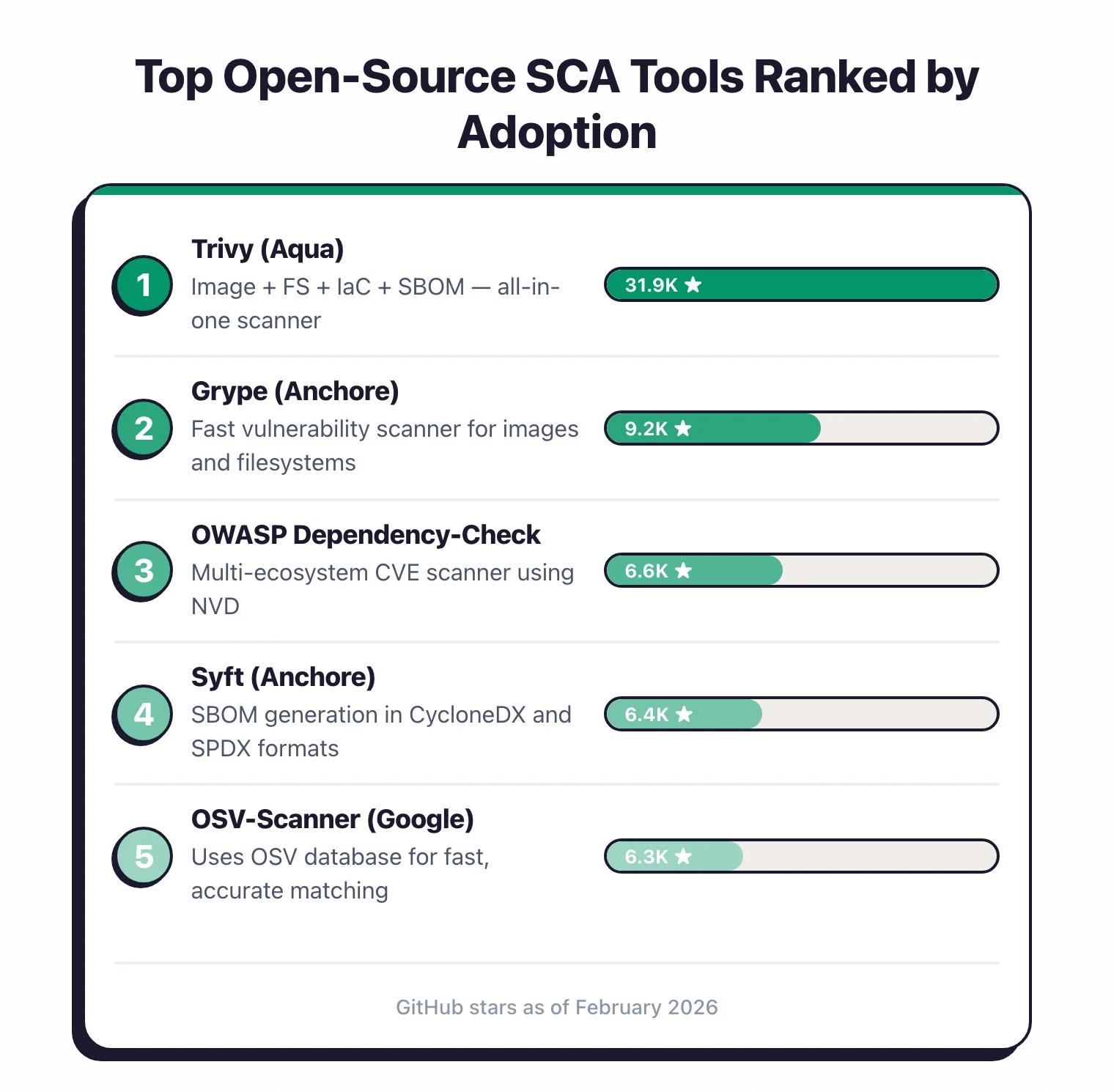
Software Composition Analysis (SCA) tools scan your application dependencies for known vulnerabilities, license risks, and outdated components. The leading open source SCA tools in 2026 are Trivy, Grype, OSV-Scanner, OWASP Dependency-Check, and Syft. All five are free, self-hosted, and backed by the same vulnerability databases commercial scanners use.
What is an open-source SCA tool?
An open-source SCA tool is a Software Composition Analysis scanner whose source code is publicly available under a permissive licence and that you can run yourself without a vendor contract. The core job is the same as a commercial SCA: read your dependency manifest, resolve the full direct and transitive tree, and check every component against one or more vulnerability databases.
The “open-source” label changes two things. First, zero licence cost — there is no per-developer or per-project fee. Second, transparency — the matching rules, database ingestion logic, and output formats are all inspectable, which matters when a scanner produces a false positive you cannot explain to a developer.
Open-source SCA differs from free commercial tiers (Snyk Free, Dependabot, Mend Bolt) in one important way. Free tiers ship a trimmed version of a vendor’s product and keep the vulnerability pipeline proprietary. Open-source tools like Trivy, Grype, and OSV-Scanner publish every piece — the scanner binary, the matching logic, and the advisory ingestion. You can fork, audit, or self-host the whole stack in an air-gapped network.
Why choose open-source SCA tools?

The core job of an SCA tool is straightforward: read your dependency manifests, resolve the full tree, and check every component against vulnerability databases. Open-source tools do this well.
They pull from the same databases that commercial tools use – NVD, GitHub Advisory Database, OSV – and they run in the same CI/CD pipelines.
The cost argument is obvious but worth stating. Commercial SCA platforms charge per-developer or per-project fees that can reach five or six figures annually.
For startups, small teams, and open-source projects, that budget simply does not exist. Open-source SCA removes the financial barrier entirely.
Beyond cost, open-source SCA tools offer transparency. You can inspect exactly how vulnerability matching works, contribute rules, and customize behavior.
When a tool produces a false positive, you can trace the logic and understand why. With commercial tools, the matching engine is a black box.
CI/CD flexibility is another advantage. Every open-source SCA tool on this list ships as a standalone CLI binary.
No agent installations, no SaaS accounts, no phone calls with sales engineers. Install it, point it at your code, and get results.
This makes open-source tools ideal for air-gapped environments, self-hosted CI systems, and teams that want full control over their toolchain.
The open-source SCA ecosystem has matured quickly. Trivy now has 32,000+ GitHub stars and scans containers, filesystems, and IaC.
Grype introduced EPSS-based risk scoring. OSV-Scanner ships with guided remediation.
These are not toy tools filling a gap until you can afford a commercial license. For many teams, they are the final answer.
Pick your next step
Trivy vs Grype head-to-head
All-in-one binary versus focused vuln matcher with EPSS scoring — pick one or run both, with setup notes for each.
→Replace Dependabot on GitLab or Bitbucket
Renovate covers 90+ managers across multi-platform Git — plus 4 more alternatives compared on reachability and noise.
→See the full SCA landscape
All 30+ SCA tools — open-source, freemium, and commercial — sorted by ecosystem coverage, reachability, and SBOM support.
→Top open-source SCA tools
1. Trivy
Trivy is the most-starred open-source security scanner on GitHub with 32,200+ stars. Built by Aqua Security and released under Apache 2.0, it scans container images, filesystems, git repositories, VM images, and Kubernetes clusters for vulnerabilities, misconfigurations, secrets, and license issues.
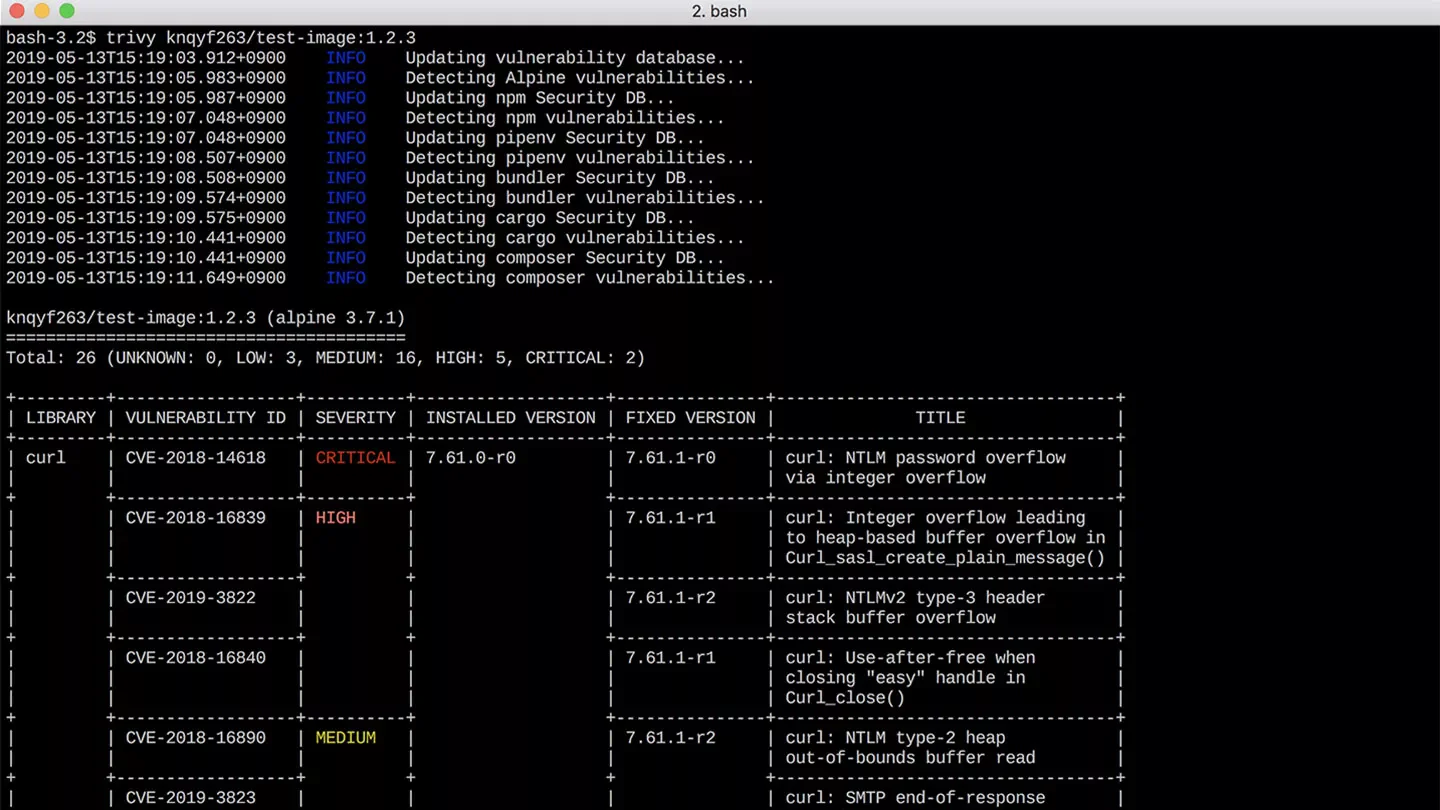
What makes Trivy stand out for SCA is its breadth. A single trivy fs . command scans your dependency lock files across Go, Java, Node.js, Python, Ruby, Rust, PHP, .NET, Dart, Elixir, and Swift.
It also generates SBOMs in CycloneDX and SPDX formats, so you get inventory and vulnerability scanning from one tool.
Trivy’s vulnerability database covers NVD, GitHub Advisories, and distribution-specific feeds (Alpine, Debian, Ubuntu, RHEL, Amazon Linux). The database downloads automatically and updates with each scan.
Best for: Teams that want a single tool covering dependency scanning, container scanning, IaC checks, and SBOM generation.
Pro tip: Start with Trivy as your default CI step — run trivy fs --severity HIGH,CRITICAL --exit-code 1 . in GitHub Actions and you get dependency, IaC and secret scanning in one binary with no tuning on day one.
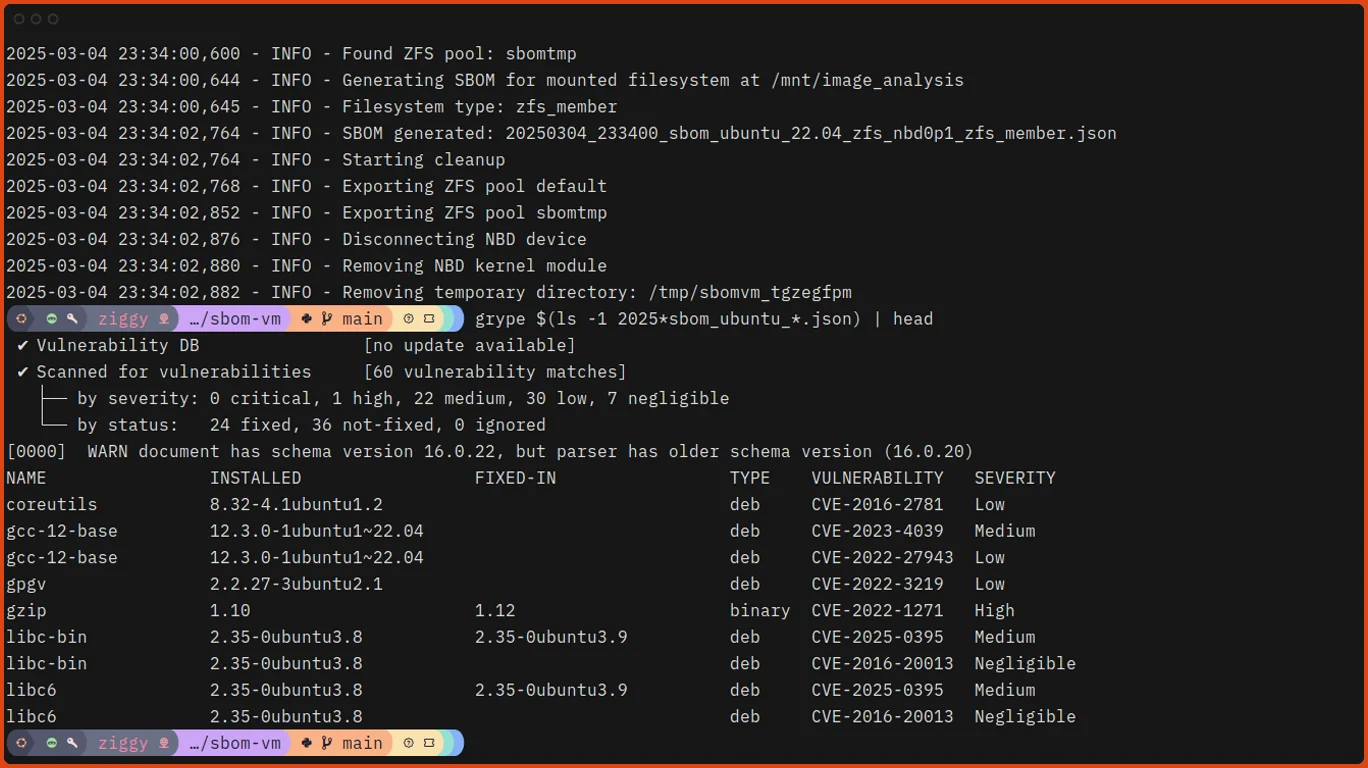
2. Grype
Grype is Anchore’s open-source vulnerability scanner with 11,500 GitHub stars. Where Trivy tries to do everything, Grype focuses on one thing: matching packages against vulnerability databases with high accuracy.
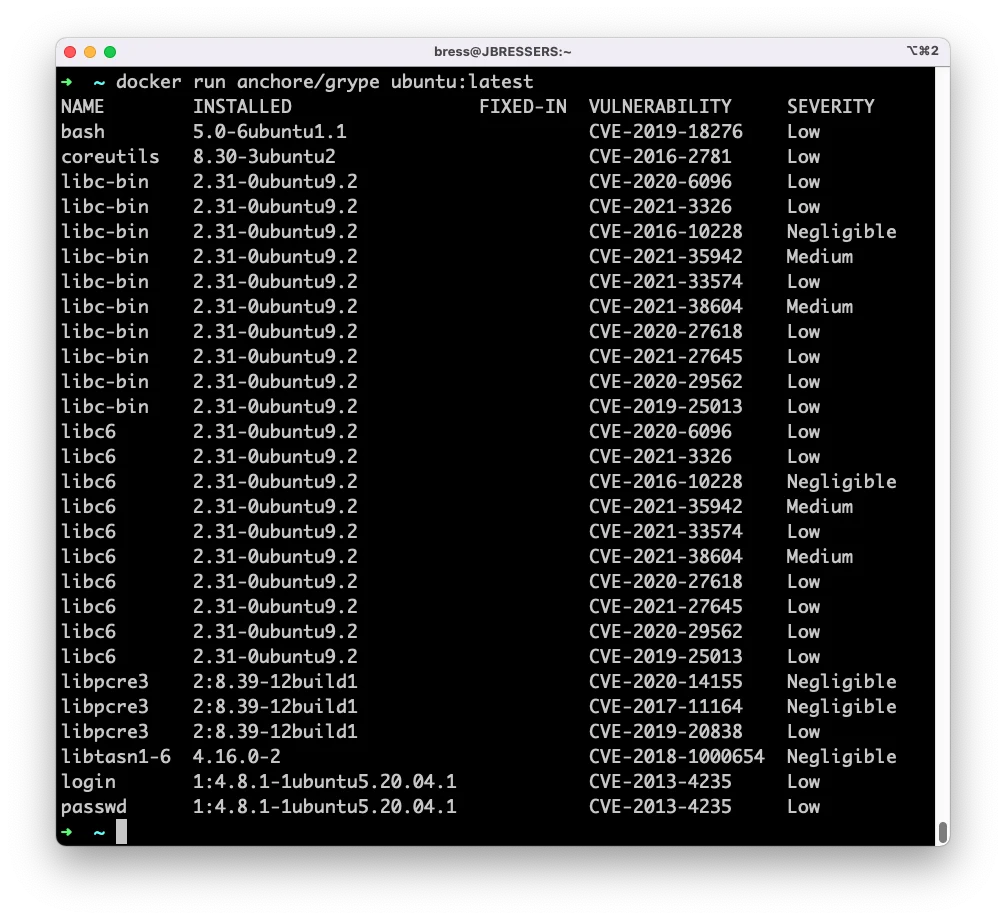
Grype’s standout feature is its risk scoring engine. Each finding gets a composite score from 0 to 10 that combines CVSS severity, EPSS exploit probability (the 30-day likelihood of exploitation), and KEV catalog status (whether CISA lists it as actively exploited).
This scoring helps teams prioritize what to fix first instead of working through a flat list sorted by CVSS alone.
Grype covers 20+ language ecosystems and all major Linux distributions. It accepts container images, filesystem directories, and SBOM files (CycloneDX, SPDX, Syft JSON) as input.
OpenVEX support lets you suppress findings your security team has already assessed.
Best for: Teams that want a fast, focused vulnerability scanner with advanced risk scoring and SBOM-first workflows.
3. OWASP Dependency-Check
OWASP Dependency-Check is the oldest actively maintained open-source SCA project. As an OWASP Flagship Project with 7,400 GitHub stars and 290+ contributors, it has been a standard in enterprise Java shops for over a decade. The current version is 12.2.0.
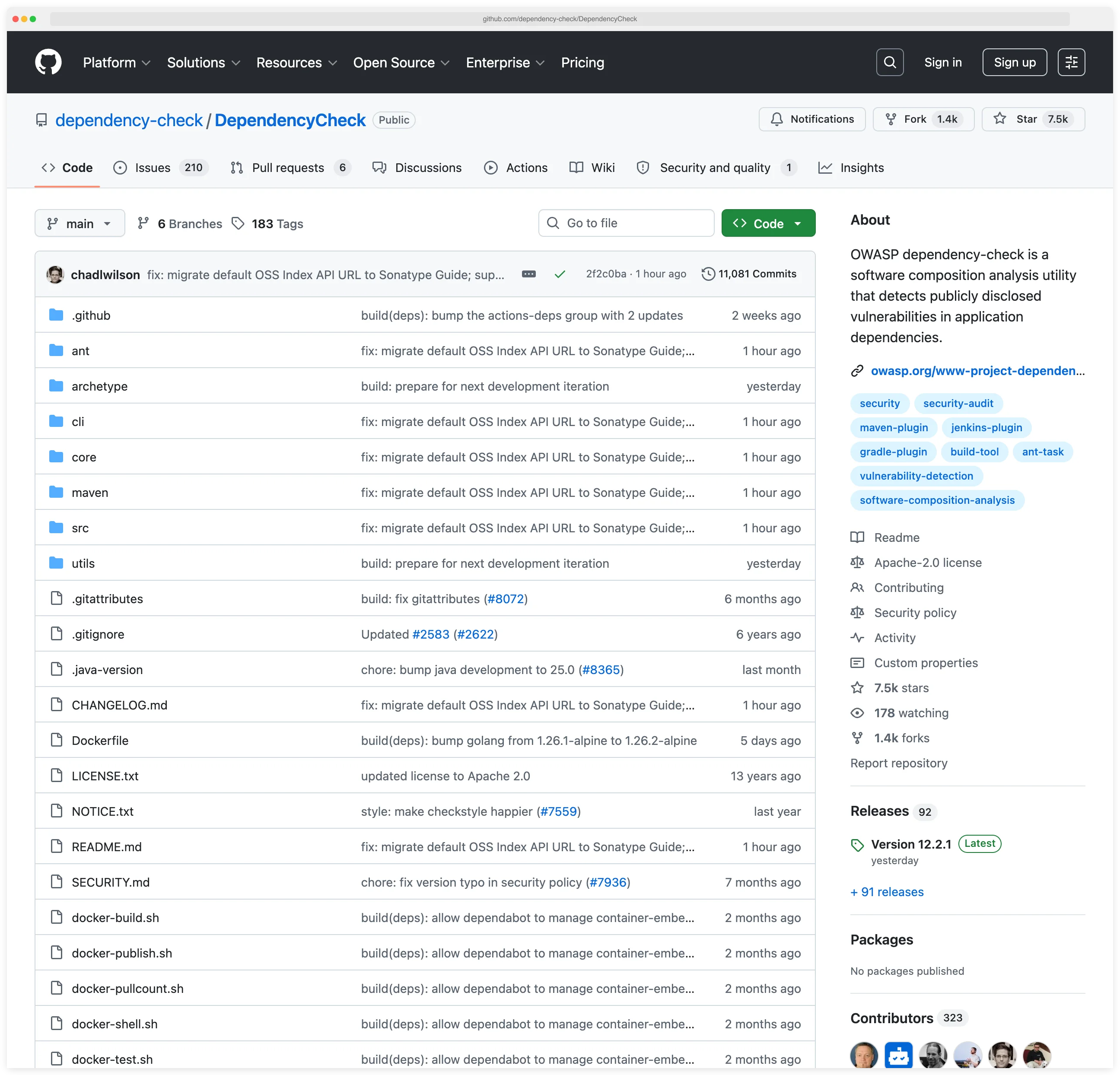
Dependency-Check identifies vulnerabilities using CPE (Common Platform Enumeration) matching against the NVD.
It has native plugins for Maven, Gradle, and Ant with failBuildOnCVSS threshold gating built in.
Beyond Java, it supports npm, pip, Ruby Bundler, Go modules, and NuGet.
The CPE matching approach produces more false positives than ecosystem-specific matching (which Grype and Trivy use), but it also catches vulnerabilities that ecosystem-specific tools sometimes miss.
An NVD API key is strongly recommended to avoid rate-limited database updates.
Note: Dependency-Check matches packages via CPE names and will produce more false positives than ecosystem-aware scanners like Grype or Trivy. Budget time to tune suppression.xml entries, and request an NVD API key before rolling it into CI — without one, the database refresh becomes the slowest step of every build.
Best for: Enterprise Java teams with Maven or Gradle builds that need a proven, OWASP-backed scanner with native build tool integration.
4. Syft
Syft is Anchore’s open-source SBOM generation tool with 8,400 GitHub stars. It does not scan for vulnerabilities itself.
Instead, it catalogs every software component in your container images, filesystems, and archives, outputting SBOMs in SPDX and CycloneDX formats.
Syft auto-detects dozens of package ecosystems – Alpine, Debian, RPM, npm, pip, Maven, Go modules, Ruby gems, Rust crates, PHP Composer, .NET NuGet, and more.
It runs entirely offline with no cloud dependencies or API calls.
The intended workflow is to pair Syft with Grype: generate the SBOM once with Syft, then scan it with Grype whenever the vulnerability database updates.
This separation lets you cache SBOMs and avoid redundant image analysis.
Syft also supports signed SBOM attestations using the in-toto specification for supply chain verification.
Best for: Teams that need SBOM generation for compliance (Executive Order 14028, EU CRA) or want a Syft + Grype pipeline for supply chain visibility.
5. OSV-Scanner
OSV-Scanner is Google’s free vulnerability scanner, querying the OSV.dev database – the largest aggregated source of open-source vulnerability data, pulling from 30+ ecosystem-specific sources. It has 8,300+ GitHub stars and is written in Go.
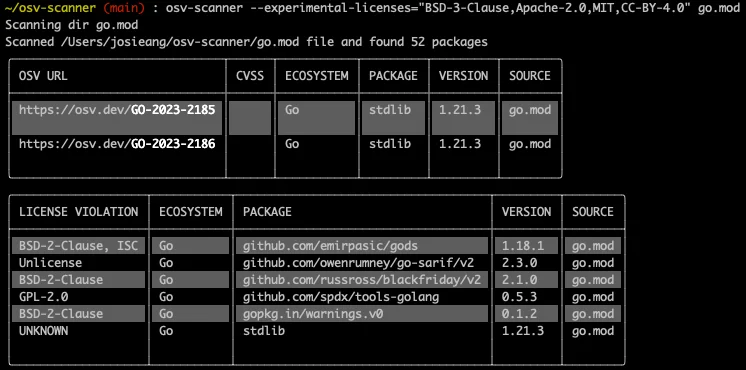
The standout capability is guided remediation. Instead of dumping a CVE list and walking away, OSV-Scanner V2 analyzes your dependency graph and recommends the minimum set of upgrades, ranked by severity, dependency depth, and return on investment.
Guided remediation currently supports npm and Maven, with more ecosystems planned.
OSV-Scanner also does layer-aware container image scanning for Alpine, Debian, and Ubuntu images. It identifies which layer introduced each package and filters vulnerabilities unlikely to affect the running container.
Interactive HTML reports make results accessible to non-terminal users.
Best for: Teams that want guided remediation advice, not just a vulnerability list. Especially useful for JavaScript and Java projects.
6. npm audit
npm audit ships with every Node.js installation. Run npm audit in any project directory and it checks your dependency tree against the GitHub Advisory Database. No installation, no configuration, no account required.
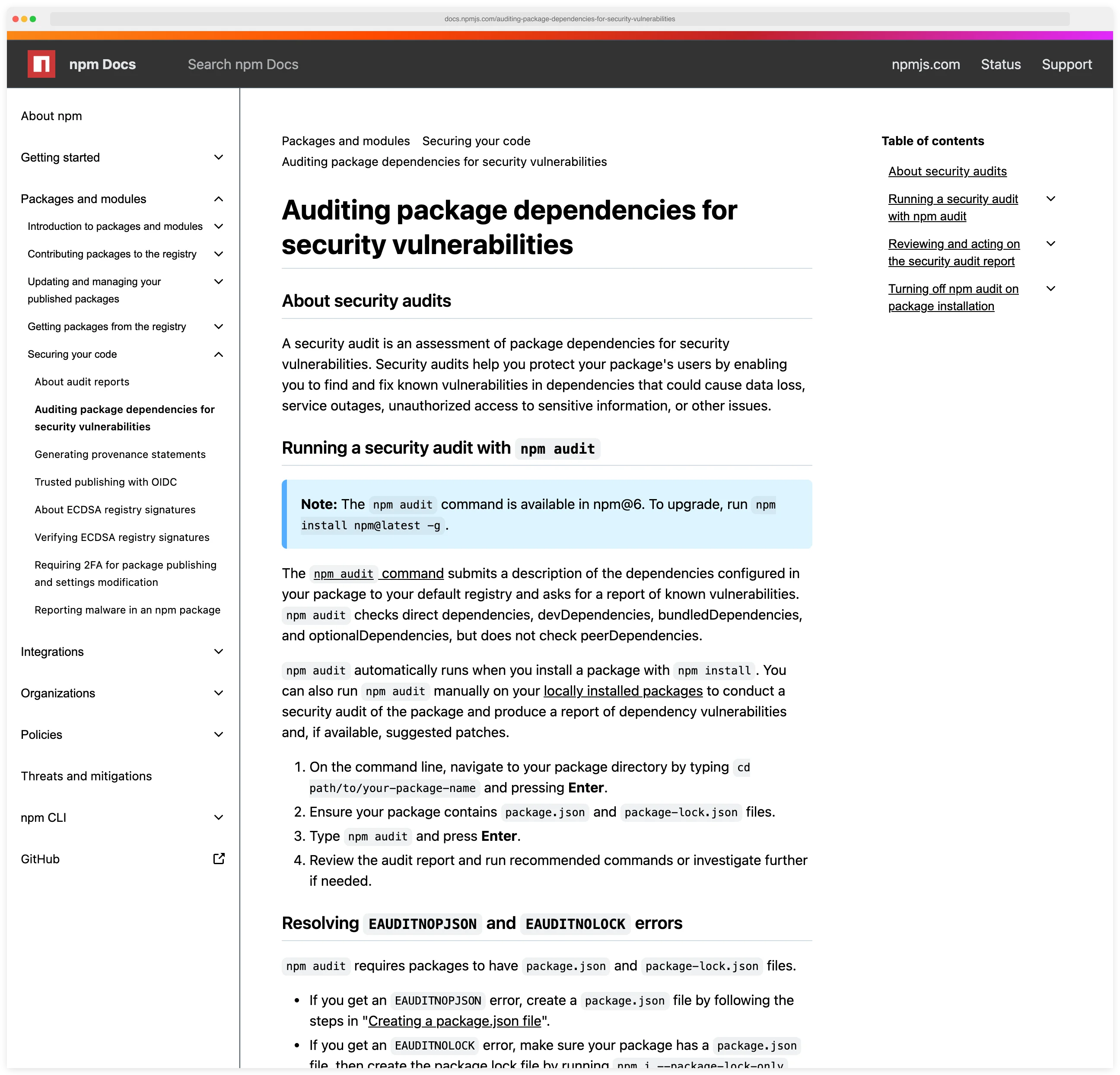
For JavaScript teams, npm audit is the zero-friction starting point. It catches known vulnerabilities in both direct and transitive dependencies and suggests upgrade paths.
The npm audit fix command applies safe upgrades automatically. The --production flag limits scanning to production dependencies, filtering out devDependencies.
The limitation is scope: npm audit only covers the npm ecosystem. It does not scan container images, generate SBOMs, or support non-JavaScript dependencies.
For polyglot projects, combine it with a broader tool like Trivy or Grype.
Best for: JavaScript/Node.js teams that want zero-setup dependency scanning as part of their existing npm workflow.
7. pip-audit
pip-audit is a Python dependency scanner maintained by the Python Packaging Authority (PyPA) and Trail of Bits. It checks installed packages against the OSV database and PyPI’s vulnerability feed.
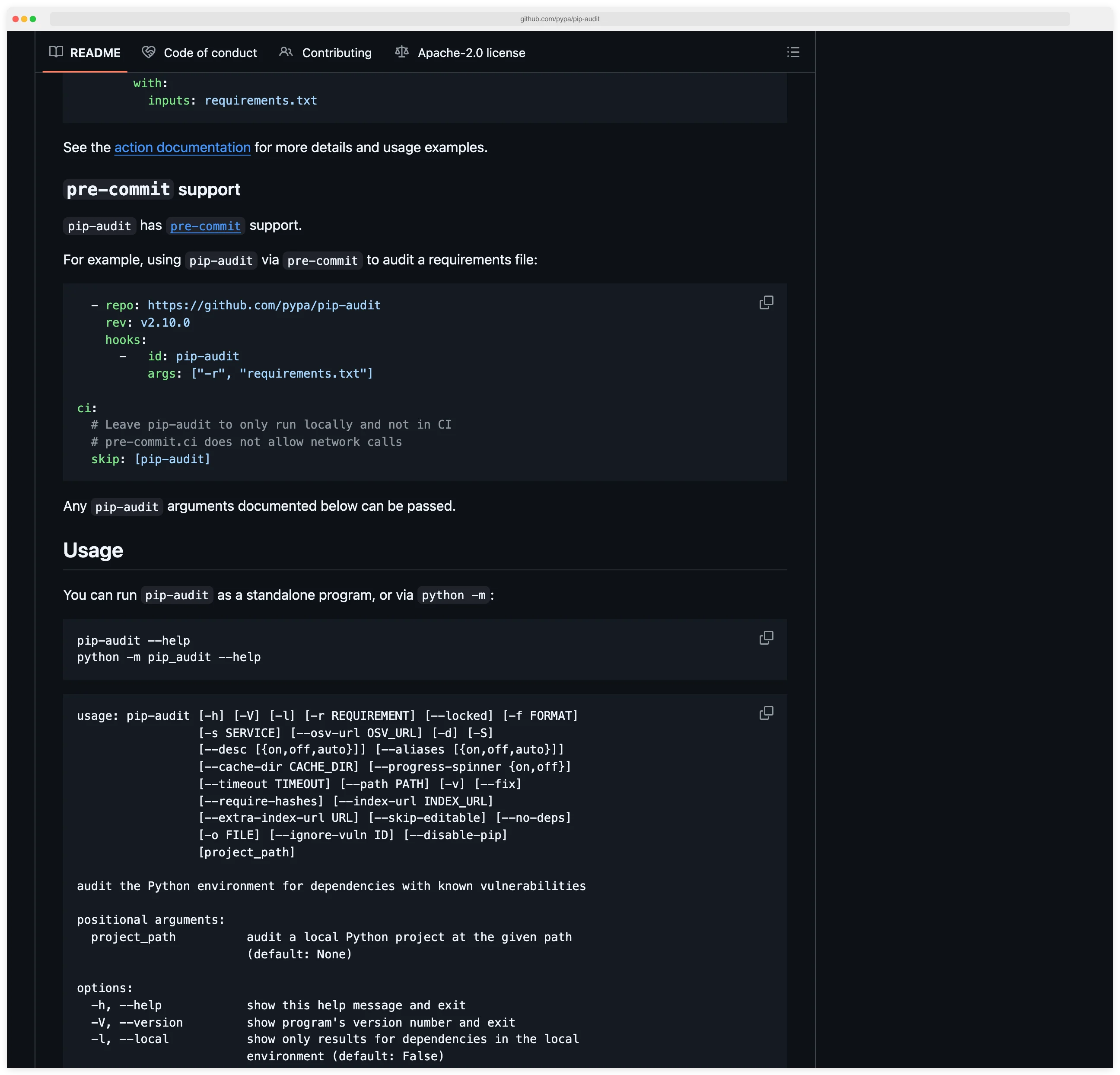
Install it with pip install pip-audit and run pip-audit in your project directory.
pip-audit resolves the full dependency tree using pip’s resolver, catching vulnerabilities in transitive dependencies that manual checks miss. It supports requirements.txt, pyproject.toml, and installed package environments. Output formats include JSON, CycloneDX, and Markdown.
Unlike OWASP Dependency-Check’s Python support (which uses NVD/CPE matching), pip-audit uses ecosystem-specific matching through the OSV database, resulting in fewer false positives for Python packages.
Best for: Python teams that want a lightweight, PyPA-maintained scanner with low false positive rates.
8. Retire.js
Retire.js scans JavaScript libraries for known vulnerabilities, focusing on both npm packages and JavaScript files loaded in web applications. It has a Burp Suite plugin, a command-line scanner, a Chrome extension, and a Grunt plugin.
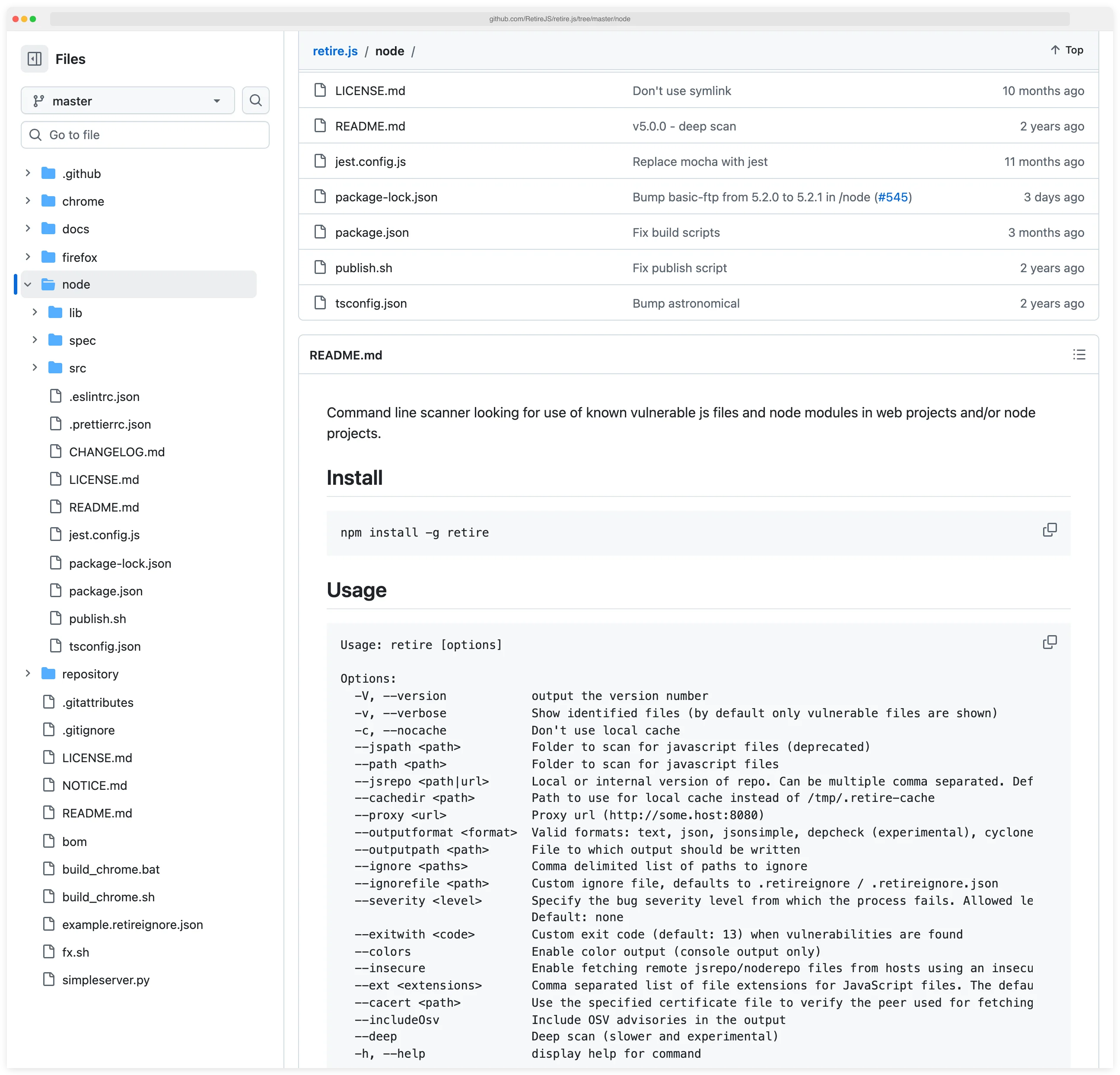
What sets Retire.js apart from npm audit is its ability to scan JavaScript files on disk or in web pages, not just packages in node_modules. It identifies vulnerable jQuery versions included via CDN, outdated Bootstrap copies, and other client-side libraries that npm audit never sees.
OWASP Dependency-Check bundles Retire.js data as one of its vulnerability sources, so if you already run Dependency-Check, you get some of this coverage. Standalone Retire.js is useful when you need to scan web applications for client-side library vulnerabilities specifically.
Best for: Web application teams with client-side JavaScript dependencies loaded via CDN or copied into the codebase rather than managed through npm.
9. Bundler-Audit
Bundler-Audit scans Ruby applications for vulnerable gem versions. Run bundle audit check against your Gemfile.lock and it reports any gems with known CVEs from the Ruby Advisory Database.
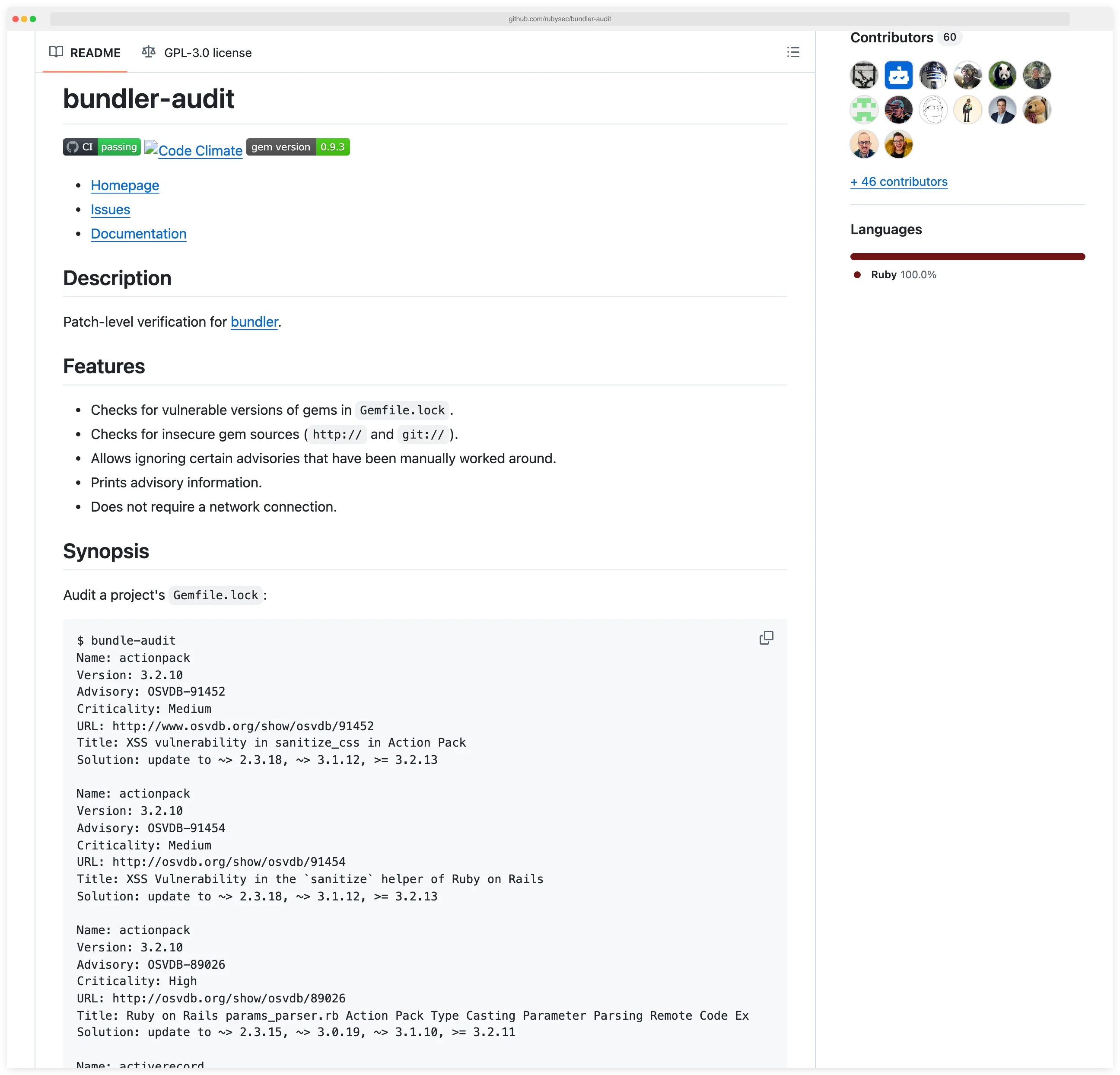
The tool is minimal and focused. It checks your locked gem versions against a curated advisory database, reports findings, and exits.
No configuration needed. Integrates into CI pipelines as a single command. Update the advisory database with bundle audit update.
For Rails teams already using Bundler, this is the path of least resistance for dependency vulnerability scanning. Pair it with Brakeman for Rails-specific SAST coverage.
Best for: Ruby on Rails teams using Bundler for dependency management.
10. Cargo-audit
Cargo-audit is the Rust equivalent of Bundler-Audit. It scans Cargo.lock files against the RustSec Advisory Database, reporting known vulnerabilities in Rust crate dependencies.
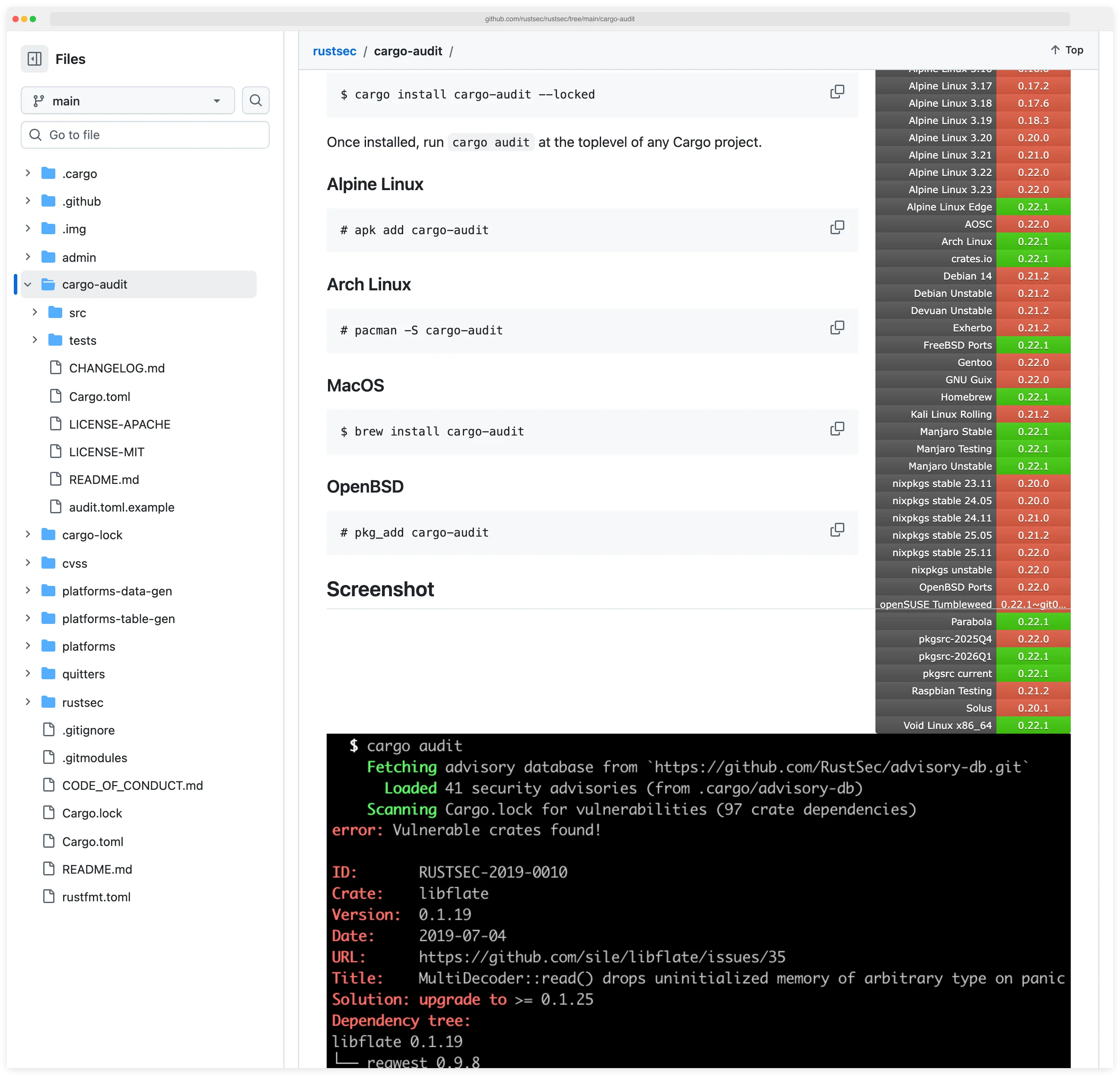
Run cargo audit in any Rust project directory. The tool checks both direct and transitive dependencies and reports CVEs, severity levels, and patched versions.
It also detects yanked crates and unmaintained dependencies, adding a supply chain hygiene layer beyond pure vulnerability matching.
The Rust ecosystem has embraced cargo-audit as a standard part of CI pipelines. Most Rust projects run it alongside cargo clippy and cargo test as part of their pre-merge checks.
Best for: Rust teams that want crate dependency scanning integrated into their Cargo workflow.
11. Safety
Safety is a Python dependency scanner that checks packages against the Safety DB (maintained by SafetyCLI, formerly PyUp). Run safety check -r requirements.txt to scan your Python dependencies.
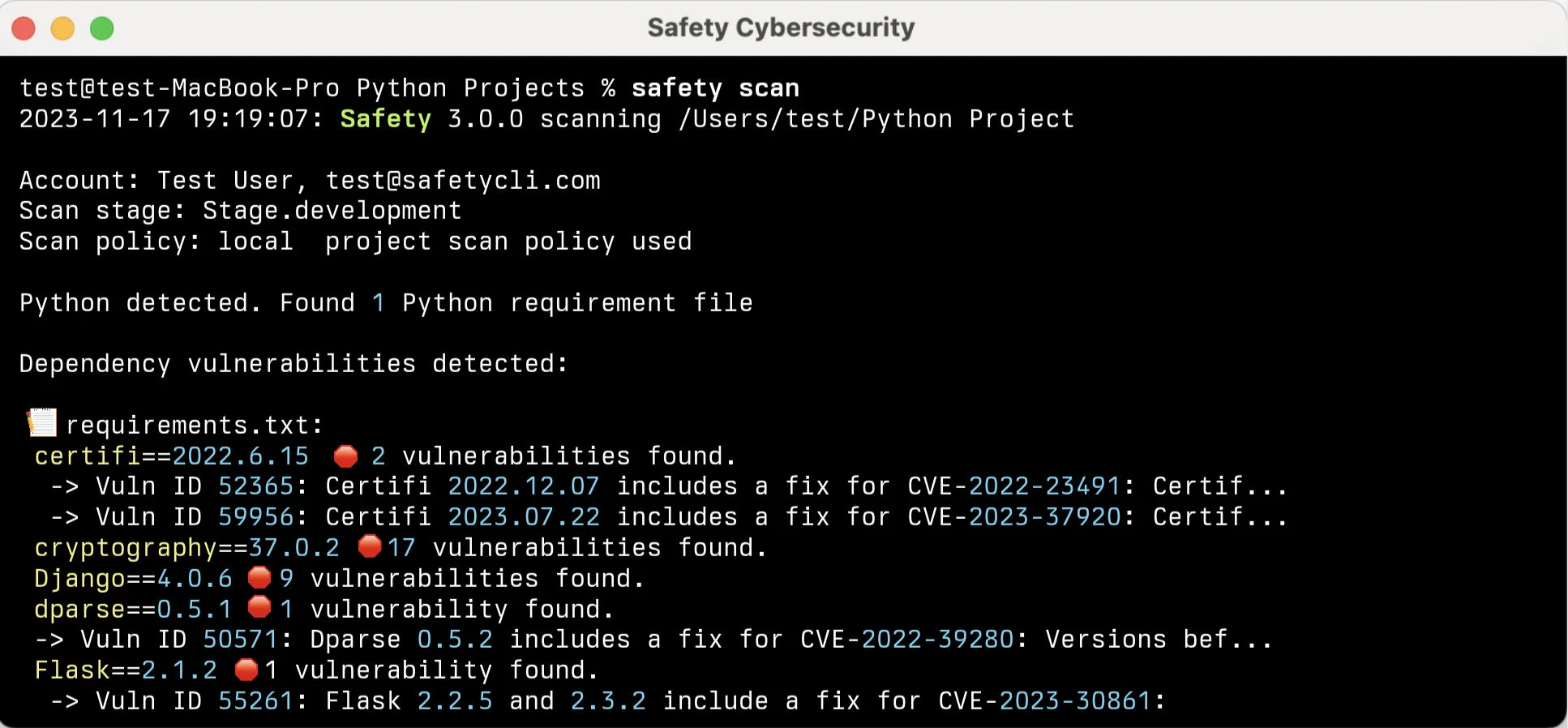
Safety’s database includes CVE data plus additional advisories that SafetyCLI curates. The free version provides basic vulnerability scanning, while the commercial version adds more frequent database updates, CI/CD integration features, and policy management.
For Python-only teams choosing between Safety and pip-audit, pip-audit has the advantage of being maintained by PyPA with OSV database access. Safety’s curated database can catch some advisories earlier, but the free tier has update frequency limitations.
Best for: Python teams already familiar with Safety’s workflow, or those wanting a second opinion alongside pip-audit.
12. Dependency-Track
Dependency-Track is not a scanner – it is a continuous monitoring platform. This OWASP Flagship Project (3,600 GitHub stars) ingests SBOMs in CycloneDX or SPDX format and continuously correlates every component against NVD, GitHub Advisories, Sonatype OSS Index, and OSV.
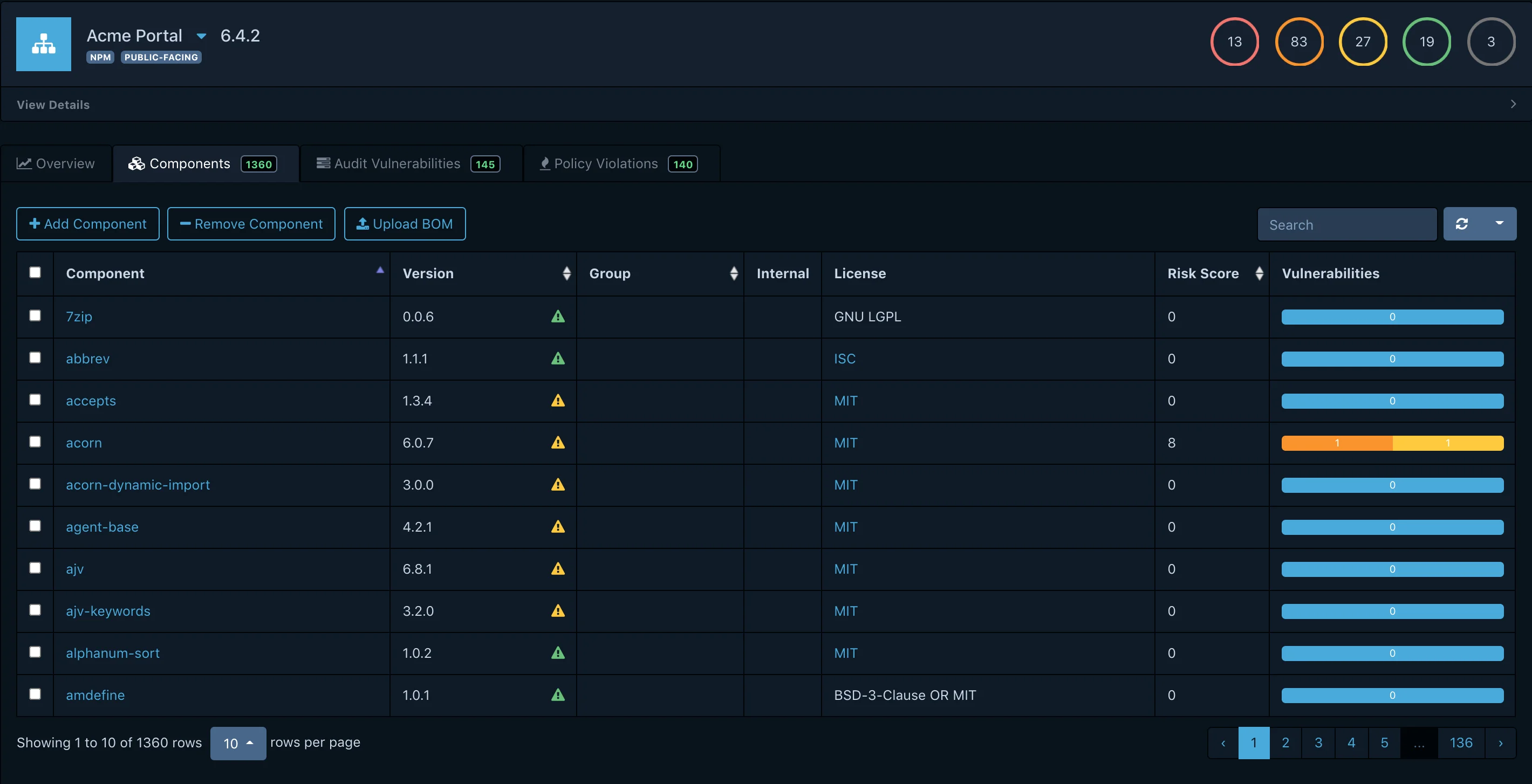
The difference from every other tool on this list: Dependency-Track does not run at build time and produce a one-time report.
It maintains a persistent inventory of components across your entire application portfolio. When a new CVE is published, it immediately flags every affected project without requiring a rescan.
Deploy it with Docker Compose, upload SBOMs from your CI pipelines (generated by Syft, Trivy, or any CycloneDX/SPDX producer), and you get portfolio-wide risk dashboards, policy enforcement, and alerting. The API-first architecture integrates with Slack, Teams, Jira, and custom webhooks.
Key Insight
Every other tool on this list answers "what is vulnerable right now?". Dependency-Track answers "what became vulnerable overnight across every repo I own?" — and that is the question that actually keeps portfolios safe once you move past a handful of projects.
Best for: Organizations managing 10+ applications that need continuous component monitoring beyond point-in-time CI scans.
Transitive dependency resolution across the top 12
Every tool on this list resolves the full transitive dependency tree — direct imports plus the packages your direct imports pull in. The practical differences are in the manifest parsers: Trivy, Grype, and OSV-Scanner cover polyglot projects across 11-20+ ecosystems in one binary; Bundler-Audit, Cargo-audit, npm audit, pip-audit, and Safety each run tight, ecosystem-native dependency-tree analysis for their single language; OWASP Dependency-Check does CPE-based transitive matching on Maven, Gradle, npm, Python, Ruby, Go, and NuGet.
Syft does not scan for vulnerabilities but catalogs the same transitive tree into a CycloneDX or SPDX SBOM. Dependency-Track consumes those SBOMs and performs transitive dependency analysis continuously against updated advisory feeds. The result is coverage of the full dependency graph, not just the top-level packages listed in a package.json or pom.xml.
Feature comparison
| Tool | Languages | SBOM output | Container scanning | Vuln database | License scanning |
|---|---|---|---|---|---|
| Trivy | 11+ ecosystems | CycloneDX, SPDX | Yes | NVD, GHSA, distro feeds | Yes |
| Grype | 20+ ecosystems | CycloneDX (output) | Yes | NVD, GHSA, distro feeds | No |
| Dependency-Check | Java, JS, Python, Ruby, Go, .NET | No | No | NVD, OSS Index, RetireJS | No |
| Syft | Dozens of ecosystems | CycloneDX, SPDX | Yes (inventory) | N/A (SBOM only) | Via SBOM |
| OSV-Scanner | 11+ ecosystems | No | Yes (Alpine/Debian/Ubuntu) | OSV.dev (30+ sources) | No |
| npm audit | JavaScript | No | No | GitHub Advisory DB | No |
| pip-audit | Python | CycloneDX | No | OSV, PyPI | No |
| Retire.js | JavaScript | No | No | RetireJS DB | No |
| Bundler-Audit | Ruby | No | No | Ruby Advisory DB | No |
| Cargo-audit | Rust | No | No | RustSec Advisory DB | No |
| Safety | Python | No | No | Safety DB | No |
| Dependency-Track | Any (via SBOM) | Ingests CycloneDX/SPDX | No | NVD, GHSA, OSS Index, OSV | Yes |
Extended comparison: reachability, malicious detection, SBOM-as-input
The table above covers the baseline capabilities. Three dimensions that often drive the actual decision are not in it: reachability analysis (does the tool check whether the vulnerable function is callable from your code?), malicious-package detection (does the tool surface typosquats and compromised releases?), and SBOM-as-input support (can you pre-generate an SBOM and scan that inventory later?).
| Tool | Reachability analysis | Malicious-package detection | SBOM-as-input |
|---|---|---|---|
| Trivy | No | Via OSV/GHSA feeds only | No |
| Grype | No | Via NVD/GHSA feeds only | Yes (CycloneDX, SPDX, Syft JSON) |
| OSV-Scanner | Guided remediation (npm, Maven) | Yes, via OpenSSF Malicious Packages feed in OSV.dev | No |
| OWASP Dependency-Check | No | No | No |
| Syft | N/A (SBOM generator) | N/A | N/A (produces input, not consumer) |
| Dependency-Track | No (policy-based, not reachability) | Via OSS Index + OSV feeds | Yes (CycloneDX, SPDX) |
Reachability remains an open-source gap — commercial tools like Endor Labs, Snyk Open Source, and Contrast SCA cover it. OSV-Scanner’s guided remediation is the closest OSS approximation today.
Vulnerability database comparison
The accuracy of an open source SCA tool comes down to the vulnerability database it queries. Every tool on this list pulls from one or more of four primary sources: the National Vulnerability Database (NVD), the GitHub Advisory Database (GHSA), Google’s Open Source Vulnerabilities (OSV.dev) aggregator, and ecosystem-specific advisory feeds.
NVD is the US government vulnerability catalog and the original source for most CVE data. OWASP Dependency-Check relies on NVD through CPE (Common Platform Enumeration) matching, which catches vulnerabilities other databases miss but produces more false positives than ecosystem-specific matching.
GitHub Advisory Database curates vulnerabilities for the ecosystems GitHub hosts: npm, PyPI, Maven, RubyGems, NuGet, Go, Composer, Rust, and more. It typically publishes advisories before they hit NVD. npm audit reads directly from GHSA, and Trivy and Grype pull it as one of their sources.
OSV.dev is Google’s aggregated vulnerability database, pulling from 30+ ecosystem-specific sources including GHSA, Rust’s RustSec, Python’s PyPA advisory database, Go’s vulndb, and Linux distribution feeds. OSV-Scanner and pip-audit use OSV as their primary source, which tends to produce fewer false positives than CPE-based matching.
Distribution feeds. Alpine, Debian, Ubuntu, RHEL, and Amazon Linux each publish their own security advisories that account for backported patches. Trivy and Grype both ingest these, which is why they report more accurate results on container images than tools that only query NVD.
For practical purposes: if you scan containers, pick a tool with distro feed coverage (Trivy, Grype, OSV-Scanner). If you scan application dependencies only, any tool backed by GHSA or OSV will give you a strong starting point. Tools that layer multiple sources on top of each other, like Trivy (NVD + GHSA + distro) or Dependency-Track (NVD + GHSA + OSS Index + OSV), have the broadest coverage.
Malicious package detection in open-source SCA
Traditional SCA tools match components against known CVEs. Malicious packages — typosquats, compromised-maintainer releases, install-time backdoors — usually have no CVE yet. That gap is where the open-source SCA stack has historically been weakest.
The tools that close the gap split into two camps. Behavioural scanners look at what a package actually does: Socket and Checkmarx SCA (on the commercial side) analyse install scripts, network calls, and filesystem access. On the open-source side, the OpenSSF Package Analysis project runs dynamic analysis on npm and PyPI and publishes findings into the OpenSSF Malicious Packages repository, which is consumable via the OSV schema.
Feed consumers pull those findings into everyday scanners. OSV-Scanner ingests the OpenSSF Malicious Packages feed through OSV.dev, which means its scans pick up known-bad packages alongside conventional CVEs. Trivy and Grype focus on CVE matching and do not block typosquats on their own — pair them with OSV-Scanner or a registry-level guard for that layer.
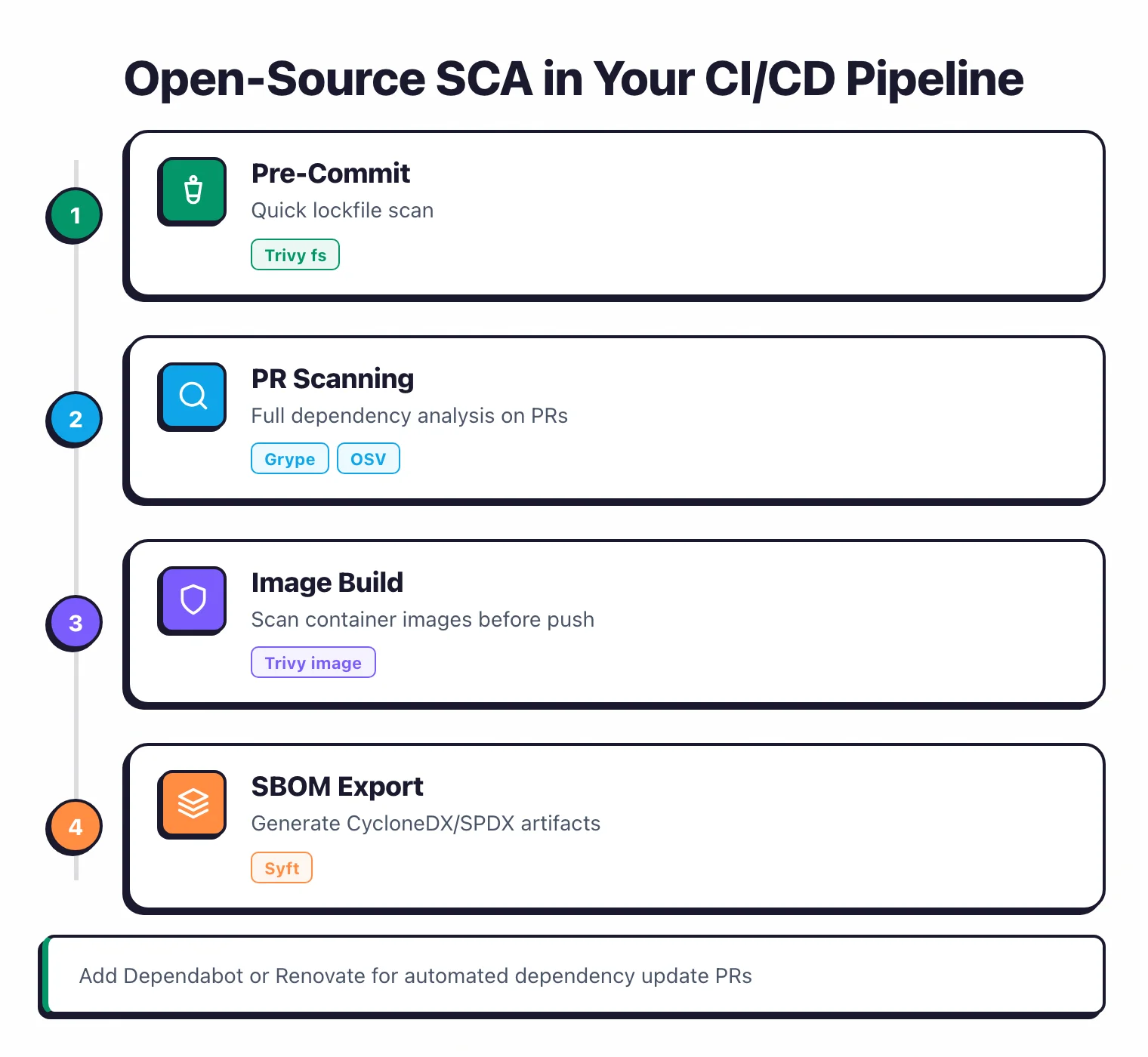
Dependency-update automation is the other half of this story. Dependabot and Renovate open pull requests that bump vulnerable dependencies to patched versions, which shortens the exposure window even for traditional CVEs. Neither is a scanner by itself, but both are part of any realistic open-source SCA pipeline that aims to close findings rather than just count them.
License compliance with open source SCA tools
License compliance is where open source SCA tools diverge sharply from commercial ones. Free scanners can flag and report licenses, but none of them ship with the policy engine, attribution report generator, or legal workflow tools that FOSSA and Black Duck provide.
Trivy scans dependency manifests and surfaces license metadata for each component, and it can fail builds when it detects copyleft licenses in a codebase that should stay proprietary. The output lists license strings alongside CVEs, but there is no built-in policy engine. You filter licenses with CLI flags or post-process the JSON yourself.
Syft goes broader on license metadata extraction. Because it catalogs every package across dozens of ecosystems, the SBOMs it produces (CycloneDX and SPDX) include the full license string for each component. This makes Syft a practical foundation for a home-grown license audit: generate the SBOM, pipe it into a policy script, and flag anything that violates your internal license list.
Dependency-Track takes this further by continuously monitoring SBOMs against a configurable license policy. It is the closest open source equivalent to a commercial license compliance dashboard. You define allowed and forbidden licenses per project, and new SBOM uploads get checked against those rules automatically.
The gap that remains is legal-grade attribution. If your product ships commercially and you need a formal third-party notice file or audit-ready compliance report, open source tools give you the raw data but not the finished deliverable. Commercial vendors like FOSSA advertise 99.8% license detection accuracy with full-text analysis that catches modified licenses, while Black Duck builds attribution reports designed to satisfy enterprise legal teams.
For most teams that just need to avoid GPL code in a proprietary product, a Syft + Dependency-Track pipeline covers the bases at zero cost.
How to choose the right tool
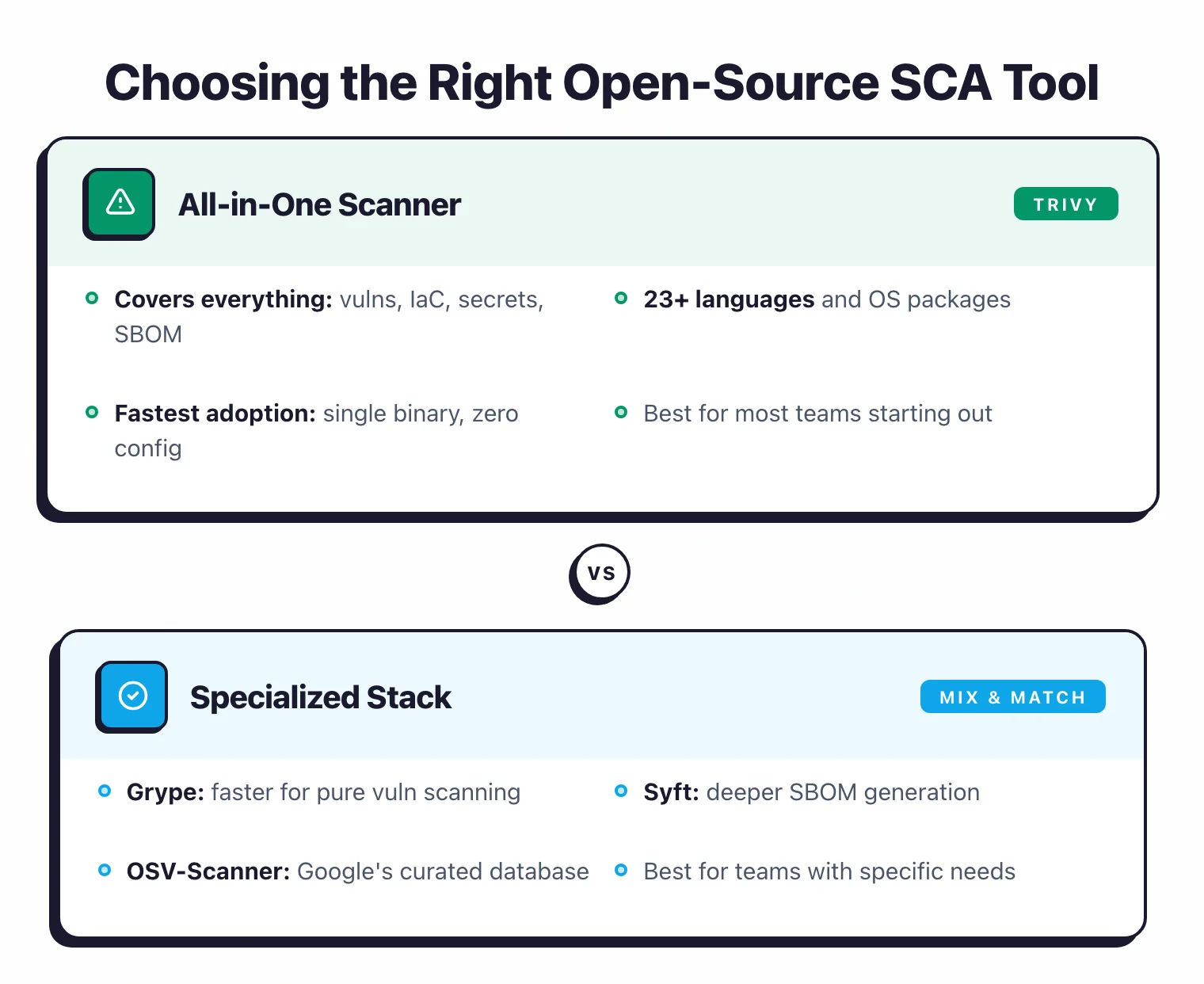
The decision depends on three factors: your language stack, whether you scan containers, and how many applications you manage.
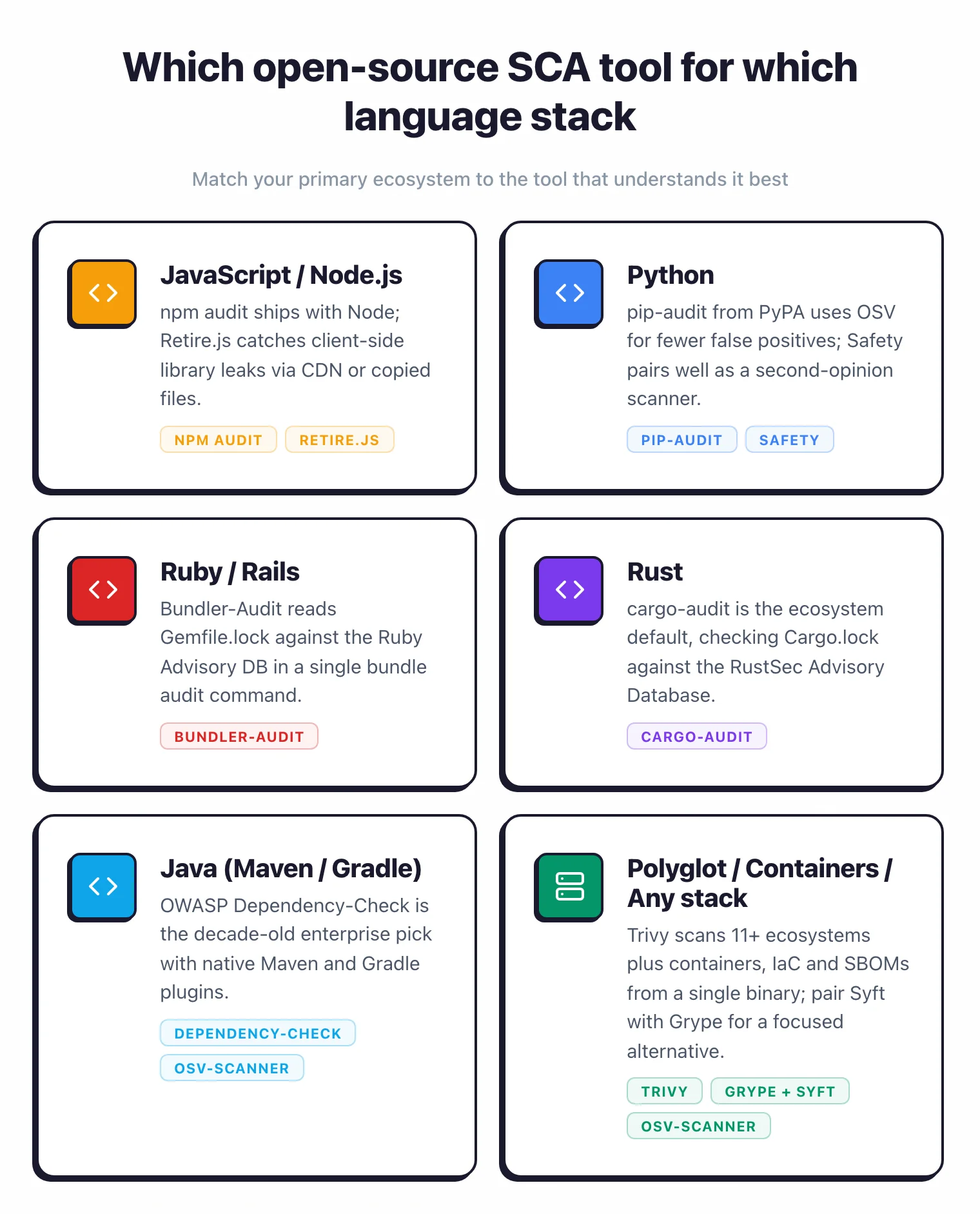
Single-language teams
If you write exclusively in one language, start with the ecosystem-specific tool. Ruby teams use Bundler-Audit.
Rust teams use Cargo-audit. Python teams use pip-audit.
JavaScript teams use npm audit. These tools are thin, fast, and produce fewer false positives than general-purpose scanners because they understand ecosystem-specific package naming and versioning.
Polyglot or container-heavy teams
If your stack spans multiple languages or you ship container images, Trivy is the default starting point. One binary scans your dependency manifests, container images, and IaC configs.
You get vulnerability detection, SBOM generation, and misconfiguration scanning without installing three separate tools.
For teams that want more focused vulnerability matching with better risk scoring, Grype paired with Syft is the alternative. Syft handles SBOM generation, Grype handles vulnerability scanning with EPSS and KEV-based prioritization.
This two-tool approach gives you more control over each step.
Enterprise Java shops
If you run Maven or Gradle builds in Jenkins, OWASP Dependency-Check is the path of least resistance.
Its native build tool plugins, OWASP branding, and decade-long track record make it an easy sell to management and audit teams. Pair it with Dependency-Track for continuous monitoring.
Multiple applications at scale
Once you manage more than a handful of applications, point-in-time scanning is not enough. A new CVE disclosed on Tuesday affects code you deployed last month.
Dependency-Track adds the continuous monitoring layer: upload SBOMs from every CI build, and the platform alerts you to new vulnerabilities across your entire portfolio.
CI/CD integration patterns
GitHub Actions
Most open-source SCA tools have official or community-maintained GitHub Actions. Here is a minimal Trivy example:
- name: Scan dependencies
uses: aquasecurity/trivy-action@master
with:
scan-type: "fs"
scan-ref: "."
severity: "HIGH,CRITICAL"
exit-code: "1"
For Grype, use the official Anchore scan action:
- name: Scan with Grype
uses: anchore/scan-action@v7
with:
path: "."
fail-build: true
severity-cutoff: high
GitLab CI
Add a security stage to your .gitlab-ci.yml:
sca-scan:
image: aquasec/trivy:latest
stage: security
script:
- trivy fs --exit-code 1 --severity HIGH,CRITICAL .
allow_failure: false
Pre-commit hooks
Catch vulnerable dependencies before they reach CI. Add a pre-commit hook that runs your SCA tool against lock files:
#!/bin/sh
# .git/hooks/pre-commit
trivy fs --severity CRITICAL --exit-code 1 --quiet .
For JavaScript projects, npm audit can run as part of a Husky pre-commit hook with zero additional tooling.
Pro tip: For a polyglot monorepo, chain Syft and Grype in one pull-request workflow — syft . -o cyclonedx-json > sbom.json && grype sbom:sbom.json --fail-on high. You cache the SBOM between runs and only re-match against the database, which cuts CI time on large repos dramatically.
Limitations vs commercial alternatives
Open-source SCA tools are strong on vulnerability detection. They fall short in areas that require significant engineering investment beyond database matching.
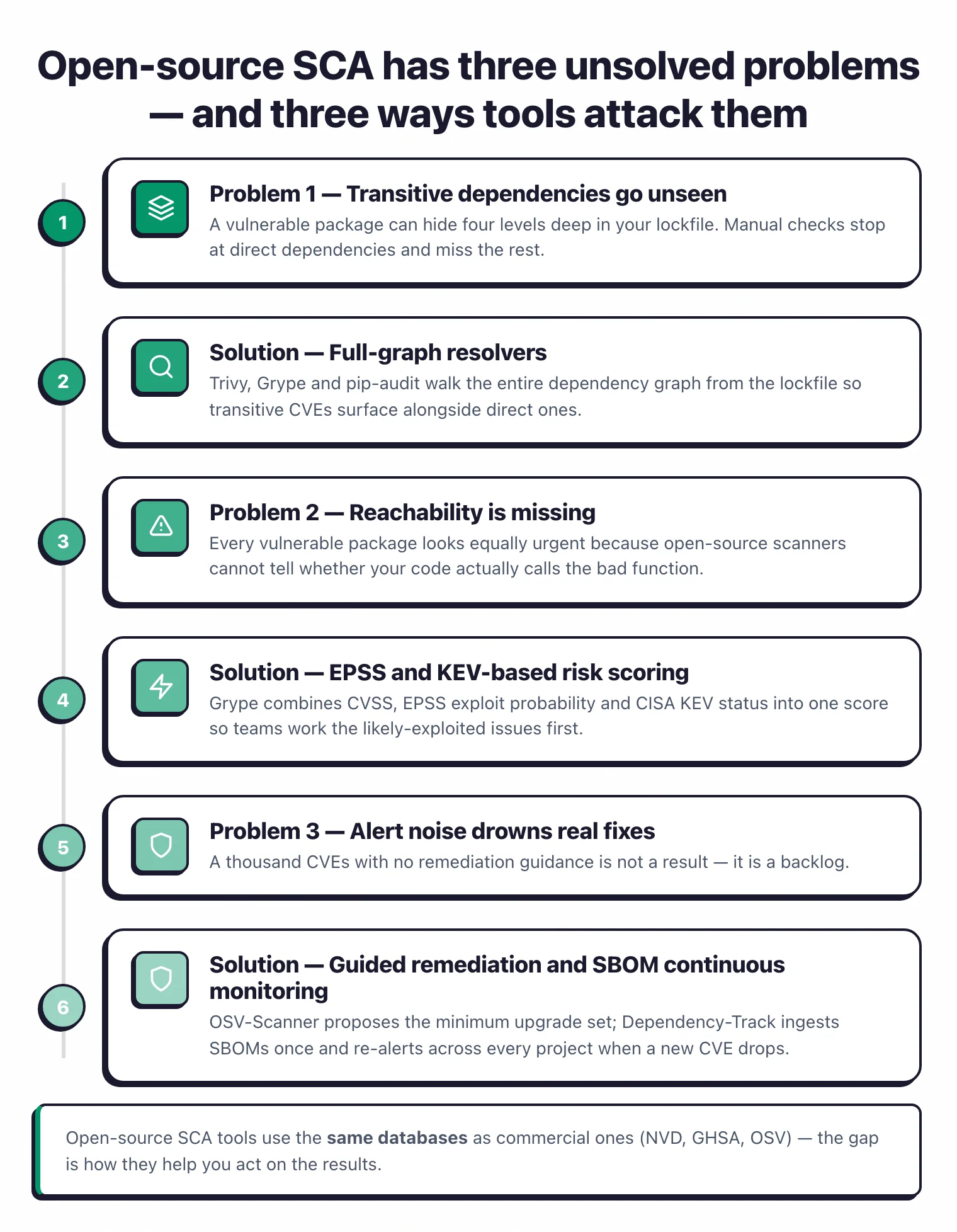
No reachability analysis. Commercial tools like Endor Labs and Snyk analyze whether your code actually calls the vulnerable function in a dependency. This cuts alert volume by 70-90%.
Open-source tools flag every vulnerable component regardless of whether the vulnerability is reachable from your code paths.
Limited fix suggestions. Dependabot and Renovate open automated pull requests that bump vulnerable dependencies. Most open-source SCA scanners report the vulnerability and stop.
You figure out the upgrade path yourself. OSV-Scanner’s guided remediation is a step forward, but it currently covers only npm and Maven.
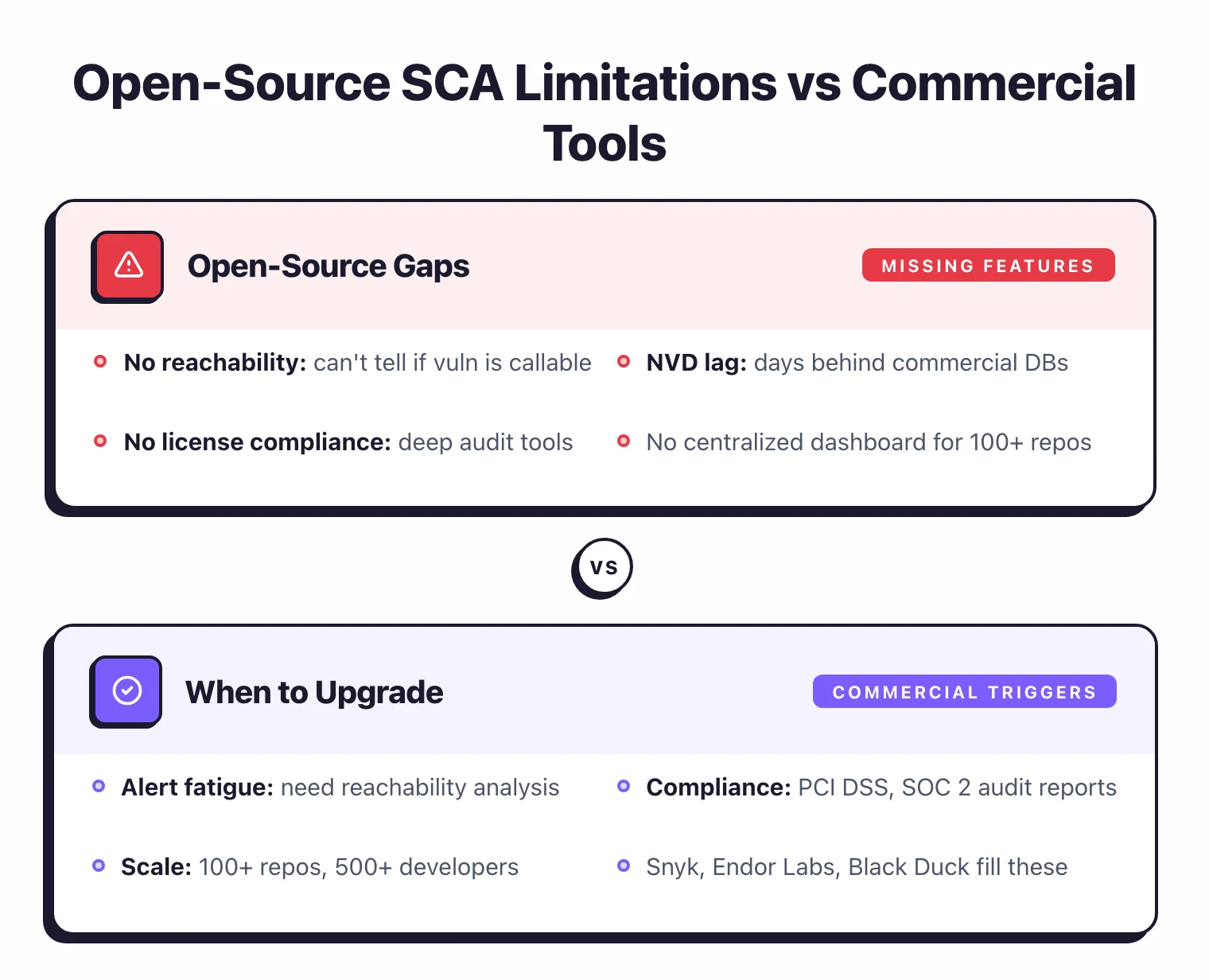
Manual license compliance. Trivy flags licenses, Syft includes them in SBOMs, but neither provides the policy engine that Mend or Black Duck offer for automated license compliance management.
If your legal team needs a full license audit with policy enforcement, open-source tools create the raw data but not the workflow.
No unified dashboard. Each open-source tool produces its own report format. Dependency-Track adds a centralized view, but it requires infrastructure to host and maintain.
Commercial platforms like Snyk and Endor Labs provide a single pane of glass out of the box.
No dedicated support. When a tool produces an unexpected result, your options are GitHub Issues, community Slack channels, and reading source code.
Commercial vendors provide support engineers, SLA-backed response times, and custom rule development.
For teams that hit these limitations, the SCA tools category covers commercial options in detail. Our Snyk vs Dependabot and Trivy vs Grype comparisons provide head-to-head analysis of specific tools.
If your blockers are alerts volume or compliance depth, the commercial stack is the natural next step: Snyk, Black Duck, Checkmarx SCA, and Endor Labs each solve a different gap (fix workflow, licence depth, compliance, reachability). The Trivy alternatives and Snyk vs Dependabot comparisons are the shortest path to a decision.
Free commercial SCA tiers
Open-source and free-tier are not the same thing, but Google treats them as one query. If you searched for a free SCA tool, these commercial products publish free plans that often satisfy small-team needs before you touch self-hosted OSS.
Snyk Free. Unlimited scans on public repositories with no developer-seat cap; private repositories get 200 Open Source tests per month on the Free plan, then the Team plan starts at $25 per contributing developer per month (snyk.io/plans). The free plan is the closest thing to “open-source equivalent” on the commercial side.
Dependabot. Free for every GitHub repository, public or private, with zero configuration. It reads the GitHub Advisory Database and can open automated fix pull requests. For GitHub-hosted projects, this is the lowest-friction SCA option that exists.
Mend Bolt. Free GitHub app with unlimited repositories per user, capped at 5 scans per repo per day. Covers public and private repos, 200+ languages, and opens an issue for every vulnerable dependency (mend.io/free-developer-tools/bolt).
Semgrep Supply Chain (Free). Included in the AppSec Platform Free plan for up to 10 contributors and 10 private repositories, alongside Semgrep Code and Semgrep Secrets. Reachability-aware scanning is included at this tier.
The free commercial tiers carry one shared trade-off: rate limits and contributor caps that tighten as your team grows. Self-hosted OSS tools like Trivy or Grype remove those ceilings entirely.
Key terms
SCA (Software Composition Analysis): The practice of scanning an application’s third-party and open-source dependencies for known vulnerabilities, license risks, and outdated components. SCA tools read dependency manifests (package.json, requirements.txt, pom.xml, go.sum), resolve the full tree including transitive dependencies, and match each component against vulnerability databases.
SBOM (Software Bill of Materials): A machine-readable inventory of every software component in an application, including direct and transitive dependencies. The two common formats are CycloneDX (OWASP) and SPDX (Linux Foundation). US Executive Order 14028 and the EU Cyber Resilience Act require SBOMs for software supplied to regulated sectors.
CVE (Common Vulnerabilities and Exposures): A unique identifier for a publicly disclosed security flaw in a software product, assigned by MITRE and its CNAs. Each CVE has a standard format like CVE-2024-12345 and is tracked in the National Vulnerability Database (NVD) alongside CVSS severity scores.
GHSA (GitHub Advisory Database): GitHub’s curated vulnerability database covering npm, PyPI, Maven, RubyGems, NuGet, Go, Composer, and Rust. GHSA advisories often publish before the same CVE hits NVD, which is why scanners like Trivy, Grype, and npm audit read from it directly.
OSV (Open Source Vulnerabilities): Google’s distributed vulnerability database at osv.dev, which aggregates 30+ ecosystem-specific sources including GHSA, RustSec, PyPA, Go vulndb, and Linux distro feeds. OSV uses a structured schema that makes package-version matching more precise than CPE-based NVD matching.
VEX (Vulnerability Exploitability eXchange): A machine-readable statement that says whether a given CVE actually affects a given product, independent of whether the vulnerable component is present. VEX documents let security teams tell their own scanners “this CVE is not exploitable in our build” so alerts stop firing. OpenVEX, supported by Grype and other tools, is the open-source implementation.
Transitive dependency: A package your application does not directly depend on, but that is pulled in by one of your direct dependencies. Most known vulnerabilities in real applications live in transitive dependencies, which is why every tool on this list resolves the full dependency tree rather than stopping at the top level.
Dependency pinning: Locking each dependency to an exact version (rather than a range like ^1.2.0) so that builds are reproducible and new vulnerable releases do not enter the graph silently. Lockfiles like package-lock.json, Pipfile.lock, Gemfile.lock, and go.sum are the standard mechanism; SCA tools scan these files rather than the manifest.
Visit these projects
- OSV-Scanner · on GitHub — Google-backed
- Trivy · maintained by Aqua Security
- Grype · Syft — both maintained by Anchore
- OWASP Dependency-Check · Dependency-Track
- npm audit · pip-audit · bundler-audit · cargo-audit
- Retire.js · Safety
Looking for managed SCA platforms beyond OSS? Snyk Open Source, Endor Labs, Mend SCA, and Sonatype Lifecycle are the most-used commercial options.

