- Snyk is the developer-first AppSec platform: SAST (Snyk Code), SCA (Snyk Open Source), IaC (Snyk IaC), and Container (Snyk Container) all share one dashboard. Wiz is the agentless CNAPP, with CSPM, container security, IaC, and ASPM rolled into one cloud-side platform.
- Snyk starts at the code (PR feedback in IDE and CI). Wiz starts at the cloud (snapshot-based scanning of running workloads). The two platforms meet in the middle on container scanning and IaC, where they overlap most.
- Snyk's container scanning runs in the build pipeline (image scanning) and in the registry. Wiz's container scanning runs against the deployed image in the cluster, with runtime context the build-time scan does not have.
- Wiz pioneered the agentless CSPM model: snapshot the cloud account, build a security graph, surface lateral-movement paths. Snyk's IaC + cloud posture is newer and shallower than Wiz's purpose-built CNAPP. Wiz became a Google Cloud company in March 2026.
- Most enterprises run both. Snyk handles AppSec from PR through container build; Wiz handles cloud posture from deployed workload through runtime context. The overlap on IaC and container is where teams pick which tool owns each phase.
Snyk vs Wiz: Which Is Better?
Snyk vs Wiz in one line: Snyk is code-first AppSec; Wiz is cloud-first CNAPP. Pick Snyk for SAST, SCA, IaC, and container build scanning with PR feedback. Pick Wiz for CSPM, runtime container scanning, and code-to-cloud attack paths — most enterprises run both.
The frame matters. Snyk is the AppSec platform, built around developer feedback in the IDE and PR. It covers SAST (Snyk Code), SCA (Snyk Open Source), IaC (Snyk IaC), and Container (Snyk Container).
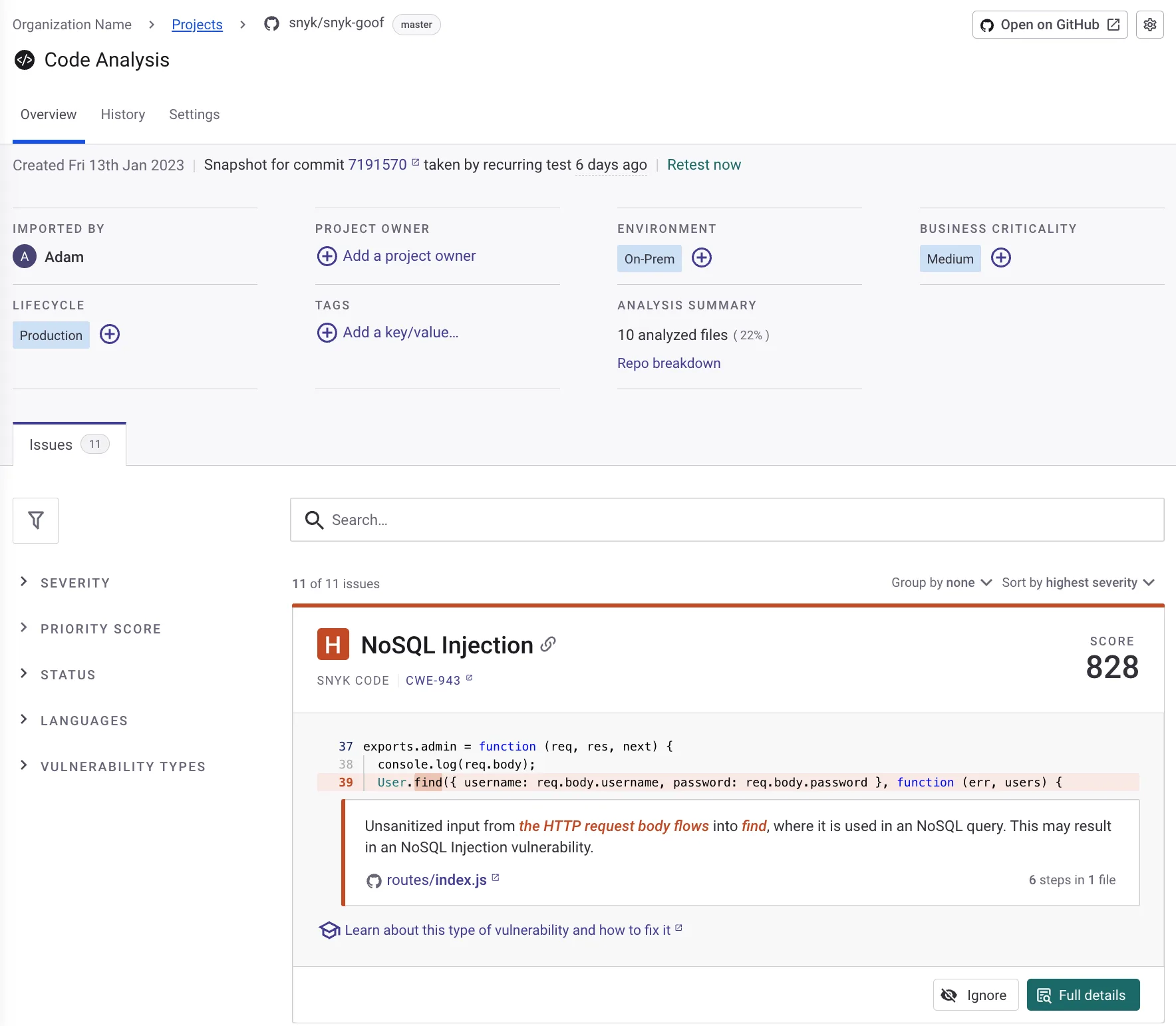 Snyk Code traces an NoSQL Injection from
Snyk Code traces an NoSQL Injection from req.body through User.find and pins it to a single line in the repo.
The mental model is left-of-deploy: catch issues in the code before they ship.
Wiz is the cloud security platform, built around agentless snapshot scanning of deployed workloads. It covers CSPM, CIEM, container runtime, IaC, and DSPM. (Wiz became a Google Cloud company in March 2026.)
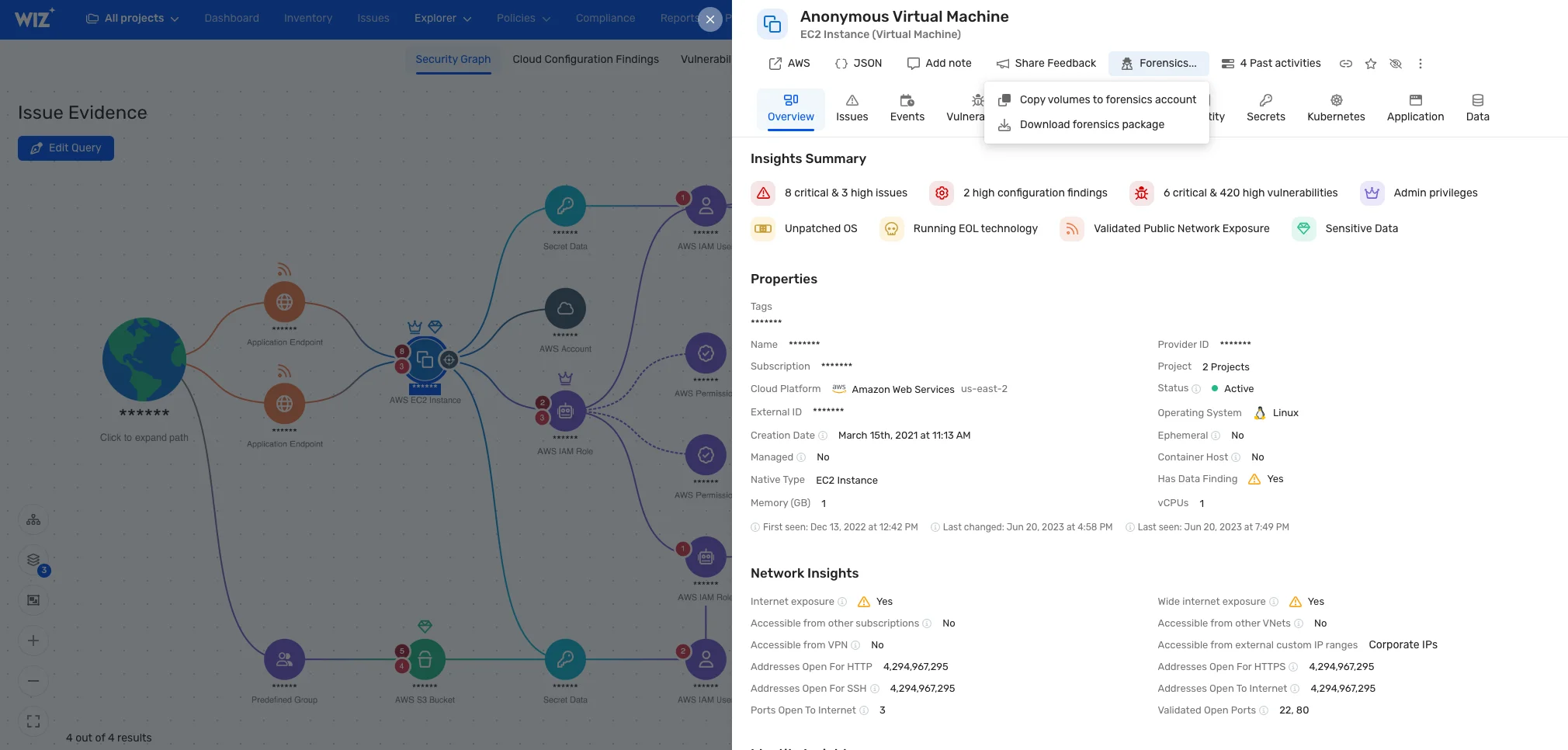 The Wiz Security Graph traces an EC2 instance’s exposure path through IAM, S3, and open ports — risk seen from the cloud, not the code.
The Wiz Security Graph traces an EC2 instance’s exposure path through IAM, S3, and open ports — risk seen from the cloud, not the code.
The mental model is right-of-deploy: see the cloud as it actually runs and trace risk paths through the security graph.
The platforms meet in the middle on container scanning and IaC, where Snyk scans at build time and Wiz scans at runtime. Picking one means losing depth on either the code side or the cloud side. Most enterprises pick both and let each one own its phase.
Key Differences
| Dimension | Snyk | Wiz |
|---|---|---|
| Primary lens | Code-first AppSec | Cloud-first CNAPP |
| Where it lives | PR / IDE / CI / registry | Deployed cloud accounts and clusters |
| SAST | Snyk Code (DeepCode AI engine) | Wiz Code (newer, code-to-cloud focused) |
| SCA | Snyk Open Source (17 languages, multi-ecosystem) | Via Wiz Code dependency scanning |
| IaC | Snyk IaC (Terraform, CloudFormation, Kubernetes) | Wiz IaC scanning + cloud posture cross-reference |
| Container | Snyk Container (build-time and registry) | Wiz Container (runtime, deployed image scanning) |
| Cloud posture | Limited | Wiz CSPM, CIEM, DSPM, attack-path graph |
| Pricing | Public per-developer pricing | Enterprise sales only |
| Best for | Developer-first AppSec from PR onwards | Cloud-first security with code-to-cloud context |
Head-to-Head
Platform philosophy
Snyk is developer-first. The product team lives close to the IDE and PR cycle, and every Snyk product ships with IDE plugins for VS Code, IntelliJ, Cursor, and Windsurf.
The pitch is: developers see security issues while writing code and fix them before they ever reach a security team.
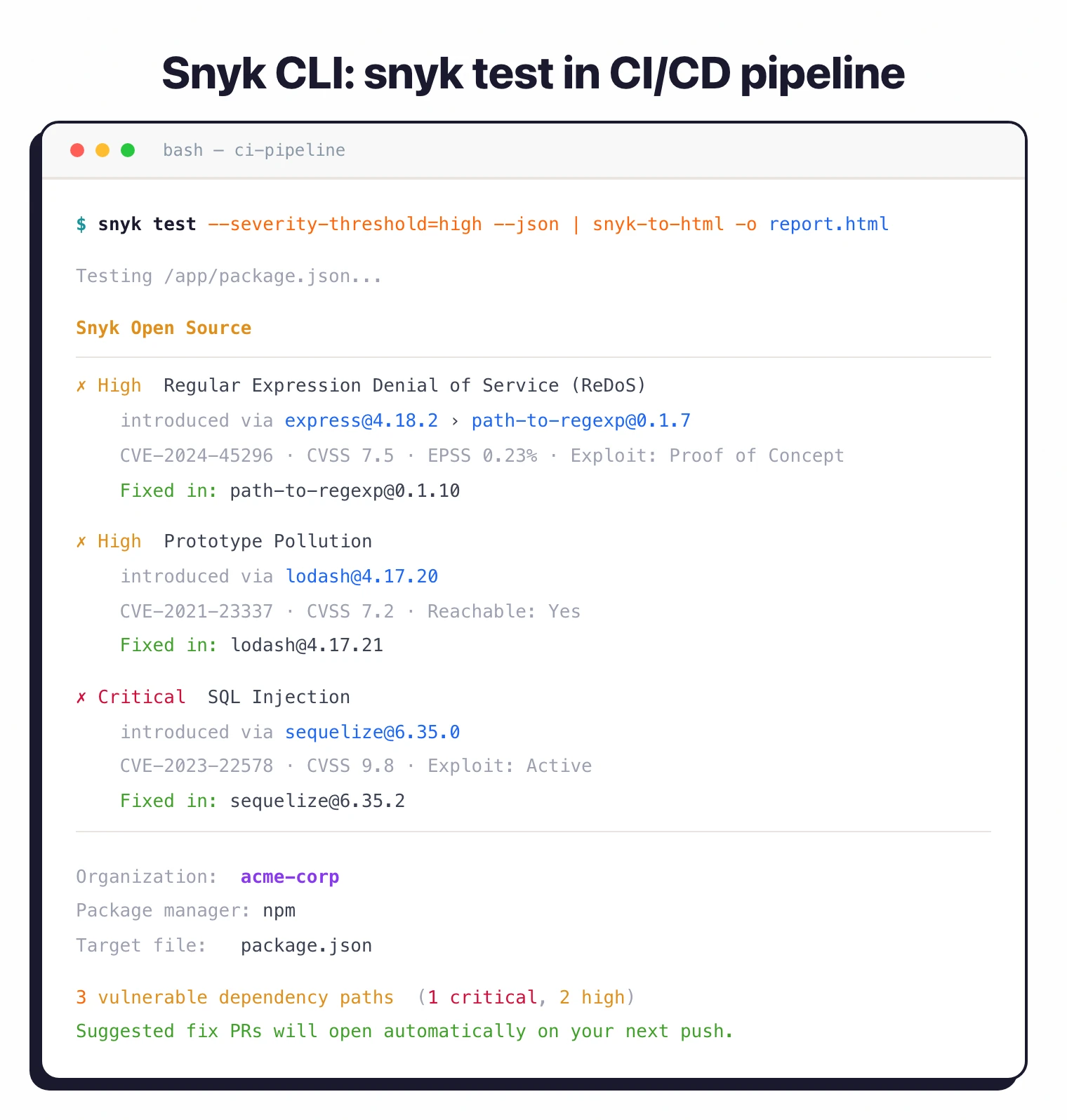 Snyk’s primary surface is the CI/PR.
Snyk’s primary surface is the CI/PR. snyk test runs in the pipeline and posts fixable findings before merge.
Wiz is cloud-first. The platform was built around agentless CSPM: snapshot the cloud account, build a Security Graph of every workload, network connection, identity, and exposed surface, then trace lateral movement paths.
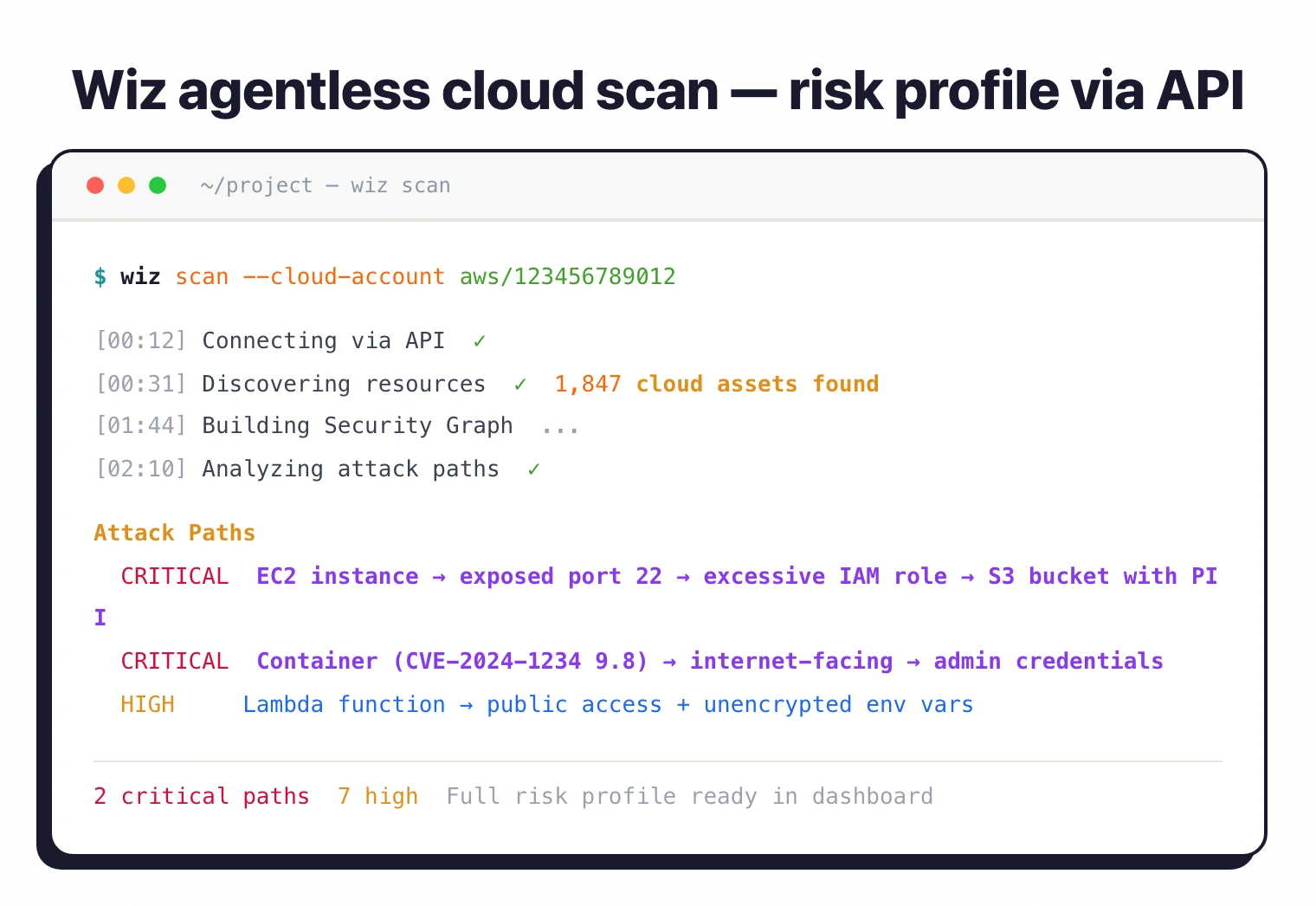 Agentless scan: Wiz snapshots the cloud account via API, builds a graph of 1,847 assets, and reports the lateral-movement paths that actually chain together.
Agentless scan: Wiz snapshots the cloud account via API, builds a graph of 1,847 assets, and reports the lateral-movement paths that actually chain together.
The pitch is: see your cloud the way an attacker would and prioritise what’s actually exploitable.
The two philosophies are not contradictory; they are complementary. The friction shows up only when budgets force a choice.
SAST and SCA
Snyk Code is built on the DeepCode AI engine that Snyk acquired in September 2020. It supports 14 languages, runs in the IDE and CI, and has years more product maturity than Wiz Code.
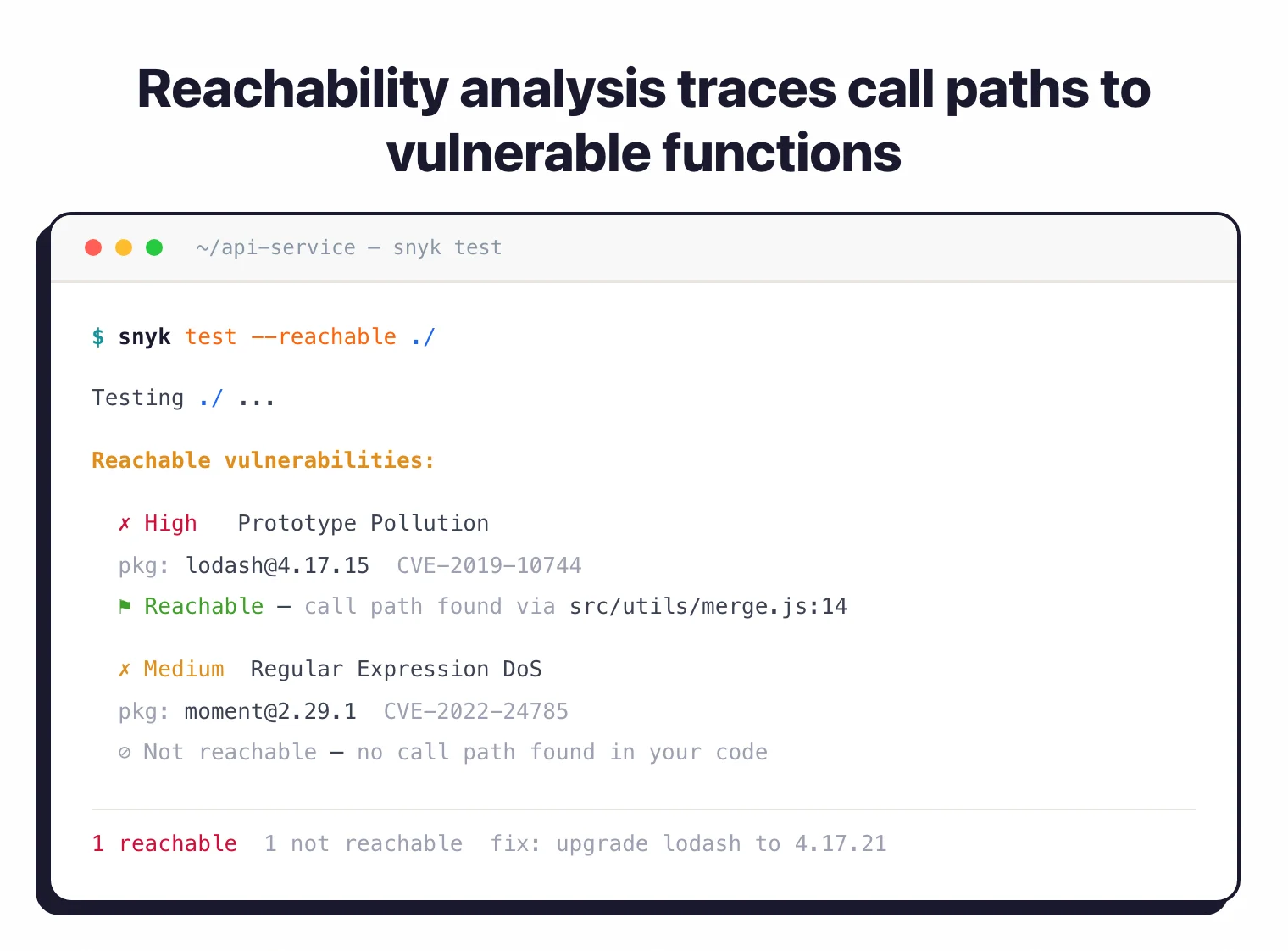 Snyk’s
Snyk’s --reachable flag prioritises the SCA findings whose vulnerable function actually appears in the call graph — a depth Wiz Code does not match today.
Wiz Code is newer. It covers SAST, secrets, and IaC scanning, and the differentiator is graph-context: each finding is mapped back to a deployed service via the Wiz Security Graph. The SAST depth is not yet at Snyk Code’s level, but the cloud-context wrapper is unique to Wiz.
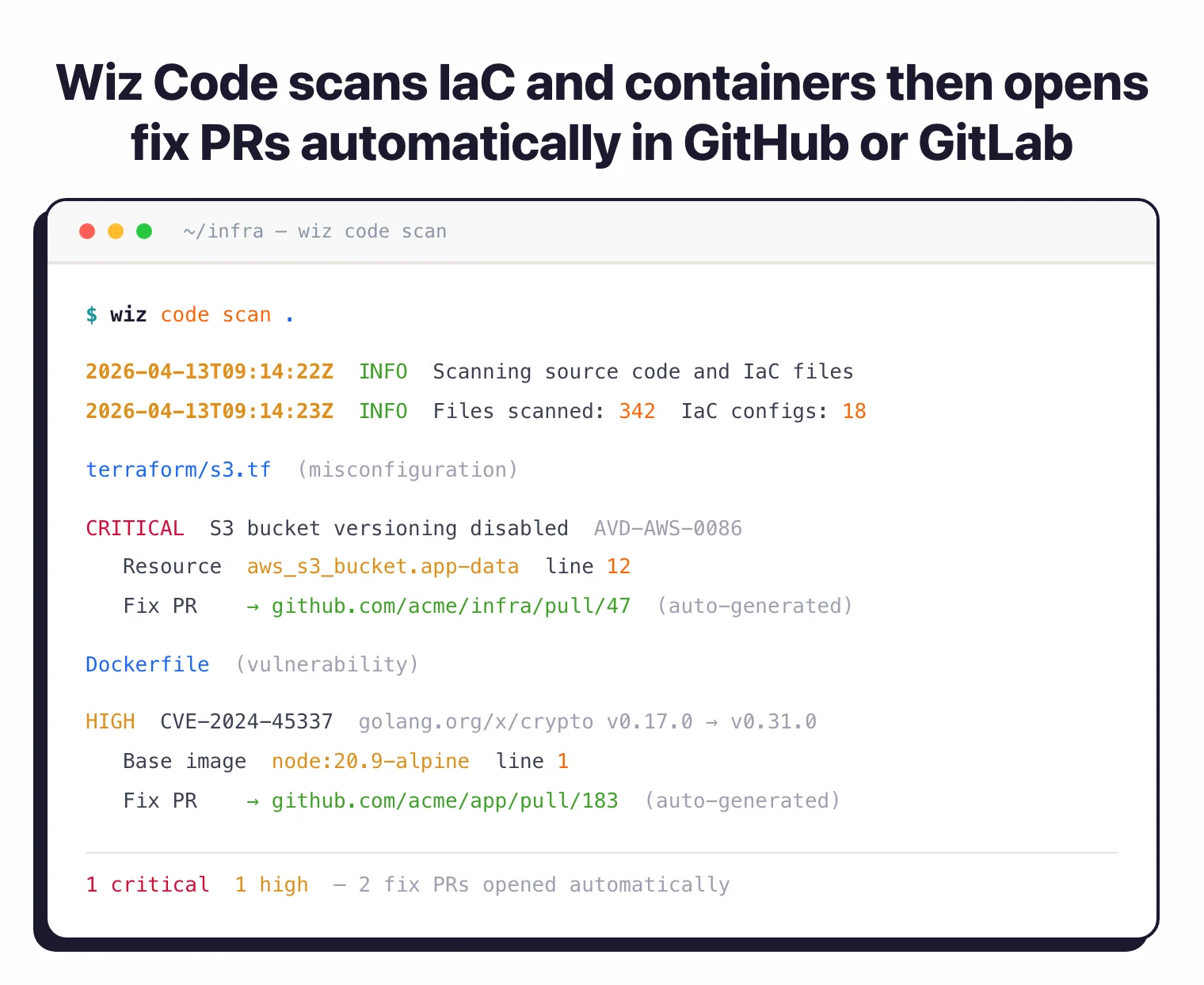 Wiz Code overlaps Snyk on IaC and dependency scanning, but ties each finding back to the deployed runtime via the Security Graph.
Wiz Code overlaps Snyk on IaC and dependency scanning, but ties each finding back to the deployed runtime via the Security Graph.
For pure SAST and SCA depth, Snyk wins today. For SAST findings tied to runtime exposure, Wiz Code is the more interesting product.
Container security
Snyk Container scans container images at build time and in the registry. It finds base-image and library vulnerabilities before deployment, and integrates with Docker Build, ECR, ACR, GCR, and Quay.
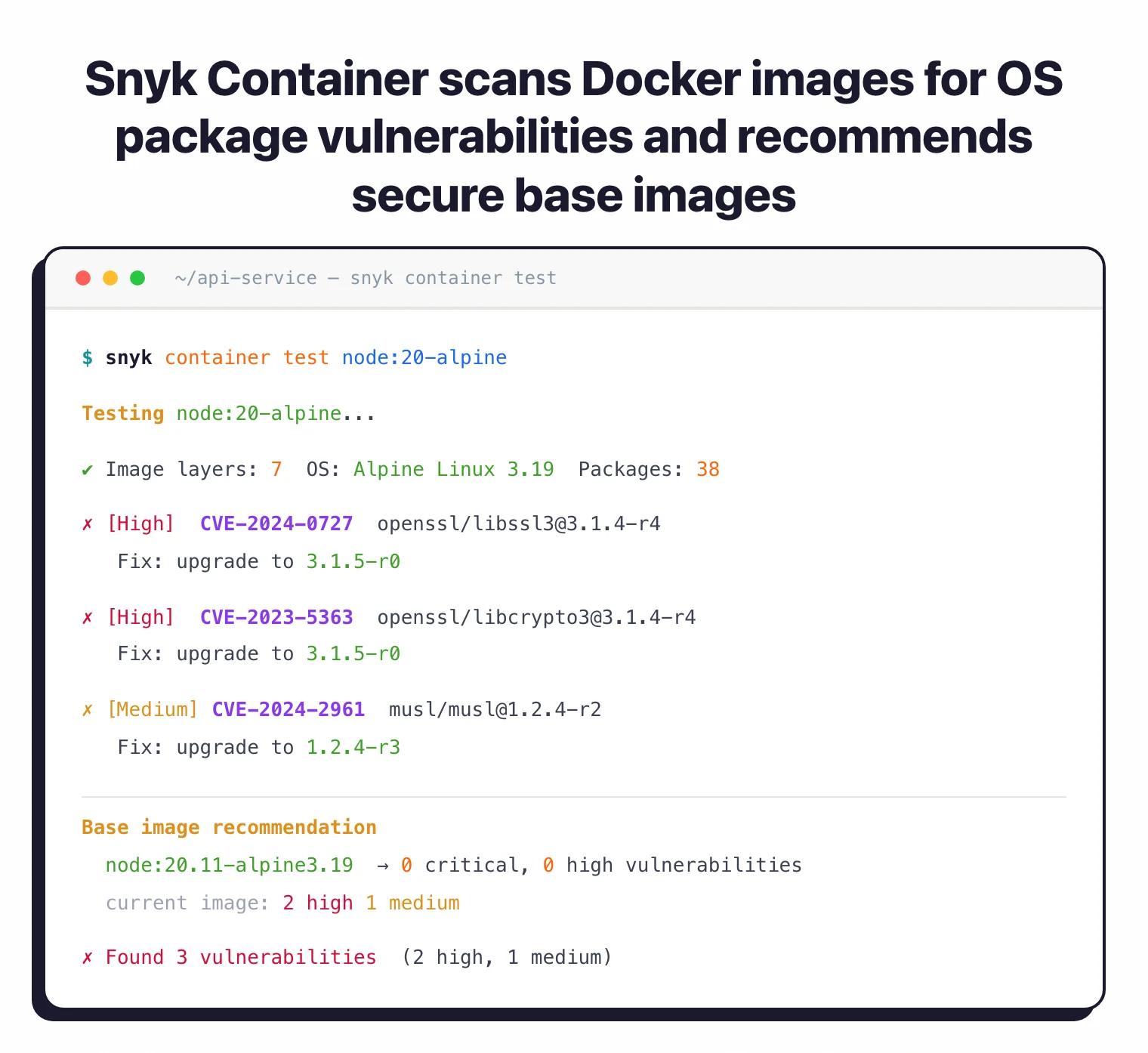
snyk container test node:20-alpine runs at build time, surfaces OS-package CVEs with fix versions, and recommends a cleaner base image.
Wiz Container scans deployed images in the cluster, with runtime context attached. The Wiz Security Graph shows which images are running in which workloads, which workloads are exposed to the internet, and which container vulnerabilities are reachable from public surfaces.
Both are useful. The common pairing is Snyk for build-time prevention and Wiz for runtime detection plus prioritisation.
IaC and cloud posture
Snyk IaC scans Terraform, CloudFormation, and Kubernetes manifests for misconfigurations. The scan runs in CI before deployment, surfacing issues like overly permissive S3 buckets, unencrypted RDS instances, and missing Kubernetes resource limits.
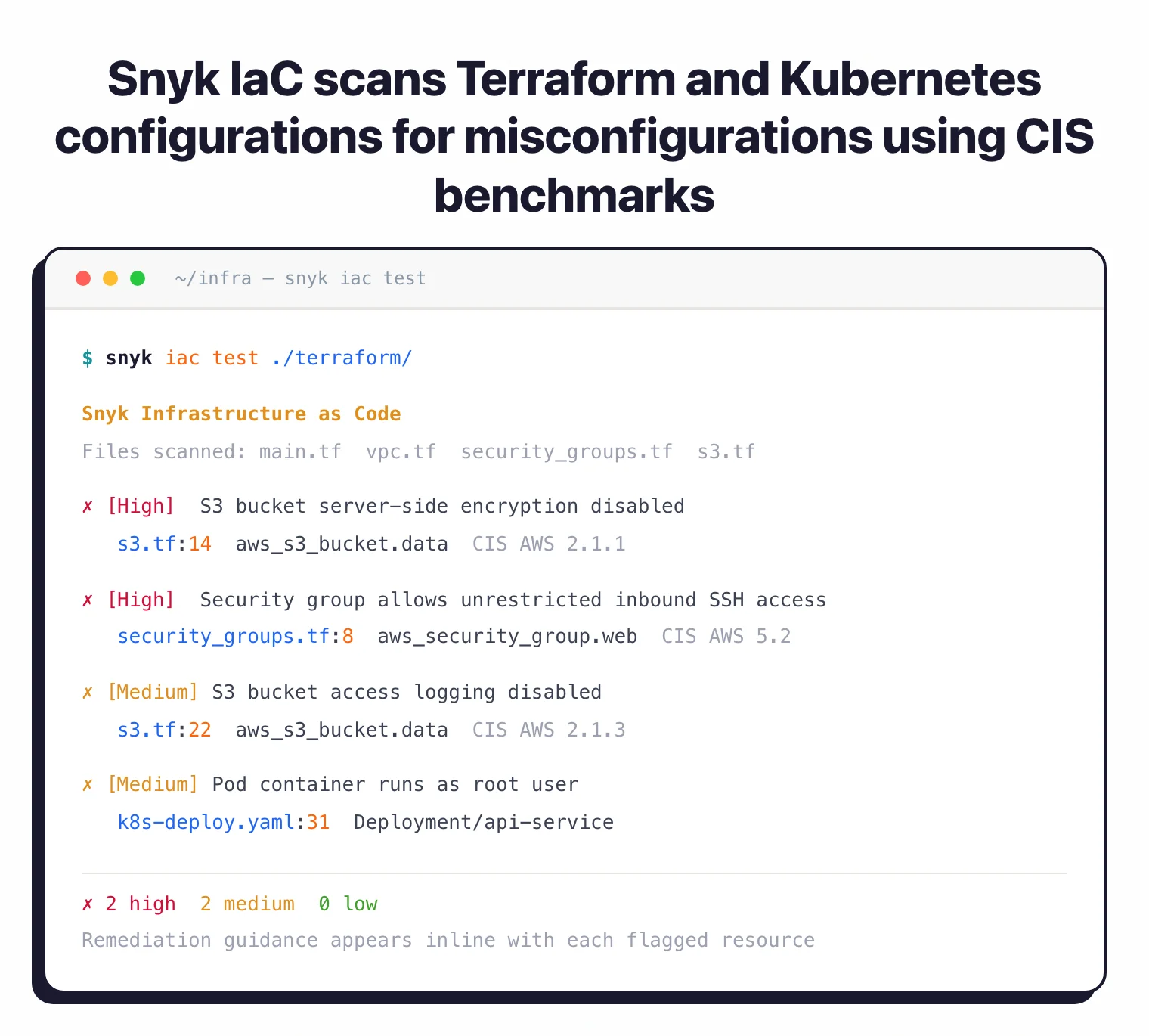
snyk iac test ./terraform/ flags Terraform and Kubernetes misconfigs against CIS benchmarks before merge — left of deploy.
Wiz IaC does the same but cross-references findings against the Wiz Security Graph. A misconfiguration in a Terraform module that deploys an internet-facing EKS cluster ranks higher than the same misconfiguration in an internal staging module.
Wiz’s CSPM, CIEM, and DSPM capabilities have no Snyk equivalent. For cloud posture, Wiz is the deeper platform.
Developer experience
Snyk’s IDE plugins (VS Code, IntelliJ, Visual Studio, Eclipse, Cursor, Windsurf) cover all four products in one panel. Findings appear inline as developers write code.
Wiz’s developer experience is improving but still cloud-first by default. The Wiz IDE plugin shows code-to-cloud risk for the file being edited, but the primary user is the cloud security team operating the Wiz dashboard.
For developer-first AppSec, Snyk is clearly ahead.
Pricing model
Snyk publishes pricing. Snyk Open Source Team is $25 per contributing developer per month, with a Free tier and an Enterprise tier above. Snyk Code, Snyk Container, and Snyk IaC are sold on top of the platform.
Wiz does not publish pricing. All deals are enterprise sales with custom contracts. Quotes typically scale with cloud account size and feature mix.
For procurement transparency, Snyk is easier. Wiz’s enterprise-only model is standard across CNAPP vendors but it does mean longer evaluation cycles.
When to Choose Each
Choose Snyk when
- Your priority is left-of-deploy AppSec — SAST, SCA, IaC scanning, container build scanning.
- Developer-first IDE and PR feedback is part of the requirement.
- Public pricing matters for procurement.
- You do not have a separate cloud security tool yet, and AppSec is the bigger gap.
- Your stack is code-heavy and your cloud footprint is modest.
Choose Wiz when
- Your priority is right-of-deploy cloud security — CSPM, CIEM, DSPM, runtime container scanning.
- You operate at multi-cloud scale with hundreds or thousands of workloads.
- Code-to-cloud context (not just code findings) is part of the requirement.
- You already have separate AppSec tooling and the cloud side is the bigger gap.
- Enterprise sales and customised contracts are normal for your organisation.
Choose both when
- You are an enterprise running both AppSec and CNAPP and want best-of-breed in each phase. Snyk owns PR through build; Wiz owns deployed workload through runtime.
Related comparisons
- Wiz vs Orca Security — Two agentless CNAPPs head-to-head.
- Wiz vs Prisma Cloud — Agentless CNAPP vs Palo Alto’s CNAPP.
- Snyk vs Veracode — Two AppSec platforms compared on SAST and platform breadth.
- Snyk alternatives — Wider field of platforms competing with Snyk.
Frequently Asked Questions
Is Snyk a competitor to Wiz?
Does Wiz do SAST?
Does Snyk do CSPM?
Which has better container security, Snyk or Wiz?
Can I use Snyk and Wiz together?

Founder, AppSec Santa
9+ years in application security. Reviews and compares 201 AppSec tools across 12 categories to help teams pick the right solution. More about me →
