Veracode SCA is an enterprise SCA tool that combines traditional vulnerability scanning with supply chain attack detection from the January 2025 Phylum acquisition. The platform claims 60% more accurate malicious package detection through ML-powered behavioral analysis that catches typosquatting, dependency confusion, and compromised maintainer accounts.
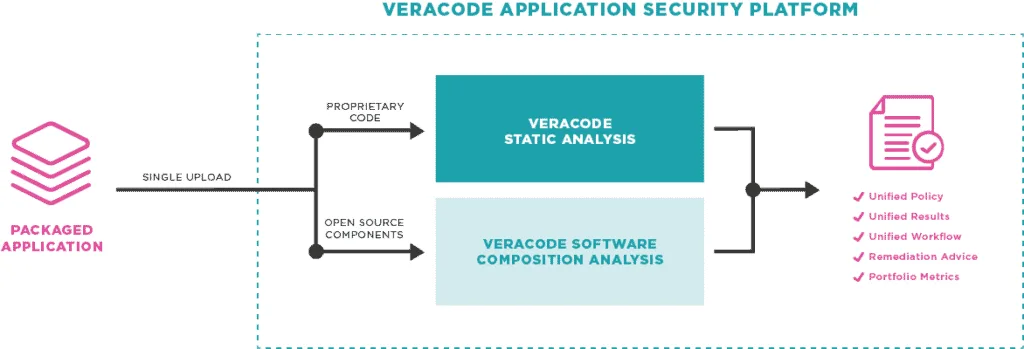
Veracode SCA integrates with the broader Veracode platform, correlating SCA findings with SAST and DAST results. A package registry firewall blocks malicious packages before developers can install them.
What is Veracode SCA?
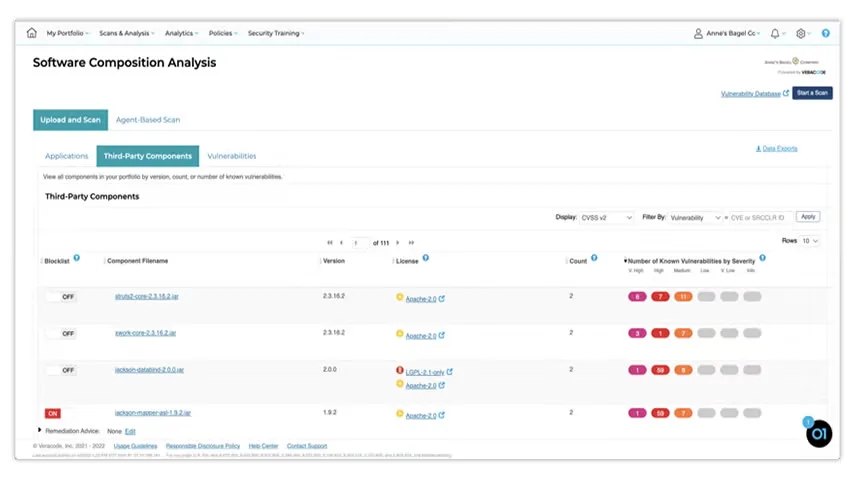
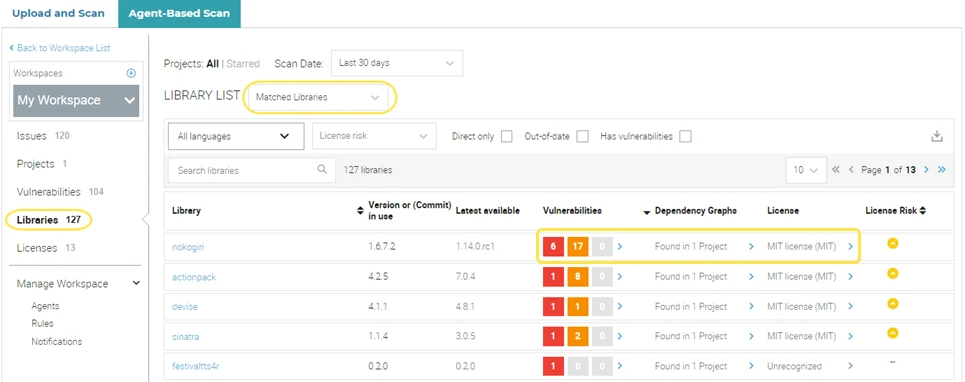
Veracode SCA scans dependencies for known vulnerabilities and uses Phylum’s technology to analyze package behavior and identify malicious code patterns. The registry firewall blocks compromised packages in real-time, and reachability analysis traces code paths to determine if vulnerable functions are actually called by your application.
Key features
| Feature | Details |
|---|---|
| Malicious package detection | 60% more accurate via Phylum ML; typosquatting, dependency confusion, compromised maintainers |
| Registry firewall | npm and PyPI proxy blocks malicious packages before installation |
| Reachability analysis | Code path tracing to determine if vulnerable functions are called |
| Ecosystems | npm, yarn, pnpm, pip, Poetry, Maven, Gradle, Go, NuGet, Bundler, Composer, Cargo |
| Container scanning | Docker and OCI image analysis across all layers |
| License compliance | Policy enforcement with SPDX and CycloneDX SBOM generation |
| Remediation | Automated fix pull requests for vulnerable dependencies |
| Platform integration | Correlated findings with Veracode SAST and DAST |
Supply chain attack detection
Phylum’s technology monitors for malicious packages entering the supply chain: typosquatting (names similar to popular libraries), dependency confusion (public packages mimicking internal names), compromised maintainer accounts, and malicious code injection in legitimate packages.
Reachability analysis
Veracode SCA traces code paths to determine if vulnerable functions are actually called by your application. This cuts through alert noise and helps teams focus on the vulnerabilities that actually pose risk.
Dependency update automation
Veracode SCA generates automated fix pull requests for vulnerable direct and transitive dependencies, proposing the minimum safe version that clears the finding. It stops short of the ongoing dependency-refresh loop that Renovate or Dependabot provide — Veracode surfaces fix PRs on security findings rather than a continuous update cadence, so most teams pair it with Renovate or Dependabot for non-security updates.
Package registry firewall
Configure npm or pip to use the Veracode proxy registry. Malicious packages get blocked before installation, preventing compromised dependencies from ever reaching your codebase.
Container scanning
Analyzes container images for vulnerabilities in OS packages and application dependencies across all layers, covering base images and added components.
License compliance and SBOM
License detection with policy enforcement and SBOM generation in SPDX and CycloneDX formats. Handles dual-licensing, license exceptions, and organizational policy rules.
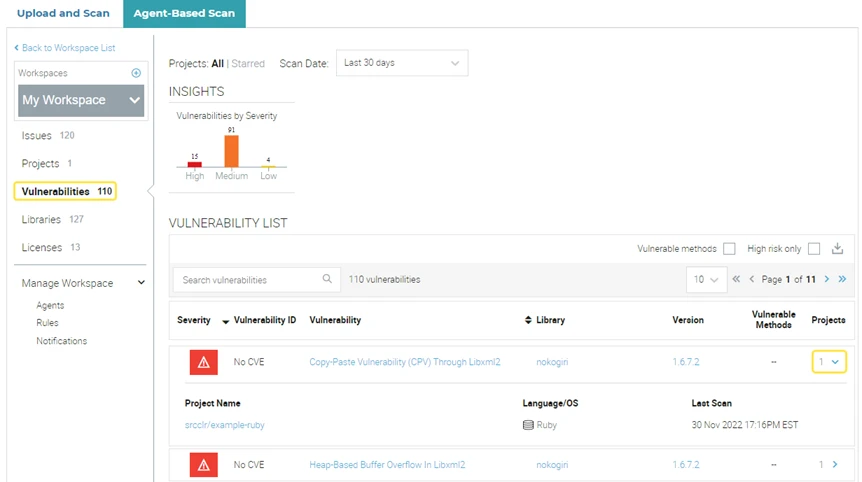
Vulnerable methods and reachability deep dive
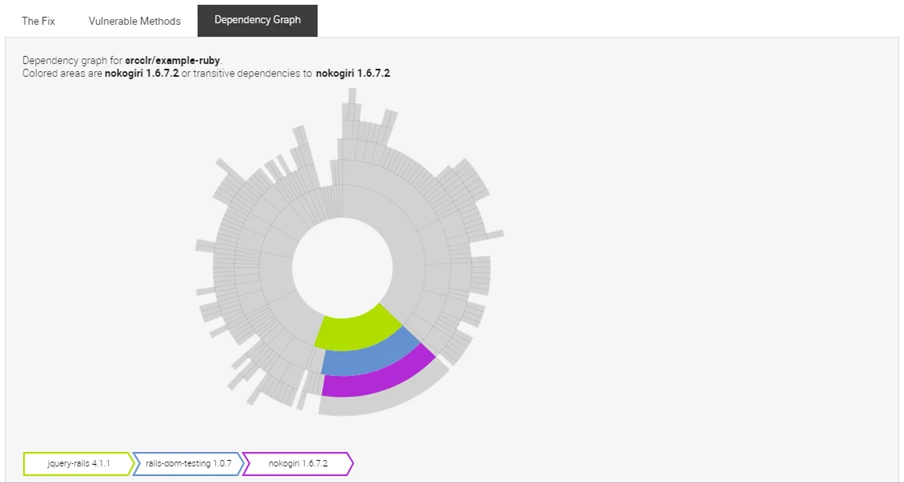
Veracode SCA’s reachability layer is called vulnerable methods analysis. During a full agent-based scan, the agent builds a call graph of your application and compares it against Veracode’s vulnerability database, which records the specific public methods affected by each disclosed CVE. A finding is flagged as a vulnerable method only when your first-party code actually reaches one of those methods, directly or through a transitive dependency.
The call graph covers both direct and transitive components, so a vulnerability in a library pulled in three levels deep still gets traced if your code path reaches it. Veracode’s docs describe the research workflow as evidence collection — security researchers tag the exact affected methods, and that tagging drives what the agent matches against at scan time.
Vulnerable methods analysis requires an agent-based scan with full build context. It is not available for upload-and-scan mode or for languages where Veracode does not publish vulnerable-method data — in those cases the scan still reports the CVE, it just cannot tell you whether the vulnerable function is reached.
Integrations
Veracode SCA supported languages
Veracode SCA’s agent-based scan works with the package managers that dominate each ecosystem. Based on the current docs, the matrix looks like this:
- Java: Maven, Gradle, Ant
- Kotlin: Gradle, Maven
- Scala: sbt
- .NET / C#: NuGet
- JavaScript / TypeScript: npm, Yarn, Bower
- Python: pip, Pipenv, Poetry
- Go: Go modules (plus older tools like Dep, Glide, GoDep, GoVendor)
- Ruby: Bundler
- PHP: Composer
- Objective-C / Swift: CocoaPods
- C / C++: Make
Rust (Cargo) is not listed as a supported ecosystem in Veracode’s current agent-based scan docs, which is worth flagging if your stack includes Rust crates. The frontmatter on this page keeps Rust as a historical entry, but until Veracode’s docs confirm agent-based Cargo support you should treat Rust coverage as CVE-only rather than full reachability.
Supported languages change between agent releases, so re-check docs.veracode.com before committing Veracode SCA as your primary scanner for a new-to-you ecosystem.
Getting started
brew install veracode-cli on macOS or download from the Veracode portal for Linux/Windows.veracode configure or set VERACODE_API_KEY_ID and VERACODE_API_KEY_SECRET environment variables.veracode scan --type sca in your project directory.When to use Veracode SCA
Veracode SCA fits organizations that need supply chain attack protection alongside traditional vulnerability scanning, especially those already using Veracode for SAST and DAST.
The Phylum acquisition brought ML-powered behavioral analysis that commercial competitors are still catching up to. The registry firewall is a concrete differentiator that blocks threats before they reach your codebase, though it is currently limited to npm and PyPI.
It is a commercial product with no free tier. Median annual Veracode contract: $19,000 (range: $9,000–$134,000), though enterprise portfolios with 50+ applications commonly reach $250,000–$500,000+. The strongest value comes from using it alongside Veracode SAST and DAST for correlated findings.
How it compares:
| vs. | Key difference |
|---|---|
| Snyk Open Source | Snyk has a broader ecosystem and free tier. Veracode SCA has stronger supply chain detection via Phylum and a registry firewall. |
| Socket | Socket focuses on behavioral analysis for npm/PyPI with a free open-source tier. Veracode SCA adds the registry firewall and integrates with a full AppSec platform. |
| Checkmarx SCA | Both offer supply chain detection. Veracode has the registry firewall; Checkmarx ties into the broader Checkmarx One platform. |
Veracode SCA alternatives
A few tools compete directly with Veracode SCA, each with a different angle.
Snyk Open Source
Snyk Open Source is the volume leader on developer-first SCA. Broader ecosystem coverage and a real free tier make it a first pick for teams that want CVE scanning plus automated fix PRs without an enterprise contract. Veracode SCA wins on AppSec-platform correlation and Phylum-derived malicious-package detection.
Black Duck SCA
Black Duck is the closest enterprise-parity alternative. Its vulnerability and license data go deeper than most competitors, especially for legal and M&A audits. Veracode SCA is lighter on license depth but carries tighter integration with Veracode SAST and DAST.
Mend SCA
Mend SCA is stronger on continuous dependency updates — it runs its own Renovate-style automation loop, not just security-driven fix PRs. Teams that treat dependency hygiene as a first-class problem often pick Mend over Veracode.
Checkmarx SCA
Checkmarx SCA folds into the Checkmarx One platform the same way Veracode SCA folds into Veracode’s. The decision usually comes down to which SAST vendor you already run.
Endor Labs
Endor Labs pushes reachability further than Veracode’s vulnerable-methods model, focusing on function-level call graphs across the full application graph. Endor and Veracode compete on the same “only exploitable CVEs” pitch, but Endor is narrower and deeper.
For the full landscape, see the open-source SCA tools hub and the SCA tools overview.
Veracode SCA pricing
Veracode does not publish SCA pricing on its public site. The product page routes every pricing intent to a contact-sales flow, and there is no self-serve tier or public plan table. Package Firewall is listed as a separate product on veracode.com/products/veracode-package-firewall/, so SCA bundles that include firewall coverage can come in at a different price point than SCA on its own.
There is no free tier. The 14-day trial Veracode promotes on sca.analysiscenter.veracode.com covers the platform’s scanning experience, not a persistent free SCA license. Expect to negotiate by application count and deployment model (SaaS vs on-prem) rather than per-developer seats.
For directional figures, Vendr aggregates public Veracode contract data at the platform level — see the Vendr footnote on this page’s frontmatter. Per site policy, I do not publish a fixed Veracode SCA list price here because none exists publicly.
For more context, see the guides on what is SCA and software supply chain security.
Veracode SCA FAQ
Is Veracode SCA different from Veracode SAST?
Yes. SCA scans third-party open-source dependencies for known CVEs, malicious packages, and license issues. SAST scans your own first-party source code for bugs and security anti-patterns. They ship as separate products inside the Veracode platform and produce separate findings, though Veracode correlates results across them.
Does Veracode SCA use Phylum’s technology?
Yes. Veracode acquired Phylum in January 2025 and has folded Phylum’s malicious-package detection and package firewall technology into Veracode SCA and the separate Veracode Package Firewall product. The 60% greater accuracy claim on Veracode’s SCA product page traces back to this ML-driven detection layer.
What is the Veracode Package Firewall?
Package Firewall is a separate Veracode product that acts as a proxy in front of package registries — npm, PyPI, and Maven — blocking packages that fail policy before a developer’s package manager can fetch them. It ships as its own SKU, not as a bundled SCA feature.
Is there a free tier?
No. Veracode SCA is commercial only, and the 14-day trial on sca.analysiscenter.veracode.com covers the scanning experience rather than a persistent free license. For an OSS-friendly alternative, look at Snyk Open Source’s free tier or OWASP Dependency-Check.
Does Veracode SCA export SBOMs?
Yes. Scan output can be exported in SPDX and CycloneDX SBOM formats, covering direct and transitive components. Reachability metadata from vulnerable-methods analysis is not part of the standard SBOM fields, so SBOM consumers see the component list but not the call-graph verdict.
Frequently Asked Questions
What is Veracode SCA?
What did the Phylum acquisition add?
Does Veracode SCA have a package firewall?
Can Veracode SCA work standalone?
* Pricing data from Vendr — anonymized contract values from real buyer transactions.