- [OSV-Scanner](/osv-scanner) queries Google's OSV.dev, which aggregates GitHub Security Advisories, PyPA, RustSec, Go, Maven, npm, Debian, Alpine, and 20+ other upstream sources into one schema.
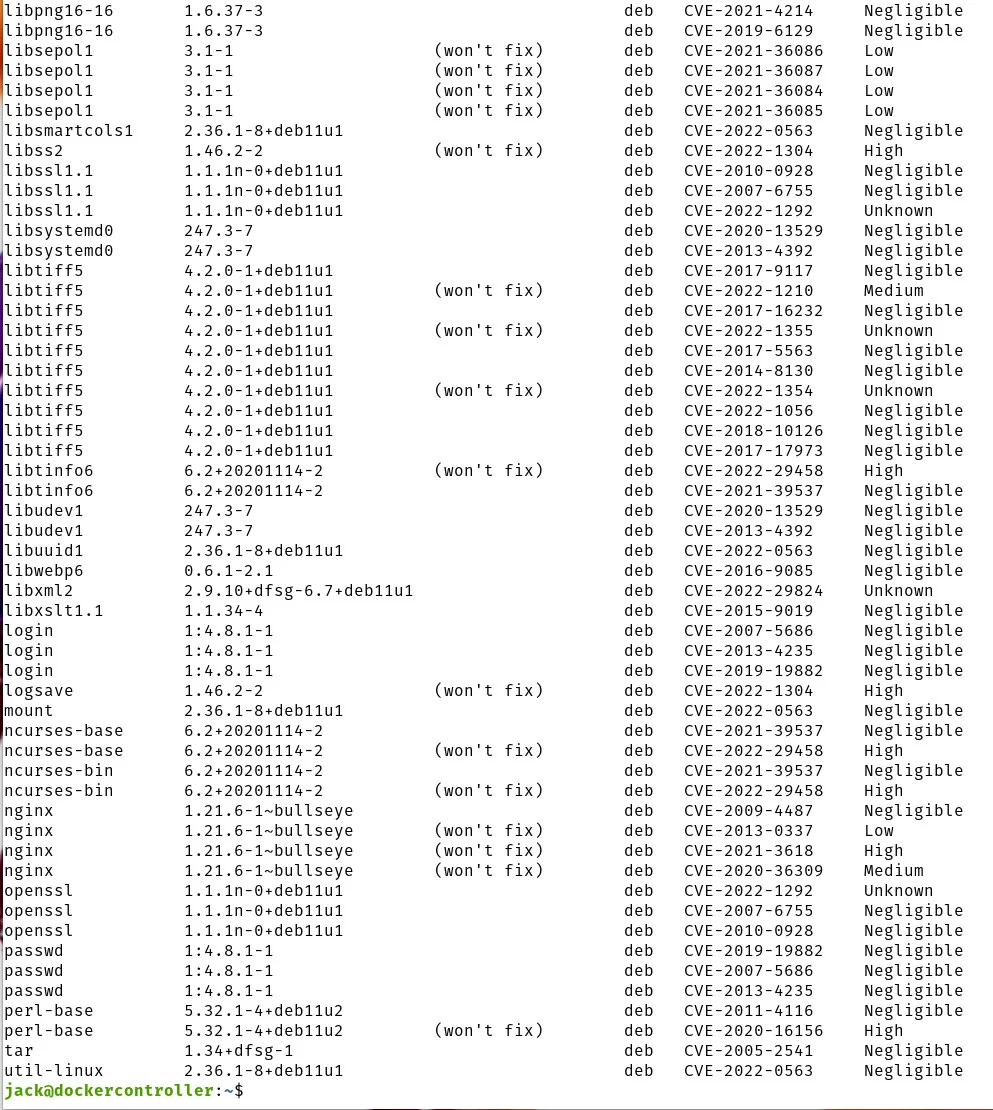
- [Grype](/grype) uses Anchore's Vunnel ETL pipeline to build a local SQLite database from NVD, GitHub Advisories, and Linux distro feeds (Debian, Red Hat, Ubuntu, Amazon, Oracle).
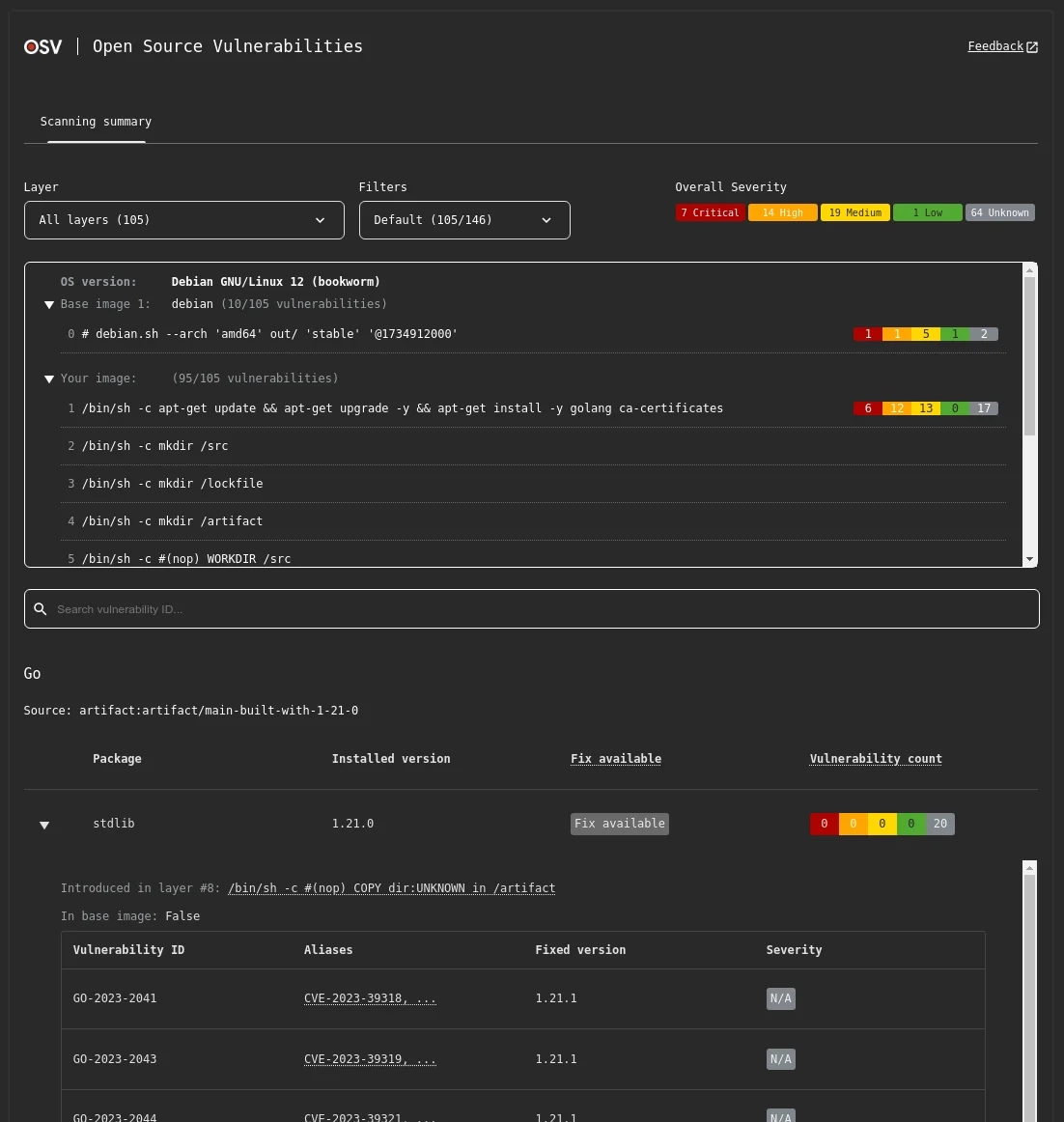
- Grype scans container images, OCI archives, and Singularity images natively; OSV-Scanner v2.0 (released March 2025) rewrote container image scanning with layer-aware support for Debian, Ubuntu, and Alpine.
- Both output JSON and SARIF and offer official GitHub Actions, but only Grype ships license detection via its Grant companion tool.
- OSV-Scanner is Apache 2.0 from Google; Grype is Apache 2.0 from Anchore. Neither has a paid tier, usage cap, or telemetry requirement.
Which Is Better: OSV-Scanner or Grype?
OSV-Scanner is Google’s frontend to the OSV.dev database — an aggregator that pulls 20+ upstream advisory sources into a single unified schema. It shines on language manifests and lockfiles.
Grype is Anchore’s focused vulnerability matcher, built to pair with Syft for an SBOM-first workflow. It ships with deeper coverage for Linux distro packages and container images.
Pick OSV-Scanner for lockfile-first scanning in CI. Pick Grype for container images and OS packages.
What Are the Key Differences?
| Feature | OSV-Scanner | Grype |
|---|---|---|
| License | Apache 2.0 | Apache 2.0 |
| Maintained By | Anchore | |
| Primary Database | OSV.dev (20+ aggregated sources) | Grype DB (NVD + GHSA + distro feeds) |
| Data Schema | OSV schema (open standard) | Proprietary SQLite, built via Vunnel |
| Container Image Scanning | Yes (v2.0+, layer-aware for Debian/Ubuntu/Alpine) | Yes (native, Docker/OCI/Singularity) |
| Lockfile / Manifest Scanning | Yes (primary use case) | Yes (via Syft cataloging) |
| OS Package Coverage | Alpine, Debian, Ubuntu | Alpine, Debian, Ubuntu, RHEL, Amazon, Oracle, SUSE, Arch |
| License Detection | No | Yes (via companion tool Grant) |
| SBOM Input | SPDX, CycloneDX | SPDX, CycloneDX, Syft JSON |
| Output Formats | Table, JSON, SARIF, Markdown, HTML, CycloneDX | Table, JSON, SARIF, CycloneDX, template |
| Risk Scoring | Severity (CVSS) | Composite score (CVSS + EPSS + KEV) |
| OpenVEX Support | Yes | Yes |
| GitHub Action | google/osv-scanner-action | anchore/scan-action@v7 |
| Offline Mode | Yes (via –offline-vulnerabilities) | Yes (via –offline cache) |
| Language | Go | Go |
Database & Coverage
This is the biggest philosophical split between the two tools. OSV.dev is an aggregator, not a source.
Google built the OSV schema as a common format for vulnerability data, then wrote importers for GitHub Security Advisories, PyPA Advisory Database, RustSec, the Go vulnerability database, npm, Maven, Debian Security Tracker, Alpine SecDB, and more. Each advisory lands in OSV.dev with a precise affected-version range per ecosystem.
Grype takes a different path. Anchore’s Vunnel ETL tool pulls from NVD, GitHub Security Advisories, Alpine, Debian, Red Hat, Ubuntu, Amazon Linux (ALAS), Oracle Linux (ELSA), and SUSE, then normalizes everything into a local database the CLI ships with.
The practical difference shows up in false positives. For Linux distro packages, Grype’s vendor-specific feeds (Debian DSA, Red Hat OVAL) are more accurate than NVD alone. Teams that scan RHEL or Ubuntu containers often see cleaner results from Grype.
Both databases update daily. Neither requires a key or a paid subscription.
Ecosystem & Container Support
OSV-Scanner
was built for source-code scanning first. Point it at a directory and it walks lockfiles: package-lock.json, yarn.lock, Pipfile.lock, poetry.lock, go.sum, Cargo.lock, Gemfile.lock, composer.lock, pom.xml, and more.
OSV-Scanner v2.0 (March 2025) rewrote container image scanning from scratch with layer-aware support. It now reports which layer introduced a package, the base image, and OS distribution — covering Alpine, Debian, and Ubuntu-based images. Support for additional distros is narrower than Grype’s.
Grype is container-native. It reads Docker daemons, registries, Docker archives, OCI directories, OCI archives, and Singularity images directly, with Syft doing the cataloging step in process.
Grype’s language ecosystem coverage is comparable to OSV-Scanner’s on the most common stacks (Go, Java, JavaScript, Python, Ruby, PHP, Rust, .NET).
If containers are your primary target, start with Grype. If you are scanning source repositories and lockfiles in pull requests, start with OSV-Scanner.
Output & CI Integration
Both tools are CI-friendly. OSV-Scanner outputs table, JSON, SARIF, Markdown, HTML, and CycloneDX.
The official action is google/osv-scanner-action, which includes a reusable workflow that posts findings as pull request comments. SARIF integrates with GitHub code scanning and GitLab.
Grype outputs table, JSON, SARIF, CycloneDX, and custom Go templates. The official action is anchore/scan-action@v7, also integrating with GitHub code scanning via SARIF.
Grype includes a composite risk score combining CVSS severity, EPSS exploit probability, and KEV catalog status. When a vulnerability appears in CISA’s KEV catalog, Grype treats it as maximum-threat regardless of EPSS — observed exploitation outweighs predicted exploitation. OSV-Scanner does not have an equivalent scoring model.
OSV-Scanner has one quiet advantage for auditability: its output references OSV IDs, which link back to the original upstream advisory (GHSA, GO, PYSEC, RUSTSEC). Grype output references CVE and vendor IDs. Neither is wrong, but OSV’s provenance trail is more transparent.
Both tools support OpenVEX for suppressing findings the security team has already assessed. Both support offline mode, which matters in air-gapped environments.
Performance Reality
For a typical monorepo with a few dozen lockfiles, OSV-Scanner
finishes in under five seconds locally. Its default mode queries the OSV.dev API, which adds some network time. The --offline-vulnerabilities flag downloads the full database and runs fully local, which is faster in CI and required in air-gapped setups.
Grype always runs against its local database. The current v6 schema database downloads at around 65 MB — a significant reduction from earlier versions thanks to a 2025 schema overhaul. A fresh install pulls the database on first run; subsequent scans use the cached copy.
On container images, Grype is typically faster because the cataloging and matching happen in one process. OSV-Scanner’s container path adds a separate matching step after package extraction.
For a 500 MB Debian-based container, both tools finish in under 30 seconds on a modern laptop. Neither is slow enough to notice in CI.
Memory use is similar. Both tools stay under 500 MB of RSS on typical workloads.
Which to Pick
Choose OSV-Scanner if:
- Your scan target is a source repo with lockfiles (npm, PyPI, Go, Cargo, Maven, RubyGems, Composer)
- You want tight version-range matching with fewer false positives on language ecosystems
- Google-backed provenance and the OSV schema’s traceability matter
- You need markdown or HTML output for human-facing reports
- You scan newer ecosystems like Dart pub, Swift Package Manager, or Haskell Hackage
Choose Grype if:
- Your scan target is a container image or Linux filesystem
- You want the composite risk score (CVSS + EPSS + KEV) for triage by exploit probability
- License detection via the Grant companion tool is part of your workflow
- You already use Syft for SBOM generation
- You need deep OS package coverage across Alpine, Debian, Ubuntu, RHEL, Amazon, Oracle, and SUSE
Many teams run both. OSV-Scanner in the pull request pipeline for lockfile scanning, Grype on the built container image before push.
The two databases are different enough that the overlap catches issues either tool alone would miss. Neither replaces a full ASPM or dependency-track deployment, but for free CLI scanning, OSV-Scanner and Grype cover most practical SCA needs.
Both tools are also commonly compared against Trivy , the Aqua Security scanner that bundles SCA, IaC, and secrets detection into one binary. For more options, browse AppSec Santa’s SCA tools category.
Frequently Asked Questions
Is OSV-Scanner better than Grype?
Are OSV-Scanner and Grype both free?
Does OSV-Scanner scan container images?
Which tool has fewer false positives?
Can I run both OSV-Scanner and Grype together?

Founder, AppSec Santa
Years in application security. Reviews and compares 215 AppSec tools across 12 categories to help teams pick the right solution. More about me →
