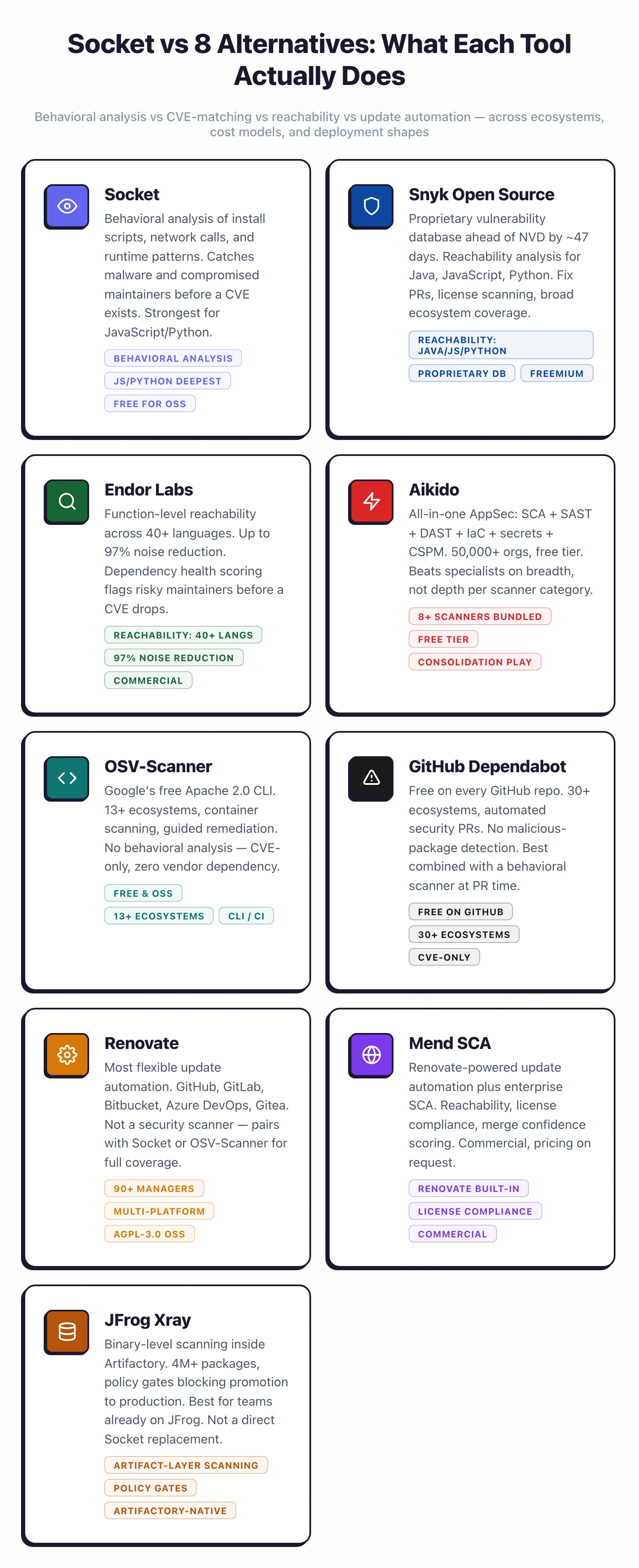
Socket Alternatives: 8 Best SCA Tools for Supply-Chain Security in 2026
Looking for Socket alternatives? Compare Snyk, Endor Labs, Aikido, Renovate, OSV-Scanner, and more for supply-chain security across every ecosystem.
- Socket focuses on behavioral analysis of packages to catch malware, typosquatting, and compromised maintainers — threats that CVE-based scanners miss entirely.
- Snyk Open Source adds a proprietary vulnerability database that Snyk says catches CVEs an average of 47 days before NVD, plus reachability analysis for Java, JavaScript, and Python.
- Endor Labs reports up to 97% noise reduction (92% average across customers) with function-level reachability across 40+ languages — the most aggressive prioritization on this list.
- OSV-Scanner is Google's free CLI backed by the OSV.dev database, covering containers and 13+ ecosystems without behavioral analysis.
- Aikido bundles SCA with SAST, DAST, IaC, and secrets in one platform, used by 50,000+ organizations, and is the stronger pick when you want consolidation instead of a specialist.
The best Socket alternatives in 2026 are Snyk Open Source, Endor Labs, Aikido, and OSV-Scanner — each covering more languages, deeper CVE analysis, or broader AppSec scope than Socket’s supply-chain-attack-focused approach.
Why Look for Socket Alternatives?
Socket is the go-to tool for catching supply-chain attacks before they merge — but it is not a general-purpose SCA platform.
Socket built its reputation on a clever pivot. Instead of matching dependencies against CVE databases like most SCA tools do, it inspects what packages actually do during install and at runtime. Install scripts, network calls, filesystem writes, and shell execution all feed into Socket’s risk analysis. That approach catches malicious packages, typosquatting, and compromised maintainer accounts — threats that no advisory database can flag in time.
For npm and JavaScript teams, Socket is one of the strongest supply-chain security tools on the market.
The tradeoffs show up once you step outside that niche. Socket’s deepest behavioral analysis is built around the JavaScript ecosystem, with lighter coverage for other languages. If your stack is Java, Go, .NET, or Ruby-heavy, you get less value per dollar than a JavaScript shop would. Teams running polyglot codebases often need a second tool to handle JVM or Go dependencies well.
Socket also plays a narrower role than full SCA platforms. It does not offer reachability analysis — tracing whether a vulnerable function is actually called from your code — the way Snyk, Endor Labs, or Mend use the term. It does not scan container images, IaC files, or source code.
Cost and complexity add up fast
Running Socket plus a CVE-based SCA tool plus a container scanner plus an IaC scanner can easily mean four separate vendor relationships, four alert queues, and four renewal conversations. For teams trying to cut tool sprawl, that picture is the primary reason to look at alternatives.
The third pressure point is consolidation. Many engineering orgs in 2026 are cutting tool count and looking for platforms that merge SCA with SAST, DAST, IaC, and secrets detection. Socket does one thing well. If the broader trend in your company is fewer vendors, Aikido or Snyk Enterprise may fit the budget conversation better than adding Socket to an already long list.
Top Socket Alternatives
1. Snyk Open Source
Snyk Open Source is the most common Socket alternative I see teams consider. It scans dependencies against Snyk’s proprietary vulnerability database, opens automated fix pull requests, and continuously monitors projects for newly disclosed issues. It works across GitHub, GitLab, Bitbucket, Azure DevOps, and any CI/CD system through the CLI.
The main differentiator is database depth. According to Snyk, its research team documents CVEs an average of 47 days before they show up in NVD or the GitHub Advisory Database. That is a self-reported figure, but the underlying logic is consistent: Snyk’s security research team actively discovers and documents vulnerabilities rather than waiting for public disclosure.
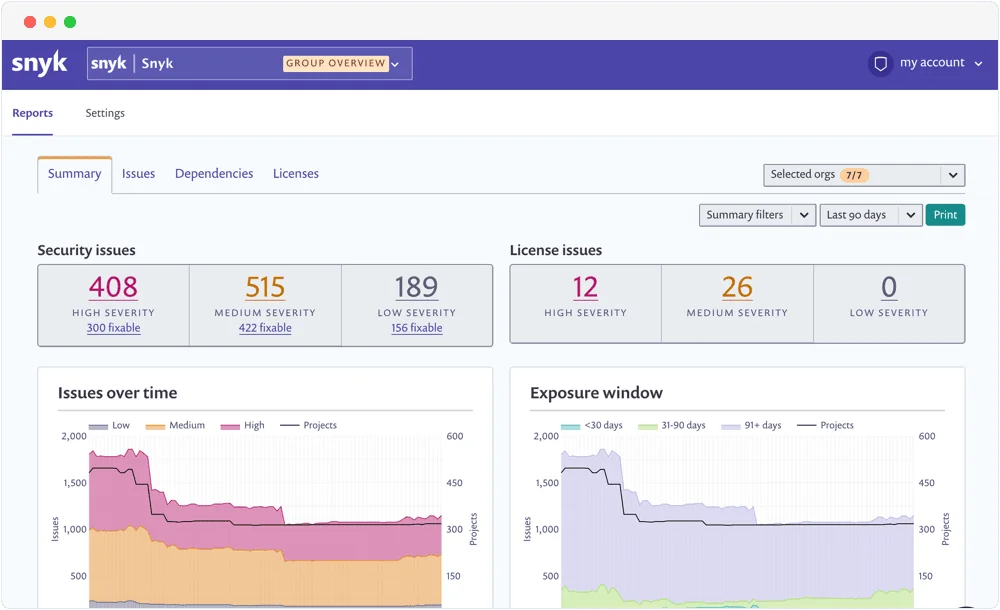
Snyk also offers reachability analysis for Java, JavaScript, and Python, which filters out alerts for vulnerabilities in functions your application never calls. That is a different type of signal than Socket’s behavioral analysis. Where Socket catches “this package is doing something weird at install time,” Snyk tells you “this CVE actually affects a function your code calls.”
Snyk’s free tier caps at 200 tests per month, which is plenty for individuals or small teams but tight at scale. Paid plans add license compliance, container scanning, and enterprise controls.
Key Insight
Snyk's proprietary database is the product, not the scanner. The ~47-day NVD lead time (Snyk's own figure) means your team gets fix PRs for critical CVEs weeks before most free scanners even know the advisory exists.
Compared to Socket’s open-source-is-free model, Snyk is more expensive but also broader.
Best for: Teams that want a mature SCA platform with proprietary CVE data and reachability across multiple Git platforms. License: Freemium Key difference: Proprietary database Snyk says catches CVEs ~47 days ahead of NVD. Reachability analysis for Java, JavaScript, and Python. Covers far more ecosystems than Socket’s deepest behavioral coverage.
2. Endor Labs
Endor Labs approaches the same problem from the prioritization angle. Most SCA tools, Socket included, will surface risky packages; Endor Labs wants to show you only the ones that matter.
The platform performs function-level reachability analysis across 40+ languages. Endor Labs reports up to 97% noise reduction (92% average across customers, with individual accounts like Zebra Technologies hitting that upper figure) — if a vulnerable function in a transitive dependency is never called from your code, the alert gets deprioritized. These are Endor Labs’ own figures, but the mechanism — call-graph tracing rather than package-level matching — is sound and well-documented.
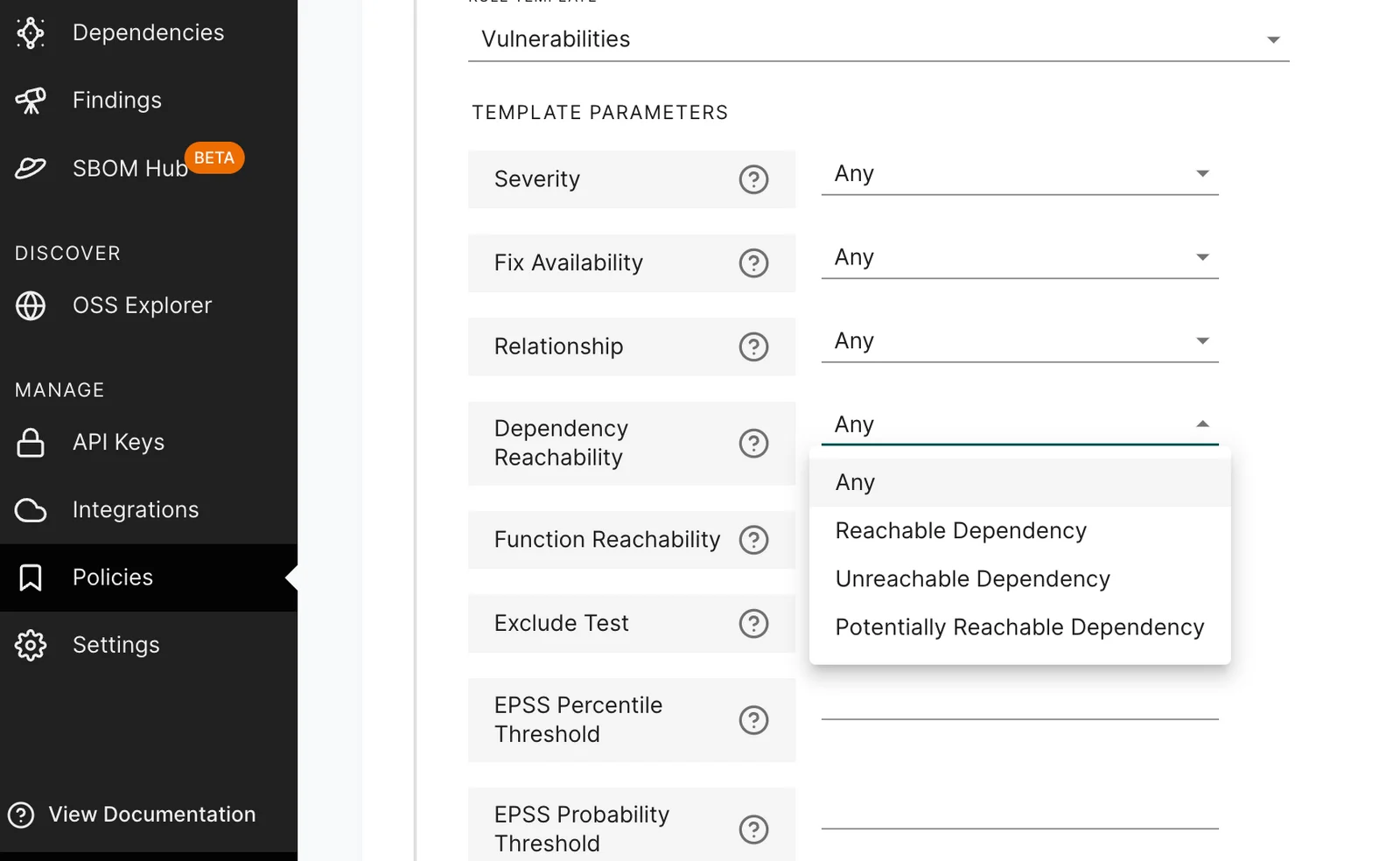
Endor also scores dependency health by tracking maintenance activity, release cadence, contributor patterns, and community engagement. A package whose sole maintainer went quiet two years ago gets flagged as a risk even before a CVE is published. That overlaps conceptually with what Socket does — catching risk before an advisory exists — but through a different lens.
Endor Labs is commercial and aimed at mid-to-large engineering organizations. There is no published pricing; expect a sales conversation.
Key Insight
The value proposition is clearest for teams drowning in alerts and spending real engineering hours on triage. If that is your Socket experience today — flagging too many packages that never pose actual risk — Endor Labs is designed to cut the queue.
Best for: Teams with 40+ language footprints that need aggressive alert prioritization and dependency health signals. License: Commercial Key difference: Function-level reachability across 40+ languages with up to 97% noise reduction (Endor Labs’ reported figure). Dependency health scoring catches risky packages before CVEs appear.
3. Aikido
Aikido takes a completely different shape from Socket. It is an all-in-one AppSec platform bundling SCA, SAST, DAST, IaC scanning, container scanning, secrets detection, and CSPM into one product.
As of 2026, Aikido is used by 50,000+ organizations across 70+ countries, with the company closing a $60M Series B at a $1B valuation in January 2026.
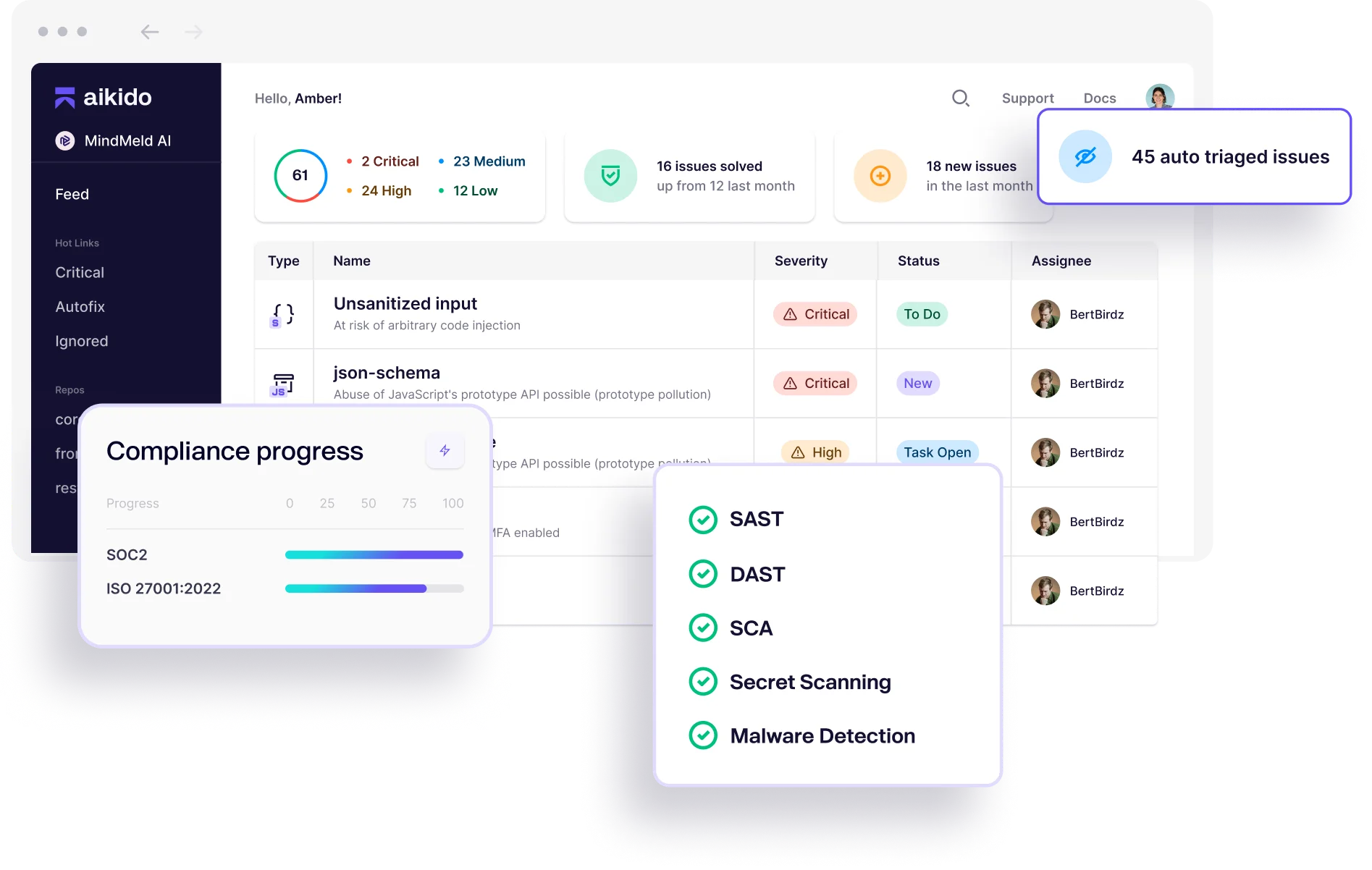
The SCA piece covers CVE matching, license analysis, and some malicious package detection. It is not as deep as Socket’s behavioral analysis, and it is not as tuned as Endor Labs on reachability. What Aikido does well is coverage: if your current stack is Socket plus a SAST tool plus an IaC scanner plus secrets scanning from different vendors, Aikido can replace several of them at once.
AutoTriage is Aikido’s noise-reduction feature, and the company reports around 95% noise reduction across the combined scanner set. A specialist like Socket, Semgrep, or Endor Labs will beat Aikido on its home turf — but Aikido is rarely competing on that axis. It competes on consolidation and budget.
Best for: Small-to-mid teams consolidating SCA, SAST, IaC, and secrets into one tool with one bill. License: Commercial (free tier available) Key difference: Bundles 8+ security scanners in one platform. Free tier covers real usage, not just trials.
4. OSV-Scanner
OSV-Scanner is Google’s free CLI that scans dependencies and containers against the OSV.dev database. It is Apache 2.0 open-source, self-hosted, and has no commercial tier. If you want Socket’s free-for-OSS feel without any vendor dependency, OSV-Scanner is the closest match.
Coverage is broad: 13+ ecosystems including npm, PyPI, Go, Maven, Cargo, RubyGems, and Debian/Alpine container packages. OSV.dev aggregates advisories from GitHub Security Advisories, PyPA, RustSec, the Go vulnerability database, and others into a normalized format.
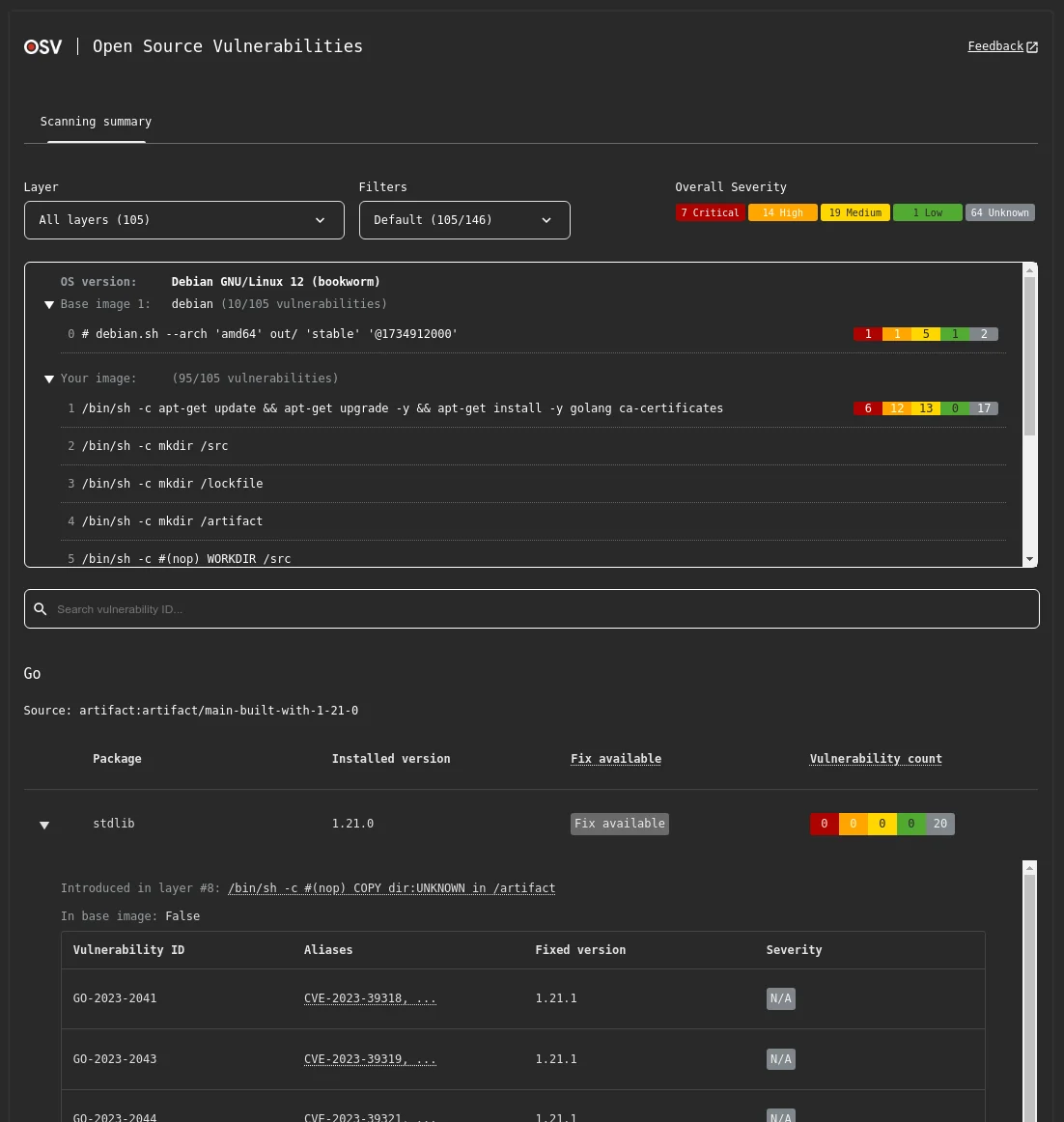
Version 2 added guided remediation suggestions and layer-aware container scanning. OSV-Scanner does not do behavioral analysis, malicious package detection, or reachability — it is a CVE scanner first. It will not tell you that an npm package is exfiltrating environment variables on install, only that the version you have has a known CVE.
For teams that want to eliminate commercial SCA spend entirely and accept the CVE-only scope, OSV-Scanner is the strongest free option. Many teams pair it with Renovate for automated updates.
Pro tip: OSV-Scanner + Renovate is a powerful free stack
Pairing OSV-Scanner for CVE detection with Renovate for automated fix PRs gives you most of what paid tools offer at the mechanical level — zero cost, no vendor lock-in, and both tools integrate cleanly into GitHub Actions.
Best for: Cost-sensitive teams or open-source projects that want credible CVE coverage with zero vendor lock-in. License: Open-source (Apache 2.0) Key difference: Google-backed OSV.dev database, free forever, 13+ ecosystems, CLI and container scanning. No behavioral analysis.
5. GitHub Dependabot
GitHub Dependabot is not a direct Socket alternative — the two solve different problems — but they are often considered together. Dependabot is free on every GitHub repository, with no usage limits, covering 30+ package ecosystems.
It matches dependencies against the GitHub Advisory Database and opens automated pull requests for security and version updates.
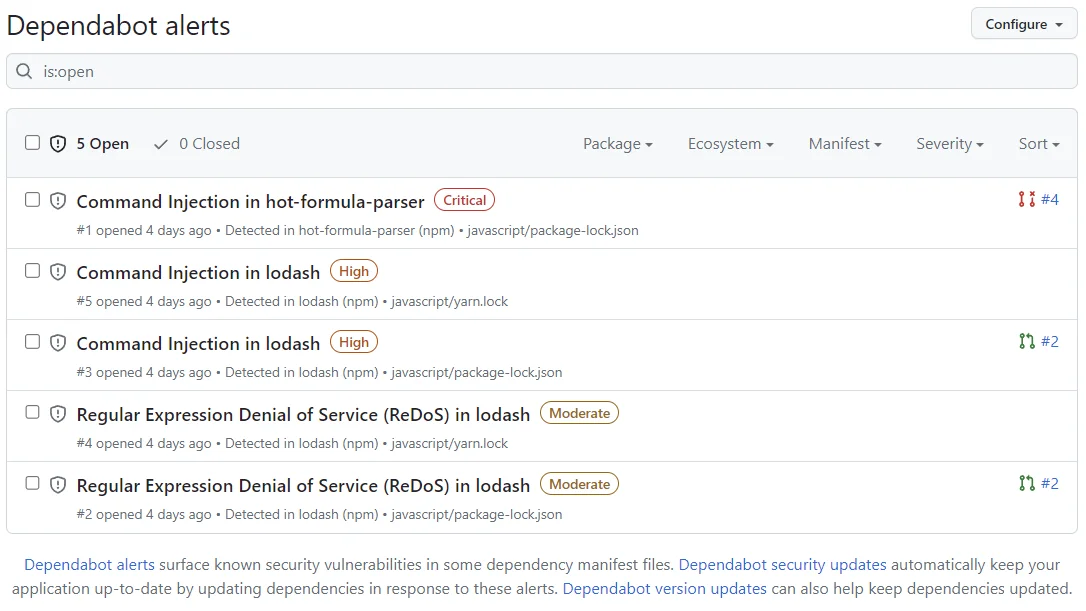
The gap compared to Socket is clear. Dependabot has very limited malicious package detection — it flags packages covered by GitHub Advisory Database entries but does no behavioral analysis of install scripts or network patterns. Compromised maintainer scenarios and typosquatting attacks routinely slip past Dependabot until someone files an advisory.
For GitHub-only teams on a zero budget, Dependabot handles the mechanical parts of dependency management well. Many teams run Dependabot for automated updates and pair it with Socket or another tool for supply-chain security review at PR time. That pairing is common enough that Socket advertises GitHub App integration specifically for this workflow.
Best for: GitHub-only teams that need free automated dependency updates and can add a second tool for malware detection. License: Free (GitHub-native) Key difference: Unlimited free usage on GitHub. 30+ ecosystems. No behavioral analysis; CVE-based only.
6. Renovate
Renovate is Dependabot’s older, more configurable cousin and the most popular multi-platform update bot. It is AGPL-3.0 open-source and runs on GitHub, GitLab, Bitbucket, Azure DevOps, Gitea, and Forgejo. Mend maintains the project and offers a free hosted app.
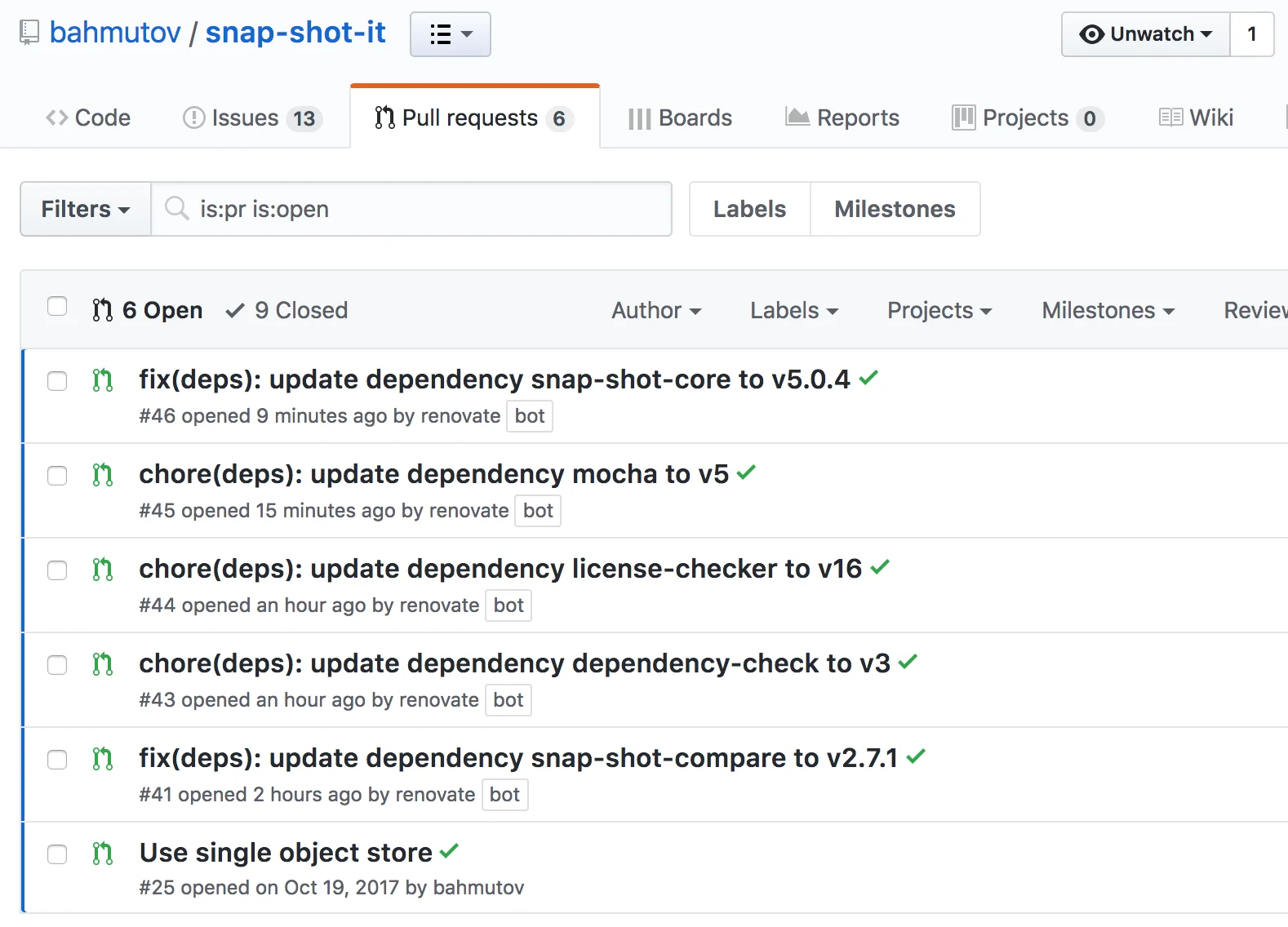
Compared to Socket, Renovate is not a security tool first — it is an update automation tool with no behavioral analysis or malicious package detection. What it offers instead is far deeper configuration: regex managers for custom file formats, shared presets across organizations, grouped updates, automerge for trusted packages, and scheduling rules per dependency type.
Teams that care about PR hygiene pick Renovate. Teams focused on supply-chain attacks pair it with Socket, OSV-Scanner, or a dedicated SCA platform. The combination of Renovate plus Socket is a common setup for npm-heavy teams, especially since both tools integrate well into the same GitHub App ecosystem.
Best for: Multi-platform teams that want granular control over dependency updates and will layer a security tool on top. License: Open-source (AGPL-3.0) Key difference: Most flexible update automation available. Not a security scanner on its own.
7. Mend SCA
Mend SCA (formerly WhiteSource) is built on Renovate’s technology for automated updates and layers enterprise security features on top. The platform covers GitHub, GitLab, Bitbucket, Azure DevOps, and all major CI/CD systems. It is a commercial product targeting mid-to-large engineering organizations.
The main Socket-overlap angle is malicious package detection. Mend added supply-chain attack detection to its platform and feeds threat intel into its advisory database.
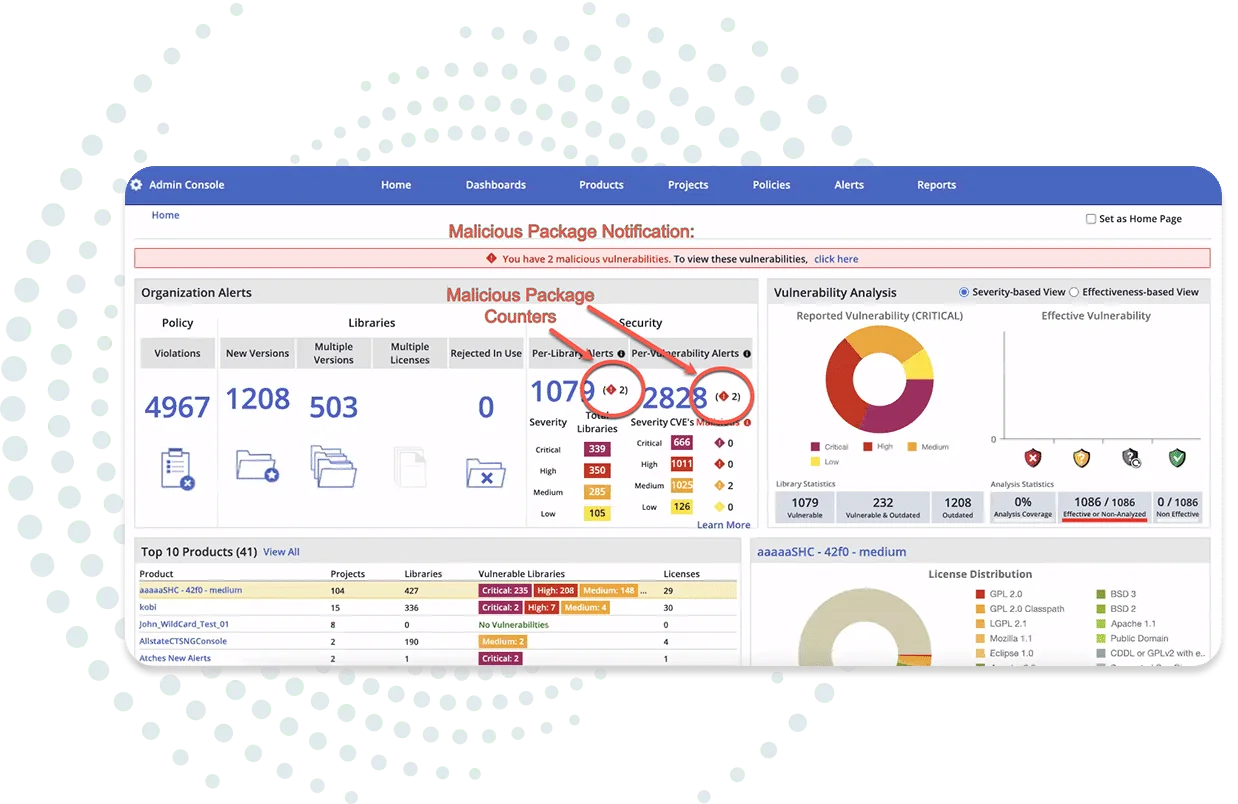
The depth is not at Socket’s level for behavioral analysis, but Mend covers it alongside CVE scanning, reachability analysis, license compliance, and merge confidence scoring — a signal that shows how likely an update is to break your build based on data from other repositories. For teams that already want Renovate’s update automation plus enterprise SCA features plus license management in one tool, Mend is a natural fit.
Pricing is enterprise-oriented and not published publicly. If you are choosing between Mend and Socket, the question is whether you want one deep specialist (Socket) or one broad platform with Renovate built in (Mend).
Best for: Enterprise teams that want Renovate’s update automation bundled with reachability, license compliance, and some malware detection. License: Commercial Key difference: Built on Renovate. Merge confidence scoring and license compliance. Multi-platform support with SaaS-first deployment.
8. JFrog Xray
JFrog Xray scans compiled artifacts in JFrog Artifactory rather than source-level manifests — a fundamentally different angle from Socket, which analyzes packages at the source and install-script level. Xray performs deep recursive analysis of container images, binaries, and packages, maintaining a vulnerability database covering over 4 million open-source packages.
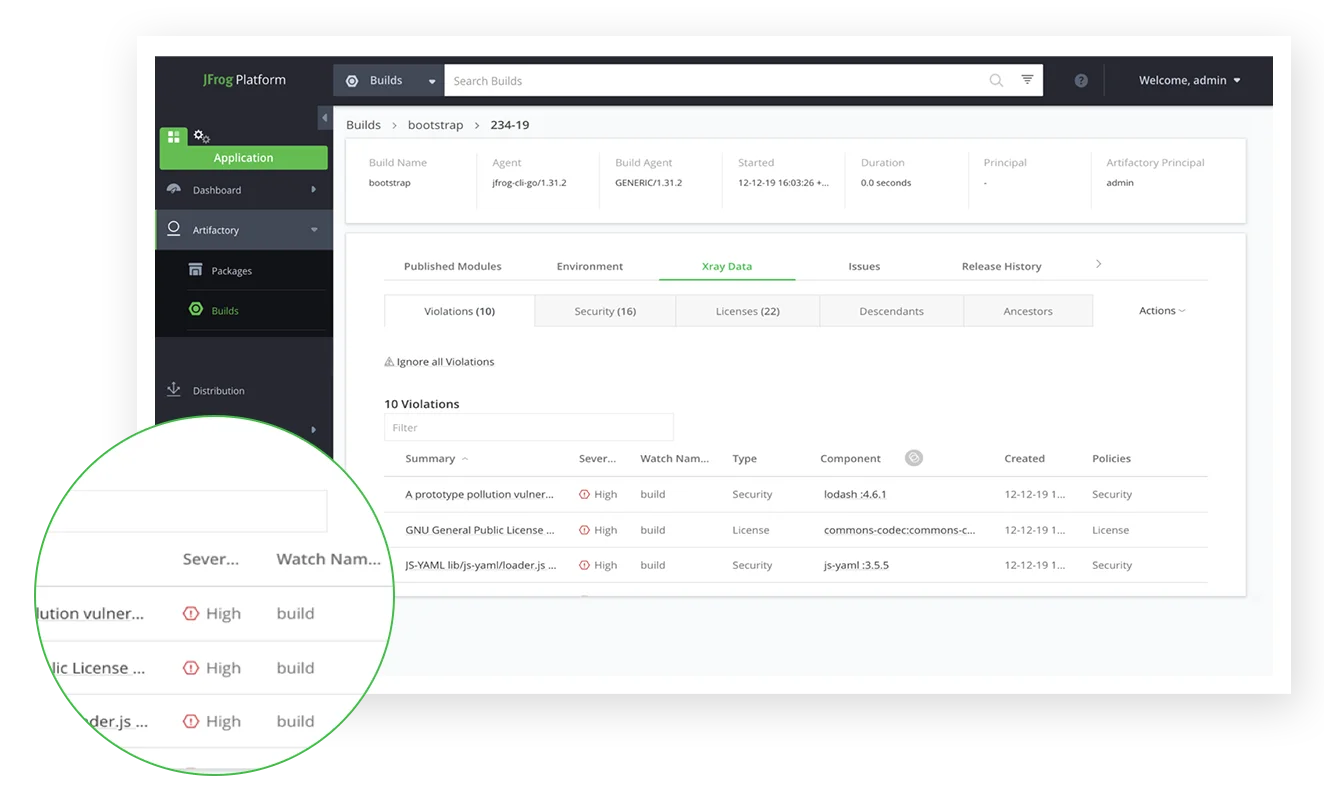
Impact analysis traces how a vulnerable component propagates through your artifact repository, and policy gates can block vulnerable artifacts from being promoted to production registries. For organizations already running Artifactory as their artifact hub, Xray is the natural SCA layer to add — scanning happens automatically as artifacts are uploaded, with no separate CI/CD step.
Xray is not a malware-first tool like Socket, but it does flag known malicious packages from its intelligence feed. The real value is the artifact-repository integration and the ability to enforce security policies at the binary layer — the actual layer you deploy from. Adopting Xray without Artifactory does not make sense; the whole JFrog stack is a significant commitment, with commercial pricing that requires a sales conversation.
Best for: Teams already standardized on JFrog Artifactory that want SCA enforcement at the artifact layer. License: Commercial Key difference: Binary-level scanning of compiled artifacts. Policy gates in Artifactory. Not a direct Socket replacement, but a different layer of the same supply-chain defense.
Feature Comparison
| Feature | Socket | Snyk | Endor Labs | Aikido | OSV-Scanner | Dependabot | Renovate | Mend SCA | JFrog Xray |
|---|---|---|---|---|---|---|---|---|---|
| License | Commercial (free OSS) | Freemium | Commercial | Commercial (free tier) | Open-source | Free | Open-source | Commercial | Commercial |
| Malicious package detection | Core feature | Limited | Adjacent (health scoring) | Some | No | Very limited | No | Some | Some |
| Reachability analysis | No | Java/JS/Python | Yes (40+ languages) | Limited | No | No | No | Yes | No |
| Auto fix PRs | Flags in PR | Yes | Yes | Yes | Guided remediation | Yes | Yes | Yes | Yes |
| Platforms | GitHub, GitLab | Multi-platform | Multi-platform | Multi-platform | CLI / CI | GitHub only | Multi-platform | Multi-platform | Artifactory-based |
| Ecosystems | 10+ (JS/Python deepest) | Broad | 40+ languages | Broad | 13+ | 30+ | 90+ managers | Broad | 4M+ packages |
| Container scanning | No | Yes | Yes | Yes | Yes | Dep graph only | Docker ecosystem | Yes | Core feature |
| License compliance | Basic | Paid plans | Yes | Yes | No | No | No | Yes | Yes |
| SAST / DAST / IaC bundled | No | Partial | No | Yes (full suite) | No | No | No | Partial | No |
| Vuln database | Behavioral + OSV | Proprietary | Multiple + health | Multiple | OSV.dev | GitHub Advisory DB | Host platform | Multiple | JFrog DB (4M+) |
When to Stay with Socket
Socket is still the right call in several scenarios:
- Your stack is npm, Yarn, or pnpm-heavy. Socket’s deepest behavioral analysis is built around the JavaScript ecosystem. If most of your risk is in a
package.json, no CVE-only tool matches what Socket catches. - You specifically care about supply-chain attacks. Typosquatting, dependency confusion, and compromised maintainer pushes all bypass CVE databases by definition. Socket’s install-script and network-behavior analysis is one of the few tools aimed directly at these threats.
- You have an existing CVE-based SCA and just need the malware layer. Pairing Socket with Dependabot, OSV-Scanner, or Snyk is a common, clean setup. Each tool owns a different slice of the problem.
- You publish open-source software. Socket is free for open-source projects with full behavioral analysis, which is a strong value proposition that most commercial competitors do not match.
- PR-time blocking is your key workflow. Socket’s GitHub App integration flags risky dependency changes on the pull request before they merge — exactly where supply-chain attacks want to slip in.
For broader coverage, browse the SCA tools category or compare against Dependabot if your current starting point is GitHub-native.
Frequently Asked Questions
What is the best Socket alternative for teams outside npm and JavaScript?
Is Socket just for malicious package detection?
Is there a free Socket alternative?
Does Socket publish pricing?
Can I run Socket alongside another SCA tool?

Founder, AppSec Santa
Years in application security. Reviews and compares 209 AppSec tools across 11 categories to help teams pick the right solution. More about me →