29 Best SCA Tools (2026)
Independent ranking — no vendor pays to appear here. See methodology.
Independent comparison of every major SCA platform — reachability analysis, supply chain attack detection, SBOM generation, and enterprise license compliance.
At a glance
The best SCA tools in 2026: Snyk, Black Duck, Socket, Endor Labs, and Trivy.
- Best developer experience: Snyk Open Source — IDE and pull-request integration with automated fix PRs
- Best supply-chain attack detection: Socket — flags malicious packages by behavior, not just known CVEs
- Best enterprise license and policy depth: Black Duck — deep license compliance and governance for regulated teams
- Best reachability analysis: Endor Labs — function-level reachability that cuts false positives
- Best free scanner: Trivy — open-source scanning across dependencies, containers, and IaC
I evaluated 29 software composition analysis tools using publicly verifiable evidence — vendor docs, GitHub activity, vulnerability-database coverage, and supply-chain detection behavior. No vendor paid to appear on this page.
What is SCA?
Software Composition Analysis (SCA) is a security testing method that automatically inventories every open-source library and third-party dependency in your software, checks each component against vulnerability databases for known security issues, and verifies license compliance.
Within a broader application security program , SCA sits alongside SAST : where SAST analyzes your own source code, SCA focuses exclusively on the third-party components your application depends on.
This page compares the full SCA market — free, freemium, and enterprise — with an emphasis on reachability analysis, supply chain attack detection, and license policy depth. For a dedicated round-up of free OSS SCA scanners with vulnerability database comparisons, see the open source SCA tools guide .
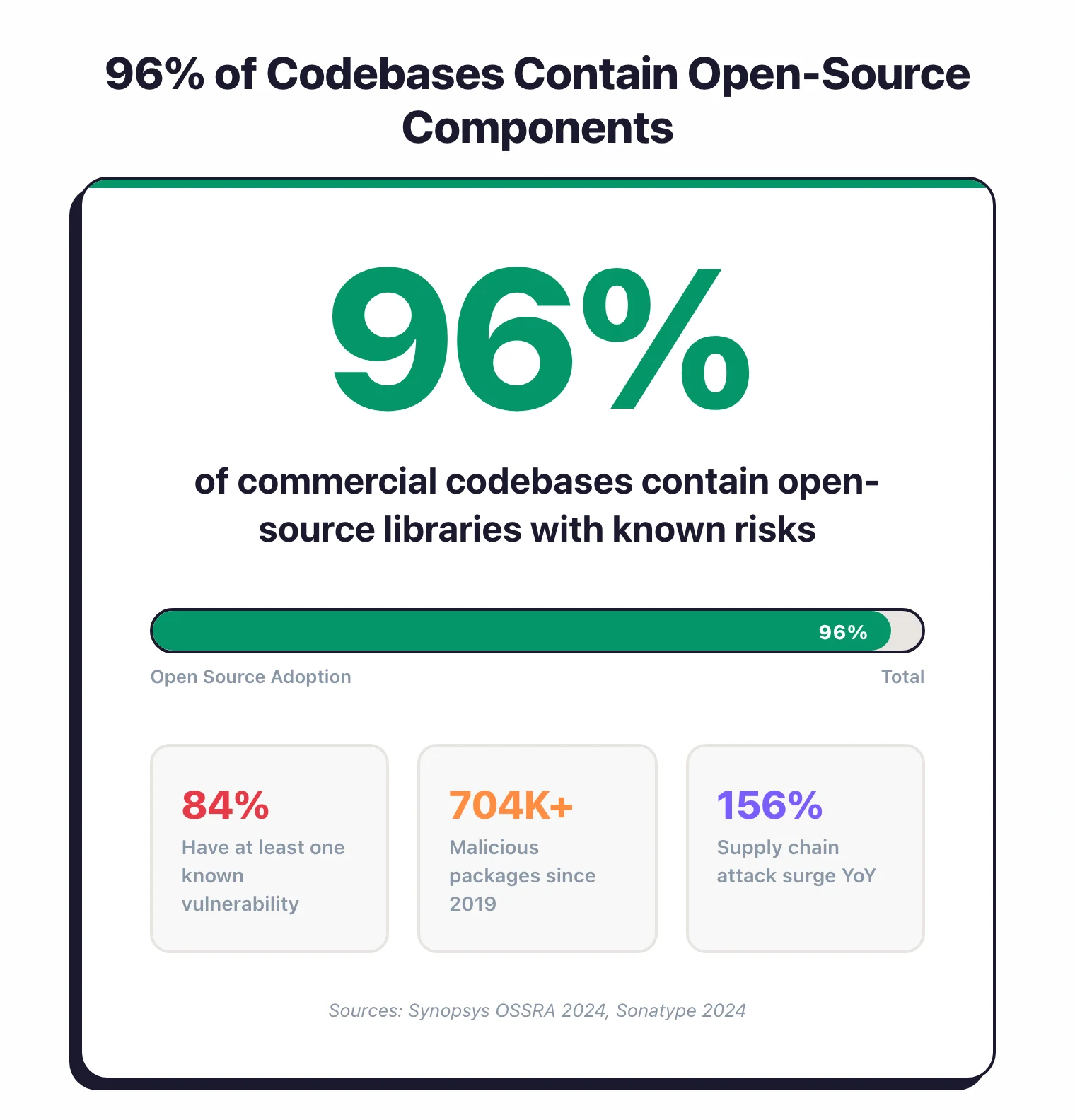
The scale of open-source usage makes manual tracking impossible. According to Synopsys’ 2024 OSSRA report, 96% of commercial codebases contain open-source components, and 84% of those contain at least one known vulnerability.
On the supply chain side, Sonatype’s 2024 State of the Software Supply Chain report found that attacks surged 156% year-over-year, with over 704,102 malicious packages identified since 2019 across npm, PyPI, and other ecosystems.
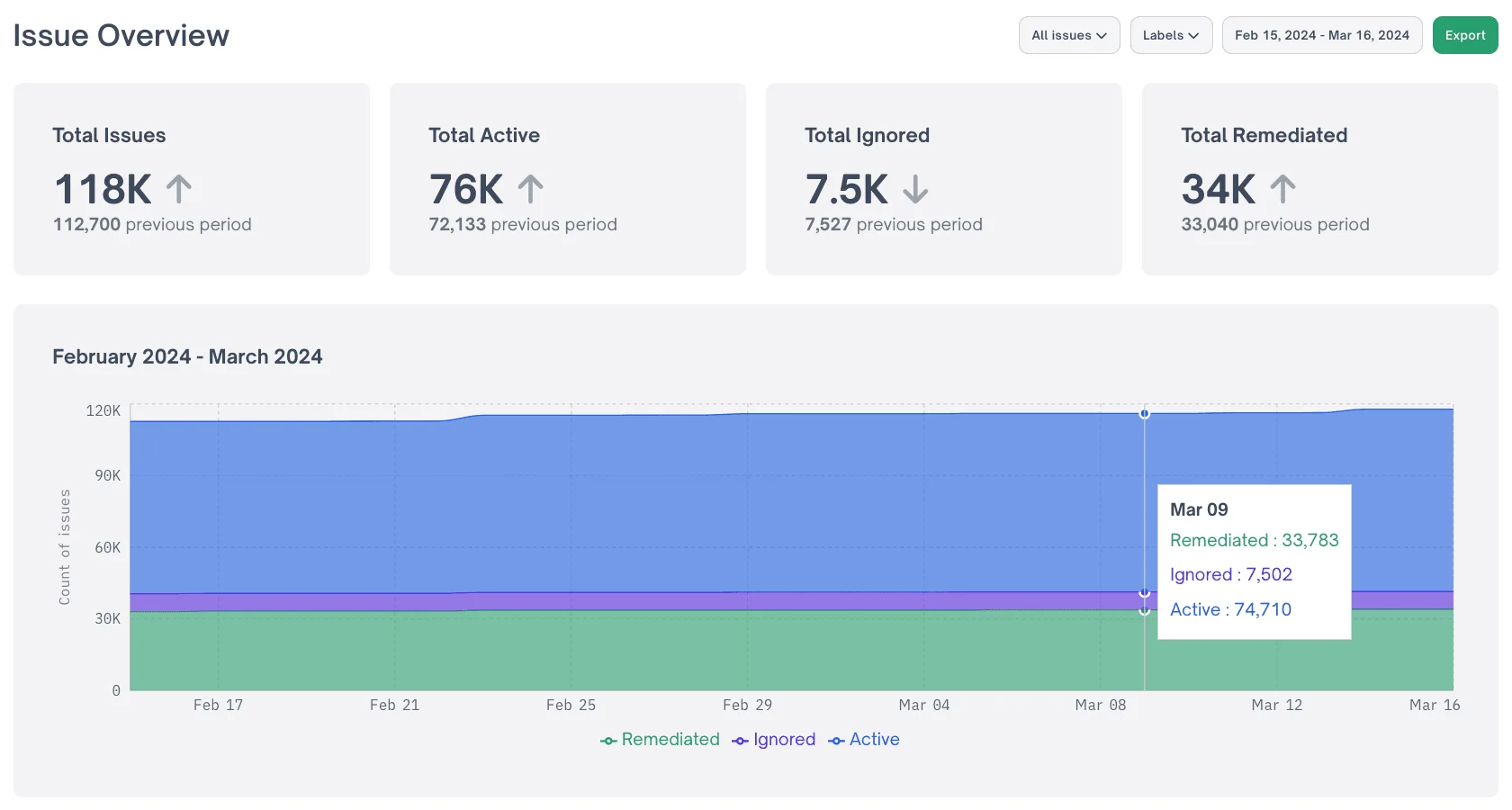
The trade-off is noise. SCA tools may report hundreds of issues, but not all vulnerabilities are actually reachable from your code.
Newer tools with reachability analysis (Endor Labs , Contrast SCA ) address this by tracing call graphs to determine which vulnerabilities are actually callable from your application — typically cutting alert volume by 70-90% according to these vendors.
How SCA Works
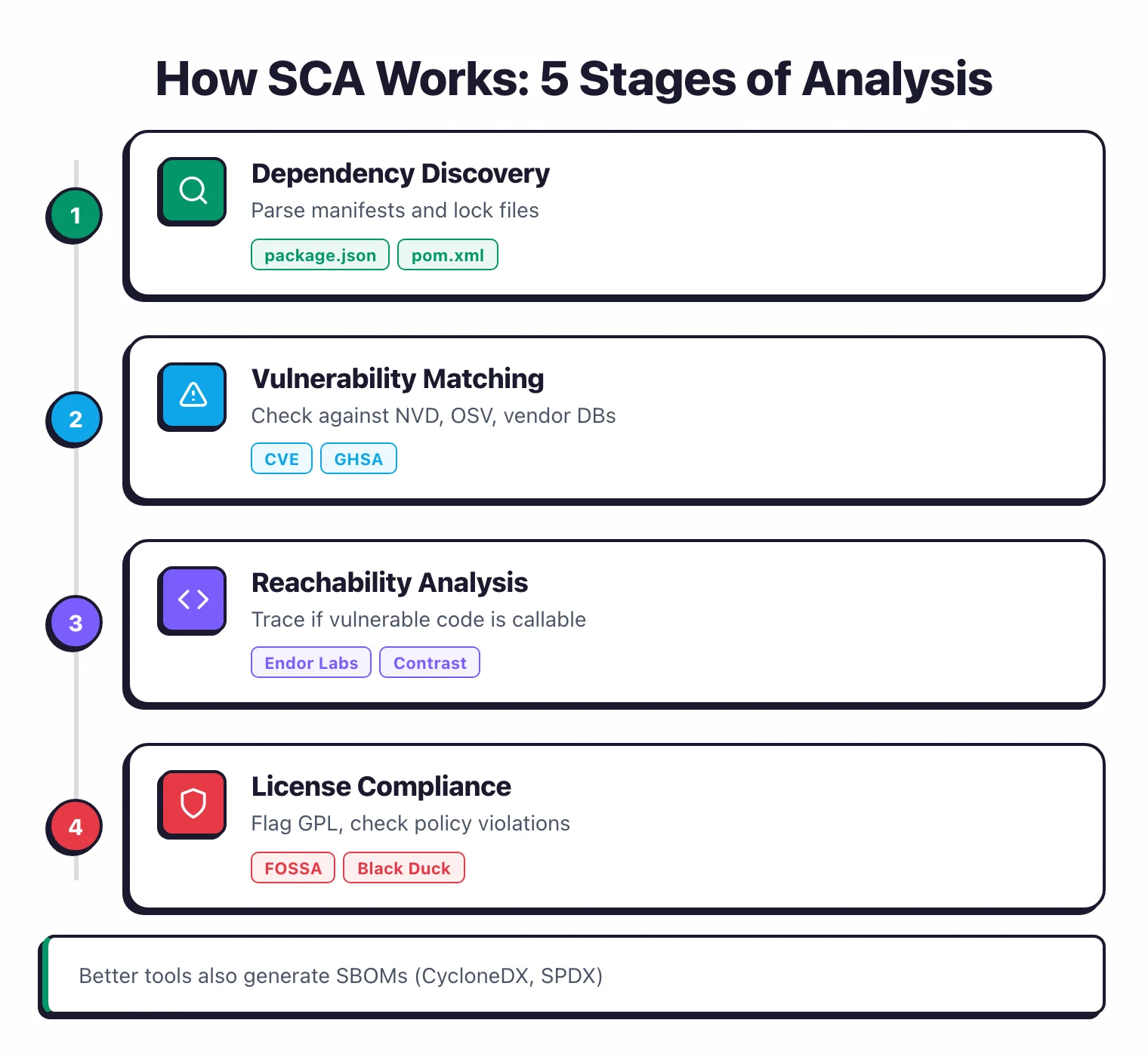
At a high level, SCA runs through five stages: dependency discovery, vulnerability matching, reachability analysis, license compliance checking, and SBOM generation.
The tool finds every open-source component in your application (including transitive dependencies), checks each one against vulnerability databases like the NVD and OSV, and reports what it finds.
The better tools then go a step further: they trace whether vulnerable code is actually callable from your application, and they flag license risks before legal gets involved.
Dependency Discovery
The tool reads your manifest files (package.json, pom.xml, Gemfile.lock, requirements.txt, go.mod) or your source code and builds a full dependency tree. That means both direct dependencies and transitive ones (the dependencies of your dependencies).
Vulnerability Matching
Every component and version gets checked against vulnerability databases: NVD, OSV, GitHub Advisory Database, and vendor-specific sources. OWASP Dependency-Check uses NVD directly. Commercial tools like Snyk Open Source and Mend run their own curated databases that tend to pick up issues faster.
Reachability Analysis
The smarter tools don't stop at matching. They trace whether the vulnerable code path in a library is actually reachable from your application. Endor Labs and Contrast SCA can tell you if a vulnerability in a dependency actually matters to your specific codebase. These vendors report that reachability analysis typically cuts alert volume by 70-90%.
License Compliance
SCA tools check every dependency's license against your organization's policies. Copyleft licenses like GPL can force you to open-source your own code. Permissive licenses like MIT and Apache 2.0 are usually fine for commercial use. FOSSA and Black Duck are the strongest options here.
SBOM Generation
Most SCA tools can export a Software Bill of Materials in CycloneDX or SPDX format. This is now a compliance requirement in many contexts: the US Executive Order on Cybersecurity (2021) requires SBOMs for software sold to federal agencies. Black Duck, Snyk Open Source, and Endor Labs all handle SBOM generation.
Why does dependency resolution matter for SCA?
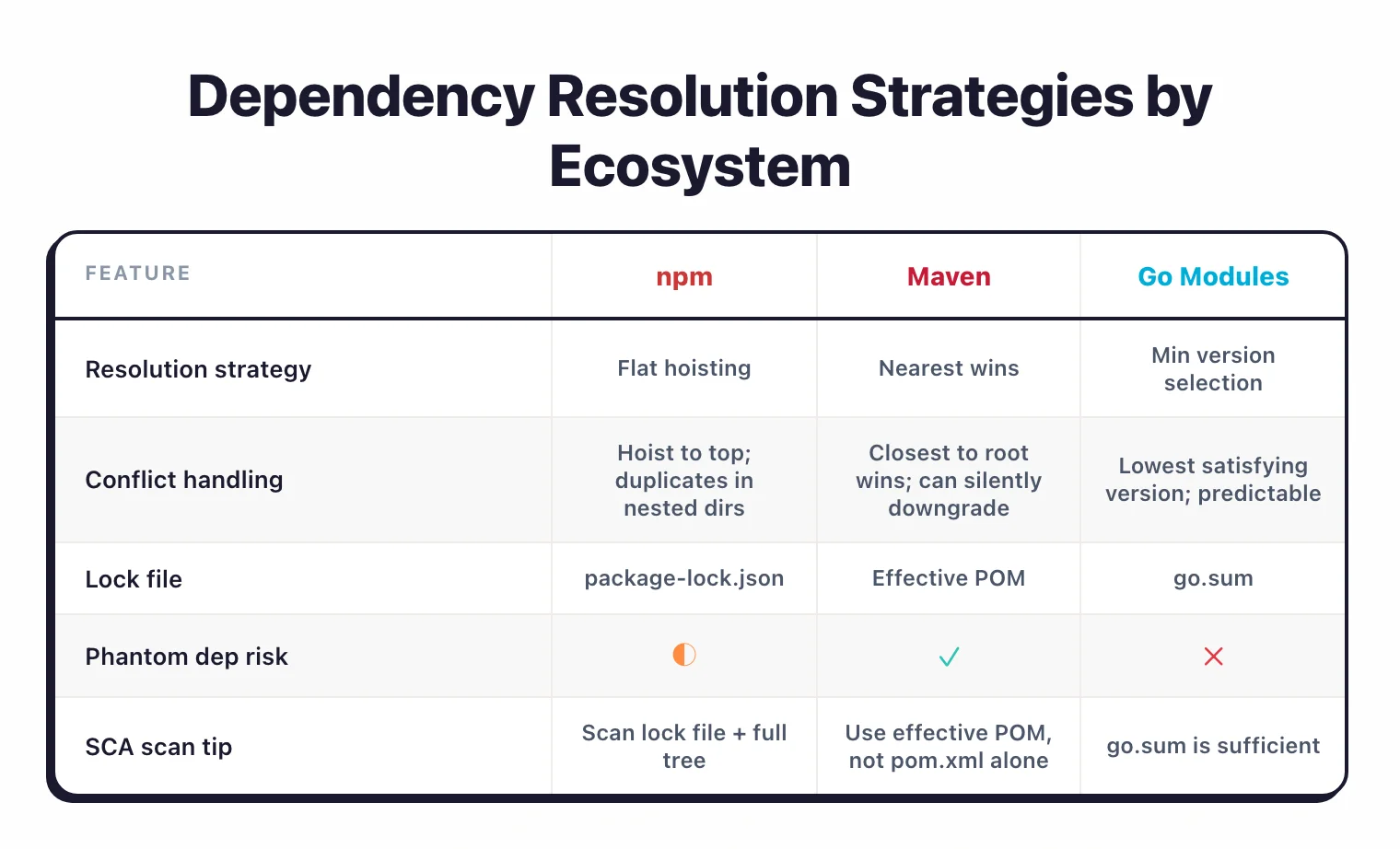
Dependency discovery works differently across ecosystems, and the resolution strategy directly affects which vulnerabilities your SCA tool can detect. npm uses a flattened node_modules structure where transitive dependencies get hoisted to the top level when possible, so your project can end up with multiple versions of the same package.
Maven resolves conflicts with a “nearest wins” strategy: the version closest to your project in the dependency tree takes precedence, which can silently downgrade a dependency to a vulnerable version.
Go modules use minimum version selection, always picking the lowest version that satisfies all constraints. More predictable, but it can mean you stay on older versions longer.
Lock files are essential for accurate SCA results. A manifest file (package.json, requirements.txt) declares what you want; a lock file (package-lock.json, poetry.lock, go.sum) records what you actually got.
Without a lock file, the SCA tool has no way of knowing exactly which versions of transitive dependencies are installed.
Some tools fall back to resolving the dependency tree themselves, but the result may not match what actually runs in production. Commit your lock files and scan them, not just the manifest.
There is also the problem of phantom dependencies — packages that work in your project but are not explicitly declared in your manifest. This happens when a package you depend on brings in a transitive dependency, and your code imports that transitive dependency directly.
If your declared dependency drops that transitive dependency in a future version, your build breaks. Some SCA tools flag phantom dependencies, but many do not.
What happens when manifest files are not available?
When manifest files are not available, tools like Black Duck and OWASP Dependency-Check can do binary and snippet scanning instead.
They fingerprint compiled code (JAR files, DLLs, binaries) and match those fingerprints against known open-source components.
This is the only option for vendor risk assessments where you receive software without source code, and it also helps verify that what shipped to production actually matches what was scanned in CI.
Quick Comparison
All 29 active SCA tools side by side, grouped by license type.
BluBracket (acquired by HashiCorp in 2023), Phylum (acquired by Veracode in 2025), and Qwiet AI (acquired by Harness in 2025) are listed separately at the bottom.
| Tool | License | Standout |
|---|---|---|
| Free / Open Source (9) | ||
| CDXgen | Free (OSS) | CycloneDX SBOM generator for 20+ languages |
| Dependabot | Free (OSS) | GitHub-native dependency security; 30+ ecosystems |
| Dependency-Track | Free (OSS) | SBOM-first vulnerability management; OWASP flagship |
| Grype | Free (OSS) | Fast container vulnerability scanner by Anchore |
| OSV-Scanner | Free (OSS) | Google-backed OSV database scanner |
| OWASP Dependency-Check | Free (OSS) | OWASP-maintained; uses NVD database; multi-platform |
| Renovate | Free (OSS) | Automated dependency updates; 90+ package managers |
| Syft | Free (OSS) | SBOM generation tool; CycloneDX and SPDX output |
| Freemium (6) | ||
| Snyk Open Source | Freemium | Auto-remediation PRs; IDE + CI/CD integration; SBOM |
| Arnica | Freemium | Pipelineless SCA with package reputation |
| Debricked | Freemium | Developer-friendly; now part of OpenText |
| FOSSA | Freemium | License compliance focus; used by Uber, Verizon, Zendesk |
| GitGuardian | Freemium | Secrets detection + SCA; supply chain security platform |
| SCANOSS | Freemium | Lightweight; multiplatform (Linux, Windows, macOS) |
| Commercial (14) | ||
| Anchore | Commercial | SBOM-first container security platform |
| Black Duck | Commercial | SBOM + license compliance; now independent (ex-Synopsys) |
| CAST Highlight | Commercial | Chrome extension for repo scanning; SBOM export to multiple formats |
| Chainguard | Commercial | Zero-CVE hardened container images |
| Checkmarx SCA | Commercial | Part of Checkmarx One; supply chain risk + behavioral analysis |
| Contrast SCA | Commercial | Runtime library prioritization; class-level execution tracking |
| Endor Labs NEW | Commercial | Reachability analysis; dependency lifecycle management |
| JFrog Xray | Commercial | Strong IDE/CI/CD and binary management integration |
| Mend SCA | Commercial | Forrester Wave Strong Performer; auto-remediation; formerly WhiteSource |
| Nexus Lifecycle | Commercial | SDLC integration; part of Sonatype platform |
| Revenera Code Insight | Commercial | License compliance and IP protection leader |
| Socket NEW | Commercial | Supply chain attack detection; analyzes package behavior |
| Veracode SCA | Commercial | Part of Veracode suite; enterprise vulnerability identification |
| Acquired (3) | ||
| BluBracket ACQUIRED | N/A | Acquired by HashiCorp in 2023 |
| Phylum ACQUIRED | N/A | Acquired by Veracode in Jan 2025; standalone product sunset |
| Qwiet AI ACQUIRED | N/A | Acquired by Harness in Sep 2025; now part of Harness STO |
Snyk Open Source and Black Duck hold the largest market share among commercial SCA tools as of 2025.
Snyk Open Source has over 2.5 million developers on its platform; Black Duck maintains one of the largest open-source vulnerability databases in the industry, built on two decades of supply chain security research.
On the disruption side, Endor Labs has picked up customers like OpenAI, Snowflake, and Atlassian by leading with function-level reachability analysis across 40+ languages. Socket carved out a different niche entirely, focusing on supply chain attack detection through behavioral analysis rather than CVE matching.
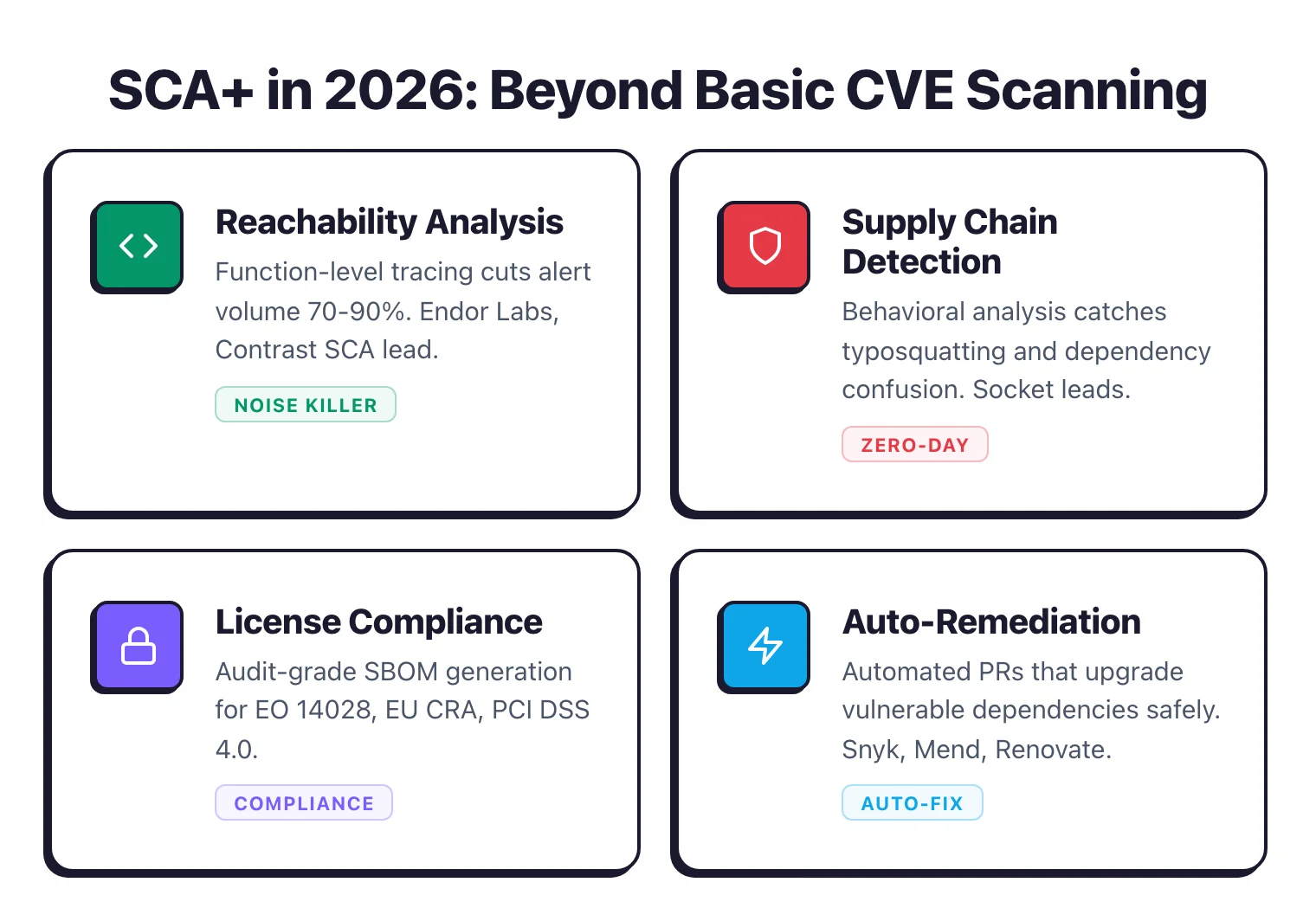
The SCA category is moving past basic vulnerability scanning toward what some analysts call “SCA+”: CVE detection, reachability analysis, supply chain threat detection, and SBOM management bundled together.
Reachability analysis in particular has gone from differentiator to table stakes — Snyk Open Source, Endor Labs, Contrast SCA, and FOSSA all offer some form of it now. The real question is how deep it goes.
Package-level reachability is a rough filter. Function-level reachability, which traces whether the specific vulnerable function is callable from your code, is far more precise.
Acquisitions keep reshaping this space. Debricked was acquired by OpenText and folded into the Fortify portfolio as OpenText Core SCA.
Veracode acquired Phylum’s malicious package detection technology in January 2025 and sunset the standalone product. Harness acquired Qwiet AI in September 2025 and integrated its Code Property Graph technology into Harness STO.
On the free side, Dependabot (free for all GitHub repos, 30+ ecosystems) and Renovate (open-source, 90+ package managers, works on GitHub/GitLab/Bitbucket/Azure DevOps) own the automated dependency update space.
They take different approaches to configuration flexibility and platform support, but between them they cover most teams.
How to Choose an SCA Tool
The right SCA tool depends on your primary need: vulnerability scanning, license compliance, supply chain protection, or automated dependency updates.
For free dependency scanning, OWASP Dependency-Check combined with Dependabot gives you basic SCA coverage at no cost.
For enterprise needs, it comes down to which combination of reachability analysis, license compliance depth, and ecosystem coverage matches your technology stack and compliance requirements.

Here is what I would evaluate when picking an SCA tool:
Package manager support. Does it cover the ecosystems you use? npm, Maven, PyPI, NuGet, Go modules, RubyGems?
Most commercial tools handle all of these, but check for less common ones like Cargo, Hex, or Pub. Renovate leads with 90+ package managers, while Dependabot covers 30+.
If you work in a polyglot environment, ecosystem breadth is a hard filter.
Vulnerability database. How fast does it pick up new CVEs? OWASP Dependency-Check relies on NVD, which can lag behind disclosure.
Snyk Open Source runs a proprietary database and claims to detect vulnerabilities an average of 47 days faster than competing sources. Black Duck Security Advisories (BDSAs) also surface issues before NVD does.
This matters because the window between public disclosure and your patch is exactly when attackers look.
Reachability analysis. If alert fatigue is a problem (and it usually is), look for tools that tell you which vulnerabilities are actually reachable from your code. Endor Labs does function-level reachability across 40+ languages and reports up to 97% noise reduction.
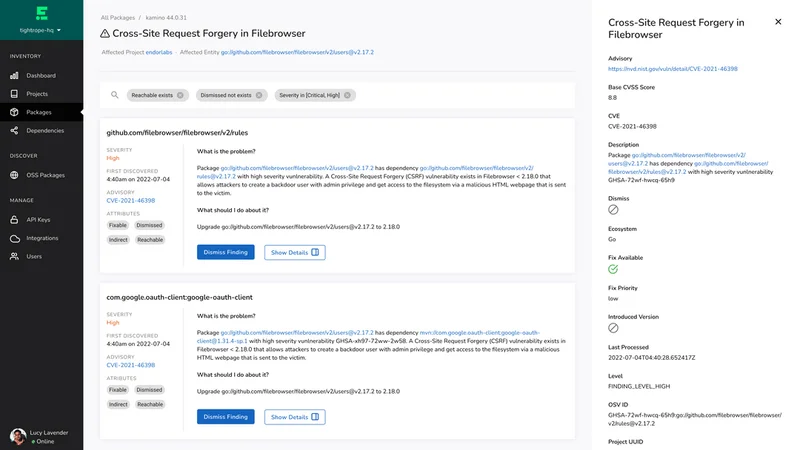
Contrast SCA uses runtime instrumentation for class-level execution tracking. Qwiet AI (now part of Harness STO) takes a different approach with code property graphs.
The depth varies a lot: package-level reachability is a rough filter, function-level reachability is far more precise.
License compliance. If you ship commercial software, pay attention to this. FOSSA leads with 99.8% license detection accuracy, full-text analysis that catches modified licenses, and a policy engine designed with open-source licensing attorneys.
Black Duck has the deepest feature set for enterprises that need attribution reports and audit-grade compliance. Snyk Open Source covers license compliance too, but not with the same depth as the dedicated tools.
CI/CD integration and auto-remediation. How easy is it to drop into your pipeline?
Does it open auto-fix PRs? Snyk Open Source
is the fastest to get started: install the CLI, run snyk test, done. Mend
is strong on auto-remediation.
For dependency updates specifically, Dependabot is free and native to GitHub, while Renovate gives you more configuration flexibility and works across more platforms.
Budget. OWASP Dependency-Check is free and solid for basic scanning. Grype and Syft are free for vulnerability scanning and SBOM generation. Dependabot is free for all GitHub repos. Most commercial tools offer free tiers for small teams.
Enterprise features like reachability, compliance dashboards, and priority support require paid plans.
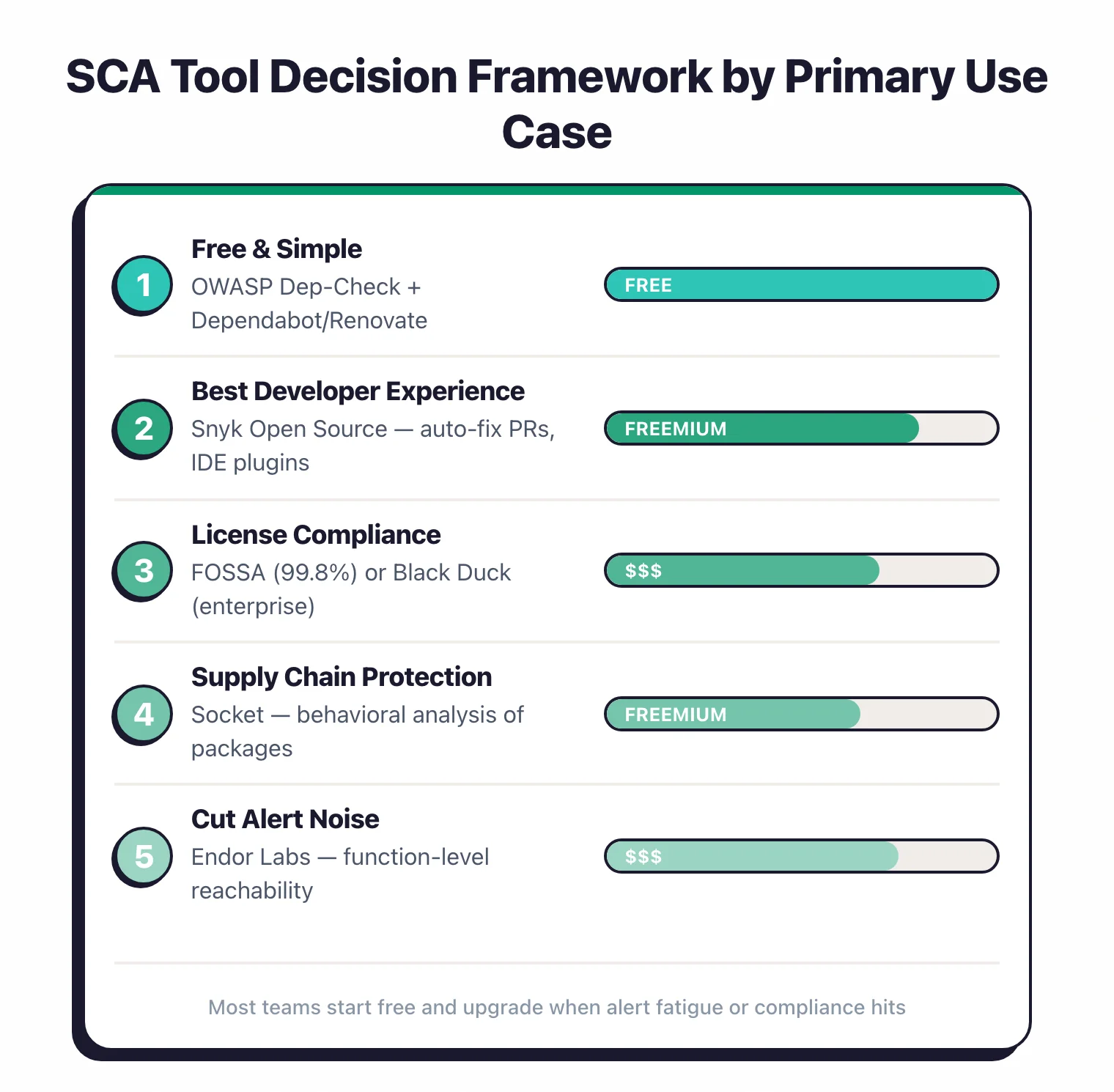
Here is a simplified decision framework based on primary use case:
- Free and simple — OWASP Dependency-Check for vulnerability scanning + Dependabot or Renovate for automated dependency updates
- Best developer experience — Snyk Open Source for auto-fix PRs, IDE plugins, and a fast vulnerability database
- License compliance is critical — FOSSA for 99.8% accuracy or Black Duck for enterprise audit-grade compliance
- Supply chain attacks worry you most — Socket for behavioral analysis of packages before they enter your codebase
- Reachability analysis to cut alert noise — Endor Labs for function-level reachability across 40+ languages, Contrast SCA for runtime-based prioritization, or Harness STO (formerly Qwiet AI ) for code property graph analysis
- All-in on JFrog — JFrog Xray for native Artifactory integration and binary scanning
Common SCA Mistakes
Having an SCA tool is not the same as using it well.
The most common mistakes I see are scanning only direct dependencies, treating every CVE as equally urgent, and ignoring license compliance until legal gets involved. Any of these can undermine an otherwise solid dependency management strategy.
Only scanning direct dependencies. If your SCA tool only checks what is in your manifest file (package.json, pom.xml) without resolving the full dependency tree, you miss the transitive dependencies where most vulnerabilities actually live.
Make sure your tool resolves lock files and scans the complete graph. A direct dependency with zero CVEs can pull in dozens of transitive packages that do have known issues.
Treating all CVEs as equally urgent. A critical-severity CVE in a function your code never calls is less dangerous than a medium-severity CVE in a code path that runs on every request. Without reachability context, teams either try to fix everything (burnout) or ignore everything below a CVSS threshold (missed real risks).
Tools like Endor Labs and Contrast SCA help prioritize based on actual exploitability.
Letting vulnerability databases go stale. The NVD publishes over 100 new CVEs per day.
If your OWASP Dependency-Check instance is running with a stale database because the NVD API key expired or the update job stopped, you are scanning against old data. Commercial tools handle updates automatically.
Self-hosted and open-source tools need you to stay on top of this.
Ignoring license compliance. Vulnerability scanning gets all the attention, but license violations carry real legal risk.
If your commercial application includes a GPL-licensed component, you may be obligated to release your source code.
According to Synopsys’ 2024 OSSRA report, 53% of audited codebases contained license conflicts. Set up license policies early. Untangling license obligations after shipping is a nightmare.
Skipping container base images. Your Dockerfile starts with FROM node:18-alpine or FROM python:3.11-slim.
Those base images contain OS-level packages (openssl, zlib, curl) with their own vulnerabilities.
Manifest-level SCA does not catch these. Tools like Grype , Trivy , Anchore , and Black Duck scan container images and surface OS-level vulnerabilities that would otherwise slip through.
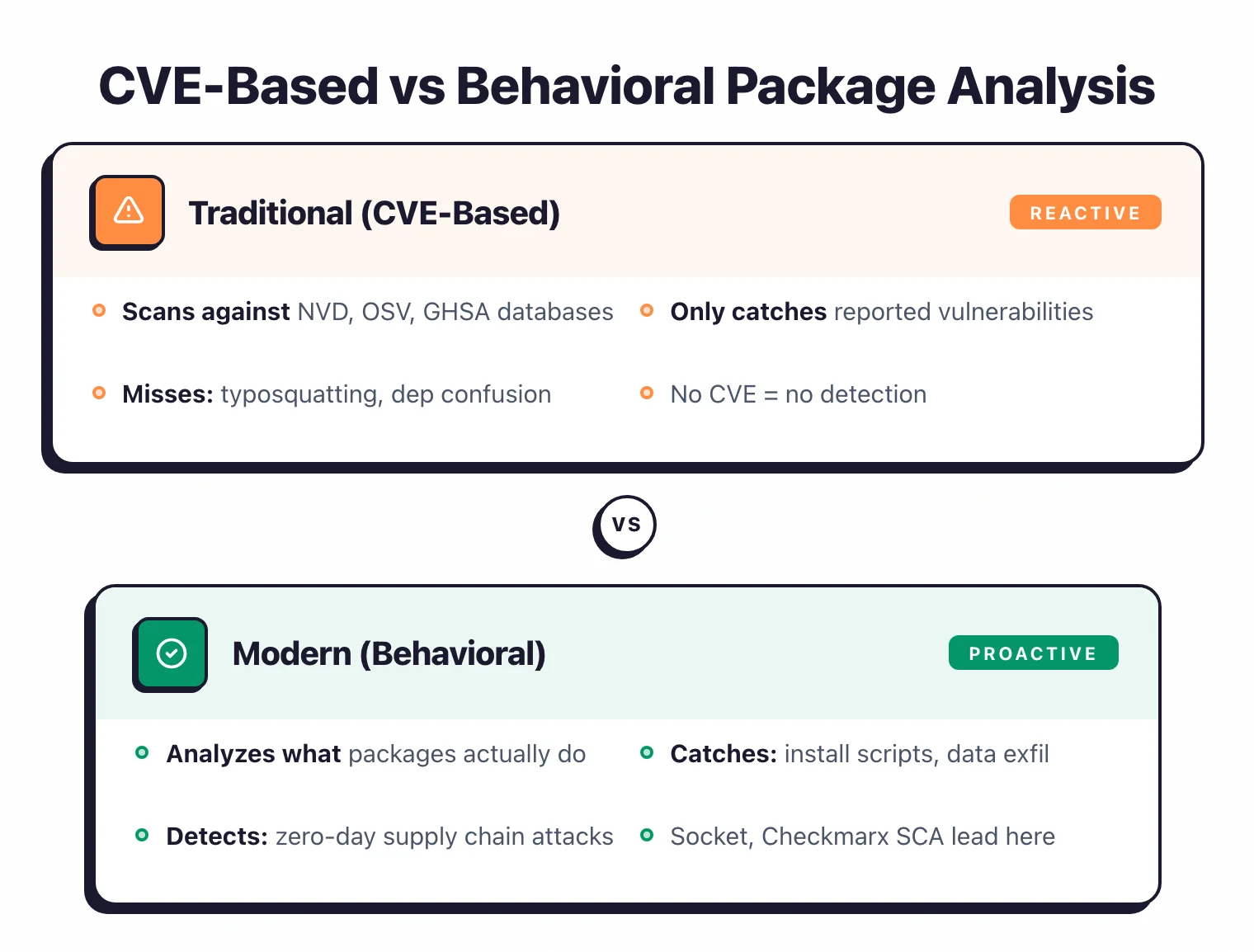
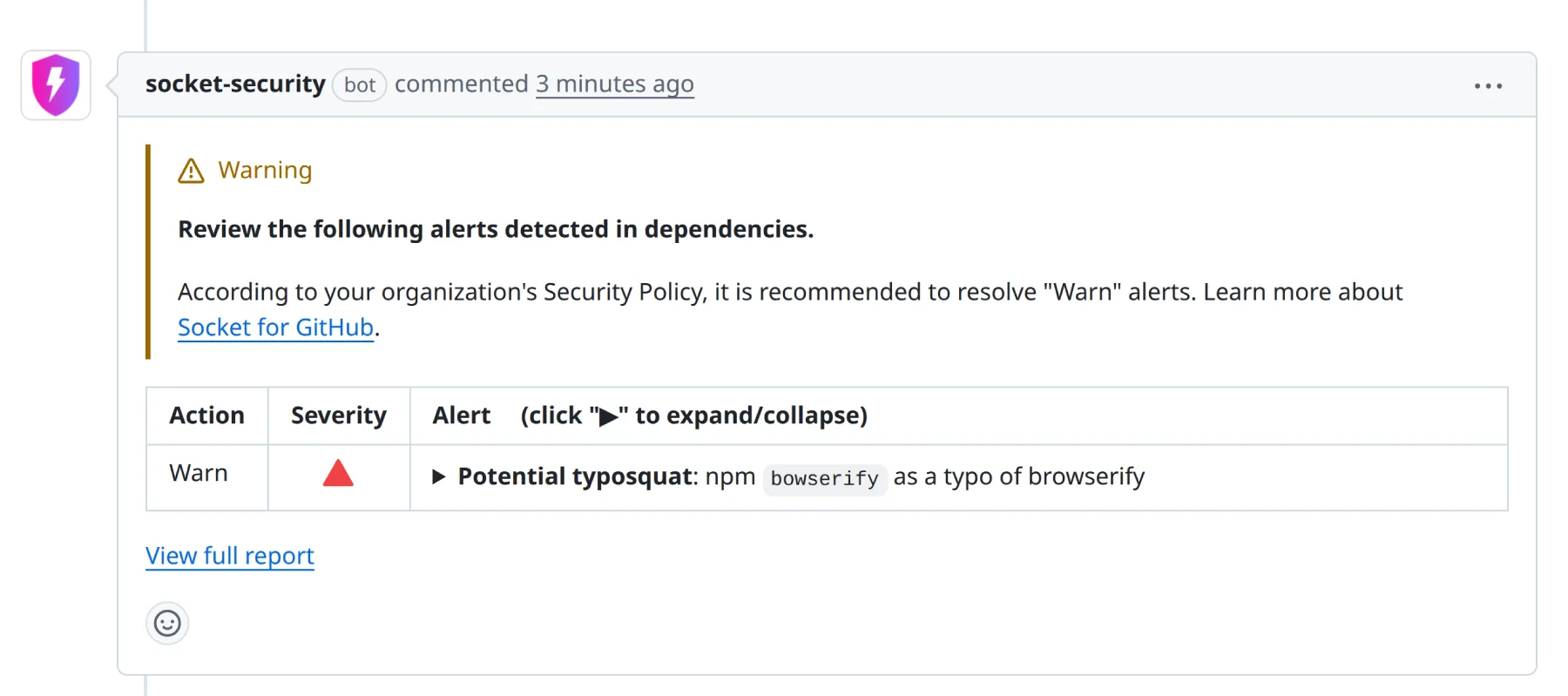
Relying only on CVE databases. CVE-based scanning only catches vulnerabilities that have been reported, assigned a CVE number, and added to a database.
Malicious packages published through typosquatting or dependency confusion have no CVE.
They are deliberate attacks, not bugs. Supply-chain-aware tools like Socket and behavioral analysis in Checkmarx SCA fill this gap by analyzing what packages actually do, rather than waiting for someone to file a report.
2026 SCA Methodology
I evaluate SCA tools against six criteria that reflect how teams actually use them in production.
Advisory database depth and latency. How many vulnerability sources does the tool aggregate — NVD, OSV, GitHub Advisory, vendor-specific advisories — and how quickly does it surface new disclosures? A tool that lags by days on a critical CVE is a liability.
Reachability analysis. Does it trace whether vulnerable code is actually callable from your application? Function-level reachability (as opposed to package-level) is far more precise. I look at how many languages are supported and whether the analysis runs in CI without a full build.
Fix-PR quality. Auto-remediation PRs save real developer time, but only if they pass tests and handle transitive dependencies cleanly. I check whether suggested fixes target the minimal safe version, include changelog context, and avoid breaking changes.
Container vs lockfile coverage. Manifest scanning and container image scanning are different problems. A tool that only reads package.json misses OS-level vulnerabilities in your base image. I review both surfaces when evaluating commercial platforms.
Pricing transparency. If a vendor does not publish pricing, I do not speculate on cost. I note whether free tiers exist, what limits apply, and whether the vendor requires a sales call for basic information.
License compliance. I evaluate whether the tool can enforce custom license policies (not just SPDX detection), generate audit-grade attribution reports, and flag copyleft obligations before legal gets involved.
Best SCA Tools by Use Case
Different teams have different primary needs. Here is how I would match tools to those needs.
For supply chain attack detection. Socket is the clear leader — it analyzes package behavior (network calls, install scripts, filesystem access) to catch malicious packages before they are ever assigned a CVE. Endor Labs adds a behavioral layer on top of reachability analysis, flagging packages with unusual dependency graphs or known maintainer compromise signals.
For GitHub-native workflows. Dependabot is built into every GitHub repository at no cost and covers 30+ ecosystems. GitHub Advanced Security extends this with secret scanning and CodeQL SAST in the same interface — the right choice if your team lives entirely in GitHub and wants minimal tooling overhead.
For polyglot enterprise stacks. Snyk Open Source covers 50+ package managers, integrates with all major Git providers, and combines reachability scoring with auto-fix PRs. Mend SCA is strong on auto-remediation and covers 200+ programming languages. JFrog Xray is the best choice when your team already uses Artifactory — it scans at the binary registry level before artifacts reach production.
For container and image-first teams. Grype and Trivy are both fast, open-source, and scan OCI images for OS packages and application dependencies. Docker Scout adds native integration if you use Docker Hub. All three are free and easy to add to any CI pipeline.
For free and open-source teams. OSV-Scanner uses Google’s OSV database and covers C/C++, Go, Python, Rust, npm, Maven, and more. Grype handles container scanning. Trivy covers both. Dependency-Track is the best free option for SBOM-centric vulnerability management with a persistent dashboard. Between these four, most open-source projects have full SCA coverage at zero cost. For alternatives to common free tools, see Dependabot alternatives , Socket alternatives , and Renovate alternatives .
For single-language stacks. Each major ecosystem has tool picks tuned to its package manager and advisory source: Node.js and TypeScript , Python , and Java . For secret scanning specifically, the best open-source secret scanning tools comparison covers TruffleHog, Gitleaks, detect-secrets, and others.
SCA Decision Framework
Five scenarios and what I would pick for each.
Scenario 1: Startup, GitHub-only, small team. Start with Dependabot for free automated PRs and OSV-Scanner in CI for vulnerability reporting. Add Socket if you depend heavily on npm packages. Total cost: zero.
Scenario 2: Mid-market, multi-cloud, mixed Git providers. Snyk Open Source is the practical default — it covers all major Git providers, has a generous free tier, and the proprietary vulnerability database catches issues that NVD misses. Upgrade to a paid plan when team size demands it.
Scenario 3: Enterprise with license compliance requirements. Black Duck for audit-grade SBOM generation and attribution reports, especially if you need to comply with US EO 14028 or the EU Cyber Resilience Act. FOSSA is a strong alternative with a better developer UX and published pricing.
Scenario 4: High-volume alert fatigue, engineering team drowning in CVEs. Endor Labs first — function-level reachability across 40+ languages eliminates the vast majority of noise. Contrast SCA is the alternative if you want runtime instrumentation instead of static call graph analysis.
Scenario 5: JFrog shop with Artifactory at the center. JFrog Xray is the only sensible choice. It scans binaries in the registry before they reach any environment, integrates directly with Artifactory policies, and blocks vulnerable artifacts from being consumed downstream.
Reachability Analysis in SCA: What It Means
Reachability analysis answers a different question than traditional CVE scanning. Instead of asking “does this dependency have a known vulnerability?”, it asks “is the vulnerable function in this dependency actually callable from my code?” The distinction matters enormously for triage. A library can have a critical-severity CVE in a function your application never invokes — without reachability context, that shows up as an urgent finding. With reachability, it gets deprioritized automatically.
Function-level reachability is the most precise form. Endor Labs builds a call graph across your entire codebase and the dependency tree, tracing whether vulnerable functions are reachable from any entry point in your application. The company reports up to 97% noise reduction compared to raw CVE counts — meaning roughly 97 out of 100 reported vulnerabilities are not reachable and can be deprioritized. This operates statically, without requiring a running application.
Cross-file reachability goes further. Snyk Open Source extends reachability analysis across file boundaries, tracking whether a vulnerable code path can be triggered from user-controlled input. Contrast SCA takes a runtime approach: it instruments the application at execution time and tracks which library classes are actually loaded, giving a data-driven answer rather than a static approximation. The practical implication for teams is that reachability analysis shifts SCA from a fire-hose of alerts to a prioritized list of vulnerabilities that actually need fixing — which is the only way to make SCA sustainable at scale.
Frequently Asked Questions
What is SCA (Software Composition Analysis)?
What is the difference between SCA and SAST?
How do enterprise SCA platforms differ from basic dependency scanners?
What is reachability analysis in SCA?
Can SCA tools detect supply chain attacks?
What is an SBOM and why does it matter?
How often should I scan dependencies?
Can SCA tools scan container images?
What is the difference between Dependabot and Snyk Open Source?
What is the best free SCA tool in 2026?
Do I need SCA if I already have SAST?
Does SCA work for npm packages specifically?
Can SCA detect malicious packages, not just vulnerable ones?
Which SCA tools are open-source-friendly?
Related SCA Resources
Explore Other Categories
SCA covers one aspect of application security tools. Browse other categories below.

Written & maintained by
Suphi CankurtEight years on the vendor side of application-security sales — thousands of evaluations and demos. I started AppSec Santa in 2022 to put that insider view to work for buyers. Independent of any vendor, paid by none, and honest about what fits whom.