Socket takes a different approach to SCA by focusing on supply chain attacks . Instead of checking dependencies against CVE databases, it analyzes what packages actually do at the code level.
This catches malicious behavior, typosquatting, and supply chain attacks before any vulnerability is disclosed.

Traditional SCA tools wait for someone to discover and report a vulnerability. Socket catches threats proactively by inspecting package behavior: network access, filesystem operations, shell execution, and obfuscated code.
If a package does something suspicious, Socket flags it regardless of whether a CVE exists.
What is Socket?
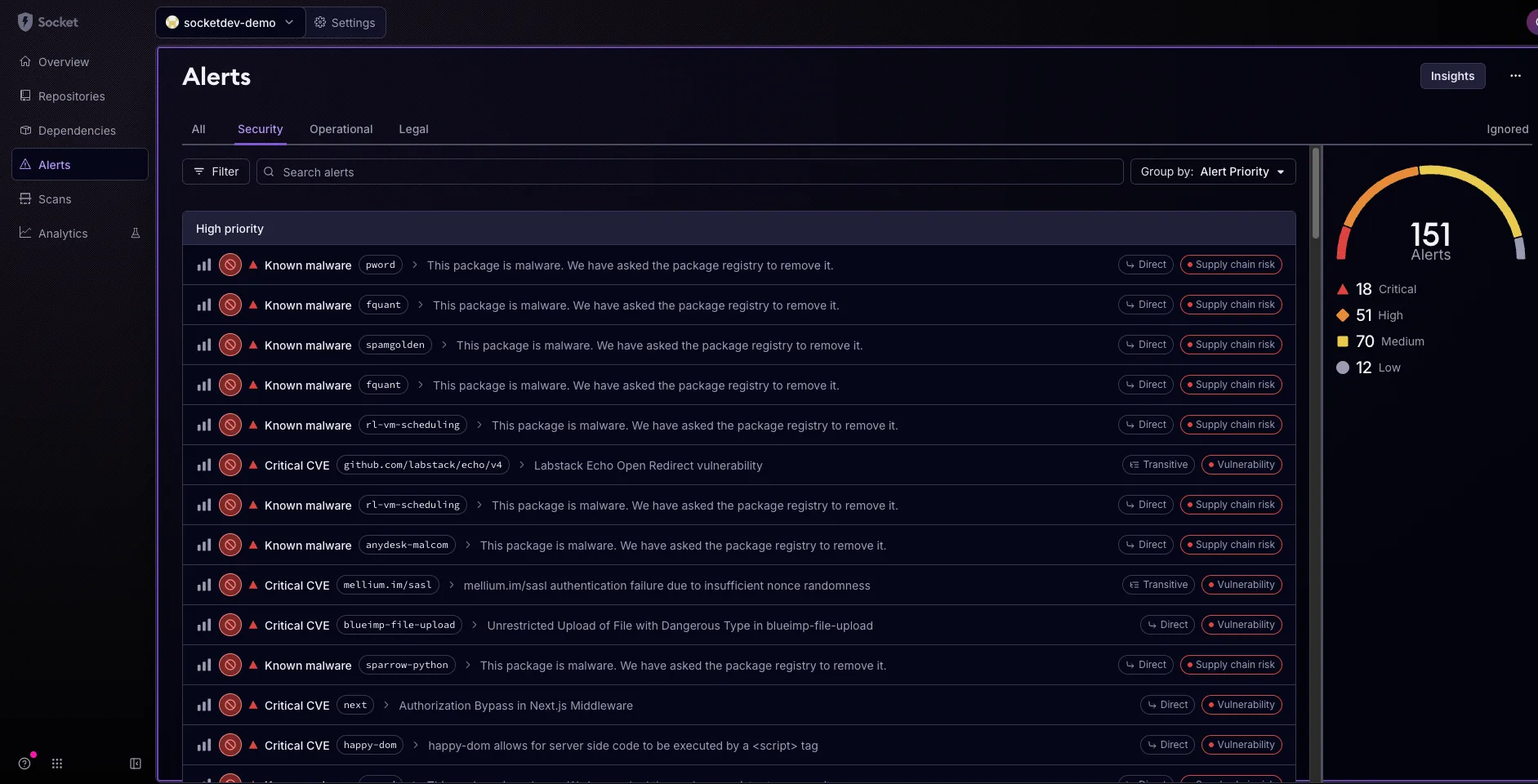
Socket monitors your dependencies for supply chain attacks. When you add or update a package, Socket analyzes its behavior and compares it against known threat patterns.
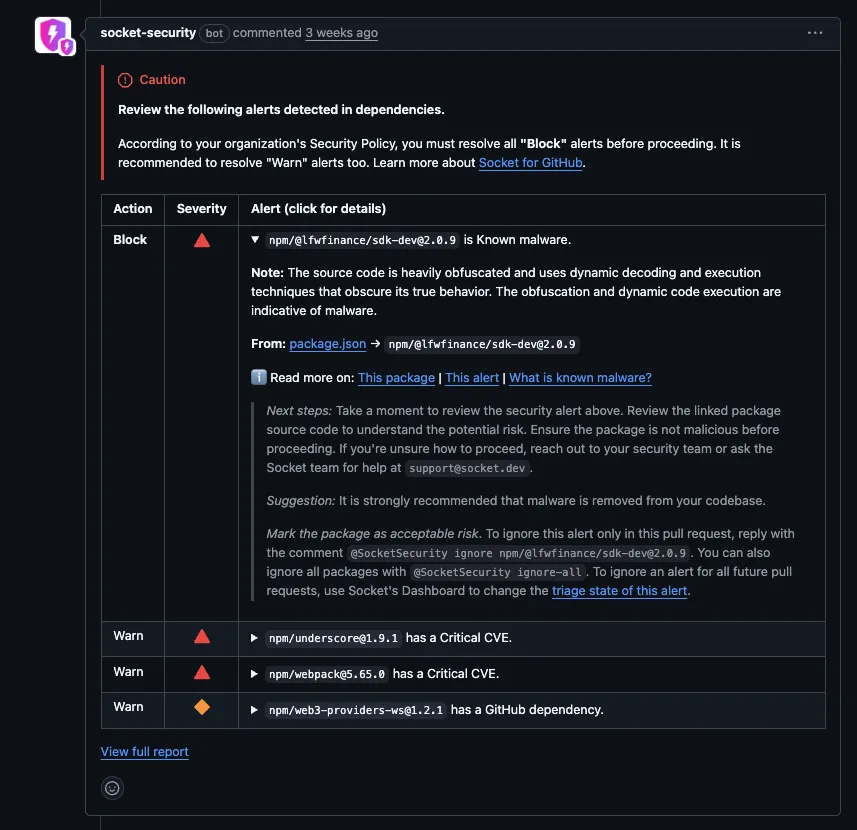
It integrates as a GitHub App that comments on pull requests with a security report for every dependency change.
Socket (socket.dev) is a supply-chain-focused SCA platform — distinct from socket.io, Socket Mobile hardware, or Socket Fiber Internet. This page covers the security tool at socket.dev.
What are Socket’s key features?
Malicious package blocking
Socket maintains a database of known malicious packages and behavioral patterns. When a dependency matches a threat signature, Socket blocks it in the PR before it reaches your codebase.
This is different from CVE-based tools that only flag known vulnerabilities after disclosure.
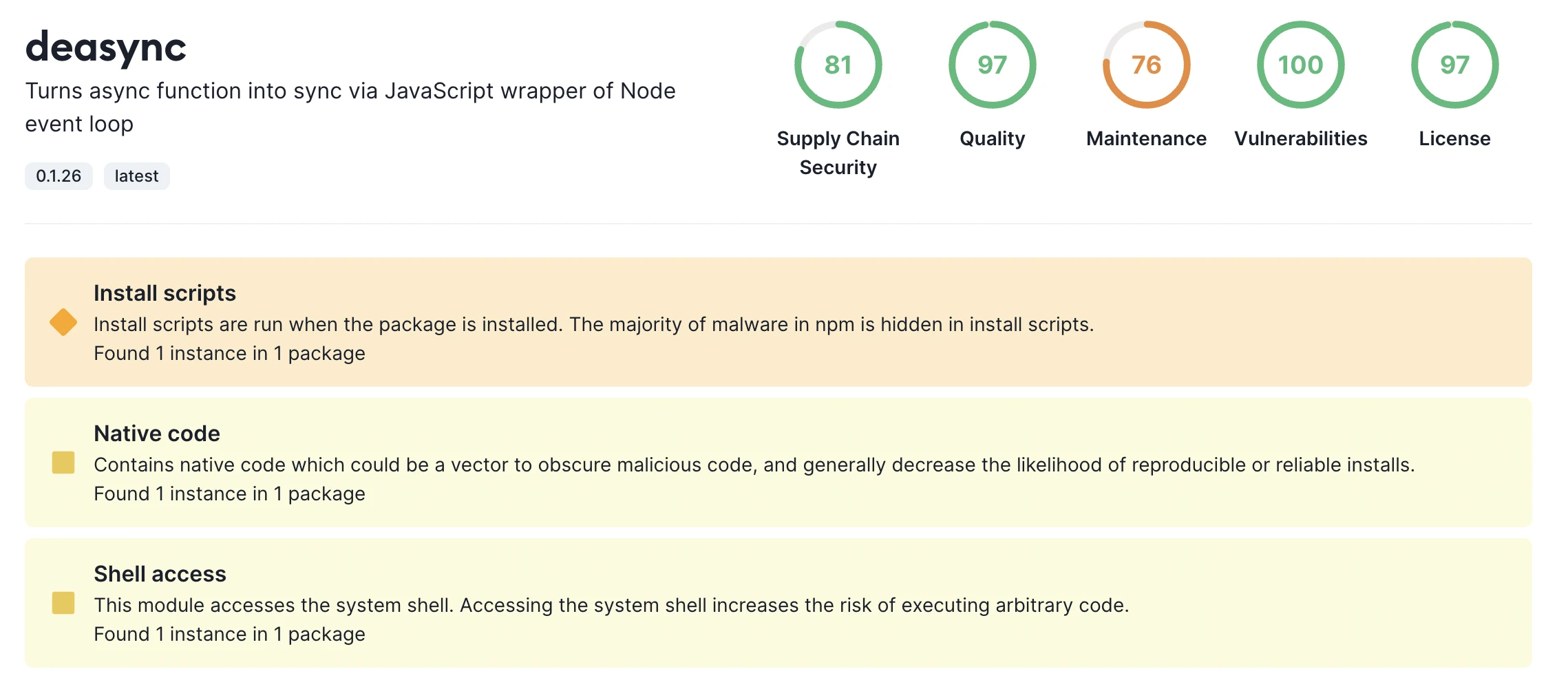
Alert categories
| Alert | Description |
|---|---|
| Malware | Known malicious code patterns |
| Install Scripts | Dangerous install hooks |
| Network Access | Unexpected outbound connections |
| Filesystem Access | Unusual file operations |
| Shell Access | Command execution |
| Obfuscation | Hidden or encoded code |
| Typosquatting | Suspicious package names |
| Protestware | Packages with political code |
PR integration
Socket adds a security report to every pull request that changes dependencies. Each new or updated package is analyzed and flagged if it exhibits suspicious behavior.
Transitive analysis and SBOM export
Socket analyzes behavior across the full transitive dependency tree, not just direct imports. The socket optimize command takes this further by suggesting tested package overrides from the Socket Registry that can reduce or replace unmaintained transitive packages.
For compliance workflows, Socket exposes a CycloneDX SBOM export endpoint in its API, currently marked beta in their docs. SBOM import and export is listed as a Business-tier feature on socket.dev/pricing — the Free and Team tiers center on PR-time alerting rather than SBOM artifacts.
Setup
npm install -g @socketsecurity/cli for local scanning with socket scan.# Install via npm
npm install -g @socketsecurity/cli
# Create and run a scan
socket scan create
# Generate report
socket scan report
Using Socket CLI
The GitHub App covers most users, but teams that need local scanning, CI-gate behavior, or pre-merge checks in non-GitHub environments use the Socket CLI.
Install and authenticate
Install the CLI from npm:
npm install -g @socketsecurity/cli
Socket’s docs also list npm install -g socket as an alias — both install the same binary. Authenticate once with:
socket login
This stores your Socket API token locally so later commands do not re-ask.
Scan a project
From a repo root, create a scan:
socket scan create ./
socket scan create --report (aliased as socket ci) runs the same scan but exits with a non-zero status if any unhealthy alerts fire, which is the primitive most teams wire into a CI failure gate.
Other useful commands
socket package score <pkg>— fetch the Socket risk score for a specific package before adding itsocket npm install <pkg>— wrap npm so every install is pre-scannedsocket optimize— suggest tested overrides from the Socket Registry for transitive dependenciessocket fix— apply available security updates to flagged packages
Use in CI
Socket’s documented GitHub Actions pattern installs the Python client (pip install socketsecurity) and runs the socketcli command inside a workflow step, with a SOCKET_SECURITY_API_TOKEN secret configured in the repo.
Supported ecosystems
| Ecosystem | Package registry | Coverage depth |
|---|---|---|
| JavaScript | npm | Full behavioral analysis |
| Python | PyPI | Full behavioral analysis |
| Go | Go modules | Vulnerability + supply chain |
| Java | Maven Central | Vulnerability + supply chain |
| Ruby | RubyGems | Vulnerability + supply chain |
| Rust | crates.io | Vulnerability + supply chain |
When to use Socket
Socket fills a gap that CVE-based SCA tools cannot. If you are concerned about supply chain attacks (and you should be), Socket catches threats that Snyk , Dependabot , and other traditional tools miss.
Strengths:
- Catches malicious packages before CVEs exist
- Behavioral analysis detects threats other tools miss
- PR-level blocking prevents compromised packages from entering your codebase
- Free for open-source projects
Limitations:
- Ecosystem coverage continues to expand (10+ ecosystems, with deepest analysis for npm and PyPI)
- Not a full vulnerability scanner; pair with a CVE-based tool for complete coverage
- Commercial plans required for private repositories
How it compares:
| vs. | Key difference |
|---|---|
| Snyk Open Source | Snyk focuses on known CVEs with automated fix PRs. Socket catches supply chain attacks before CVEs are published. Complementary tools. |
| Veracode SCA | Veracode added Phylum-based supply chain detection. Socket has deeper behavioral analysis for npm and PyPI. |
For background, see the guides on supply chain attacks and What is SCA? .
What are alternatives to Socket?
Socket is one of a small set of tools focused on supply chain attack detection. The closest alternatives each take a different angle on the same problem.
Snyk Open Source
Snyk Open Source leads on CVE-driven SCA with automated fix PRs and broad ecosystem coverage. Teams that want a wide vulnerability scanner with a mature fix-PR workflow often pick Snyk first, then add Socket for behavioral detection. Most “Socket vs Snyk” search traffic reflects this pairing decision rather than a head-to-head replacement.
Veracode SCA (Phylum)
Veracode acquired Phylum’s malicious-package technology in January 2025 and is folding it into Veracode SCA. If you already run Veracode for SAST or policy reasons, Veracode SCA with Phylum-derived malicious-package detection is the minimum-friction path. Socket’s behavioral analysis for npm and PyPI is deeper today, but Veracode’s enterprise policy and compliance tooling is broader.
Endor Labs
Endor Labs emphasizes function-level reachability across the full application graph, aiming to cut CVE noise by flagging only exploitable paths. Endor Labs and Socket solve overlapping problems from opposite ends: Endor starts from your own code’s reachability, Socket starts from the dependency’s behavior. Some larger engineering orgs run both.
For the full competitor breakdown, see Socket alternatives . For broader context, the SCA tools overview and supply chain attacks guide are the right starting points.
How much does Socket cost?
Socket publishes per-contributor pricing on socket.dev/pricing with four tiers: Free, Team, Business, and Enterprise.
The Free tier is explicitly unlimited for open-source projects — “Socket is and will always be free to use for open-source” — and includes unlimited developers and repos with a monthly scan cap. It covers malicious-dependency blocking and 70+ risk-type detection.
Team is listed at $25 per developer per month. It raises the scan cap, adds precomputed reachability to cut CVE false positives, priority scoring, and Slack alerts. Socket offers a free Team tier for qualifying open-source projects on request.
Business is listed at $50 per developer per month. It removes scan and API quotas, adds SBOM import/export, SSO/SAML, webhook automation, and compliance integrations.
Enterprise is contact-sales pricing and adds full application function-level reachability, broader SCM support (GitLab, Bitbucket, Azure DevOps), SCIM provisioning, and a named account manager.
Re-check the pricing page before budgeting — vendor tiers and limits change.
Socket FAQ
Is Socket free for open-source projects?
Yes. Socket’s Free tier is unlimited for open-source use, and the vendor states “Socket is and will always be free to use for open-source.” Qualifying open-source projects can also request a free Team tier with the larger scan cap and reachability features.
Does Socket replace Snyk?
Not really. Snyk Open Source is a CVE-first SCA with automated fix PRs; Socket is a behavioral supply-chain-attack detector. Most teams use them together — Snyk for known vulnerabilities with fix workflow, Socket for malicious-package blocking at PR time.
Does Socket work without GitHub?
The GitHub App is the fastest onboarding path, but Socket also ships a CLI (@socketsecurity/cli on npm, socketsecurity on PyPI). GitLab, Bitbucket, and Azure DevOps support is listed as an Enterprise-tier feature on socket.dev/pricing.
Does Socket scan PyPI packages?
Yes. Python (PyPI) is one of the two ecosystems with full behavioral analysis, alongside npm. Other supported ecosystems (Go, Maven, RubyGems, Cargo, NuGet) get vulnerability plus supply-chain coverage that is less deep than the npm/PyPI tier.
Does Socket export SBOMs?
Socket’s API includes a CycloneDX SBOM export endpoint, currently marked beta in their docs. SBOM import and export is listed as a Business-tier feature on the pricing page, so Free-tier users do not have SBOM export today.








