Trivy Alternatives
Thinking of switching from Trivy? Compare top container and SCA scanning alternatives including Grype, Snyk Container, Docker Scout, Anchore Enterprise, Clair, Wiz, and Aqua Security.
- Trivy is a multi-target open-source scanner covering container images, IaC, Kubernetes, secrets, and Git repos — most alternatives specialize in one of these areas rather than replacing all of them.
- Grype is the closest open-source alternative for pure container image CVE scanning — it is fast, outputs SARIF and CycloneDX, and uses a regularly updated vulnerability database.
- Snyk Container adds base image recommendations, fix advice, and exploitability-based prioritization that Trivy's database does not provide — meaningful for teams drowning in CVE noise.
- For enterprises needing centralized vulnerability management, policy enforcement, and compliance reporting, Anchore Enterprise (commercial) or Aqua Security provide governance features the open-source tools lack.
- Wiz and Prisma Cloud go further than container image scanning — they correlate image vulnerabilities with the runtime context (is this image actually running? is the vulnerable package reachable?) to reduce noise at scale.
Trivy is one of the most widely adopted open-source security scanners in the container ecosystem. It scans container images, filesystems, Git repositories, IaC files, Kubernetes manifests, and live Kubernetes clusters — all from a single CLI tool maintained by Aqua Security.
Where Trivy lives on AppSec Santa. Trivy is a multi-domain scanner. Its tool review is canonicalised under IaC Security because of its
tfsec/config-scanning lineage and Aqua’s continued investment in the IaC side of the project. Container image scanning, dependency CVEs, and SBOM workflows still apply, and that is why this alternatives page sits under the SCA hub — most “Trivy alternatives” queries are about replacing it as a CVE/SBOM scanner. The alternatives below cover both directions.
For many teams, Trivy is the right answer. But teams looking for deeper vulnerability prioritization, managed policy enforcement, enterprise compliance reporting, or a tighter integration with commercial cloud platforms may find alternatives worth considering.
Why look for Trivy alternatives?
Trivy’s broad scanner coverage is also its main constraint: each capability is somewhat basic compared to specialized tools.
Container image scanning is solid, but Trivy does not offer base image recommendations, exploitability scoring, or fix advice beyond listing the CVE. Its IaC scanning covers common misconfigurations but has less depth than Checkov or KICS for Terraform and Bicep.
Trivy’s vulnerability database pulls from NVD, GitHub Advisory Database, and distro-specific sources and updates daily. It has no proprietary research team adding advisories ahead of NVD — unlike Snyk , which claims its database captures CVEs an average of 47 days earlier than competing sources.
For fast-moving threats, that gap matters. For SCA tools that manage application dependencies beyond container images, see the SCA tools comparison .
There is also no persistent policy layer. Each Trivy scan is stateless — there is no central server tracking findings over time, no ticket integration, no team workflow. Teams scaling beyond a few engineers typically need a tool that persists results and tracks remediation.
Finally, Trivy has no SaaS component. For teams that prefer vendor-managed updates, SLA-backed support, and a UI for non-CLI users, Trivy requires more operational investment than a commercial alternative.
Top Trivy alternatives
1. Grype
Grype from Anchore is the most direct open-source alternative to Trivy for container image vulnerability scanning. It accepts Docker images, OCI images, directory paths, and SBOMs as input and outputs findings in table, JSON, SARIF, CycloneDX, or SPDX formats .
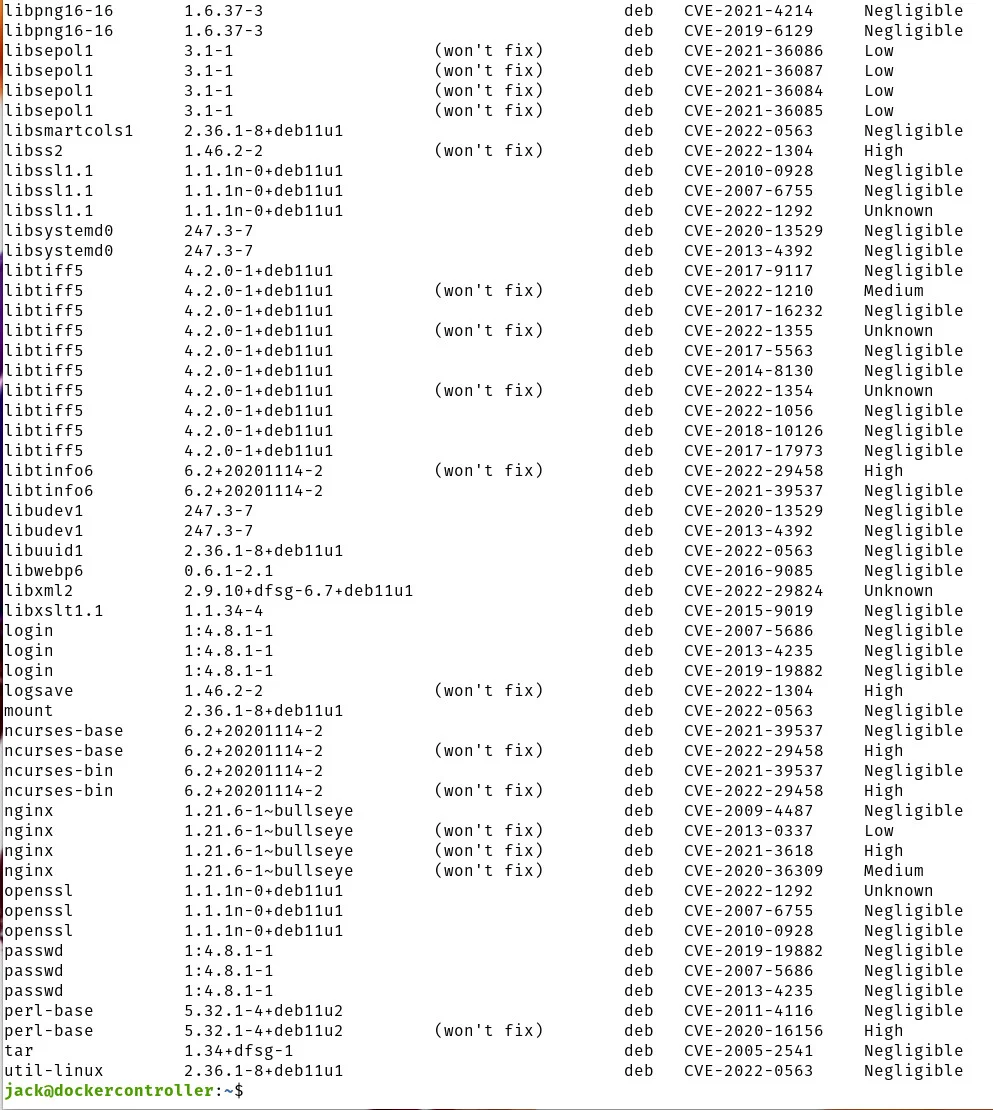
What Grype does well: Grype is purpose-built for container and filesystem vulnerability scanning — it is fast, produces clean SARIF output for GitHub Advanced Security integration, and works offline with a cached database. The Grype vulnerability database is updated daily and sourced from NVD, GitHub Advisory, Alpine SecDB, Amazon Linux, RHEL, Ubuntu, Debian, and others.
Where Grype falls short: Grype does not scan IaC files, Kubernetes manifests, or secrets — it is a pure CVE scanner. For teams replacing Trivy’s full multi-target capability, Grype covers the container image scanning slice only.
Best fit: Teams that want a fast, open-source container image scanner with clean SARIF output for CI/CD integration and prefer a focused tool over Trivy’s multi-target scope. For a direct comparison, see Trivy vs Grype .
2. Snyk Container
Snyk Container is a commercial container image security scanner with a proprietary vulnerability database and actionable fix recommendations. It integrates with Docker, CI/CD pipelines, container registries, and Kubernetes clusters.
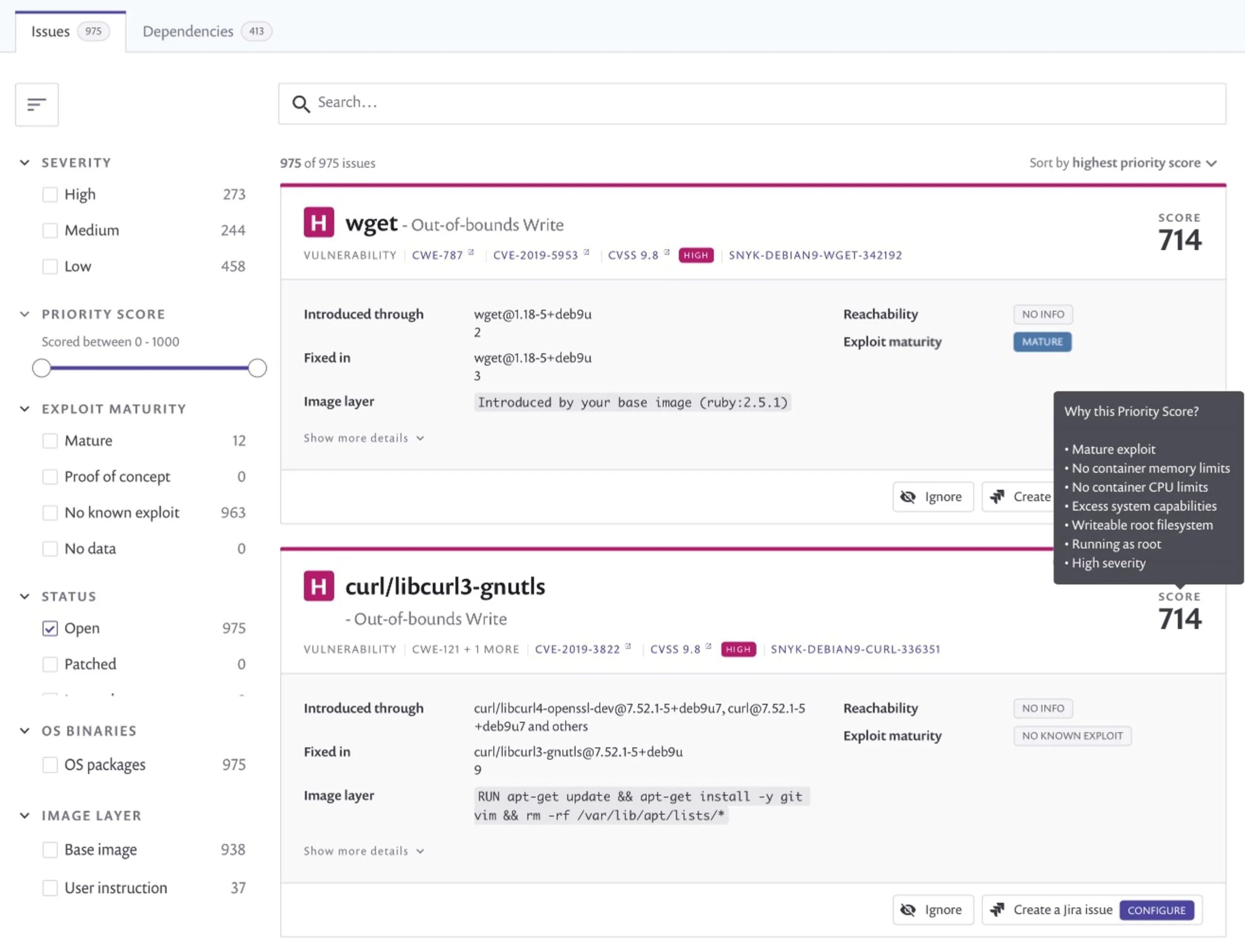
What Snyk Container does well: Fix advice is the main differentiator. Snyk Container analyzes each container image and recommends the lowest-vulnerability base image alternative — for example, suggesting node:18-alpine instead of node:18 to eliminate 80% of OS-level CVEs by switching to a minimal base. It also provides exploitability prioritization
using Snyk’s research database, filtering out CVEs with no known exploit path. The free tier includes 200 container tests per month.
Where Snyk Container falls short: It is not a multi-target scanner like Trivy — container images are its primary focus. IaC scanning and Kubernetes cluster scanning require separate Snyk products (Snyk IaC and Snyk Open Source ).
Best fit: Teams that are already using Snyk for application dependencies and want unified SCA + container scanning in one platform, or teams that need base image recommendations to meaningfully reduce their container CVE count.
3. Docker Scout
Docker Scout is Docker’s native vulnerability scanner, built into Docker Desktop, the Docker CLI, and Docker Hub. It provides real-time image analysis, SBOMs, base image comparisons, and fix recommendations directly in the Docker workflow.
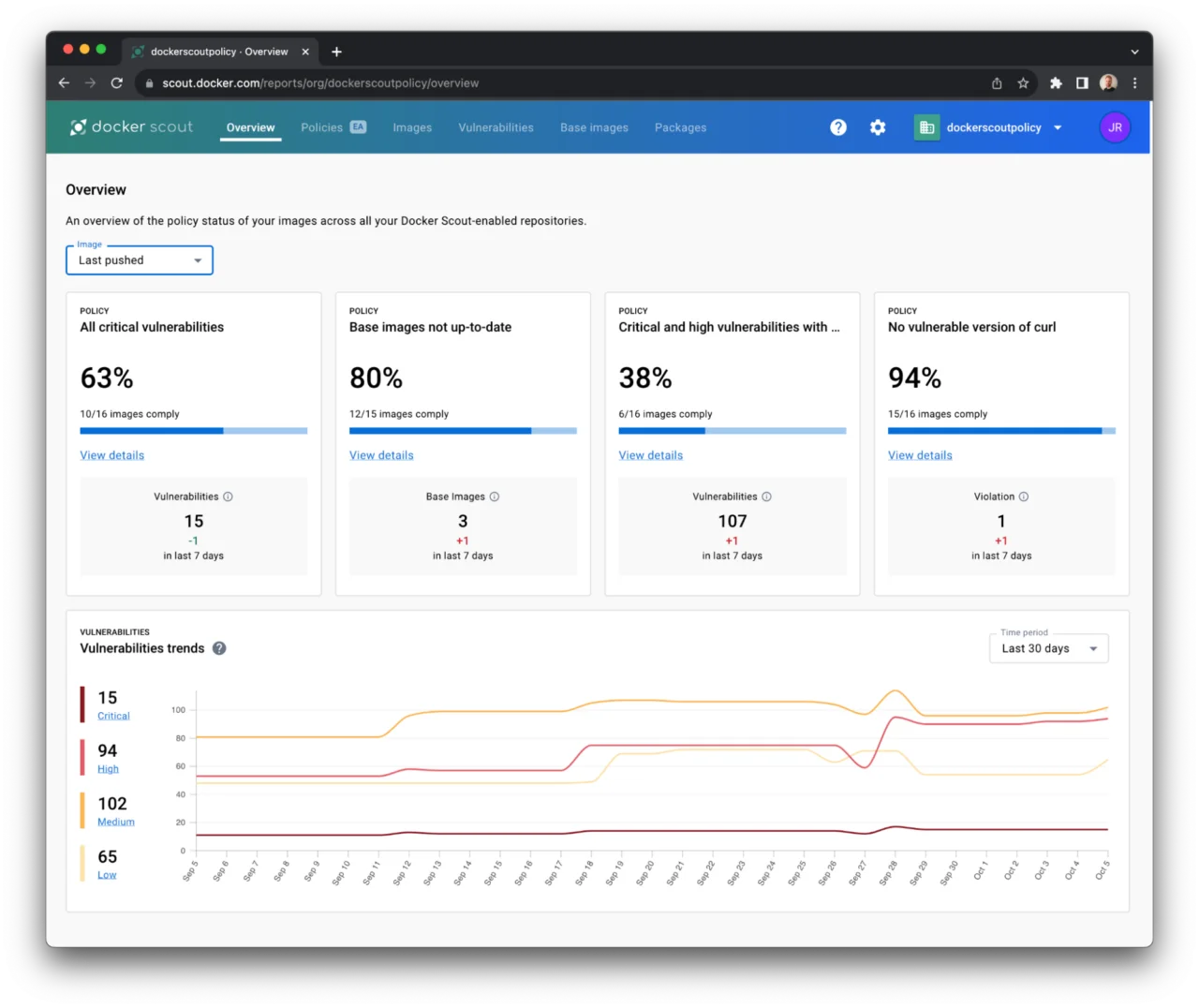
What Docker Scout does well: Zero-setup vulnerability scanning for Docker Hub users — Scout analyzes images as they’re pushed and displays findings in the Docker Hub UI and Docker Desktop interface. The docker scout cves command shows vulnerabilities with base image context, and docker scout recommendations
suggests lower-vulnerability base image alternatives. A free tier covers public repositories and a limited number of private repositories.
Where Docker Scout falls short: Scout is tightly scoped to Docker images and Docker Hub workflows. It does not scan filesystems, Git repos, IaC files, or live Kubernetes clusters. For teams using container registries other than Docker Hub (ECR, GCR, ACR), Scout integration requires additional configuration.
Best fit: Teams working primarily in Docker’s ecosystem who want vulnerability scanning integrated directly into Docker Desktop and Docker Hub without deploying a separate tool.
4. Anchore Enterprise
Anchore provides both open-source tools (Grype for CVE scanning, Syft for SBOM generation) and a commercial platform (Anchore Enterprise) for organizations that need centralized container security management.
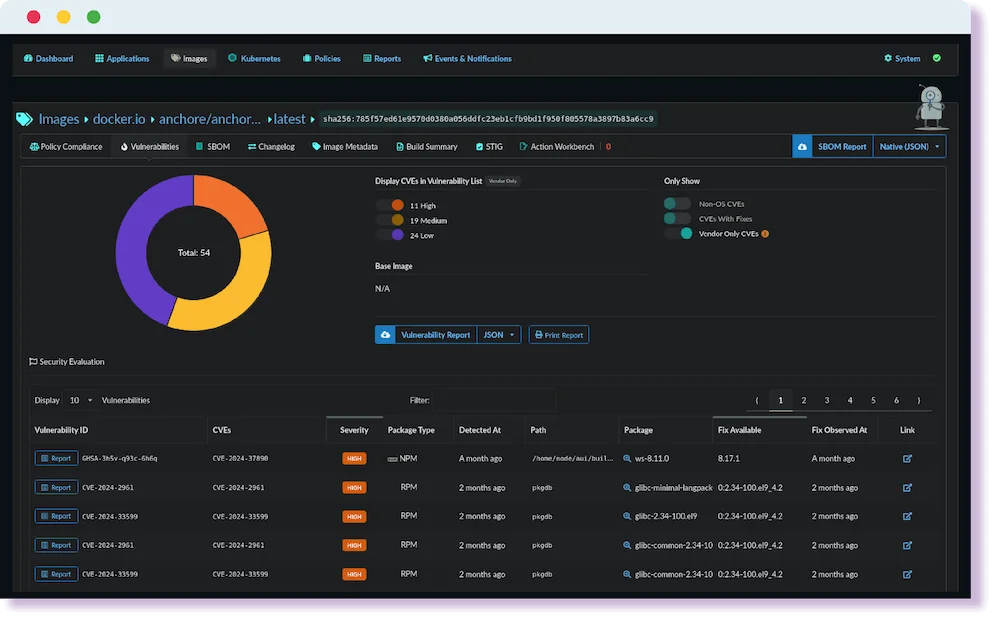
What Anchore Enterprise does well: Policy management is the key commercial differentiator. Anchore Enterprise lets security teams define admission policies — images must pass a vulnerability threshold, must have a valid SBOM, must come from approved registries, must have no critical CVEs with available fixes — and enforce them as gates in CI/CD pipelines. The enterprise platform persists scan results, integrates with Jira and ServiceNow for remediation tracking, and provides compliance reports for SOC 2 and PCI DSS. For Kubernetes-native admission policy enforcement, see Kyverno and OPA Gatekeeper .
Where Anchore Enterprise falls short: The platform is primarily a container and image security tool — it does not cover IaC scanning, Kubernetes configuration, or cloud posture management. Full multi-target coverage requires pairing Anchore with other tools.
Best fit: Organizations that need centralized container image security policy governance, audit trails, and compliance reporting — typically in regulated industries or at scale with dozens of container registries.
5. Clair
Clair is an open-source container vulnerability scanner originally developed by CoreOS (now Red Hat). It provides static analysis of container images by comparing image contents against a vulnerability database sourced from NVD, RedHat Security, Ubuntu CVE Tracker, and others.
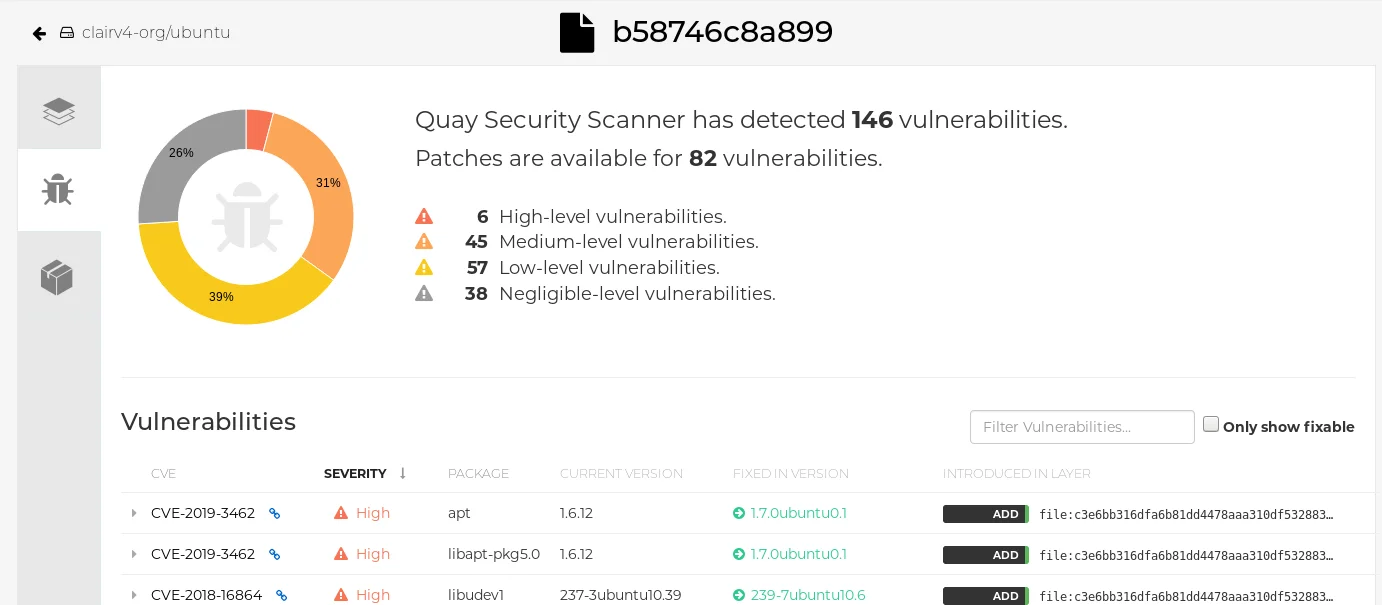
What Clair does well: Clair is designed for self-hosted container registry integration — it was built to power Quay.io’s vulnerability scanning and is commonly deployed alongside self-hosted container registries. It operates as a long-running service (unlike Trivy’s CLI model), receiving image layers via API and returning vulnerability reports. For organizations running self-hosted container registries, Clair provides registry-native vulnerability scanning.
Where Clair falls short: Clair is a narrower tool than Trivy — no IaC scanning, no Kubernetes scanning, no secrets detection. Development velocity has slowed compared to Trivy. Clair v4 is a significant architectural rewrite but adoption has not kept pace with Trivy and Grype.
Best fit: Organizations running self-hosted container registries (Quay, Harbor) that want native registry-side vulnerability scanning integrated at push time.
6. Wiz Container Scan
Wiz is a commercial CNAPP platform with container image scanning integrated into its broader cloud security posture management capability. Unlike pure container scanners, Wiz correlates image vulnerabilities with runtime context — is this image actually running? is the vulnerable package reachable? is this container exposed to the internet?
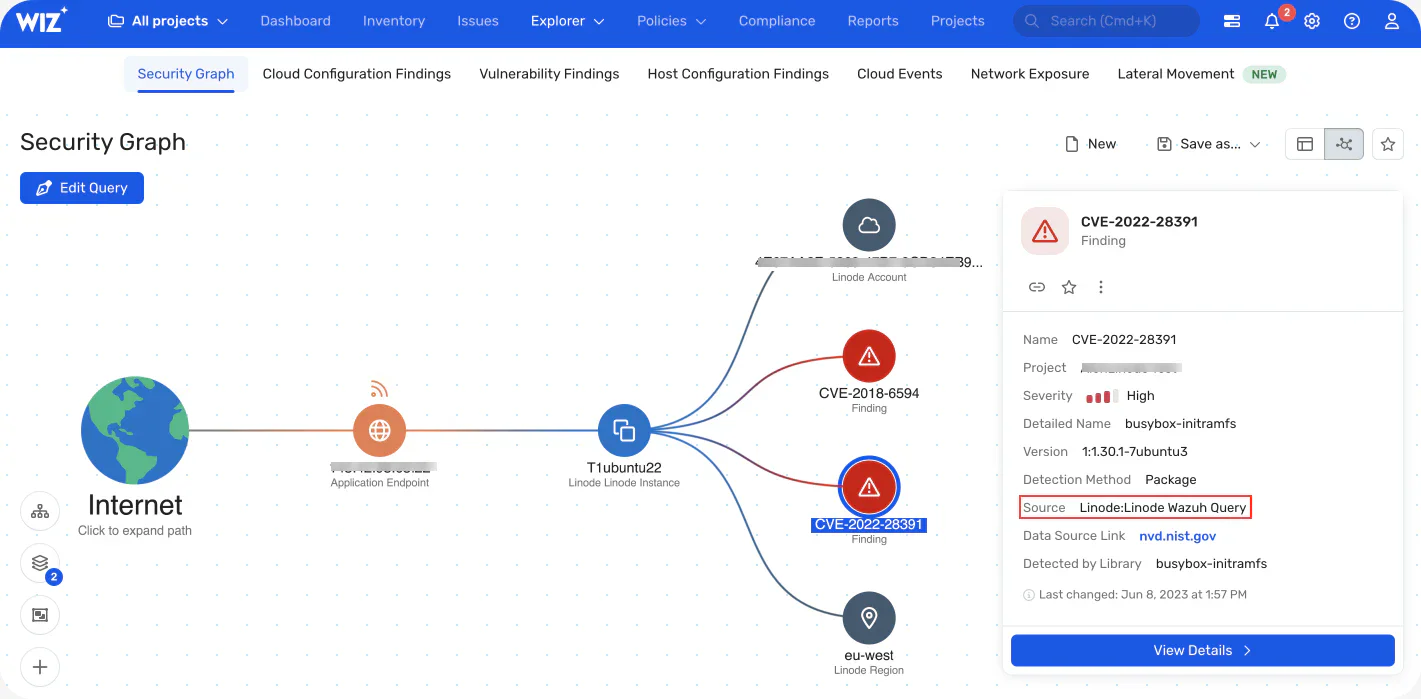
What Wiz does well: Contextual prioritization is Wiz’s core strength. A container image with 200 CVEs is overwhelming; Wiz narrows to the 3 that matter because the vulnerable package is loaded, the container is internet-exposed, and there is a known exploit. Runtime context cuts alert noise in ways static image scanners like Trivy cannot.
Where Wiz falls short: Wiz is a CNAPP platform with contact-sales pricing. For teams that only want container image scanning, Wiz’s scope and cost are overkill. Its value accrues when used across the full cloud security posture — agentless VM scanning, cloud configuration, DSPM, and container scanning together.
Best fit: Enterprises with complex multi-cloud environments where container scanning is one piece of a broader cloud security program.
7. Prisma Cloud
Prisma Cloud (Palo Alto Networks) provides container and workload security as part of its CNAPP platform, with origins in the Twistlock product. Its container security capabilities cover registry scanning, CI/CD pipeline integration, admission control, and Kubernetes runtime protection.
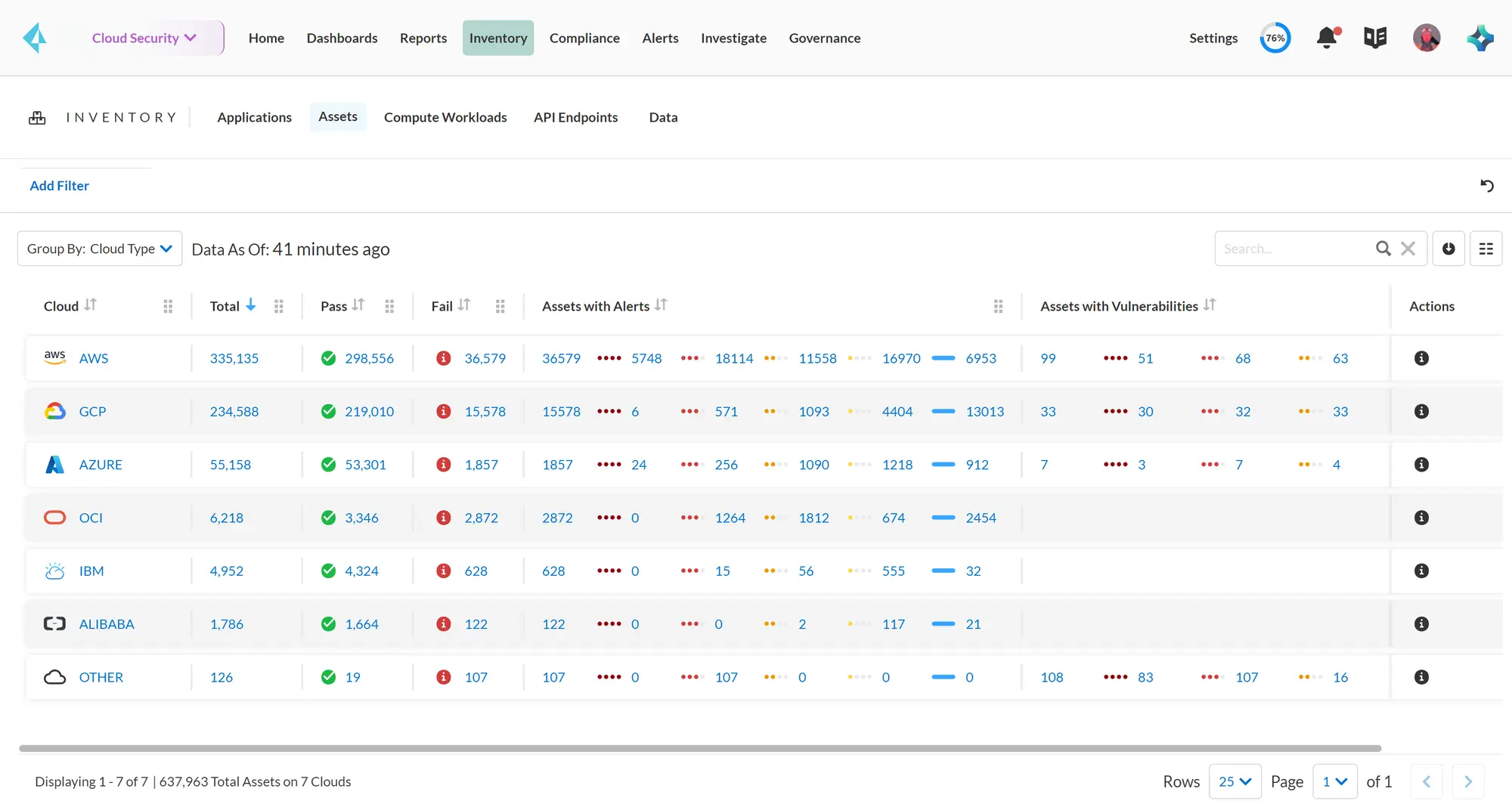
Prisma Cloud’s container scanning integrates with ACR, ECR, GCR, Docker Hub, JFrog Artifactory, and other registries. It provides vulnerability scanning, compliance checks against CIS Docker Benchmark, and secrets detection in images. The Compute module (the Twistlock heritage) adds runtime protection for containers in production — monitoring process execution, file access, and network connections.
Best fit: Enterprise organizations already using Prisma Cloud for cloud posture management that want to extend the same platform to container image scanning and runtime protection.
8. Aqua Security
Aqua Security offers a full commercial container security platform covering image scanning, admission control, runtime protection, and SBOM management. Aqua’s image scanning integrates with CI/CD pipelines, container registries, and Kubernetes clusters with policy-gated deployment workflows.
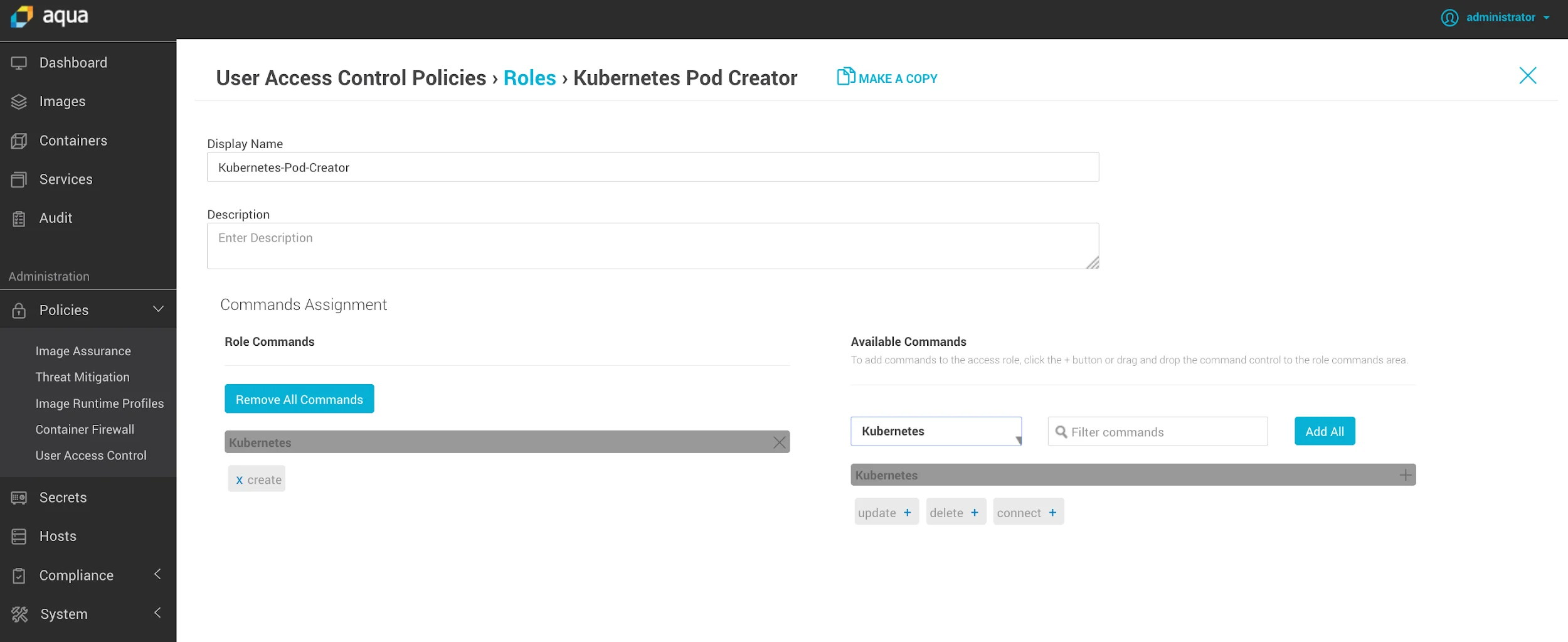
Aqua’s image assurance policies let security teams define that only images with passing scans, from approved registries, with valid Aqua certificates can be deployed to production. Runtime protection monitors container behavior using eBPF and enforces behavioral policies — blocking unexpected process execution, file access, and network connections in running containers.
Best fit: Enterprises that want a single commercial vendor for the full container security lifecycle: build-time scanning, registry policy enforcement, and runtime protection.
Comparison table
| Tool | Type | Multi-target | Base image advice | Runtime | Cost |
|---|---|---|---|---|---|
| Trivy | Multi-target scanner | Yes (images, IaC, K8s, secrets) | No | No | Open source |
| Grype | Image/filesystem scanner | No | No | No | Open source |
| Snyk Container | Image scanner | No | Yes | No | Commercial (free tier) |
| Docker Scout | Image scanner | No | Yes | No | Free (limited) |
| Anchore Enterprise | Image + policy | No | No | No | Commercial |
| Clair | Image scanner | No | No | No | Open source |
| Wiz | CNAPP | Cloud-wide | Yes (contextual) | Yes | Commercial |
| Prisma Cloud | CNAPP | Cloud-wide | No | Yes | Commercial |
| Aqua Security | Full lifecycle | Yes | Yes | Yes | Commercial |
When to stay with Trivy
Trivy remains the right choice for most teams. If you need a single open-source tool that scans container images, IaC files, Kubernetes clusters, Git repositories, and detects secrets — with no external dependencies and no API keys — Trivy is the only tool that covers all of these without cost or vendor lock-in.
Teams at smaller scale, those with open-source commitments, or those who need offline scanning in air-gapped environments should default to Trivy . The multi-target coverage means you get more value per installed tool than any pure container scanner. For a comparison of Trivy against specific tools, see Trivy vs Grype , Trivy vs Snyk Container , and Checkov vs Trivy .
The cases where alternatives win are: base image recommendations (Snyk Container, Docker Scout), centralized policy governance at scale (Anchore Enterprise, Aqua), or full cloud posture correlation that turns 200 container CVEs into 3 actionable ones (Wiz, Prisma Cloud).
FAQ
Frequently Asked Questions
What is the best free alternative to Trivy for container scanning?
Is Snyk Container better than Trivy?
What is the difference between Trivy and Grype?
Does Docker Scout replace Trivy?
Is Anchore Enterprise open source?

Founder, AppSec Santa
Years in application security. Reviews and compares 215 AppSec tools across 12 categories to help teams pick the right solution. More about me →






