- GitHub CodeQL converts code to a relational database and queries it with QL — giving advanced security teams the ability to write custom vulnerability checks specific to their codebase and frameworks.
- Snyk Code uses a semantic AI engine (DeepCode) for near-real-time SAST results in seconds, without requiring a code compilation step — making it faster to integrate and faster to give developers feedback.
- CodeQL is free for open-source repositories on GitHub; private repositories require GitHub Advanced Security (GHAS) on GitHub Enterprise, which adds per-committer licensing cost.
- Snyk Code has a free tier for individuals and open-source projects; the full IDE integration, priority support, and enterprise features require a paid Snyk plan.
- For teams on GitHub Enterprise that already pay for GHAS, CodeQL is the obvious starting point — it is already included. Teams not on GitHub Enterprise, or those needing multi-platform IDE integration and faster setup, should evaluate Snyk Code.
Snyk Code vs GitHub CodeQL: which SAST approach fits your team?
Snyk Code is an AI-powered SAST tool that delivers near-real-time scan results without requiring code compilation. GitHub CodeQL is a query-based static analysis engine that converts code into a relational database, letting security teams write custom QL queries to find complex vulnerability patterns.
Snyk Code and GitHub CodeQL are both modern SAST tools , but they solve the static analysis problem in fundamentally different ways — and serve different buyer profiles.
GitHub CodeQL is a research-grade static analysis engine that converts source code into a queryable relational database. Security engineers write queries in the QL language to find vulnerability patterns.
This approach is powerful and flexible — it can find complex inter-procedural taint flows and custom vulnerability patterns specific to your codebase. The tradeoff is complexity: CodeQL’s full power requires learning QL and investing in query development.
Snyk Code uses a semantic code analysis engine (the DeepCode AI engine from the Deepcode.ai acquisition) that provides scan results in seconds without compiling code.
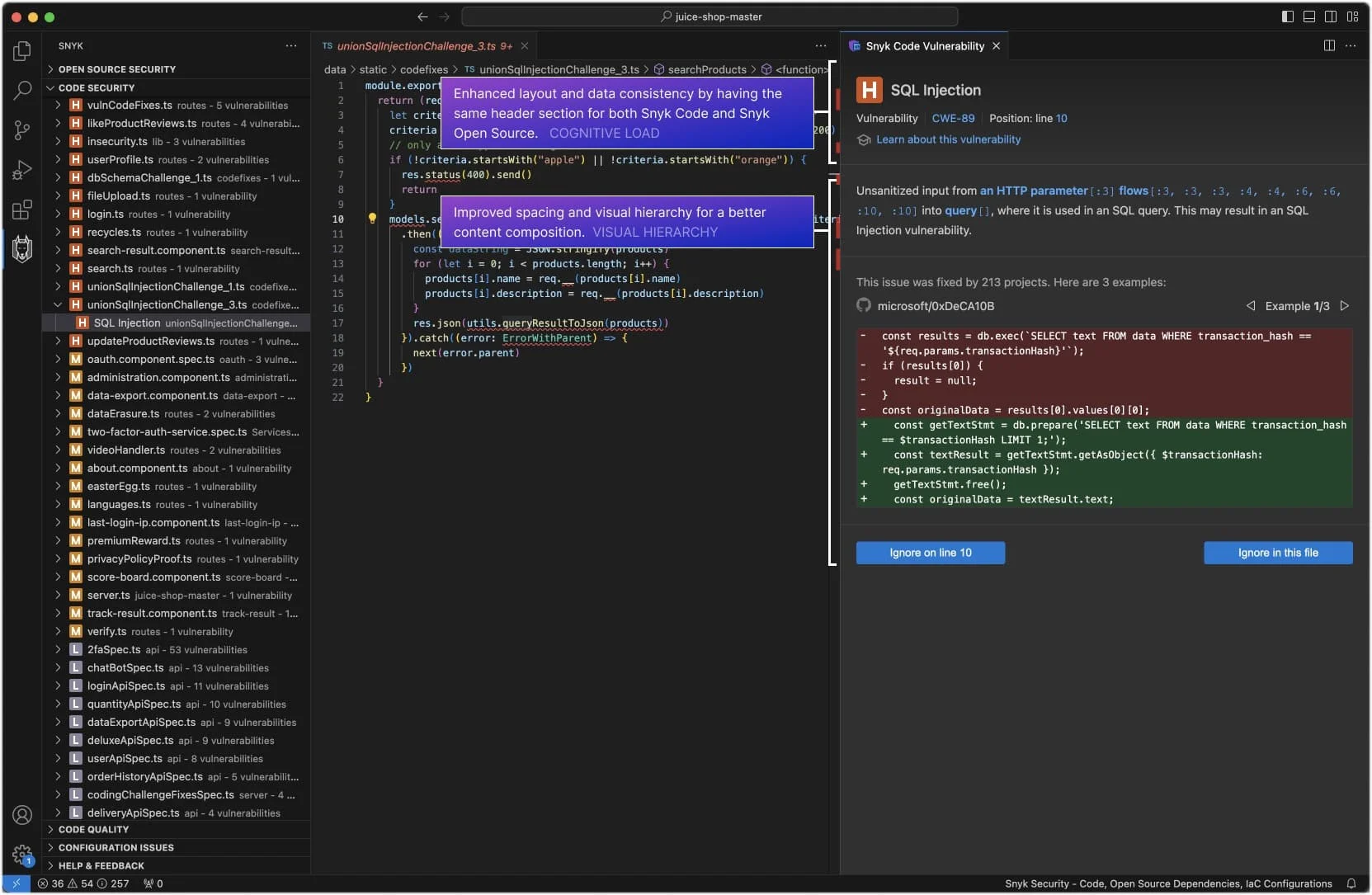
Developers get findings in their IDE as they type and in pull request comments without writing a single query. The tradeoff is less customizability — Snyk Code’s detection logic is managed by Snyk’s research team, not the user.
The practical choice is often determined by your existing infrastructure: if you are on GitHub Enterprise with GHAS already licensed, CodeQL is included and the most pragmatic starting point.
If you need cross-platform IDE integration, faster scan setup, or SAST alongside SCA and container scanning in one vendor, Snyk Code is the stronger choice.
Key differences
| Feature | Snyk Code | GitHub CodeQL |
|---|---|---|
| License | Freemium | Free for OSS; GHAS for private repos |
| Pricing | Free tier (limited); paid plans from $25/dev/month | Free for public GitHub repos; GHAS included in GitHub Enterprise |
| SAST Approach | Semantic AI engine (DeepCode) | Query-based (QL language, relational code database) |
| Scan Speed | Near real-time (seconds) | Minutes to hours depending on codebase size |
| Custom Queries | No | Yes (QL language, extensive library) |
| Compilation Required | No | Required for compiled languages (Java, C++, C#, Go) |
| Languages | 19+ | 10+ (C/C++, C#, Go, Java/Kotlin, JavaScript/TypeScript, Python, Ruby, Swift, Rust) |
| IDE Integration | VS Code, IntelliJ, Eclipse, and others | VS Code (CodeQL extension), GitHub native |
| CI/CD Integration | GitHub, GitLab, Bitbucket, Azure DevOps, Jenkins | GitHub Actions native; CodeQL CLI for others |
| GitHub Integration | GitHub App | Native (code scanning, PR checks, Copilot Autofix) |
| Fix Suggestions | DeepCode AI Fix | Copilot Autofix (GitHub Enterprise only) |
| False Positive Rate | Low (tuned for precision) | Low (default suites); varies with custom queries |
| GitHub-independent | Yes | Partial (CLI works standalone; full UX is GitHub-only) |
Head-to-head comparison
Detection approach and scan architecture
The core architectural difference shapes everything else about these tools.
GitHub CodeQL builds a relational database from your source code — called a CodeQL database — that captures the full syntactic and semantic structure of the code: every function call, data flow edge, control flow path, and type relationship.
Security engineers query this database using QL to find vulnerability patterns. CodeQL can track a user-controlled value from an HTTP request parameter through multiple function calls to a dangerous sink like a SQL query or file write.
The tradeoff is build time. For compiled languages (Java, C++, C#, Go), CodeQL must compile the code as part of database creation, which adds minutes to CI runs and requires correct build environment configuration. Interpreted languages like Python and JavaScript are faster but still slower than Snyk Code.
Snyk Code uses a semantic code analysis engine that does not require compilation. It analyzes abstract syntax trees and semantic representations of the code directly. Results appear in the IDE as developers write code, not after a multi-minute build step. This near-real-time feedback loop is Snyk Code’s primary developer experience advantage.
Custom vulnerability queries
This is CodeQL’s biggest competitive advantage for security-mature organizations. The QL query language lets security engineers write checks for vulnerability patterns specific to their internal frameworks, custom cryptography usage, or proprietary API misuse.
If your application uses an internal data access layer that has specific injection risk, you can write a CodeQL query that checks for unsafe use of that internal API — something no off-the-shelf SAST tool would detect. GitHub’s open-source CodeQL query libraries provide thousands of community-contributed queries as a starting point.
Snyk Code does not offer custom query authoring. Snyk’s research team maintains the detection rules. If you need detection for a custom pattern, you submit a request to Snyk or rely on the existing ruleset. This is appropriate for most teams, but security teams with advanced custom requirements will hit this limit.
GitHub ecosystem integration
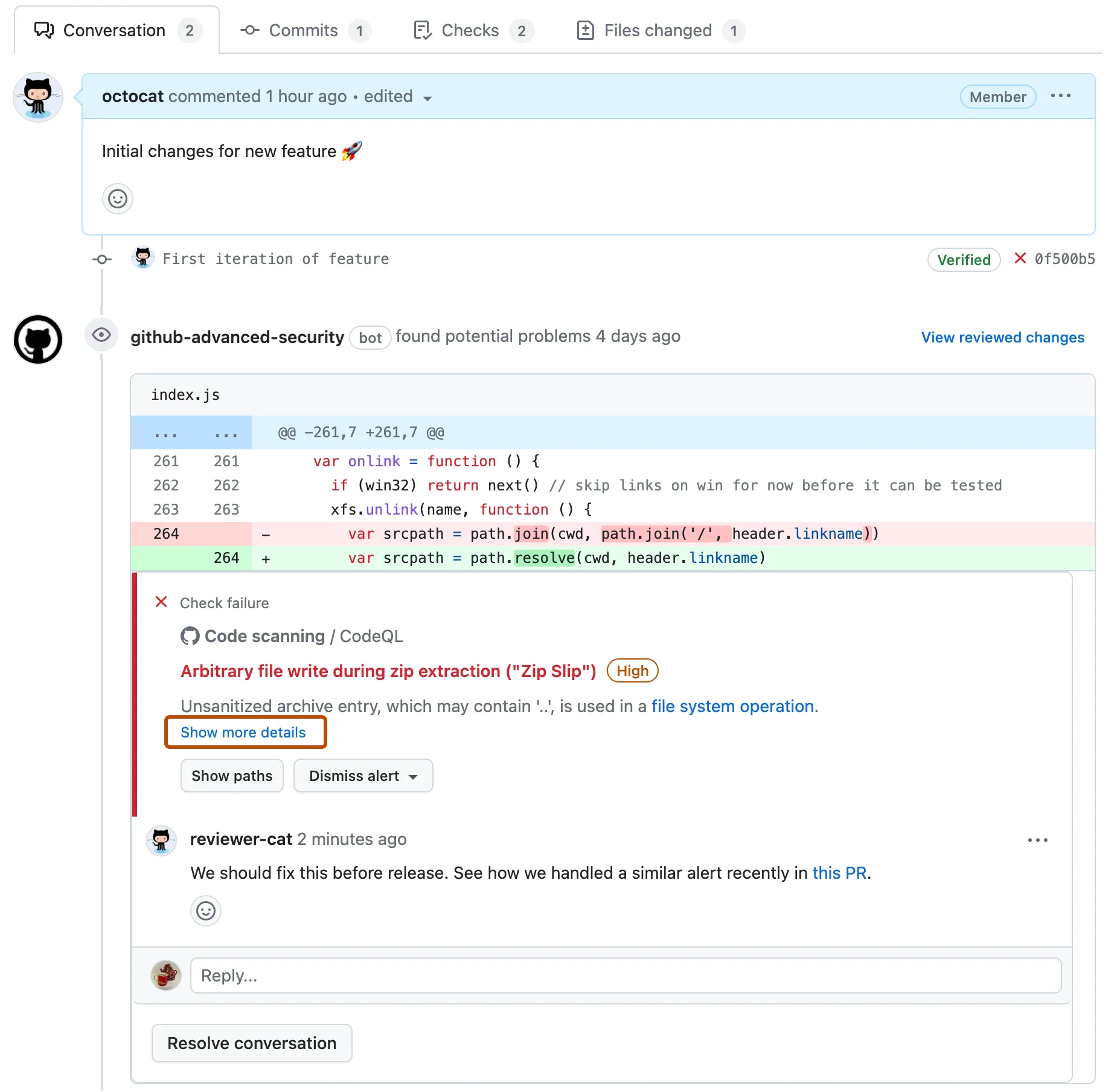
GitHub CodeQL is native to GitHub. Code scanning results appear directly in the GitHub Security tab. Pull request checks show SAST findings inline on the diff. GitHub Copilot Autofix (in GitHub Advanced Security) uses AI to suggest code fixes for CodeQL findings directly in the PR — a genuinely useful integration that reduces the time from finding to fix.
Snyk Code integrates with GitHub via a GitHub App, and shows findings in pull request checks, but it is not as deeply embedded in the GitHub UI as CodeQL. The Snyk advantage is cross-platform support: Snyk works equally well on GitLab, Bitbucket, and Azure DevOps, while CodeQL’s full experience is GitHub-specific.
Language coverage
Snyk Code supports 19+ languages and frameworks, including languages that CodeQL does not cover — PHP, Scala, Apex, Dart/Flutter, Elixir, and Groovy. For organizations with polyglot codebases, that breadth matters.
GitHub CodeQL supports 10+ primary languages with deep analysis depth. For the languages it covers — particularly Java, C/C++, Python, JavaScript, and Go — CodeQL’s analysis depth is exceptional. The query libraries for Java and C++ in particular are among the most mature SAST rulesets in the industry.
Pricing and access
GitHub CodeQL is free for public open-source repositories on GitHub — GitHub’s default code scanning is enabled for free with no limits. For private repositories, CodeQL requires GitHub Advanced Security (GHAS), which is available on GitHub Enterprise Cloud and GitHub Enterprise Server. GHAS pricing is per active committer in addition to the GitHub Enterprise base cost.
Snyk Code has a free tier for individuals and open-source projects, with a cap on the number of tests. The Team plan at $25/developer/month includes unlimited scanning plus IDE integration and priority support. Snyk Code is also part of the broader Snyk platform alongside Snyk Open Source , Snyk Container, and Snyk IaC — teams that want SCA + SAST in one platform from one vendor benefit from the Snyk platform approach.
When to choose each tool
Choose GitHub CodeQL if:
- You are on GitHub Enterprise with GHAS already licensed — CodeQL is included
- Your security team needs custom vulnerability queries for internal frameworks or business logic
- You primarily use Java, C++, C#, Go, or Python (CodeQL’s deepest coverage languages)
- GitHub-native integration (Security tab, PR checks, Copilot Autofix) matters to your workflow
- You maintain open-source projects and need free SAST with no usage limits
Choose Snyk Code if:
- You need near-real-time IDE feedback as developers write code (seconds, not minutes)
- You use GitLab, Bitbucket, or Azure DevOps rather than GitHub
- You want SAST + SCA + Container + IaC in a single platform without GHAS
- You have polyglot codebases that include languages CodeQL does not support
- You want managed detection rules without maintaining custom queries
Consider both for complementary coverage: CodeQL for deep taint analysis and custom queries on your primary languages, plus Snyk Code for fast IDE feedback and SCA coverage across all repositories. See also Semgrep vs CodeQL , Snyk Code vs Checkmarx , and Semgrep vs Snyk Code for related SAST comparisons. The SAST tools list covers all major options, and what is SAST explains the category in depth.
FAQ
Frequently Asked Questions
Is Snyk Code or GitHub CodeQL better for SAST?
What is the difference between CodeQL and Snyk Code's approach to SAST?
Is GitHub CodeQL free?
Can I use CodeQL outside of GitHub?
How does Snyk Code compare to CodeQL on false positives?

Founder, AppSec Santa
Years in application security. Reviews and compares 215 AppSec tools across 12 categories to help teams pick the right solution. More about me →
