- Snyk bundles Snyk Code (SAST powered by DeepCode AI) with Snyk Open Source (SCA) and works across GitHub, GitLab, Bitbucket, and Azure DevOps.
- GitHub Advanced Security is a GitHub-only bundle that includes CodeQL for SAST, Dependabot for SCA, secret scanning, and dependency review.
- According to Snyk, its proprietary vulnerability database catches CVEs an average of 47 days before public sources like NVD; CodeQL ships 2,000+ queries maintained by GitHub Security Lab.
- Snyk has a free tier capped at 200 Open Source tests per month; GHAS is free for public repositories and billed per active committer on GitHub Enterprise.
- Snyk offers reachability analysis for Java, JavaScript, and Python and auto-fix PRs; GHAS leans on native PR checks, code scanning alerts, and tight GitHub Actions integration.
Snyk and GitHub Advanced Security both combine SAST with SCA, but they solve the problem from opposite ends: Snyk is a multi-platform developer-security vendor, while GHAS is a GitHub-native bundle anchored by CodeQL and Dependabot.
Which Is Better: Snyk or GitHub Advanced Security?
Scope of this comparison: SAST, SCA, and secret scanning coverage across both platforms — CodeQL and Dependabot under GitHub Advanced Security vs Snyk Code, Snyk Open Source, and Snyk Container. If you’re evaluating Snyk’s SAST engine specifically against another SAST vendor, the Checkmarx vs Snyk engine deep-dive goes further on CWE detection.
Snyk and GitHub Advanced Security are both credible choices for teams that want SAST and SCA in one purchase. They diverge on platform reach, vulnerability intelligence, and how deeply they integrate with the rest of your developer workflow.
Snyk is the safer bet if your repositories are spread across GitHub, GitLab, Bitbucket, and Azure DevOps. Snyk Code ships its DeepCode AI engine for SAST, Snyk Open Source handles SCA with auto-fix pull requests, and the same dashboard covers containers and IaC.
If you care about a proprietary vulnerability database, reachability analysis for Java, JavaScript, and Python, or consolidated reporting across clouds and orgs, Snyk earns its keep.
GitHub Advanced Security is the stronger pick when GitHub is your only platform and you want security to feel like a native part of the product. CodeQL runs inside GitHub Actions, alerts surface in the Security tab, and Dependabot opens PRs without another vendor login.
The tight integration is the selling point. You trade multi-platform flexibility and the richer Snyk dashboard for a setup that matches how GitHub-centric teams already work.
What Are the Key Differences?
| Feature | Snyk | GitHub Advanced Security |
|---|---|---|
| Primary focus | Developer-first AppSec platform | GitHub-native security bundle |
| SAST engine | Snyk Code (DeepCode AI) | CodeQL (2,000+ queries) |
| SCA engine | Snyk Open Source | Dependabot + dependency graph |
| Secret scanning | Yes | Yes (push protection available) |
| Container scanning | Snyk Container | Not part of GHAS |
| IaC scanning | Snyk IaC | Not part of GHAS |
| Platforms | GitHub, GitLab, Bitbucket, Azure DevOps | GitHub only |
| Vulnerability DB | Proprietary, ~47 days ahead per Snyk | GitHub Advisory Database |
| Reachability analysis | Java, JavaScript, Python | No |
| Auto-fix PRs | Yes (Snyk Open Source) | Yes (Dependabot) |
| Free tier | 200 OSS tests/month; unlimited OSS for Snyk Code | Free on public repos |
| Paid model | Per-developer (Team / Enterprise) | Per active committer (Enterprise) |
| CI/CD | CLI, GitHub Actions, GitLab CI, Jenkins, more | GitHub Actions-first |
| Reporting | Cross-org dashboard and APIs | Security tab + Advanced Security API |
Snyk vs GitHub Advanced Security: How Do They Compare?
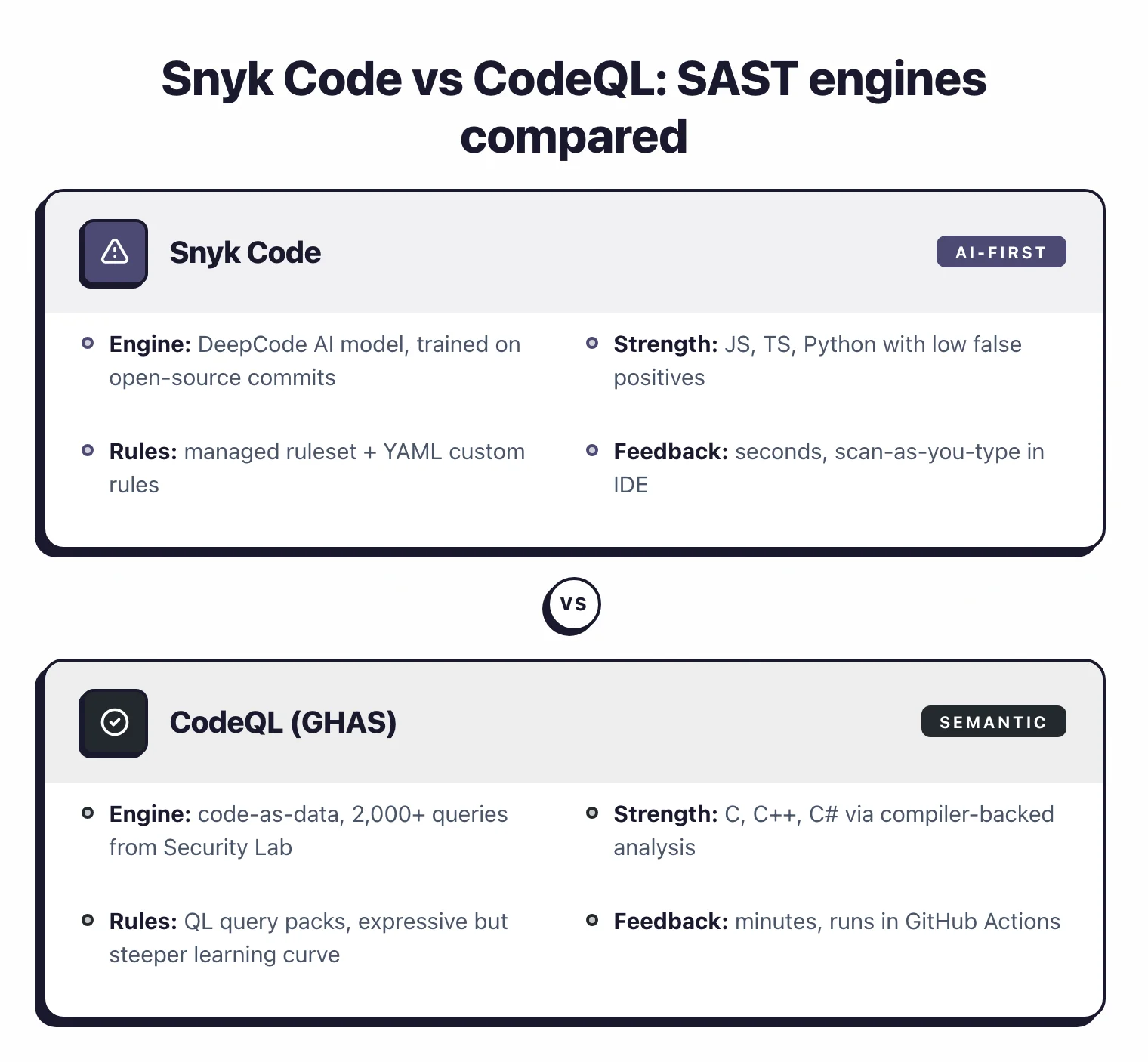
SAST: Snyk Code vs CodeQL
Snyk Code is the SAST engine inside Snyk, built on the DeepCode AI models Snyk acquired. It scans in the IDE, in PRs, and in CI, and focuses on developer feedback speed. Findings include fix suggestions generated from the same model family.
CodeQL is GitHub’s semantic analysis engine and the SAST core of GHAS. It treats code as data, lets you query vulnerabilities across a codebase, and ships 2,000+ queries maintained by GitHub Security Lab.
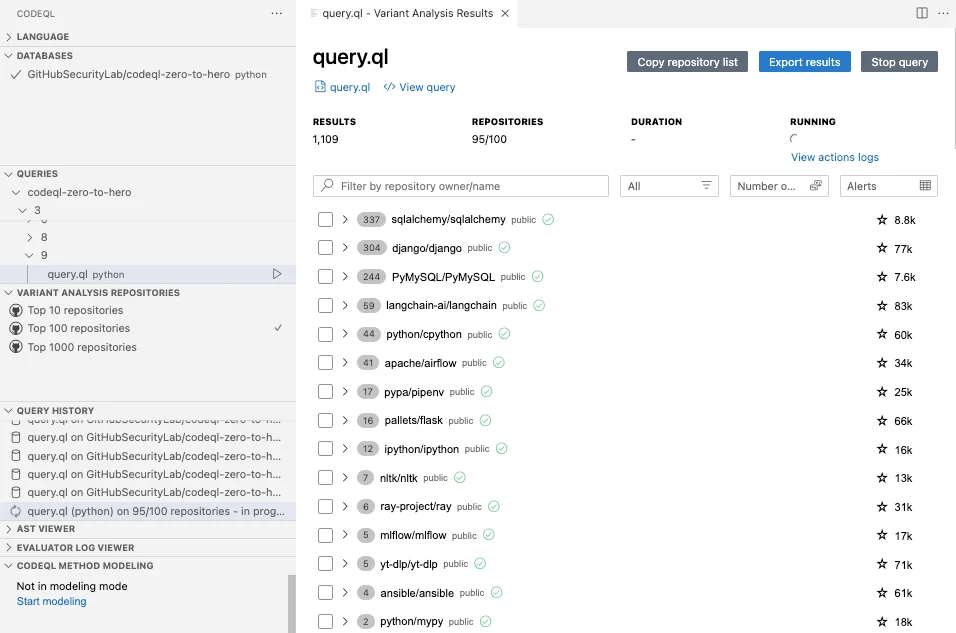
Both tools cover the mainstream language set. CodeQL is especially strong on C, C++, and C# thanks to its compiler-backed analysis. Snyk Code has an edge on runtime-heavy JavaScript, TypeScript, and Python projects where the AI model reduces false positives.
Teams writing custom rules often prefer CodeQL because QL queries are expressive and well-documented. Teams that want out-of-the-box coverage with minimal tuning lean toward Snyk Code.
SCA: Snyk Open Source vs Dependabot
Snyk Open Source uses Snyk’s proprietary vulnerability database. According to Snyk, that database catches CVEs an average of 47 days before they appear in NVD or public sources, and it feeds reachability analysis for Java, JavaScript, and Python.
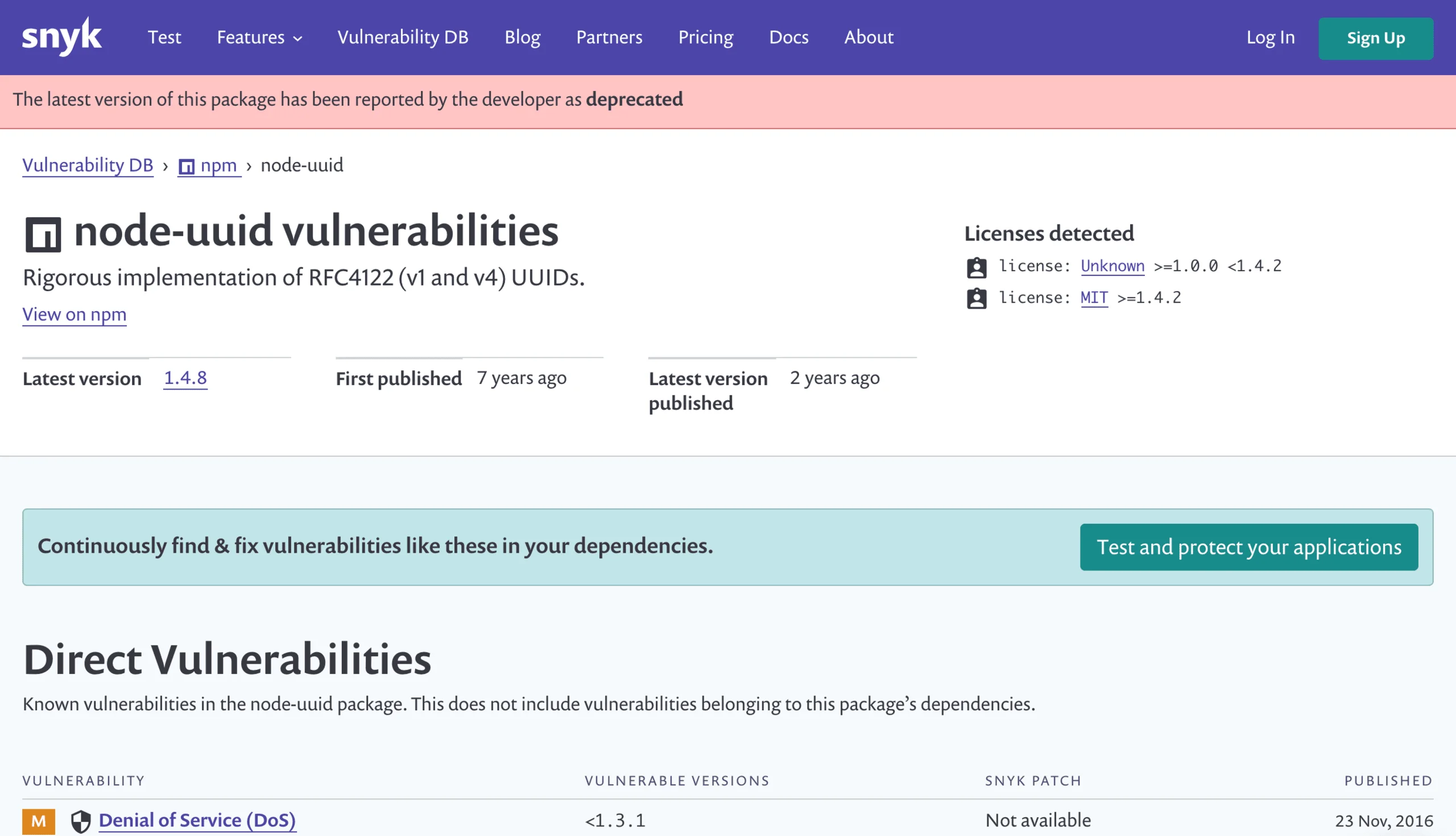
Fix PRs include upgrade paths that minimize breaking changes and, where available, apply runtime patches instead of forcing a major version bump.
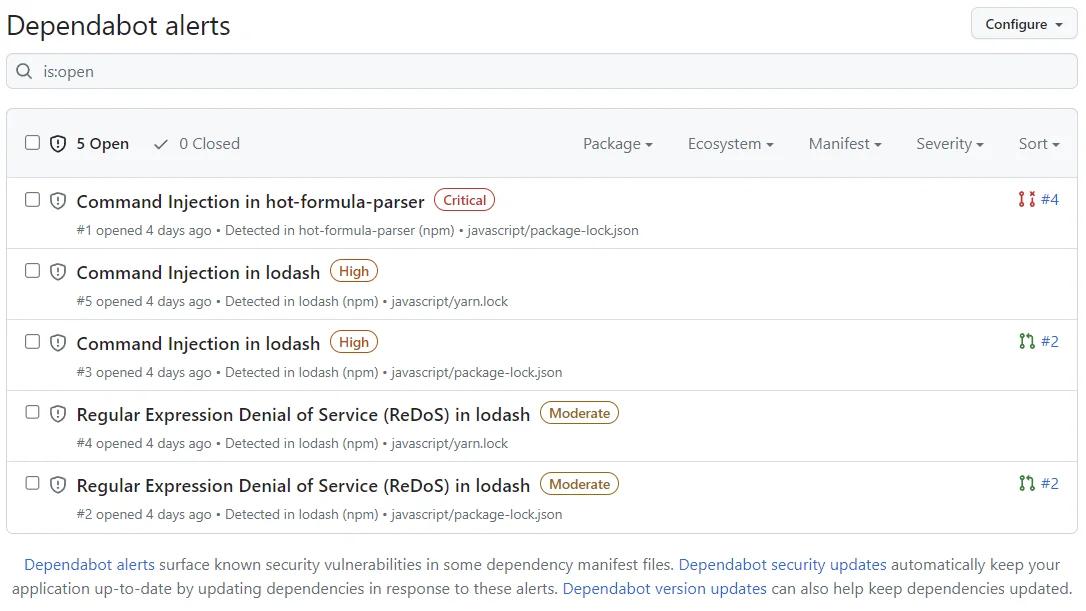
Dependabot uses the GitHub Advisory Database with more than 23,000 reviewed advisories. It covers 30+ ecosystems including npm, pip, Maven, Gradle, Cargo, Docker, Terraform, and GitHub Actions.
On GitHub, Dependabot is free and requires zero external service. It opens version updates, security updates, and grouped PRs, and it is configured with a single dependabot.yml file.
The tradeoff is depth. Dependabot does not perform reachability analysis or function-level prioritization. It reports every known vulnerability in your tree, regardless of whether the vulnerable code is reachable from your app.
Secret Scanning and Dependency Review
GHAS secret scanning runs on public and private repos and supports push protection, which blocks commits that contain known secret formats before they land on the server. It partners with dozens of cloud providers for verified token detection.
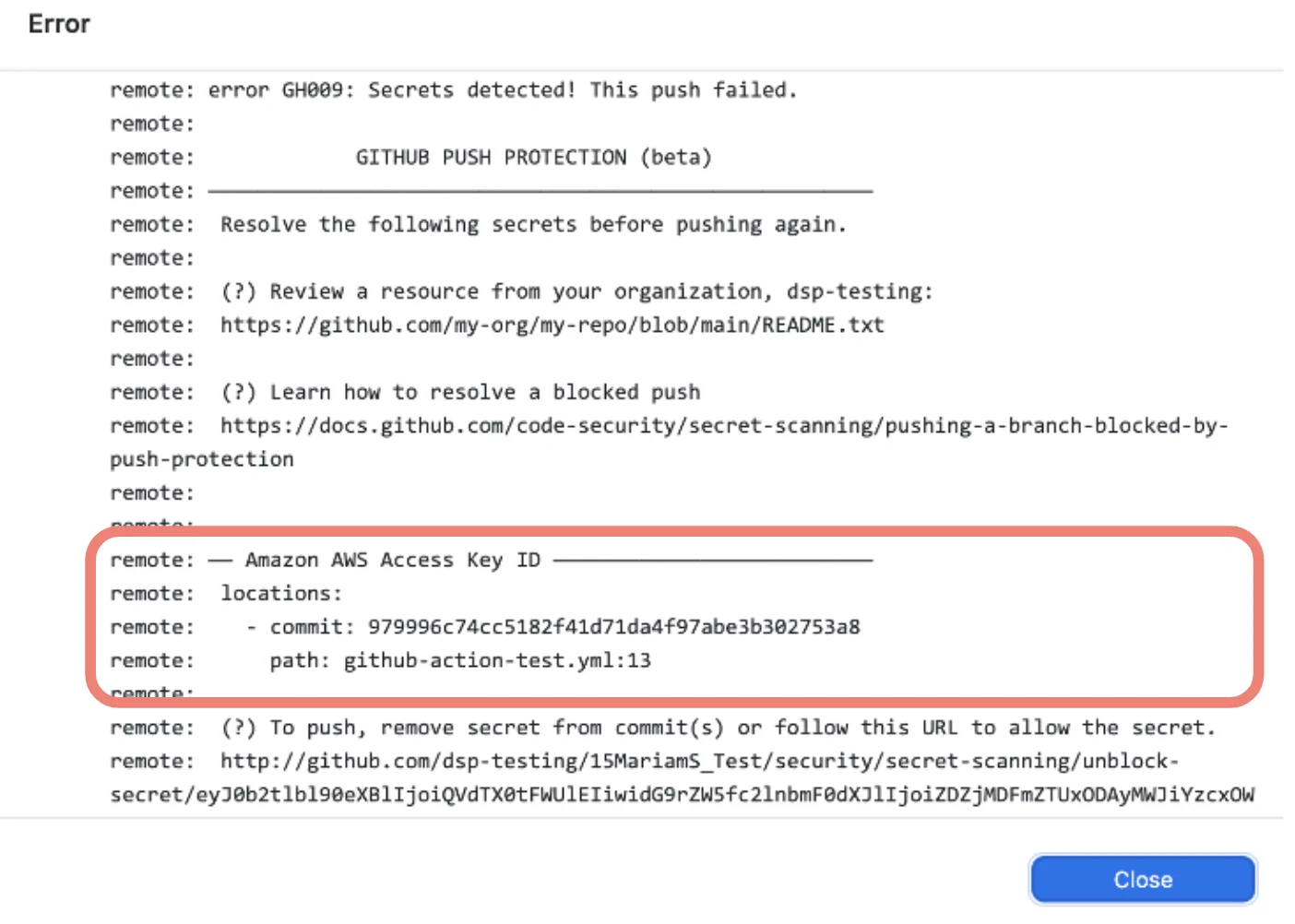
Snyk has secret detection in Snyk Code and Snyk Container, but it is not the selling point that it is for GHAS. Teams that want push-time secret blocking on GitHub usually keep GHAS secret scanning in place even when using another SAST.
Note: Teams that adopt Snyk on a GitHub-heavy estate usually keep GHAS secret scanning enabled alongside it. Push-time blocking is the strongest path-to-production defense against leaked credentials, and no Snyk module replicates the exact push-protection flow on github.com.
GHAS also includes dependency review in PRs, which diff-highlights vulnerable dependencies introduced by a pull request. Snyk shows similar information in its PR checks but routes it through its own UI.
Platform Coverage
This is the clearest dividing line. GHAS works on GitHub and only GitHub.
Key Insight
Platform reach is the one trade-off that cannot be tuned away. If any of your code lives off GitHub, GHAS can only cover part of the estate, and the rest of the feature-by-feature debate stops mattering.
If your source code lives on GitLab, Bitbucket, Azure DevOps, or a mix of platforms, GHAS is off the table for those repositories. Teams sometimes run GHAS on their GitHub estate plus a second tool for the rest, which doubles the tooling surface.
Snyk works across every major Git platform with the same dashboard, the same policies, and the same reporting. Multi-platform organizations often pick Snyk for that reason alone, even when GHAS could cover part of the estate.
Pricing and Licensing
Snyk has a public free tier (200 Open Source tests per month, unlimited Snyk Code on open-source projects) and Team and Enterprise plans priced per developer. Snyk’s pricing page lists Team starting at $25 per developer per month when billed annually.
GHAS is free on public repositories. On GitHub Enterprise, GHAS is licensed per active committer, meaning anyone who has pushed a commit to a GHAS-enabled repo in the billing month. The per-committer price is listed on the official GitHub pricing page and has been adjusted over time, so verify the current rate before budgeting.
Note: GHAS per-committer pricing has been adjusted more than once since 2022. Always verify the current rate on github.com/pricing before building a budget — forecasts that use last year's number drift quickly.
Large engineering orgs sometimes find GHAS more predictable because committer counts are easier to forecast than developer seats plus test volume. Smaller teams often find Snyk cheaper because not every developer is a daily committer.
Developer Experience
GHAS feels like part of GitHub because it is. Alerts show up in the Security tab, PR checks gate merges, dismissals flow through the same review UI, and everything is under one login.
For GitHub-only teams, that integration removes friction that bolt-on tools create.
Snyk invests heavily in IDE plugins, CLI ergonomics, and a cross-platform dashboard. The VS Code and IntelliJ plugins catch issues as you type, the CLI fits cleanly in any CI, and the dashboard rolls up findings across dozens of repos and orgs.
Teams that value the Snyk UI often cite the cross-org view as something GHAS cannot match, since GHAS reports live inside each repository and are aggregated only through the Advanced Security API.
Custom Rules and Extensibility
CodeQL is the standout here. You can write QL queries against your code’s abstract syntax tree, run them locally, and publish them to a pack that applies across repos. Security research teams at major companies maintain private CodeQL packs for project-specific rules.
Snyk Code supports custom rules through a different model, with YAML and SDK-based authoring. It is easier to get started than CodeQL but less expressive for complex cross-function data-flow rules.
If writing custom static analysis is part of your security program, CodeQL has the better story. If you mostly want high-quality out-of-the-box rules, Snyk Code’s defaults are closer to production-ready.
When Should You Choose Snyk?
Choose Snyk if:
- Your code lives on more than one Git platform (GitHub, GitLab, Bitbucket, Azure DevOps)
- You want a proprietary vulnerability database with reachability analysis for Java, JavaScript, and Python
- You need container and IaC scanning in the same dashboard as SAST and SCA
- Your team values IDE-first developer experience with fix suggestions
- Cross-org reporting and policy-as-code across business units matter
When Should You Choose GitHub Advanced Security?
Choose GitHub Advanced Security if:
- GitHub is your only source platform and likely to stay that way
- You want SAST, SCA, and secret scanning to live inside the GitHub UI
- CodeQL’s custom-query power matches your security program
- Push-time secret protection is a requirement
- Billing by active committer is easier to plan than by developer seat
Many teams start with GHAS because it is already available on GitHub Enterprise and add Snyk later for multi-platform reach or deeper SCA. Other teams begin with Snyk for its cross-platform dashboard and keep GHAS secret scanning enabled alongside it.
Both tools belong on a shortlist of serious SAST tools and SCA tools . Browse the full category pages for more head-to-head comparisons.
Related Comparisons
- Snyk vs Dependabot : just the SCA layer, head to head.
- Snyk Alternatives : broader list if Snyk is not the right fit.
- Snyk vs SonarQube : the SCA-angle view of this matchup.
- Checkmarx vs Snyk : SAST engine deep-dive against another enterprise vendor.
- SAST Tools : every SAST tool I have reviewed.
- SCA Tools : SCA-specific shortlist, including Dependabot and Snyk Open Source.
Frequently Asked Questions
Is Snyk better than GitHub Advanced Security?
Does GitHub Advanced Security include SAST?
Is Snyk free for open source?
Can I run Snyk and GitHub Advanced Security together?
How much does GitHub Advanced Security cost?

Founder, AppSec Santa
9+ years in application security. Reviews and compares 201 AppSec tools across 12 categories to help teams pick the right solution. More about me →
