Wallarm is an API security platform that protects over 160,000 APIs and processes billions of requests daily. It pairs a web application firewall with ML-based API protection, automatic API discovery, and bot management in a single product.
The company is headquartered in Austin, TX with an additional office in San Francisco. Customers include Panasonic, Victoria’s Secret, Miro, Samsung, Dropbox, and Semrush.
Wallarm also maintains several open-source projects: API Firewall, GoTestWAF, and the libDetection library.
What is Wallarm?
Wallarm started as a WAF and expanded into API security tools as API traffic outgrew traditional web application traffic. The platform treats API protection as the primary concern rather than a bolt-on to WAF rules.
It works in two modes. Inline mode sits in the request path and blocks attacks before they reach your backend.
Out-of-band mode mirrors traffic for analysis without touching the live request flow. Both feed the same Wallarm Console for visibility.
The platform organizes into four product areas:
Key Features
| Feature | Details |
|---|---|
| APIs protected | 160,000+ |
| Requests processed | Billions daily |
| API Discovery | Automatic inventory from live traffic, shadow/zombie/orphan API detection |
| Threat detection | ML-based anomaly detection + signature matching |
| OWASP coverage | Full OWASP API Security Top 10 |
| Bot management | Credential stuffing, ATO, L7 DDoS, scraping detection |
| GraphQL | Query depth limits, complexity analysis, introspection blocking |
| Deployment options | Docker, Kubernetes, NGINX, cloud connectors, DNS edge, eBPF |
| Integrations | Slack, Teams, PagerDuty, Jira, Splunk, Datadog, Sumo Logic, and more |
API Discovery
Wallarm builds your API inventory by analyzing real traffic rather than relying on uploaded specs. The API Discovery module identifies endpoints, request methods, parameters, data types, and authentication patterns.
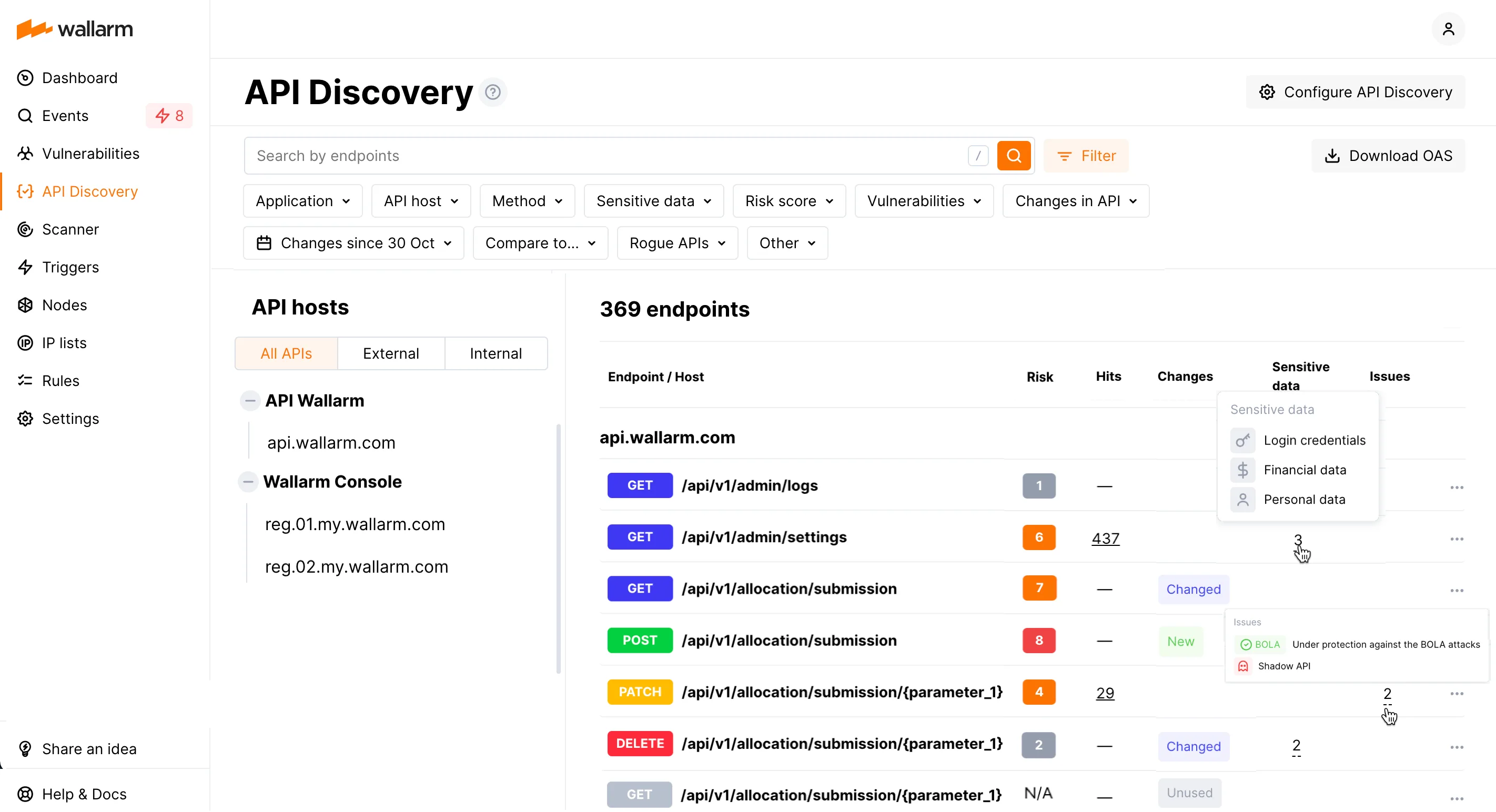
It flags shadow APIs (undocumented endpoints handling live traffic), zombie APIs (deprecated endpoints still accessible), and orphan APIs (endpoints with no owner). Sensitive data detection picks up PII, financial data, credentials, and health information flowing through your APIs.
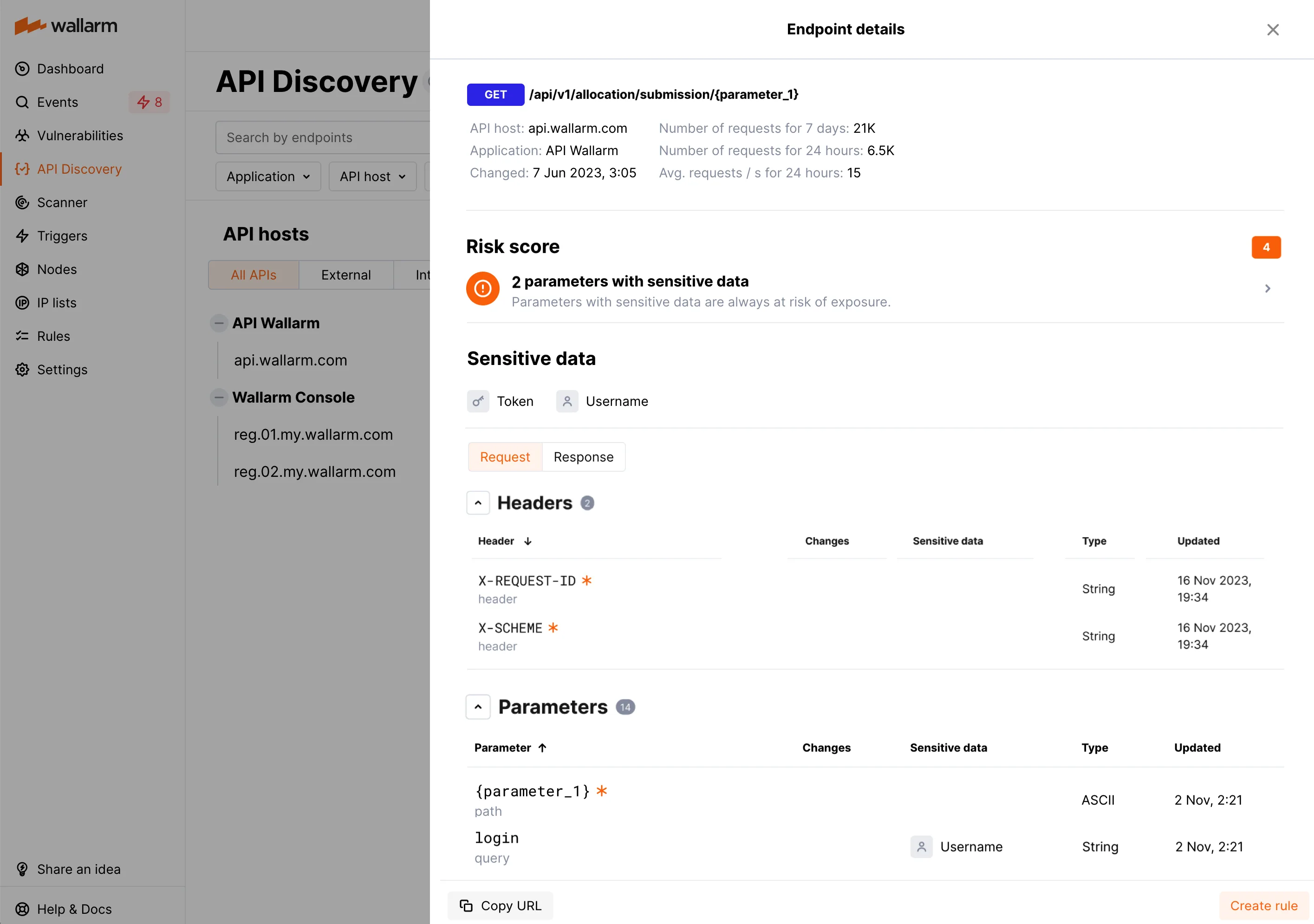
Risk scoring ranks endpoints by attack likelihood. Business-critical flows like authentication, billing, and account management are tagged automatically.
Threat Detection and WAAP
ML models establish baselines of normal API behavior and flag deviations. This catches zero-day attacks and business logic abuse that signature-only tools miss.
Wallarm also uses traditional signature matching for known attack patterns, so the two approaches cover different ground.
Protection covers the OWASP API Security Top 10:
- BOLA (Broken Object Level Authorization) with automatic protection rules
- Broken Authentication detection
- Excessive Data Exposure monitoring
- Rate Limiting enforcement
- Broken Function Level Authorization detection
- Mass Assignment blocking
- Injection attacks (SQLi, XSS, RCE)
- Security Misconfiguration identification
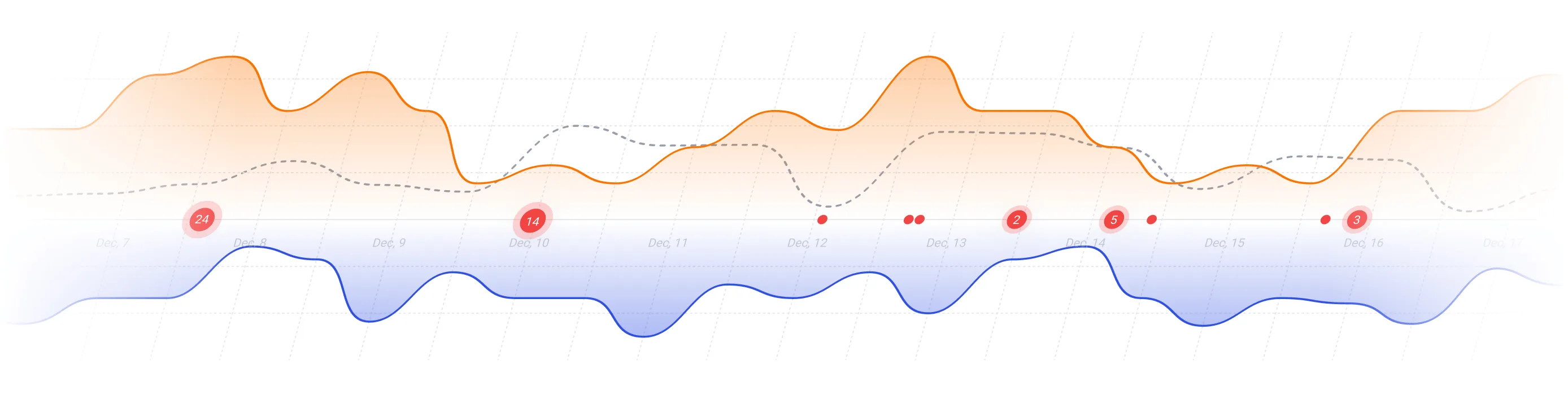
API Abuse Prevention
The API Abuse Prevention module targets automated attacks that traditional WAFs miss. It uses specialized detectors for:
- Account takeover and credential stuffing — identifies automated login attempts by analyzing request patterns and timing
- L7 DDoS — detects high-volume API abuse that overwhelms application logic
- Scraping — blocks automated data extraction across API endpoints
- Security crawlers — identifies scanning tools probing your API surface
Each detector has adjustable weighting and thresholds. Session-level blocking lets you stop a specific malicious session without affecting legitimate users sharing the same IP.
GraphQL Security
Wallarm includes protections specific to GraphQL APIs:
- Query depth limiting to prevent deeply nested queries
- Query complexity analysis
- Introspection blocking in production
- Batching attack prevention
Bot Management
The platform distinguishes legitimate automation (monitoring tools, partner integrations) from malicious bots. Policies can allow, challenge, or block different bot categories based on signatures, behavioral patterns, and client fingerprints.
Deployment
Wallarm offers several deployment paths depending on your infrastructure. All installation commands below come from the official documentation.
Docker
The NGINX-based Docker image runs on both x86_64 and ARM64. The current image is wallarm/node:6.10.1 based on Alpine Linux 3.22 with NGINX stable 1.28.0.
docker run -d \
-e WALLARM_API_TOKEN='<YOUR_TOKEN>' \
-e WALLARM_LABELS='group=<GROUP>' \
-e NGINX_BACKEND='your-backend.example.com' \
-e WALLARM_API_HOST='us1.api.wallarm.com' \
-p 80:80 \
wallarm/node:6.10.1
Set WALLARM_MODE to block, safe_blocking, monitoring, or off to control filtering behavior. Omit WALLARM_API_HOST if using the EU cloud.
Kubernetes (Helm)
Wallarm provides a Helm chart that wraps the community NGINX Ingress Controller (v1.11.8) with Wallarm filtering built in. The chart supports Kubernetes 1.26 through 1.30.
helm repo add wallarm https://charts.wallarm.com
helm repo update wallarm
helm install --version 6.10.1 wallarm-ingress wallarm/wallarm-ingress \
-n wallarm-system \
-f values.yaml
The values.yaml requires at minimum:
controller:
wallarm:
enabled: "true"
token: "<NODE_TOKEN>"
apiHost: "us1.api.wallarm.com" # omit for EU cloud
Enable traffic analysis per ingress with annotations:
kubectl annotate ingress <YOUR_INGRESS> \
nginx.ingress.kubernetes.io/wallarm-mode=monitoring
Additional Kubernetes options include sidecar proxy injection and eBPF-based out-of-band analysis.
All-in-One Installer (NGINX)
For compute instances running NGINX, the all-in-one installer auto-detects your OS and NGINX version:
curl -O https://meganode.wallarm.com/6.10/wallarm-6.10.1.x86_64-glibc.sh
sudo env WALLARM_LABELS='group=<GROUP>' \
sh wallarm-6.10.1.x86_64-glibc.sh -- \
--batch -t <YOUR_TOKEN> -c US
ARM64 builds are available at the same path with aarch64-glibc in the filename.
Cloud Connectors
Native connectors are available for:
- AWS — ALB, API Gateway, CloudFront
- Azure — Application Gateway, Front Door
- GCP — Cloud Armor, Load Balancer
- Cloudflare — Workers integration
- CDN/Gateway — Kong, MuleSoft, Fastly, Akamai
Security Edge
Security Edge is the fastest deployment option. Point your DNS at Wallarm’s edge network and traffic is filtered before reaching your origin.
No infrastructure changes, no agents to install. Wallarm claims setup in 15 minutes.
Integrations
Getting Started
When to Use Wallarm
Wallarm is a good fit if:
- You need API-specific protection beyond what a standard WAF provides
- You want automatic API inventory built from live traffic, not manual spec uploads
- Your APIs face bot abuse, credential stuffing, or scraping attacks
- You run GraphQL endpoints that need query-level controls
- You deploy across multiple clouds and need consistent API protection
- You want the option of DNS-based deployment without infrastructure changes
It’s probably not the right pick if:
- You only need a basic WAF for static web pages without significant API traffic
- You already use a dedicated API security tool like 42Crunch for spec-driven security and want a different approach
- Your environment requires all security tooling to run entirely on-premise with no cloud component (though Wallarm does support on-premise Wallarm Cloud)
Wallarm also offers a Terraform provider for infrastructure-as-code management and a free API Security Certification program through Wallarm University.