StackRox is an open-source Kubernetes-native security platform that protects containerized applications across build, deploy, and runtime phases. Originally founded as a startup in 2014, StackRox was acquired by Red Hat in February 2021 and open-sourced under the Apache 2.0 license.
The commercially supported downstream product is Red Hat Advanced Cluster Security for Kubernetes (RHACS). 1.3k GitHub stars, latest RHACS version 4.10.0 (March 2026).
Unlike image-only scanners or runtime-only monitors, StackRox covers the full container lifecycle in a single tool — scanning images before deployment, enforcing 300+ policies at the admission controller, and detecting threats while containers run in production.

Overview
StackRox deploys as a Kubernetes-native application within the clusters it protects.
There are no external appliances or agents running outside the Kubernetes control plane — everything runs as containers managed by Kubernetes itself.
The architecture consists of four main components:
| Component | Role |
|---|---|
| Central | API server, UI, data storage, and image scanning engine. One Central manages multiple clusters. |
| Scanner V4 | Vulnerability scanner built on ClairCore. Analyzes image layers for OS and language-level vulnerabilities. |
| Sensor | One per secured cluster. Collects Kubernetes events, deployment metadata, and policy evaluation data. |
| Collector | One per node. Monitors runtime activity — process execution, network connections, and file system changes. |
This distributed architecture lets StackRox secure clusters at scale without creating a single point of failure.
Central can run in one cluster while Sensors and Collectors protect workloads across dozens of remote clusters.
| Feature | Details |
|---|---|
| Architecture | Kubernetes-native (Central, Scanner V4, Sensor, Collector) |
| Scanner engine | Scanner V4 built on ClairCore |
| Built-in policies | 300+ mapped to CIS, NIST, PCI DSS, HIPAA, SOC 2 |
| Lifecycle coverage | Build (CI/CD scanning), Deploy (admission control), Runtime (threat detection) |
| Supported distros | EKS, GKE, AKS, OpenShift, RKE, self-managed K8s |
| Image OS support | RHEL, Alpine, Debian, Ubuntu, Amazon Linux 2023, SLES, Oracle Linux |
| Deployment options | Self-managed, Cloud Service (SaaS), OpenShift bundled |
| CLI tool | roxctl for automation and CI/CD integration |
| GitHub | 1.3k stars, Apache 2.0 |
| Latest version | RHACS 4.10.0 (March 2026) |
Key Features
Admission Control
StackRox includes a Kubernetes admission controller that intercepts deployment requests before they reach the cluster.
When a developer applies a deployment manifest, the admission controller evaluates it against configured policies — checking for things like images from untrusted registries, containers running as root, deployments without resource limits, or images with critical CVEs.
Violations can trigger hard enforcement (block the deployment), soft enforcement (allow but alert), or informational logging. This prevents security issues from reaching production without requiring developers to run separate pre-deployment checks.
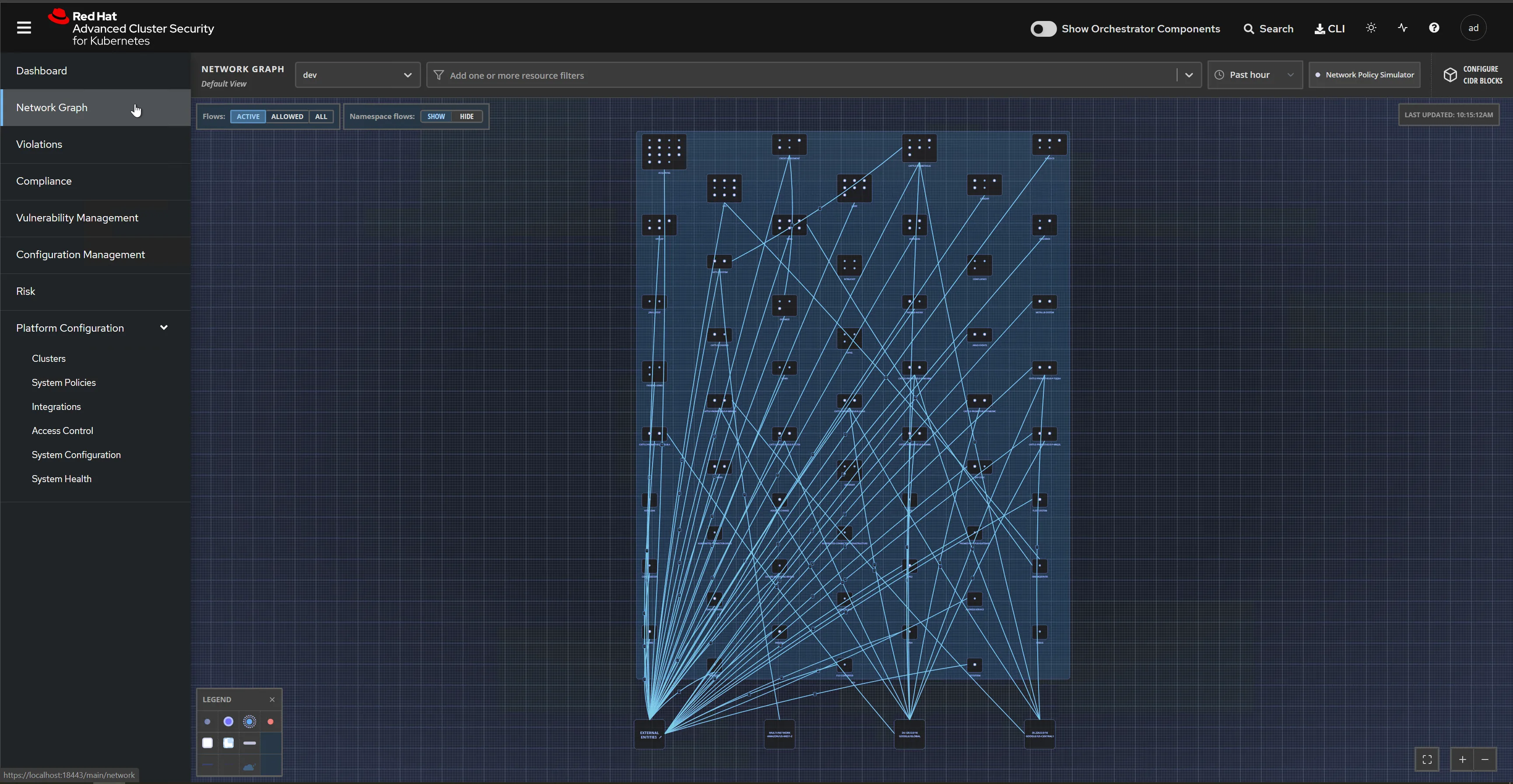
Network Segmentation Visibility
StackRox automatically maps network communication between all deployments in a cluster, creating a visual network graph that shows which pods are talking to each other.
This baseline helps security teams identify unexpected connections — a frontend pod connecting directly to a database, or an internal service making outbound internet calls.
The platform generates Kubernetes NetworkPolicy recommendations based on observed traffic patterns, making it easier to implement least-privilege network segmentation without manually defining rules for every service pair.
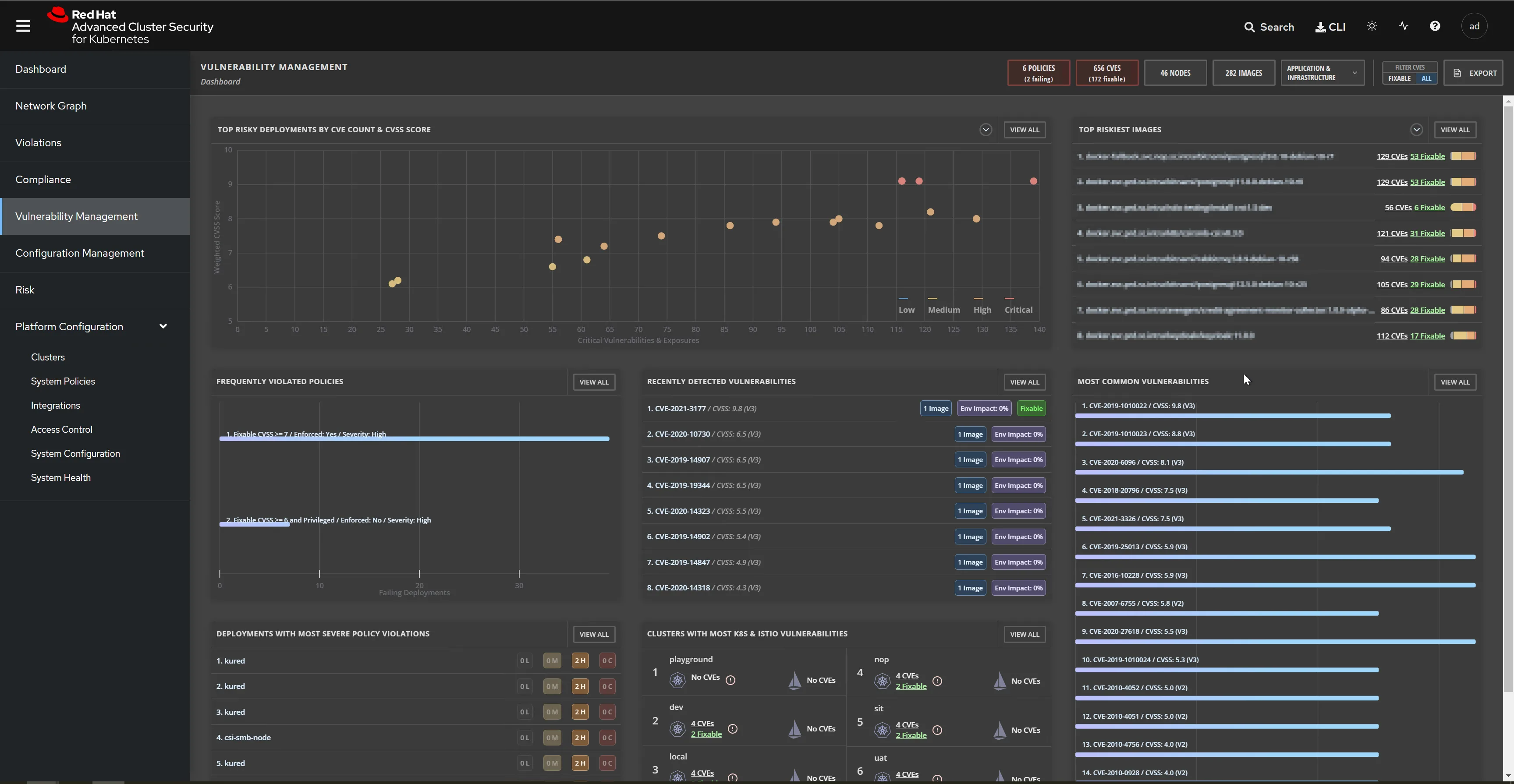
Risk-Based Prioritization
Not every vulnerability or policy violation deserves the same urgency.
StackRox calculates a risk score for each deployment by weighing vulnerability severity, exploitability, container configuration (privileged, host network, writable volumes), network exposure, and the deployment’s role in the cluster.
This risk-based prioritization helps security teams focus on the deployments that actually matter instead of drowning in a flat list of thousands of CVEs.
Use Cases
DevSecOps pipeline integration — StackRox integrates with CI/CD tools (Jenkins, GitLab CI, GitHub Actions, Tekton) to scan images and check policies during the build phase.
Failed policies break the pipeline before vulnerable images reach a registry. The roxctl CLI makes scripting straightforward.
Multi-cluster security management — A single Central instance manages security policies, vulnerability data, and compliance reports across dozens of Kubernetes clusters on different cloud providers and on-premises environments.
One policy set applies everywhere without duplicating configuration.
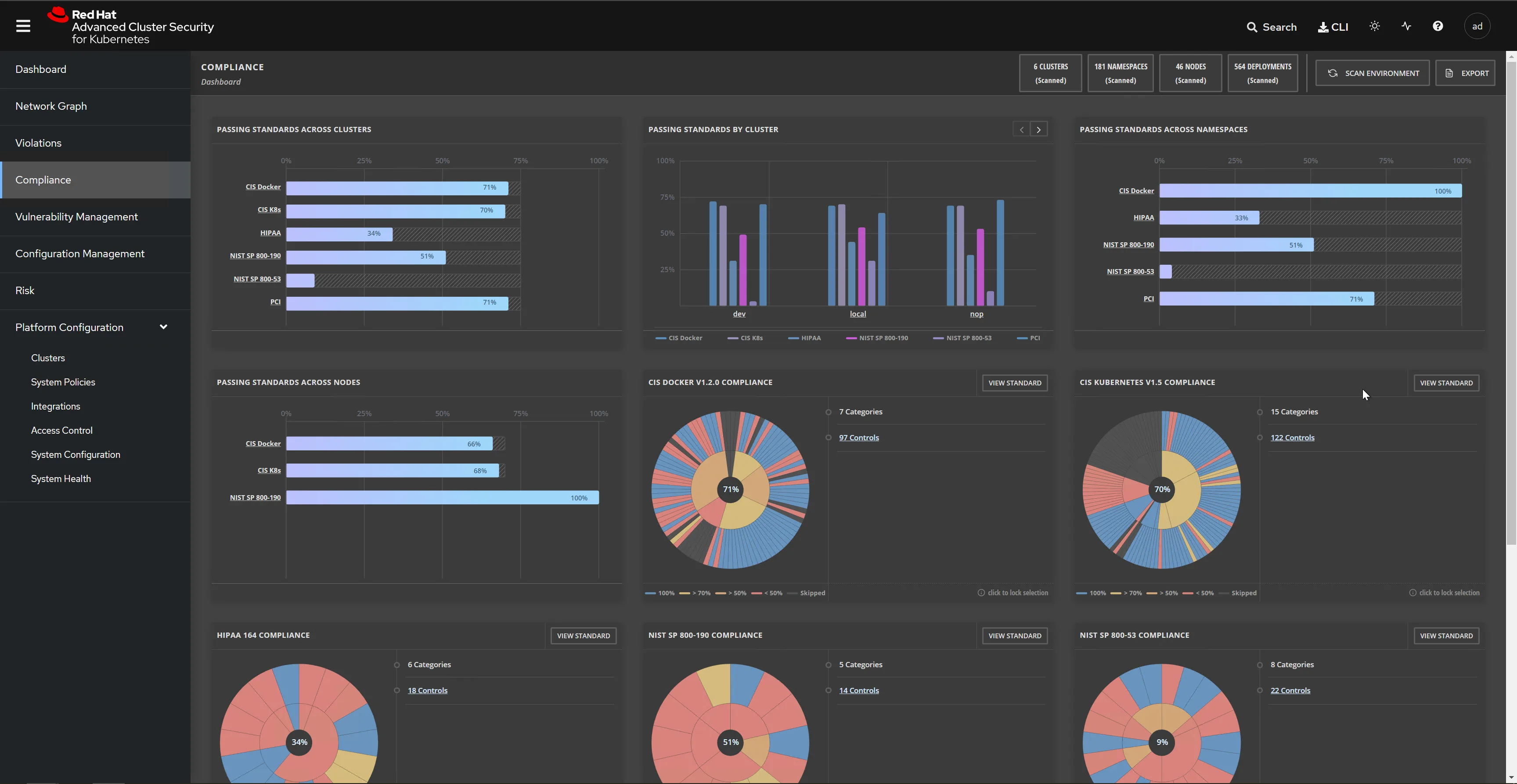
Compliance automation — The built-in compliance framework maps 300+ controls to CIS Benchmarks, NIST guidelines, PCI DSS, HIPAA, and SOC 2.
Checks run continuously and generate audit-ready reports, replacing manual evidence collection during compliance cycles.
Runtime incident response — When Collectors detect anomalous behavior (unexpected process execution, network connections to known-bad IPs, file system modifications in read-only containers), StackRox generates alerts with full context: what happened, which deployment, what image, and what the normal baseline looks like.
Teams can kill pods, scale deployments to zero, or apply network policies directly from the alert.
Integrations
Pricing
StackRox Open Source is free under the Apache 2.0 license. RHACS (the commercial product) does not publish fixed pricing on the Red Hat website. RHACS is available as:
- Self-managed — deployed on any Kubernetes cluster, priced per secured cluster through Red Hat subscription
- Cloud service — fully managed SaaS, available through AWS Marketplace with pay-as-you-go billing
- OpenShift bundled — included in some OpenShift subscription tiers
Red Hat offers a 60-day no-cost trial for RHACS Cloud Service.
Getting Started
Install Central services. Deploy the Central server and Scanner V4 using Helm charts, the roxctl CLI, or the OpenShift Operator. Central needs persistent storage for the vulnerability database and policy configuration.
Connect secured clusters. Install Sensor, Collector, and Admission Controller on each Kubernetes cluster you want to protect. Sensor connects back to Central for policy updates and data aggregation.
Review the default policies. StackRox ships with 300+ built-in policies covering image vulnerabilities, deployment configurations, runtime behavior, and network access. Enable or customize policies based on your security requirements and risk tolerance.
Integrate with CI/CD. Use the roxctl CLI or REST API to add image scanning and policy checks to your build pipelines. Configure the admission controller enforcement level (inform, block, or audit) for deploy-time controls.
Set up compliance profiles. Select the compliance frameworks relevant to your organization (CIS, NIST, PCI, HIPAA) and run an initial compliance scan to baseline your clusters. Schedule automated reports for ongoing compliance monitoring.
Strengths & Limitations
Strengths:
- Full lifecycle coverage (build, deploy, runtime) in one platform, so you need fewer separate tools
- 300+ built-in policies mapped to real compliance frameworks save significant setup time
- Kubernetes-native architecture deploys as containers without external dependencies
- Network segmentation visualization and auto-generated NetworkPolicy recommendations
- Risk-based prioritization helps teams focus on what matters instead of CVE counts
- Scanner V4 built on the proven ClairCore engine provides reliable vulnerability detection
- Works on any Kubernetes distribution, not just OpenShift
Limitations:
- Smaller open-source community (1.3k stars) compared to Falco (8.7k+), Trivy (33k+), or NeuVector (1.3k)
- No container-level network firewall or deep packet inspection (unlike NeuVector’s Layer 7 DPI)
- Red Hat acquisition means development priorities naturally favor OpenShift integration
- Central component requires meaningful storage and compute resources, especially at scale with many secured clusters
- Runtime detection focuses on process and network anomalies — does not inspect application-layer traffic
- Documentation is split between StackRox community docs and Red Hat product docs, which can be confusing
For a broader view of Kubernetes and container security options, see the container security tools category page.
StackRox complements network policy tools like Calico for Kubernetes microsegmentation and lightweight image scanners like Trivy for CI/CD pipeline integration.