Python depends on PyPI the way Node.js depends on npm. A medium Django or FastAPI project can resolve 80 to 200 transitive dependencies through requirements.txt or poetry.lock, and a single compromised maintainer account can push a malicious release that runs arbitrary code on every developer laptop and CI runner.
This guide compares 7 SCA tools for Python: pip-audit, Safety, Snyk Open Source , Socket , OSV-Scanner , Trivy , and Dependabot .
Why Python SCA is different
PyPI has characteristics that make SCA for Python distinct from other ecosystems.
**Install-time code execution. ** A Python package can run arbitrary code via setup.py or a PEP 517
build backend the moment pip install runs. That means a malicious package does not need your code to call it.
It executes during install, on a developer laptop or a CI runner, before any static scanner has a chance to catch it. Wheel-only distributions reduce this risk but do not eliminate it.
Note: Traditional CVE-based SCA tools only know about advisories that have already been published. A brand-new malicious PyPI package with an unreleased typosquat has no CVE, so pip-audit, Safety, and OSV-Scanner will not catch it. That is the gap Socket is built for.
Typosquatting and name confusion. PyPI has been hit repeatedly by typosquat attacks. Packages like reqeusts or python-dateutil clones have shipped credential stealers to thousands of machines before detection. Tools like Socket
focus on detecting these behavioral patterns before the package lands in your lockfile.
Lockfile fragmentation. Modern Python projects use requirements.txt (pip), Pipfile.lock (pipenv ), poetry.lock (poetry), or pdm.lock (pdm). Older projects often have a requirements.txt that is hand-written, not lock-generated, which means transitive versions are not pinned. SCA tools vary in how well they handle each format.
Deep transitive trees. A single pip install fastapi pulls in starlette, pydantic, typing-extensions, and more. Add a data stack (pandas, numpy, scipy) and you are past 50 packages before writing a line of application code. Most vulnerabilities live in that transitive layer, not in the packages you explicitly installed.
Maintainer churn on long-tail packages. A small utility package with one maintainer can go years between releases, which means known CVEs often stay unpatched. SCA tools surface this, but the fix is often forking or replacing the dependency.
Top SCA tools for Python
1. pip-audit
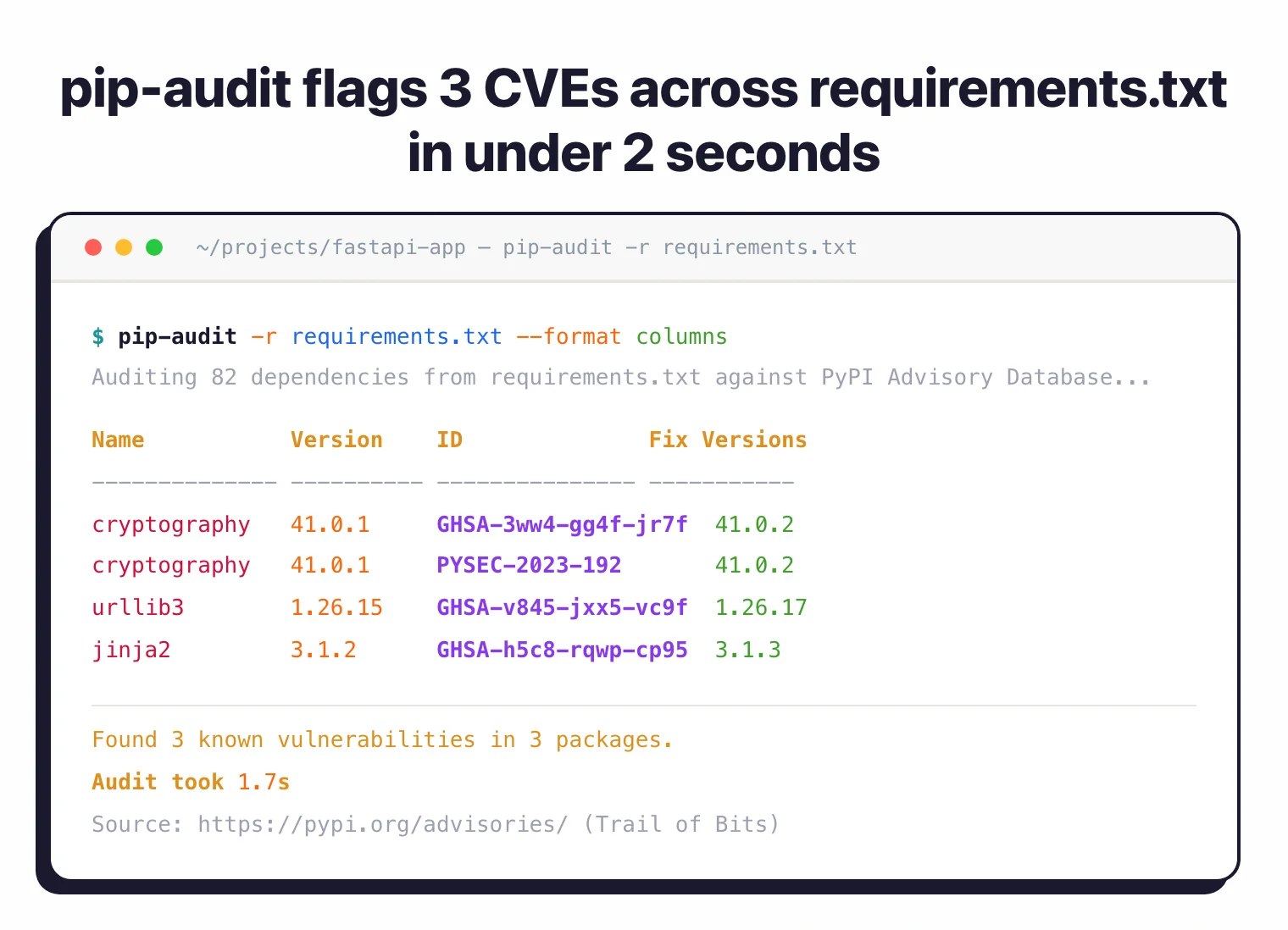
pip-audit is the Python SCA tool I reach for first. Maintained by Trail of Bits under Apache 2.0, it queries the PyPI Advisory Database (the same source GitHub uses) and scans requirements.txt, pyproject.toml, poetry.lock, or an installed environment.
What pip-audit does well: Zero configuration. Running pip-audit against an installed environment or pip-audit -r requirements.txt against a requirements file produces accurate CVE counts in seconds. It is a single pip install, which makes it easy to drop into any CI job. JSON and SARIF output support landing findings in GitHub code scanning is straightforward.
Where pip-audit falls short: No supply chain behavior analysis, no license checks, no auto-remediation. It is a scanner, not a platform. It also does not catch a malicious package that has no CVE.
Best fit: Every Python project as a baseline first gate in CI. If you only add one tool, add this one.
2. Safety
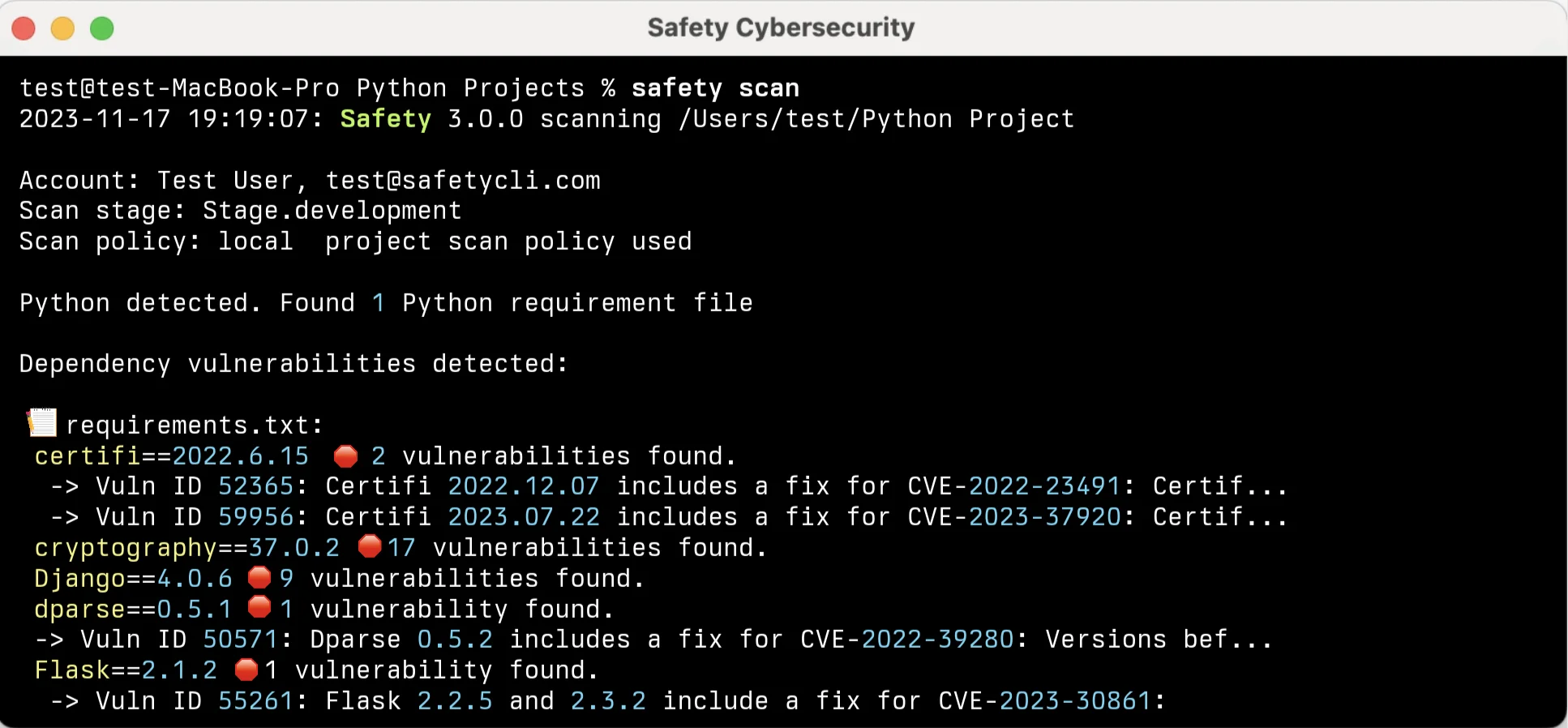
Safety
is built by PyUp. The open-source safety CLI scans your installed packages against the Safety DB, and the commercial tier adds a web dashboard, policy enforcement, license compliance, and a hosted vulnerability database that claims broader coverage than public sources.
What Safety does well: Mature CLI that has been around longer than pip-audit. The commercial tier is straightforward to adopt: CLI usage stays the same, but you get dashboards, SSO, and policy controls on top. The free tier covers most CVEs and is a reasonable second opinion when run alongside pip-audit.
Where Safety falls short: The free CLI database lags the commercial database on recency. Safety is focused on CVE detection, so supply chain analysis, reachability, and deep license policy features are not its core strengths. The line between free and paid has shifted a few times over the last two years, which can be confusing when you first evaluate it.
Best fit: Teams that want a commercial Python-first SCA vendor without paying for a general-purpose platform like Snyk or Mend. Runs well alongside pip-audit for dual coverage.
3. Snyk Open Source
Snyk Open Source scans PyPI dependencies from requirements.txt, poetry.lock, Pipfile.lock, and pyproject.toml. It checks a database that aggregates PyPI advisories, NVD, GitHub Security Advisories , and Snyk’s own research, and it provides auto-fix PRs and reachability analysis on paid plans.
What Snyk does well: Reachability analysis for Python identifies whether your code actually calls the vulnerable function in a dependency, which cuts noise significantly on large codebases. License compliance is bundled. Fix PRs open automatically and suggest the minimum version bump that clears the advisory without breaking compatibility. The IDE plugins work well in VS Code and PyCharm.
Where Snyk falls short: The free tier limits private projects and advanced features. Reachability for Python requires a paid plan. Snyk is SaaS, so manifests and lock files are uploaded to their infrastructure, which some teams cannot accept.
Best fit: Teams that want commercial-grade depth and are willing to pay for fewer false positives, IDE coverage, and GitHub, GitLab, or Bitbucket integrations.
![GitHub pull request from snyk-bot titled [Snyk] Security upgrade Jinja2 from 2.11.1 to 2.11.3 automatically updating requirements.txt, with a vulnerabilities-that-will-be-fixed table listing the advisory, priority score, severity, and upgrade path, concrete evidence of the auto-fix PRs and minimum version bumps described in the prose](/images/pages/sca-tools-for-python/03-snyk.webp)
4. Socket
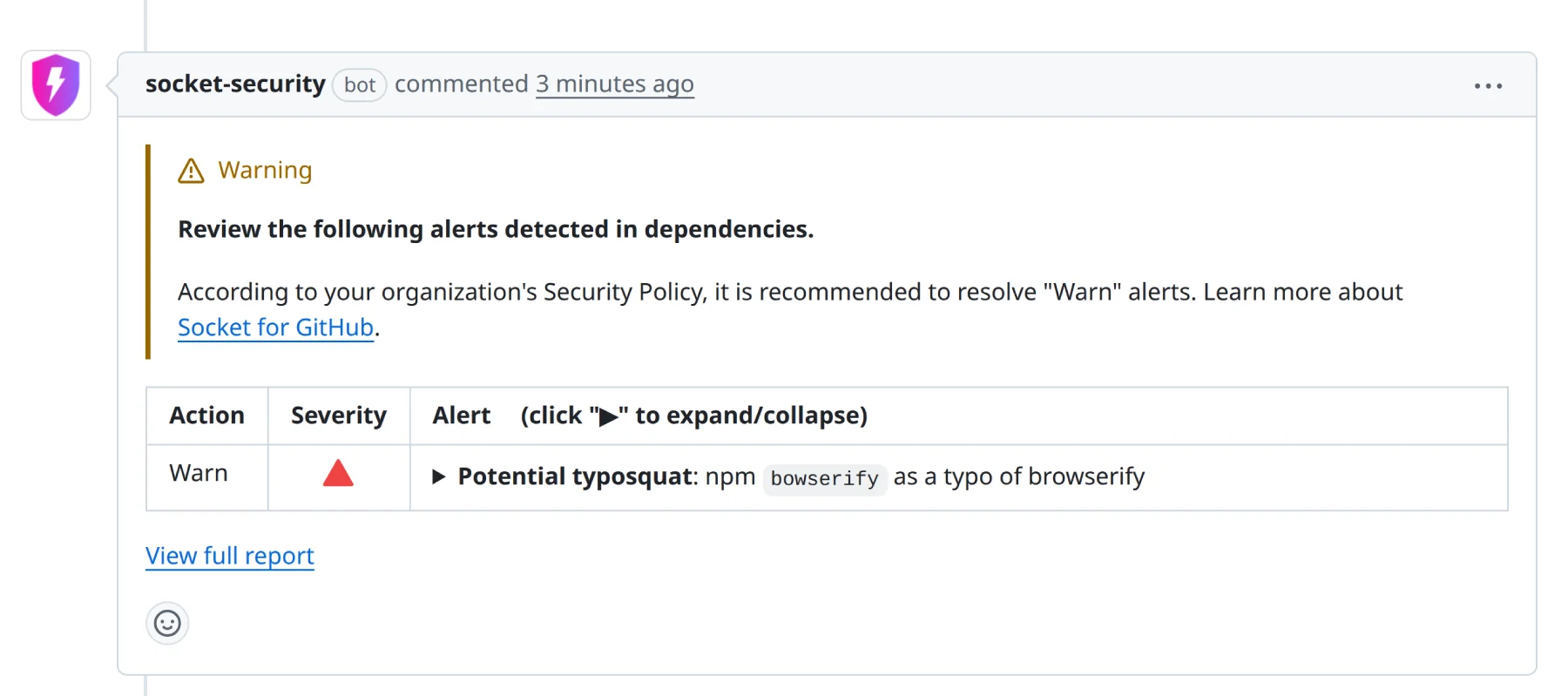
Socket analyzes what PyPI packages actually do rather than looking up CVEs. It flags install scripts that make unexpected network calls, setup.py files that execute dynamic code, packages that typo-squat popular names, and new maintainer takeovers.
What Socket does well: Detects malicious PyPI packages before any CVE is published, which is the single biggest gap in traditional SCA tooling. The GitHub app comments on pull requests that introduce suspicious dependencies and can block the merge. Free tier is generous for open-source repos.
Where Socket falls short: Not a replacement for CVE scanning. You still need pip-audit, Safety, or OSV-Scanner for known vulnerabilities. Socket is focused on the behavior side, not the advisory side.
Best fit: Any Python project that installs new PyPI packages regularly. Socket is especially valuable during developer bootstrap and in CI right after pip install completes.
5. OSV-Scanner
OSV-Scanner is Google’s open-source SCA tool that queries the OSV.dev database. OSV aggregates advisories from PyPI, GitHub, NVD, and dozens of other sources, so scanning against it typically catches advisories that single-source tools miss.
What OSV-Scanner does well: Free, fast, single static binary with zero runtime dependencies. Parses requirements.txt, Pipfile.lock, and poetry.lock natively. SARIF output drops straight into GitHub code scanning. Running osv-scanner --lockfile poetry.lock is one of the fastest ways to get a second advisory source into your pipeline.
Where OSV-Scanner falls short: Pure scanner, no supply chain analysis, no license checking, no auto-fix PRs, no IDE integration. If you want more than a CVE list, you need another tool alongside.
Best fit: Teams that want a second free advisory source on top of pip-audit. The combination catches more than either tool alone.
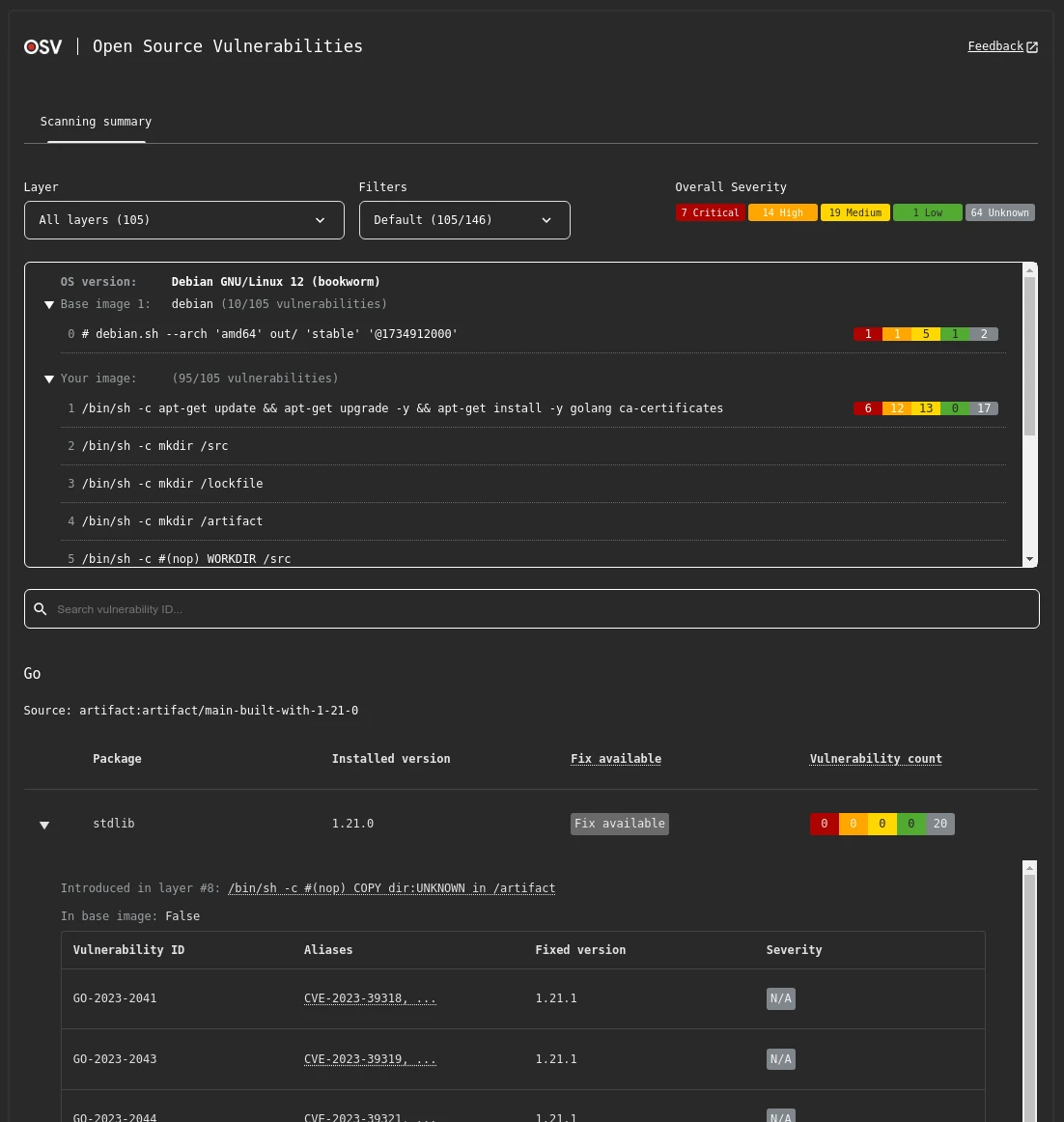
6. Trivy
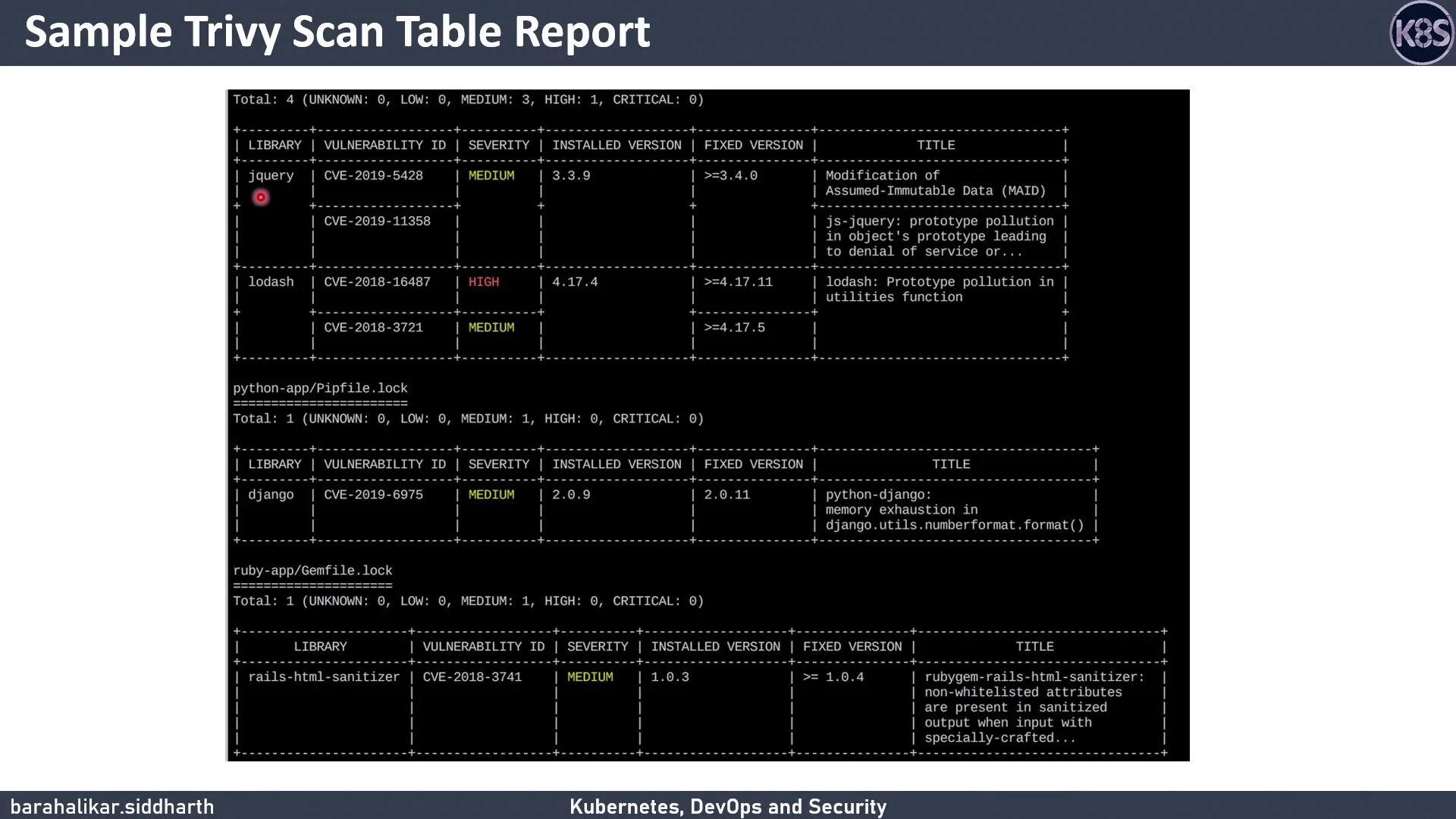
Trivy started life as a container scanner and grew into a broad SCA tool. For Python it reads requirements.txt, pyproject.toml, Pipfile.lock, and poetry.lock directly, and it also detects Python packages inside container images via the filesystem scanner.
What Trivy does well: One tool covers filesystem SCA, container image scanning, IaC scanning, and secret detection. For teams that already run Trivy for Docker images, adding Python lockfile scanning is free and immediate. Trivy’s database updates frequently and the CLI is fast.
Where Trivy falls short: Reachability analysis is not its focus. Python dependency parsing is accurate but the noise level on transitive trees can be higher than pip-audit or Snyk. Auto-remediation is limited compared to dedicated SCA platforms.
Best fit: Teams that already use Trivy for container image scanning and want to consolidate SCA on the same tool. Also a reasonable default if you want one scanner for source code and images.
7. Dependabot
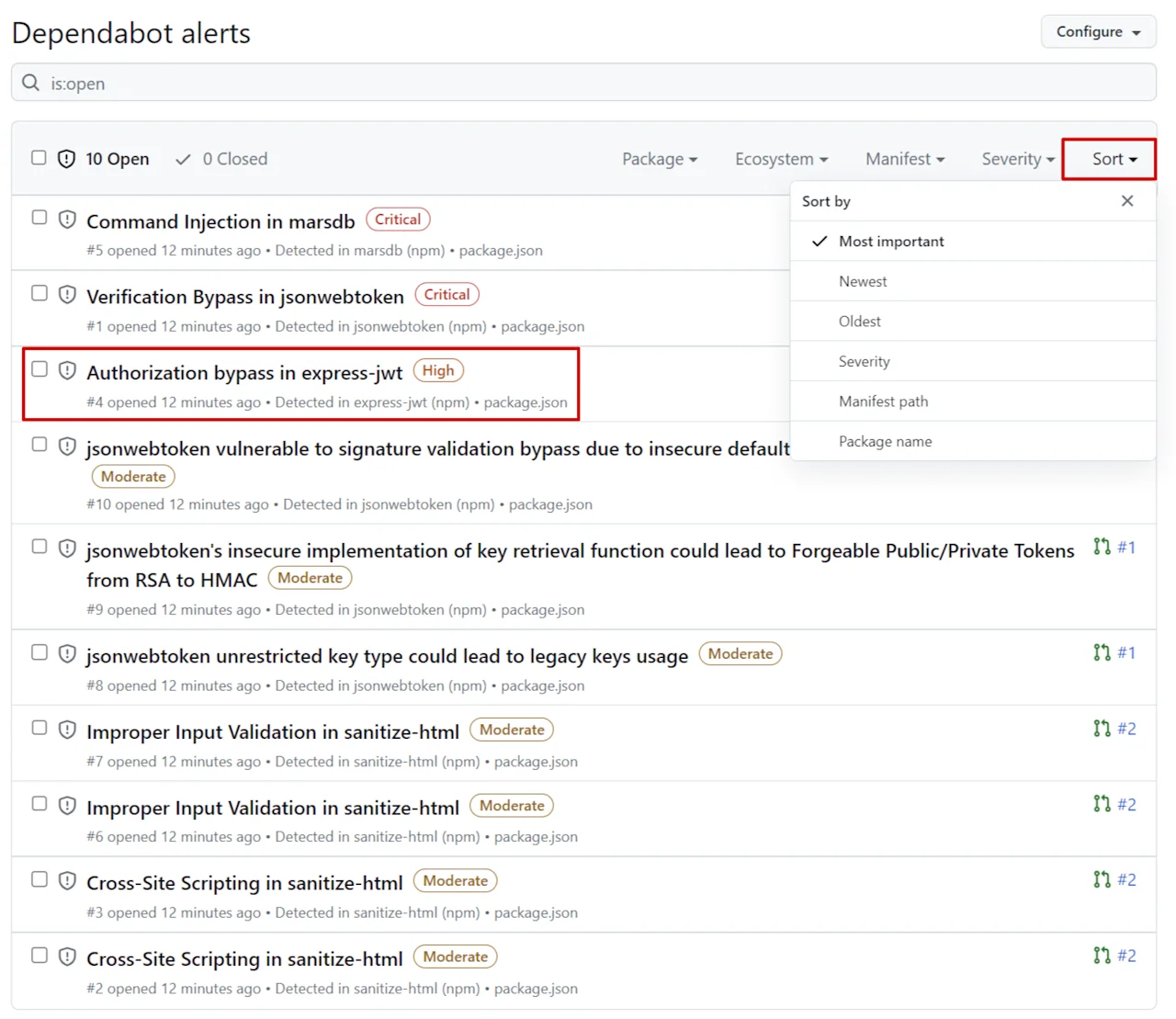
Dependabot is GitHub’s built-in automated dependency updater and vulnerability alerter. It monitors requirements.txt, pyproject.toml, Pipfile, poetry.lock, and setup.py for outdated packages and PyPI security advisories, then opens PRs to update them.
What Dependabot does well: Zero-cost, zero-maintenance for GitHub repos. Security updates are prioritized and opened automatically when a new advisory matches a Python dependency. The .github/dependabot.yml
config file covers the common cases (package-ecosystem: pip, schedule, grouping).
Where Dependabot falls short: GitHub-only. Configuration is less flexible than Renovate for monorepo Python layouts, scheduled batching, or cross-ecosystem consolidation. It does not do supply chain behavior analysis or license checking.
Best fit: GitHub-hosted Python projects that want automated security update PRs with no extra tooling. Pairs well with pip-audit running in CI.
Comparison table
| Tool | CVE Detection | Supply Chain | License Checks | Auto-fix PRs | License | Best For |
|---|---|---|---|---|---|---|
| pip-audit | PyPI Advisory DB | No | No | No | Open source | Baseline CI gate |
| Safety | Safety DB | No | Commercial tier | No | Free + Commercial | Python-first commercial SCA |
| Snyk Open Source | Deep + reachability | Limited | Yes | Yes | Free + Commercial | Commercial-grade SCA |
| Socket | No | Yes (behavioral) | No | No | Free + Commercial | Supply chain attacks |
| OSV-Scanner | OSV DB (broad) | No | No | No | Open source | Free second source |
| Trivy | Multi-source | No | Limited | No | Open source | Teams already using Trivy |
| Dependabot | GitHub Advisory DB | No | No | Yes (auto-PR) | Free (GitHub) | GitHub repos |
How to choose for your use case
Solo developer or small project. pip-audit plus Dependabot if you are on GitHub. Free, zero config, covers the basics. Add OSV-Scanner for a second advisory source.
Growing team with a production FastAPI or Django app. pip-audit as the first CI gate, Socket free tier for supply chain protection, Dependabot for automated update PRs. Add Snyk Open Source if reachability analysis and auto-fix PRs would cut triage time enough to justify the spend.
Enterprise team with compliance requirements. Snyk Open Source or a commercial Mend SCA -style platform for audit trails, SBOM generation, license policy enforcement, and role-based access control.
Teams already running Trivy. Use Trivy for Python lockfile scanning and keep pip-audit as a secondary CI gate. No need to add another tool.
Python monorepo with multiple service directories. Renovate for update automation (strongest monorepo support), pip-audit running per-service in CI, and Socket for supply chain protection across all packages.
For the full picture on SCA tooling beyond Python, see the complete SCA tools list and the open-source SCA tools guide .
Open source vs commercial
Most Python teams can get surprisingly far on free tools. The combination of pip-audit, OSV-Scanner, Socket free tier, and Dependabot covers CVE detection from two sources, supply chain attack detection, and automated update PRs without a single commercial invoice.
Commercial tools earn their spend on three axes.
Reachability analysis. Snyk Open Source can tell you which vulnerable functions your Python code actually calls. On a 50-service codebase, this can cut the weekly triage load by half or more. pip-audit and OSV-Scanner flag every vulnerable package regardless of whether the vulnerable code path is reachable.
License compliance. Commercial tools like Snyk and Mend SCA enforce license policies across transitive dependencies. A transitive GPL or AGPL dependency can create a legal problem for commercial Python applications, and a pure CVE scanner will not flag it.
Auto-remediation at scale. Both Dependabot (free) and Snyk (commercial) open PRs for vulnerable packages. Snyk goes further on fix accuracy and grouping, which matters more as your service count grows.
The practical recommendation: start with pip-audit plus Dependabot plus Socket free. Graduate to Snyk or a Mend-style platform when reachability analysis, license policy, or SBOM generation become hard requirements.
Pro tip: Pipe pip-audit output into OSV-Scanner on the same lockfile in CI. Two free advisory sources (PyPI Advisory DB + OSV.dev) catch CVEs that single-source tools miss, and both finish in well under a minute on typical requirements.txt files.
If your stack also uses other ecosystems, the dedicated SCA picks for Node.js and TypeScript and Java cover the tool nuances that a generic SCA list misses.






