PHP still runs a large share of the web, WordPress, Drupal, Magento, Laravel and Symfony apps, Shopware, and countless bespoke CMSes. The PHP SAST landscape is narrower than JavaScript or Python, but the tools that do support it are solid.
This guide compares 8 SAST tools with real PHP support: Psalm , PHPStan , SonarQube , Snyk Code , Semgrep , RIPS (now part of SonarSource), Progpilot, and Exakat.
Why PHP SAST is different
PHP has a history of dynamic, loosely typed code that makes static analysis harder than statically typed languages. Modern PHP (7.x and 8.x) added return types, union types, readonly properties, enums, and more, which closes a lot of the gap.
Type checkers like Psalm and PHPStan now produce very useful signal, and SAST tools that understand modern PHP type annotations return far fewer false positives than they did a decade ago.
PHP projects also depend on large frameworks that ship their own conventions. A useful PHP SAST tool understands Laravel’s Eloquent and request helpers, Symfony’s HttpFoundation and Doctrine, WordPress’s $wpdb and sanitization functions, and Drupal’s form API. Without framework awareness you get either missed sinks or noisy alerts.
The common PHP-specific vulnerability patterns SAST tools target:
- SQL injection in raw
mysql_*legacy code and string-concatenated PDO queries - XSS in templates that skip
htmlspecialcharsore() - Remote code execution via
eval,system,exec,passthru, andpreg_replacewith the deprecated/emodifier - File inclusion (LFI and RFI via
include,require, andfile_get_contents) unserializevulnerabilities- Type juggling in
==comparisons - Weak session and cookie configuration
- Weak cryptography (
md5,sha1,DES)
PHP also pairs naturally with SCA tools
for Composer package coverage, SAST handles your code, SCA handles your composer.json dependencies.
Top SAST tools for PHP
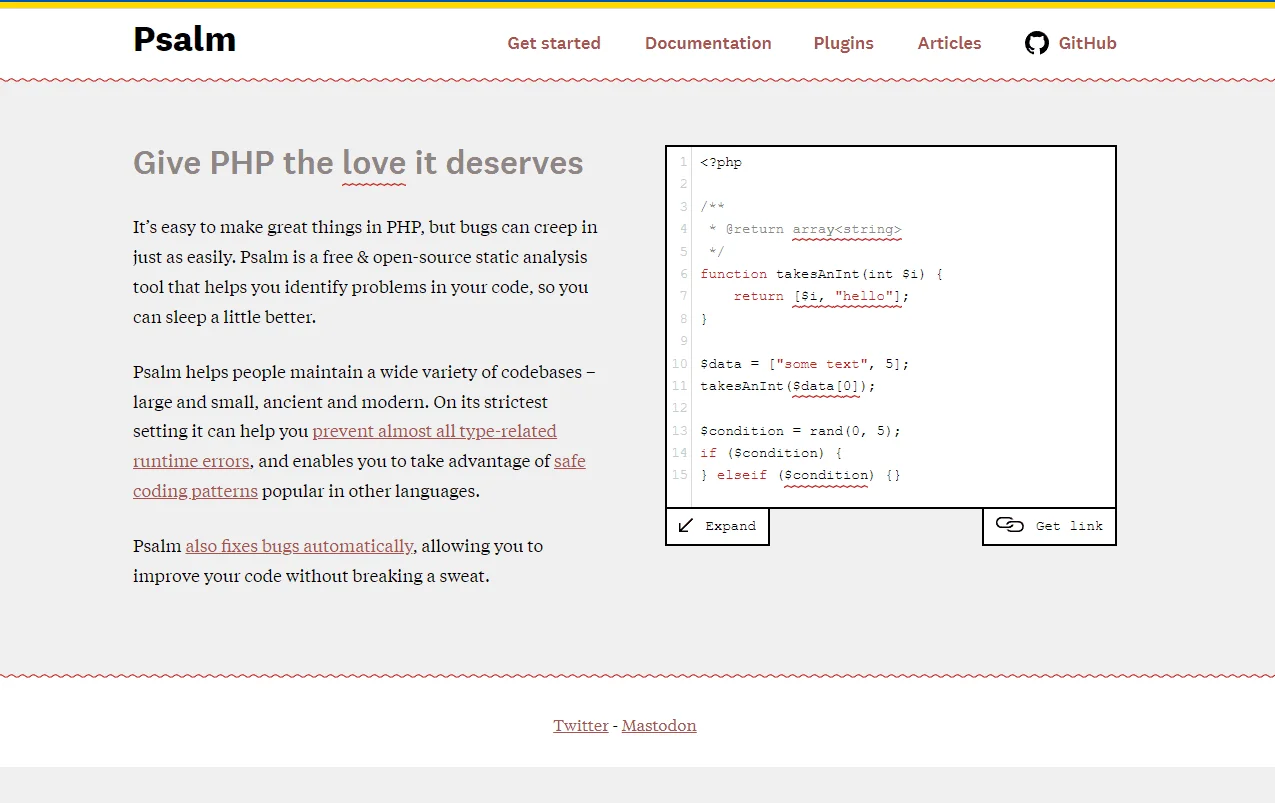
1. Psalm
Psalm is a static analysis tool for PHP built by Vimeo and open sourced under MIT . It started as a type checker and grew to include a TaintAnalysis mode that traces untrusted input to sensitive sinks.
What Psalm does well: Precise type inference for modern PHP, with rich support for generics, conditional return types, and PHPDoc annotations.
The TaintAnalysis plugin makes it the rare open-source PHP tool with real cross-function taint tracking. Psalm understands Laravel and Symfony well and has a large ecosystem of plugins for framework-specific rules.
Where Psalm falls short: Dedicated security rules outside TaintAnalysis are thinner than in Semgrep or SonarQube. Development activity is steady but more conservative than a decade ago. Configuring the taint engine on a legacy codebase takes effort.
Best fit: Any modern PHP project that wants both type safety and a baseline of taint analysis in one tool. Pair it with Semgrep or SonarQube for dedicated security rules.
2. PHPStan
PHPStan
is the other major open-source PHP static analyzer. It is a pure type and correctness checker by default, it does not ship a built-in security analyzer the way Psalm does, but the community has built security-focused extensions such as phpstan-safe-rule and framework-specific rule packs.
What PHPStan does well: Fast, precise, and extremely popular in the PHP community, with first-class Laravel (Larastan ), Symfony, Doctrine, and WordPress extensions. The rule levels (0 through 9) make it easy to introduce into a legacy codebase without drowning in errors on day one.
Where PHPStan falls short: No built-in taint analysis. Security coverage depends on third-party extensions, which are maintained at varying levels. You will get more direct security signal from Psalm’s TaintAnalysis or from dedicated tools like Semgrep.
Best fit: PHP teams that already rely on PHPStan for type checking. Keep it and layer a dedicated security scanner (Semgrep or SonarQube) on top rather than expecting PHPStan to do both jobs.
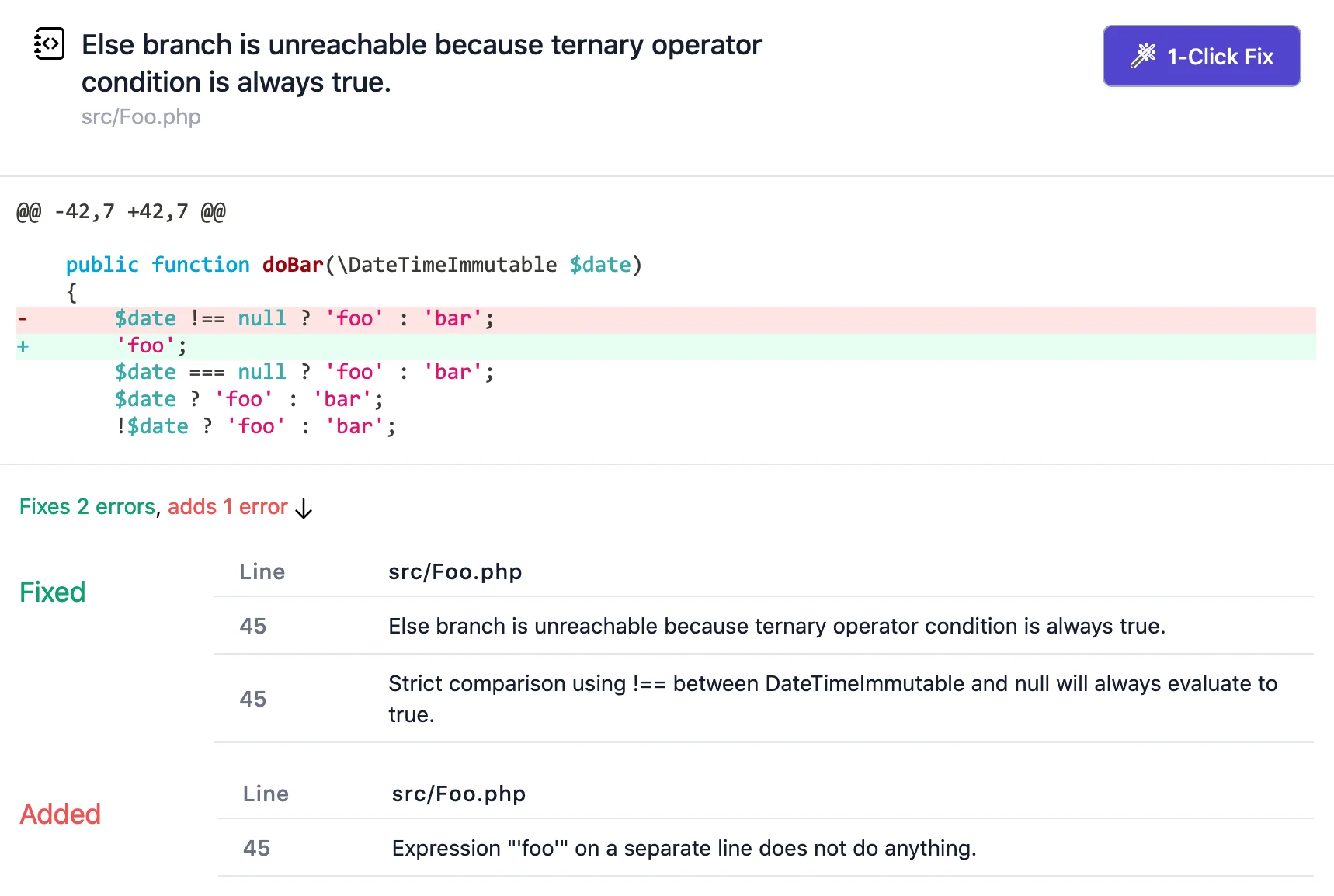
3. SonarQube
SonarQube has first-party PHP support and, after the 2021 RIPS acquisition, inherited one of the strongest PHP taint engines in the industry. Community Edition covers a broad set of security and quality rules for PHP; Developer Edition and above add cross-procedural taint analysis .
What SonarQube does well: Deep PHP rule coverage, hundreds of rules across security, reliability, and maintainability. Quality gates block pull requests that introduce new issues. The taint engine understands major PHP frameworks including Laravel, Symfony, WordPress, and Drupal.
Where SonarQube falls short: Community Edition catches pattern-based issues but not cross-function taint. The jump to Developer Edition is a paid commercial tier. For small open-source projects the free slice is strong; for real taint on large PHP monoliths you need the paid version.
Best fit: PHP teams that want one tool for both security and code quality, with a serious upgrade path once you need cross-file taint.
4. Snyk Code
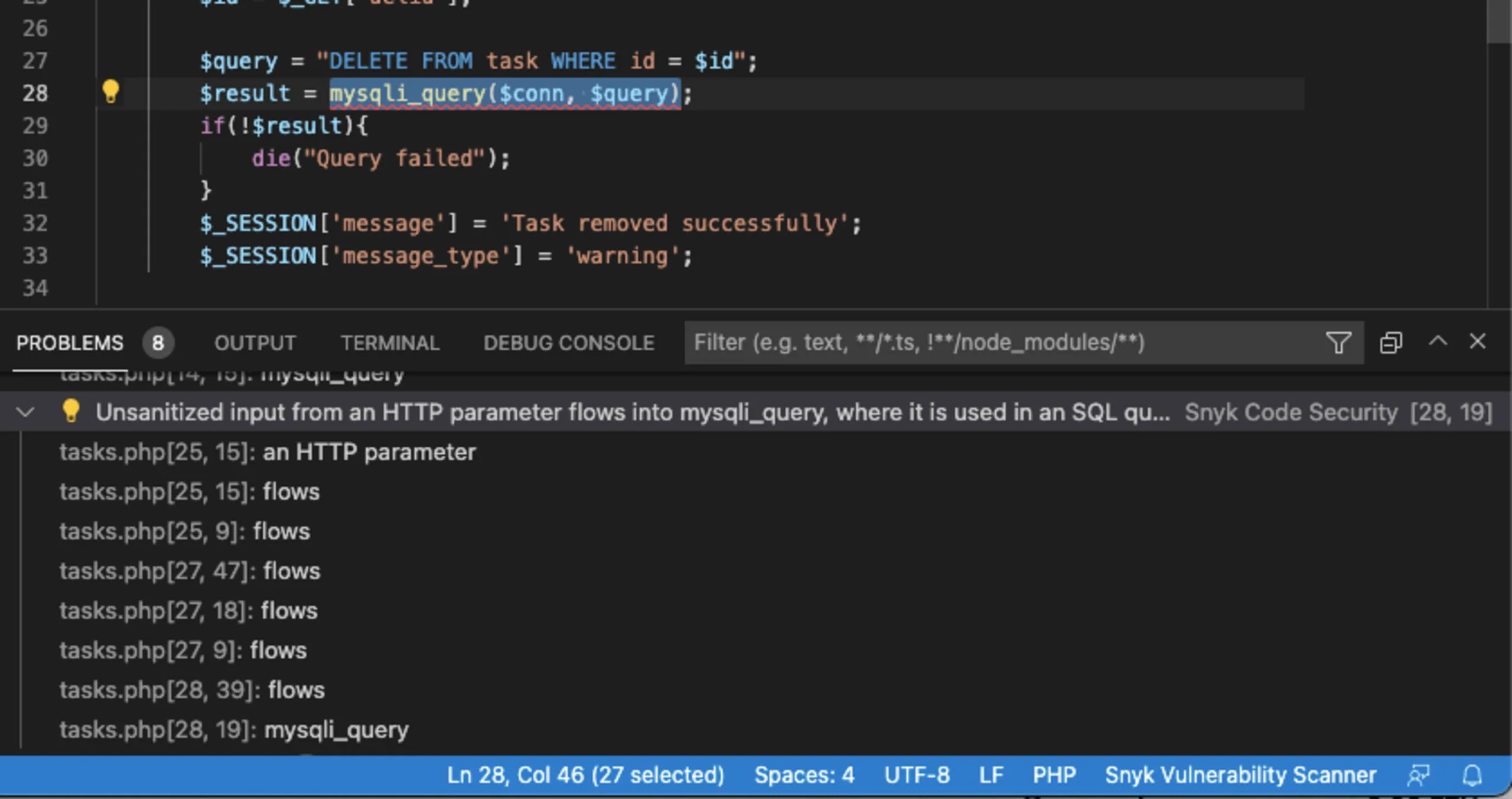
Snyk Code supports PHP through its DeepCode-derived engine . It performs cross-file taint analysis and runs fast enough to give in-IDE feedback as you code.
What Snyk Code does well: Modern PHP taint analysis with real data flow across files, not just single-function pattern matches. Good IDE integrations (VS Code, PhpStorm). Fix guidance is concrete enough to act on without digging into docs every time.
Where Snyk Code falls short: The free tier is IDE-only. CI/CD integration with full taint requires a paid plan. It is SaaS, source code is sent to Snyk, which rules it out for air-gapped or classified environments. PHP coverage is thinner than Python or JavaScript, though still usable for common frameworks.
Best fit: PHP teams that want developer-friendly commercial taint analysis with a fast IDE workflow and don’t have a regulated-enterprise procurement process.
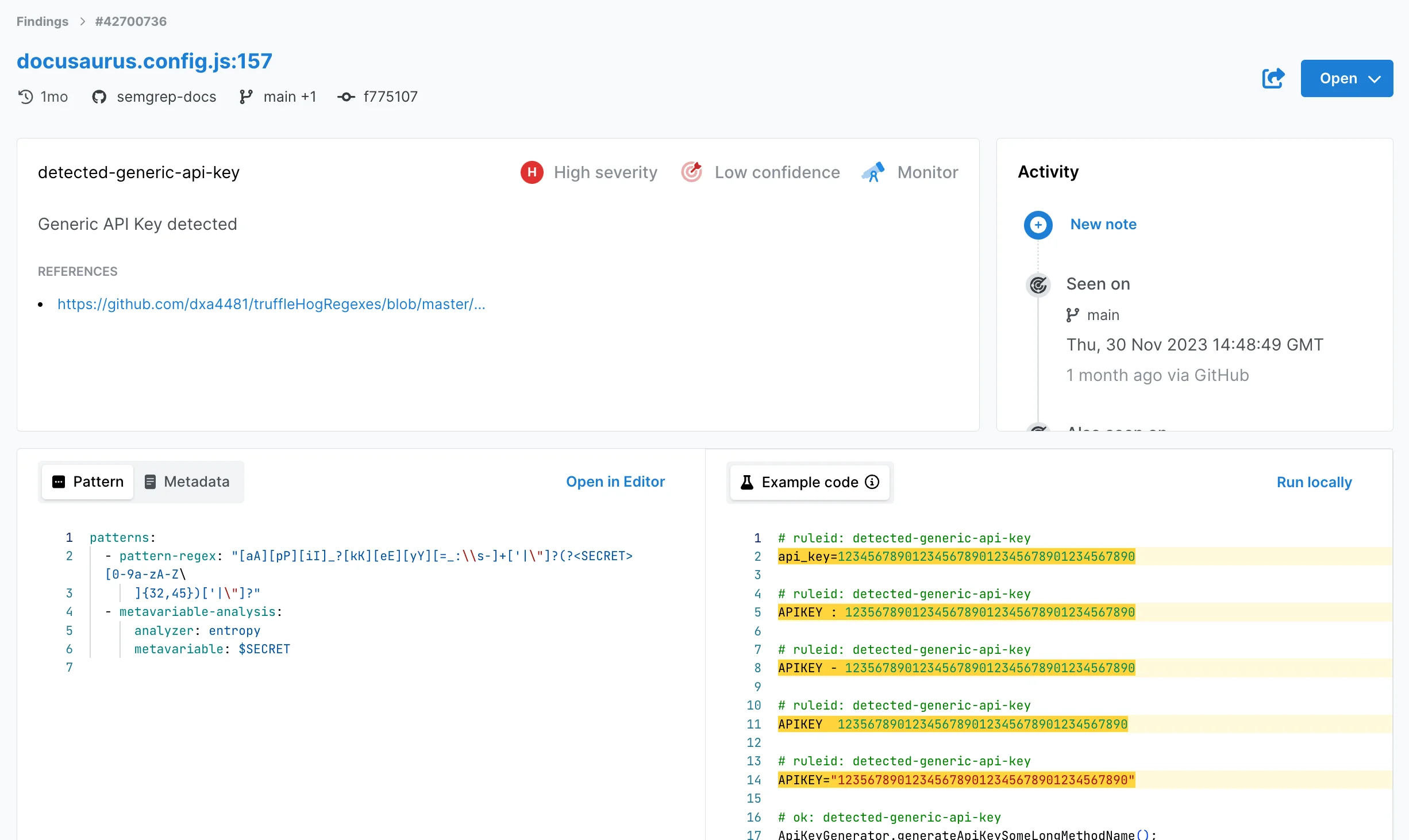
5. Semgrep
Semgrep supports PHP as a first-class language in its pattern engine. The Semgrep Registry includes PHP rulesets covering OWASP Top 10, Laravel security, WordPress patterns, Symfony misuse, and template injection.
What Semgrep does well: Custom PHP rules in YAML are readable and fast to write, which is the killer feature for teams with internal frameworks or recurring review patterns. The community registry is solid. Multi-language support matters when PHP sits alongside JavaScript, Python, or Go in the same repo.
Where Semgrep falls short: Community Edition taint analysis for PHP is limited compared to SonarQube Developer Edition or Snyk Code. Deep cross-file taint is a paid feature. For pure PHP-specific depth, Psalm’s TaintAnalysis and SonarQube still have an edge.
Best fit: Teams that want to author their own PHP rules, or polyglot shops that want a single scanner across multiple languages.
6. RIPS (now part of SonarSource)
RIPS was one of the most respected PHP-specific SAST tools for years. It was acquired by SonarSource in 2021, and the standalone product was discontinued. The PHP analysis engine lives on inside modern SonarQube and SonarCloud.
What the RIPS engine did well: Deep PHP-specific taint analysis with framework awareness, specifically tuned for the quirks of PHP semantics, type juggling, reference aliasing, the $$ variable-variable construct, magic methods, and framework-level sinks.
Where RIPS falls short today: It is no longer a standalone product. If a vendor claims to sell you “RIPS” in 2026, check carefully. The still-available community academic version from TU Darmstadt is very old and not maintained. In practice, “I want RIPS” today means “I want SonarQube Developer Edition or above.”
Best fit: For modern use, this is a reason to evaluate SonarQube Developer Edition if you are a PHP shop. Use the RIPS branding awareness to understand the lineage behind SonarQube’s current PHP engine.
Note: If a vendor claims to sell you "RIPS" in 2026, check carefully. The original RIPS product was discontinued after the 2021 SonarSource acquisition, and the only living RIPS engine is inside SonarQube Developer Edition and above. The TU Darmstadt academic version is public but unmaintained.
![The discontinued RIPS 0.52 scanner showing a SQL Injection finding in work.php with the user-input-reaches-sink trace and the work_functions.php source with the $_SESSION['Userid'] tainted variable flowing into a mysql_query system call - the PHP-specific taint analysis engine now absorbed into SonarQube](/images/pages/sast-tools-for-php/06-rips.webp)
7. Progpilot
Progpilot is an open-source PHP taint analysis tool hosted on GitHub (designsecurity/progpilot
). It focuses specifically on tracking untrusted data flow through PHP applications.
What Progpilot does well: Free, PHP-specific taint analysis, an unusual and valuable combination. It can flag common injection and RCE patterns by tracing user input across functions and files. The CLI is simple to wire into CI.
Where Progpilot falls short: Development activity is slow, and community adoption is small compared to Psalm or PHPStan. Framework awareness is limited, so you will see both misses and false positives on Laravel and Symfony codebases. It is best used as a second opinion, not the primary scanner.
Best fit: Open-source PHP projects looking for a free dedicated taint scanner to complement Psalm, PHPStan, or Semgrep. Treat it as a supplementary check.
![Progpilot CLI output scanning a PHP app and reporting SQL_INJECTION from UserController _GET[id] to mysqli_query, XSS from SearchController _GET[q] to echo in a template, and UNSERIALIZE from _COOKIE[data] to an unserialize sink - the source-to-sink taint flow described in the prose](/images/pages/sast-tools-for-php/07-progpilot.webp)
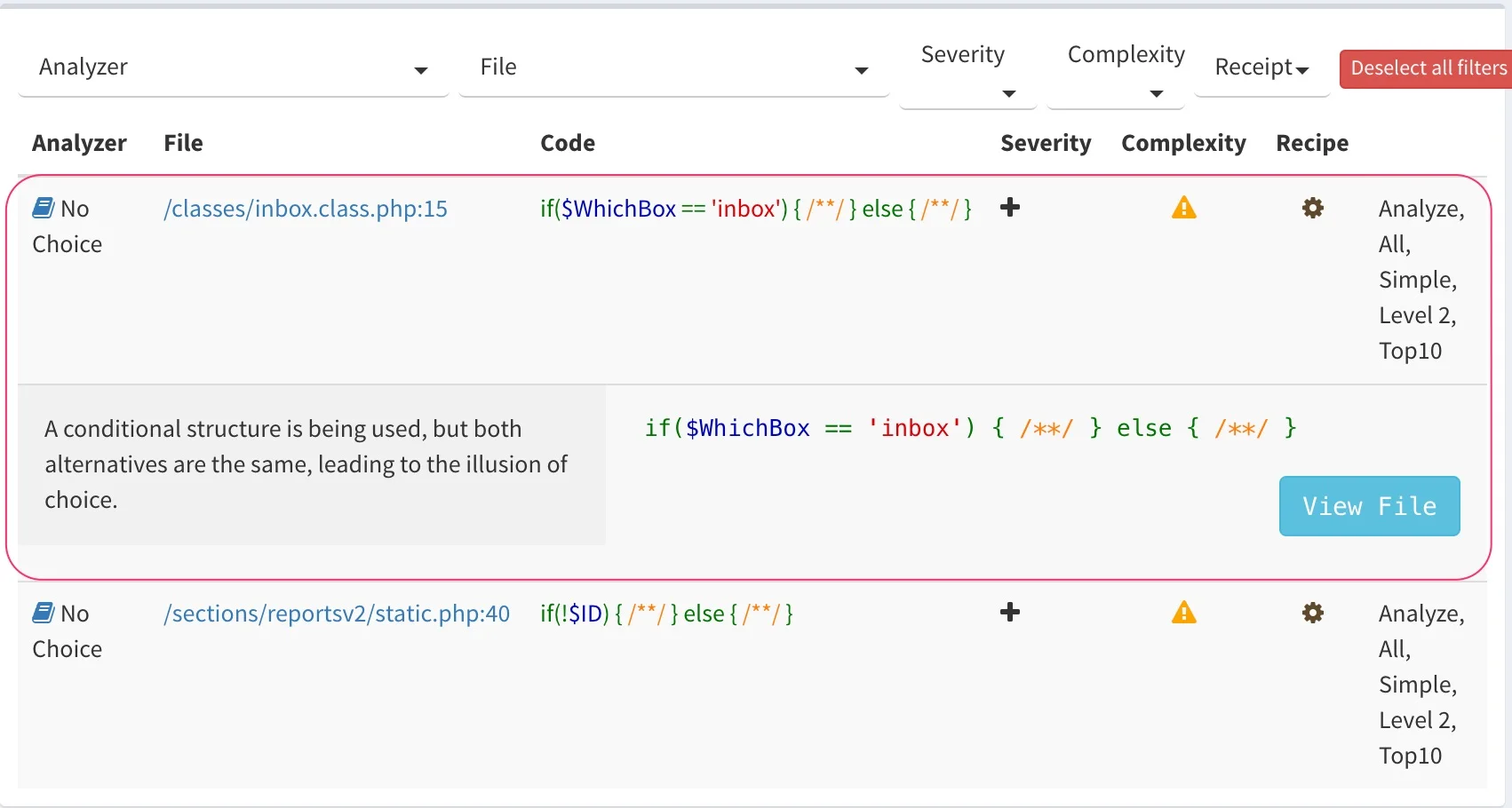
8. Exakat
Exakat is an open-source PHP audit tool that focuses on broad code quality, compatibility, and security analysis. It ships hundreds of analyzers for different aspects of a PHP codebase.
What Exakat does well: Broad coverage beyond pure security, compatibility checks between PHP versions, dead code detection, suggestions for modern PHP idioms, and a long list of security patterns (weak crypto, insecure randomness, insecure unserialize, dangerous eval and system calls). Reports are thorough.
Where Exakat falls short: No dedicated taint engine. Output can be overwhelming, the sheer volume of analyzers produces a lot of findings that need tuning before the signal rises above the noise. Framework awareness is limited.
Best fit: Teams doing periodic deep audits of a PHP codebase, especially when migrating between PHP versions. It is more of an auditor’s tool than a CI gate.
Comparison table
| Tool | Type | PHP Depth | Taint Analysis | License | Best For |
|---|---|---|---|---|---|
| Psalm | Type checker + taint | Deep types + taint plugin | Cross-function (plugin) | Open source (MIT) | Types + baseline taint in one tool |
| PHPStan | Type checker | Deep types | None (extensions only) | Open source | PHP teams already standardized on PHPStan |
| SonarQube | SAST + quality | Deep, RIPS-derived | Paid tiers | Open source / Commercial | Quality + security combined |
| Snyk Code | SAST (commercial) | Moderate | Cross-file | Commercial (free IDE) | Developer-first taint |
| Semgrep | SAST (multi-language) | Strong patterns | Limited (paid for full) | Open source / Commercial | Custom rules, polyglot |
| RIPS (SonarSource) | SAST (discontinued) | Historically very deep | Yes, now inside SonarQube | Commercial (via SonarQube) | Modern equivalent is SonarQube DE+ |
| Progpilot | PHP taint scanner | Narrow, taint-focused | Basic cross-function | Open source | Free supplementary taint |
| Exakat | PHP audit tool | Broad rule-based | None | Open source | Deep periodic audits |
How to choose for your use case
Small team or open-source PHP project: Run Psalm with TaintAnalysis enabled plus Semgrep’s PHP ruleset in CI. Both are free, both understand modern PHP, and together they cover types, correctness, and dedicated security rules. Add SonarQube CE as a quality gate if you want formal PR blocking.
Growing Laravel or Symfony team: Psalm or PHPStan (with Larastan or the Symfony extension) for type safety, Semgrep for security rules, plus SonarQube Community Edition for broader coverage. When you outgrow the free tier and need real cross-file taint, SonarQube Developer Edition is the natural upgrade because it inherits the RIPS engine.
Enterprise PHP shop (Magento, WordPress VIP, legacy monoliths): This is where SonarQube Developer Edition or higher really pays off, because the RIPS lineage means deep PHP taint analysis was a first-class concern. Snyk Code is the other commercial option worth piloting. See the enterprise SAST tools guide for the broader landscape.
Polyglot monorepo (PHP plus JavaScript, Python, Go): Semgrep is the most practical single tool, one scanner, many languages, YAML rules you can write in minutes. Add Psalm for PHP-specific type depth.
WordPress or Drupal plugin author: Psalm with WordPress extension plus Semgrep’s WordPress ruleset. Both understand WordPress’s sanitization idioms and will flag common missing escapes.
Open source vs commercial
The free PHP SAST stack, Psalm with TaintAnalysis, PHPStan, Semgrep CE, SonarQube CE, and niche tools like Progpilot and Exakat, is surprisingly strong for modern PHP. The gap versus commercial tools is still real in two places: cross-procedural taint analysis on large codebases, and framework-specific sinks for Laravel, Symfony, WordPress, Drupal, and Magento.
SonarQube Developer Edition is the clearest commercial upgrade path for PHP teams because it inherits the RIPS engine. The RIPS acquisition in 2021 consolidated what used to be two products into one, and the modern SonarQube PHP analyzer is where that engine now lives. If you specifically want a PHP-depth taint engine, this is where it went.
Key Insight
"I want RIPS for PHP" today means "I want SonarQube Developer Edition or higher". The brand is retired, but the engine is the same one that defined deep PHP taint analysis for a decade, and it still carries the franchise.
Snyk Code is the other commercial option I see PHP teams evaluate. Its PHP support is less deep than Python or JavaScript, but it is fast, cross-file, and has strong IDE ergonomics.
The specialized commercial PHP SAST vendors of the 2015-2020 era are mostly gone, RIPS was acquired, and most of the rest consolidated into broader platforms. That leaves PHP with fewer dedicated commercial options than Java or C#, but the open-source side is healthier than it was a decade ago.
For a more detailed look at free options, see the open source SAST tools guide . For buying considerations, see SAST vs SCA: which do you need first .
If your team works across multiple languages, the dedicated SAST picks for Java , Python , JavaScript and TypeScript , Go , and C#/.NET each cover tool nuances that generic SAST lists miss.