Trivy is an open-source security scanner by Aqua Security. It scans container images, filesystems, git repositories, virtual machine images, and Kubernetes clusters for vulnerabilities, misconfigurations, secrets, and license issues. One binary, five target types, four scanner engines.
With 34,600+ GitHub stars, 513+ contributors, and 178+ releases, it is the most-starred open-source security scanner on GitHub.
Note: Trivy's official GitHub Action (aquasecurity/trivy-action) was compromised twice in March 2026 by the TeamPCP supply chain campaign — always pin to a specific commit SHA rather than mutable version tags like @v1 or @master.
v0.70.0 (April 17, 2026): GPG signing keys for the deb and rpm repositories were rotated as a follow-up to an Aqua security incident. Re-import the new key before running
apt updateoryum updateon pipelines that install Trivy through the official package repositories. Other highlights: Go-trimpathbinary version detection via ELF symbol table (fewer “unknown version” results on stripped binaries), a PEP 751pylock.tomlparser (pip 25.x emits this file), and Azure misconfiguration scanning parity for ARM-based AKS clusters.
What Trivy does
Trivy started as a container vulnerability scanner. It has since absorbed tfsec (Terraform security scanner) and grown into a multi-target tool that covers most of what DevSecOps teams need from a single CLI.
The scanner works locally, in CI/CD pipelines, and as a Kubernetes operator. Written in Go, it ships as a static binary with no dependencies. Install it, point it at a target, get results.
What are Trivy’s key features?
The matrix below combines 5 target types (container images, filesystems, git repos, VM images, Kubernetes clusters) with 4 scanner engines (vulnerabilities, misconfigurations, secrets, licenses). One binary covers every cell.
| Feature | Details |
|---|---|
| Targets | Container images, filesystems, git repos, VM images, Kubernetes clusters, SBOMs |
| Scanners | Vulnerabilities, misconfigurations, secrets, licenses |
| OS coverage | Alpine, Debian, Ubuntu, RHEL, CentOS, Amazon Linux, SUSE, Photon, Windows |
| Language ecosystems | Go, Java, Node.js, Python, Ruby, Rust, PHP, .NET, Dart, Elixir, Swift |
| IaC types | Terraform, CloudFormation, Kubernetes, Helm, Dockerfile, ARM, Ansible (CIS -aligned) |
| Output formats | Table, JSON, SARIF, CycloneDX, SPDX, template-based custom formats |
| SBOM generation | CycloneDX and SPDX for container images and filesystems |
| Policy engine | Rego (OPA) for custom misconfiguration checks |
| Kubernetes | Cluster scanning, workload assessment, KBOM (Kubernetes Bill of Materials) |
| Databases | trivy-db (general vulnerabilities), trivy-java-db (JAR/WAR identification) |
Container image scanning
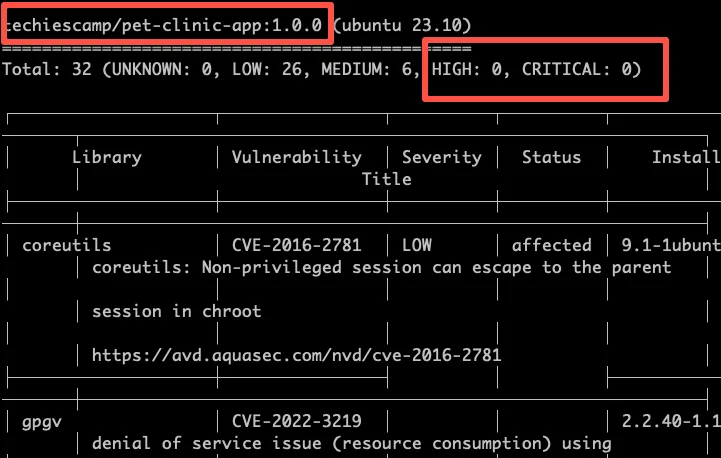
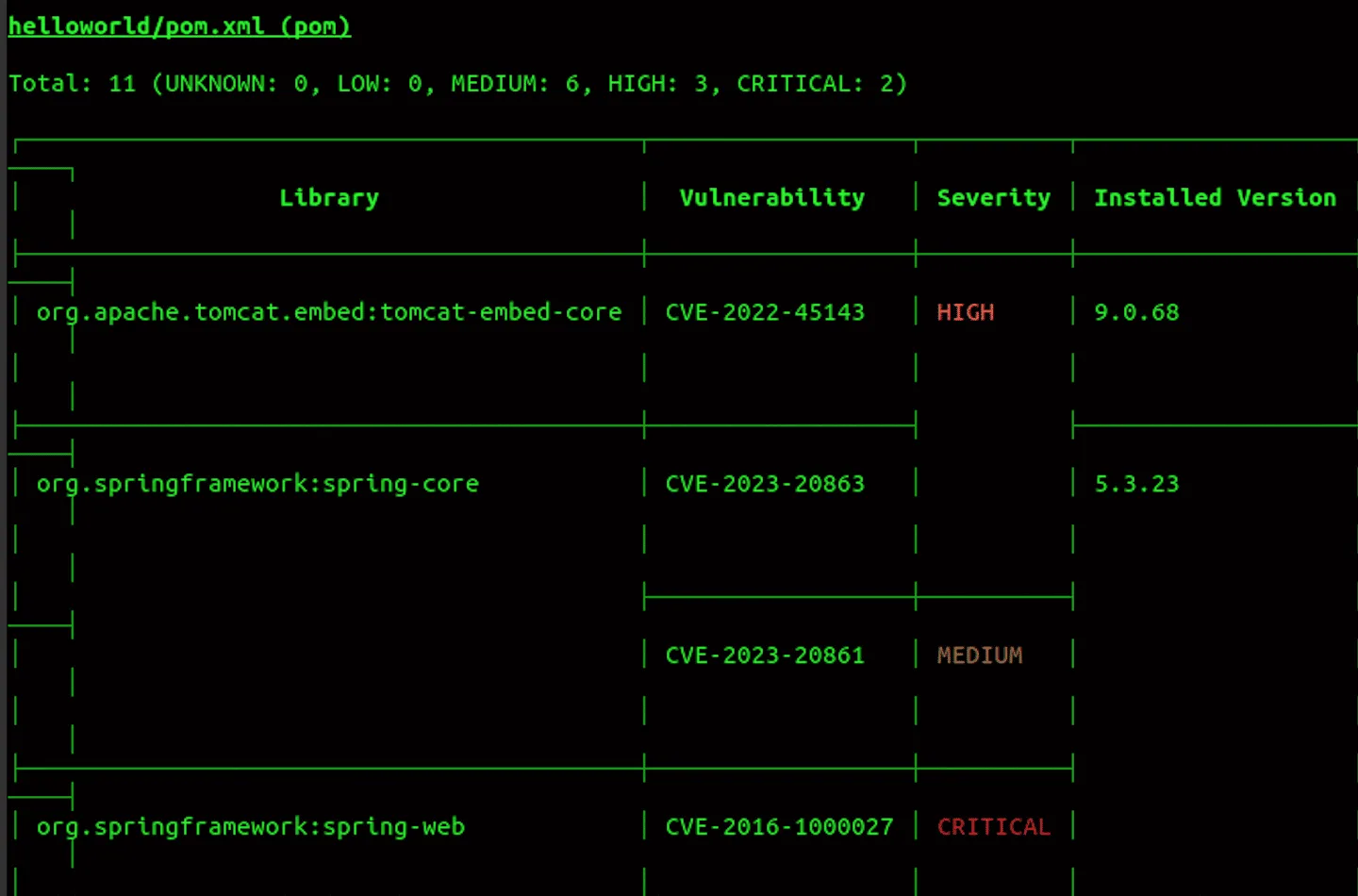
Trivy scans Docker and OCI images for known vulnerabilities in both OS packages and application dependencies. Point it at any image reference and it pulls the layers, extracts packages, and checks them against its vulnerability database.
Results include the CVE ID, severity, installed version, fixed version (if available), and a link to the advisory. You can filter by severity to focus on HIGH and CRITICAL findings only.
IaC misconfiguration scanning
After absorbing tfsec, Trivy’s misconfiguration scanner covers Terraform, CloudFormation, Kubernetes manifests, Helm charts, Dockerfiles, ARM templates, and Ansible playbooks.
Drop your IaC files in a directory and run trivy config ./. Trivy auto-detects the file types and applies the right checks. No need to specify which IaC format you’re using.
Custom checks use Rego (the OPA policy language). Write your own rules and place them alongside the built-in check set.
Note: tfsec was fully merged into Trivy — all tfsec check IDs (like AVD-AWS-0086) work unchanged in Trivy's misconfiguration scanner. The tfsec repository now redirects to Trivy; no separate installation needed.
Kubernetes cluster scanning
Trivy scans running Kubernetes clusters directly. The trivy k8s command connects to your cluster and checks workloads for vulnerabilities, misconfigurations, and secrets.

Two report modes are available: summary gives a quick overview per namespace, and all provides the full detail for every resource. The Trivy Operator can run these scans continuously inside the cluster.
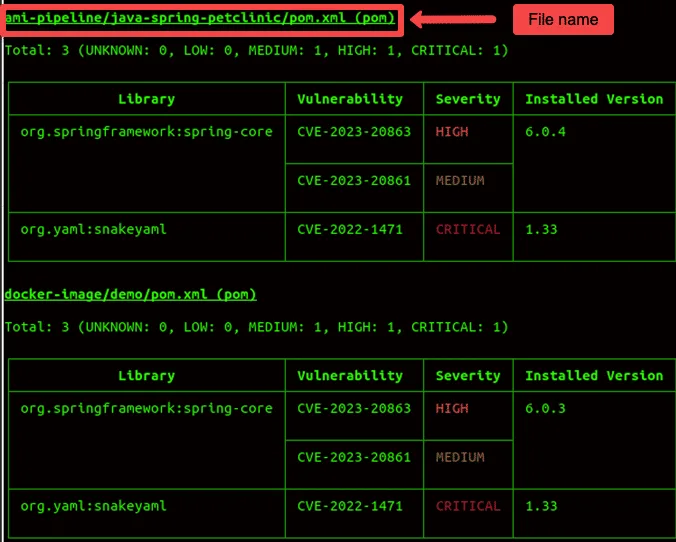
Filesystem and repository scanning
Trivy scans local directories and remote git repositories for vulnerabilities in application dependencies. It reads lock files (package-lock.json, go.sum, Gemfile.lock, requirements.txt, and others) to identify packages and check them against known CVEs.
The filesystem scanner also picks up secrets and IaC misconfigurations in the same pass. Run trivy fs --scanners vuln,secret,misconfig . to get everything at once.
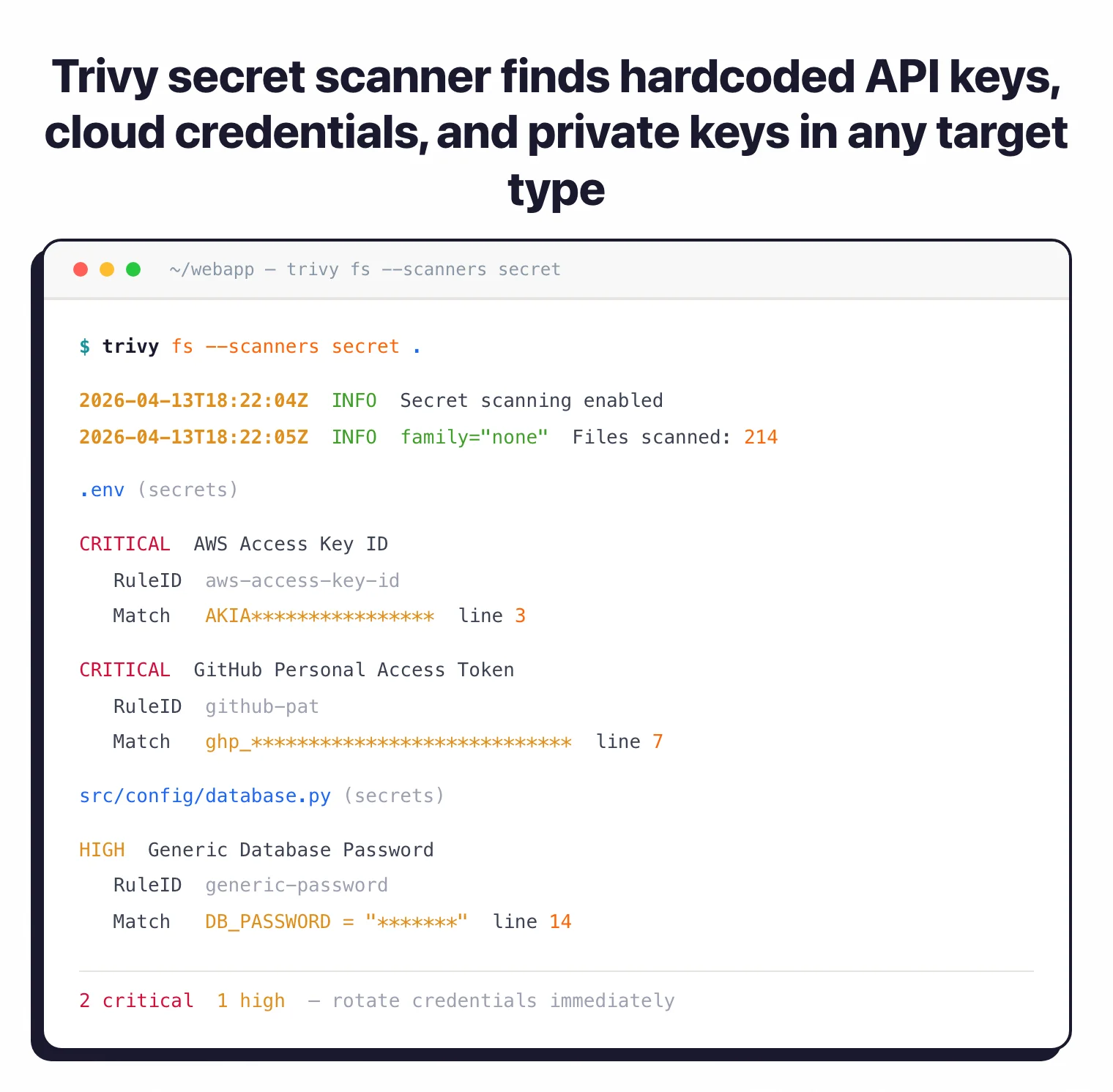
Secret detection
The secret scanner uses regex patterns to find hardcoded credentials: API keys, passwords, private keys, cloud access keys, and database connection strings. It runs against any target type — container images, filesystems, or repositories.
SBOM generation
Trivy generates Software Bill of Materials in CycloneDX and SPDX formats. Useful for supply chain compliance, vulnerability tracking, and responding to incidents like Log4Shell where you need to know which images contain a specific library.
# CycloneDX format
trivy image --format cyclonedx myapp:latest > sbom.json
# SPDX format
trivy image --format spdx-json myapp:latest > sbom.spdx.json
VM image scanning
Trivy also scans virtual machine images. Amazon Machine Images (AMIs) and other VM formats go through the same vulnerability database used for container scanning.
How do I get started with Trivy?
brew install trivy), apt (sudo apt-get install trivy), Docker (docker run aquasec/trivy), or download the binary from GitHub releases. Available for Linux, macOS, and Windows.trivy image nginx:latest to check a container image for vulnerabilities. Add --severity HIGH,CRITICAL to filter results.trivy config ./terraform/ to check Terraform files for misconfigurations. Trivy auto-detects the IaC type.trivy k8s --report summary cluster to assess all workloads in your cluster.trivy image --format cyclonedx myapp:latest > sbom.json to produce a CycloneDX bill of materials.CI/CD integration
Trivy fits into any CI/CD pipeline. The official GitHub Action (aquasecurity/trivy-action) handles container image and IaC scanning with SARIF output for GitHub Code Scanning. Important: After the March 2026 supply chain compromise, always pin the action to a specific commit SHA (e.g., aquasecurity/trivy-action@<commit-sha>) rather than using mutable version tags.
For GitLab CI, the Docker image runs in a security stage. Jenkins and CircleCI work through the CLI binary.
Exit codes control whether builds pass or fail: set --exit-code 1 with --severity HIGH,CRITICAL to fail on serious findings only.
Pro tip: Use trivy image --exit-code 1 --severity HIGH,CRITICAL myapp:latest to fail CI builds only when HIGH or CRITICAL vulnerabilities are found. This avoids blocking deployments over LOW and MEDIUM findings that can be triaged separately.
What does Trivy integrate with?
Configuration
Create a trivy.yaml file to set defaults:
severity:
- HIGH
- CRITICAL
vulnerability:
ignore-unfixed: true
misconfiguration:
terraform:
exclude-downloaded-modules: true
# To skip specific checks, use a .trivyignore file:
# Create .trivyignore with check IDs (one per line):
# AVD-AWS-0086
# Or use CLI: trivy config --skip-checks AVD-AWS-0086 .
The ignore-unfixed option hides vulnerabilities with no available patch. Useful for reducing noise in reports when you can only act on fixable issues.
Individual findings can be suppressed with a .trivyignore file listing CVE IDs or check IDs, one per line.
When to use Trivy
Trivy works well when you want a single scanner that handles containers, IaC, secrets, and dependencies without stitching together separate tools. Getting all of that from one binary is why most teams reach for it first.
It’s the default scanner in Harbor (the CNCF container registry) and has integrations with GitLab, AWS Security Hub, and the Kubernetes operator ecosystem. If you’re already in that stack, Trivy slots in with minimal setup.
For IaC-specific scanning with a larger policy library, Checkov or KICS offer more checks and compliance framework mappings. For commercial support and curated fix recommendations, Snyk IaC is worth evaluating.
But if you want one open-source tool that does most of the job, Trivy is the obvious starting point.
For a broader view of IaC security strategy, see the cloud infrastructure security guide . Browse other IaC security tools to compare options.
Trivy and tfsec — what changed in 2023
Aqua Security archived the standalone tfsec project in 2023 and merged its Terraform misconfiguration checks directly into Trivy. The tfsec README now leads with “tfsec is now part of Trivy” and the GitHub repository points users to the Trivy migration guide.
The transition is mechanical for most teams. Every tfsec check ID — including familiar ones like AVD-AWS-0086 for unencrypted S3 buckets — works unchanged in Trivy’s misconfiguration scanner. The only meaningful change is the command surface: replace tfsec . with trivy config . and the same checks run against the same Terraform sources.
What shipped along with the merge: broader IaC coverage (CloudFormation, Helm, Dockerfile, ARM, Ansible) under a single binary, plus shared Rego policy support so custom rules written for one engine work in the other. If you maintained a .tfsec.yml exclusion file, Trivy reads .trivyignore and CLI --skip-checks flags as the modern equivalents.
Who uses Trivy
Trivy ships as the default scanner inside Harbor , the CNCF-graduated container registry, which means every Harbor operator runs Trivy on push. That single integration footprint puts Trivy in front of more clusters than most commercial scanners reach.
Beyond Harbor, the install surface is wide. AWS Security Hub ingests Trivy SARIF output through a published integration. The official aquasecurity/trivy-action GitHub Action and the GitLab CI template both wrap the binary for pipeline use. The Trivy Operator runs continuous scans inside Kubernetes clusters and writes findings back as custom resources.
Large open-source projects use Trivy in their own release pipelines — Kubernetes itself, Argo CD, and many CNCF projects gate releases on Trivy scans. Aqua Security maintains the upstream code and offers a paid Aqua Platform on top, but the scanner itself stays Apache 2.0 with no upsell gating between free and commercial use.
Getting started with Trivy
Trivy installs via Homebrew on macOS (brew install trivy), apt or yum on Linux, or Docker (docker run aquasec/trivy). trivy --version confirms the install.
A first scan covers four common targets:
- Container image:
trivy image nginx:latest— pulls the image, scans OS packages, reports vulnerabilities by severity. - Filesystem / IaC:
trivy fs .for SCA on local code,trivy config .for Terraform, Kubernetes, and Dockerfile misconfigurations. - Kubernetes cluster:
trivy k8s --report summary cluster— scans running workloads, RBAC, and images in the cluster. - SBOM ingest:
trivy sbom path/to/sbom.jsoningests an existing CycloneDX or SPDX file.
The IaC misconfiguration check IDs match the legacy tfsec catalog one-to-one after the 2023 merge, so existing tfsec rule references carry over. SARIF output (-f sarif) feeds GitHub Code Scanning directly, and AWS Security Hub also ingests Trivy SARIF through a published integration.