Renovate Alternatives: 7 Best Dependency Update Tools in 2026
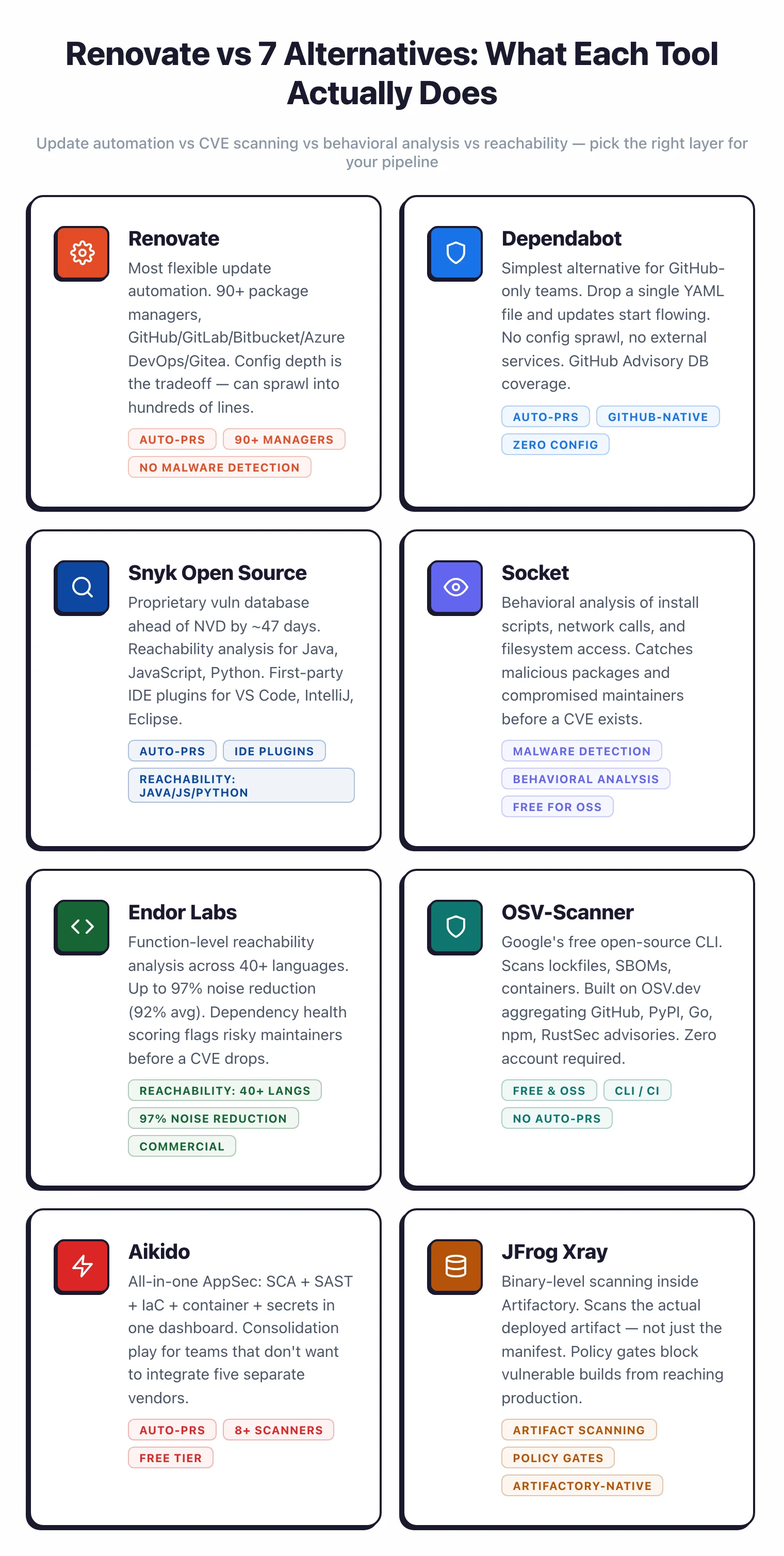
Renovate is powerful but its config can sprawl. Compare the best Renovate alternatives in 2026 — Dependabot, Snyk Open Source, Socket, Endor Labs, and more.
- Renovate supports 90+ package managers across GitHub, GitLab, Bitbucket, Azure DevOps, and Gitea (as of 2026), but its configuration depth is also its biggest complaint — most teams seeking alternatives want simpler config, better IDE integration, or lower maintenance overhead.
- [Dependabot](/dependabot) is the simplest alternative for GitHub-only teams: drop a YAML file into `.github/` and you are done, with no external services or config sprawl.
- According to Snyk, its proprietary database catches CVEs an average of 47 days before NVD, and [Snyk Open Source](/snyk-open-source) bundles automated fix PRs with IDE plugins for VS Code, IntelliJ, and Eclipse.
- [Socket](/socket) detects malicious packages through behavioral analysis of install scripts and network access — threats that neither Renovate nor CVE-based tools catch.
- According to Endor Labs, its function-level reachability analysis across 40+ languages achieves up to 97% noise reduction (92% average across customers) — analysis that Renovate does not perform.
The best Renovate alternatives in 2026 are Dependabot , Snyk Open Source , Socket , Endor Labs , and OSV-Scanner . Each addresses a gap Renovate’s update automation does not cover.
Dependabot is the zero-configuration choice for GitHub-only teams — a single YAML file in .github/ enables automated dependency updates with no external services or config sprawl.
Snyk Open Source adds a proprietary vulnerability database that catches CVEs an average of 47 days before NVD, plus IDE plugins for VS Code, IntelliJ, and Eclipse that Renovate lacks entirely.
Socket detects malicious packages through behavioral analysis of install scripts and network access — threats that neither Renovate nor CVE-based scanners catch.
Endor Labs performs function-level reachability analysis across 40+ languages and reports up to 97% noise reduction (92% average across customers), filtering out vulnerabilities in code paths your application never executes. OSV-Scanner is a free CLI option built on Google’s OSV.dev database for teams that want vulnerability scanning without vendor lock-in.
| Alternative | Best for | License |
|---|---|---|
| Dependabot | GitHub-only teams, zero config | Free |
| Snyk Open Source | CVE-first with 47-day NVD lead time | Freemium |
| Socket | Malicious package behavioral detection | Freemium |
| Endor Labs | Reachability analysis, noise reduction | Commercial |
| Mend SCA | Enterprise control, SLA support | Commercial |
When Dependabot is enough: teams on GitHub with straightforward dependencies and no need for regex managers or multi-platform support. When to stay on Renovate: teams on GitLab, Bitbucket, or Azure DevOps, or teams that need fine-grained grouping, scheduling, and automerge rules across 90+ package managers.
Why Look for Renovate Alternatives?
Renovate is an open-source dependency update bot that supports 90+ package managers across GitHub, GitLab, Bitbucket, Azure DevOps, and Gitea under an AGPL-3.0 license . Mend maintains the project and offers a free hosted app for GitHub and GitLab. For teams that need fine-grained control over how updates flow into their codebase, it is hard to beat.
The problem is that same configurability. Renovate’s config file can grow into hundreds of lines once you add package rules, schedules, grouping, automerge conditions, and regex managers for custom file formats. Presets help, but understanding which preset does what still requires reading the docs.
Note: Teams that adopted Renovate for "just keep my deps current" often find themselves maintaining a config that feels like its own small codebase. The hosted Mend app helps, but org-wide presets and advanced automerge rules still require significant upfront investment to get right.
Beyond config complexity, Renovate has gaps that matter for security-focused teams. It does not perform reachability analysis, so it cannot tell you whether a vulnerable function is actually called from your code. It does not detect malicious packages through behavioral analysis. It relies on whatever vulnerability data the host Git platform provides rather than a proprietary database.
IDE integration is another weak spot. Renovate is a CI-side bot that opens pull requests; there is no VS Code or IntelliJ plugin that flags risky dependencies while you code. For developers who want vulnerability context inside the editor, Renovate alone is not enough.
For teams drowning in update PRs, Renovate’s “here is every update, you decide” approach can feel like noise rather than signal. These are the three main reasons I see teams look elsewhere: simpler config, better IDE-adjacent vulnerability context, or lower maintenance cost.
Top Renovate Alternatives
1. Dependabot
Dependabot
is GitHub’s built-in dependency update tool, acquired by GitHub in 2019 and now deeply integrated with the GitHub Advisory Database. It is free with no usage limits and is configured with a single dependabot.yml file
in .github/. For GitHub-centric teams, it is the simplest path to automated dependency updates.
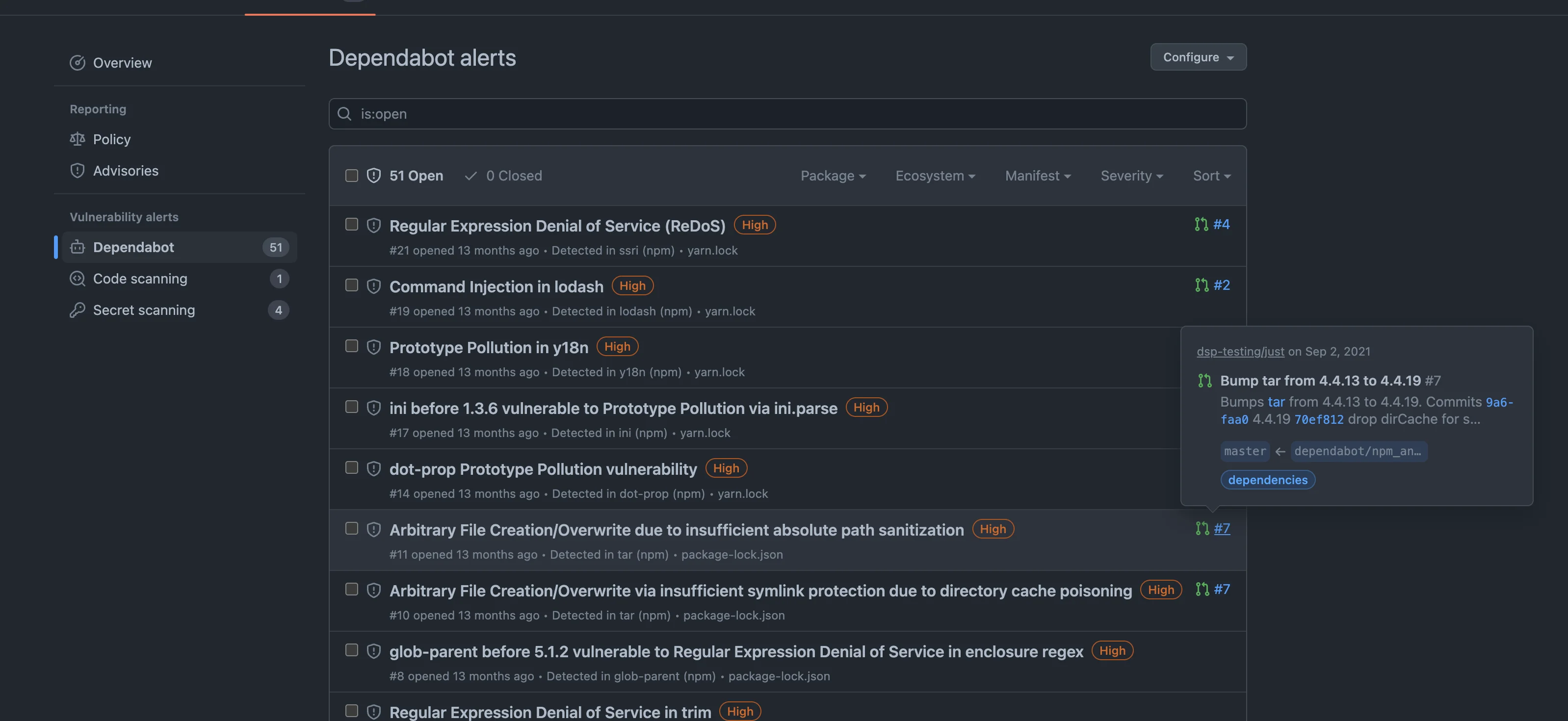
The tradeoff is straightforward. Dependabot only works on GitHub — there is no GitLab, Bitbucket, or Azure DevOps support, no self-hosted option, and no CLI you can run outside the GitHub ecosystem. Its 30+ package ecosystems cover most mainstream stacks, but Renovate’s 90+ is noticeably broader.
Where Dependabot wins is setup time and maintenance. Turn on security alerts in settings, drop a YAML file to enable version updates, and you are done. For small teams with a handful of GitHub repositories and straightforward update needs, that is all that matters.
Dependabot added grouped updates in 2023 , which narrowed Renovate’s historical lead on grouping. It still lacks Renovate’s regex managers, shared organization presets, and advanced scheduling. For teams that never used those features anyway, Dependabot is a cleaner fit.
Best for: GitHub-only teams that want automated dependency updates without config sprawl. License: Free (GitHub-native). Key difference: Zero-config setup on GitHub. No multi-platform support, no self-hosting, no regex managers.
Dependabot review · Dependabot alternatives
2. Snyk Open Source
Snyk Open Source is a commercial SCA tool that goes beyond dependency updates into full vulnerability scanning. It opens automated fix pull requests, continuously monitors your dependencies for newly disclosed issues, and integrates with GitHub, GitLab, Bitbucket, Azure DevOps, and any CI/CD system through its CLI.
The main differentiator is Snyk’s proprietary vulnerability database. According to Snyk, its research team identifies and documents CVEs an average of 47 days before they appear in public databases like NVD or GitHub Advisories.
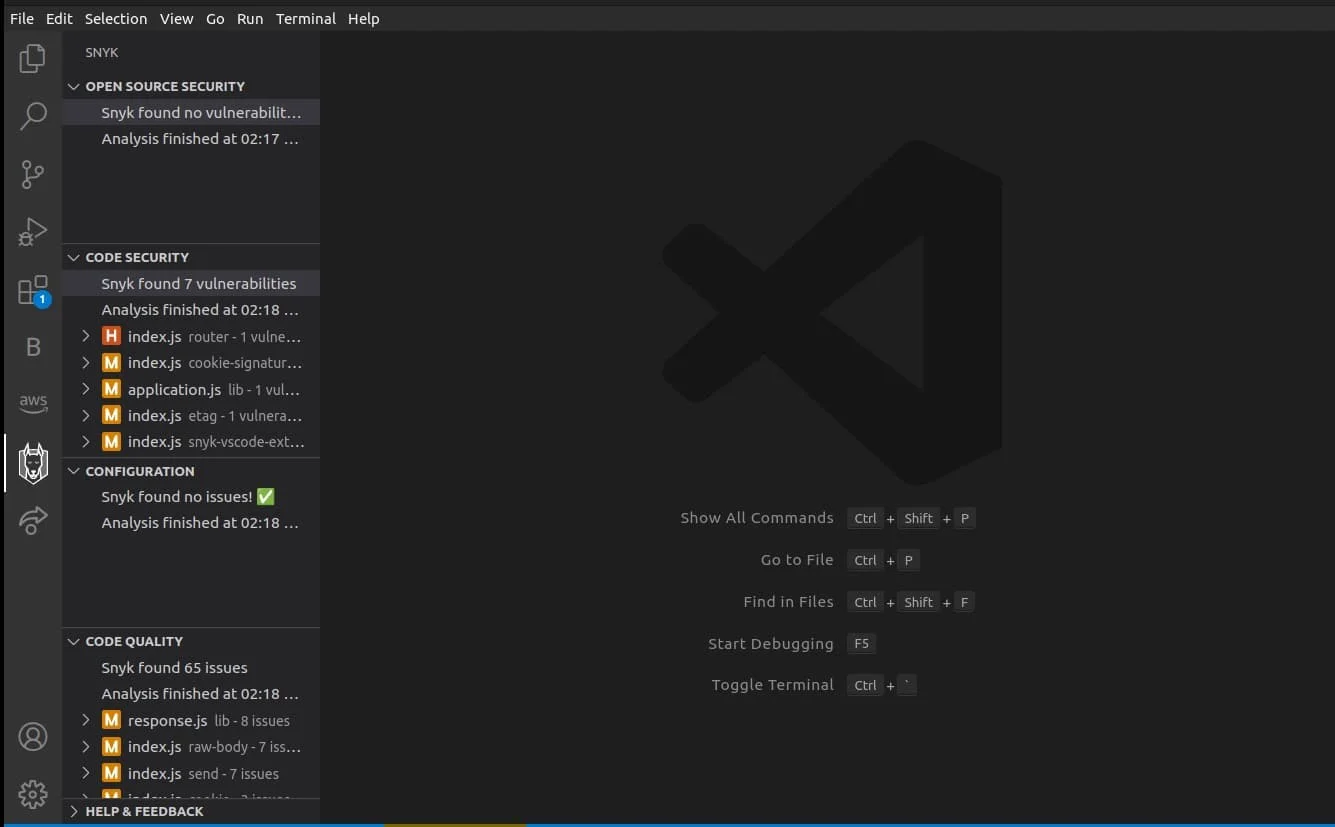
For organizations where early patching matters, that lead time is real value. Snyk also offers reachability analysis for Java, JavaScript, and Python , which filters out vulnerabilities in functions your application never calls.
Snyk’s IDE plugins are the second differentiator. VS Code, IntelliJ, Eclipse, and PyCharm all have first-party Snyk plugins that flag vulnerable dependencies as you edit. Renovate has no equivalent — its feedback loop is the pull request, not the editor.
The free tier caps at 200 tests per month, which is enough for solo developers or small teams but not for organizations scanning dozens of repositories. Paid plans scale with project count and contributors.
Best for: Teams that want a richer vulnerability database with IDE integration and fix PRs. License: Freemium. Key difference: Proprietary database catches CVEs an average of 47 days earlier than public sources, according to Snyk. First-party IDE plugins. Reachability analysis for Java, JavaScript, and Python.
3. Socket
Socket is a supply chain security tool that analyzes what packages actually do rather than matching versions against CVE databases. It inspects install scripts, network access patterns, filesystem operations, and environment variable reads to detect malicious packages, typosquatting, and compromised maintainer accounts.
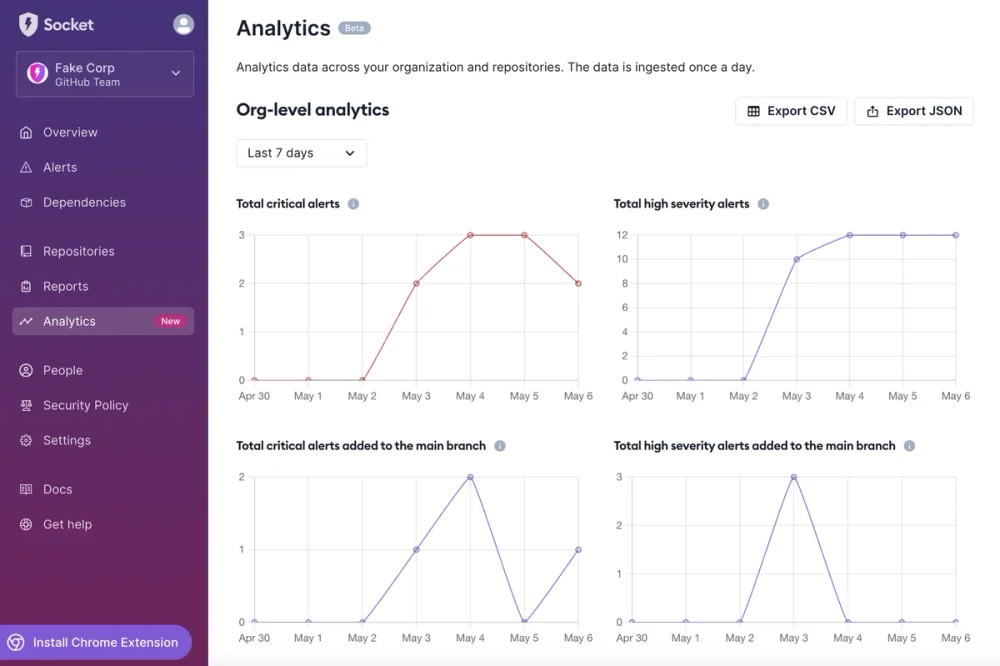
This behavioral approach catches threats that neither Renovate nor CVE-based scanners see. A newly published malicious package has no CVE. A compromised maintainer pushing a backdoored update will not trigger a vulnerability alert until someone discovers and reports it. Socket catches these scenarios by flagging suspicious behavior regardless of whether an advisory exists.
Key Insight
Socket's behavioral analysis and Renovate's update automation solve different problems. Renovate automates the mechanics of keeping dependencies current; Socket catches malicious packages before they reach production. Many teams run both layers — Renovate opens the PRs, Socket gates what merges.
Socket is commercial but free for open-source projects. It integrates with GitHub and GitLab pull requests, flagging risky dependency changes before they merge. Install the app and it works with no additional config required.
For teams that already run Renovate for update automation, Socket layers on supply chain security that Renovate cannot provide. The combination gives you both automated update mechanics and behavioral threat detection.
Best for: Teams worried about supply chain attacks and malicious packages. License: Commercial (free for open-source). Key difference: Behavioral analysis of install scripts, network calls, and filesystem access. Catches malicious packages Renovate cannot see.
4. Endor Labs
Endor Labs is a commercial SCA platform built to solve alert overload. Most SCA tools report every known vulnerability in your dependency tree, regardless of whether the vulnerable code is reachable from your application. Endor Labs performs function-level reachability analysis across 40+ languages and reports up to 97% noise reduction (92% average across customers), according to the company.
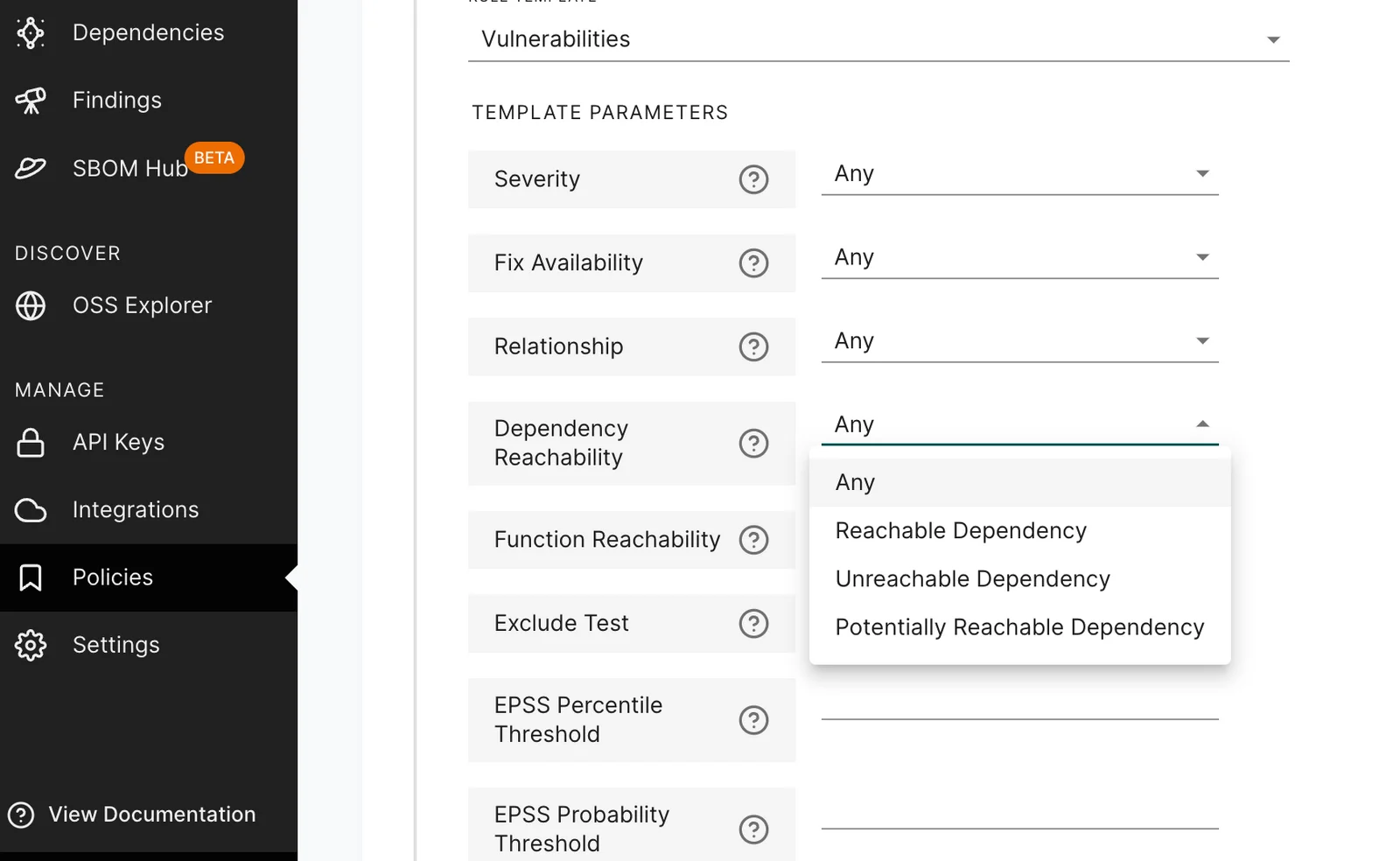
If the vulnerable function in a transitive dependency is never called from your code, the alert gets deprioritized. That means your team focuses on the vulnerabilities that can actually be reached in production.
The platform also scores dependency health by tracking maintenance activity, release cadence, and contributor patterns. A package with no releases in two years and a quiet sole maintainer gets flagged as a risk even when no CVE exists yet.
Key Insight
Endor Labs is designed for teams whose Renovate-plus-scanner pipeline generates more alerts than engineers can triage. Function-level reachability filters out the 90%+ of vulnerabilities in code paths your application never executes, letting the team focus on what actually matters.
Endor Labs is aimed at mid-to-large engineering organizations where alert triage consumes meaningful engineering time. If your Renovate-plus-scanner pipeline generates more alerts than your team can triage, that is exactly the problem Endor Labs addresses.
Best for: Teams drowning in vulnerability alerts who need intelligent noise reduction. License: Commercial. Key difference: Function-level reachability analysis across 40+ languages — up to 97% noise reduction (92% average across customers per Endor Labs). Dependency health scoring flags risky packages before CVEs exist.
5. OSV-Scanner
OSV-Scanner is Google’s open-source vulnerability scanner built on the OSV.dev database . It scans lockfiles, SBOMs, container images, and Git repositories for known vulnerabilities across Go, JavaScript, Python, Rust, Java, and more. A single static binary makes it easy to drop into any CI/CD pipeline without agents or long-lived services.
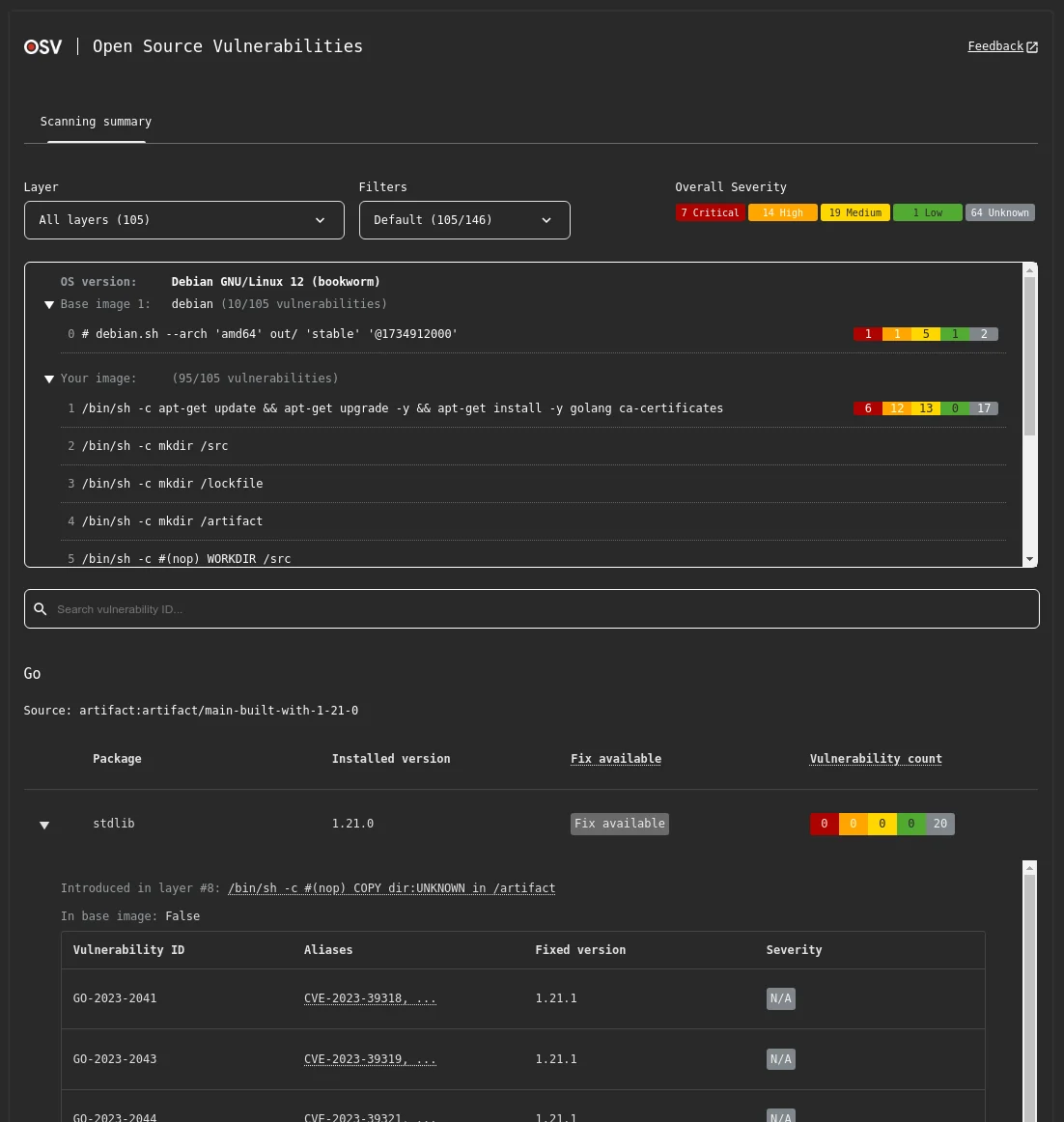
OSV-Scanner does not open update pull requests — that is not its job. If you want automated remediation, you still need Renovate or Dependabot for the update mechanics. What OSV-Scanner adds is a fast, free, Google-maintained vulnerability check that runs locally or in CI with zero account setup.
The OSV.dev database aggregates advisories from GitHub, PyPI, Go, npm, RustSec, and other upstreams, giving broader coverage than any single ecosystem’s advisories alone.
Pro tip: OSV-Scanner and Renovate are an effective free pairing — Renovate opens PRs to keep dependencies current, OSV-Scanner blocks CI on known vulnerabilities. The OSV.dev database is open and aggregates advisories from GitHub, PyPI, npm, Go, and RustSec, so coverage is broad without needing a vendor account.
For teams that want a lightweight, open-source vulnerability check alongside Renovate, OSV-Scanner is the obvious pick. It is CLI-only, scripts cleanly into CI, and has no vendor lock-in.
Best for: Teams that want a free, CLI-based vulnerability scanner alongside their update tool. License: Open-source (Apache 2.0). Key difference: Built on OSV.dev, a Google-maintained distributed vulnerability database. Single binary, no account, CLI-first.
6. Aikido
Aikido is an all-in-one SaaS platform used by 50,000+ organizations (per Aikido’s Series B press release, January 2026) that bundles SCA, SAST , IaC scanning , container scanning, and secrets detection in a single dashboard. For dependency management specifically, it combines vulnerability scanning with automated fix suggestions and integrates with GitHub, GitLab, Bitbucket, and Azure DevOps.
The core pitch is consolidation. Instead of running Renovate for updates, a separate SCA tool for vulnerabilities, and a third tool for container scans, Aikido handles all of it from one dashboard.
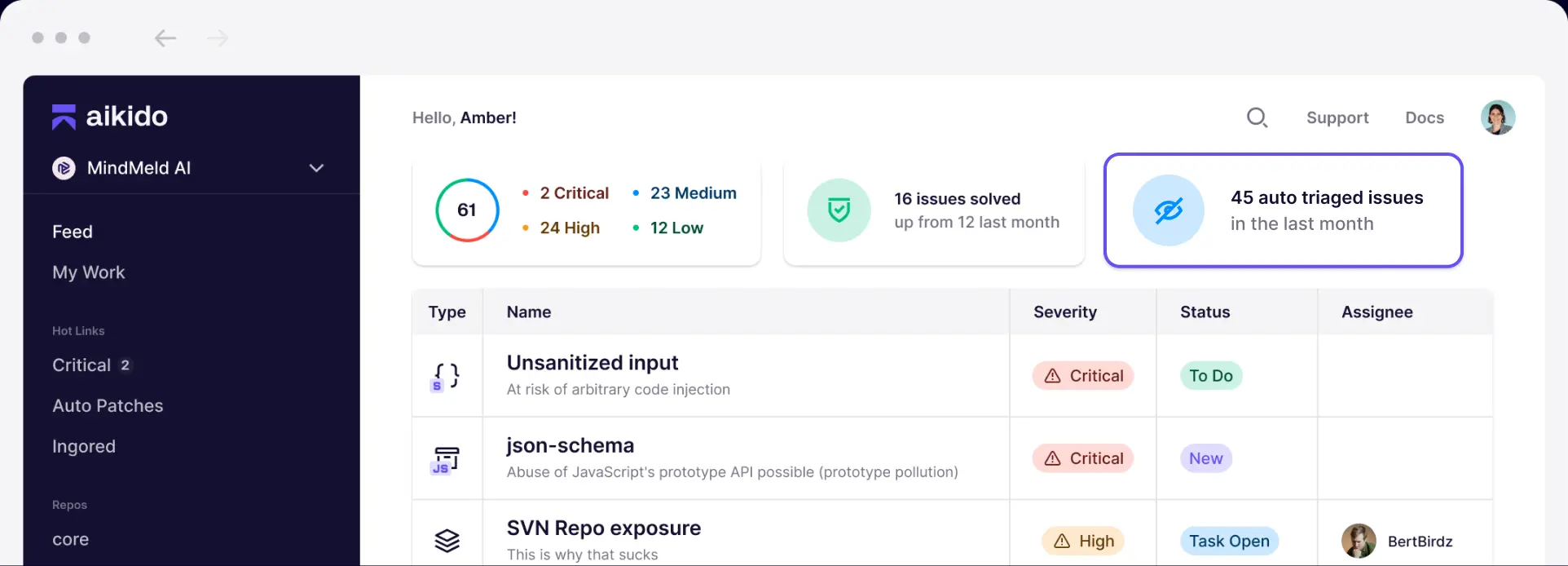
That reduces maintenance overhead and gives security teams a single view across the codebase.
Aikido is commercial with a free tier that covers small teams. The all-in-one approach trades depth for breadth. None of its individual capabilities match what a specialist tool like Snyk or Endor Labs offers in its niche, but the combined footprint is useful for teams that do not want to integrate five different vendors.
For teams choosing Renovate primarily because it was free and configurable, Aikido is worth evaluating once the hidden cost of stitching multiple tools together becomes visible.
Best for: Teams that want one platform covering SCA, SAST, IaC, containers, and secrets instead of Renovate plus separate tools. License: Commercial (free tier available). Key difference: All-in-one AppSec platform. Consolidates update automation, vulnerability scanning, and container scanning in one dashboard.
7. JFrog Xray
JFrog Xray is a commercial security scanner that analyzes compiled artifacts stored in JFrog Artifactory rather than source-level manifest files. This matters because what you deploy is not always what your manifest declares — build tools resolve dependencies, apply overrides, and pull in transitives that may not match the lock file. Xray scans the actual binary artifact, catching issues that source-level scanners miss.
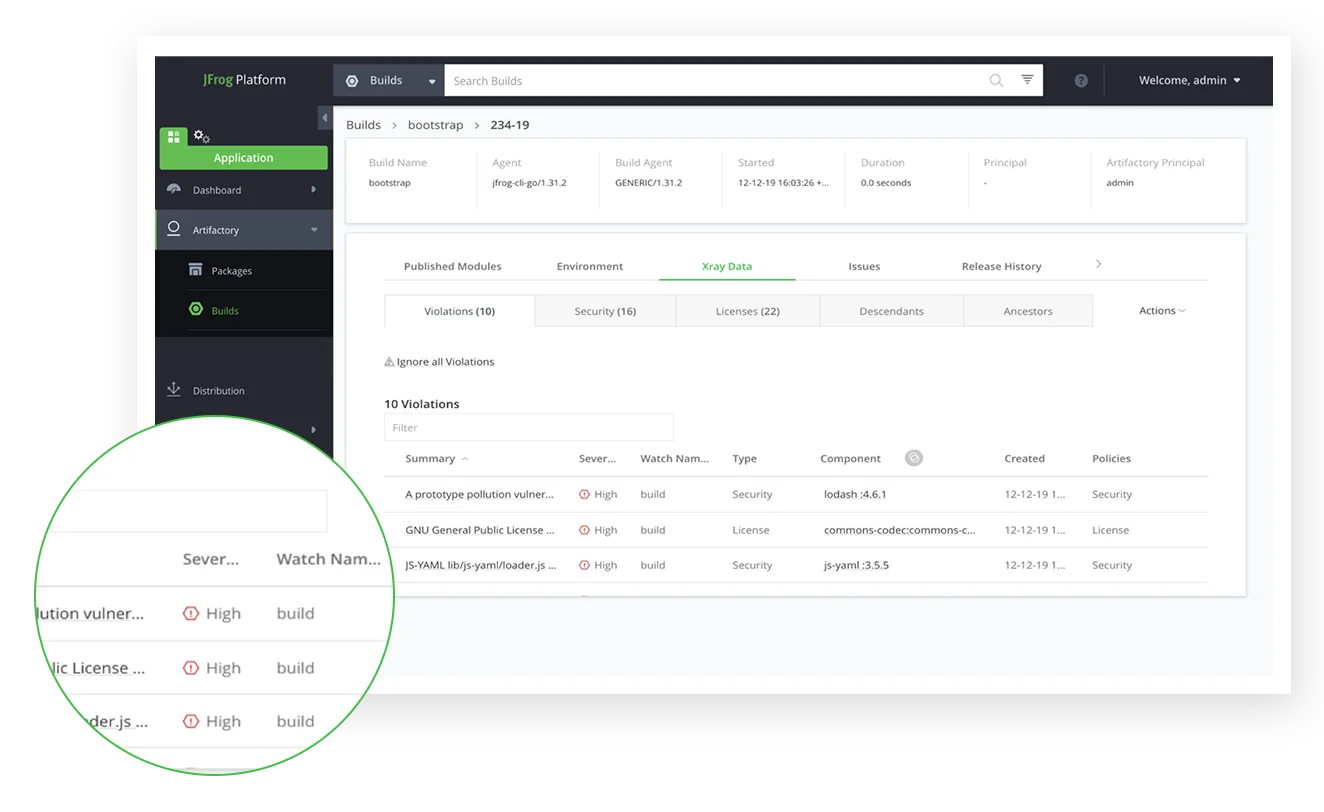
The platform performs deep recursive analysis of container images, binaries, and packages. It maintains a vulnerability intelligence database covering millions of open-source packages and offers impact analysis that traces how a vulnerable component propagates through your artifact repository. Policy gates can block vulnerable artifacts from being promoted to production registries.
JFrog Xray is most valuable for teams already running Artifactory. The tight integration means scanning happens automatically as artifacts are uploaded, with no separate CI/CD step required.
For teams not using Artifactory, adopting Xray means adopting the entire JFrog platform, which is a significant commitment. Renovate and Xray can sit side by side: Renovate for update automation at source level, Xray for vulnerability scanning at the binary level.
Best for: Teams using JFrog Artifactory that want binary-level scanning of deployment artifacts. License: Commercial. Key difference: Scans compiled artifacts in Artifactory rather than source manifests. Impact analysis across your entire artifact repository.
Feature Comparison
| Feature | Renovate | Dependabot | Snyk OSS | Socket | Endor Labs | OSV-Scanner | Aikido | JFrog Xray |
|---|---|---|---|---|---|---|---|---|
| License | Open-source | Free | Freemium | Commercial | Commercial | Open-source | Freemium | Commercial |
| Auto fix PRs | Yes | Yes | Yes | No | Yes | No | Yes | No |
| Platforms | GitHub, GitLab, Bitbucket, Azure DevOps, Gitea | GitHub only | Multi-platform | GitHub, GitLab | Multi-platform | CLI/CI | Multi-platform | Multi-platform |
| Package managers | 90+ | 30+ | Major ecosystems | Major ecosystems | 40+ languages | Major ecosystems | Major ecosystems | Multi-ecosystem |
| Reachability | No | No | Java, JS, Python | No | Yes (broad) | No | Limited | No |
| Malicious package detection | No | Limited | Limited | Core feature | Yes | No | Yes | Limited |
| IDE integration | No | Basic (GitHub UI) | First-party plugins | Limited | Plugins | No | Plugins | Limited |
| Config complexity | High | Low | Low | Low | Medium | Low | Low | Medium |
| Self-hosted | Yes | No | Enterprise | No | Yes | Yes (CLI) | No | Yes |
| Vuln database | Uses host platform | GitHub Advisory DB | Proprietary | Behavioral | Multiple + health | OSV.dev | Multiple | Multiple |
When to Stay with Renovate
Renovate is still the right tool in several situations. Here is when I would keep it:
- You run on more than one Git platform. Renovate works on GitHub, GitLab, Bitbucket, Azure DevOps, and Gitea from a single config. Dependabot only covers GitHub, so a mixed platform setup means running two tools unless you centralize on Renovate.
- You need 90+ package managers. Renovate covers ecosystems most alternatives never touch: Helm, Terraform, Kustomize, Gradle catalogs, and custom regex managers for internal file formats. If your stack leans uncommon, Renovate is likely the only option that works out of the box.
- You need granular update rules. Group minor and patch updates but split majors. Different schedules per ecosystem. Automerge trusted packages with passing tests. Shared presets across every repo in the org. Renovate’s config depth is painful to learn, but it unlocks workflows nothing else matches.
- You want a free, open-source tool with no vendor lock-in. Renovate is AGPL-3.0 with a free hosted app from Mend. You can self-host the CLI or Docker image. No paid tiers, no usage caps.
- You already pair Renovate with a scanner. Many teams run Renovate for update mechanics and Snyk , Socket , or Endor Labs for deeper vulnerability and supply-chain analysis. If that split already works, swapping Renovate out usually creates more friction than it solves.
For more AppSec Santa SCA comparisons, see the SCA tools category or the Dependabot alternatives page.
Frequently Asked Questions
What is the best alternative to Renovate for GitHub-only teams?
.github/dependabot.yml. You lose Renovate’s multi-platform reach and advanced grouping controls, but you also lose the configuration sprawl that makes Renovate hard to maintain at scale. For GitHub-only teams with straightforward update needs, Dependabot is the path of least resistance.Is Dependabot better than Renovate?
Does Renovate detect vulnerabilities?
Which tool has the lowest maintenance overhead for dependency updates?
Can I use Renovate and another SCA tool together?

Founder, AppSec Santa
Years in application security. Reviews and compares 215 AppSec tools across 12 categories to help teams pick the right solution. More about me →






