- Trivy is completely free (Apache 2.0, 32,200+ GitHub stars) with no usage limits; Snyk offers a free tier for individuals but requires paid plans for team features like custom rules and SSO.
- Snyk Open Source generates automated fix pull requests and uses reachability analysis to prioritize vulnerabilities that your code actually calls; Trivy reports vulnerabilities but does not suggest fixes.
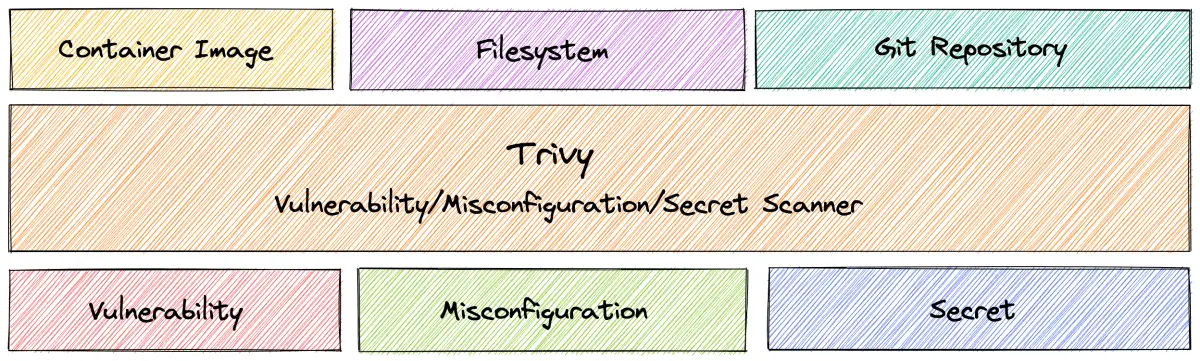
- Trivy scans dependencies, containers, IaC, secrets, and licenses from a single binary; Snyk covers SCA, SAST, container, IaC, and DAST as separate products under one platform.
- Snyk's curated vulnerability database added 24,000+ new vulnerabilities in 2024 (per Snyk's annual report) and includes reachability and exploit maturity data; Trivy uses Aqua's trivy-db with daily updates from public advisory sources.
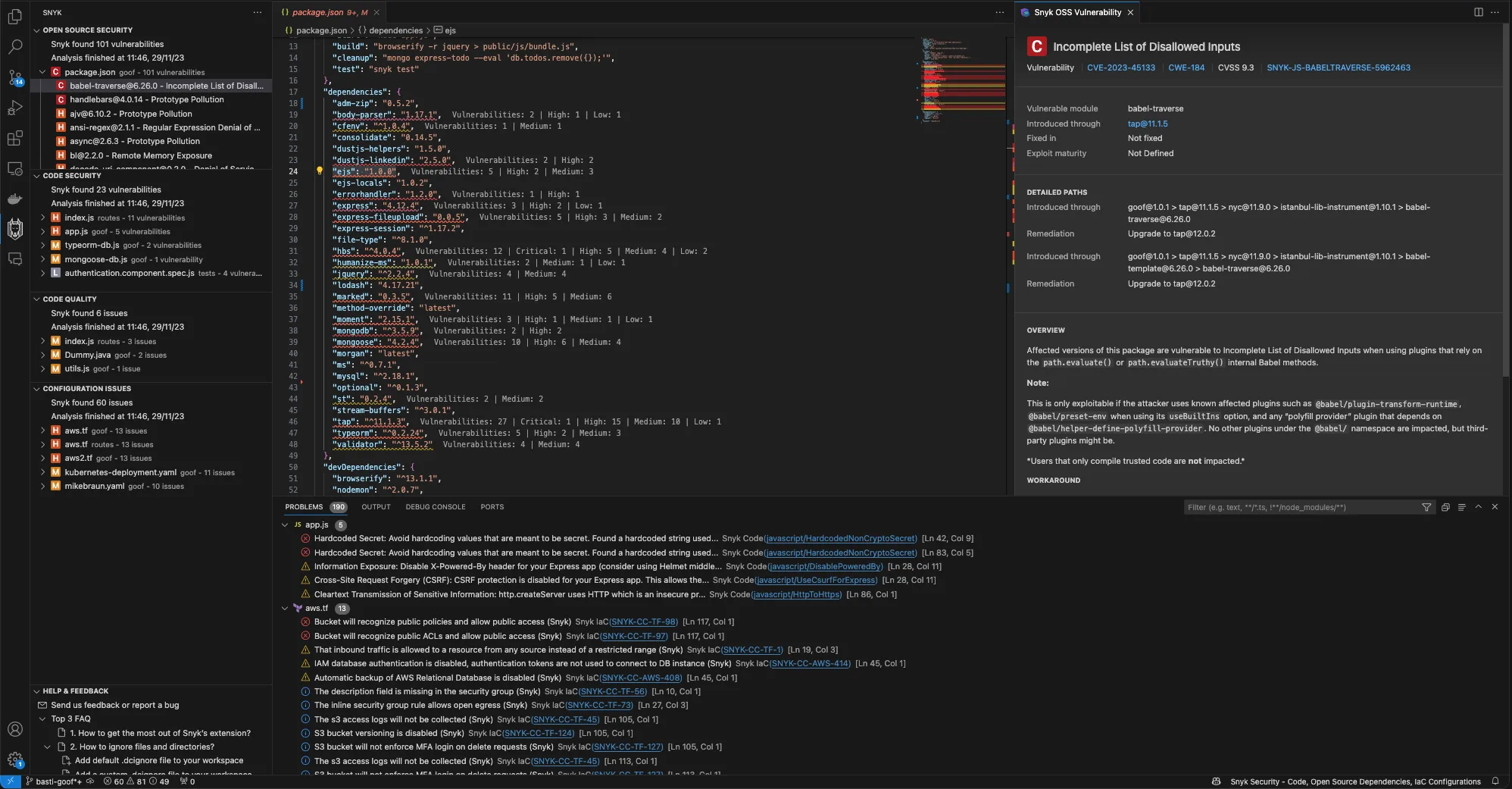
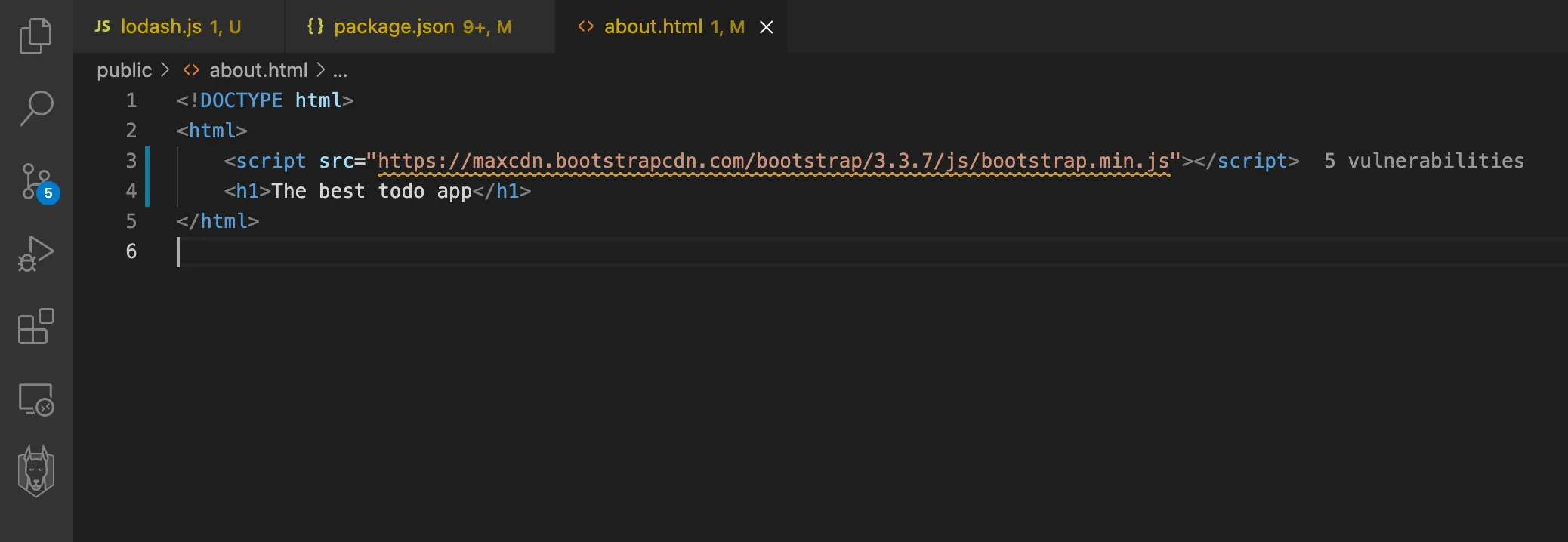
- Both tools support 10+ language ecosystems, integrate with GitHub Actions and GitLab CI, and offer IDE extensions; Snyk's VS Code, IntelliJ, and Eclipse plugins are more mature than Trivy's VS Code and JetBrains extensions.
Which Is Better: Trivy or Snyk?
Trivy is a free, open-source security scanner (Apache 2.0, 32,200+ GitHub stars) that detects vulnerabilities in dependencies, containers, IaC, secrets, and licenses from a single binary with no usage limits. Snyk is a commercial developer security platform that combines SCA, SAST, container, IaC, and DAST scanning with automated fix pull requests and reachability analysis.
Pick Trivy if you need a cost-free scanner that covers multiple security domains from one CLI. Pick Snyk if automated remediation and tighter developer workflow integration justify the investment.
What Are the Key Differences?
| Feature | Trivy | Snyk |
|---|---|---|
| License | Free (Apache 2.0) | Freemium (free tier + paid plans) |
| GitHub Stars | 32,200+ | N/A (proprietary) |
| Maintained By | Aqua Security | Snyk Ltd |
| SCA (Dependency Scanning) | Yes | Yes (Snyk Open Source) |
| SAST (Code Scanning) | No | Yes (Snyk Code) |
| Container Scanning | Yes | Yes (Snyk Container) |
| IaC Scanning | Yes (Terraform, CloudFormation, K8s, Helm, Docker, ARM, Ansible) | Yes (Terraform, CloudFormation, K8s, Helm, ARM) |
| DAST | No | Yes (Snyk API & Web) |
| Secrets Detection | Yes | Yes (via Snyk Code) |
| License Compliance | Yes | Yes (Team/Enterprise plans) |
| Automated Fix PRs | No | Yes |
| Reachability Analysis | No | Yes |
| AI Fix Suggestions | No | Yes (DeepCode AI) |
| SBOM Generation | CycloneDX, SPDX | Via API/dashboard |
| Vulnerability Database | Aqua trivy-db (daily updates) | Curated DB (24k+ new vulns in 2024) |
| Language Ecosystems | Go, Java, Node.js, Python, Ruby, Rust, PHP, .NET, Dart, Elixir, Swift | npm, Maven, Gradle, pip, Go modules, NuGet, RubyGems, Composer, Cocoapods, Cargo, Hex |
| IDE Integration | VS Code, JetBrains | VS Code, IntelliJ, Eclipse |
| Risk Prioritization | Severity-based (CVSS) | Reachability + exploit maturity + EPSS/CVSS |
| Custom Policies | Rego (OPA) | Snyk policy engine (paid plans) |
| Output Formats | Table, JSON, SARIF, CycloneDX, SPDX, template | Dashboard, JSON, SARIF, HTML |
| GitHub Action | aquasecurity/trivy-action | snyk/actions |
| Kubernetes Operator | Yes (Trivy Operator) | Yes (Snyk Controller) |
| Written In | Go | Proprietary |
Trivy vs Snyk: How Do They Compare?
How Do Trivy and Snyk Scan Dependencies?
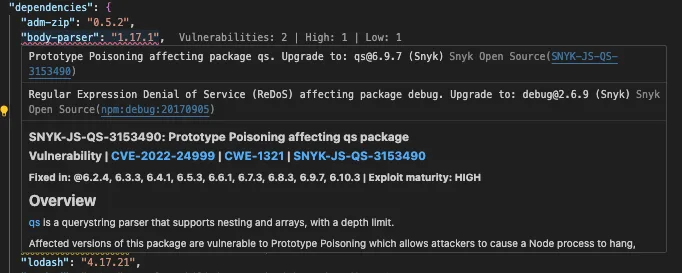
Trivy and Snyk both scan package manifests and lock files to find known vulnerabilities in third-party dependencies, but they differ in what happens after detection.
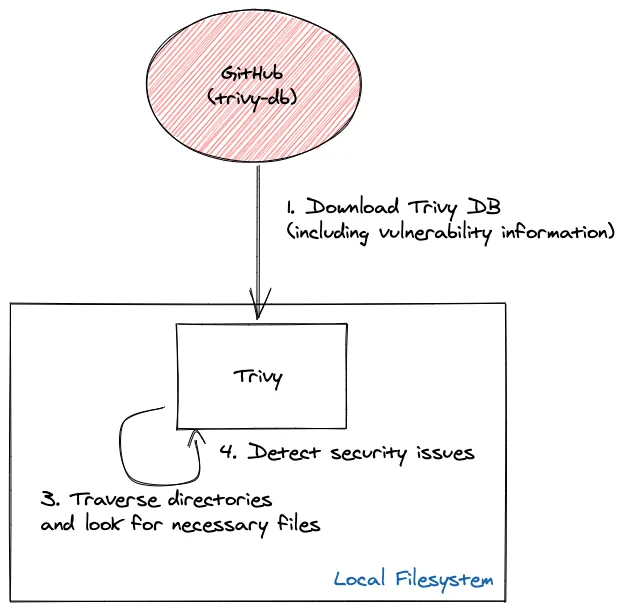
Trivy reads lock files (package-lock.json, go.sum, Gemfile.lock, requirements.txt, pom.xml, and others) and checks them against its trivy-db database. You run trivy fs --scanners vuln . on any project directory and get results immediately with no account required.
Snyk Open Source performs the same scan but adds automated fix pull requests and reachability analysis on top — two capabilities Trivy does not offer.
When Snyk finds a vulnerable dependency, it can open a PR in your Git repository with the exact version upgrade needed. Reachability analysis checks whether your code actually calls the vulnerable function — an important signal because many flagged dependencies contain vulnerabilities in code paths your application never touches.
Trivy reports what is vulnerable. Snyk reports what is vulnerable, whether it is reachable, and how to fix it.
For teams that want actionable results without manual triage, Snyk’s workflow cuts remediation time.
Which Tool Has Better Vulnerability Intelligence?
Snyk’s vulnerability database and Trivy’s trivy-db take fundamentally different approaches to coverage and curation.
Snyk maintains a curated database backed by a dedicated security research team that added 24,000+ new vulnerabilities in 2024, according to Snyk’s annual report.
The database includes proprietary metadata — exploit maturity, reachability data, and EPSS/CVSS composite scoring — and evaluates over a dozen factors to rank findings by actual business impact.
Trivy uses Aqua Security’s trivy-db, which pulls from multiple public advisory sources and updates daily. A separate trivy-java-db handles JAR and WAR file identification.
The database covers OS packages and language-specific advisories across major ecosystems. Trivy’s prioritization is severity-based: you filter by LOW, MEDIUM, HIGH, or CRITICAL using CVSS scores.
The practical difference is triage speed. Snyk’s reachability and exploit maturity data narrow the list to vulnerabilities worth acting on.
Trivy gives you the raw findings and lets you decide. Teams with dedicated security engineers may prefer Trivy’s open data; teams that want the platform to handle prioritization lean toward Snyk.
How Do They Fit into Developer Workflows?
Snyk and Trivy integrate into developer workflows through different models: Snyk meets developers inside their IDE, while Trivy meets them in the terminal and CI pipeline.
Snyk was built as a developer tool from the start, with IDE plugins for VS Code, IntelliJ, and Eclipse that surface vulnerabilities as you write code.
Git integrations with GitHub, GitLab, and Bitbucket monitor repositories continuously and open fix PRs automatically. The unified dashboard shows findings across SCA, SAST, container, and IaC in one view.
Trivy is a CLI-first tool. It runs in terminals, CI/CD pipelines, and Kubernetes clusters.

Aqua Security provides a VS Code extension and a JetBrains plugin for scanning directly in the IDE, though these are less mature than Snyk’s IDE integrations.
For CI/CD, the official GitHub Action (aquasecurity/trivy-action) and Docker images handle most pipeline setups.
Snyk reduces context-switching by meeting developers where they work. Trivy stays out of the way and fits into any pipeline that can run a shell command.
Teams that want security feedback in the IDE prefer Snyk; teams that want a fast CLI scanner for automation prefer Trivy.
What Else Can Each Tool Scan Beyond SCA?
Both Trivy and Snyk extend well beyond dependency scanning, though they package their capabilities differently. Trivy covers vulnerabilities, IaC misconfigurations, secrets, and licenses in a single binary.
After absorbing tfsec (the Aqua Security-maintained Terraform linter), it scans Terraform, CloudFormation, Kubernetes manifests, Helm charts, Dockerfiles, ARM templates, and Ansible playbooks. The Trivy Operator runs continuous scans inside Kubernetes clusters.
SBOM generation in CycloneDX and SPDX formats is built in.
Snyk covers SCA (Snyk Open Source), SAST (Snyk Code), container scanning (Snyk Container), IaC (Snyk IaC), DAST (Snyk API & Web), and AI-generated code (Snyk Studio). DeepCode AI powers code analysis across 19+ languages with AI-generated fix suggestions.
Neither tool stops at SCA. Trivy consolidates scanning types into one open-source binary.
Snyk consolidates them into one commercial platform with more automation per product. The trade-off is cost: Trivy is free regardless of team size; Snyk’s advanced features require paid plans.
When Should You Choose Trivy vs Snyk?
Choose Trivy if…
- Budget is a primary concern — Trivy is free with no usage limits, scan caps, or feature restrictions
- You want a single binary that handles dependency scanning, IaC checks, secrets detection, and license compliance
- Your team runs Kubernetes and needs an operator for continuous cluster scanning
- SBOM generation in CycloneDX or SPDX is a compliance requirement
- You prefer open-source tools with transparent vulnerability databases
- CLI-based automation in CI/CD pipelines is your primary integration pattern
Choose Snyk if…
- Automated fix pull requests and reachability analysis will cut your team’s triage time
- Developer experience matters — IDE plugins and Git integrations surface findings where your team works
- You need SAST alongside SCA from the same platform (Snyk Code + Snyk Open Source)
- A curated vulnerability database with exploit maturity and reachability metadata is worth the investment
- Your organization wants a single vendor for SCA, SAST, container, IaC, and DAST
- Gartner MQ recognition and enterprise features (SSO, custom policies, advanced reporting) are requirements
Many teams use both: Trivy in CI/CD for fast, free scanning across containers and IaC, and Snyk for SCA with automated remediation in developer workflows. The tools complement each other when budget allows.
For more options, browse AppSec Santa’s SCA tools category.
Frequently Asked Questions
Is Trivy better than Snyk for SCA?
Is Trivy free and is Snyk free?
Can Trivy replace Snyk?
Which tool has a better vulnerability database?
Do Trivy and Snyk support SBOM generation?

+7 Years in AppSec
10+ years in application security. Reviews and compares 208 AppSec tools across 11 categories to help teams pick the right solution. More about me →
