Terrascan is an open-source static code analyzer for Infrastructure as Code.
Built by Tenable, it ships 500+ security policies and uses the Open Policy Agent (OPA) engine for custom rules written in Rego.
The project accumulated 5.2k GitHub stars and 542 forks before being archived.
Terrascan was archived by its maintainers on November 20, 2025. The GitHub repository is now read-only — no new issues, pull requests, or releases are accepted.
The documentation site (runterrascan.io) redirects to Tenable’s commercial cloud security page. The codebase remains available under Apache 2.0 for community forks. For actively maintained alternatives, see Checkov , KICS , or Trivy .
What Terrascan Does
Terrascan scans IaC files against a policy library and flags security misconfigurations before they reach production.
It covers seven IaC formats: Terraform HCL2, CloudFormation, Kubernetes manifests, Helm v3, Kustomize, ARM Templates, and Dockerfiles.
The scanner also handles Docker image vulnerability detection across ECR, Azure Container Registry, GCP Artifact Registry, and Harbor.
Policies map to compliance frameworks including CIS Benchmarks , NIST 800-53 , PCI-DSS, HIPAA, and SOC 2.
Each policy includes a risk description and remediation steps.
Key Features
| Feature | Details |
|---|---|
| Policy count | 500+ built-in policies across all supported cloud providers |
| Policy engine | Open Policy Agent (OPA) with Rego language |
| IaC formats | Terraform HCL2, CloudFormation, K8s, Helm v3, Kustomize, ARM, Dockerfile |
| Cloud providers | AWS, Azure, GCP, GitHub |
| Compliance mapping | CIS Benchmarks, NIST 800-53, PCI-DSS, HIPAA, SOC 2 |
| Output formats | Human-readable, JSON, SARIF, YAML, XML |
| K8s admission controller | Validating webhook blocks non-compliant resources at deploy time |
| Drift detection | Compares IaC definitions against live cloud resources |
| Container scanning | Docker image vulnerability detection (ECR, ACR, GAR, Harbor) |
| Server mode | Runs as HTTP API server for integration with other tools |
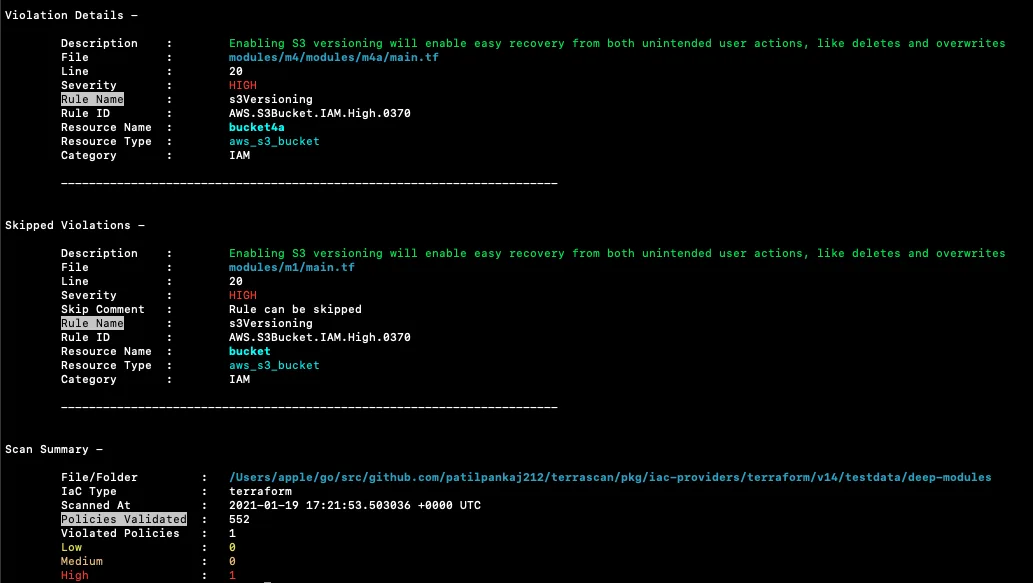
Scan Output
Terrascan reports violations with the policy name, description, severity level, file path, and line number. Exit codes indicate the result: 0 for clean, 3 for violations found, 4 for errors, 5 for both.
Custom Policies with Rego
Teams write their own rules in Rego and place them alongside the built-in policy set. Useful for things standard benchmarks don’t cover: naming conventions, tagging policies, region restrictions, or internal network rules.
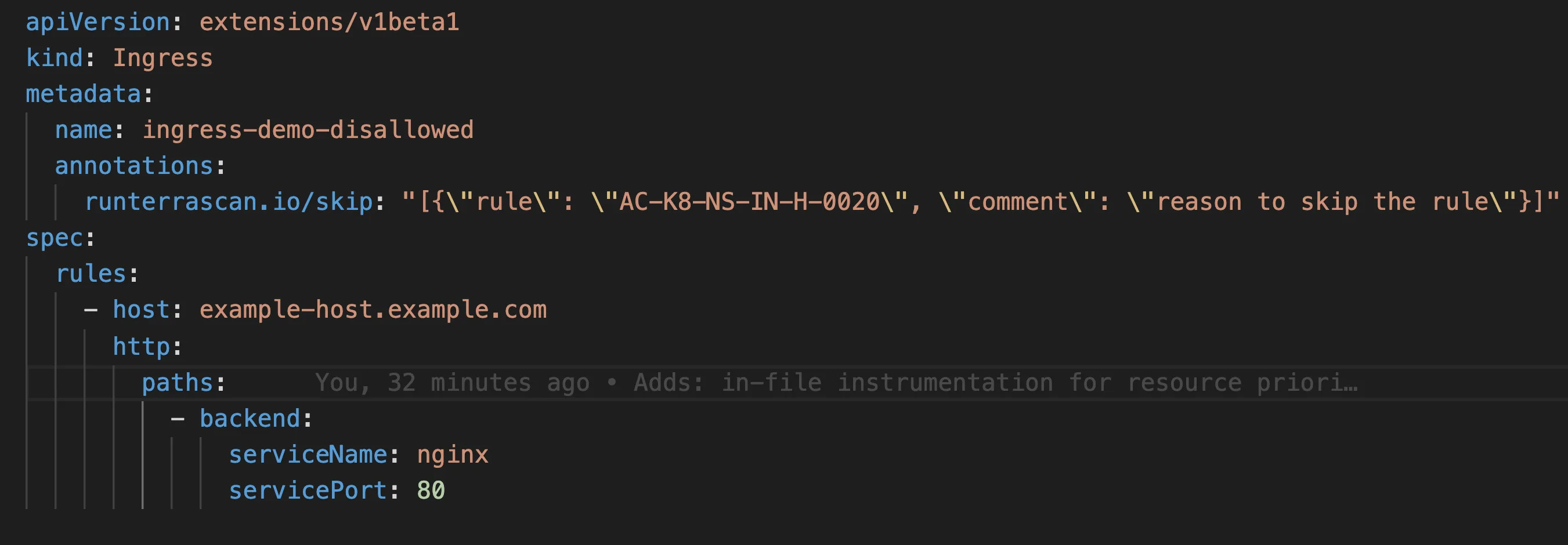
Kubernetes Admission Controller
Terrascan can deploy as a Kubernetes validating webhook. Every resource submitted to the API server gets checked against the policy set before admission.
Resources that fail checks are rejected with a clear error message.
Drift Detection
The scanner compares your IaC definitions against live cloud resources and flags differences. Useful for catching manual changes made outside of Terraform that cause configuration drift.
Skip Rules
You can suppress specific policies per resource using inline comments in your IaC files. Terrascan reads #ts:skip=RULE_ID annotations directly from the code.
Getting Started
brew install terrascan), Docker (docker run tenable/terrascan), or download the binary from GitHub releases. Available for Linux, macOS, and Windows.terrascan init to download the latest policy set. Policies are stored locally and can be updated independently.terrascan scan -t aws -i terraform -d ./infrastructure/ to scan Terraform files. Replace the type and directory flags for other IaC formats.-o sarif to generate SARIF files for GitHub Code Scanning integration.Configuration
Create a .terrascan.toml file to customize scan behavior:
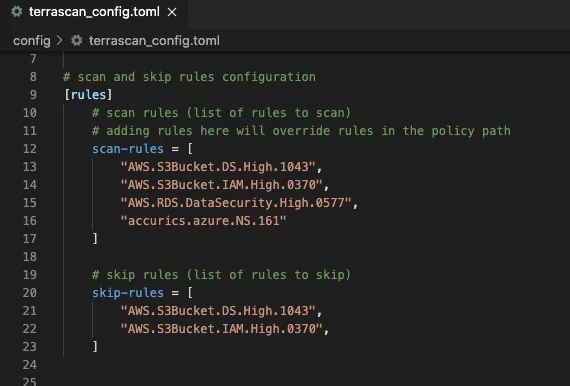
The config file supports skipping specific rules by ID, setting minimum severity thresholds, and configuring webhook notifications for scan results.
CI/CD Integration
Terrascan plugs into CI/CD pipelines through its Docker image or the official GitHub Action (tenable/terrascan-action). SARIF output feeds directly into GitHub Code Scanning alerts, putting IaC violations in the same Security tab as your other code analysis findings.
For GitLab CI, the Docker image runs in a pipeline stage and produces SAST-compatible reports. Jenkins and other CI tools work through the CLI binary or Docker container.
terrascan scan -o sarif > results.sarif to generate output compatible with GitHub Code Scanning. Upload the file with the github/codeql-action/upload-sarif action to see IaC violations in your repository’s Security tab.When to Consider Terrascan
Terrascan made sense for teams that wanted a free IaC scanner with broad compliance coverage and OPA/Rego extensibility.
The policy library covers most common misconfigurations without needing custom rule development.
Given the November 2025 archival, new adopters should evaluate actively maintained alternatives.
Checkov and KICS are both open-source and cover similar IaC formats. Trivy adds container and dependency scanning to its IaC capabilities.
Existing Terrascan users can continue running the last release.
There will be no patches for new vulnerabilities or support for newer versions of Terraform, Kubernetes, or cloud provider APIs.
For a broader view of IaC security strategy, see the cloud infrastructure security guide . Browse other IaC security tools to compare options.
Should I still use Terrascan in 2026?
No. Tenable archived the Terrascan repository on November 20, 2025. The last shipped release was March 2024 — nearly two years ago at the time of writing — and the GitHub repo is now read-only. New CVEs touching Terrascan’s parsers, new Terraform language features, and new compliance benchmarks won’t get backported.
The r/Terraform thread asking whether Terrascan was abandoned predates the official archive by more than a year, which gives a sense of how long the project drifted before maintainers made the deprecation explicit. If you’re picking a scanner for a 2026 pipeline, start somewhere actively maintained.
For migration: Checkov is the broadest like-for-like replacement, KICS is the closest match for teams that valued Terrascan’s OPA/Rego policy authoring, and Trivy is the right pick if you’d also like the same binary to scan containers, secrets, and SBOMs. The next section walks through each path.
Migrating from Terrascan
Three active scanners cover the ground Terrascan used to. The right choice depends on which Terrascan trait you valued most.
Checkov is the breadth pick. It scans Terraform, CloudFormation, Kubernetes, Helm, ARM, Dockerfile, and Serverless framework code with the largest built-in policy library in the open-source IaC space. Graph-based analysis catches multi-resource issues Terrascan’s single-file rules missed. Custom policies use Python or YAML — different DSL than Terrascan’s Rego, so existing custom rules need rewriting.
KICS (Checkmarx) is the closest spirit-of-Terrascan replacement. Both are policy-engine-driven, both lean on declarative query languages, and KICS has the largest collection of openly-published query libraries you can fork from. KICS uses Rego-style queries, so the mental model carries over even though the syntax isn’t 1:1.
Trivy (Aqua Security) is the consolidate-tools pick. One binary scans IaC (Terraform, CloudFormation, Helm, Dockerfile, Kubernetes, ARM, Ansible) plus container images, filesystems, and SBOMs. Custom checks use Rego, so the policy authoring style is closer to what Terrascan trained your team on. Trivy absorbed tfsec in 2023 and continues active development.
For any of these targets, the command surface is similar — point the scanner at a directory of IaC files and read the findings. The script glue around your CI pipeline is the part that changes most.
Terrascan history (Accurics, then Tenable)
Terrascan started life inside Accurics, a cloud security startup focused on IaC drift and misconfiguration. Tenable acquired Accurics in 2021 and folded the scanner into its broader cloud security portfolio while continuing to ship the open-source binary. Tenable also bundled Terrascan into Nessus Professional and Nessus Essentials so vulnerability assessment users got IaC scanning out of the box.
For about three years the open-source release cadence held up. The shift came in 2024: shipped releases slowed, then stopped after the March 2024 cut. By late 2025 Tenable formalized the situation by archiving the repository and pointing users toward its commercial Tenable Cloud Security product.
The codebase remains under Apache 2.0, so a community fork is technically possible. None has reached meaningful traction at the time of writing, and the install effort isn’t worth it when Checkov , KICS , and Trivy cover the same surface area with active engineering teams.