What SCA actually does
Software Composition Analysis finds known vulnerabilities in the open-source libraries your application depends on. It does not scan your code. It scans your dependencies.
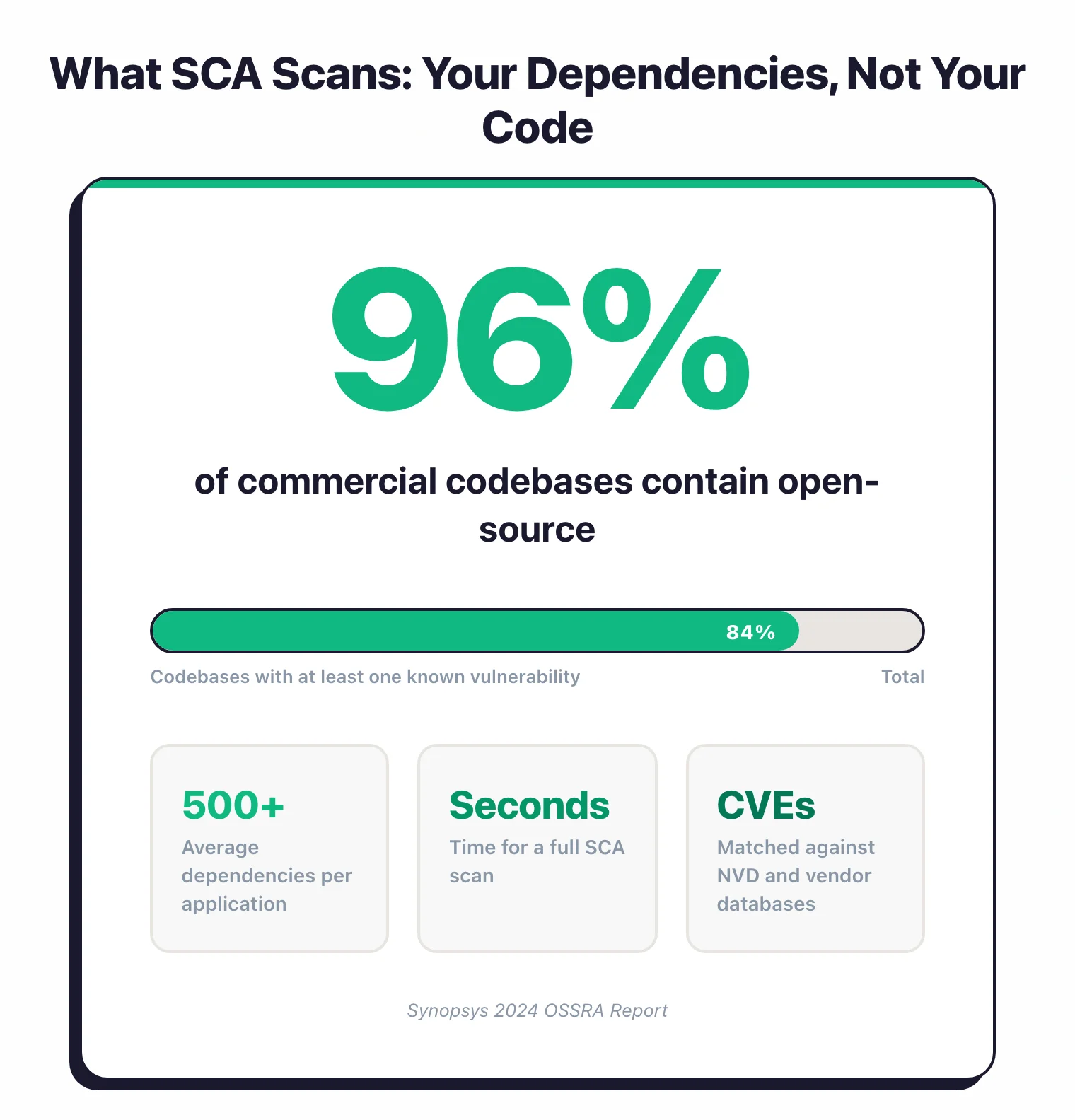
Modern applications are mostly open source. The Black Duck 2026 OSSRA report found 98% of commercial codebases contain open-source components and 87% have at least one known vulnerability, with the mean number of vulnerabilities per codebase climbing 107% year-over-year to 581.
You can write the most secure code in the world, but if you import a library with a critical vulnerability, you inherit that risk.
SCA tools read your manifest files (package.json, pom.xml, requirements.txt, go.mod, Gemfile.lock), identify every direct and transitive dependency.
They then cross-reference them against vulnerability databases like the National Vulnerability Database (NVD), OSV, and vendor-curated databases.
The tool runs in seconds. It tells you which dependencies have known CVEs, how severe they are, and in many cases, which version to upgrade to.
SCA also handles license compliance. Open source does not always mean “free to use however you want.” A copyleft license like GPL can require you to open-source your own code.
If you ship commercial software, SCA catches licensing conflicts before they become legal problems.
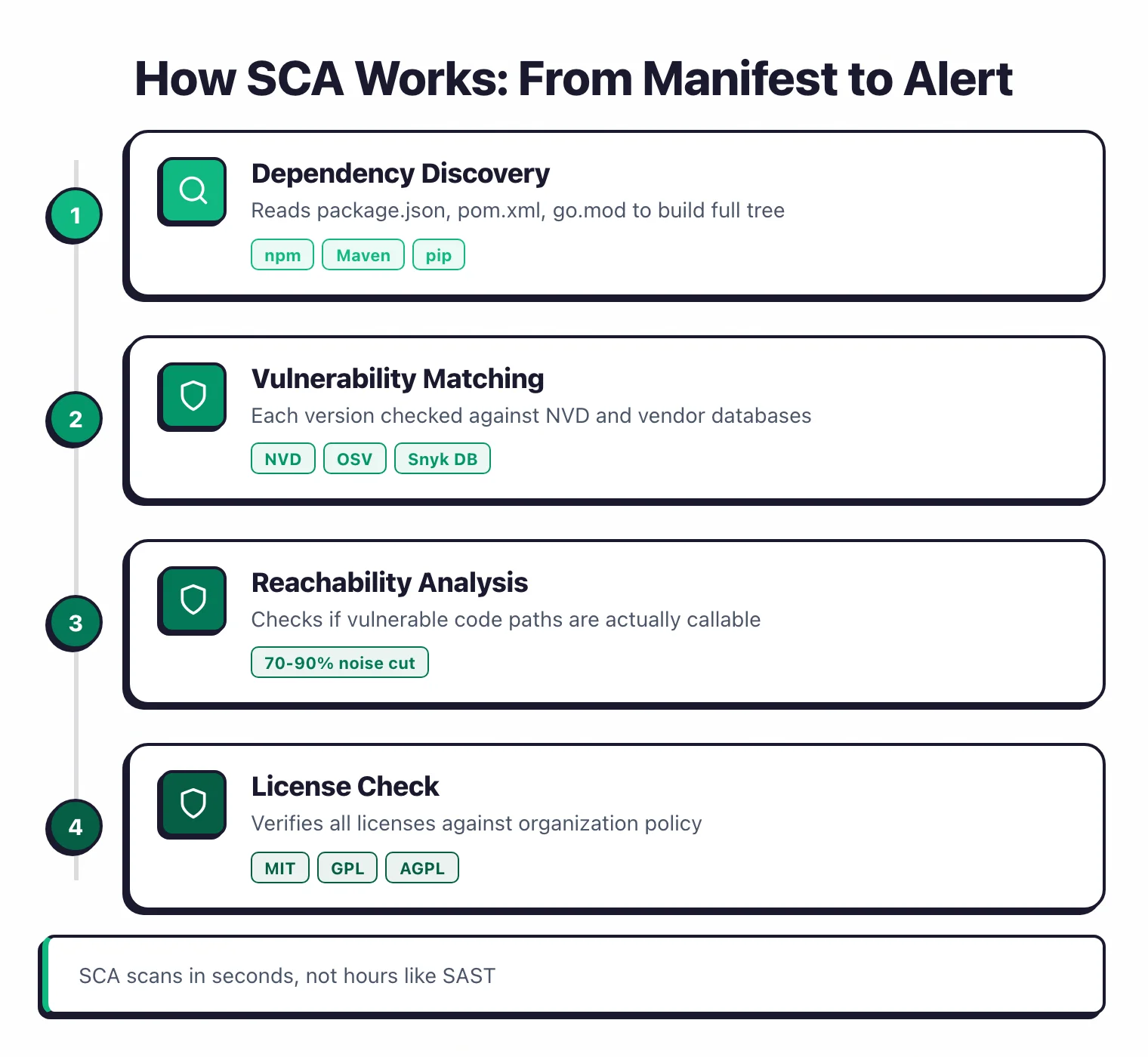
How does SCA work?
SCA follows a simpler pipeline than SAST or DAST. Identify dependencies, check them against databases, report what you find.
Dependency discovery
The tool scans your manifest files and lock files to build a complete dependency tree: direct dependencies (what you explicitly installed) and transitive dependencies (what your dependencies depend on). A typical Node.js project with 20 direct dependencies might have 200+ transitive dependencies.
Some tools also scan compiled binaries and container images to identify components not in manifest files. Black Duck is particularly strong at binary analysis.
Vulnerability matching
Each component and version is checked against vulnerability databases. OWASP Dependency-Check uses NVD directly. Commercial tools like Snyk and Mend maintain their own curated databases that update faster.
The speed difference matters: NVD can take weeks to publish a new CVE, while vendor databases often pick it up within hours.
Reachability analysis
This is what separates basic SCA from actually useful SCA. A dependency might have a vulnerability in a function your application never calls.
Traditional tools report it anyway, and the noise piles up.
Reachability analysis checks whether the vulnerable code path is actually reachable from your application. Endor Labs and Contrast SCA do this through static call graph analysis. Qwiet AI uses code property graphs.
According to vendors like Endor Labs, the result is typically a 70-90% reduction in alerts, which makes a huge difference for developer adoption.
License compliance
SCA tools check the licenses of every dependency against your organization’s policies. Common license types:
- MIT, Apache 2.0, BSD — Permissive. Generally safe for commercial use.
- GPL, AGPL — Copyleft. Can require you to open-source your own code if you distribute software.
- LGPL — Weak copyleft. Typically okay for dynamic linking in commercial software.
FOSSA and Black Duck are the strongest tools for license compliance. Snyk covers it too, but with less depth on complex licensing scenarios.
SBOM generation
Most SCA tools can produce a Software Bill of Materials in CycloneDX or SPDX format.
The US Executive Order on Cybersecurity (2021) mandates SBOMs for software sold to federal agencies, and adoption is growing beyond government.
Even if compliance is not your concern today, having an SBOM makes it much faster to check whether you are affected when the next Log4Shell drops.
For the full SBOM walkthrough, see SBOM tools comparison. If you want a free tool that covers the whole pipeline, the open-source SCA tools guide shortlists the twelve most-used options. For a broader view of the category, the SCA tools hub collects all 30+ tools in one place.
What does SCA catch?
SCA focuses on a specific attack surface:
- Known vulnerabilities (CVEs) — The core function. If a dependency version has a published CVE, SCA flags it.
- License violations — Dependencies with licenses that conflict with your organization’s policies or commercial distribution model.
- Outdated dependencies — Components that are several versions behind, which may indicate unmaintained or abandoned libraries.
- Malicious packages — Newer tools like Socket analyze package behavior to detect typosquatting, dependency confusion, and other supply chain attack patterns.
Beyond the bullet list above, three things are worth spelling out because they trip people up when they first evaluate SCA.
CVE detection in dependencies is about matching, not discovery. An SCA tool does not find new vulnerabilities; it matches your component versions against CVEs that have already been published to NVD, GHSA, OSV, or an ecosystem-specific feed. The tool’s value is how fast and how accurately that match happens, not novel research.
Transitive-dependency-only vulnerabilities are the majority. Most real-world findings live in packages your code does not import directly — they are pulled in by something you did import. A direct dependency scan catches only the tip; every tool on the comparison list resolves the full tree.
Reachable vs raw CVE counts tell different stories. A scanner without reachability reports every CVE in every component. A scanner with reachability (Endor Labs, Contrast SCA, OSV-Scanner guided remediation) reports only CVEs in code your application actually calls — usually 10-30% of the raw count. Both numbers are correct; they answer different questions.
Licence conflicts and typosquats round out the surface. Licence conflicts are the non-security half of SCA — a GPL-licensed library in proprietary code is a legal exposure, not a CVE. Typosquats and compromised-maintainer releases are packages that behave maliciously without a CVE yet; catching those requires a behavioural scanner like Socket, not a CVE matcher.
Why is SCA so noisy?
The biggest complaint about SCA is alert volume.
A typical enterprise application might show hundreds of vulnerable dependencies, most of which are transitive (dependencies of dependencies) and many of which are not exploitable in context.
I have seen teams disable SCA alerts entirely because the noise was unbearable. That is worse than having no SCA at all, because it creates a false sense of coverage.
Three things help.
Reachability analysis. Endor Labs and Contrast SCA cut alerts by 70-90% by showing which vulnerabilities are actually reachable from your code. The most effective noise reduction available.
Severity filtering. Not every CVE is critical. Block merges on critical and high, warn on medium, suppress low. Most tools support this.
Transitive dependency focus. A vulnerability in a direct dependency you control is more actionable than one buried three levels deep. Some tools let you prioritize accordingly.
Benefits and limits of SCA
SCA is a high-leverage control, but it is not a complete one. The honest picture is a short list of each.
Benefits:
- Visibility into transitive dependencies. Most real-world vulnerabilities live several levels deep in your dependency graph, beyond what a manual
package.jsonreview catches. SCA resolves the full tree in seconds. - Compliance automation. US Executive Order 14028, the EU Cyber Resilience Act, and PCI DSS 4.0 all lean on machine-readable component inventories. SCA tools that emit CycloneDX or SPDX cover the paperwork.
- Continuous CVE monitoring. When a new critical CVE drops, you want to know which of your applications is affected within minutes, not weeks. SCA backed by a persistent SBOM store (Dependency-Track, Anchore Enterprise) answers that instantly.
- Lowest-cost supply-chain hygiene. Free tiers of Snyk, Dependabot, and Trivy + Grype cover the core capability at zero licence cost.
Limits:
- Noise and false positives. Flat CVE lists without reachability make alert fatigue inevitable. Endor Labs, Contrast SCA, and Qwiet AI cut that by 70-90% with reachability; most open-source scanners do not.
- Custom-compiled and vendored libraries. If your team forks a library and vendors it into your repo, SCA has nothing to match against. Binary composition analysis (Black Duck, FOSSA) is the only reliable answer.
- Licence vs malicious-package overlap. SCA is strong on known CVEs and licence strings. It is weak on typosquats and compromised-maintainer releases, which is why teams pair SCA with behavioural scanners like Socket.
- Dependent on database freshness. An SCA tool is only as good as the feeds it consumes. NVD publication lag, GHSA review queues, and ecosystem-specific advisory gaps all land in your scan results.
Supply chain attacks
Traditional SCA checks dependencies against databases of known vulnerabilities. That works for CVEs that have already been reported. Supply chain attacks are a different problem.
An attacker compromises a legitimate package or publishes a malicious one that looks legitimate. There is no CVE because nobody has reported it yet. Traditional SCA misses these entirely.
The numbers are ugly. The Sonatype 2024 State of the Software Supply Chain report found a 156% year-over-year increase in malicious packages, with over 704,102 malicious packages identified since 2019 across npm, PyPI, and other ecosystems.
Socket takes a different approach to this problem. Instead of matching against CVE databases, it analyzes what packages actually do: network calls, filesystem access, obfuscated code, install scripts.
If a package that is supposed to be a string formatting library suddenly starts making HTTP requests to an unknown server, Socket flags it.
Checkmarx SCA has a similar behavioral analysis feature that evaluates package provider credibility, update cadence, and runtime behavior.
For teams worried about supply chain risk, the combination of traditional SCA (for known CVEs) and behavioral analysis (for unknown threats) provides the broadest coverage.
SBOMs and compliance
A Software Bill of Materials is an inventory of every component in your software. If you sell a food product, you list the ingredients. An SBOM does the same for software.
The push for SBOMs accelerated after the US Executive Order on Cybersecurity in 2021, which requires SBOMs for software sold to federal agencies. The EU Cyber Resilience Act has similar requirements coming.
SBOMs are useful beyond compliance. When Log4Shell (CVE-2021-44228) was disclosed in December 2021, organizations with SBOMs could immediately check whether they were affected.
Everyone else spent days or weeks manually inventorying their dependencies.
Standard formats:
- CycloneDX — OWASP-maintained, lightweight, widely supported.
- SPDX — Linux Foundation-maintained, ISO standard, more detailed.
Most SCA tools generate SBOMs in both formats. Black Duck, Snyk, and Endor Labs all include SBOM generation.
SCA vs SAST
SCA and SAST are often confused because both run before deployment. They look at completely different things.
| SCA | SAST | |
|---|---|---|
| What it scans | Third-party libraries and dependencies | Your own source code |
| What it looks for | Known CVEs, license violations | Code-level flaws (SQLi, XSS, etc.) |
| Input needed | Manifest files or compiled binaries | Source code or bytecode |
| Speed | Seconds | Minutes to hours |
| False positives | Low (matched against known CVEs) | Higher (depends on analysis depth) |
You want both. SCA checks what you imported.
SAST checks what you wrote. Together they cover the full picture of what goes into production.
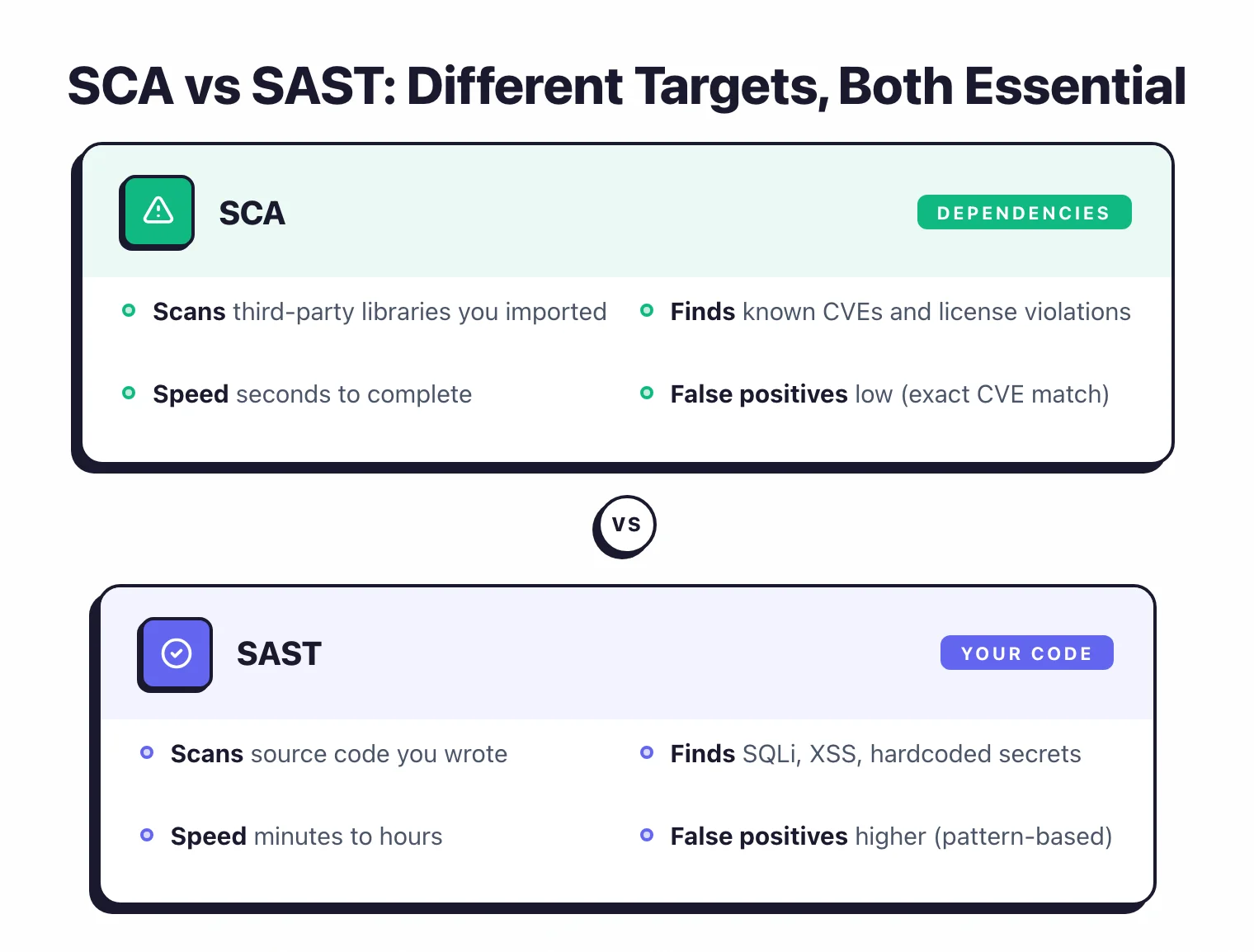
For a deeper look at how these two approaches differ, see the SAST vs SCA comparison.
For a broader comparison that includes DAST and IAST, see the SAST vs DAST vs IAST guide.
Top SCA tools to know
SCA is not a one-tool category. A short landing list covers the options most teams actually evaluate — three commercial, three open-source — with one sentence on positioning. The deeper comparisons live on the full SCA tools hub.
Commercial:
- Snyk Open Source — developer-first SCA with automated fix pull requests and a Free plan that scans unlimited public repositories.
- Black Duck — enterprise SCA with deep licence-compliance tooling and binary composition analysis for compiled artefacts.
- FOSSA — licence-compliance-first SCA with 99.8% licence detection accuracy and a centralised SBOM Portal for distribution.
Open-source:
- Trivy — all-in-one scanner that covers container images, filesystems, and IaC in a single binary (32K+ GitHub stars).
- Grype — SBOM-first vulnerability scanner from Anchore with composite CVSS + EPSS + KEV risk scoring.
- OSV-Scanner — Google’s scanner backed by the aggregated OSV.dev database, with guided remediation for npm and Maven.
For a side-by-side matrix of 30+ tools with pricing context, see the SCA tools comparison. For the free-only shortlist, the open-source SCA tools guide drills into the twelve most-used options.
Getting started
SCA is probably the easiest security tool category to adopt. Here is a practical path.
Start with a free tool. Snyk Open Source has the smoothest onboarding.
Run snyk test in your project directory and you have results in seconds. OWASP Dependency-Check is the fully free alternative.
Review the initial findings. Your first scan will probably show dozens of vulnerable dependencies.
Do not panic. Sort by severity, focus on critical and high first, check whether the affected library is actually used in a way that exposes the vulnerability.
Update what you can. Many findings are fixed by bumping a dependency version. Snyk and Mend can open auto-remediation PRs.
Review the updates before merging since version bumps can introduce breaking changes.
Add it to CI. Run the tool on every pull request.
Block merges on critical vulnerabilities. Warn on high and medium.
Set up license policies. Define which licenses your organization allows. Block any dependency with a copyleft license if you ship commercial software.
Consider SBOM generation. Add it to your release pipeline. Costs nothing and gives you an inventory you can query when the next Log4Shell drops.
FAQ
Is SCA the same as SBOM?
No. SCA is the scanning activity — resolve dependencies, match against CVE databases, report findings. An SBOM is an artefact — a structured inventory of every component in your software, typically in CycloneDX or SPDX format. Most SCA tools can produce SBOMs, and many consume them for continuous monitoring, but the two are not interchangeable terms.
Does SCA replace SAST?
No. SAST scans your own source code for code-level flaws like SQL injection and insecure deserialisation. SCA scans the third-party libraries you imported for known CVEs and licence conflicts. Most teams need both — SCA is usually the faster first win because it does not require code-path analysis.
Why do SCA tools disagree on vulnerability counts?
Two scanners running against the same code can disagree by 30-40% of findings. The differences come from the vulnerability database each tool consumes (NVD vs GHSA vs OSV vs distro feeds), the matching method (CPE-based vs ecosystem-specific), and whether reachability or VEX annotations filter the raw count. Neither output is “wrong” — they answer slightly different questions.
Is Dependabot a full SCA tool?
Partially. Dependabot reads the GitHub Advisory Database, reports vulnerable dependencies in your GitHub repositories, and opens automated fix PRs. It covers the core SCA job for GitHub-hosted projects at zero cost. It does not cover reachability analysis, custom-compiled libraries, or licence-compliance policy — teams that need those typically layer Snyk, Black Duck, or FOSSA on top.
Does SCA find malicious packages?
Most SCA tools do not. Traditional SCA matches against databases of already-reported CVEs; typosquats and compromised-maintainer releases usually have no CVE when they are published. Tools that combine SCA with behavioural analysis (Socket, Checkmarx SCA) or that consume the OpenSSF Malicious Packages feed (OSV-Scanner via OSV.dev) close that gap.

