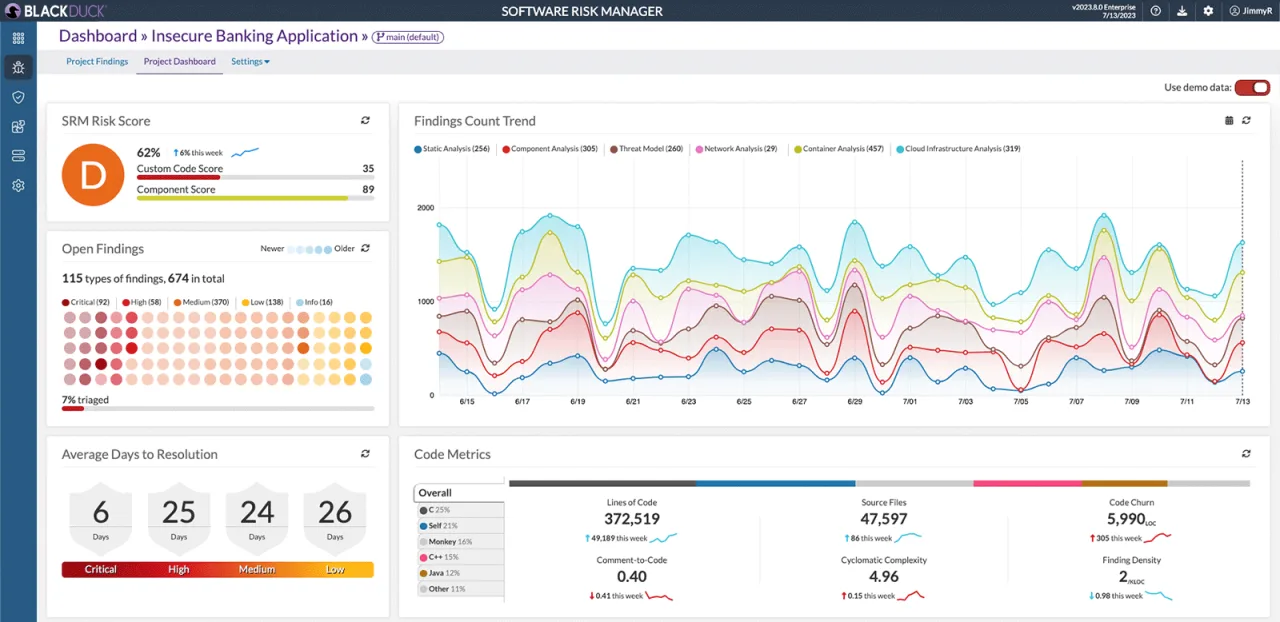
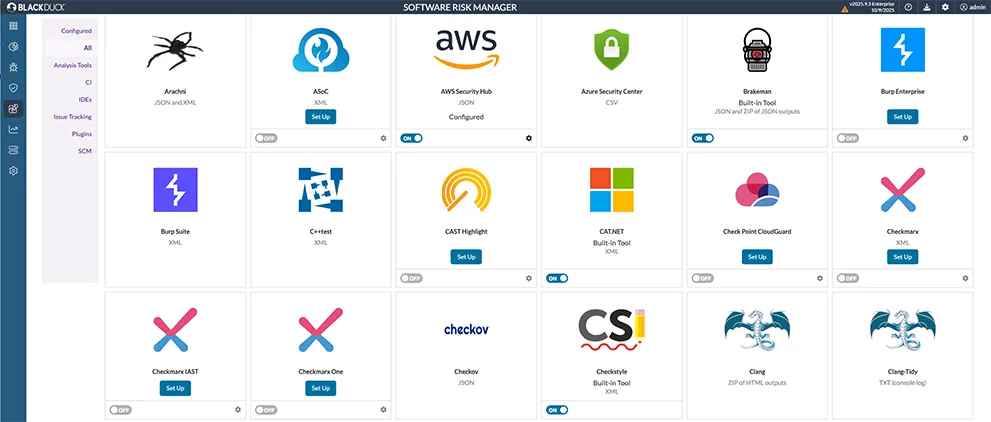
Software Risk Manager (SRM) is Black Duck’s ASPM platform that correlates findings from 150+ security tools. Formerly Code Dx, it normalizes results across SAST, DAST, IAST, SCA, and manual pentesting into a single view where the same issue found by multiple scanners appears once, backed by multiple sources.
Originally developed as Code Dx, the technology was acquired by Synopsys in 2021 and became part of Black Duck following Synopsys’ divestiture of its Software Integrity Group in 2024. Over 4,000 organizations use Black Duck products.
Notable customers include Broad Institute, NASA, DHS, Trend Micro, Honeywell, and FINRA.
What is Software Risk Manager?
SRM solves a specific problem: you run multiple security scanners, and they produce overlapping, inconsistent results. SRM ingests all of it, normalizes the findings into a common taxonomy, correlates duplicates, and gives you one prioritized list.
Key features
Multi-tool aggregation
SRM integrates with 150+ security tools:
| Category | Tools |
|---|---|
| SAST | Checkmarx, Fortify, Coverity, SonarQube, Veracode |
| DAST | Burp Suite, OWASP ZAP, Acunetix |
| SCA | Black Duck, Snyk, Dependency-Check |
| Secrets | GitLeaks, TruffleHog |
| Containers | Trivy, container analysis tools |
| Infrastructure | Network scanning, cloud security tools |
Vulnerability correlation
The correlation engine matches findings across tools:
Tool A: SQL Injection in login.php:42
Tool B: SQL Injection in login.php:42
Tool C: Database Query Issue in login.php
SRM → Single finding with 3 supporting sources
More sources = higher confidence. This also eliminates duplicate Jira tickets — a problem that wastes developer time at organizations running multiple scanners.
Simple deduplication removes exact duplicates. SRM’s correlation goes further by matching findings that different tools describe differently.
A “SQL Injection” from one tool and a “Database Query Issue” from another can be linked to the same root cause based on file, line, and vulnerability characteristics.
Risk-based prioritization
SRM prioritizes vulnerabilities based on multiple factors:
| Factor | How it affects priority |
|---|---|
| Severity and exploitability | CVSS scores combined with known exploit availability |
| Business context | Asset criticality and data sensitivity of affected applications |
| Corroboration | More tools confirming the same issue means higher confidence |
| Remediation history | Past fix patterns inform expected resolution timelines |
SBOM generation
Generate Software Bills of Materials in standard formats:
| Format | Use case |
|---|---|
| CycloneDX | Security-focused SBOM with vulnerability data |
| SPDX | License compliance and component inventory |
| Custom | Organization-specific reporting formats |
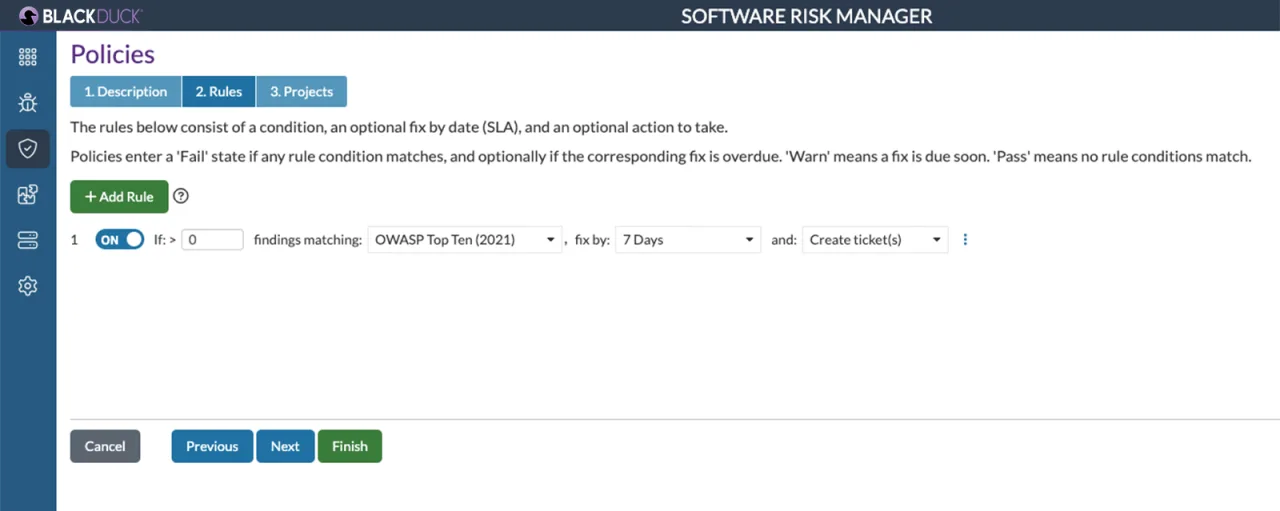
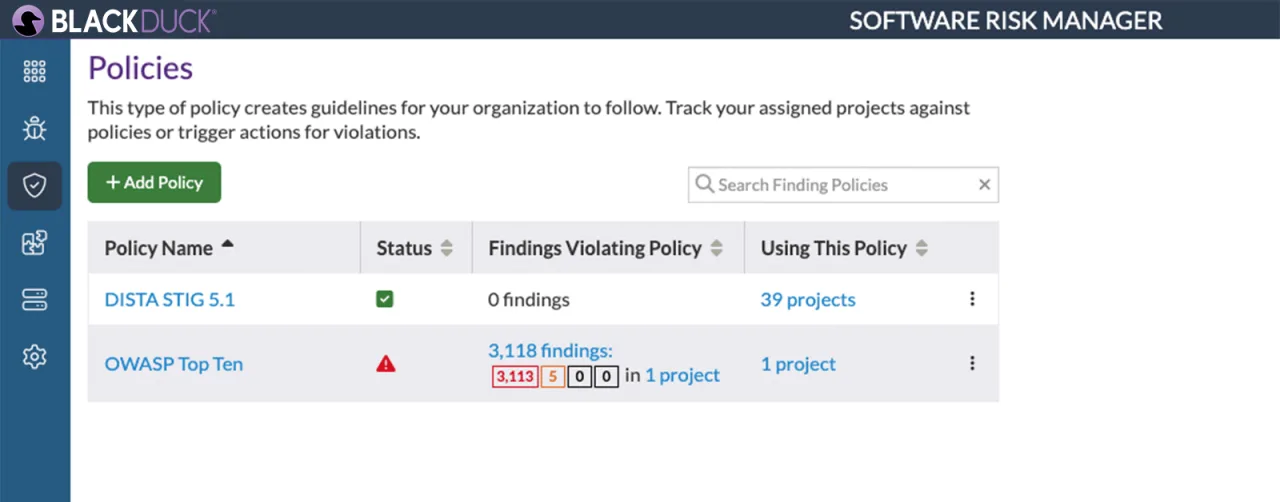
Policy-driven quality gates
Define security policies that block releases when criteria aren’t met. Policies can check for critical vulnerabilities, compliance gaps, or missing scan coverage before code ships.
Integrations
Getting started
Jenkins integration
pipeline {
stages {
stage('Security Scan') {
steps {
step([$class: 'CodeDxPublisher',
url: 'https://srm.example.com/codedx',
keyCredentialId: 'srm-api-key',
projectId: '1',
sourceAndBinaryFiles: 'scan-results/*.xml'
])
}
}
}
}
When to use Software Risk Manager
SRM makes sense for organizations already in the Black Duck ecosystem (Coverity, Black Duck SCA) that want a unified view of findings across all their security tools. The correlation engine’s ability to match findings across different scanners is where it adds the most value — if you’re running 5+ scanning tools and getting duplicate tickets in Jira, SRM fixes that.
For organizations without existing Black Duck investments, ArmorCode offers broader integration (320+ tools) with AI correlation. For open-source aggregation, DefectDojo covers 200+ tools at no cost.