools through the Wiz Integration Network (WIN).
Where Wiz lives on AppSec Santa. Wiz is primarily a CNAPP (cloud-native application protection platform) — its canonical scope is cloud-posture and runtime, not application security. AppSec Santa covers Wiz only for its IaC scanning surface (Wiz Code, Checkov-derived rules), which is why this page sits under IaC Security. For container runtime, CSPM, and CWP comparisons that fall outside AppSec, dedicated CNAPP coverage is out of scope here.
What is Wiz?
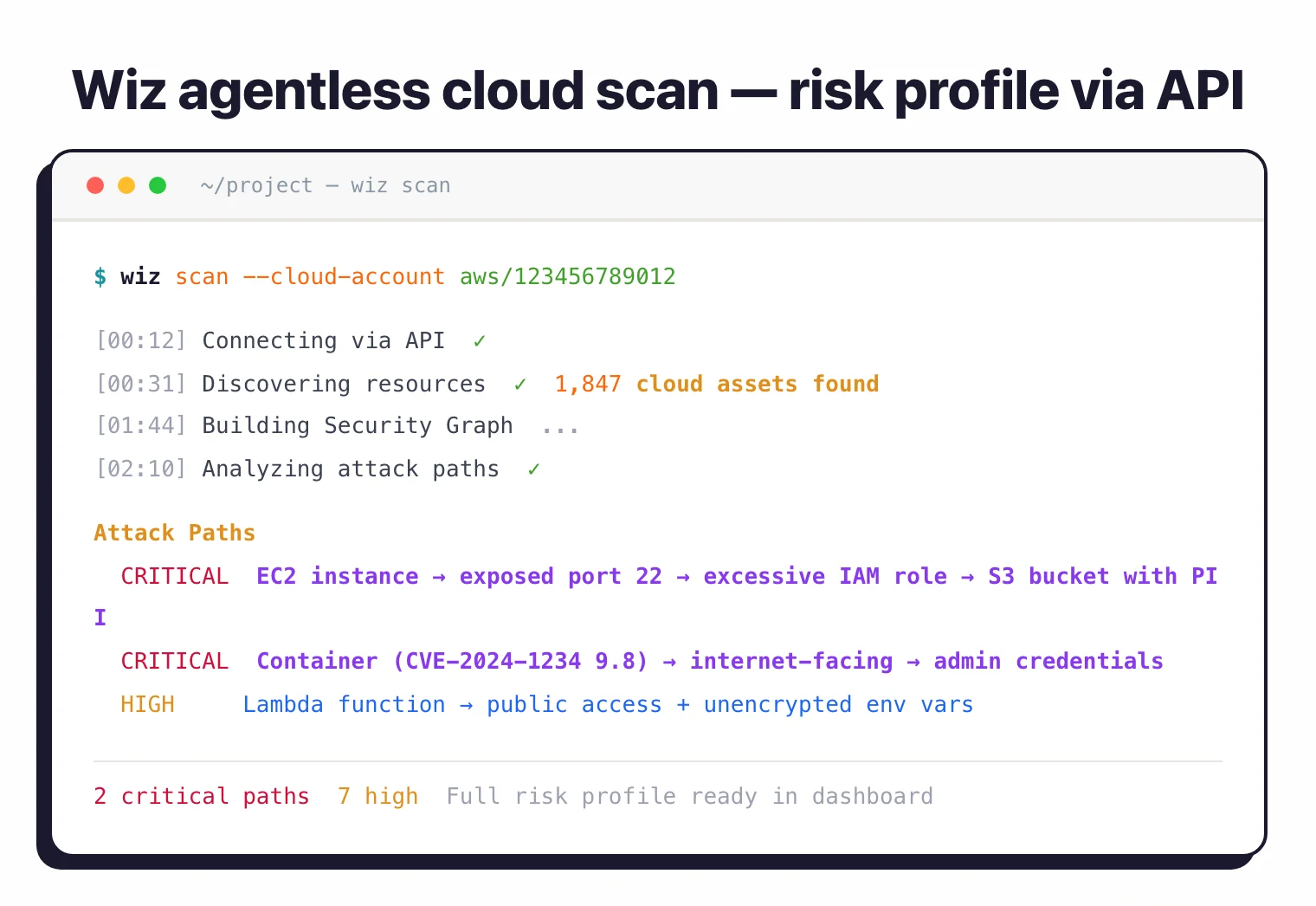
Wiz connects to cloud provider APIs and scans every layer of infrastructure without agents. It covers virtual machines, containers, serverless functions, storage, databases, identity systems, and networking.
A full risk profile is available within 24 hours of connecting your cloud accounts.
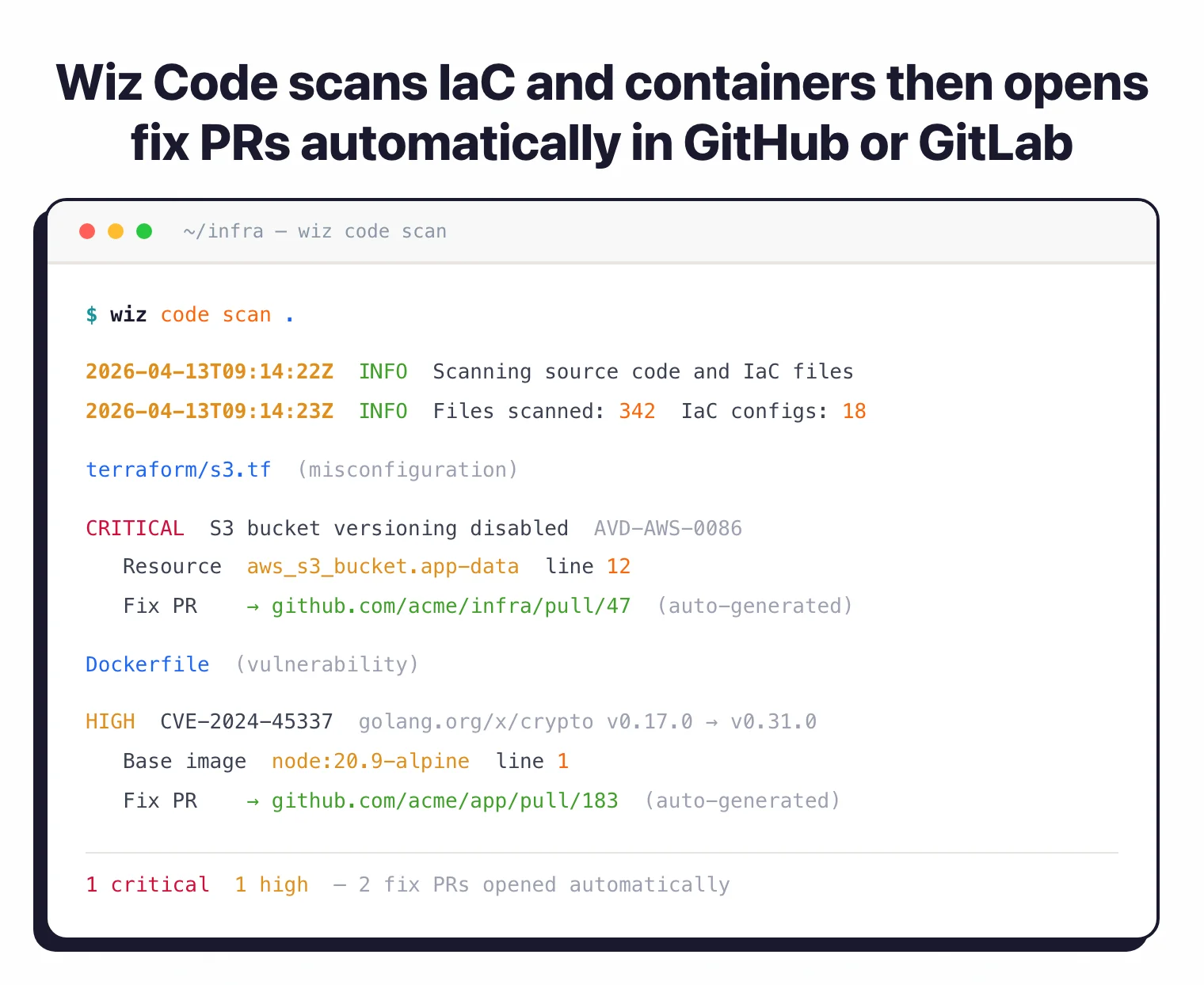
The platform has three main modules. Wiz Code scans repositories, CI/CD pipelines, container registries, and images. It generates 1-click fix PRs when it finds issues.
Wiz Cloud handles agentless posture management: CSPM, CWPP, CIEM, vulnerability scanning, and IaC checks. Wiz Defend adds eBPF-based runtime protection and threat detection for workloads that need real-time monitoring.
Wiz automatically discovers new cloud resources as they’re added. A free 14-day trial is available.
Key features
| Module | Details |
|---|---|
| Wiz Code | Code, CI/CD, registry, and container image scanning with 1-click fix PRs |
| Wiz Cloud | Agentless CSPM, CWPP, CIEM, DSPM, vulnerability management, IaC scanning |
| Wiz Defend | eBPF runtime sensor, threat detection, CDR, forensic collection, threat hunting |
| Security Graph | Context-driven risk analysis connecting resources, identities, and vulnerabilities |
| Attack paths | Toxic risk combinations identifying exploitable multi-factor attack paths |
| AI-SPM | AI model inventory, ML pipeline security, training data exposure detection |
| Compliance | PCI-DSS, HIPAA, SOC 2, ISO 27001, GDPR, CIS benchmarks |
| Integrations | 200+ tools via WIN (Wiz Integration Network) |
| Cloud support | AWS, Azure, GCP, OCI, Alibaba Cloud, VMware vSphere, Kubernetes, OpenShift |
Agentless cloud scanning
Wiz reads cloud configurations and workload data through provider APIs. No agents, no network taps, no code running inside your environment.
It scans VMs, containers, serverless functions, storage buckets, databases, and networking configurations.
The initial scan completes in minutes. Within 24 hours you have a full risk profile of your cloud estate. New resources get picked up automatically as they’re deployed.
Note: Wiz popularized the agentless-first model — most scanning happens via cloud API. For workloads that need real-time runtime protection, the optional Wiz Sensor (eBPF-based) adds process-level visibility and blocking without the overhead of traditional agents.
Security Graph
The Security Graph is the core of how Wiz prioritizes risk. It maps every cloud resource, identity, network path, and vulnerability into a single graph.
When the platform finds a CVE in a container image, it checks whether that container is running, whether it’s internet-facing, what identity it runs as, and whether that identity can reach sensitive data.
This is what separates Wiz from scanners that just produce vulnerability lists. A critical CVE on an internal, isolated workload with no network exposure gets a different priority than the same CVE on a public-facing service with admin credentials.
Wiz Defend
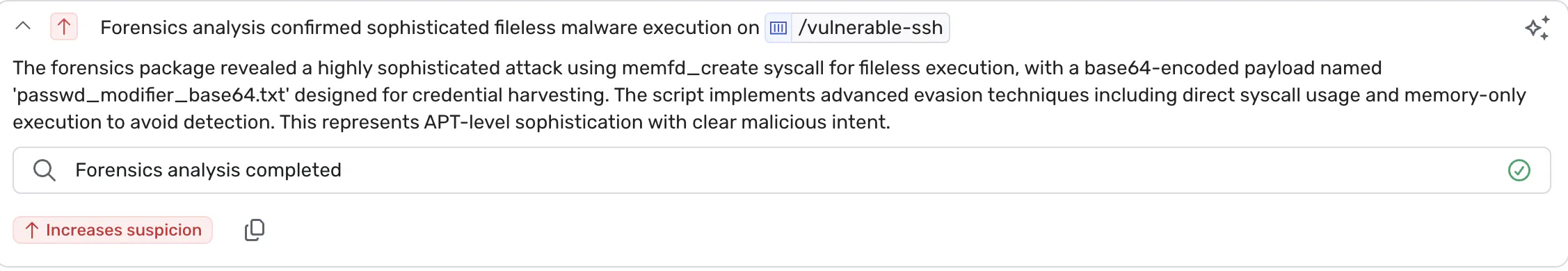
Wiz Defend is the runtime layer. It uses an eBPF-powered sensor to capture system-level activity on workloads and correlate it with posture data from the Security Graph.
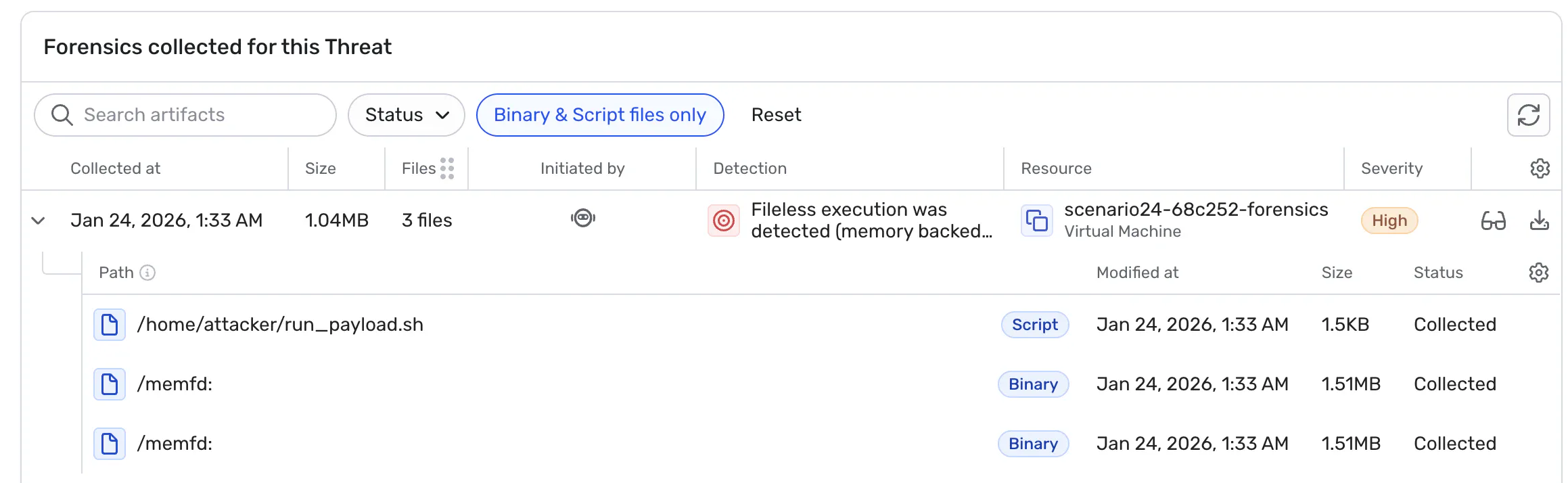
The module covers real-time threat detection, cloud detection and response (CDR), forensic collection for post-incident analysis, and threat hunting workflows.
Alerts include full context: which resources are affected, what vulnerabilities exist on them, and what remediation steps to take.

You don’t need Wiz Defend on every workload. Most organizations deploy the sensor selectively on production systems handling sensitive data or facing the internet.
The agentless scanning from Wiz Cloud covers everything else.
Wiz Code
Wiz Code scans source code, CI/CD pipelines, container registries, and container images for security issues. When it finds a vulnerability or misconfiguration, it can generate a fix PR directly in your repository.
The code-to-cloud correlation traces running resources back to the source code and developer who created them. If a misconfigured Terraform module is deployed to production, Wiz shows which repo, which file, and which developer to notify.
IDE plugins are available for JetBrains and VS Code.

The WizExtend browser extension overlays security context directly onto AWS, Azure, and GCP console pages so you can see risk data while working in your cloud provider’s portal.
AI Security Posture Management (AI-SPM)
Wiz extends its scanning to AI workloads. The AI-SPM module inventories AI models, tracks ML pipeline configurations, and detects exposed training data or vulnerable model APIs across your cloud environment.
Compliance
Pre-built frameworks cover PCI-DSS, HIPAA, SOC 2, ISO 27001, GDPR, and CIS benchmarks.
The platform monitors configurations against these requirements continuously and flags drift. Compliance dashboards produce audit-ready reports.
Integrations
Wiz integrates with 200+ tools through the Wiz Integration Network (WIN).
Getting started
When to use Wiz
Wiz works best for organizations running cloud infrastructure at scale across multiple providers. If you have hundreds of cloud accounts and thousands of workloads, the agentless approach gives you visibility without the operational overhead of deploying and maintaining agents everywhere.
Strengths
No agents to manage. Full cloud visibility within 24 hours.
The Security Graph connects findings across CSPM, CWPP, CIEM, and vulnerability management into prioritized attack paths instead of separate alert streams.
The 200+ integrations via WIN connect to existing SIEM, ticketing, and orchestration workflows.
Limitations
Wiz is a cloud-native platform. If you have significant on-premises infrastructure, you’ll need something else for that. The platform requires cloud provider API access for scanning.
Pricing is based on cloud workloads (compute, data, AI) and requires a sales conversation. Median annual contract: $149,000 (range: $25,000–$414,000).
Smaller organizations or teams early in cloud adoption may find other IaC security tools more cost-effective.
For a broader view of cloud security platforms, see the cloud infrastructure security guide.
Wiz acquisition by Google ($32B, closing 2026)
Google announced its $32 billion acquisition of Wiz in March 2025 — the largest cybersecurity deal on record. The transaction cleared regulatory review during the first half of 2026, and at Google Cloud Next ‘26 Wiz appeared on stage as part of the Google Cloud Security family.
The public commitments matter for buyers evaluating Wiz today. Google has stated Wiz will continue to operate as a multi-cloud platform — AWS, Azure, OCI, and Alibaba Cloud customers keep getting first-class scanning, not a slow degradation toward GCP-only. Existing customer contracts carry over, and the Wiz roadmap continues independently within Google Cloud’s security organization.
What this changes long-term is integration depth on GCP: tighter ties to Chronicle, Mandiant threat intel, and Google Cloud’s identity stack. For multi-cloud shops the immediate impact is small. For GCP-first shops, the trajectory is a unified Google Cloud + Wiz security plane.
If you’re under procurement review, the acquisition is now a settled fact rather than a pending risk. Wiz pricing, contract terms, and renewal logic continue through Google Cloud’s enterprise sales motion.
Wiz vs other CNAPP platforms
The CNAPP market is crowded with platforms that share the same five-letter acronym but optimize for different buyers. Here’s how Wiz sits against the alternatives I see in the same procurement shortlists most often:
- Prisma Cloud (Palo Alto Networks) — broader portfolio integration and a larger compliance library; chosen when Palo Alto is already the network and SOC anchor. The Wiz vs Prisma Cloud guide covers the trade-offs.
- Orca Security — sidescanning specialist that pioneered agentless cloud scanning. The Wiz vs Orca comparison breaks down which graph model fits which org.
- Sysdig Secure — runtime-first via Falco, stronger when eBPF visibility and container threat detection drive the buy.
- Lacework — behavioral anomaly detection focus, often picked when ML-driven runtime baselining is a hard requirement.
- CrowdStrike Falcon Cloud Security — endpoint vendor extending into cloud; chosen when CrowdStrike is already the EDR standard.
For a wider survey of the category and where Wiz fits, the what is CNAPP explainer and the CSPM vs CNAPP breakdown cover the surrounding landscape. The Wiz alternatives hub aggregates the full short list.
How I researched Wiz
Wiz is enterprise-tier and sales-gated, so I reviewed the platform from the outside rather than running a free-tier pilot. The notes here come from public Wiz product pages, the Gartner Peer Insights review corpus (618 reviews at the time of writing, 4.7/5), G2 reviews, and a sample of practitioner-led Reddit threads on r/cybersecurity, r/devsecops, and r/Cloud comparing Wiz against Orca, Prisma Cloud, and Cortex Cloud.
For pricing context I used the Vendr-collected anonymized contract data flagged in this page’s frontmatter — Vendr aggregates real procurement outcomes rather than vendor-published list prices, which Wiz does not publish. Where Reddit threads and Gartner reviews disagreed (typical pattern: Reddit emphasizes painful integrations, Gartner emphasizes platform breadth), I noted both.
I did not receive paid access from Wiz or any commercial relationship with the vendor. The screenshots in this page come from Wiz’s public marketing surfaces. Any procurement decision should still include a hands-on trial — Wiz offers a 14-day unlimited trial — because cloud surface area varies enough that one team’s experience rarely matches another’s.
Frequently Asked Questions
What is Wiz?
How does Wiz differ from traditional cloud security tools?
Does Wiz support Kubernetes security?
What clouds does Wiz support?
Is there a free trial?
* Pricing data from Vendr — anonymized contract values from real buyer transactions.