TruffleHog Alternatives
Thinking of switching from TruffleHog? Compare top competitors including Gitleaks, GitGuardian, Detect-Secrets, and GitHub Secret Scanning for secret detection.
- Gitleaks is the fastest TruffleHog alternative — it runs in milliseconds as a pre-commit hook while TruffleHog's credential verification makes it slower but more thorough.
- GitGuardian monitors 550+ secret types in real-time across public and private repositories, adding enterprise features like incident dashboards and automated remediation workflows.
- Detect-Secrets uses a plugin architecture that lets teams write custom detectors for internal secret formats that generic regex-based scanners miss.
- GitHub's built-in Secret Scanning is free for public repos but requires Advanced Security licensing for private repos and covers fewer patterns than dedicated tools.
TruffleHog alternatives are secret scanning tools that detect hardcoded credentials, API keys, and tokens in source code and git history. The best TruffleHog alternatives in 2026 are Gitleaks for fast pre-commit blocking, GitGuardian for managed dashboards and incident workflows, Detect-Secrets for baseline-aware legacy codebase scanning, and GitHub Secret Scanning for zero-configuration detection on GitHub repositories.
Why Look for TruffleHog Alternatives?
TruffleHog is one of the most capable open-source secret scanners available. It detects over 800 credential types, verifies whether discovered secrets are still active, and scans well beyond git repositories into S3 buckets, Docker images, Slack workspaces, and CI/CD platforms.
With 24,500 GitHub stars and 250,000+ daily scans, it has earned a strong reputation among security practitioners.
So why look elsewhere?
The most common reason is speed. TruffleHog’s credential verification feature — its biggest strength — adds latency to every scan.
For developers who want sub-second feedback from a pre-commit hook, that verification step gets in the way. You can disable it, but then you lose the main reason to pick TruffleHog over lighter tools.
Complexity is another factor. TruffleHog’s AGPL-3.0 license creates friction for some organizations with strict open-source policies.
The tool’s broad source coverage (S3, Docker, Slack, etc.) means more configuration surface area. Teams that only need git repository scanning may find simpler tools easier to maintain.
Some teams also need features TruffleHog’s open-source version lacks: centralized dashboards, team-based incident workflows, or integration with collaboration tools like Jira and Confluence. TruffleHog Enterprise offers these, but teams already evaluating commercial options have several alternatives worth comparing.
For a broader look at the secret scanning space, see the secret scanning tools comparison.
Top TruffleHog Alternatives
1. Gitleaks
Gitleaks is a lightweight secret scanner written in Go that focuses on speed above everything else. It scans git repositories for 150+ secret patterns using regex rules defined in a TOML configuration file.
Where TruffleHog might take minutes to scan and verify a large repository, Gitleaks finishes in seconds.
The tool shines as a pre-commit hook. Developers get instant feedback when they attempt to commit code containing secrets.
The hook blocks the commit and shows the offending lines. The official GitHub Action makes CI/CD integration straightforward, and SARIF output feeds directly into GitHub’s Security tab.
Gitleaks does not verify whether detected secrets are active. It tells you a string matches a known credential pattern, not whether that API key still works.
Many teams pair Gitleaks locally for fast feedback with TruffleHog in CI for deeper verification. The MIT license means no restrictions on commercial use.
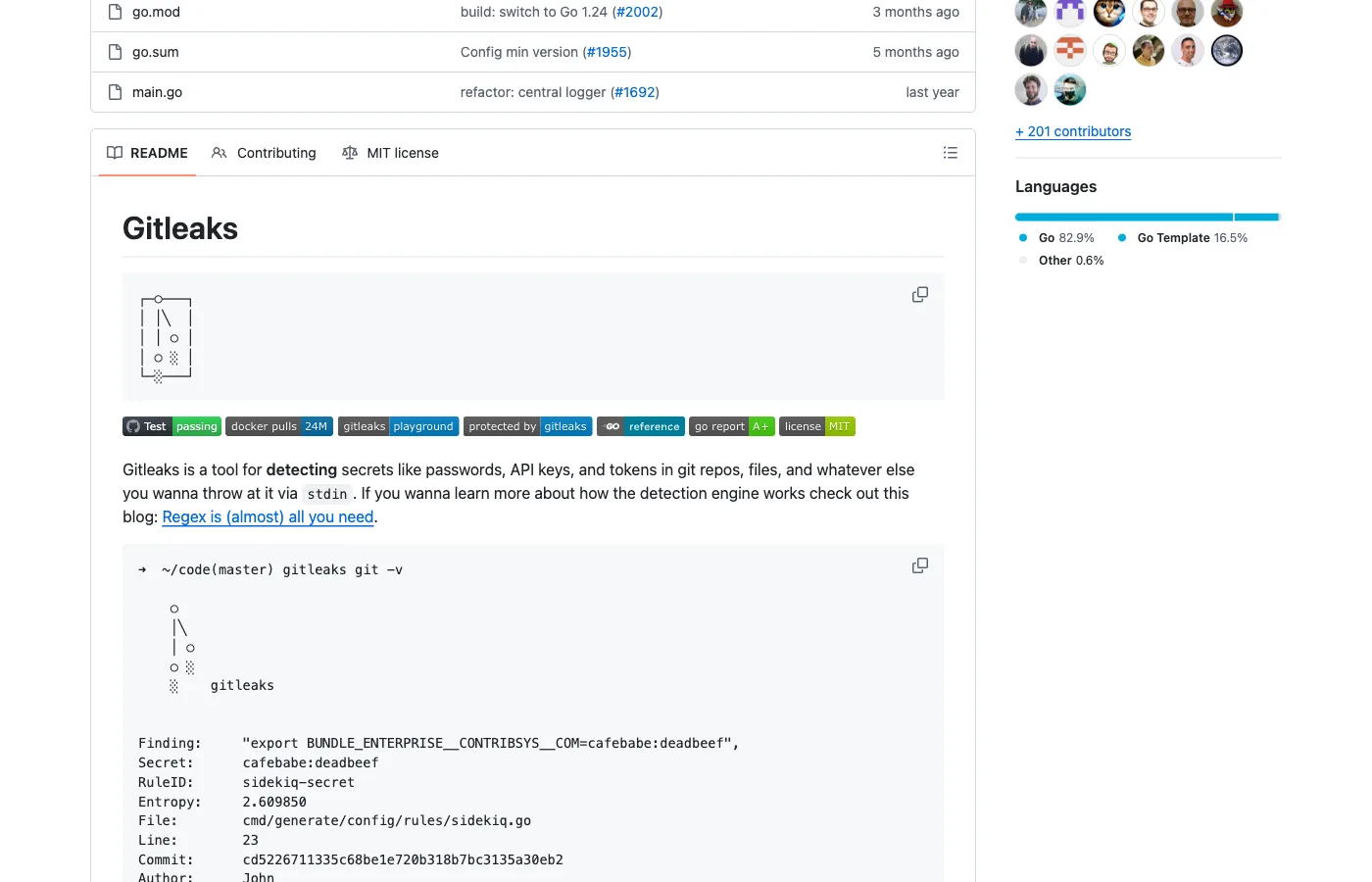
Best for: Developers wanting the fastest pre-commit secret scanning with minimal configuration overhead.
2. GitGuardian
GitGuardian is a commercial secrets detection platform that monitors repositories in real time. As the #1 security app on GitHub Marketplace, it detects 550+ secret types across GitHub, GitLab, Bitbucket, and collaboration tools like Slack, Jira, and Confluence.
GitGuardian’s main advantage over TruffleHog is the operational layer. The incident dashboard tracks every detected secret through a remediation workflow, from discovery to rotation to closure.
The ggshield CLI runs pre-commit hooks and CI/CD gates similar to TruffleHog, but the web dashboard gives security teams visibility across all repositories and developers. Non-Human Identity (NHI) governance tracks machine credentials organization-wide.
A free tier is available for individual developers. The platform validates detected secrets to confirm they are still active, similar to TruffleHog’s verification approach.
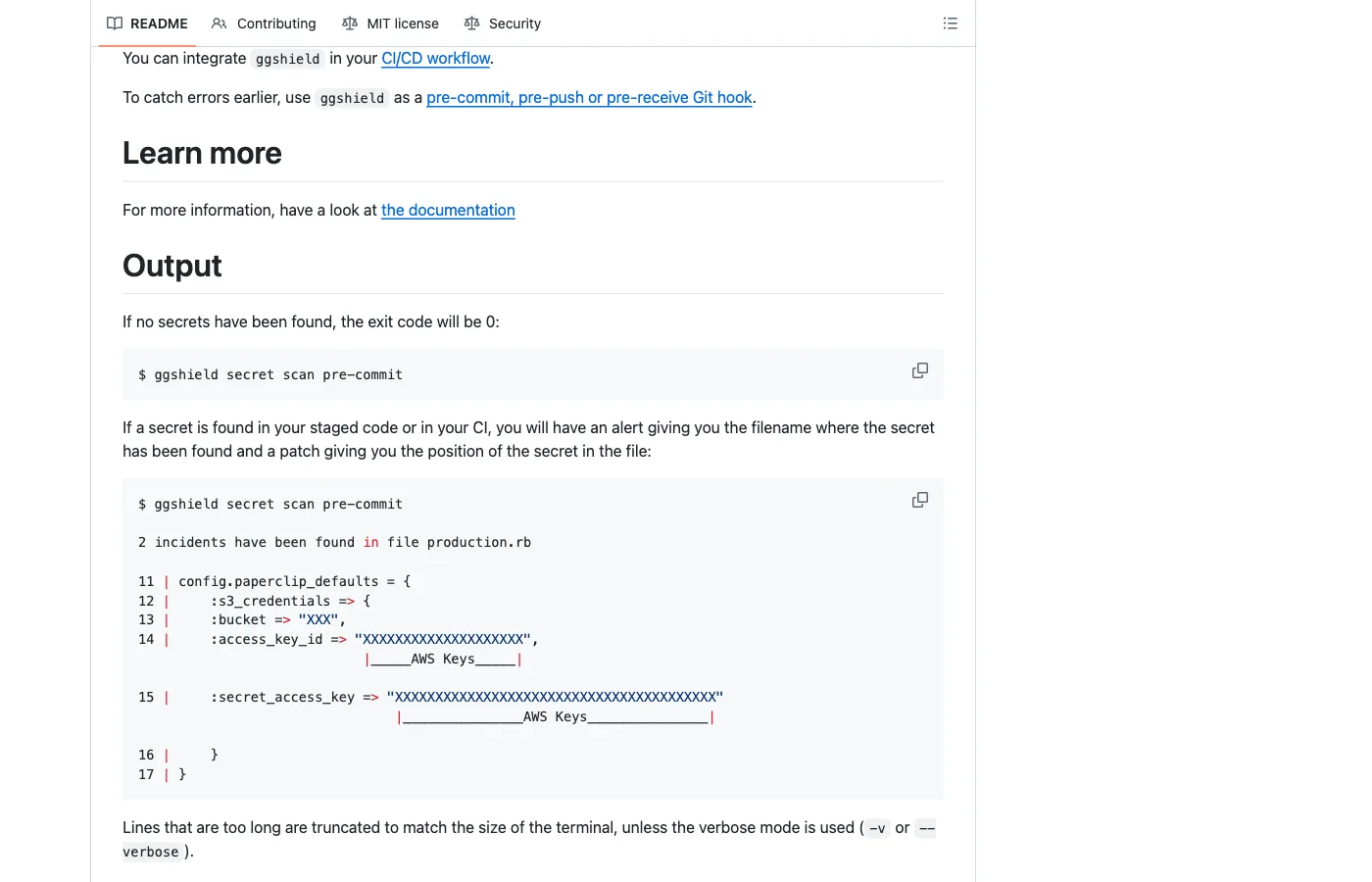
Best for: Security teams that need centralized incident management and remediation workflows alongside secret detection.
3. Detect-Secrets
Detect-Secrets takes a completely different approach from TruffleHog. Instead of reporting every secret in a repository, it maintains a baseline file of known secrets and only flags new ones.
This makes it practical for legacy codebases where hundreds of existing secrets cannot all be fixed at once.
Yelp built detect-secrets with a plugin architecture. Its 27 built-in detectors cover common patterns (AWS keys, GitHub tokens, Slack webhooks), and teams can write custom regex-based plugins for internal credential formats.
The tool scans git diffs rather than full repositories, keeping pre-commit hooks fast even on monorepos.
The trade-off is scope. Detect-secrets scans files and git history but does not cover S3 buckets, Docker images, or collaboration tools.
Optional verification exists via the --only-verified flag, but it is less mature than TruffleHog’s verification engine.
Best for: Enterprise teams with legacy codebases that need to prevent new leaks without remediating all existing secrets first.
4. GitHub Secret Scanning
GitHub’s built-in Secret Scanning detects credentials pushed to repositories by matching against patterns registered by 200+ service providers (AWS, Google Cloud, Stripe, Twilio, and others).
When a match is found, GitHub can notify the service provider to automatically revoke the credential. Push protection blocks commits containing detected secrets before they reach the repository.
The zero-configuration experience is the key advantage. There is nothing to install, configure, or maintain.
Alerts appear in the Security tab alongside Dependabot and code scanning results. The feature is free for public repositories and requires GitHub Advanced Security licensing for private repos.
The limitations are clear. It only covers GitHub repositories — not GitLab, Bitbucket, or any non-git sources.
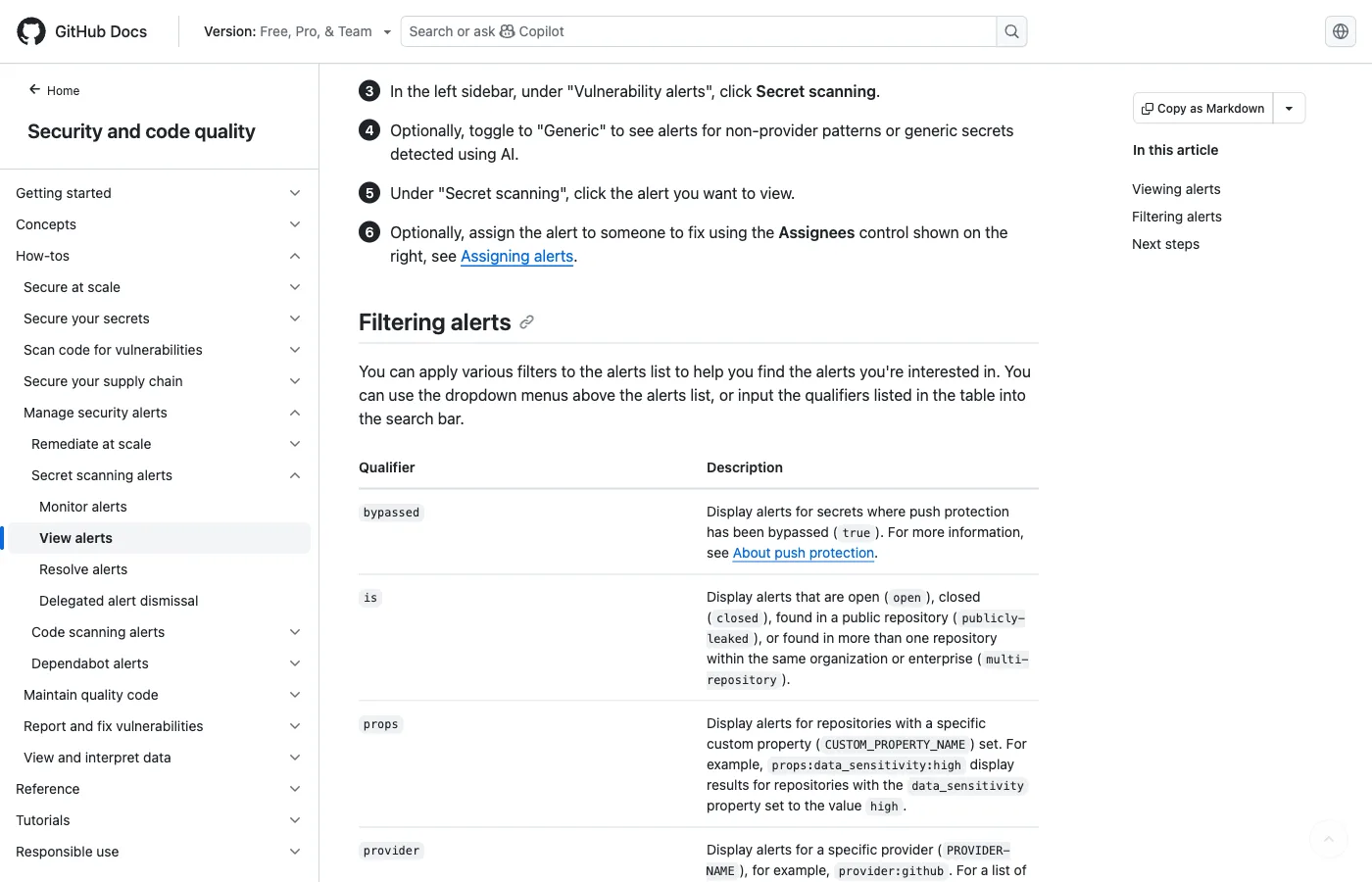
The 200+ partner patterns are fewer than TruffleHog’s 800+ detectors. Custom pattern support exists but is less flexible.
For GitHub-only teams with straightforward needs, it covers the baseline. For multi-platform environments, a dedicated scanner is necessary.
Best for: GitHub-native teams wanting zero-setup secrets detection with automatic credential revocation.
5. AWS git-secrets
AWS git-secrets is a lightweight tool built by AWS Labs specifically to prevent AWS credentials from being committed to git repositories. It installs git hooks that scan commits, commit messages, and merges for AWS access keys, secret keys, and credential file patterns.
The tool is intentionally narrow in scope. It catches AWS-specific secrets reliably but ignores everything else: no Stripe keys, no GitHub tokens, no database passwords.
Teams running primarily on AWS infrastructure sometimes use git-secrets alongside a broader scanner. The install-and-forget simplicity appeals to teams that want a quick safety net for their most sensitive credential type.
Best for: AWS-focused teams wanting a simple, targeted pre-commit hook for AWS credentials specifically.
6. SpectralOps (Check Point)
SpectralOps, acquired by Check Point in 2022, combines secrets detection with Infrastructure-as-Code misconfiguration scanning in a single binary. The tool scans source code, CI/CD pipelines, and configuration files for both hardcoded credentials and security misconfigurations.
Custom detectors and integrations with GitHub, GitLab, Bitbucket, and Azure DevOps are supported.
The dual-purpose approach reduces tool sprawl for teams that would otherwise run separate scanners for secrets and IaC issues. Check Point has folded SpectralOps into its broader CloudGuard platform, which may appeal to organizations already invested in the Check Point ecosystem.
Best for: Teams wanting combined secrets and IaC misconfiguration scanning from a single vendor.
7. Talisman
Talisman is a pre-commit hook tool developed by ThoughtWorks that validates outgoing changes for secrets, credentials, and sensitive file patterns. It runs as a git hook (pre-push or pre-commit) and checks file content, file names, and file sizes against configurable patterns.
Talisman takes a conservative approach and flags potentially sensitive files (like .pem, .key, .env) based on naming conventions in addition to scanning file content for credential patterns. The tool supports a checksum-based ignore mechanism for known false positives.
It is less feature-rich than TruffleHog or Gitleaks but serves well as a lightweight safety net at the commit level.
Best for: Teams wanting a simple, opinionated pre-commit hook that catches both credential patterns and sensitive file types.
Feature Comparison
| Tool | License | Patterns | Verification | Pre-commit | CI/CD | Multi-source |
|---|---|---|---|---|---|---|
| TruffleHog | OSS (AGPL-3.0) | 800+ | Yes (live API) | Yes | Yes | S3, Docker, Slack, CI |
| Gitleaks | OSS (MIT) | 150+ | No | Yes | Yes (GitHub Action) | No (git only) |
| GitGuardian | Freemium | 550+ | Yes | Yes (ggshield) | Yes | Slack, Jira, Confluence |
| Detect-Secrets | OSS (Apache-2.0) | 27 plugins | Optional | Yes | Yes | No (git/files only) |
| GitHub Secret Scanning | Free / GHAS | 200+ partners | Partner revocation | Push protection | Native | No (GitHub only) |
| AWS git-secrets | OSS (Apache-2.0) | AWS-specific | No | Yes | Manual | No (git only) |
| SpectralOps | Commercial | 100+ | Yes | Yes | Yes | IaC configs |
| Talisman | OSS (Apache-2.0) | Pattern + filename | No | Yes | Manual | No (git only) |
Two more TruffleHog alternatives worth knowing
Cycode — managed ASPM platform that bundles secret scanning with SCA, IaC, container, and CI/CD posture in one console. The wedge over TruffleHog is correlation: a leaked credential is tied back to the workload that uses it and the developer who owns it, not just reported as a finding. A fit when the goal is a single ASPM dashboard rather than a CLI scanner. License: commercial, contact-sales.
Semgrep Secrets — semantic secret detection layered on Semgrep’s SAST engine. Distinguishes real API keys from test fixtures by reading the surrounding code context (variable name, assignment pattern, surrounding function). Often catches secrets that regex-only scanners miss because they appear in unusual code shapes. License: commercial (Semgrep Team/Enterprise). A fit when Semgrep is already in the SAST stack and the team wants secrets detection without adding another vendor.
When to Stay with TruffleHog
TruffleHog remains the strongest choice in several scenarios.
You need credential verification. No other open-source tool matches TruffleHog’s ability to test discovered secrets against live APIs.
When you find an AWS key, TruffleHog tells you whether it still works and what permissions it has.
This eliminates false positives and tells your team exactly which secrets need emergency rotation versus which are already revoked. The --results=verified flag filters output to only active credentials, saving hours on large scans.
You scan beyond git. If secrets could be hiding in S3 buckets, Google Cloud Storage, Docker images, Jenkins servers, Elasticsearch clusters, or Postman workspaces, TruffleHog is the only open-source option that covers all these sources natively.
Gitleaks and detect-secrets are limited to git repositories and local files.
You need the broadest detector coverage. TruffleHog’s 800+ credential detectors outpace every alternative on this list.
For organizations running diverse infrastructure with many SaaS integrations, that breadth reduces the chance of a secret type slipping through undetected.
You want identity mapping. TruffleHog maps each discovered secret to a specific user account, service account, or API key.
This context helps security teams assess blast radius and contact credential owners directly, a workflow that pattern-only scanners cannot support.
For teams that need TruffleHog’s depth but also want a managed dashboard and team workflows, TruffleHog Enterprise adds those capabilities on top of the open-source scanning engine.
Visit these tools
- Gitleaks on GitHub — fast OSS pre-commit scanner
- GitGuardian — commercial platform with dashboards and incident workflows
- Detect-Secrets on GitHub — Yelp-built, baseline-aware OSS scanner
- GitHub Secret Scanning — native GitHub feature
- TruffleHog on GitHub · TruffleHog Enterprise
- SpectralOps (Check Point) · Talisman on GitHub · AWS git-secrets
See also: GitGuardian Alternatives for a comparison focused on commercial secret scanning platforms.
Frequently Asked Questions
What is the best free alternative to TruffleHog?
Is Gitleaks better than TruffleHog?
Does GitHub have built-in secret scanning?
Which secret scanner has the fewest false positives?

Founder, AppSec Santa
Years in application security. Reviews and compares 215 AppSec tools across 12 categories to help teams pick the right solution. More about me →