Java applications have some of the deepest transitive dependency trees in software. A mid-sized Spring Boot service can resolve 300 or more JARs through Maven, many of them buried three or four levels deep, some of them bundled inside other JARs via shading.
Log4Shell in December 2021 made the cost of missing any of them painfully clear. This guide compares 7 SCA tools for Java: OWASP Dependency-Check , Dependency-Track , Snyk Open Source , Nexus Lifecycle , JFrog Xray , Trivy , and Dependabot .
Why Java SCA is different
The Java ecosystem has characteristics that make SCA meaningfully different from scanning npm or PyPI.
**Deep transitive trees. ** Maven’s default behavior resolves transitive dependencies without any lockfile. A single spring-boot-starter-web declaration pulls in 30+ JARs, and those pull in more.
A CVE can sit four levels deep in a dependency you never chose. Log4Shell was that exact shape: log4j-core was a transitive dependency for many Spring and ElasticSearch users, not a direct declaration.
Key Insight
Log4Shell is the single best capability test for a Java SCA tool. How quickly did the vendor add CVE-2021-44228 in December 2021, and can the tool still find log4j-core buried three levels deep in a Spring Boot tree today? If either answer is weak, the tool is not ready for the next emergency.
Shaded and uber JARs. Java applications often ship as a single fat JAR that bundles all dependencies inside. Some build configurations rename packages (shading) to avoid runtime conflicts. A naive scanner that only reads pom.xml will miss vulnerable code that is physically present inside the final artifact. Good Java SCA tools inspect JAR contents and use binary fingerprinting, not just manifest parsing.
Note: Before you commit to any Java SCA tool, check how it handles shaded JARs against a build you actually ship. Snyk, Nexus Lifecycle, and JFrog Xray use binary fingerprinting that is more robust; naive manifest-only scanners quietly miss vulnerable code bundled inside fat JARs.
Build tool variance. Maven, Gradle, and Ant all produce Java builds with different conventions. Gradle does not lock dependencies by default, so two builds a week apart can resolve different versions. SCA tools handle the three build systems with different levels of polish.
Java Native Interface (JNI). Some Java libraries bundle native shared libraries (.so, .dll, .dylib) inside the JAR. A vulnerability in the native component is invisible to a pure JAR scanner. Only a few SCA tools inspect native binaries inside JARs.
Long release cycles. Enterprise Java applications often run on a framework version that is years old. That creates a specific SCA profile: many known CVEs, limited upgrade paths, and a real need for compensating controls rather than straight version bumps.
Top SCA tools for Java
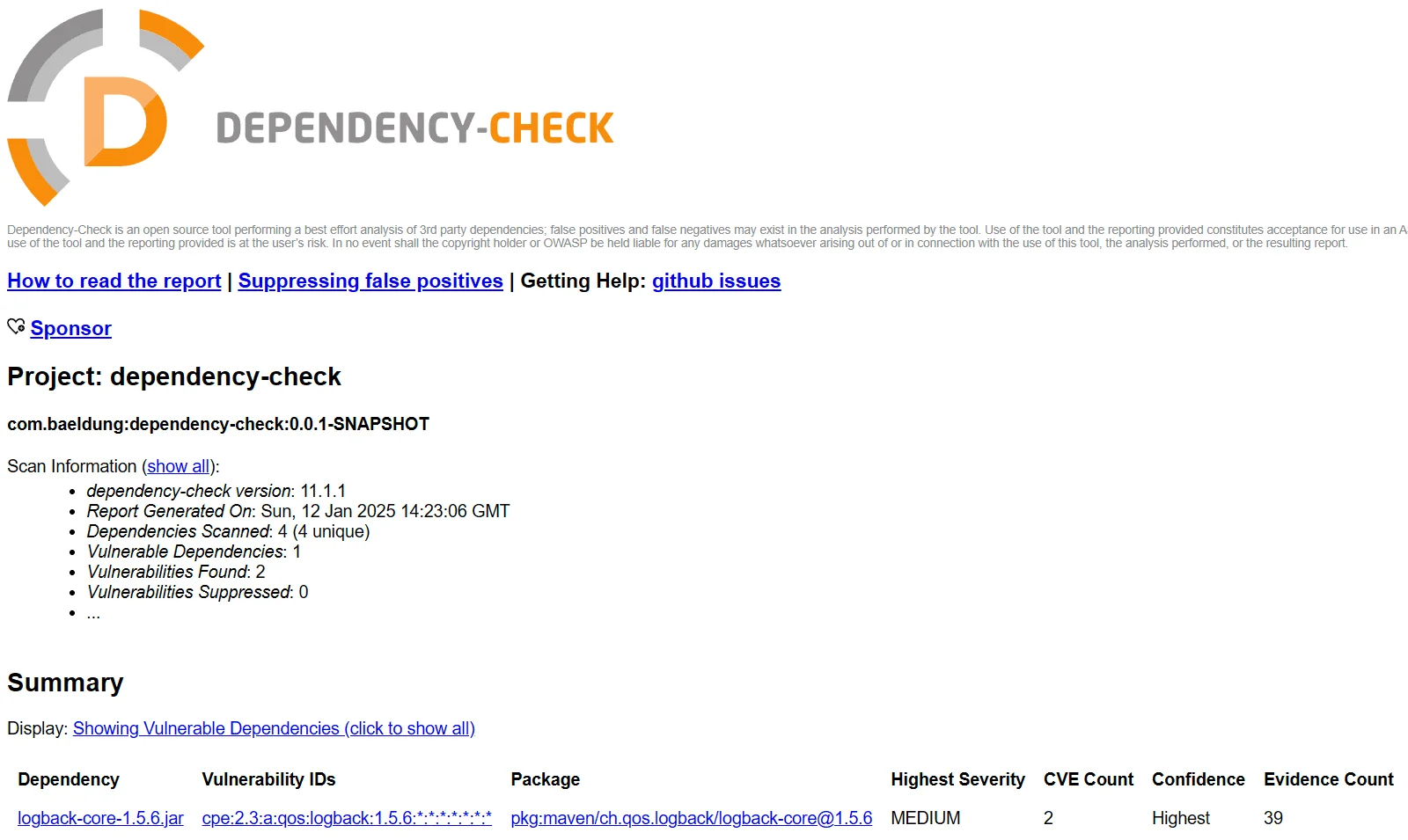
1. OWASP Dependency-Check
OWASP Dependency-Check is the original free Java SCA tool. It ships as a CLI, Maven plugin, Gradle plugin, and Jenkins plugin under the Apache 2.0 license . It uses evidence-based matching to identify libraries (including some shaded JARs), then queries the NVD for known CVEs.
What Dependency-Check does well: Mature, widely deployed, and free. The Maven plugin is one line in the build, and the HTML report is easy to hand to a developer without training. The evidence-based identifier approach handles many real-world edge cases that purely manifest-based scanners miss.
Where Dependency-Check falls short: NVD is the primary data source, which means advisories that first appear on GitHub Security Advisories can lag. The first-time NVD download is large and slow. False positives on ambiguous CPE matches are a known pain point. No built-in auto-remediation or fix suggestions.
Best fit: Every Java project as a first gate. Also a strong default for teams that want a free, self-hosted, vendor-neutral SCA baseline.
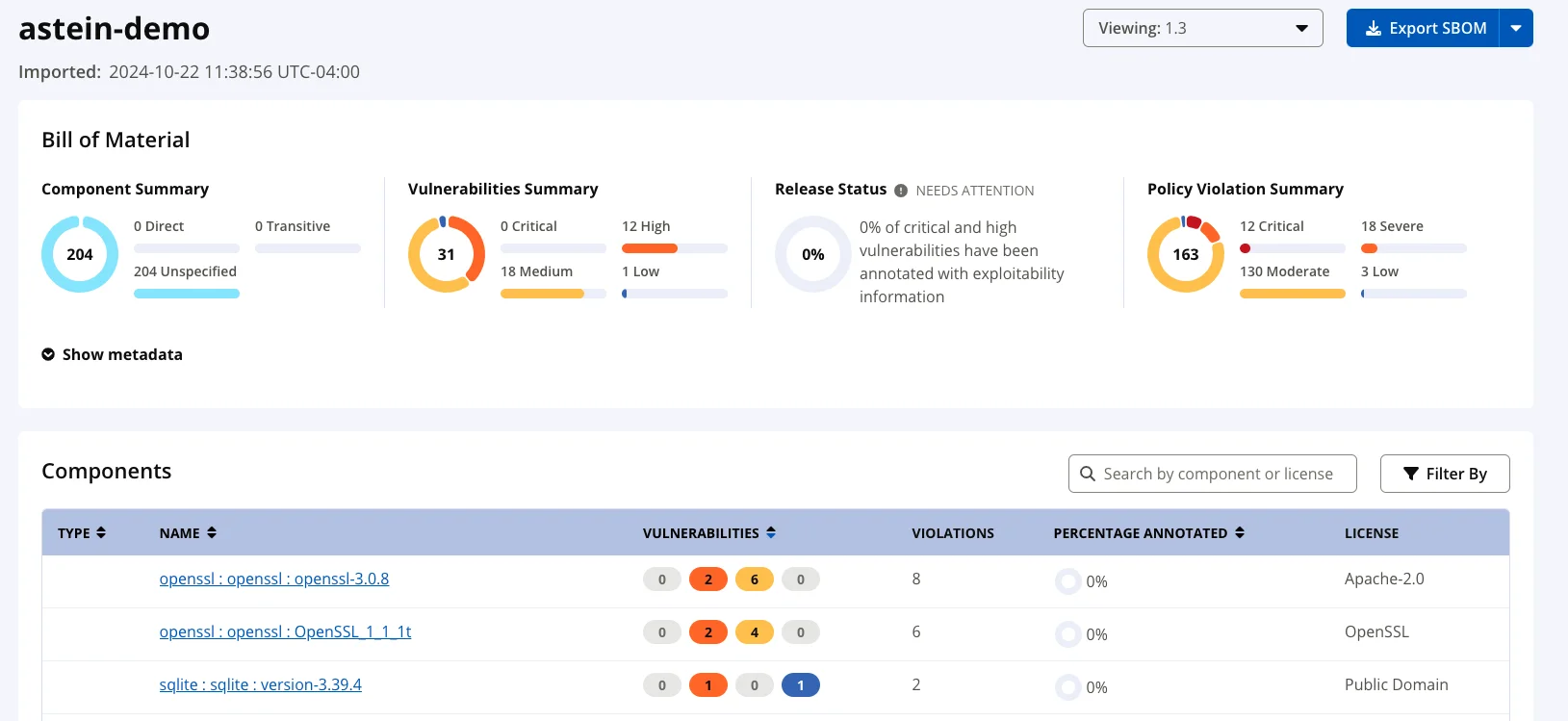
2. Dependency-Track
Dependency-Track is an OWASP flagship project that approaches SCA differently. Instead of scanning in the build, you generate a CycloneDX SBOM as part of each build (via cyclonedx-maven-plugin or cyclonedx-gradle-plugin ) and upload it to Dependency-Track. The server stores every SBOM and continuously re-evaluates all of them against new advisories.
What Dependency-Track does well: Continuous SBOM analysis is the killer feature. When a new CVE drops, you do not re-run scans against every repo. The server already knows which applications contain the affected component and flags them. Free, self-hosted, Apache 2.0 license. Integrates advisories from NVD, GitHub Security Advisories, OSS Index, Snyk (commercial), and VulnDB.
Where Dependency-Track falls short: Requires operating a server. The initial setup (SBOM generation in each build, service token per project, integration into the CI pipeline) takes meaningful engineering time. Not a drop-in scanner.
Best fit: Enterprises with more than a handful of Java services that want continuous SBOM-based vulnerability management without paying for a commercial platform.

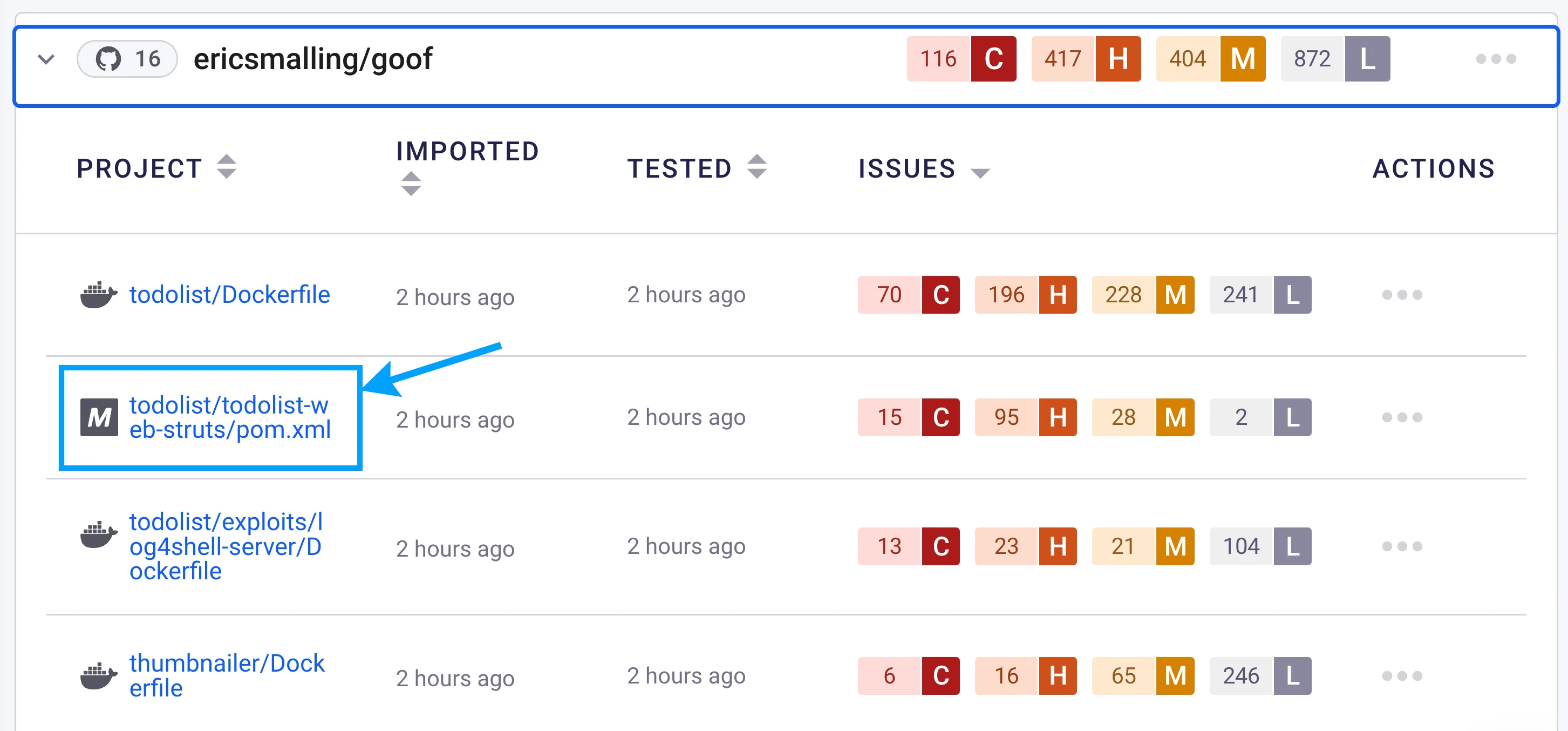
3. Snyk Open Source
Snyk Open Source scans Java projects via Maven, Gradle, Ivy, or SBT. It reads pom.xml and build.gradle, builds the full transitive dependency tree, and checks it against a vulnerability database that aggregates NVD, GitHub advisories, Snyk’s own research, and commercial feeds.
What Snyk does well: Reachability analysis for Java identifies whether your code actually calls the vulnerable function in a dependency. Auto-fix PRs open with the minimum version bump that clears the advisory. License compliance across the full tree is included. IDE integration works well in IntelliJ and Eclipse.
Where Snyk falls short: The free tier limits private projects and advanced features. Reachability requires a paid plan. SaaS-based: manifests and dependency graphs are uploaded to Snyk’s infrastructure.
Best fit: Teams that want commercial-grade SCA for Java with good pipeline integration and less noise than NVD-only tools.
4. Sonatype Nexus Lifecycle
Sonatype Nexus Lifecycle is the commercial SCA counterpart to the widely used Nexus Repository. Sonatype has exceptional depth on the Java ecosystem because they operate the Maven Central proxy for most of the world.
What Nexus Lifecycle does well: The Sonatype data set on Java libraries is unusually deep. Their research team investigates components at a level most competitors do not match. Integration with Nexus Repository means you can enforce policies at the repository level: block downloads of vulnerable components before they even reach a build.
Where Nexus Lifecycle falls short: Commercial, enterprise-priced. Best suited to teams that already use Nexus Repository as their Maven artifact proxy. Simpler teams get most of the value from Dependency-Track plus OSS Index (which Sonatype runs).
Best fit: Enterprises standardized on Nexus Repository that want SCA policy enforcement at the proxy layer, not just the build layer.
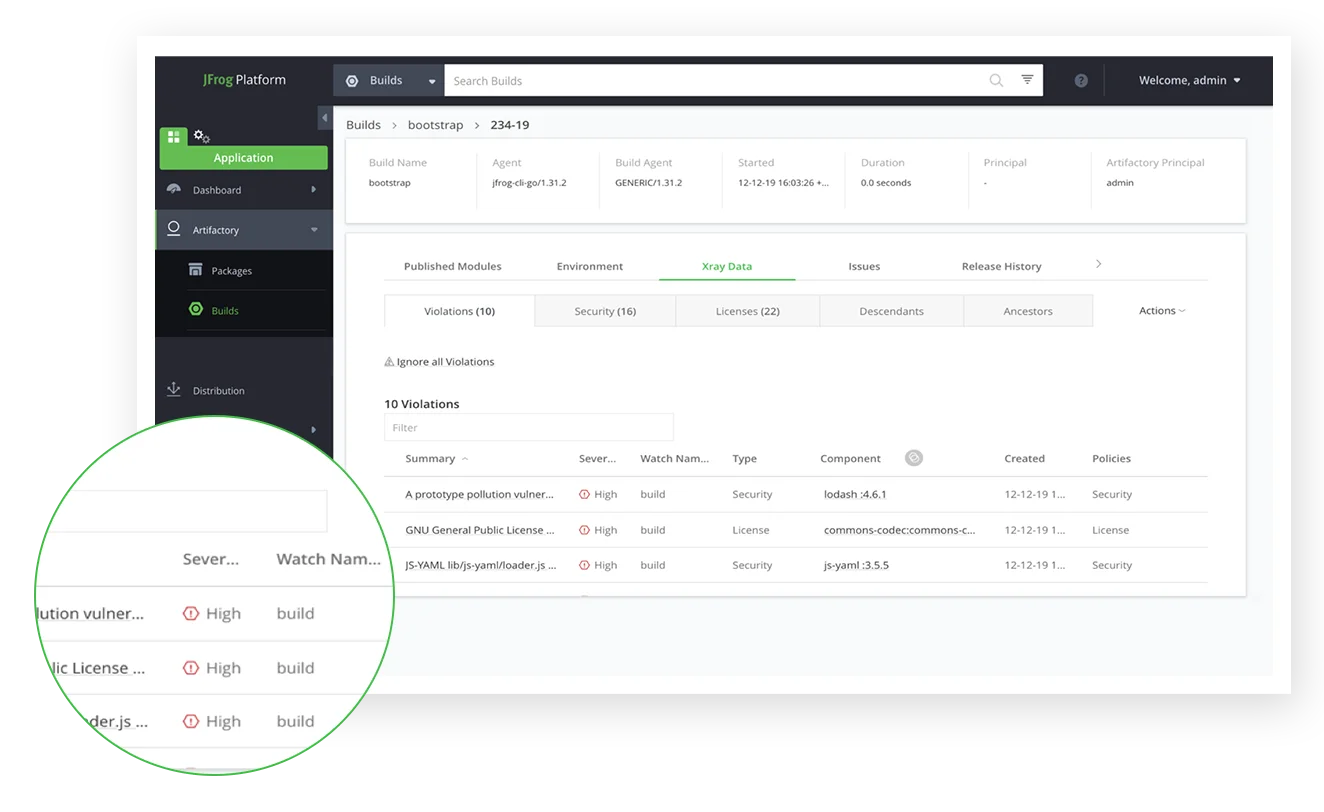
5. JFrog Xray
JFrog Xray is the SCA and compliance layer on top of JFrog Artifactory. Like Nexus Lifecycle it is deeply integrated with the repository manager, and JFrog has built a vulnerability research database (JFrog Security Research) that feeds Xray.
What Xray does well: If you already use Artifactory as your Maven and Gradle proxy, Xray bolts on cleanly. It scans artifacts in the repo, in builds, and inside Docker images. Binary-level impact analysis traces which downstream artifacts depend on a vulnerable component. Advanced contextual analysis can distinguish exploitable from non-exploitable instances of the same CVE.
Where Xray falls short: Commercial. Full value requires an Artifactory subscription. The pricing tiers can be complex to navigate.
Best fit: JFrog Artifactory customers. The integration value is significant, and Xray covers Java, Docker, npm, PyPI, and more from the same UI.
6. Trivy
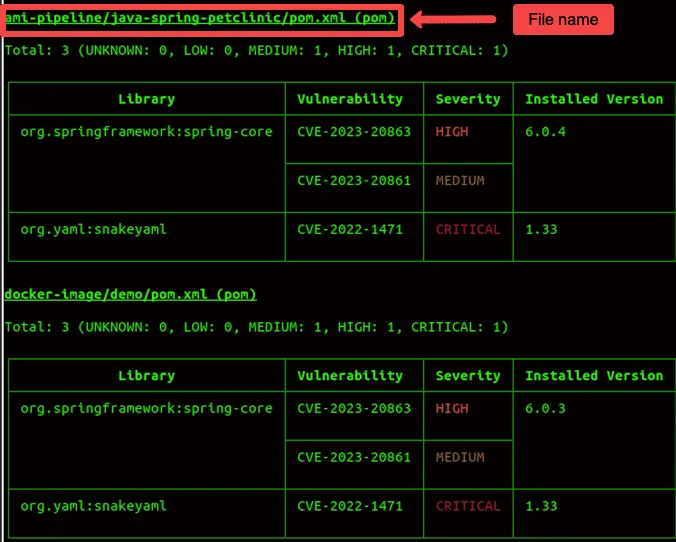
Trivy started as a container scanner and expanded to broad SCA coverage. For Java it reads pom.xml, gradle.lockfile, and scans JAR files directly, including inside container images.
What Trivy does well: Single static binary, no runtime dependencies, fast. Scans source code, Gradle lockfiles, and Docker images with the same CLI. Active maintenance and frequent database updates. Free and open source (Apache 2.0 ) under Aqua Security.
Where Trivy falls short: Shaded JAR handling is improving but not as deep as Snyk or Nexus. Reachability analysis is not supported. Gradle scanning is best when a gradle.lockfile exists; without one, transitive coverage is limited.
Best fit: Teams that already use Trivy for container image scanning and want to consolidate Java source SCA on the same tool. Also a good default if you want one scanner across source code, IaC, and images.
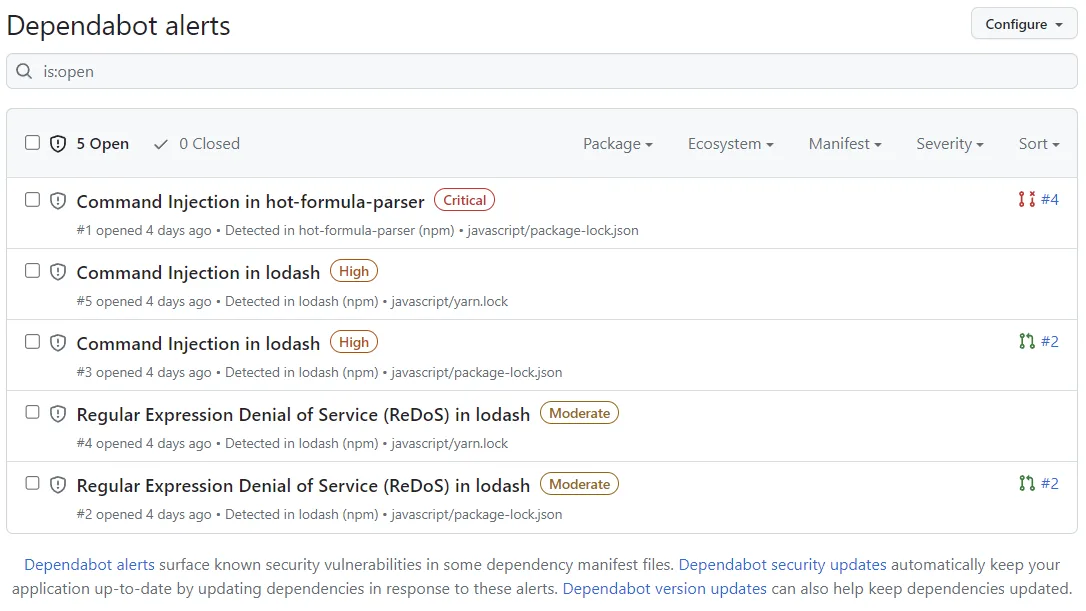
7. Dependabot
Dependabot
is GitHub’s built-in automated dependency updater and vulnerability alerter. It supports Maven and Gradle ecosystems (package-ecosystem: maven or gradle in dependabot.yml) and opens PRs for outdated or vulnerable components against the GitHub Advisory Database.
What Dependabot does well: Zero cost and zero maintenance for GitHub-hosted Java repos. Security updates are prioritized. The GitHub Advisory Database has broad Java coverage and updates faster than NVD for many advisories.
Where Dependabot falls short: GitHub-only. Gradle support is less robust than Maven (Gradle build scripts are Groovy or Kotlin code, so parsing is harder). It does not inspect JAR contents, so shaded JAR components are invisible to it. No license policy engine.
Best fit: GitHub-hosted Java projects that want automated update PRs alongside a deeper scanner like Dependency-Check or Snyk. Running both in parallel is a common pattern.
Comparison table
| Tool | CVE Detection | Shaded JAR | License Checks | Auto-fix PRs | License | Best For |
|---|---|---|---|---|---|---|
| OWASP Dependency-Check | NVD (evidence-based) | Limited | No | No | Open source | Free build-time gate |
| Dependency-Track | Multi-source via SBOM | Via SBOM | Limited | No | Open source | SBOM-driven enterprise SCA |
| Snyk Open Source | Deep + reachability | Yes | Yes | Yes | Free + Commercial | Commercial-grade SCA |
| Nexus Lifecycle | Deep, proprietary | Yes (binary) | Yes | Yes | Commercial | Nexus Repository customers |
| JFrog Xray | Deep, proprietary | Yes (binary) | Yes | Yes | Commercial | Artifactory customers |
| Trivy | Multi-source | Improving | Limited | No | Open source | Teams already using Trivy |
| Dependabot | GitHub Advisory DB | No | No | Yes (auto-PR) | Free (GitHub) | GitHub repos |
How to choose for your use case
Solo developer or small Java project. OWASP Dependency-Check in the build plus Dependabot on GitHub. Free, well-documented, catches the common issues. Add Trivy if you also build container images.
Growing team with several Spring Boot services. Dependency-Check as the per-build gate, a CycloneDX plugin to emit SBOMs, and Dependency-Track as the server of record. Dependabot for update PRs on GitHub. This stack is entirely free and scales to hundreds of services.
Enterprise team with compliance requirements. Snyk Open Source , Nexus Lifecycle , or JFrog Xray depending on which repository manager you standardized on. All three provide license policy, SBOM generation, audit trails, and role-based access control. Pair with Dependency-Track for a second opinion if you want vendor-neutral SBOM archiving.
Teams already running Trivy for containers. Use Trivy for Java source and JAR scanning too. Add Dependency-Check for evidence-based shaded JAR coverage where it matters.
Polyglot shop with Java plus Node.js plus Python. Snyk Open Source gives you a single pane of glass across ecosystems, which is valuable even if the per-ecosystem quality is slightly behind best-of-breed tools.
For the full picture on SCA tooling beyond Java, see the complete SCA tools list and the open-source SCA tools guide .
Open source vs commercial
Java SCA is one of the few areas where the open source stack is legitimately competitive with commercial tooling. The combination of OWASP Dependency-Check, Dependency-Track, and a CycloneDX plugin in the build covers CVE detection, SBOM archival, continuous re-scanning against new advisories, and multi-source advisory data without a single commercial invoice.
Commercial tools earn their spend on three axes.
Reachability analysis. Snyk Open Source identifies which vulnerable Java functions your code actually calls. On a large service portfolio, this cuts the weekly triage load significantly. Dependency-Check and Trivy flag every vulnerable JAR regardless of whether the vulnerable code path is reachable.
Repository manager integration. Nexus Lifecycle and JFrog Xray enforce policy at the Maven proxy layer. If a vulnerable or license-incompatible JAR is requested, the proxy can block the download before a build ever starts. Build-time scanners cannot match this.
License policy engines. Commercial tools run per-organization license policies that flag GPL, AGPL, or unusual custom licenses across the full transitive tree and can block the build. Dependency-Track does some license tracking but does not match the policy engine depth of Snyk, Nexus, or JFrog.
The practical recommendation: start free with Dependency-Check, Dependency-Track, and Dependabot. Graduate to a commercial platform when reachability analysis, repository-layer enforcement, or a formal license policy engine become hard requirements.
If your stack also uses other ecosystems, the dedicated SCA picks for Node.js and TypeScript and Python cover the tool nuances that a generic SCA list misses.






