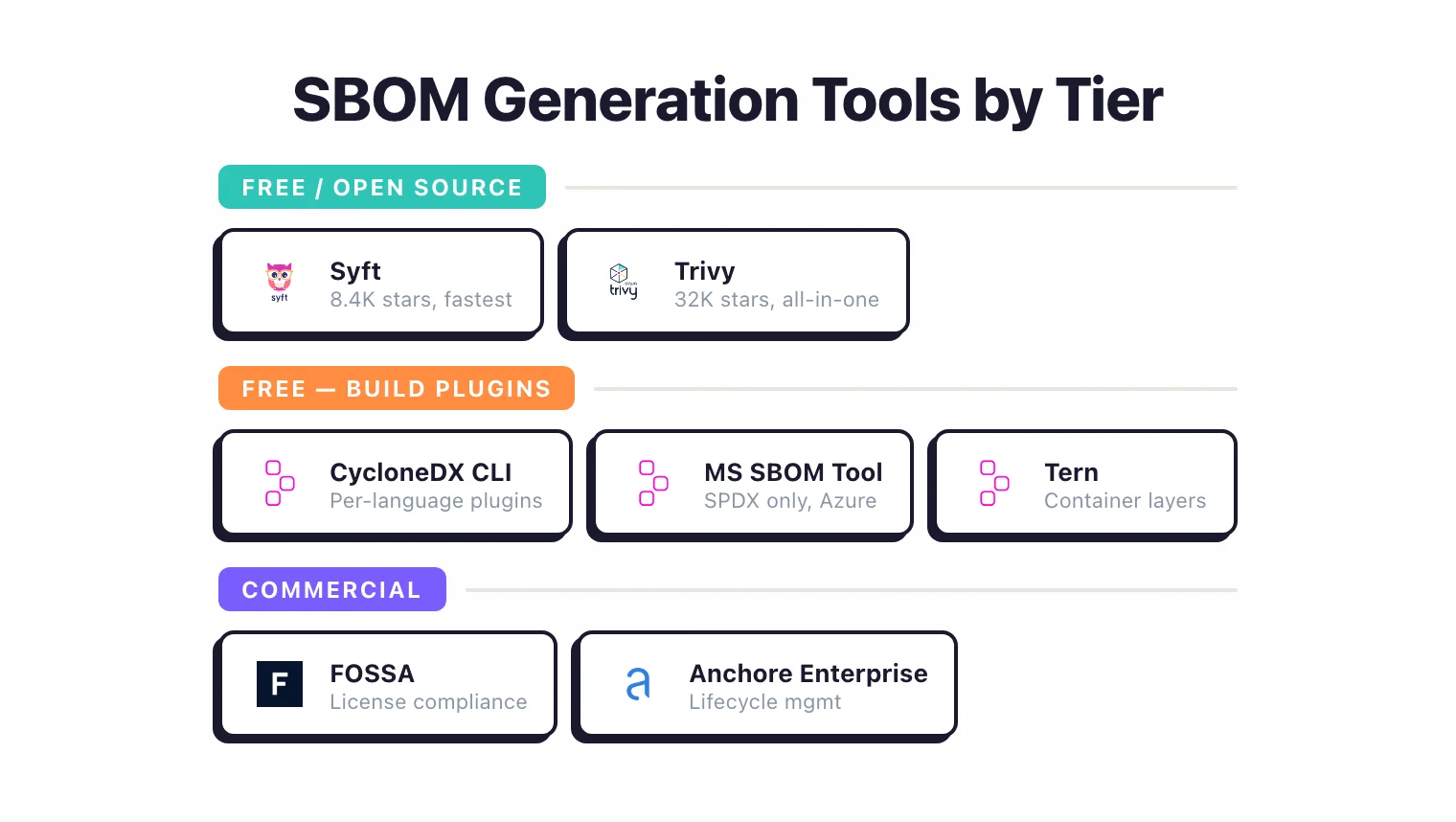
This SBOM tools comparison walks every major Software Bill of Materials generator and analyzer I use in 2026, from free CLI tools like Syft and Trivy to commercial platforms like FOSSA and Anchore Enterprise .
Each tool is compared on CycloneDX and SPDX output, ecosystem coverage across container images, filesystems, and build artifacts, and license detection — grounded in vendor docs, GitHub repos, and published case studies rather than marketing claims.
The timing matters.
US Executive Order 14028 is already enforced in federal procurement, the EU Cyber Resilience Act starts vulnerability reporting in September 2026 with full SBOM delivery by December 2027, and analysis tools like Grype , Dependency-Track , GUAC , and Bomber decide whether those SBOMs actually compress CVE response time from weeks to hours.
What is an SBOM?#
A Software Bill of Materials (SBOM) is a machine-readable inventory of every component in a piece of software — libraries, frameworks, direct and transitive dependencies, and the exact versions in use. The name is borrowed from manufacturing’s bill of materials, which lists every part that goes into a physical product.
The difference between a BOM and an SBOM is the domain. A BOM is the parts list for a physical good; an SBOM is the parts list for a compiled binary or container image. An SBOM includes package names, version numbers, supplier identifiers, component hashes, and dependency relationships, expressed in a structured format like CycloneDX or SPDX rather than free-form text.
SBOM tools are the scanners and platforms that generate, analyse, distribute, and monitor those inventories — the eleven options compared below split across generation (Syft, Trivy, build plugins), analysis (Grype, Dependency-Track, Bomber, GUAC), and lifecycle management (FOSSA, Anchore Enterprise).
Pick your next step
I want OSS-only SBOM tools
Free SCA and SBOM stack ranked: Syft, Trivy, Grype, Dependency-Track, OSV-Scanner. Zero-cost coverage for EO 14028 and the EU CRA.
→Compare Trivy vs Grype
Head-to-head benchmark of the two most popular free vulnerability scanners. Database depth, scan speed, SBOM input, and CI fit.
→Pick a specific tool
Browse 23 reviewed SCA tools across open-source and commercial tiers. Filter by license, ecosystem coverage, and pricing model.
→Why SBOM tools matter in 2026#
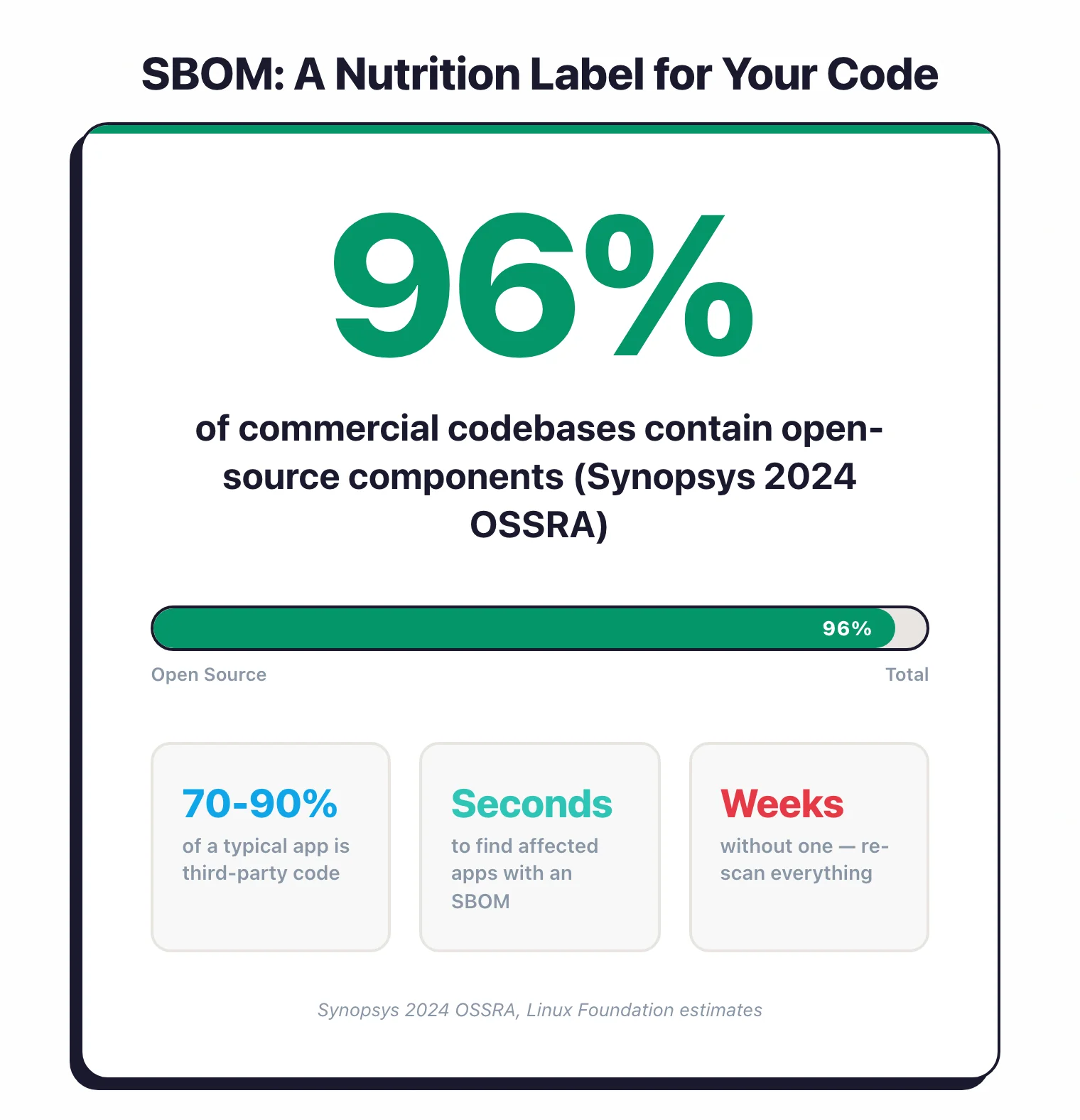
A Software Bill of Materials (SBOM) is a machine-readable inventory of every component in a piece of software: libraries, frameworks, dependencies, and their versions. Think of it as a nutrition label for code.
Without one, answering “are we affected by this new CVE?” requires re-scanning every application from scratch. With one, the answer takes seconds.
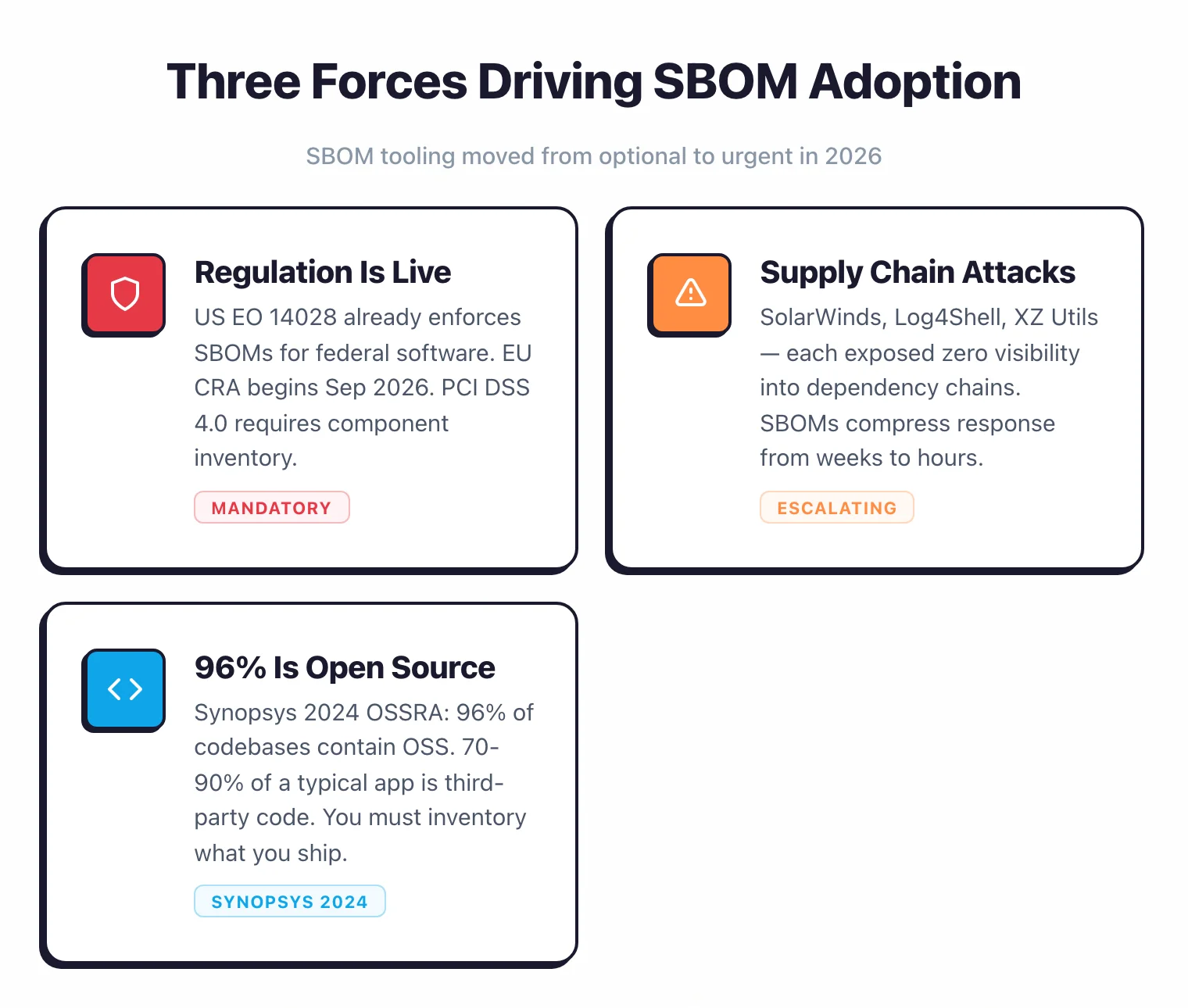
SBOM tooling has moved from optional to urgent. Three forces are driving the shift.
Regulation is no longer theoretical. US Executive Order 14028 already requires SBOMs for software sold to federal agencies.
The EU Cyber Resilience Act begins enforcing vulnerability reporting obligations in September 2026 and full SBOM requirements by December 2027. PCI DSS 4.0 requires a component inventory for cardholder-data environments.
Organizations that sell software into these markets need tooling in place now, not next year.
Key Insight
The compliance clock is running in 2026. EO 14028 already blocks non-SBOM vendors from federal contracts, the CRA starts enforcing vulnerability reporting in September, and PCI DSS 4.0 is already in the auditors' hands. You are either shipping SBOMs or you are losing deals.
Supply chain attacks keep escalating. SolarWinds, Log4Shell, the XZ Utils backdoor: each incident exposed how little visibility most organizations had into their dependency chains.

An SBOM does not prevent these attacks, but it compresses response time from weeks to hours. When the next critical CVE drops, the teams with SBOMs already know which applications are affected.
Software is mostly assembled, not written. The Black Duck 2026 OSSRA report found that 98% of commercial codebases contain open-source components, 87% have at least one known vulnerability, and the mean number of vulnerabilities per codebase has more than doubled year-over-year to 581.

The Linux Foundation estimates 70-90% of a typical application is third-party code. Securing the software you write is necessary.
Securing the software you ship, including everything you pulled from npm, PyPI, Maven Central, and Docker Hub, requires an inventory.
Pro tip: Start with Syft + Grype wired into CI/CD before you touch any commercial tool. The pair covers generation plus vulnerability scanning at zero cost and satisfies the core EO 14028 and CRA machine-readable inventory requirement in an afternoon.
For background on the concept itself, read the What is SBOM? explainer.
CycloneDX vs SPDX: choosing an SBOM format#
Two formats dominate the SBOM space. Both are accepted by US and EU regulators.
Both are machine-readable. The right choice depends on your primary use case.
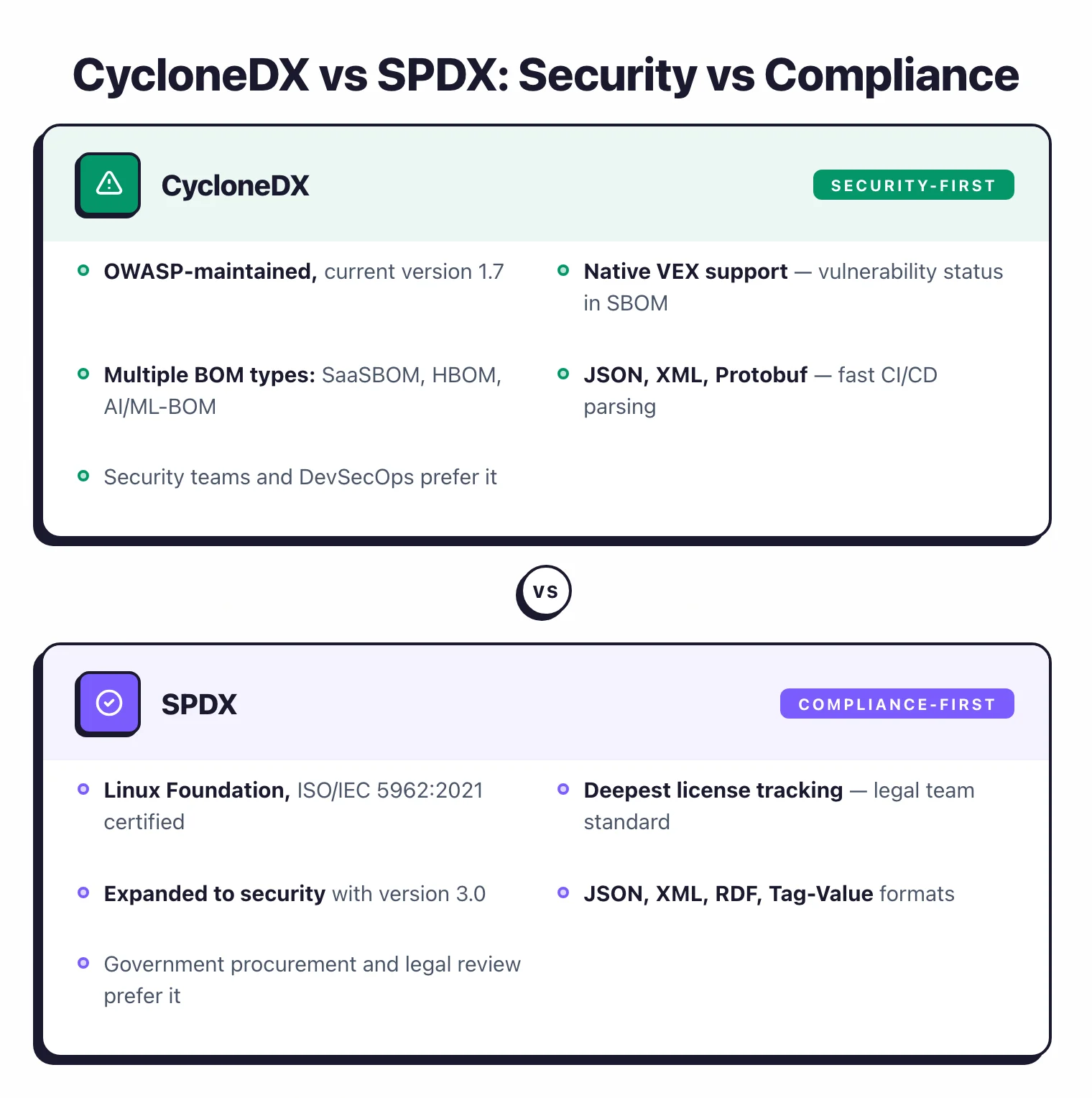
CycloneDX#
CycloneDX is an OWASP-maintained, ECMA-standardized SBOM format designed with security and vulnerability management as its primary focus. The current version is 1.7, released October 2025.
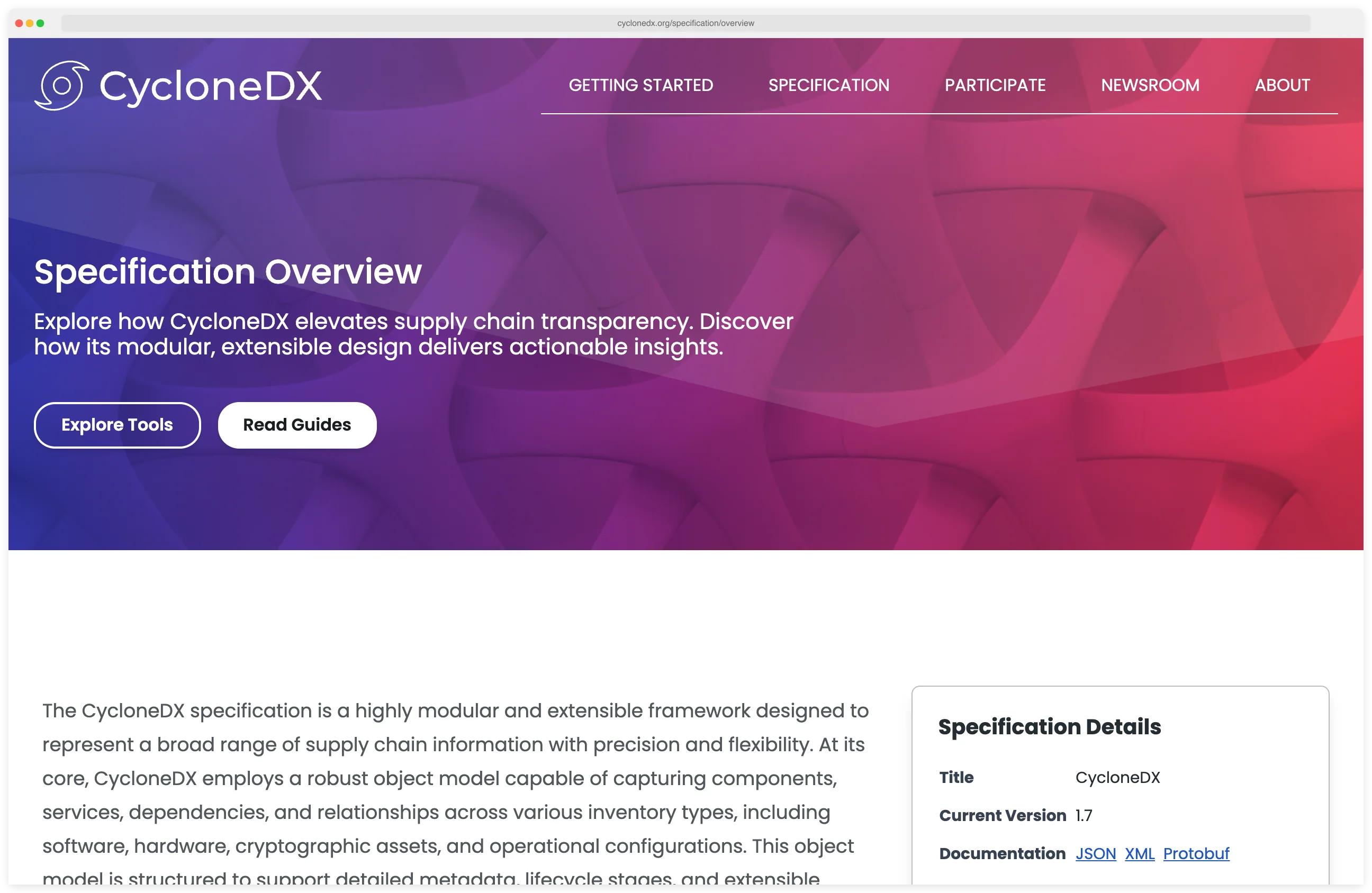
It supports multiple BOM types beyond software: SaaSBOM, HBOM (hardware), AI/ML-BOM, and CBOM (cryptographic).
Native VEX (Vulnerability Exploitability eXchange) support lets you communicate whether a vulnerability actually affects your product, directly inside the SBOM.
CycloneDX is available in JSON, XML, and Protocol Buffers. Its lightweight schema makes it the faster option to generate and parse in CI/CD pipelines. Most security teams prefer it.
SPDX#
SPDX (Software Package Data Exchange) is a Linux Foundation SBOM standard ratified as ISO/IEC 5962:2021, the first SBOM format to earn an international ISO standard.
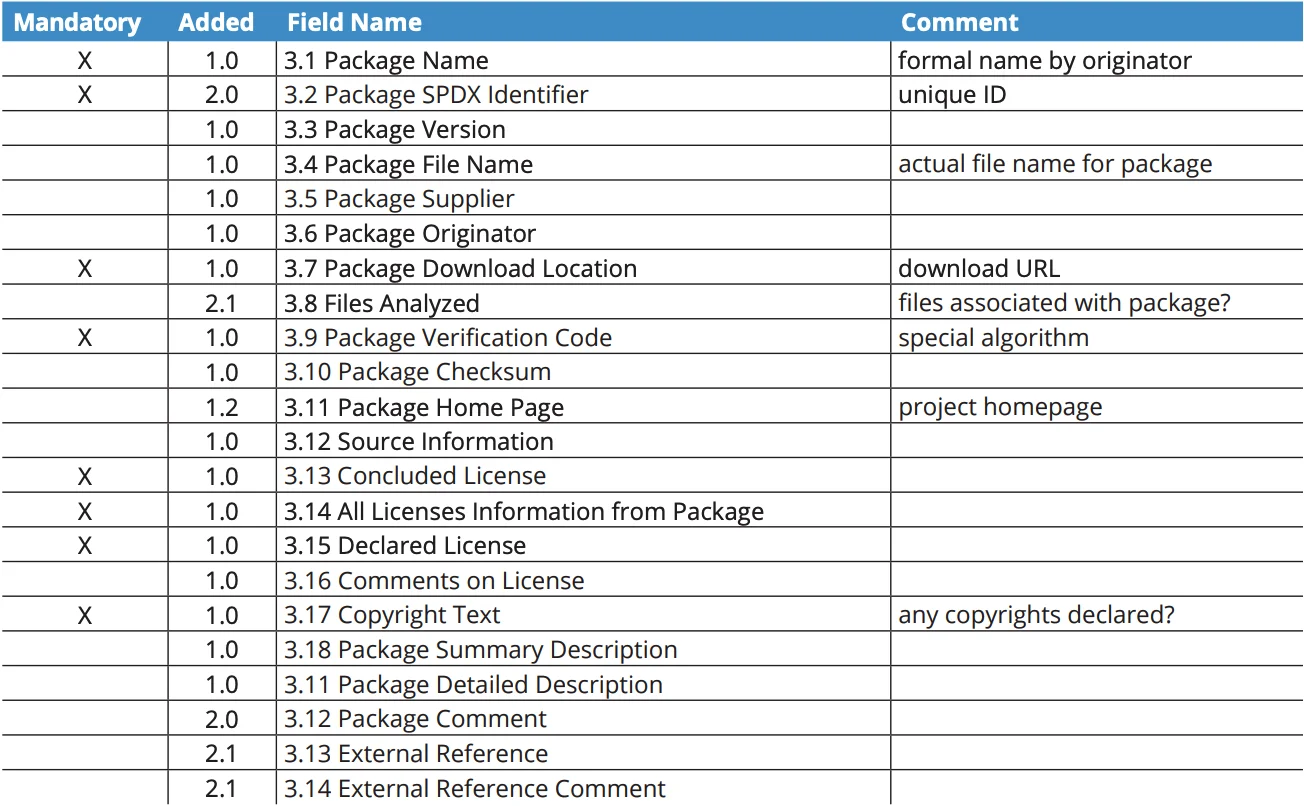
It originated in the licensing and compliance space and has since expanded to cover security use cases with version 3.0. SPDX serializes in JSON, XML, RDF, and Tag-Value formats.
SPDX has the deepest support for license compliance tracking. Legal teams, procurement departments, and government agencies that care primarily about open-source license obligations tend to prefer it.
Format comparison#
| Feature | CycloneDX | SPDX |
|---|---|---|
| Primary focus | Security and vulnerability management | License compliance (expanded to security) |
| VEX support | Native, first-class | Supported via external linking (SPDX 3.0) |
| Serialization | JSON, XML, Protocol Buffers | JSON, XML, RDF, Tag-Value |
| Governance | OWASP | Linux Foundation (ISO/IEC 5962:2021) |
| BOM types | SBOM, SaaSBOM, HBOM, AI/ML-BOM, CBOM | SBOM focused |
| Best for | Security teams, DevSecOps | Legal review, license compliance |
| Current version | 1.7 (October 2025) | 3.0 (January 2024) |
When to use which. If your primary driver is security and vulnerability management, start with CycloneDX.
If your primary driver is license compliance for legal review, start with SPDX.
Many organizations generate both – CycloneDX for their security team and SPDX for their legal team. Every tool in this comparison supports at least both formats.
Note: CycloneDX and SPDX are not interchangeable. When a regulator asks for one format specifically, regenerate from the source rather than converting an existing SBOM — native VEX entries and SPDX license expressions do not round-trip cleanly between the two schemas.
Key Insight
The format wars are over. Every serious SBOM tool emits both CycloneDX and SPDX now, so the real decision is which format matches your downstream consumer — security platforms expect CycloneDX, license reviewers and federal procurement expect SPDX, and you generate whichever one the next person in the pipeline is going to open.
What to look for in an SBOM tool#
Before picking a tool, it helps to know which dimensions actually differ across the 11 options below. Six criteria cover most real decisions.
1. Format support. Every serious tool now emits CycloneDX and SPDX. The differences are in completeness: some tools omit component hashes, dependency relationships, or VEX fields that regulators increasingly check.
2. Generation method. Build-plugin generators (CycloneDX Maven/Gradle/npm plugins) use the build system’s own dependency resolver, producing the most accurate SBOM. Binary scanners (Syft, Trivy, Anchore) read compiled artefacts and container layers — faster and broader, occasionally less precise.
3. Component detection depth. Coverage varies by ecosystem. Syft catalogs 30+ ecosystems; Microsoft SBOM Tool focuses on npm, NuGet, pip, Maven, Go; Tern maps each component back to the Dockerfile layer that installed it.
4. Lifecycle features. Generation is step one. Tools that also support VEX annotations, version-diff tracking, and continuous drift detection (Dependency-Track, Anchore Enterprise) cut post-deployment CVE triage time dramatically.
5. CI/CD integration. The practical question is how much glue code you write. Official GitHub Actions, GitLab CI templates, and Jenkins plugins beat hand-rolled shell wrappers — and they are what procurement auditors look for when they ask “is SBOM generation enforced in your pipeline?”
6. Regulatory fit. If you sell into federal procurement, FedRAMP or NIST 800-53 policy packs matter. If you sell into medical-device markets, FDA SBOM field requirements matter. Anchore Enterprise and FOSSA both ship pre-built compliance frameworks; open-source tools leave that to you.
SBOM generation tools#
Generation is the first step. These tools scan your source code, container images, and filesystems to produce an SBOM listing every component and its version.
Syft#
Syft is Anchore’s open-source SBOM generator and the most popular standalone tool in this category. With 8.4k GitHub stars and 219 contributors, it has become the default choice for teams that want fast, reliable SBOM output without a commercial license.
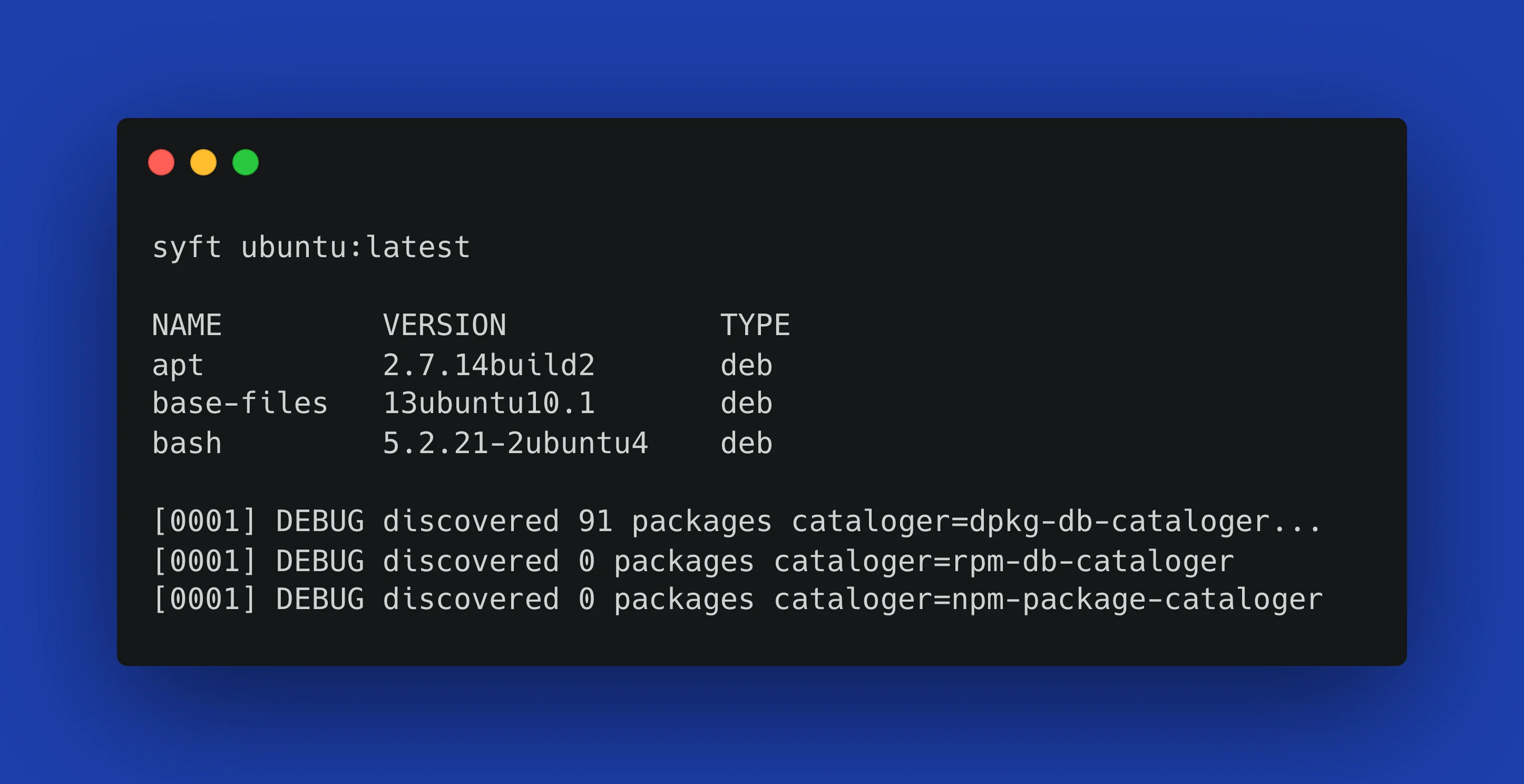
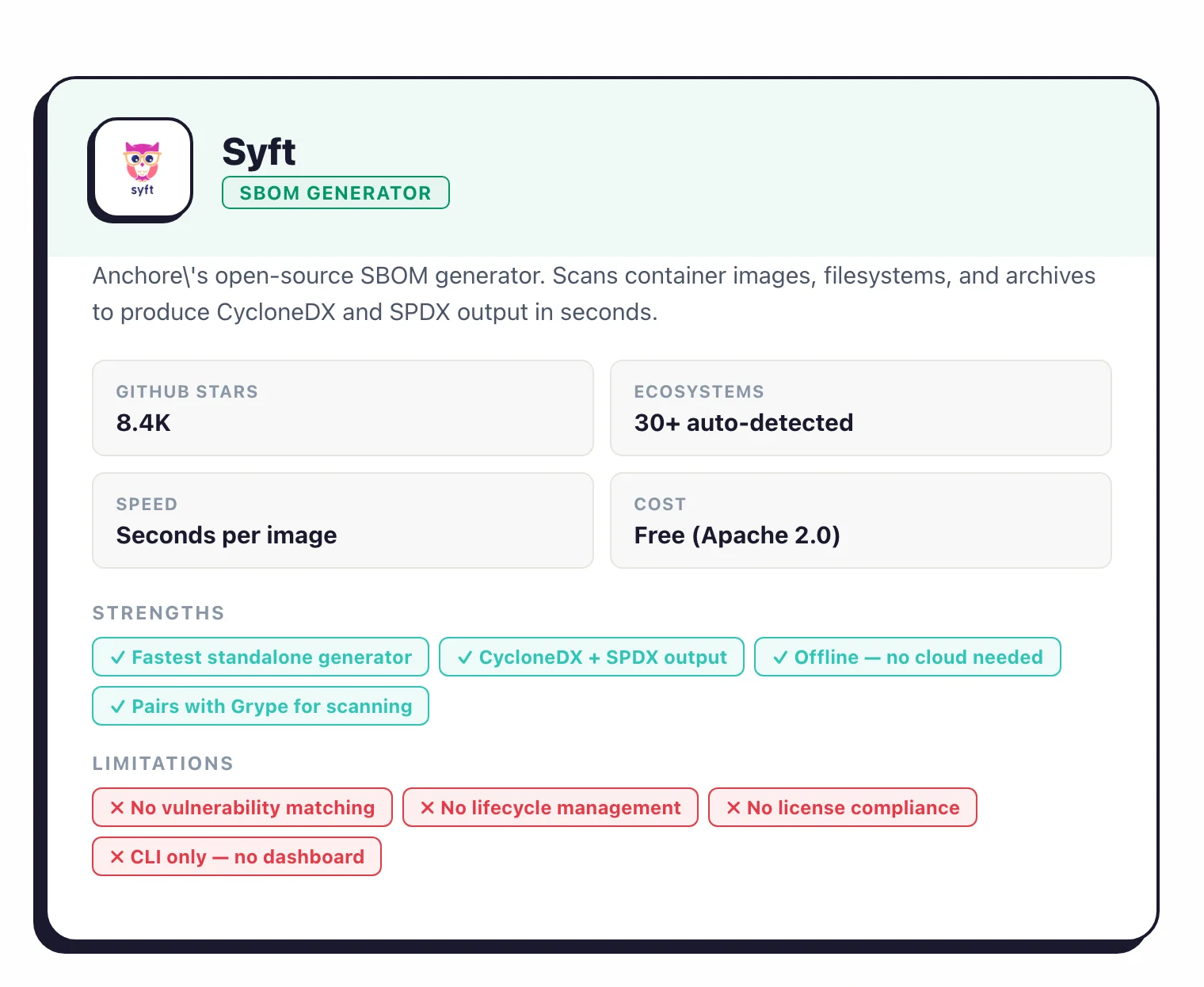
Syft scans container images (Docker, OCI, Singularity), filesystems, and archive files. It auto-detects dozens of package ecosystems (Alpine, Debian, RPM, npm, pip, Maven, Go modules, Cargo, Composer, NuGet, and more) without requiring configuration.
Output formats include CycloneDX, SPDX, and Syft’s own JSON format.
The tool runs entirely offline with no cloud dependencies. Point it at an image or directory, and you get a complete SBOM in seconds.
Pair it with Grype
for vulnerability scanning: Syft generates the inventory, Grype checks it against CVE databases. The official GitHub Action (anchore/sbom-action) makes CI/CD integration straightforward.
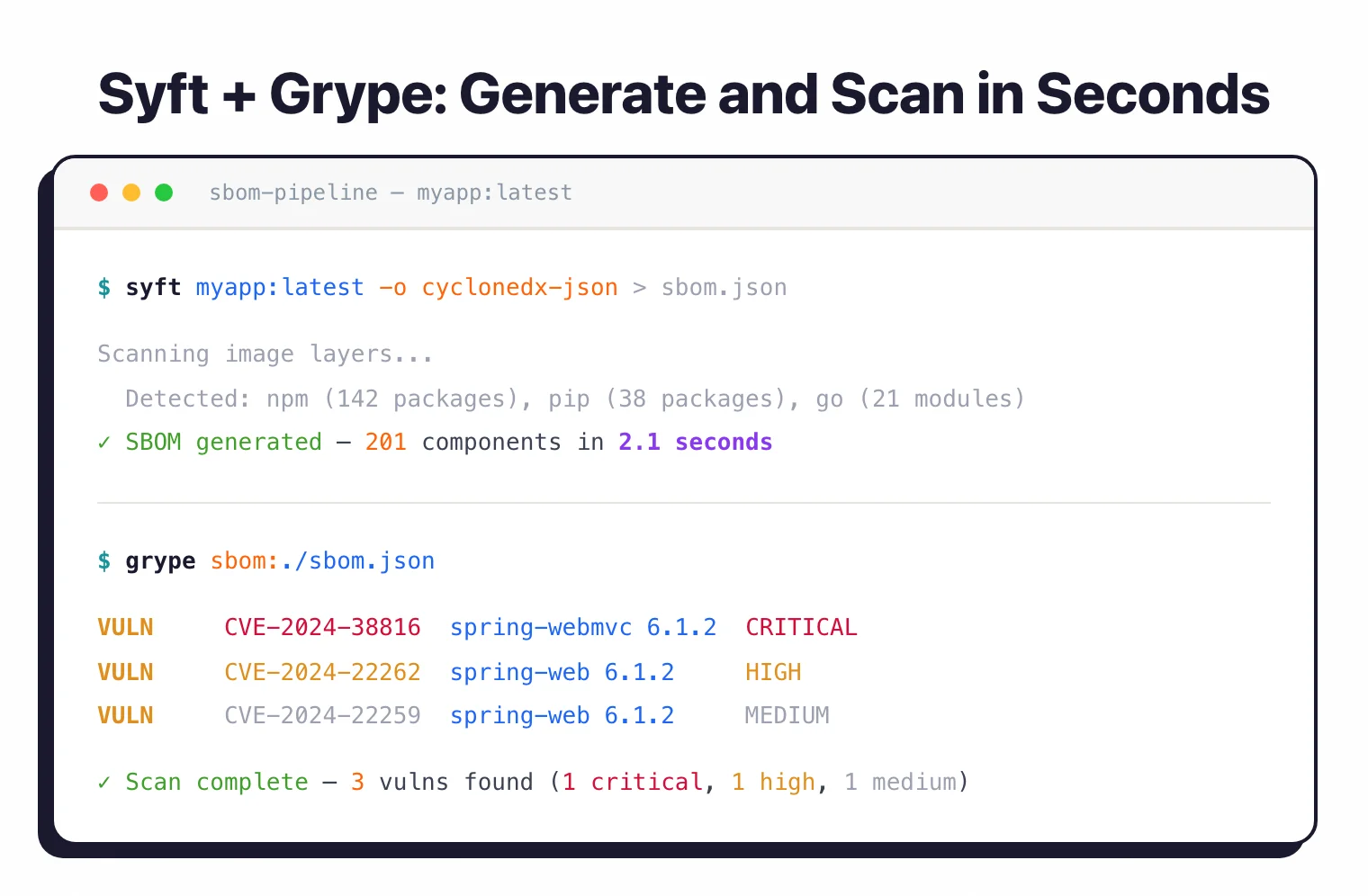
Pro tip: Drop the official anchore/sbom-action GitHub Action into your release workflow. It runs Syft against the built image, attaches the CycloneDX and SPDX SBOMs to the GitHub release, and requires zero custom shell — that is usually enough to check the "SBOM delivered to customer" box in a procurement review.
Best for: Teams that need a dedicated, fast SBOM generator without the overhead of a full SCA platform.
Trivy#
Trivy is Aqua Security’s all-in-one scanner with 32.2k GitHub stars. While it is primarily known for vulnerability and IaC scanning, Trivy also generates SBOMs in CycloneDX and SPDX formats directly from container images and filesystems.
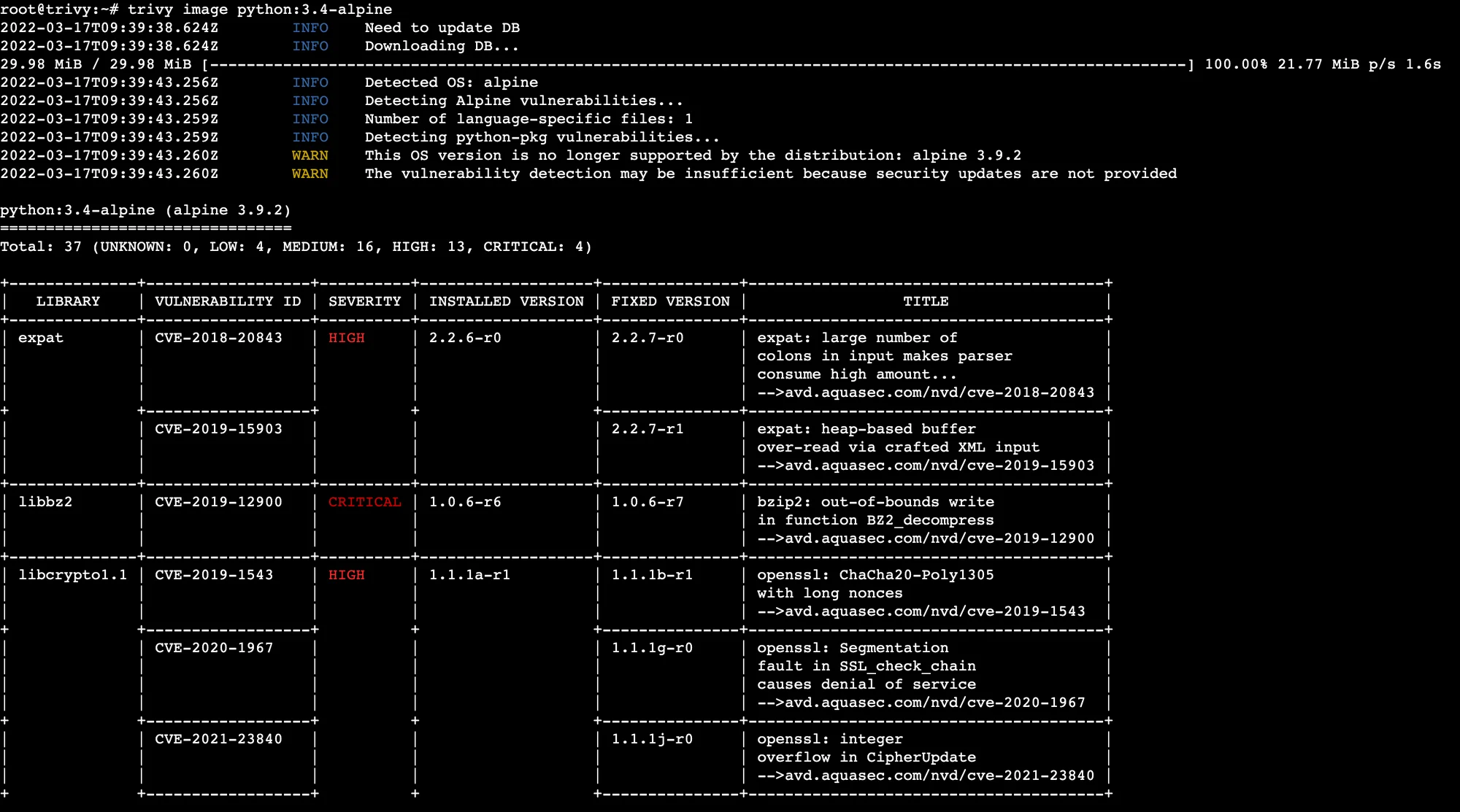
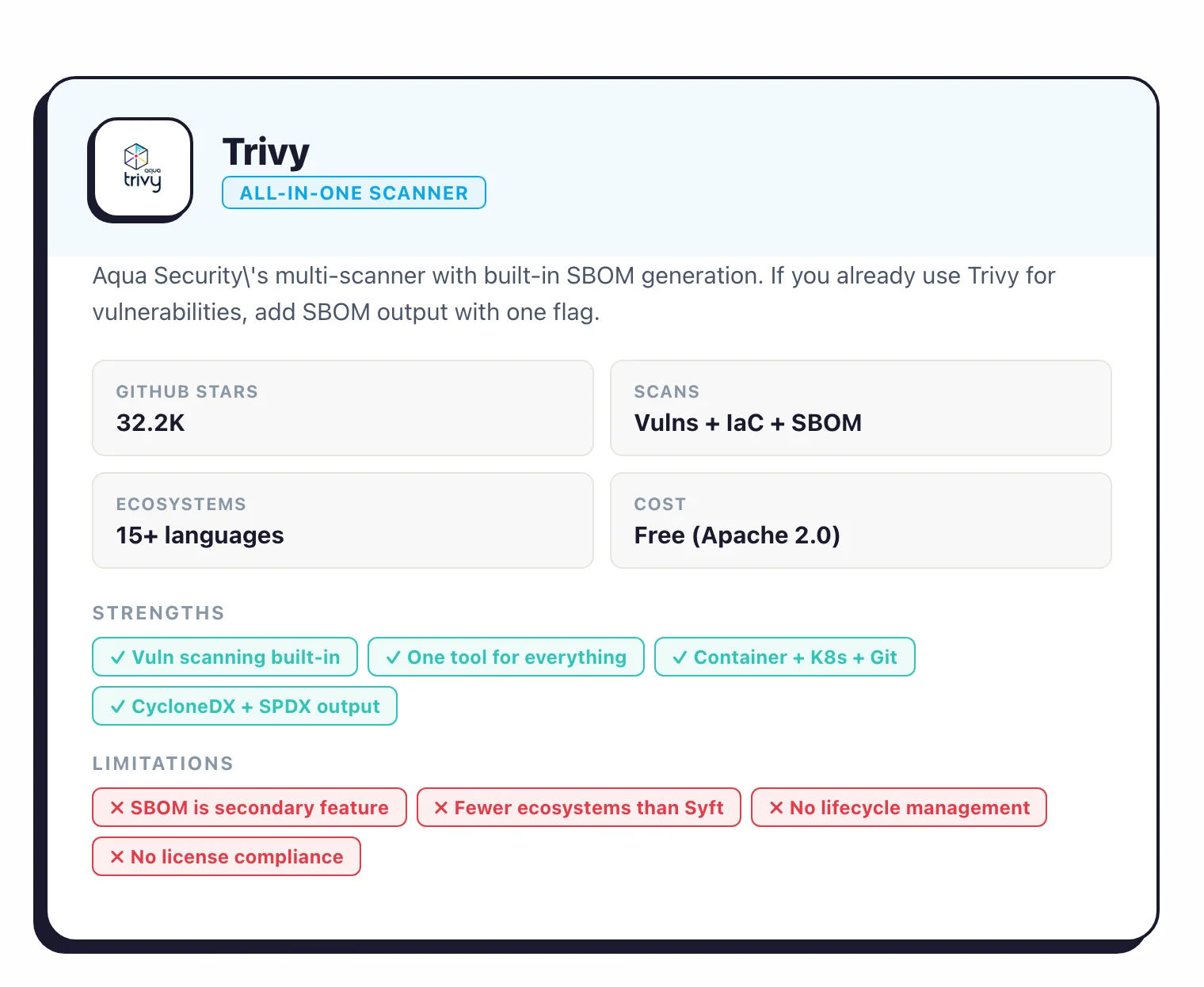
The advantage of Trivy is consolidation. If your team already uses it for vulnerability scanning, adding SBOM generation requires zero additional tooling: just change the output format flag.
Trivy covers the same language ecosystems as Syft (Go, Java, Node.js, Python, Ruby, Rust, PHP, .NET, and more) and scans container images, git repos, and Kubernetes clusters.
# Generate CycloneDX SBOM with Trivy
trivy image --format cyclonedx myapp:latest > sbom.json
# Generate SPDX SBOM
trivy image --format spdx-json myapp:latest > sbom.spdx.json
Note: Syft and Trivy disagree on the same image more often than you would expect — sometimes by 30-40% of components. Neither output is "wrong"; they interpret package metadata differently. When an auditor asks which SBOM is correct, the answer is "the one the build system produced", which is usually a CycloneDX build plugin, not a scanner.
Best for: Teams already using Trivy for vulnerability or IaC scanning who want SBOM generation without adding another tool.
CycloneDX CLI and build plugins#
The CycloneDX project maintains language-specific build plugins for Maven, Gradle, npm, pip, Go, Rust, .NET, and others. These plugins hook directly into your build system and produce CycloneDX SBOMs from the resolved dependency tree.
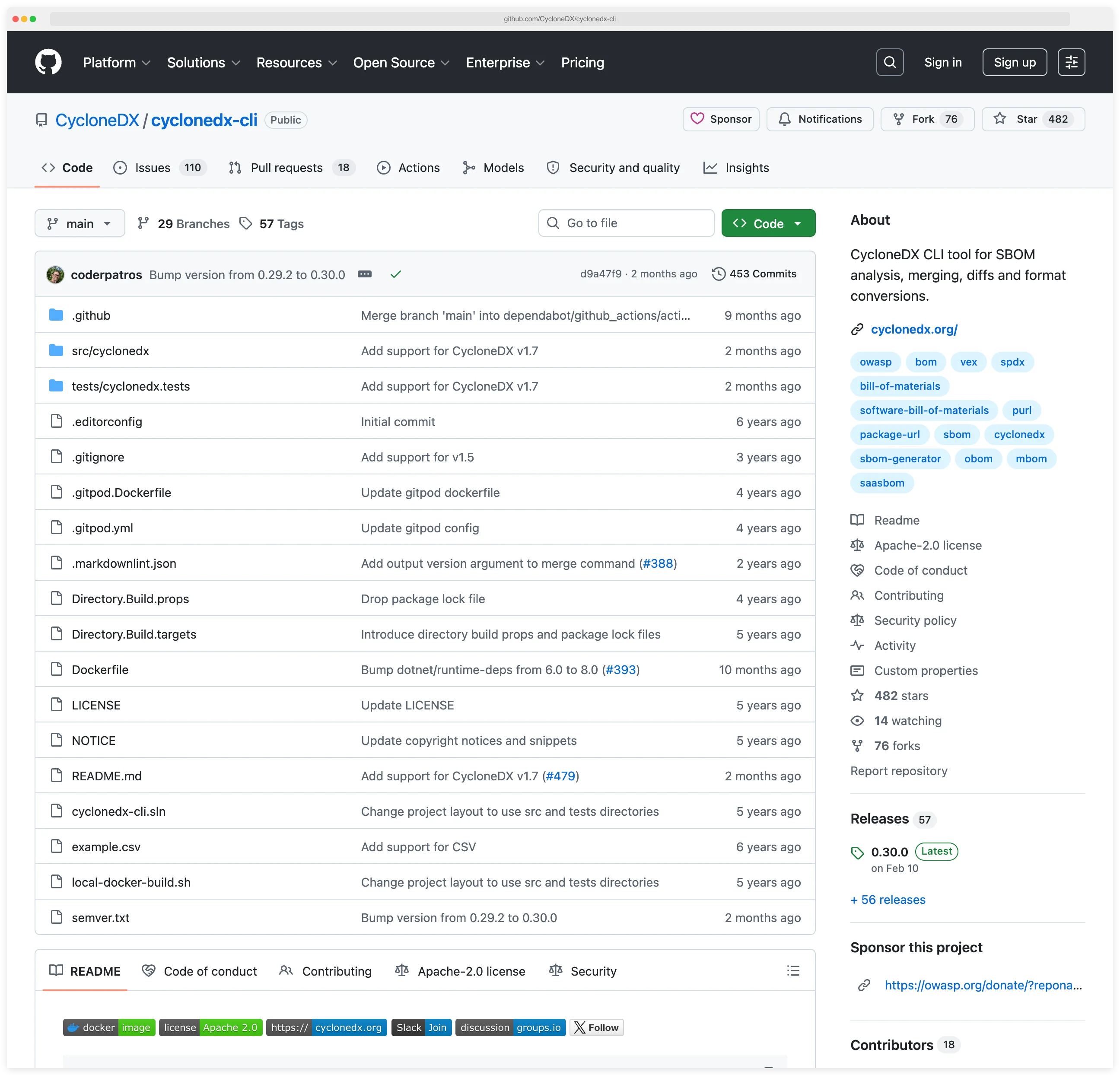
The CycloneDX CLI tool handles format conversion, validation, and merging of SBOMs from different sources. If you need to combine SBOMs from a Java backend and a Node.js frontend into a single inventory, the CLI handles that.
The build plugin approach produces the most accurate SBOMs for source-level analysis because it uses the same dependency resolution your build system uses. The tradeoff is that you need a plugin per language ecosystem, rather than a single binary.
Best for: Teams that want the highest accuracy SBOM from their build system, or need to combine SBOMs from multi-language projects.
FOSSA#
FOSSA is a commercial SCA platform where license compliance is the primary differentiator. It generates SBOMs in CycloneDX and SPDX formats across 17+ languages and 20+ build systems.
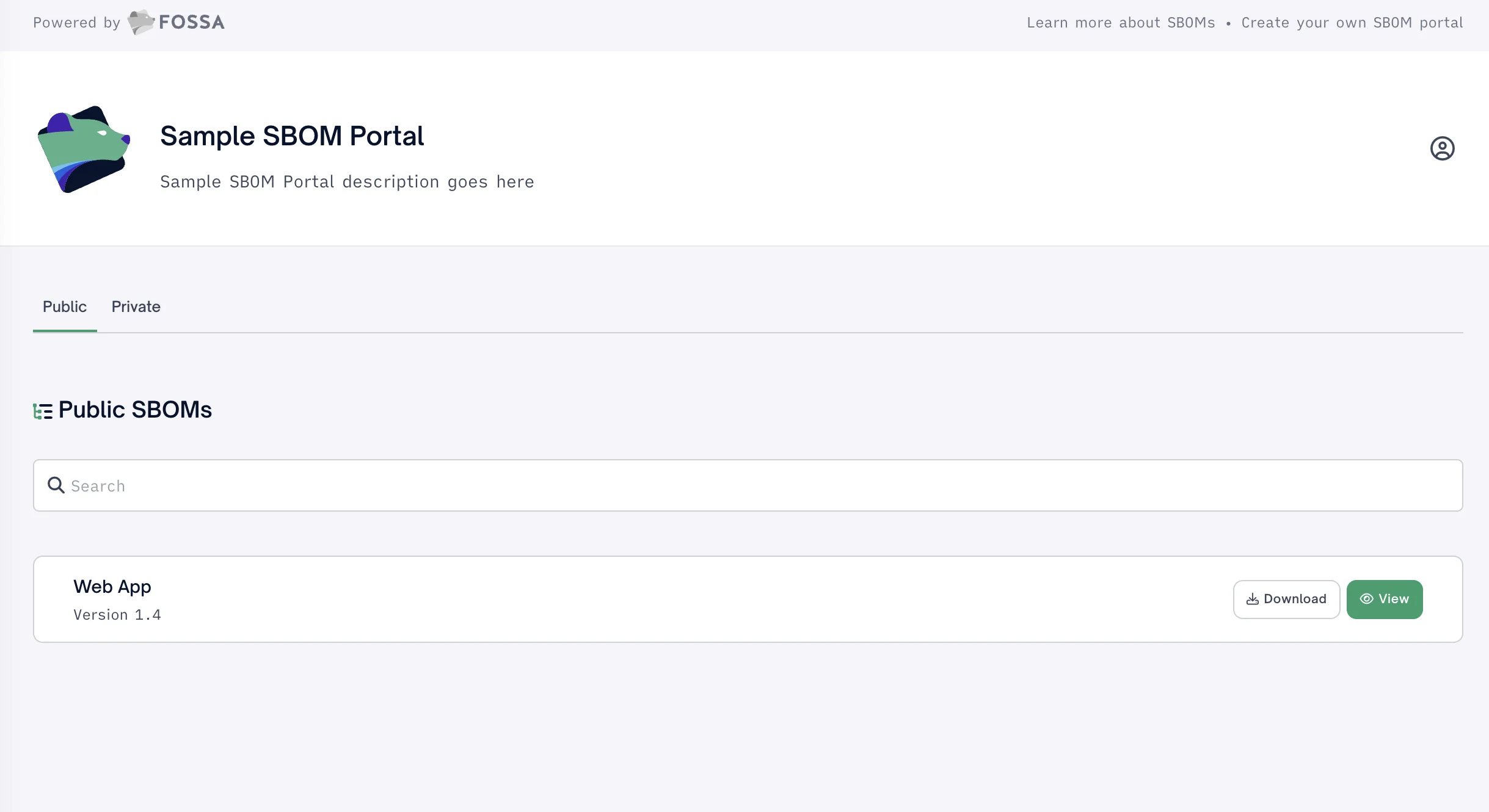
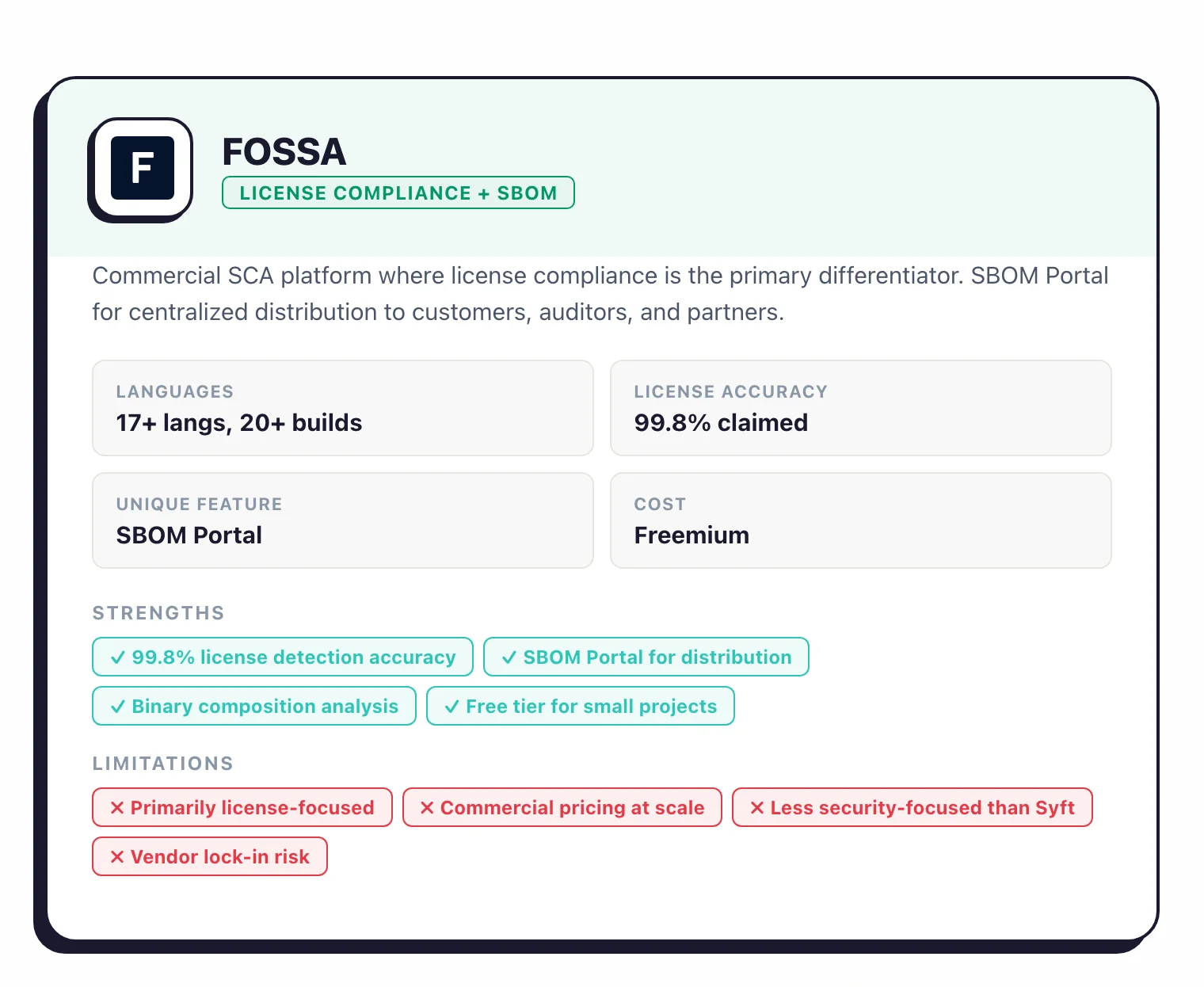
Where FOSSA goes beyond pure generation is its SBOM Portal, a centralized distribution point where you share SBOMs with customers, auditors, and partners using access tokens. It also imports third-party SBOMs for tracking.
FOSSA’s license detection engine claims 99.8% accuracy, which matters when your legal team needs to verify open-source obligations alongside the security inventory.
FOSSA supports binary composition analysis for scanning compiled artifacts (JARs, DLLs) when source code is not available. A free tier covers basic scanning for smaller projects.
Best for: Organizations that need license compliance tracking alongside SBOM generation, or need a centralized SBOM distribution portal.
Anchore Enterprise#
Anchore Enterprise extends the open-source Syft and Grype tools into a platform with centralized SBOM management, continuous monitoring, and compliance automation.
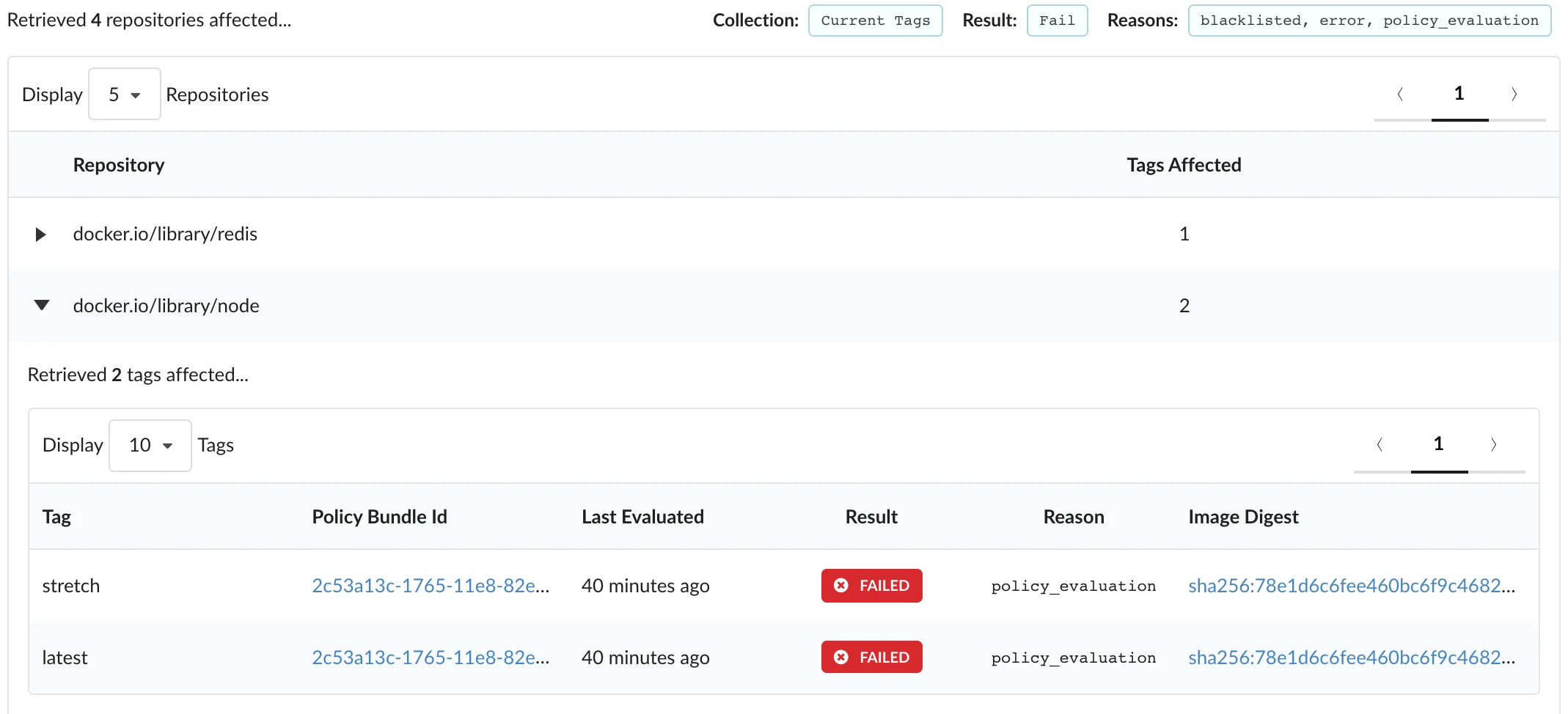
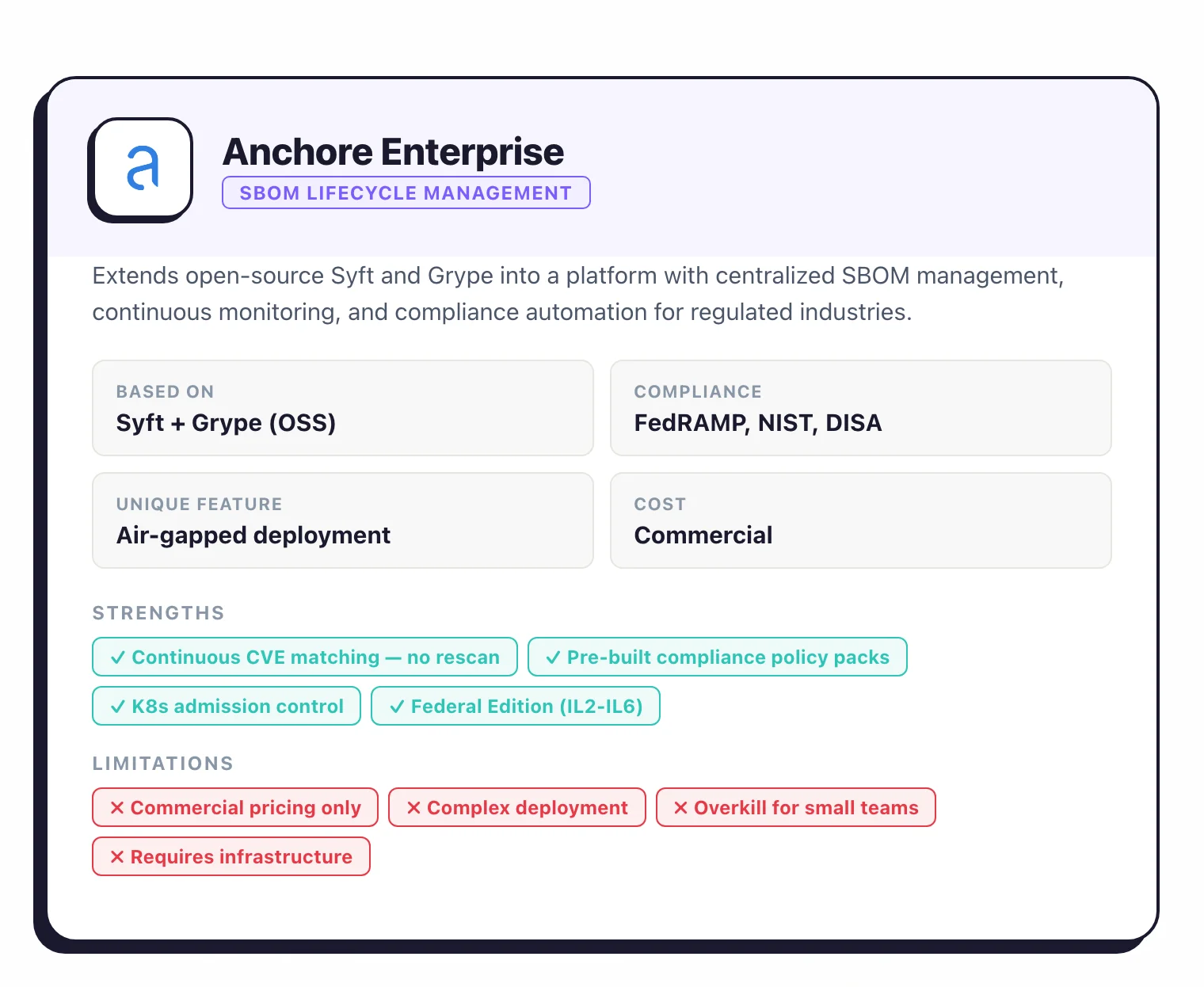
The key differentiator is lifecycle management. Anchore Enterprise stores every SBOM generated from your pipeline and continuously matches them against updated vulnerability feeds.
When a new CVE is published, it identifies affected images instantly without requiring a rescan. Pre-built compliance policy packs automate checks for FedRAMP, NIST 800-53, and DISA standards.
The platform includes policy-based admission control for Kubernetes, secret and malware detection in container image layers, and a Federal Edition that supports air-gapped deployment from IL2 through IL6 classified environments.
Best for: Government agencies, defense contractors, and regulated enterprises that need SBOM lifecycle management with compliance automation.
Microsoft SBOM Tool#
Microsoft’s open-source SBOM Tool generates SPDX SBOMs and is used internally across Microsoft’s products. It scans project directories and produces SPDX 2.2 output with component hashes for integrity verification.
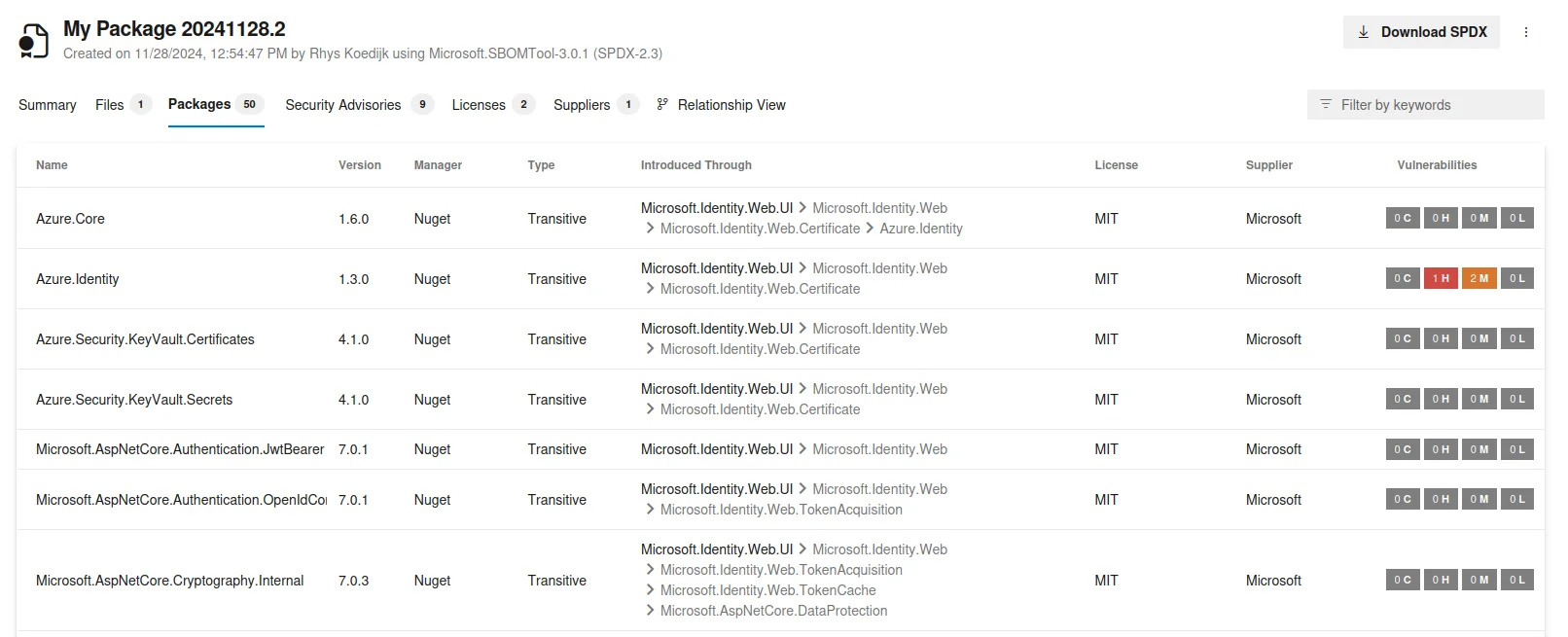
The tool integrates with Azure DevOps pipelines and supports common package ecosystems (npm, NuGet, pip, Maven, Go). It is more narrowly focused than Syft (SPDX output only, no CycloneDX), but it is a solid choice for organizations already invested in the Microsoft ecosystem.
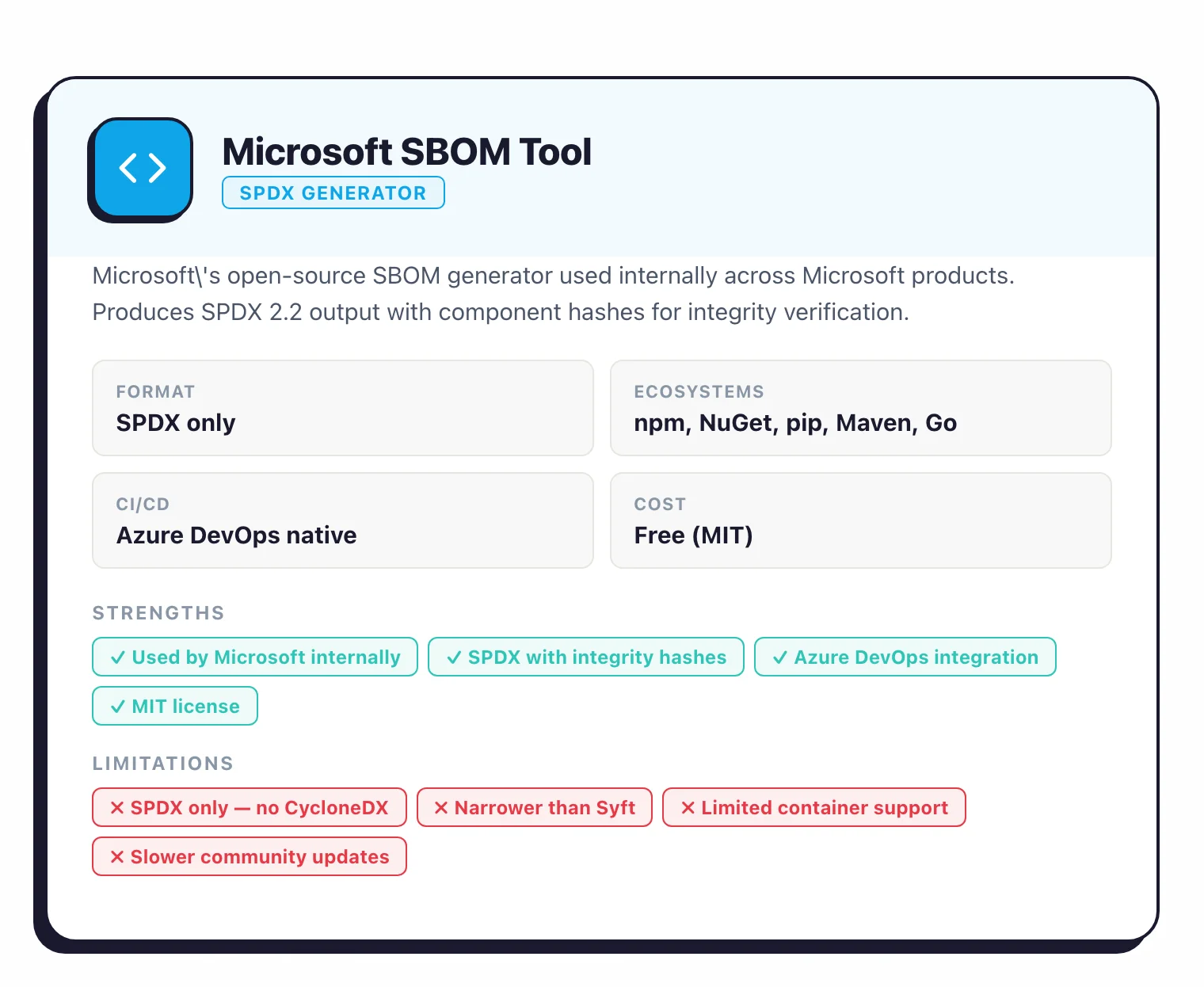
Best for: Teams on Azure DevOps that need SPDX-formatted SBOMs.
Tern#
Tern is a Linux Foundation project focused specifically on container image analysis. It inspects Dockerfile instructions and image layers to identify packages, mapping each component back to the specific layer that installed it.
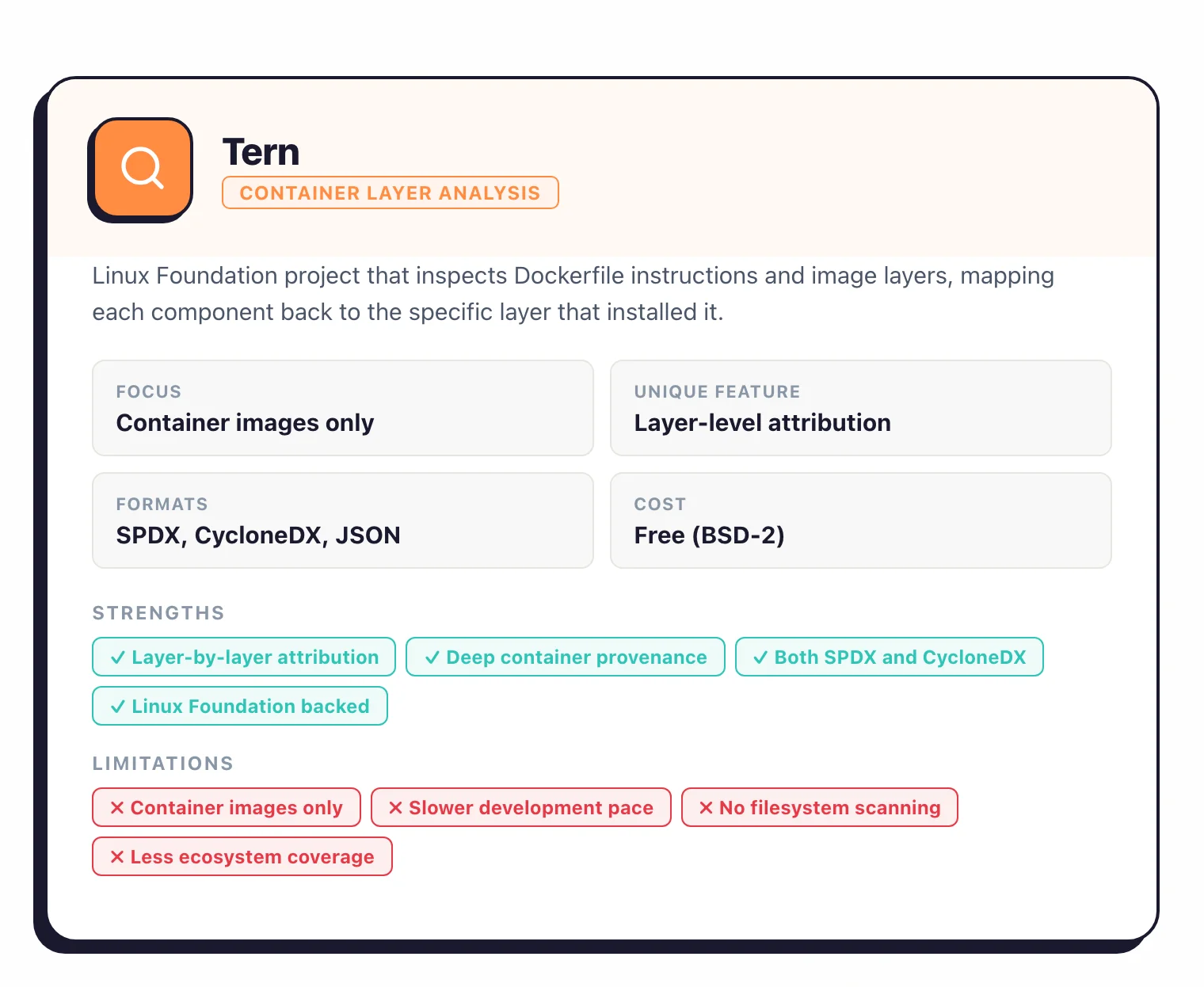
Tern outputs in SPDX, CycloneDX, and its own JSON format. Its layer-level attribution is useful for understanding which base image or build step introduced a particular dependency.
Development has slowed compared to Syft and Trivy, but it remains a viable option for teams that want deep container provenance.
Best for: Teams that need layer-by-layer attribution of components in container images.
For deeper single-tool analysis, the per-tool reviews (linked above) cover pricing, changelog, and known limitations. For head-to-head comparisons, Trivy vs Grype and OSV-Scanner vs Grype benchmark the fastest free stacks against each other. If you are choosing between Anchore and Syft, the Syft page covers the Anchore-Engine lineage and current Syft + Grype workflow.
SBOM analysis and lifecycle management#
Generating an SBOM is step one. The next step is using that inventory to find vulnerabilities, track risk over time, and respond when new CVEs drop.
Dependency-Track#
OWASP Dependency-Track is an open-source platform for continuous SBOM monitoring. Upload CycloneDX or SPDX SBOMs from any generation tool, and Dependency-Track correlates every component against NVD, GitHub Security Advisories, Sonatype OSS Index, and OSV.
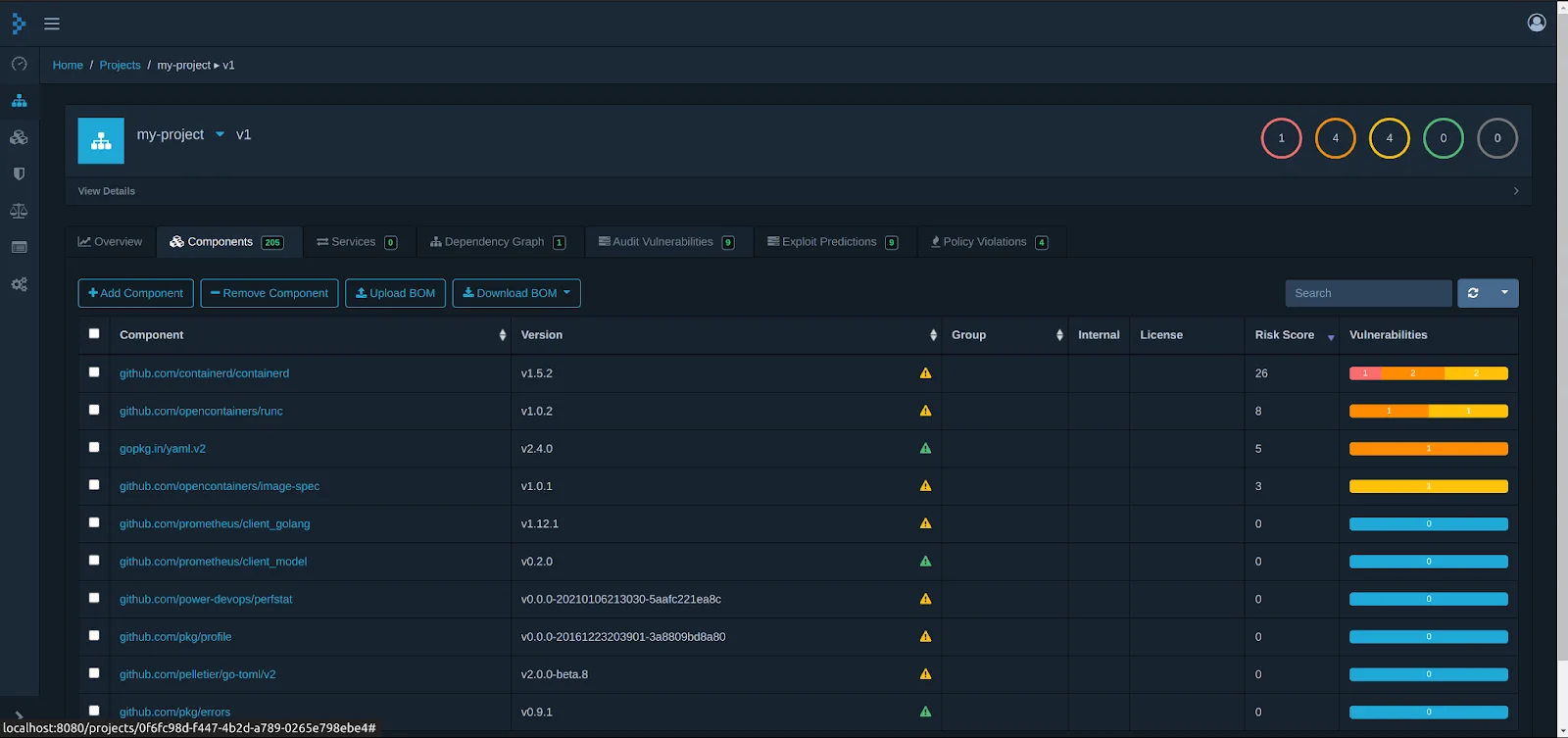
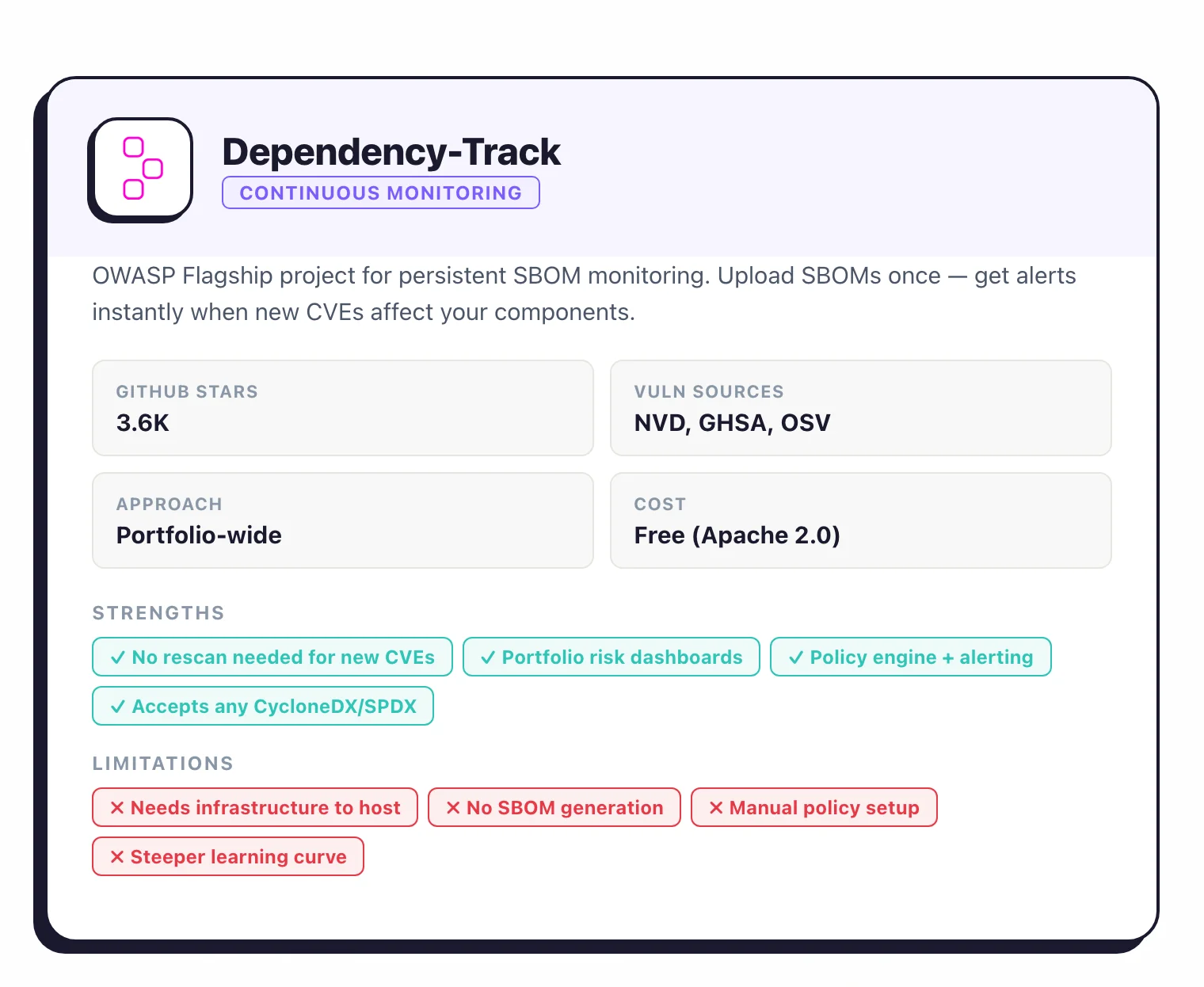
Unlike build-time scanners, Dependency-Track maintains a persistent inventory. When a new CVE is published, it immediately identifies every project that contains the affected component, without requiring a rescan.
The platform tracks risk trends across your entire application portfolio with dashboards, policy engine, and alerting.
Deploy it with Docker Compose and feed it SBOMs from Syft or Trivy in your CI pipeline. It is an OWASP Flagship Project with 3.6k GitHub stars.
Pro tip: Deploy Dependency-Track from the official Docker Compose file and have your CI pipeline POST SBOMs to the /api/v1/bom endpoint on every merge. New CVEs then trigger alerts against every deployed application you have ever shipped, without re-running any scan.
Best for: Organizations managing multiple applications that need continuous, portfolio-wide vulnerability monitoring from SBOMs.
Grype#
Grype is Anchore’s open-source vulnerability scanner that accepts SBOMs as input. It matches components against NVD, GitHub Security Advisories, and distribution-specific feeds, then ranks findings using a composite risk score that combines CVSS severity, EPSS exploit probability, and KEV catalog status.
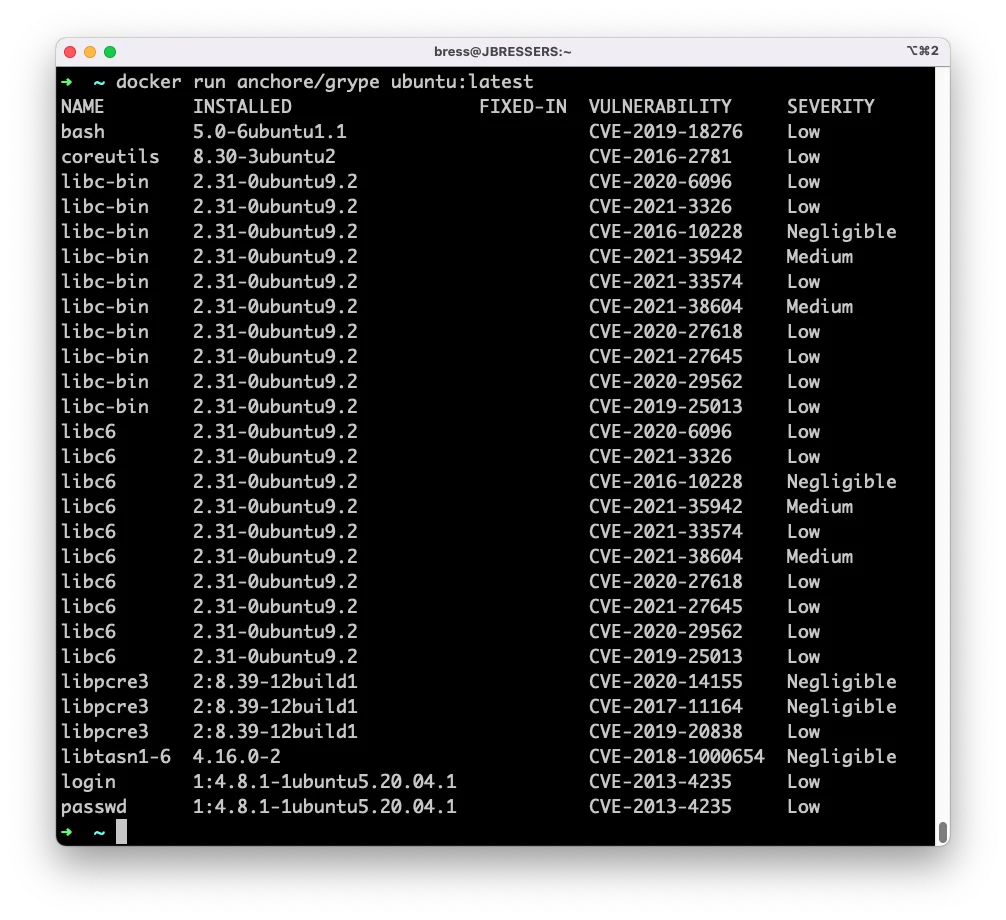
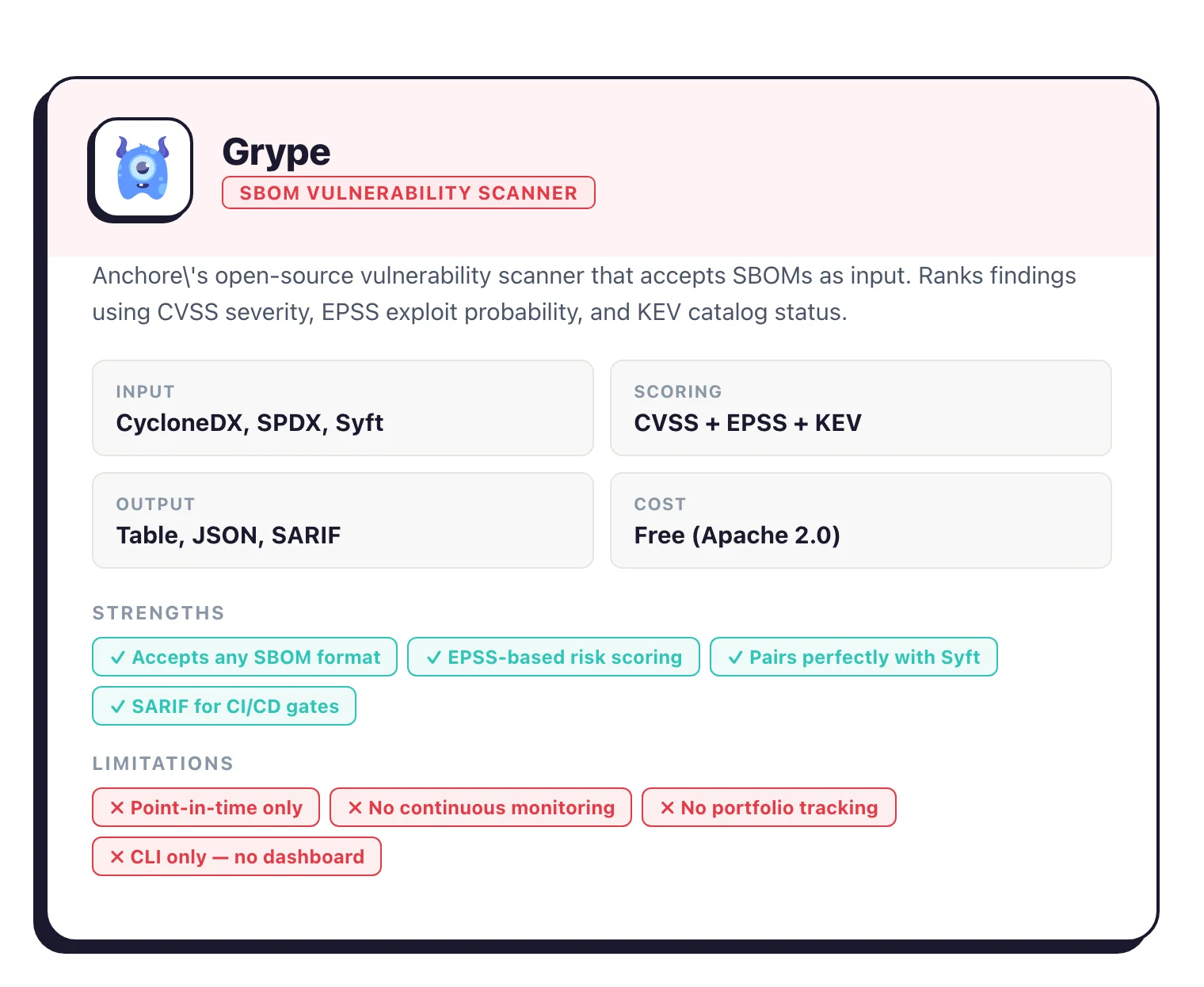
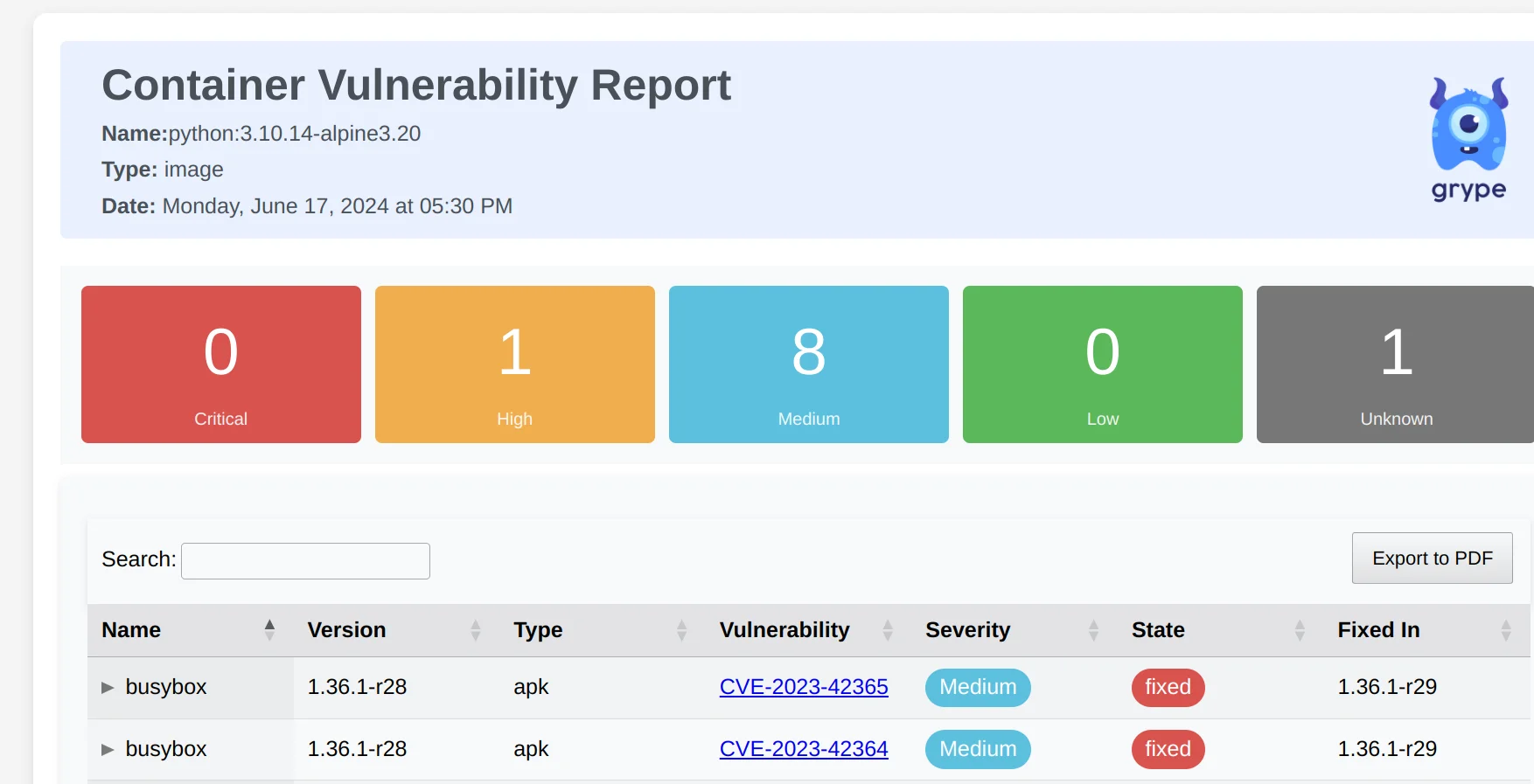
The Syft-plus-Grype workflow is a common pattern: generate an SBOM once with Syft, then rescan it with Grype whenever vulnerability databases update. No need to re-analyze the original image.
Grype outputs table, JSON, SARIF, and CycloneDX formats for CI/CD integration.
# Scan an SBOM file with Grype
grype sbom:./sbom.json
# Pipe Syft output directly to Grype
syft alpine:latest -o cyclonedx-json | grype
Best for: Teams that want fast, SBOM-based vulnerability scanning in CI/CD without infrastructure or licensing costs.
GUAC#
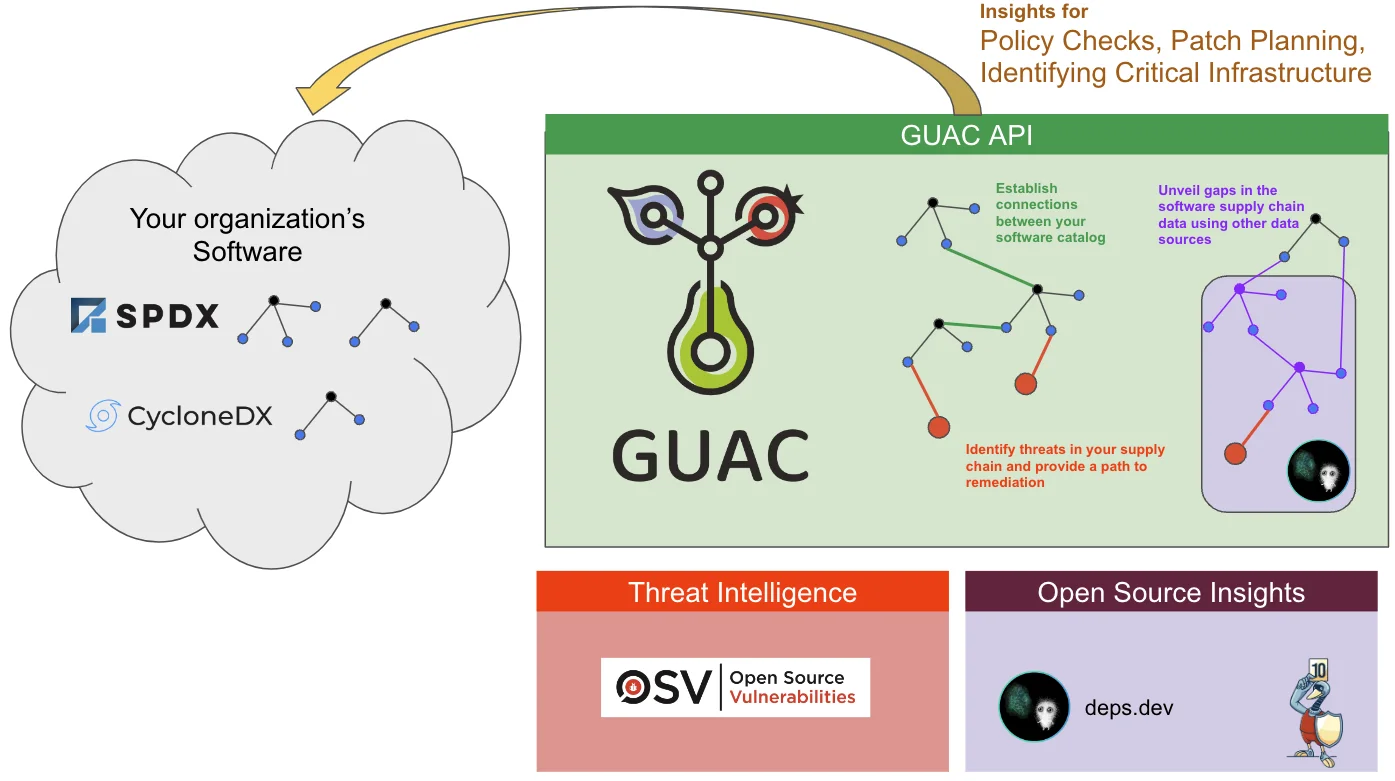
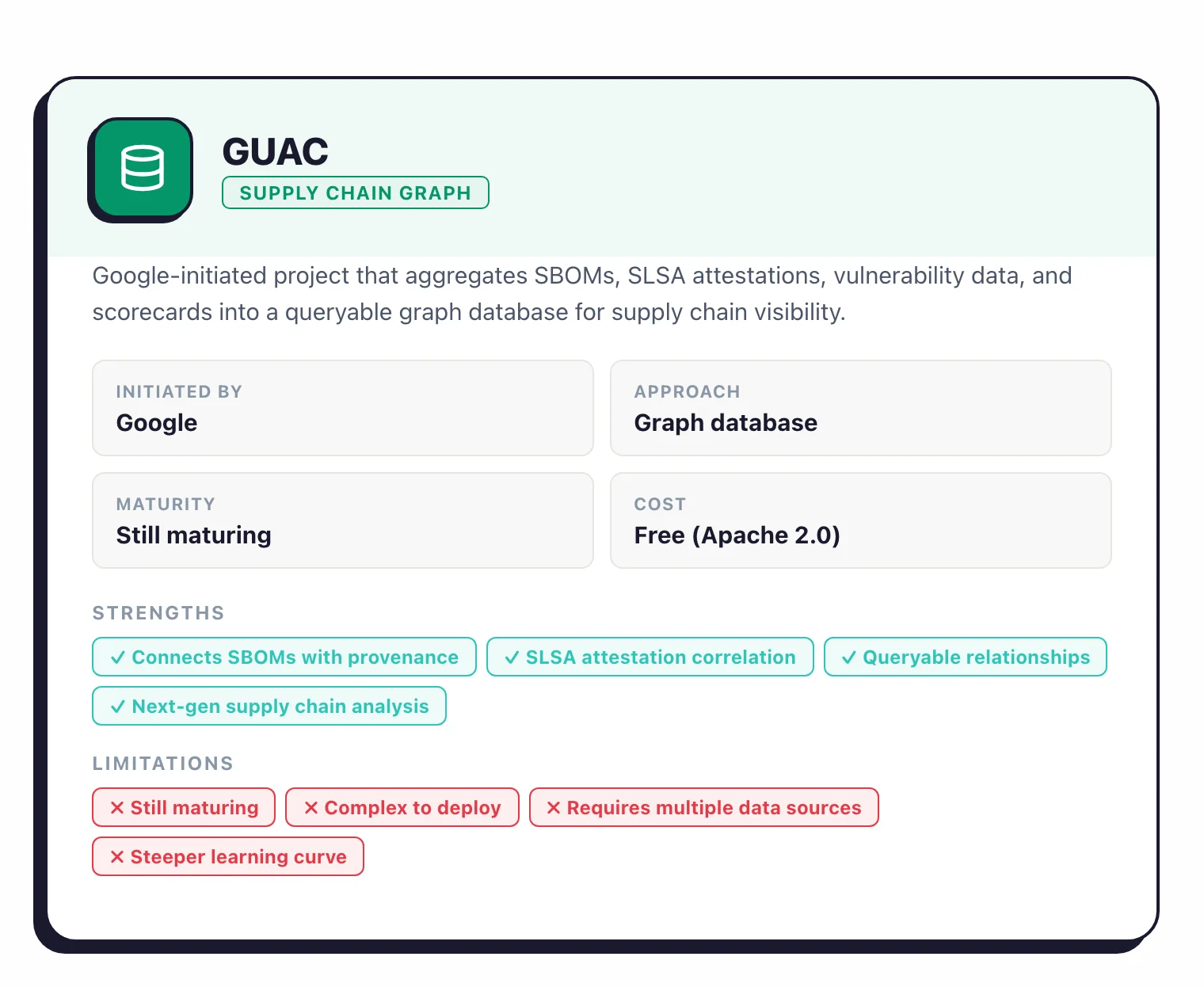
GUAC (Graph for Understanding Artifact Composition) is a Google-initiated open-source project that aggregates software supply chain metadata (SBOMs, SLSA attestations, vulnerability data, and scorecard results) into a queryable graph database.
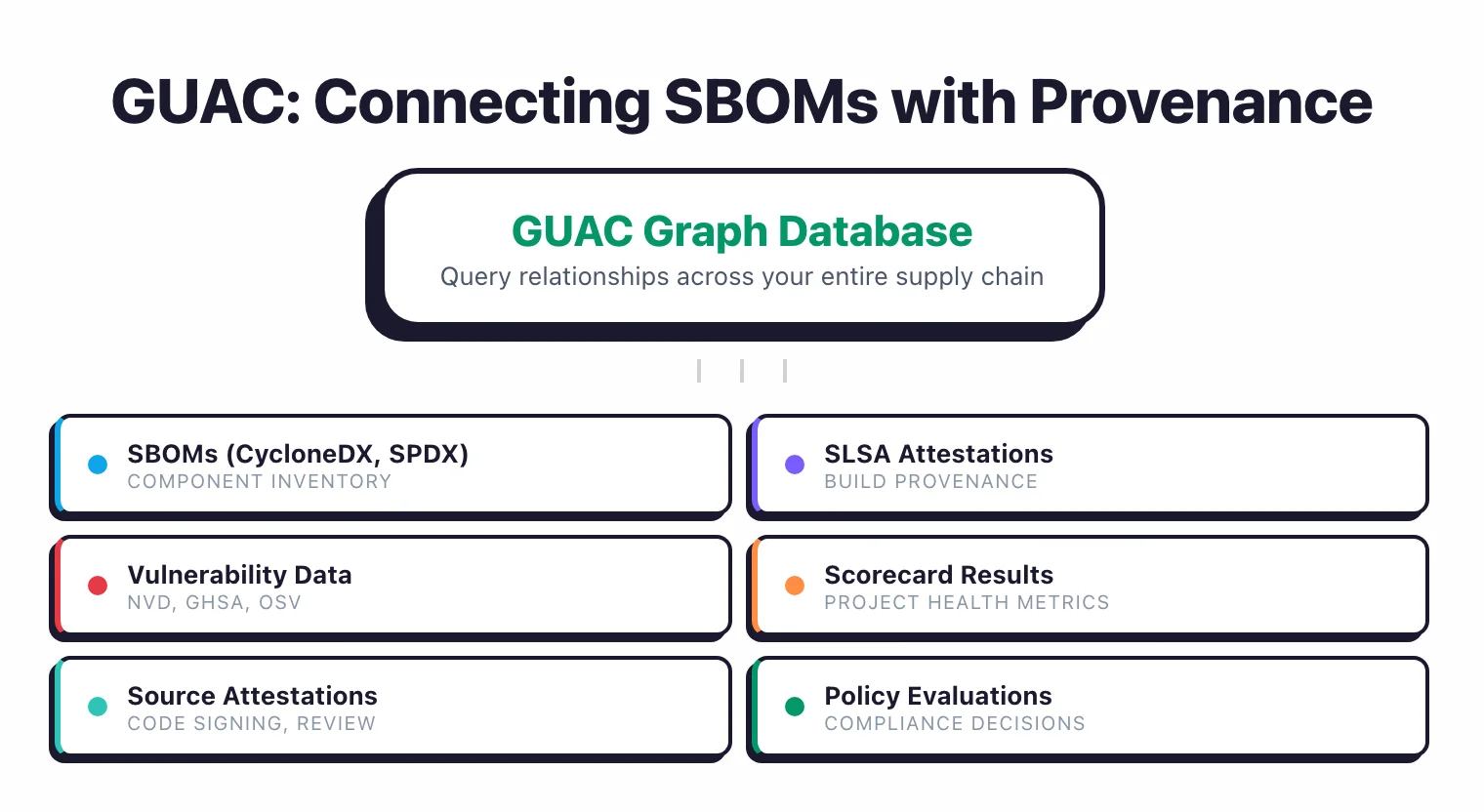
Where Dependency-Track tracks vulnerabilities against SBOMs, GUAC connects SBOMs with build provenance, source attestations, and organizational context. You can query relationships like “show me every deployment that uses a package built without SLSA Level 2 provenance.” The project is still maturing but represents the next evolution of SBOM analysis.
Best for: Organizations building advanced supply chain security programs that need to correlate SBOMs with provenance, attestations, and policy data.
Bomber#
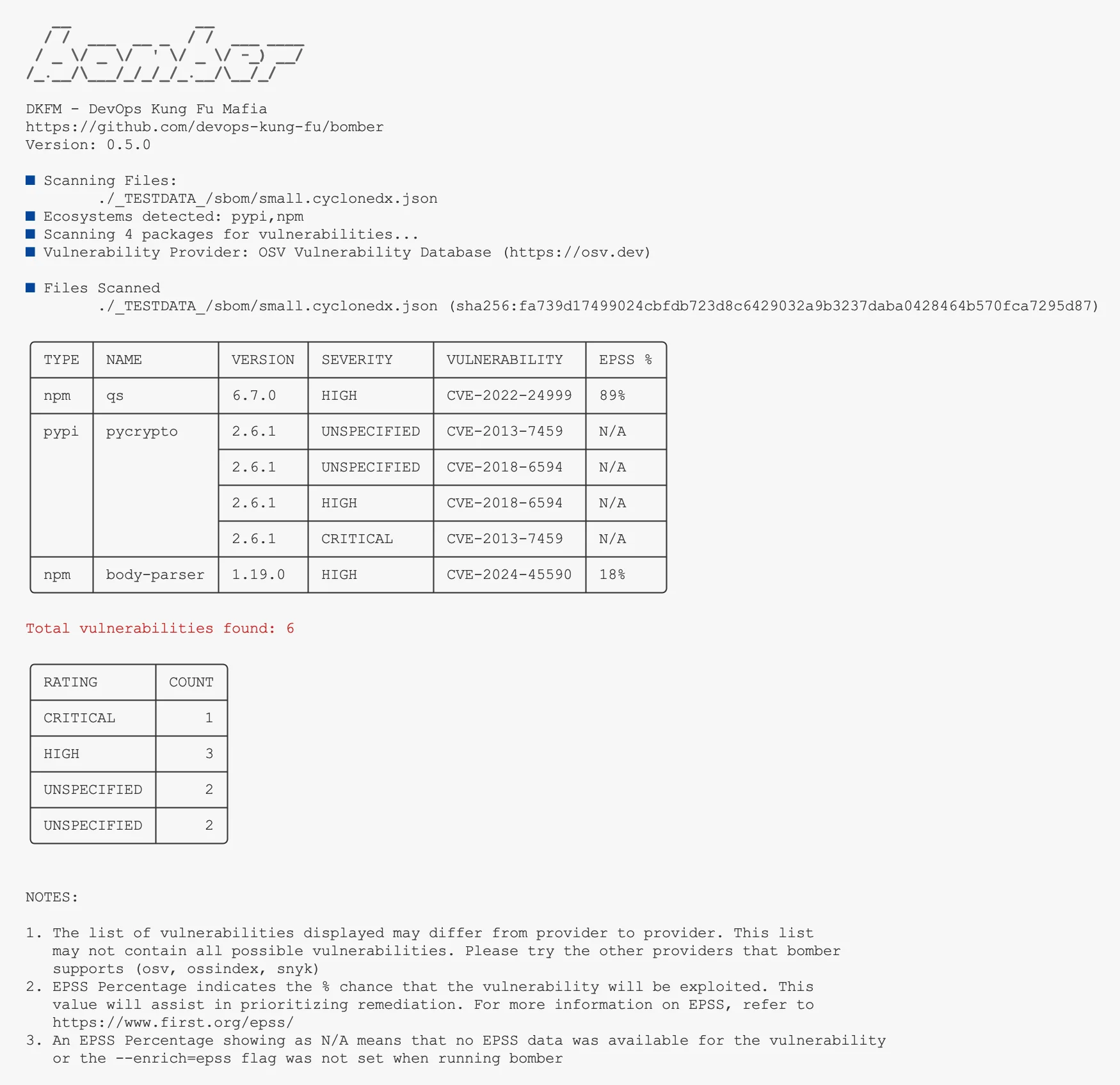
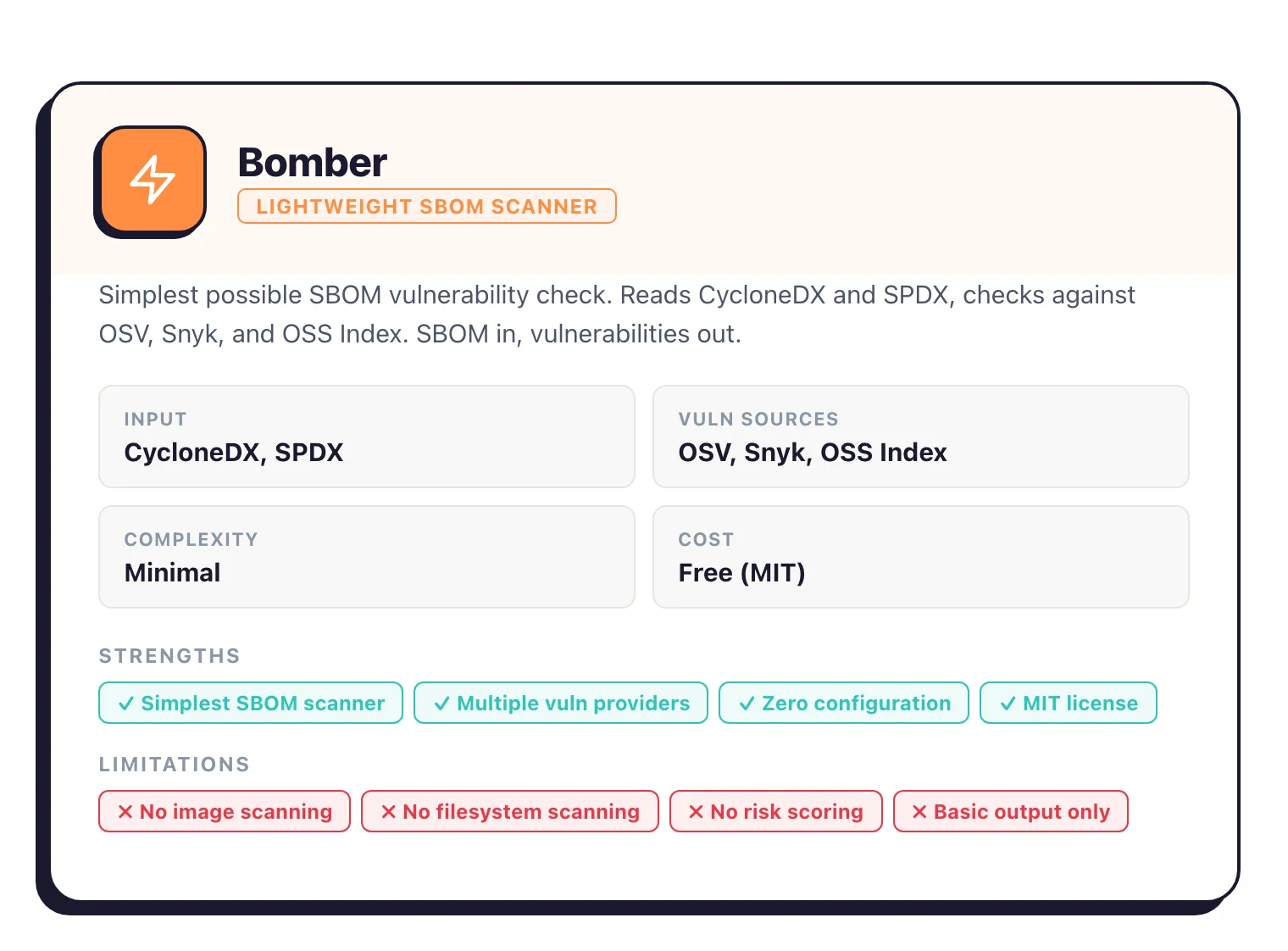
Bomber is a lightweight open-source tool that scans SBOM files for known vulnerabilities. It reads CycloneDX and SPDX SBOMs and checks components against multiple providers (OSV, Snyk, OSS Index).
It is simpler than Grype – no image scanning, no filesystem scanning, just SBOM-in, vulnerabilities-out.
Best for: Teams that want the simplest possible SBOM vulnerability check without the broader feature set of Grype.
Malicious package detection with SBOM data#
An SBOM tells you what is in your software. It does not tell you whether any of those components is a typosquat, a compromised-maintainer release, or a package that silently exfiltrates secrets at install time. Catching those requires a second layer on top of the SBOM itself.
Dependency-Track runs a portfolio-wide policy engine that consumes SBOM uploads and evaluates each component against configurable rules — you can, for example, fail any SBOM that contains a package flagged in the OpenSSF Malicious Packages feed. Its VEX support lets your security team mark specific CVEs as non-exploitable so alerts quiet down without losing the finding.
Socket takes the complementary angle: it imports SBOMs via the Socket API and scores each dependency using behavioural analysis (install-script inspection, network-call profiling, obfuscation detection) rather than CVE matching alone. That catches malicious packages before a CVE exists.
GUAC sits at the graph layer — it aggregates your SBOMs, SLSA provenance, and vulnerability feeds into a queryable knowledge graph so you can ask questions like “show every deployment that contains a package built without SLSA Level 2 provenance.” It is the newest of the three and still maturing, but it is the right long-term answer for organisations with a mature supply-chain programme.
Dependency update automation sits alongside this stack. Dependabot , Renovate , and the anchore/sbom-action workflow all push SBOM-aware automation into the pull-request lifecycle, which is where exposure windows actually close.
Feature comparison table#
Generation tools#
| Tool | License | Formats | Language ecosystems | Container support | CI/CD integration | Vuln matching |
|---|---|---|---|---|---|---|
| Syft | Apache 2.0 | CycloneDX, SPDX | 30+ | Docker, OCI, Singularity | GitHub Action | No (pair with Grype) |
| Trivy | Apache 2.0 | CycloneDX, SPDX | 15+ | Docker, OCI | GitHub Action, GitLab CI | Yes (built-in) |
| CycloneDX plugins | Apache 2.0 | CycloneDX | Per-plugin | No | Build system native | No |
| FOSSA | Freemium | CycloneDX, SPDX | 17+ | Yes | GitHub, GitLab, Jenkins | Yes |
| Anchore Enterprise | Commercial | CycloneDX, SPDX | 30+ | Docker, OCI | GitHub, GitLab, Jenkins | Yes (continuous) |
| Microsoft SBOM Tool | MIT | SPDX | 10+ | Limited | Azure DevOps | No |
| Tern | BSD-2 | CycloneDX, SPDX | OS packages | Docker | Limited | No |
Analysis and management tools#
| Tool | License | SBOM input | Continuous monitoring | Vulnerability sources | Portfolio tracking |
|---|---|---|---|---|---|
| Dependency-Track | Apache 2.0 | CycloneDX, SPDX | Yes | NVD, GHSA, OSV, OSS Index | Yes |
| Grype | Apache 2.0 | CycloneDX, SPDX, Syft JSON | No (point-in-time) | NVD, GHSA, distro feeds | No |
| GUAC | Apache 2.0 | CycloneDX, SPDX | Graph-based | Multiple (via integration) | Yes (graph queries) |
| Bomber | MIT | CycloneDX, SPDX | No | OSV, Snyk, OSS Index | No |
Regulatory requirements#
SBOM mandates are live in multiple jurisdictions. Here is what each regulation specifically requires and when.
US Executive Order 14028#
Signed May 2021, EO 14028 requires software vendors selling to US federal agencies to provide SBOMs as part of their software supply chain security practices.
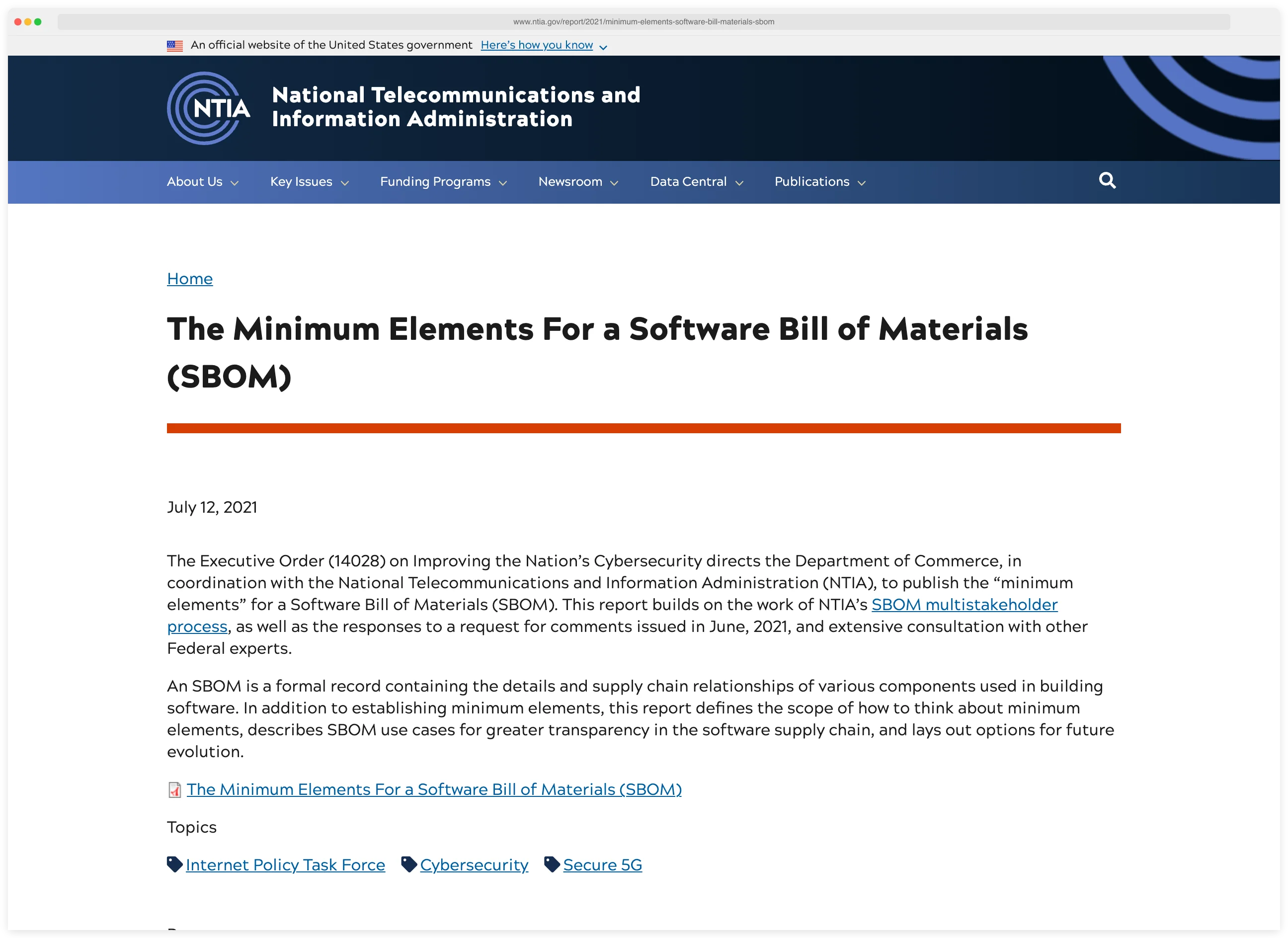
NTIA published minimum elements guidance defining what an SBOM must contain: supplier name, component name, version, dependency relationships, author, and timestamp. SBOMs must be machine-readable in CycloneDX or SPDX format.
Federal agencies are already enforcing this in procurement. If you sell software to the US government, SBOM generation is not optional.
EU Cyber Resilience Act (CRA)#
The CRA applies to manufacturers of products with digital elements sold in the EU market. The timeline has two phases:
- September 11, 2026: Vulnerability and incident reporting obligations take effect. Manufacturers must report actively exploited vulnerabilities within 24 hours of becoming aware of them.
- December 11, 2027: Full compliance required, including machine-readable SBOM delivery as part of technical documentation, available for audit by market surveillance authorities.
The CRA affects any software, firmware, or connected device sold in the EU. Open-source projects that are not monetized are exempt, but commercial products that incorporate open-source components are not.
Note: The CRA exempts unmonetized open-source projects, but it does not exempt open-source components bundled inside commercial products. If you ship a paid SaaS backed by Postgres and Nginx, the CRA obligations apply to the whole stack you ship — including every OSS dependency baked into the image.
PCI DSS 4.0#
PCI DSS 4.0 requires organizations handling payment card data to maintain an inventory of all software components, both custom and third-party, and a process for identifying vulnerabilities in those components. While it does not explicitly mandate “SBOM” by name, the inventory requirement maps directly to what SBOM tooling produces.
FDA medical device guidance#
Since October 2023, the FDA requires an SBOM as part of premarket cybersecurity submissions for medical devices. All commercial, open-source, and off-the-shelf software components must be disclosed with versions and known vulnerabilities.
What this means for tooling#
The regulations converge on the same requirement: know what is in your software and prove it with a machine-readable inventory.

Key Insight
Every major regulator converges on the same ask: a machine-readable inventory plus a way to prove it. The US wants SPDX or CycloneDX via EO 14028, the EU wants the same under the CRA, the FDA wants it for medical devices, and PCI DSS 4.0 wants it for payment environments. One tool stack covers all four if it emits both formats.
Any tool that generates CycloneDX or SPDX output meets the format requirement. The choice between open-source and commercial depends on whether you also need lifecycle management, audit reporting, and policy enforcement.
How to choose#
SBOM tooling is not a single-tool problem. Most organizations need a combination: one tool to generate, another to analyze, and possibly a third to manage and distribute.
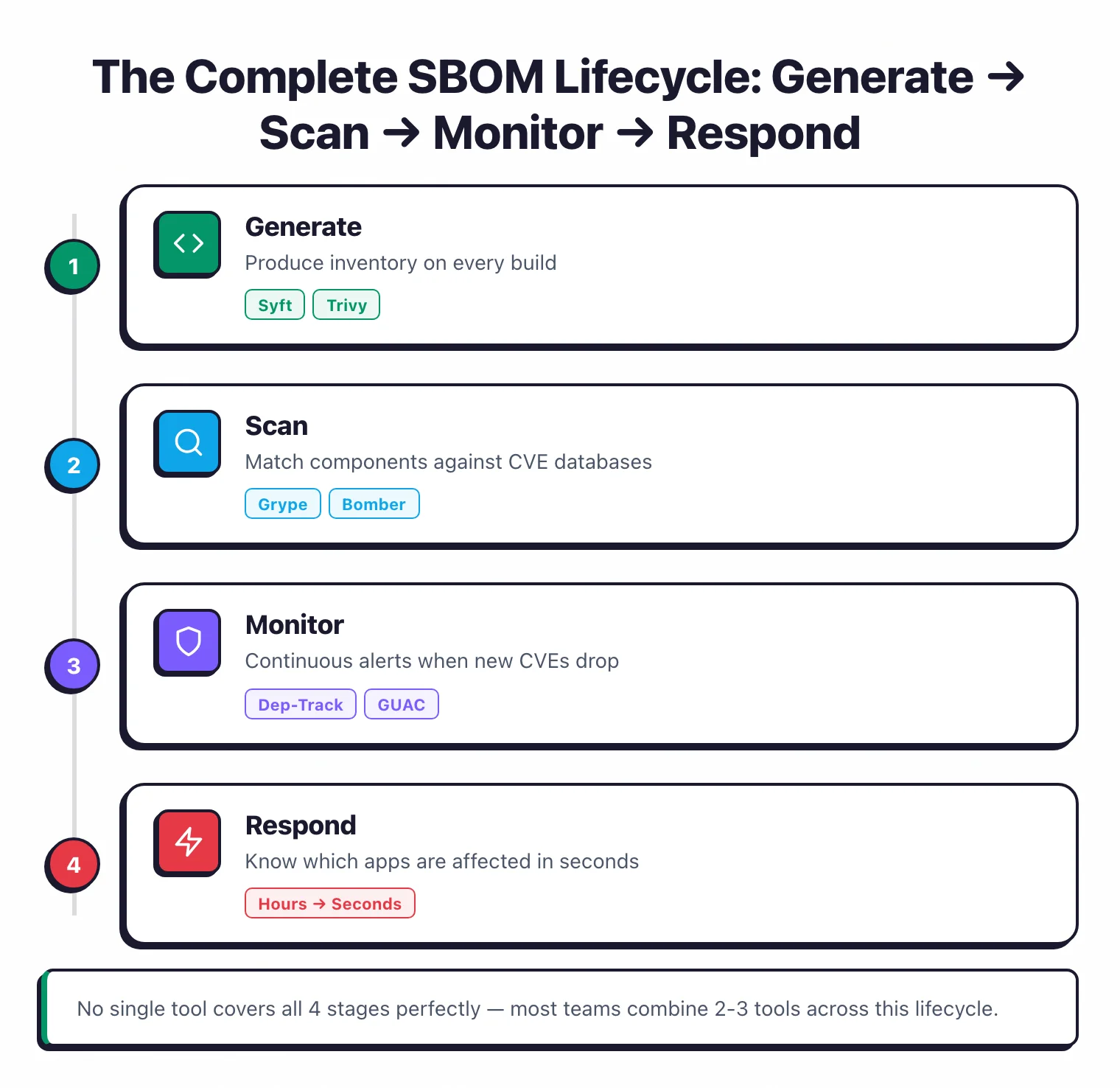
Start with the question: what do you need?#
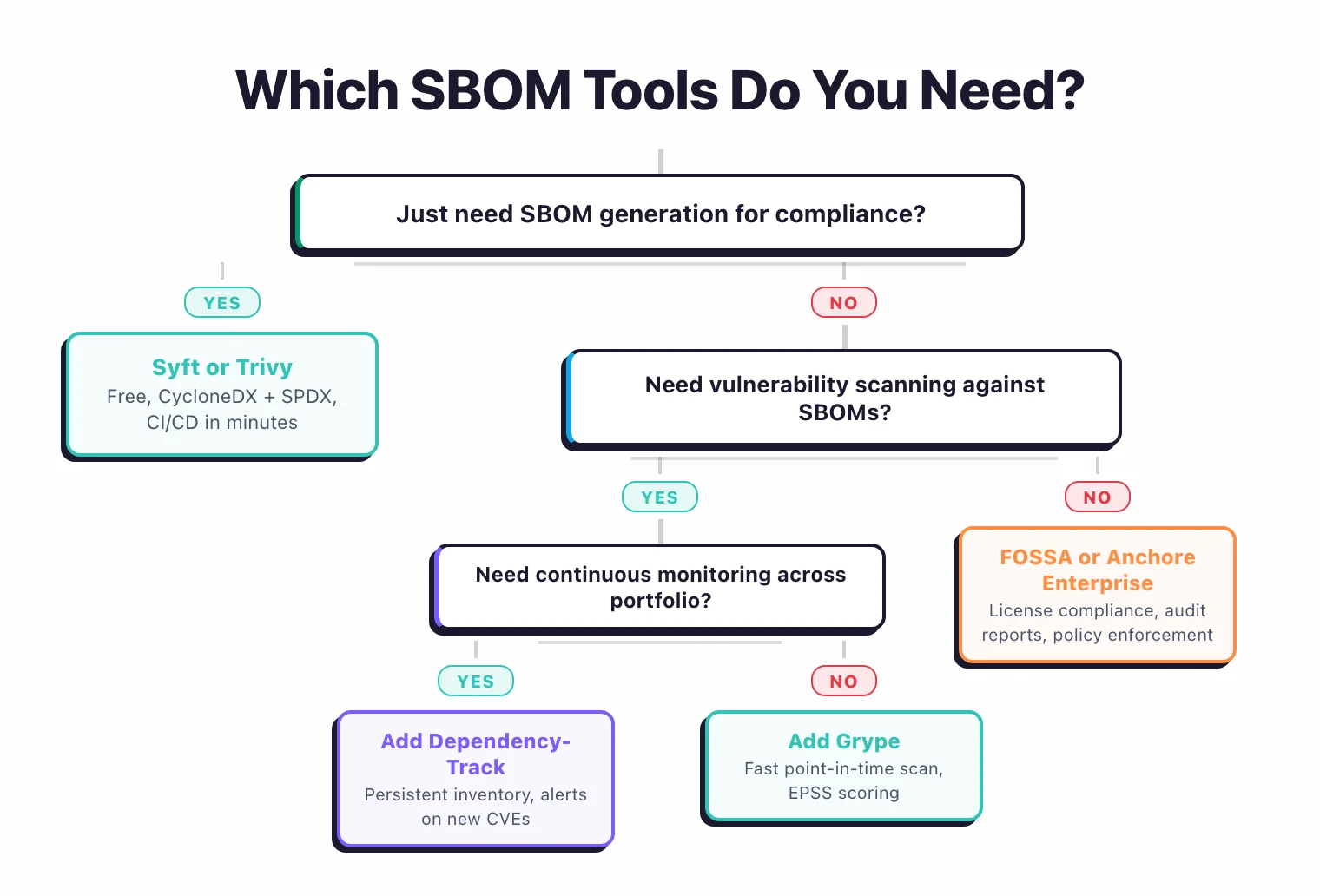
Just generation for compliance? Syft or Trivy. Both are free, produce CycloneDX and SPDX output, and integrate into CI/CD in minutes.
If you already use Trivy for vulnerability scanning, use its SBOM output flag. If you want a dedicated generator, use Syft.
Vulnerability matching against SBOMs? Add Grype. It accepts Syft output directly and scans against multiple vulnerability databases with EPSS-based risk scoring.
Continuous monitoring across a portfolio? Add Dependency-Track. Upload SBOMs from your CI pipeline and get alerts when new CVEs affect components you already shipped.
License compliance alongside security? FOSSA or Black Duck. These platforms track license obligations, generate attribution reports, and provide SBOM portals for distribution.
Government compliance with policy enforcement? Anchore Enterprise. Pre-built policy packs for FedRAMP, NIST, and DISA, with air-gapped deployment for classified environments.
Open-source vs commercial#
The open-source stack – Syft, Grype, and Dependency-Track – covers generation, vulnerability scanning, and continuous monitoring at no cost. It handles the core requirements of EO 14028 and CRA.
The tradeoff is that you manage the infrastructure, write your own policies, and build your own reporting.
Commercial platforms like FOSSA, Anchore Enterprise, and Snyk add license intelligence, pre-built compliance frameworks, audit-ready reports, and support contracts. The added cost makes sense when your compliance requirements go beyond “generate and scan” into “prove it to an auditor.”
Key Insight
The open-source stack covers compliance. The commercial stack covers audits. Syft + Grype + Dependency-Track will generate, scan, and monitor at zero cost — that is enough for EO 14028 and the CRA on paper. FOSSA and Anchore Enterprise earn their price tag when the procurement team needs a portal, a branded PDF, and a support contract to hand to an auditor.
Recommended stacks#
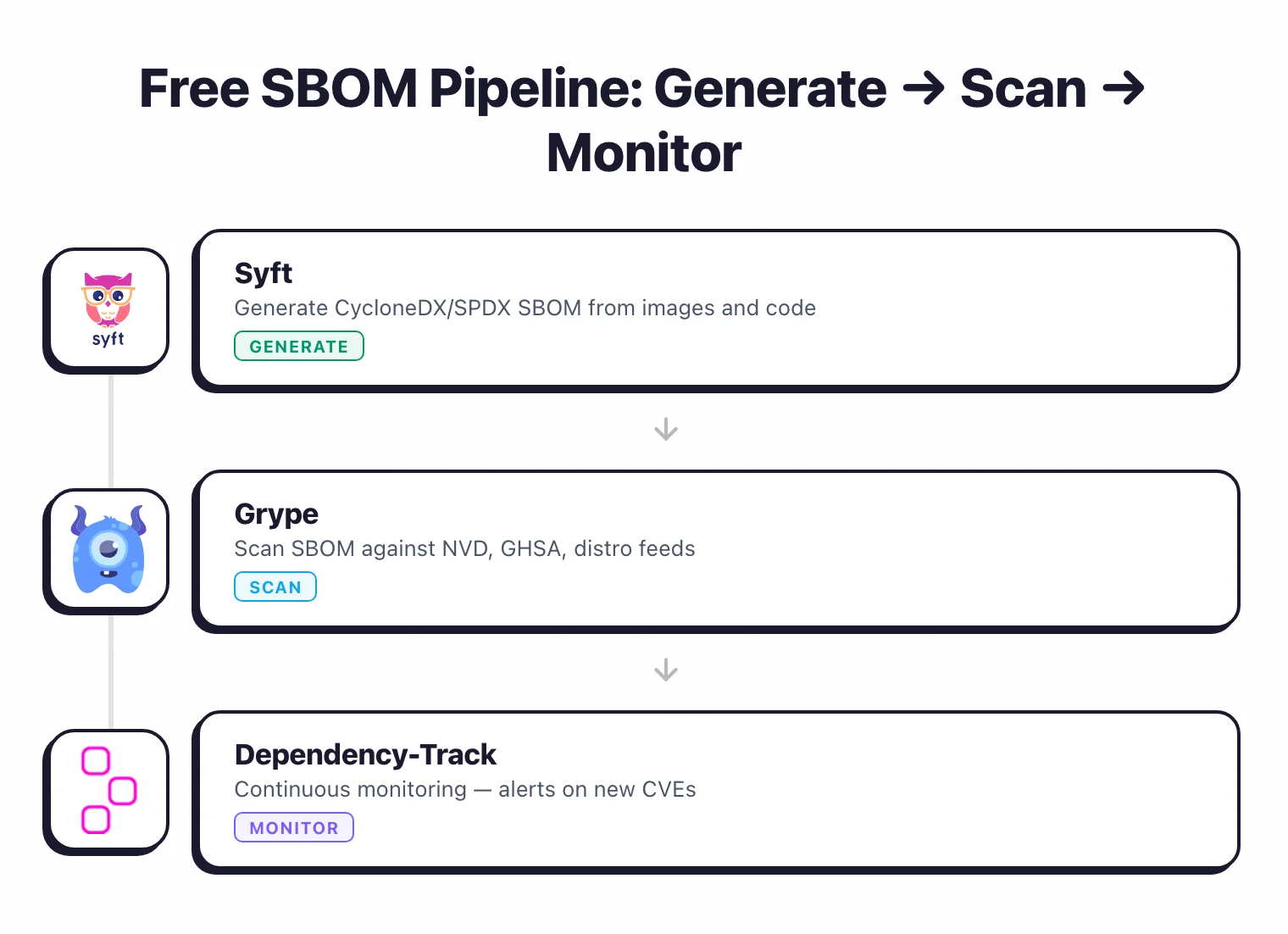
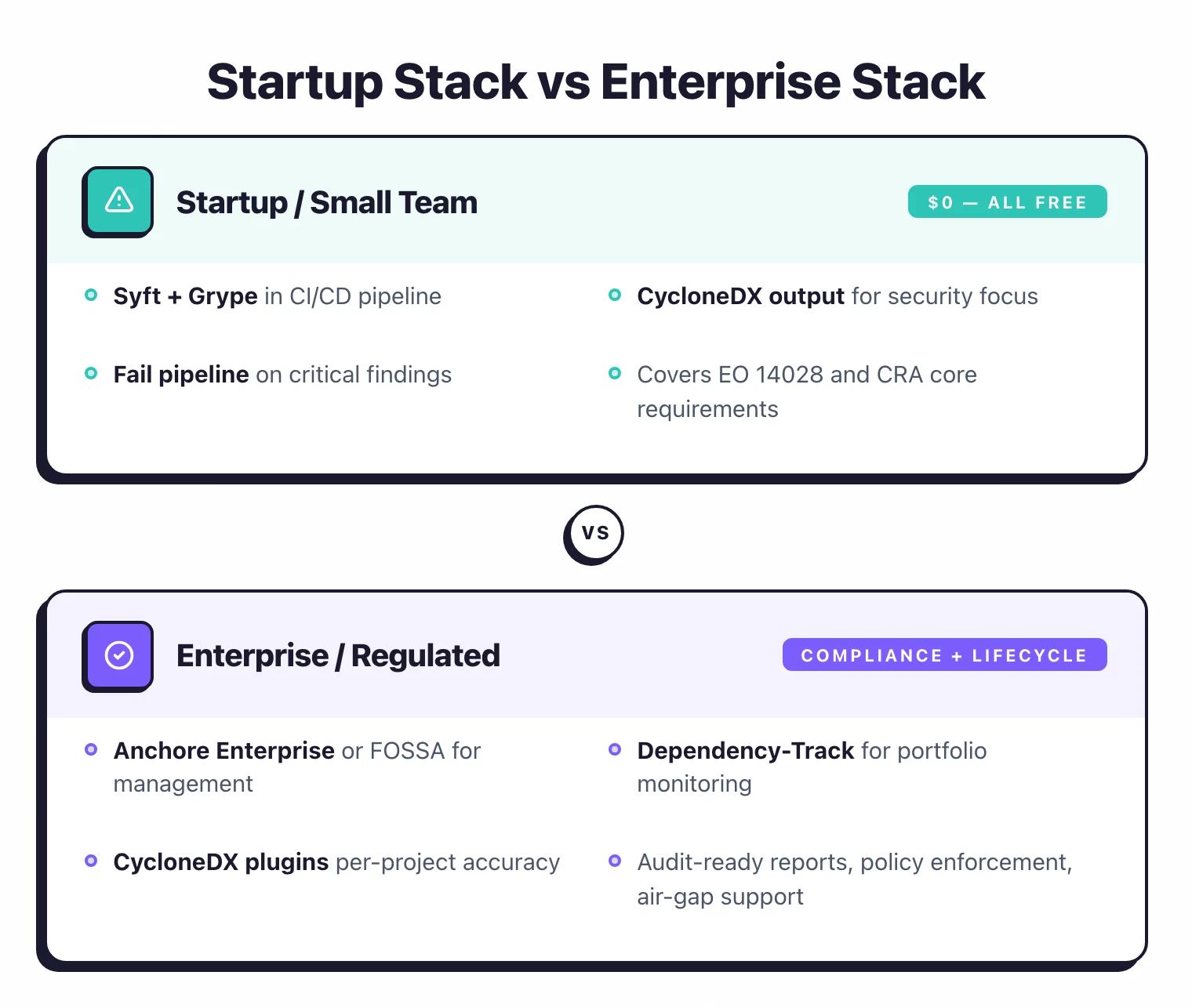
Startup / small team: Syft + Grype in CI/CD. Generate SBOMs on every build, scan for vulnerabilities, fail the pipeline on critical findings. Total cost: zero.
Mid-size engineering org: Syft + Grype + Dependency-Track. Add continuous monitoring so new CVEs trigger alerts against deployed applications. Host Dependency-Track on Docker or Kubernetes.
Enterprise / regulated industry: Anchore Enterprise or FOSSA for centralized management, plus Dependency-Track for portfolio-wide monitoring. Add CycloneDX build plugins for the most accurate per-project SBOMs.
Government / defense: Anchore Enterprise Federal Edition with air-gapped deployment, FedRAMP policy packs, and SBOM attestation support.
FAQ#
Further reading: What is SBOM? | What is SCA? | SCA Tools | Supply Chain Attacks Guide | Trivy vs Grype
Which SBOM format should I pick — CycloneDX or SPDX?#
Pick the one your downstream consumer expects. Security platforms, scanner pipelines, and most DevSecOps tooling expect CycloneDX. Federal procurement, licence review, and legal teams usually expect SPDX. Generate whichever format matches the next person in the pipeline; every tool in this comparison emits both.
Does Syft need Grype?#
Not strictly — Syft on its own produces a valid CycloneDX or SPDX SBOM you can hand to any consumer. But Syft does not match against CVEs. The Syft + Grype pair is the common pattern because Grype is purpose-built to scan SBOMs that Syft produces, and the two share a maintainer team at Anchore.
Do I need an SBOM for EU CRA compliance?#
Yes, by December 11, 2027. The EU Cyber Resilience Act starts enforcing vulnerability reporting on September 11, 2026 and full machine-readable SBOM delivery on December 11, 2027. Open-source projects that are not monetized are exempt; commercial products that bundle open-source components are not.
Can I convert between CycloneDX and SPDX?#
The CycloneDX CLI supports format conversion, but the round-trip is lossy. Native CycloneDX VEX entries may not survive the jump to SPDX 2.x, and SPDX licence expressions sometimes flatten into plain strings in CycloneDX. If a regulator asks for a specific format, regenerate the SBOM in that format from source rather than converting an existing one.
Is there a free enterprise-grade SBOM tool?#
Yes. Syft (generation) + Grype (vulnerability matching) + Dependency-Track (continuous monitoring) is the zero-cost open-source stack that satisfies the core EO 14028 and EU CRA machine-readable-inventory requirement. The commercial tier earns its price tag when you need SBOM distribution portals, audit-ready reports, and licence-compliance policy engines — see FOSSA and Anchore Enterprise .
Visit these projects#
- Syft on GitHub · Grype on GitHub — maintained by Anchore
- Trivy — maintained by Aqua Security
- Dependency-Track — OWASP Flagship project
- CycloneDX · SPDX — SBOM format standards
- GUAC · Bomber on GitHub
Looking for commercial SBOM platforms? FOSSA , Anchore Enterprise , Snyk , and Black Duck are the most-used options for license intelligence and audit-ready reporting.







