Node.js applications depend on npm packages more heavily than almost any other runtime — a typical Express.js application pulls in hundreds of transitive dependencies through node_modules.
That dependency depth creates a large SCA attack surface: known CVEs in lodash or the colors package sabotage, supply chain attacks via typosquatting and package hijacking, license compliance across hundreds of packages, and lockfile drift between environments.
This guide compares 7 SCA tools for the Node.js and npm ecosystem: npm audit, Snyk Open Source , Socket , Dependabot , Renovate , OSV-Scanner , and Mend SCA .
Why Node.js SCA is different
The npm ecosystem has characteristics that make SCA for Node.js distinct from other runtimes.
**Dependency tree depth. ** A single npm install for a medium Express.js app can install 400–700 packages. Most of those are transitive — you depend on package A, which depends on B, which depends on C.
A CVE in package C affects your application even though you never explicitly installed it. npm audit
and dedicated SCA tools trace this tree; naive package.json scanning misses most of it.
Supply chain attack surface. The npm registry has had more supply chain incidents than any other package registry — typosquatting, dependency confusion, and maintainer account takeovers are all documented npm attack vectors. Tools like Socket focus specifically on detecting malicious package behavior before it reaches production.
License diversity. npm packages ship under a wide range of licenses — MIT, ISC, Apache-2.0, GPL, LGPL, UNLICENSED. For commercial Node.js applications, a transitive GPL dependency can create a licensing problem that a pure CVE scanner will not flag.
Lockfile sprawl. Node.js projects often have package-lock.json (npm), yarn.lock (Yarn), or pnpm-lock.yaml (pnpm) with different formats. SCA tools vary in how well they handle all three.
Top SCA tools for Node.js
1. npm audit
npm audit is Node.js’s built-in vulnerability scanner. Running npm audit checks your installed packages against the npm advisory database and reports known CVEs with severity levels and affected versions. It is already installed — there is nothing to add.
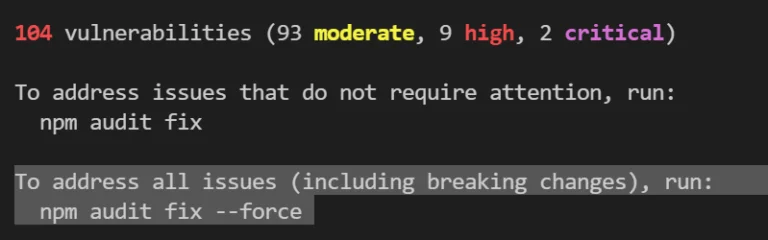
What npm audit does well: Zero configuration, instant feedback. It checks the installed dependency tree (including transitive dependencies from package-lock.json), reports CVSS scores, and provides npm audit fix to auto-update safe patches. For a small project or team new to SCA, it is the fastest way to start.
Where npm audit falls short: It only checks the npm advisory database — it does not detect supply chain attacks, malicious packages, license issues, or vulnerabilities from non-npm sources. npm audit fix can sometimes upgrade to a version that breaks your application. The false positive rate for low-severity advisories can be high in some ecosystems.
Best fit: Every Node.js project as a baseline first gate in CI. Not a replacement for dedicated SCA tooling in production applications.
2. Snyk Open Source
Snyk Open Source
is the most widely adopted commercial SCA tool for Node.js. It scans package-lock.json and yarn.lock, checks a database that aggregates npm advisories, NVD, GitHub Security Advisories, and Snyk’s own research, and provides fix recommendations with auto-PR creation.
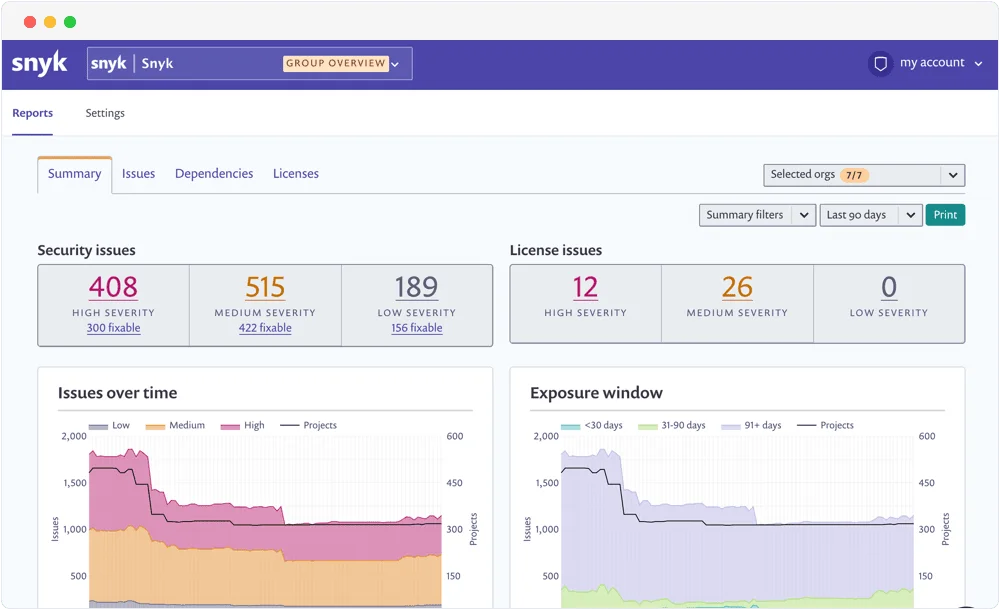
What Snyk does well: Reachability analysis is Snyk’s headline differentiator — it identifies whether your code actually calls the vulnerable function in a dependency, which dramatically reduces noise for Node.js projects. License compliance checking across the full dependency tree is included. Fix PRs open automatically with upgrade suggestions that preserve compatibility.
Where Snyk falls short: The free tier limits the number of private projects and advanced features. Reachability analysis for JavaScript requires a paid plan. SaaS-based — source code and dependency manifests are sent to Snyk.
Best fit: Teams that want commercial SCA depth with minimal setup. Snyk integrates with GitHub, GitLab, Bitbucket, Jira, and Slack, making it the most pipeline-friendly option for larger teams.
3. Socket
Socket takes a fundamentally different approach: instead of checking CVE databases, it analyzes what npm packages actually do. It looks for packages that make unexpected network requests in install scripts, use dynamic code execution, contain obfuscated code, escalate permissions, or access the file system in unusual ways.
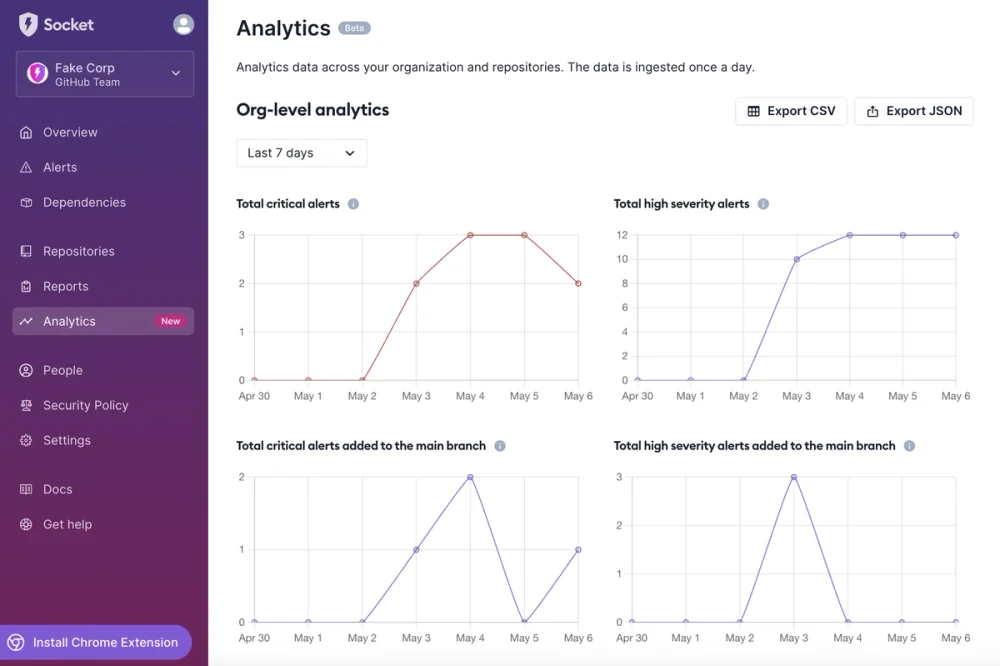
What Socket does well: Supply chain attack detection that CVE-based tools cannot provide. Socket flags packages that might be malicious before any CVE is ever published — a critical gap in traditional SCA tooling given the npm ecosystem’s supply chain history. The GitHub app blocks PRs that introduce suspicious packages.
Where Socket falls short: Supply chain analysis is its focus — it does not replace CVE scanning. You need npm audit, Snyk, or OSV-Scanner alongside Socket for known vulnerability coverage.
Best fit: Any Node.js project adding npm dependencies regularly. Socket is most valuable for teams that install packages frequently and want protection against supply chain attacks before they become CVEs.
4. Dependabot
Dependabot
is GitHub’s built-in automated dependency updater. It monitors package.json and package-lock.json for outdated packages and security advisories, then opens PRs to update them. It is enabled per-repository via a .github/dependabot.yml config file.
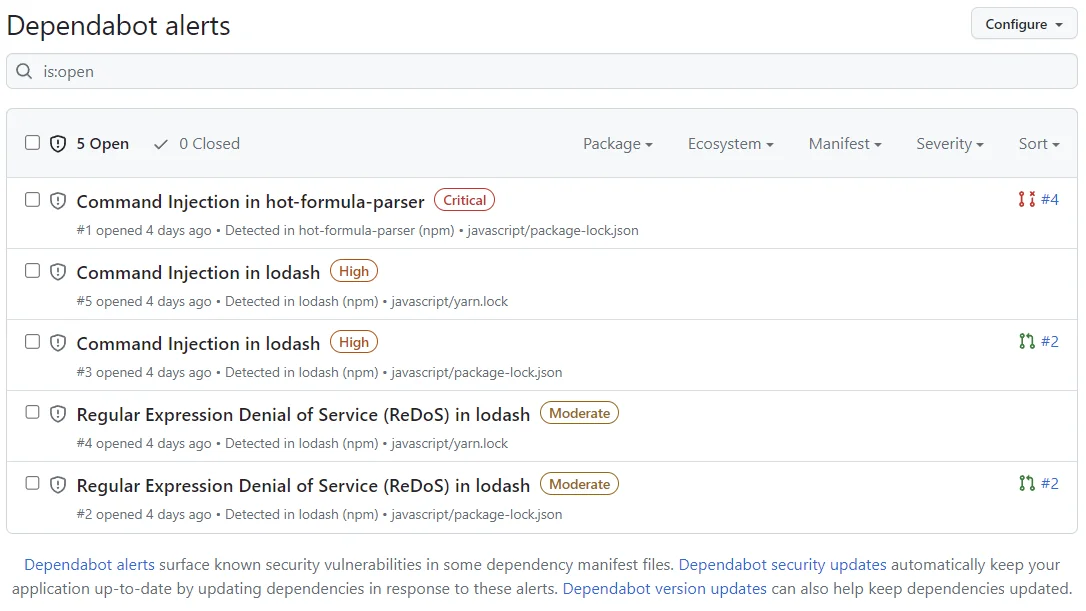
What Dependabot does well: Zero-cost and zero-maintenance for GitHub repos. Security updates are prioritized and opened automatically when a new advisory matches a dependency. Dependabot groups related updates to reduce PR noise (available in Dependabot Grouped Updates).
Where Dependabot falls short: GitHub-only. Configuration is less flexible than Renovate for monorepos, scheduled batching, or cross-ecosystem consolidation. It does not offer supply chain analysis or license checking.
Best fit: GitHub-hosted Node.js projects that want automated security and version update PRs with no additional tooling cost.
5. Renovate
Renovate is the most configurable automated dependency update tool. It supports npm, yarn, pnpm, and all major CI/CD platforms — GitHub, GitLab, Bitbucket, Azure DevOps, and self-hosted.
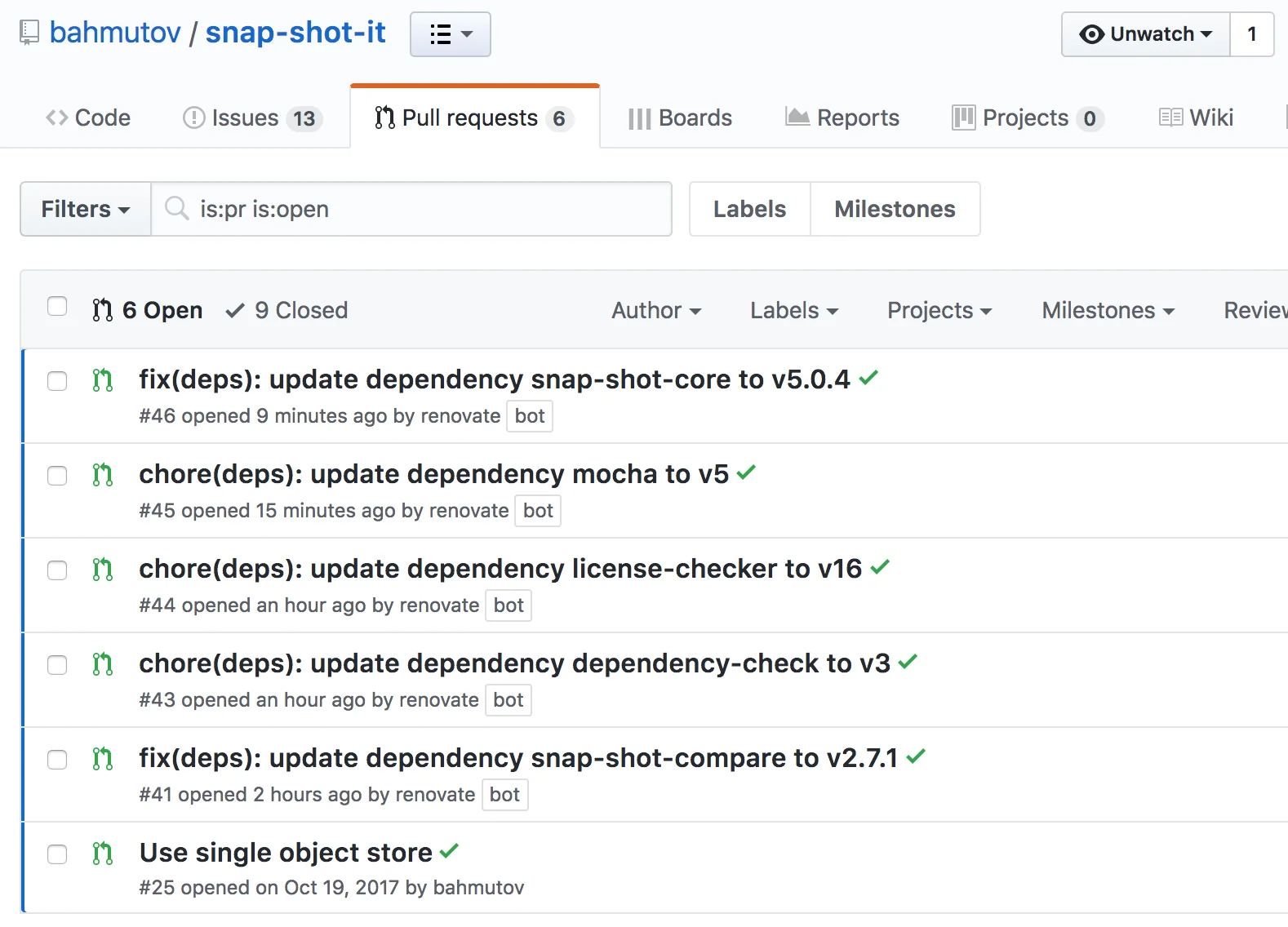
What Renovate does well: Fine-grained control over update batching, scheduling, grouping by ecosystem or scope, and monorepo workspace support. Renovate understands npm workspaces and can open separate PRs per package or bundle updates for review. The renovate.json config file is powerful enough to handle complex Node.js monorepo update workflows.
Where Renovate falls short: Zero-config setup is less polished than Dependabot. The configuration options are extensive — which means there is more to learn before it behaves exactly as expected. Renovate Bot requires a GitHub App installation or self-hosting.
Best fit: Node.js monorepos, teams on GitLab or Azure DevOps, or projects that need fine-grained control over how updates are batched and scheduled.
6. OSV-Scanner
OSV-Scanner
is Google’s open-source SCA tool that queries the OSV (Open Source Vulnerabilities) database — a federated database that aggregates advisories from GitHub, npm, PyPI, crates.io, and dozens of other ecosystems. It supports package-lock.json and yarn.lock natively.
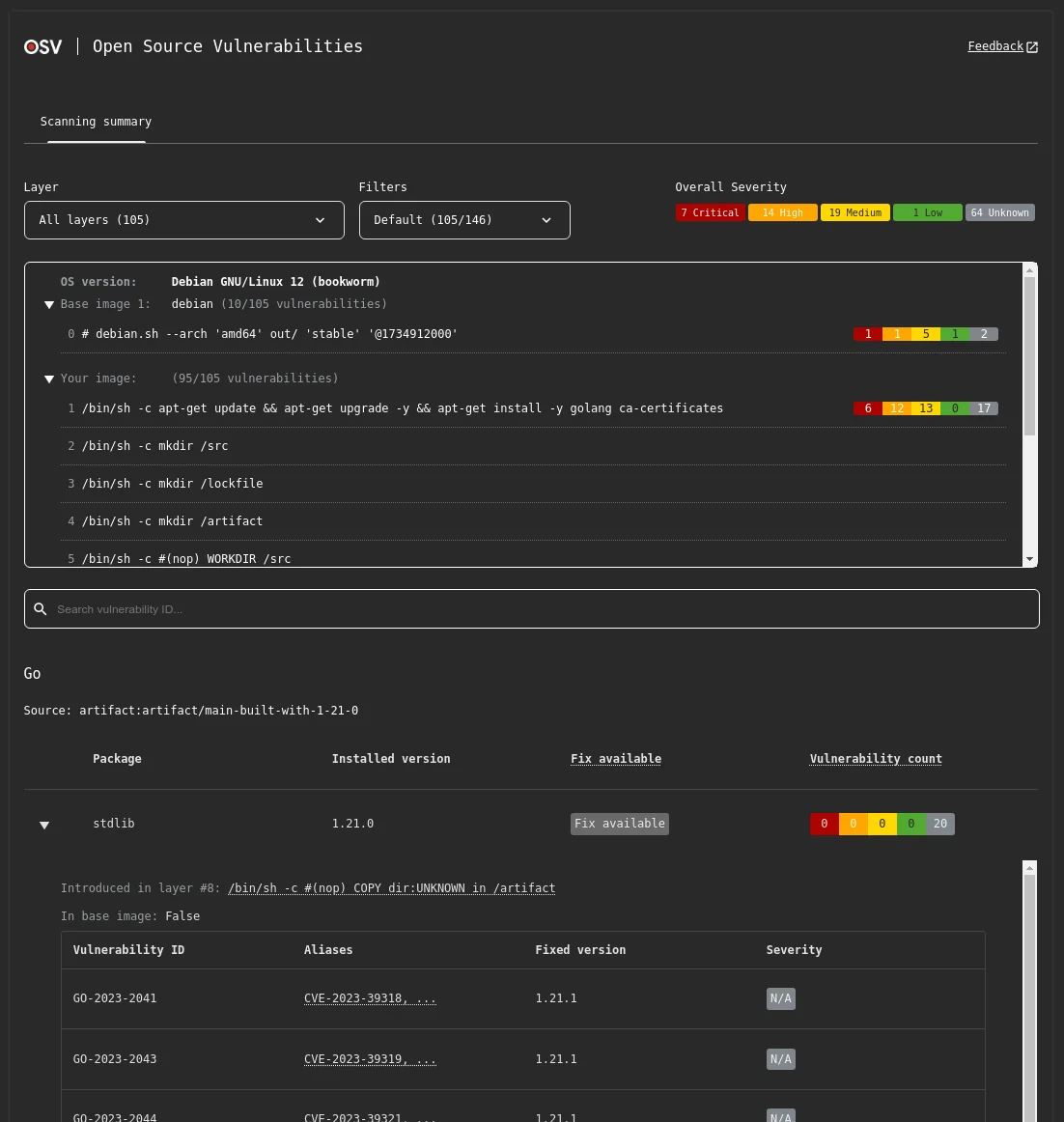
What OSV-Scanner does well: Free, fast, and accurate against a large advisory database. OSV-Scanner produces SARIF output compatible with GitHub Advanced Security, making it easy to surface findings in the GitHub Security tab. Running osv-scanner --lockfile package-lock.json is the fastest way to check a Node.js project against a broad advisory source.
Where OSV-Scanner falls short: No supply chain analysis, no license checking, no auto-remediation, and no IDE integration. It is a scanner, not a full SCA platform.
Best fit: Teams that want a free, open-source CVE scanner for Node.js CI/CD without a commercial subscription. Use alongside Socket for supply chain coverage.
7. Mend SCA
Mend SCA is a commercial SCA platform with strong npm support, covering CVE detection, license compliance, policy enforcement, and SBOM generation. It integrates with GitHub, GitLab, Bitbucket, Jenkins, and Azure DevOps.

What Mend SCA does well: License compliance management is one of Mend’s strongest features — it can block builds based on license policies, which matters for commercial Node.js applications with GPL transitive dependencies. SBOM generation in SPDX and CycloneDX format is supported. Mend pairs with Mend SAST for teams consolidating SAST and SCA.
Where Mend SCA falls short: Contact-sales pricing. No supply chain attack detection equivalent to Socket’s approach.
Best fit: Enterprise teams with license compliance requirements or those consolidating SCA with SAST under a single vendor.
Comparison table
| Tool | CVE Detection | Supply Chain | License Checks | Auto-fix PRs | License | Best For |
|---|---|---|---|---|---|---|
| npm audit | npm DB only | No | No | npm audit fix | Free (built-in) | Baseline CI gate |
| Snyk Open Source | Deep + reachability | Limited | Yes | Yes | Free / Commercial | Commercial-grade SCA |
| Socket | No | Yes (behavioral) | No | No | Free / Commercial | Supply chain attacks |
| Dependabot | GitHub Advisory DB | No | No | Yes (auto-PR) | Free (GitHub) | GitHub repos |
| Renovate | Via advisories | No | No | Yes (auto-PR) | Open source | Monorepos, non-GitHub |
| OSV-Scanner | OSV DB (broad) | No | No | No | Open source | Free CI scanner |
| Mend SCA | Deep | No | Yes | Yes | Commercial | Enterprise license compliance |
How to choose for your use case
Solo developer or small project: npm audit plus Dependabot (if on GitHub). Free, zero-config, covers the basics. Add OSV-Scanner in CI for broader advisory coverage.
Growing team with a production Node.js API: npm audit as the first CI gate, Socket for supply chain protection, Dependabot or Renovate for automated update PRs. Add Snyk Open Source if reachability analysis — knowing which vulnerable functions your code actually calls — would meaningfully reduce noise for your team.
Enterprise team with compliance requirements: Mend SCA or Snyk Open Source for audit trails, SBOM generation, license policy enforcement, and RBAC. Both integrate with JIRA, Slack, and enterprise CI/CD platforms.
npm monorepo: Renovate for update automation (strongest monorepo support), Snyk Open Source for workspace-level CVE scanning, and Socket for supply chain protection across all packages.
For the full picture on SCA tooling beyond Node.js, see the complete SCA tools list and the open source SCA tools guide .
npm audit vs external SCA tools
npm audit is the most common first step teams take toward Node.js SCA — and for good reason. It is already installed, requires no configuration, and catches the most obvious known vulnerabilities in published npm advisories.
But npm audit has structural limitations that become visible as applications grow.
Coverage: npm audit queries only the npm advisory database. OSV-Scanner queries a federated database that includes npm advisories plus GitHub Security Advisories, NVD, and other sources — broader coverage from a single scan.
Supply chain: npm audit cannot detect a malicious package — one that exfiltrates environment variables or opens a reverse shell — because no CVE will have been published yet. Socket exists specifically to fill this gap.
Reachability: npm audit flags every package with a known vulnerability regardless of whether your code ever calls the vulnerable function. A medium-severity vulnerability in a utility package used only in tests gets the same treatment as a critical vulnerability in your API authentication library. Snyk Open Source ’s reachability analysis addresses this by distinguishing reachable from unreachable vulnerable paths.
Remediation workflow: npm audit fix sometimes proposes breaking changes — major version upgrades that require code changes. Dedicated tools like Dependabot
and Renovate
open PRs with compatible upgrades that trigger your CI test suite before merging.
The practical recommendation: use npm audit as a CI gate that fails on high-severity findings, and add one or two dedicated SCA tools for supply chain protection and automated remediation.






