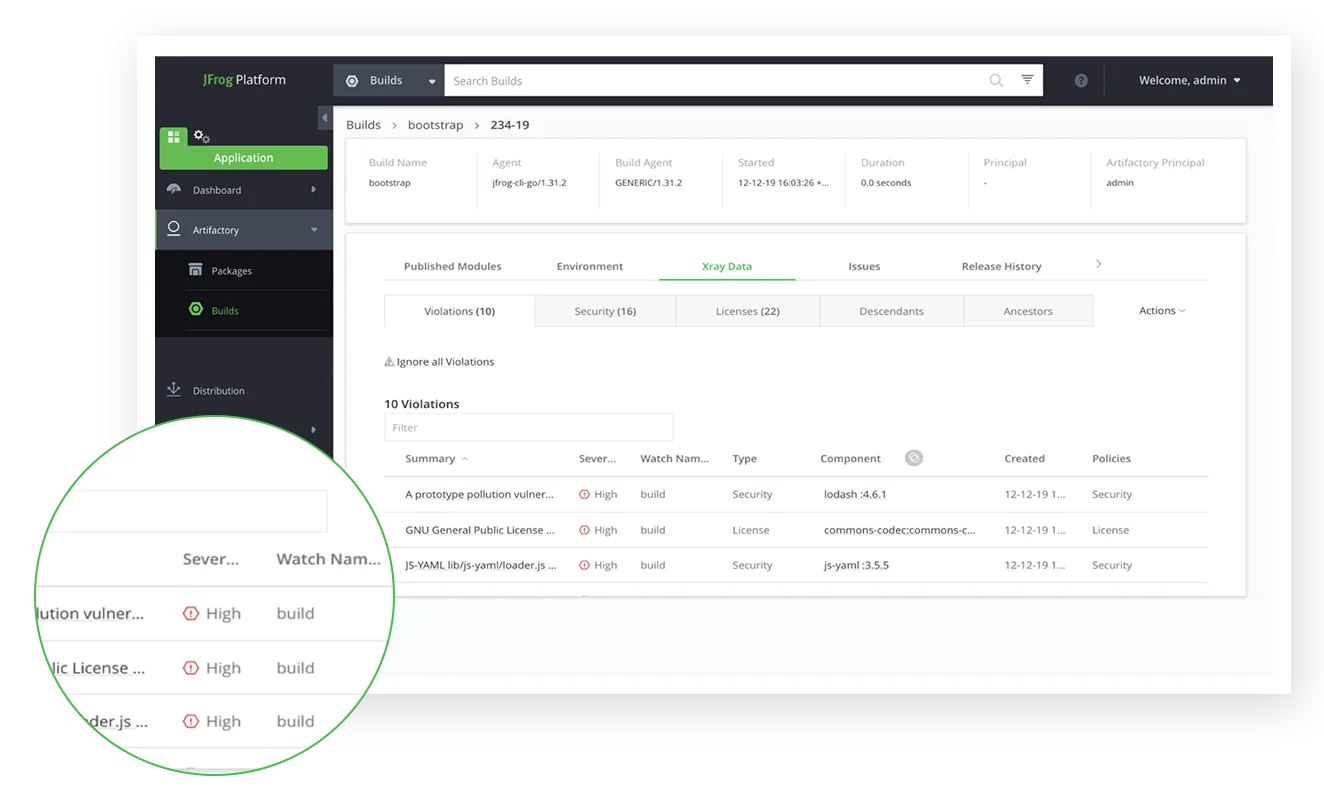
- JFrog Xray scans compiled artifacts in Artifactory — analyzing what you actually deploy rather than just source manifests. It requires an Artifactory Pro X or Enterprise subscription; there is no free tier.
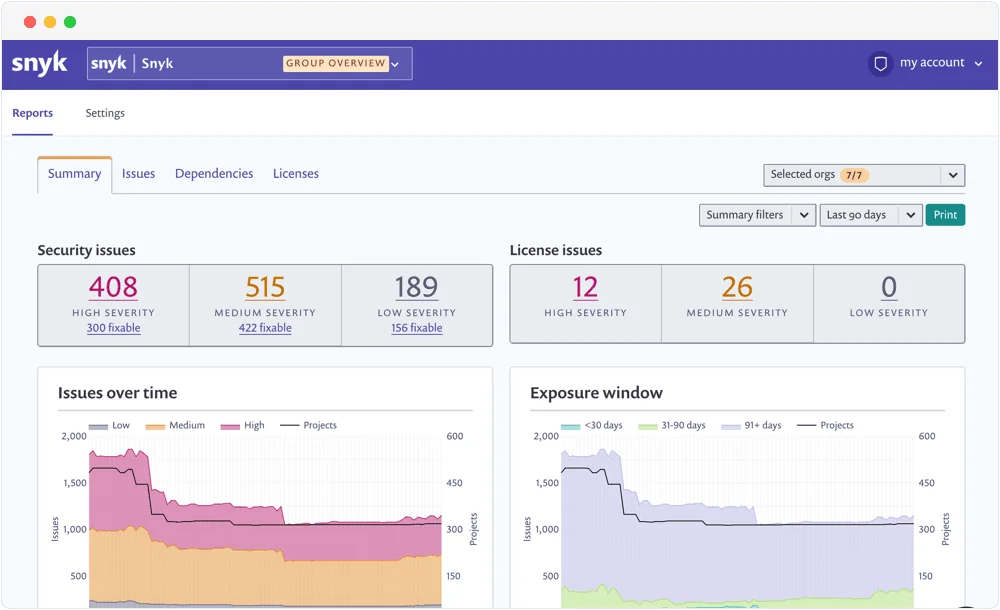
- Snyk Open Source analyzes source repository dependency files with a vulnerability database that covers CVEs 47 days ahead of NVD on average, plus automated fix pull requests and proprietary patches.
- Organization-wide impact analysis is Xray's standout feature: when a new CVE drops, Xray instantly identifies every build, artifact, and deployment across your Artifactory instance that is affected.
- Snyk is the stronger choice for developer adoption — IDE plugins, CLI, and GitHub integration put SCA findings directly in the developer's workflow with minimal friction.
- Teams already using Artifactory as their artifact repository have a clear path to Xray. Teams without Artifactory should evaluate Snyk, Mend SCA, or other manifest-based alternatives.
JFrog Xray vs Snyk: which SCA tool fits your stack?
JFrog Xray is a binary-level software composition analysis (SCA) tool built into JFrog Artifactory. Snyk Open Source is a developer-first SCA tool that scans source repository dependency manifests and generates automated fix pull requests.
JFrog Xray and Snyk take fundamentally different architectural approaches to software composition analysis. Xray lives inside the artifact repository: it scans what you actually build and store in Artifactory. Snyk lives inside the source repository: it scans the dependency manifests in your code before artifacts are built.
If your organization uses JFrog Artifactory as your artifact management platform, Xray is the natural choice for SCA. It integrates directly into the artifact lifecycle, enforces security policies on promotion gates, and gives you organization-wide CVE impact analysis across every built artifact simultaneously.
If your organization does not use Artifactory, or if you need developer-first SCA that finds vulnerabilities before code leaves the developer’s machine, Snyk Open Source is typically the stronger option.
Its vulnerability database covers new CVEs an average of 47 days ahead of NVD, automated fix pull requests reduce remediation friction, and its IDE and CLI integrations make SCA part of the development workflow rather than a gate after the build.
For teams that already rely heavily on the JFrog platform, Xray and Snyk are sometimes used together: Snyk in the development phase for rapid developer feedback, Xray at the artifact storage and promotion phase for binary-level assurance and policy enforcement.
Key differences
| Feature | JFrog Xray | Snyk |
|---|---|---|
| License | Commercial | Freemium |
| Pricing | Requires Artifactory Pro X, Enterprise X, or Enterprise+ | Free tier; Team from $25/dev/month; Enterprise custom |
| SCA Approach | Binary-level (compiled artifacts in Artifactory) | Manifest-based (source dependency files) |
| Vulnerability DB | JFrog Security Research + public feeds | Snyk proprietary DB (47 days ahead of NVD avg) |
| Fix PRs | No | Yes (automated fix pull requests) |
| Impact Analysis | Organization-wide across all Artifactory artifacts | Repository-level |
| Container Scanning | Yes (Docker images in Artifactory) | Yes (Snyk Container, separate product) |
| IaC Scanning | No | Yes (Snyk IaC) |
| SAST | No | Yes (Snyk Code) |
| License Compliance | Yes | Yes |
| CI/CD Integration | Jenkins, GitHub Actions, GitLab CI, Azure DevOps | Jenkins, GitHub Actions, GitLab CI, Azure DevOps, CircleCI |
| IDE Integration | Limited | VS Code, IntelliJ, Eclipse, and others |
| Artifactory Required | Yes | No |
| Free Tier | No | Yes (limited) |
| On-Premise | Yes (self-hosted Artifactory) | Cloud only (Snyk Broker for hybrid) |
Head-to-head comparison
Scanning approach and architecture
The most fundamental difference between JFrog Xray and Snyk is where in the development lifecycle they operate.
JFrog Xray scans artifacts stored in Artifactory. After your CI/CD pipeline builds a JAR, npm package, Docker image, or any other artifact and pushes it to Artifactory, Xray automatically scans it.
This binary-level approach means Xray sees what you actually built: transitive dependencies that may not appear cleanly in a manifest file, and dependency resolutions that differ from what the manifest specifies.
Snyk
(specifically Snyk Open Source) analyzes the dependency manifest files in your source repository: package.json, requirements.txt, pom.xml, go.mod, Gemfile.lock, and equivalents. It runs at the source code level, before the build, and integrates with GitHub, GitLab, Bitbucket, and Azure DevOps to scan on every pull request.
For SCA coverage, both approaches are valid — they catch different things. Manifest scanning catches declared vulnerabilities faster and earlier in the cycle. Binary scanning catches what actually ended up in the built artifact, which may differ from the manifest.
Vulnerability database
Snyk maintains a proprietary vulnerability database with a team of security researchers who curate, triage, and add CVEs. Snyk’s database covers new vulnerabilities an average of 47 days before they appear in the National Vulnerability Database (NVD). For fast-moving vulnerability situations like Log4Shell, Snyk’s database advantage is material — teams using Snyk know about a CVE before NVD-based tools do.
JFrog Xray uses the JFrog Security Research team’s database plus multiple public feeds. JFrog’s strength is in understanding binary package formats across different ecosystems — Maven, npm, PyPI, NuGet, Go, Docker, Debian, RPM, and more — and mapping CVEs to the exact artifact versions and layers in Artifactory.
Neither database has a decisive advantage across all scenarios. For open-source library CVE coverage speed, Snyk leads. For binary artifact and container image coverage breadth within the Artifactory ecosystem, Xray is the more integrated option.
Organization-wide impact analysis
JFrog Xray’s most distinctive feature is organization-wide impact analysis. When a new critical CVE is published — a Log4j-style event — Xray can instantly query across every artifact in your Artifactory instance and identify every build, every release artifact, and every deployed container image that contains the vulnerable component.
This is genuinely difficult to replicate with manifest-based SCA tools. Snyk can scan repositories and PRs, but identifying every artifact across your entire build history that contains a specific vulnerable library version requires a different kind of index. Xray builds that index as part of Artifactory.
For enterprises with large Artifactory deployments and complex internal artifact graphs, this capability is valuable — particularly for regulatory breach response and impact scoping.
Developer experience and adoption
Snyk leads significantly on developer experience. Snyk IDE plugins (VS Code, IntelliJ, Eclipse) show vulnerabilities inline while developers write code. Automated fix pull requests propose the exact dependency version upgrade needed to resolve a finding, so developers review and merge rather than manually researching fixes.
JFrog Xray is an artifact-layer security tool, not a developer-workflow tool. Developers interact with it primarily when a policy gate blocks a build promotion or when a CI/CD step fails. The feedback loop is longer: the developer builds, pushes to Artifactory, Xray scans, and only then does the developer learn of the issue. This is not a flaw — it is the appropriate layer for artifact-level security controls — but it means developer adoption of Xray as a daily SCA tool is lower than Snyk.
License compliance
Both tools handle open-source license compliance. JFrog Xray can enforce license policies on artifact promotion — blocking a Docker image from moving to a production repository if it contains a GPL library that violates the organization’s license policy. Snyk checks license compliance at the source dependency level and flags license issues in pull requests.
For license compliance enforcement at the point of release, Xray’s promotion gate approach is effective. For catching license issues during development before code reaches a build, Snyk’s earlier-in-the-cycle detection is more actionable.
When to choose each tool
Choose JFrog Xray if:
- Your organization uses JFrog Artifactory as your artifact repository platform
- You need binary-level SCA — scanning built artifacts, not just source manifests
- Organization-wide CVE impact analysis across your entire Artifactory instance is a requirement
- You need artifact promotion gates that enforce security and license policies before moving artifacts to production repositories
- On-premises deployment is required for your security tooling
Choose Snyk if:
- You do not use Artifactory (or are evaluating artifact repositories)
- You need developer-first SCA with IDE integration and automated fix pull requests
- Fast CVE database coverage is important (Snyk’s database leads NVD by ~47 days)
- You want a freemium option with a functional free tier for small teams
- You need SCA + SAST + Container + IaC in a single platform (Snyk covers all four)
- Cloud-first deployment is preferred
Consider both for complementary coverage: Snyk in the development phase for fast developer feedback and fix PRs, plus Xray at the Artifactory layer for binary artifact assurance and organization-wide impact analysis. See Mend SCA vs Snyk and Snyk vs Mend for additional SCA comparisons.
For related comparisons: Snyk alternatives covers the broader SCA market, and the SCA tools list compares all major options. For understanding the SCA category, see what is SCA .
FAQ
Frequently Asked Questions
Is JFrog Xray better than Snyk for SCA?
What is binary-level SCA and why does JFrog Xray do it differently?
Can I use JFrog Xray without Artifactory?
Does Snyk do binary scanning?
Which tool has a better vulnerability database?

Founder, AppSec Santa
Years in application security. Reviews and compares 215 AppSec tools across 12 categories to help teams pick the right solution. More about me →
