JavaScript and TypeScript power both frontend and backend applications — SPAs, API services, serverless functions, and full-stack frameworks — and each of these contexts has distinct security concerns.
This guide compares 8 SAST tools with strong JavaScript and TypeScript support: Semgrep , ESLint security plugins, Snyk Code , SonarQube , CodeQL , NodeJSScan , Gitleaks , and Mend SAST .
Why JavaScript SAST is different
JavaScript’s dynamic type system, prototype inheritance, and pervasive asynchronous patterns create specific challenges for static analysis. Taint flows in a Node.js API can pass through Promise chains, callbacks, middleware arrays, and dynamic property access in ways that confuse static analysis engines built for typed languages.
TypeScript improves the situation with explicit types — CodeQL and Semgrep both use TypeScript’s type information to produce more accurate results. But many production Node.js codebases mix TypeScript and plain JavaScript, and a surprising amount of attack surface lives in configuration files, template literals, and dynamic require() calls.
The major vulnerability patterns in JavaScript that SAST tools target: XSS via innerHTML and dangerouslySetInnerHTML, prototype pollution
, server-side template injection, command injection through child_process, SQL injection in query strings, SSRF via fetch or axios without allowlist validation, eval() and Function() misuse, and regular expression denial of service (ReDoS).
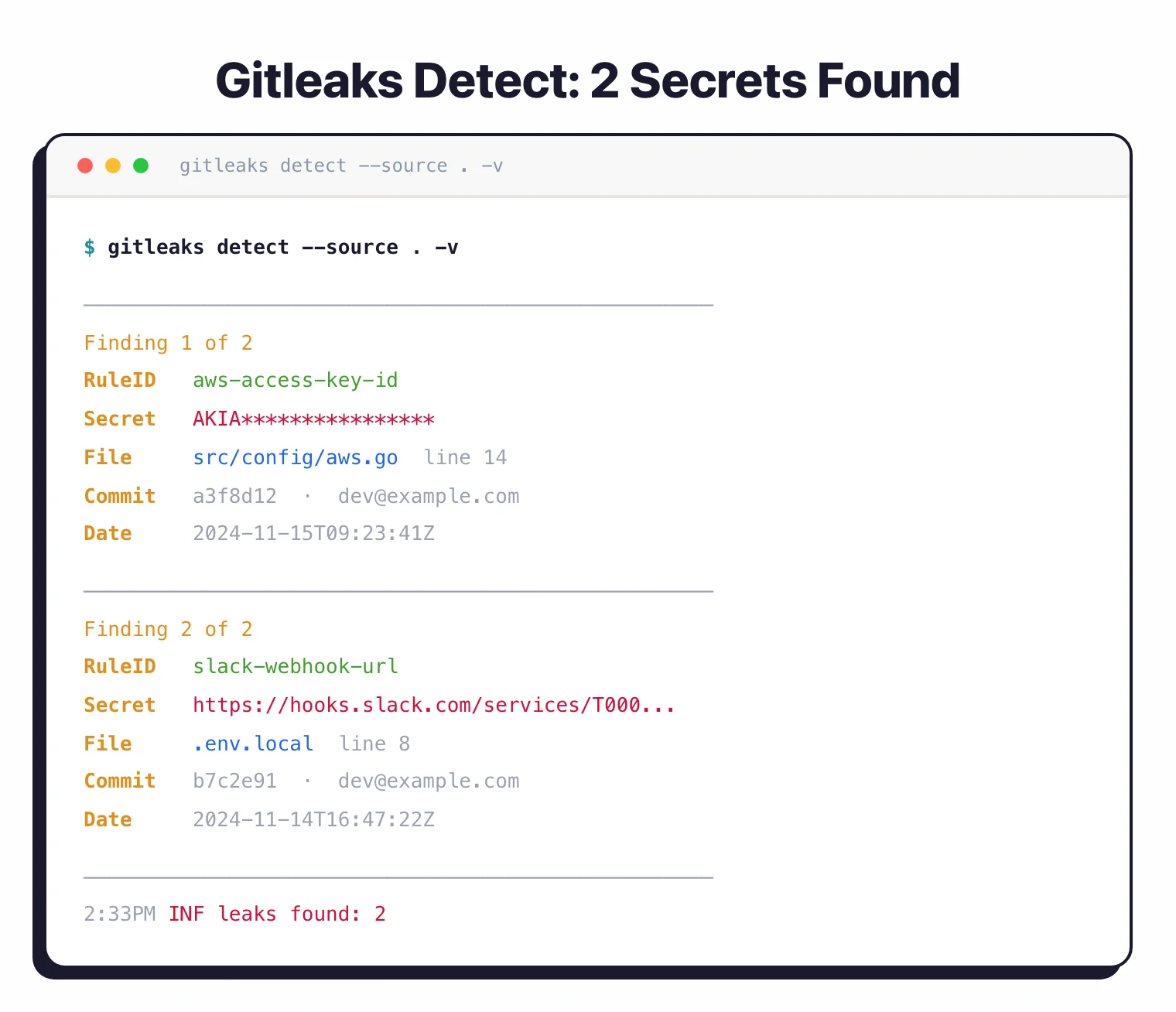
JavaScript repos also have a secrets problem that Python and Java repos do not see at the same scale.
API keys, tokens, and credentials in .env files, config files, and git history are endemic — which is why Gitleaks
belongs in any JS repo security stack even though it is not a traditional SAST tool.
Top SAST tools for JavaScript
1. Semgrep
Semgrep supports JavaScript and TypeScript natively with structural pattern matching that understands the AST rather than matching text. The Semgrep Registry includes rulesets for Express.js, React XSS patterns, Node.js security, Next.js, and OWASP Top 10 for JavaScript.
What Semgrep does well: Custom rules that match JavaScript and TypeScript patterns are fast to write and easy to test. Semgrep can match across destructured assignments, template literals, and async/await chains. Community rules cover the most common Express.js and React vulnerability patterns out of the box.
Where Semgrep falls short: Cross-file inter-procedural taint analysis (following a tainted value from an Express req.body through multiple middleware files to a database call) requires Semgrep Code platform tier. The community engine does cross-function analysis within a file but stops at module boundaries for complex flows.
Best fit: The default anchor for any JavaScript SAST stack — especially in multi-language repos. Add ESLint security plugins for the IDE layer and CodeQL on the main branch for deep taint analysis.
2. ESLint security plugins
ESLint is the dominant JavaScript linter, and a family of security plugins extends it into SAST territory:
eslint-plugin-security— checks foreval, unsafe regex,child_processwith user input, andfswith variable pathseslint-plugin-no-unsanitized— enforces sanitization beforeinnerHTML,outerHTML,insertAdjacentHTMLeslint-plugin-react-security— React-specific XSS patterns
What ESLint plugins do well: They run in the IDE and pre-commit hooks, giving developers instant feedback. The no-unsanitized plugin is particularly valuable for React codebases — it catches dangerouslySetInnerHTML misuse and unsafe DOM manipulation at the point of writing.
Where ESLint plugins fall short: No data flow analysis — they match syntactic patterns only. A tainted value renamed to safeData will not be flagged even if it is not actually sanitized. ESLint plugins are a first layer, not a complete SAST solution.
Best fit: Every JavaScript project. ESLint security plugins are the fastest way to add a security layer and should run on every commit regardless of what other SAST tools are in the pipeline.

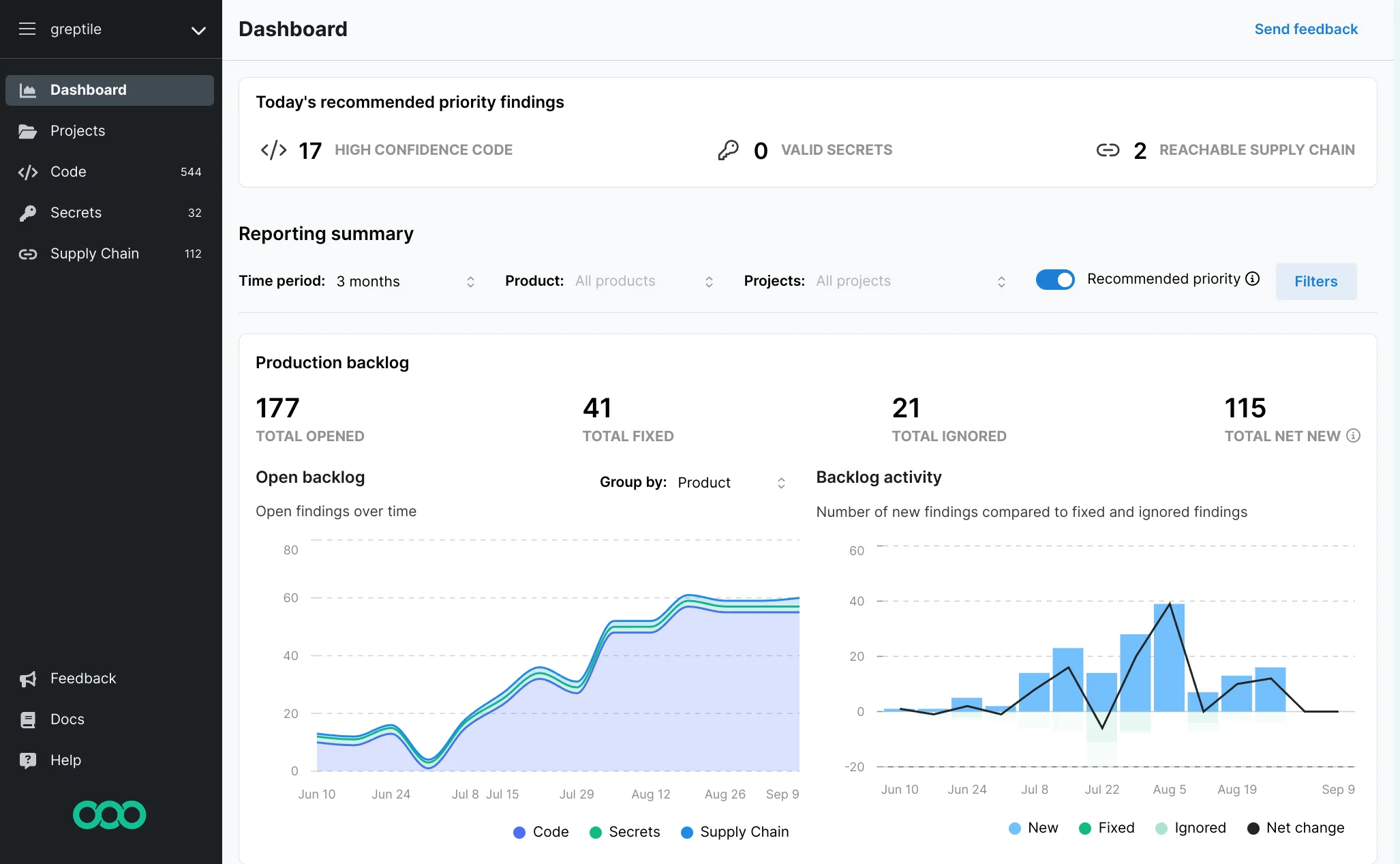
3. Snyk Code
Snyk Code provides commercial-grade JavaScript and TypeScript SAST with IDE and CI/CD integration. Its analysis engine understands React, Vue, Angular, Express, and Next.js patterns — including cross-file taint flows through React component prop chains and Express middleware.
What Snyk Code does well: Data flow analysis across files and modules is the headline capability. Snyk Code can trace a tainted req.body property through three middleware functions to a MongoDB $where call and flag it as a NoSQL injection. The fix suggestions are developer-friendly and specific.
Where Snyk Code falls short: Full CI/CD taint analysis requires a paid plan. It is SaaS — source code goes to Snyk’s infrastructure. For some regulated environments that is a procurement blocker.
Best fit: Development teams that want commercial-quality JavaScript taint analysis with IDE-first feedback and specific fix guidance.
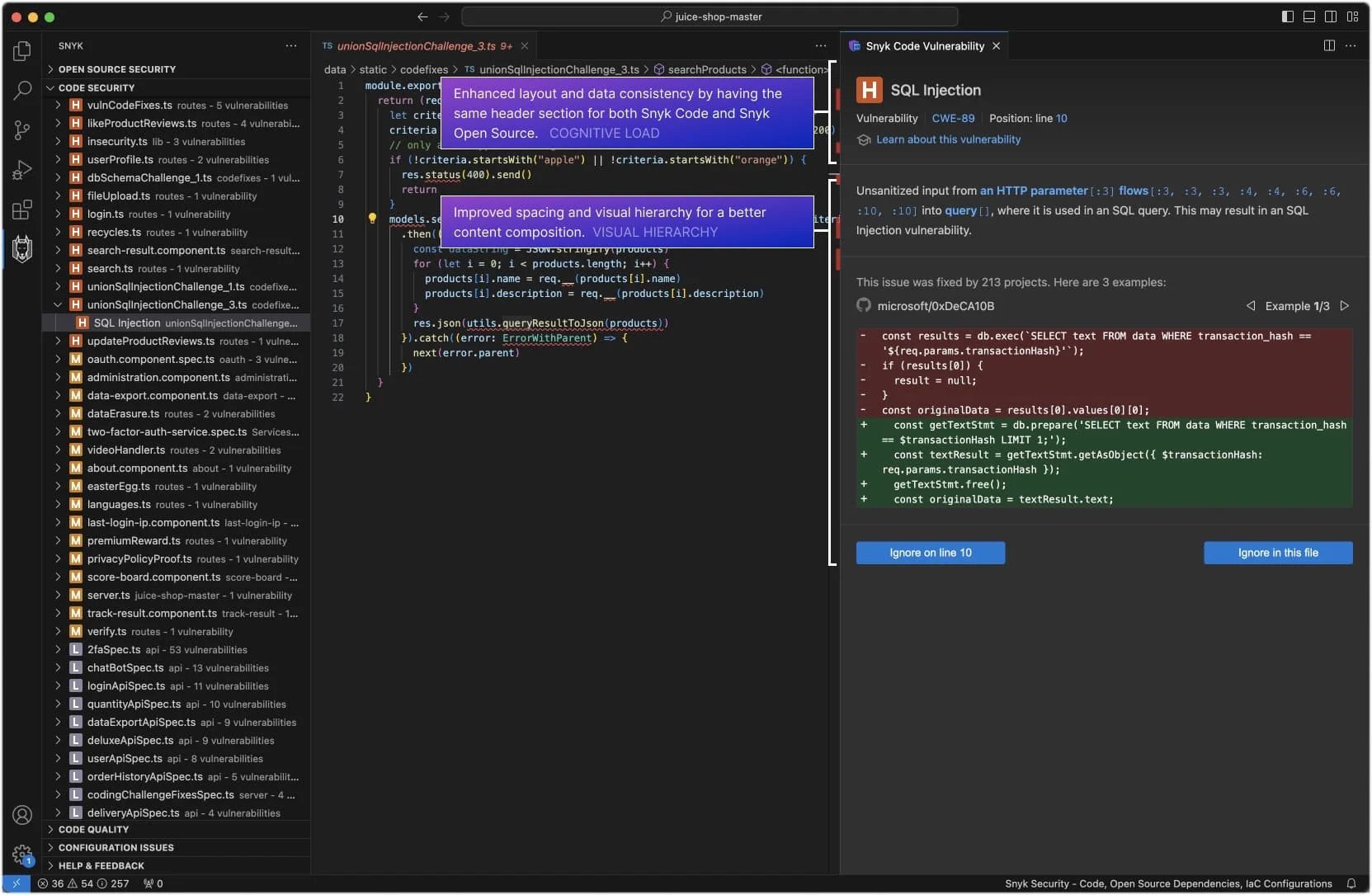
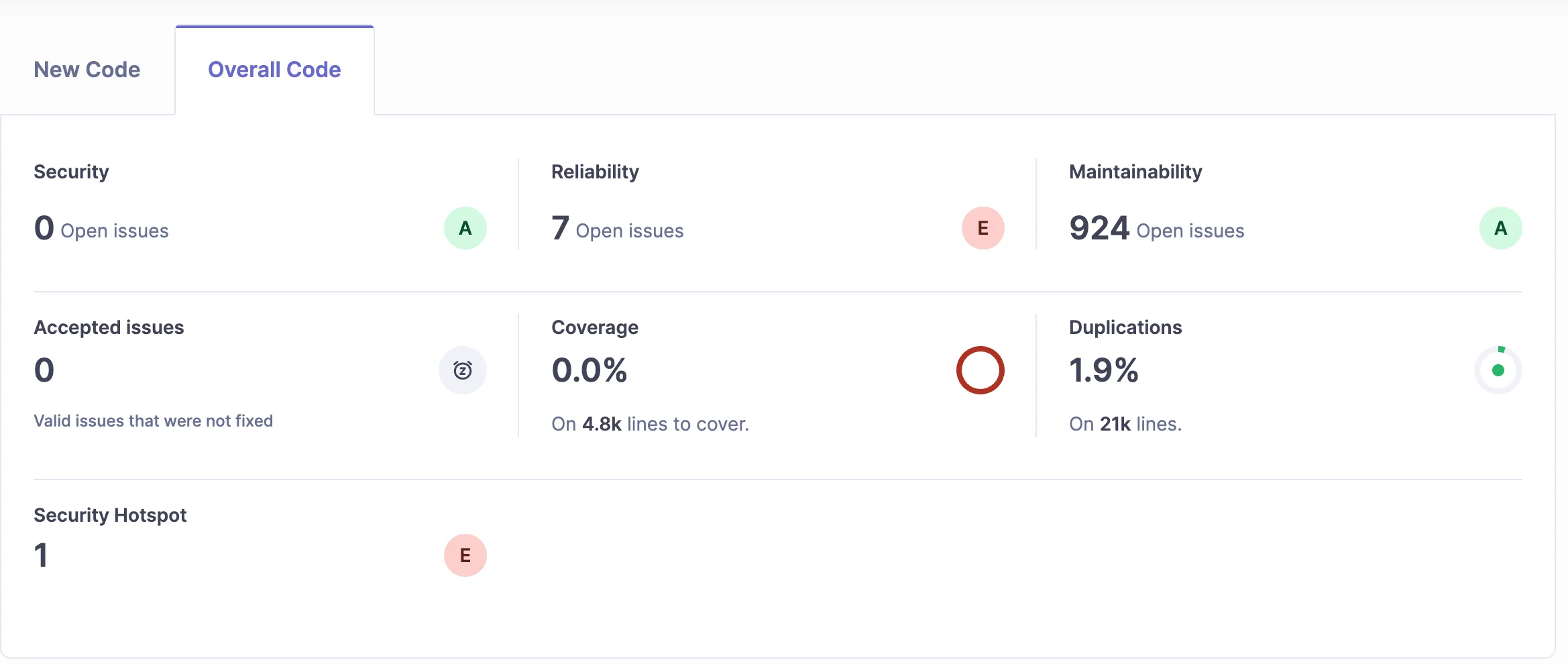
4. SonarQube
SonarQube supports JavaScript and TypeScript with security rules covering injection, XSS, weak cryptography, insecure cookies, and SSRF. Community Edition provides pattern-based analysis; Developer Edition adds inter-procedural taint tracking. SonarQube is often the practical choice for organizations already using it for code quality who want to add security coverage.
What SonarQube does well: The TypeScript integration is one of the strongest in open-source — SonarQube uses TypeScript’s type system to reduce false positives. Its security categories map to OWASP, CWE, and SANS Top 25, making it easy to align findings with compliance requirements.
Where SonarQube falls short: Deep taint analysis requires a paid edition. Community Edition misses complex multi-file injection patterns that commercial tools catch.
Best fit: Teams using SonarQube for code quality who want security scanning in the same platform and quality gate.
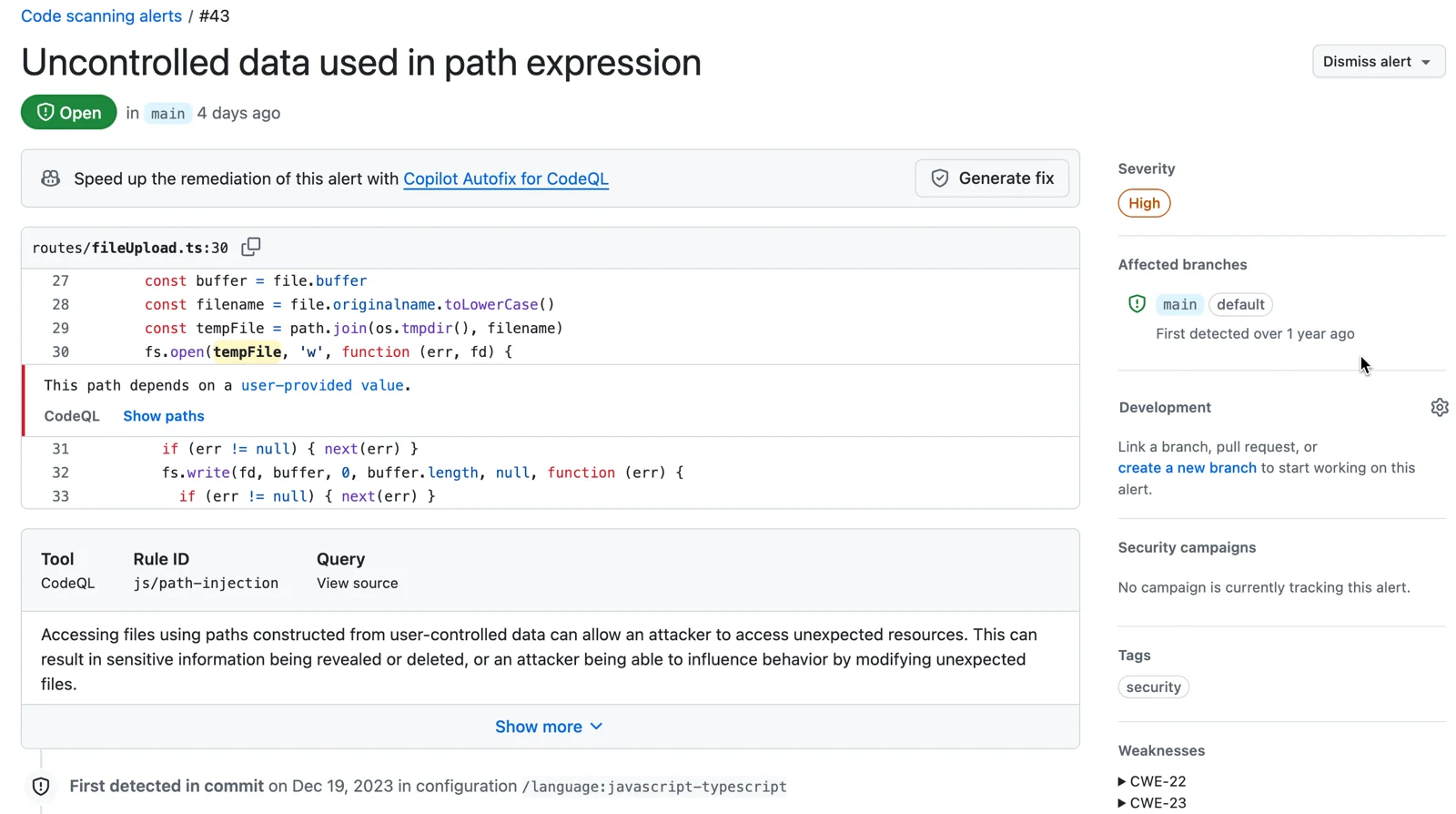
5. CodeQL
CodeQL provides the deepest JavaScript and TypeScript data flow analysis available. GitHub ships CodeQL queries for Node.js and browser JavaScript covering XSS, prototype pollution, path traversal, SSRF, injection, and more. CodeQL models the actual JavaScript runtime semantics including prototype chains and dynamic property access.
What CodeQL does well: Inter-procedural taint tracking through entire Express.js applications — following req.params, req.body, and req.query through middleware chains, utility functions, and database calls. For complex Node.js services, CodeQL routinely finds vulnerabilities that pattern-based tools miss entirely.
Where CodeQL falls short: Analysis is slow — 10–30 minutes for a large Node.js monorepo. It is free for public repositories via GitHub Actions but requires GitHub Advanced Security for private repos. Query writing has a steep learning curve beyond the default bundle.
Best fit: Node.js API services and web applications processing untrusted user input where deep inter-procedural taint analysis matters.
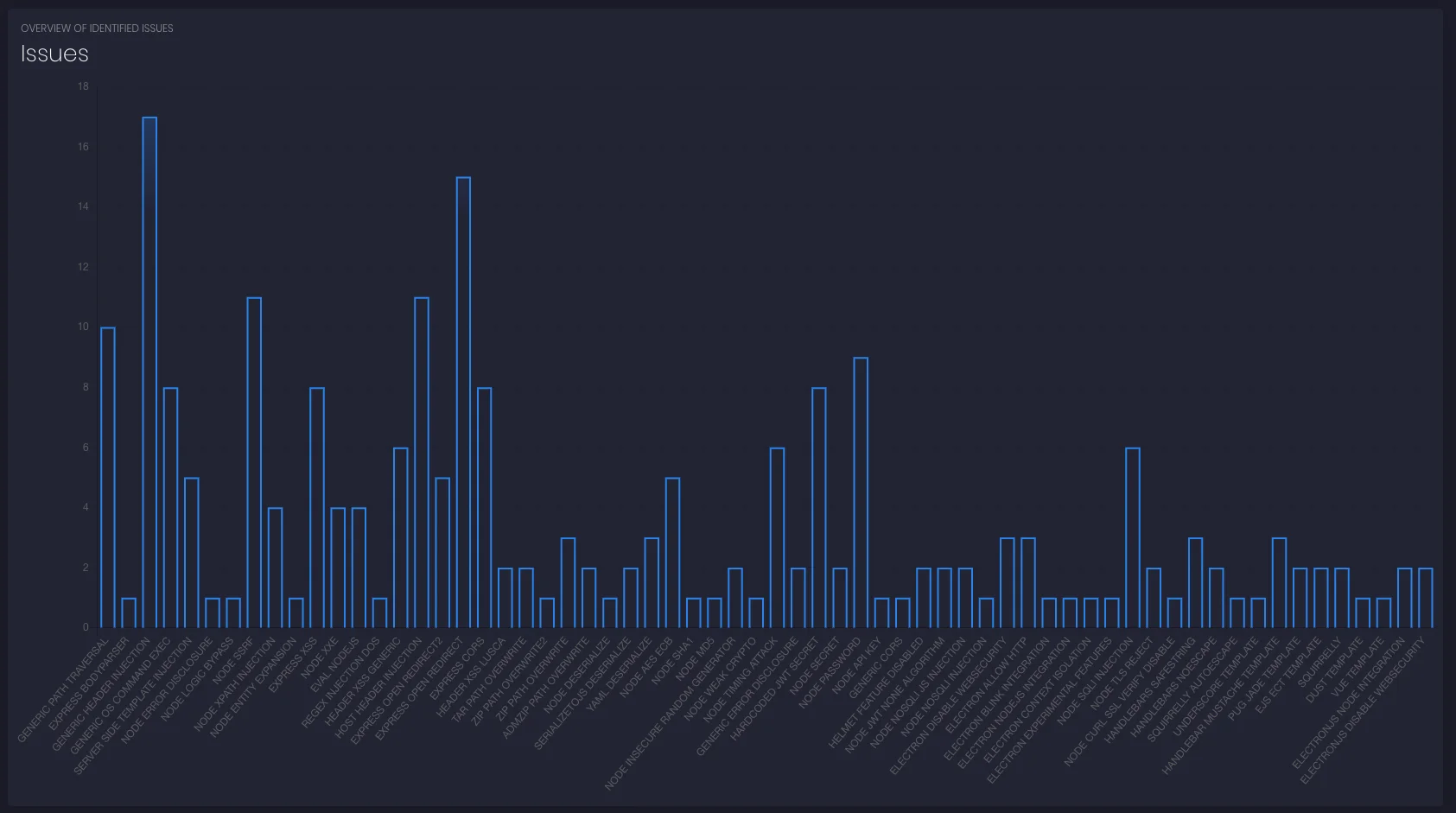
6. NodeJSScan
NodeJSScan
is a purpose-built SAST tool for Node.js applications
. It includes an AST parser and a set of security rules targeting Node.js-specific patterns: child_process injection, eval usage, insecure cookie settings, JWT misconfigurations, and SSRF through http.get and axios.
What NodeJSScan does well: Node.js-specific detection that generic multi-language tools sometimes miss. The rules cover Express.js, Hapi.js, and bare Node.js HTTP modules with context that language-agnostic tools lack.
Where NodeJSScan falls short: Less actively maintained than Semgrep or commercial tools. No cross-file data flow analysis. Coverage of modern frameworks like Next.js and Nest.js is limited.
Best fit: Node.js backend projects that want a lightweight, framework-specific secondary scanner alongside Semgrep.
7. Gitleaks
Gitleaks
is a secret detection tool, not a traditional SAST tool — but it belongs in every JavaScript security pipeline. JavaScript repos accumulate hardcoded tokens in config files, .env files, CI scripts, and git history at a rate that is genuinely unusual compared to other languages.
What Gitleaks does well: Scanning git history and current files for API keys, tokens, credentials, and high-entropy strings. It catches secrets that are already committed — not just future ones. It supports custom regex rules for internal token formats.
Where Gitleaks falls short: It does not find vulnerability patterns in application logic. Its value is entirely in the secrets category.
Best fit: Every JavaScript and TypeScript repo, running on every commit and as a historical scan on the full git log.
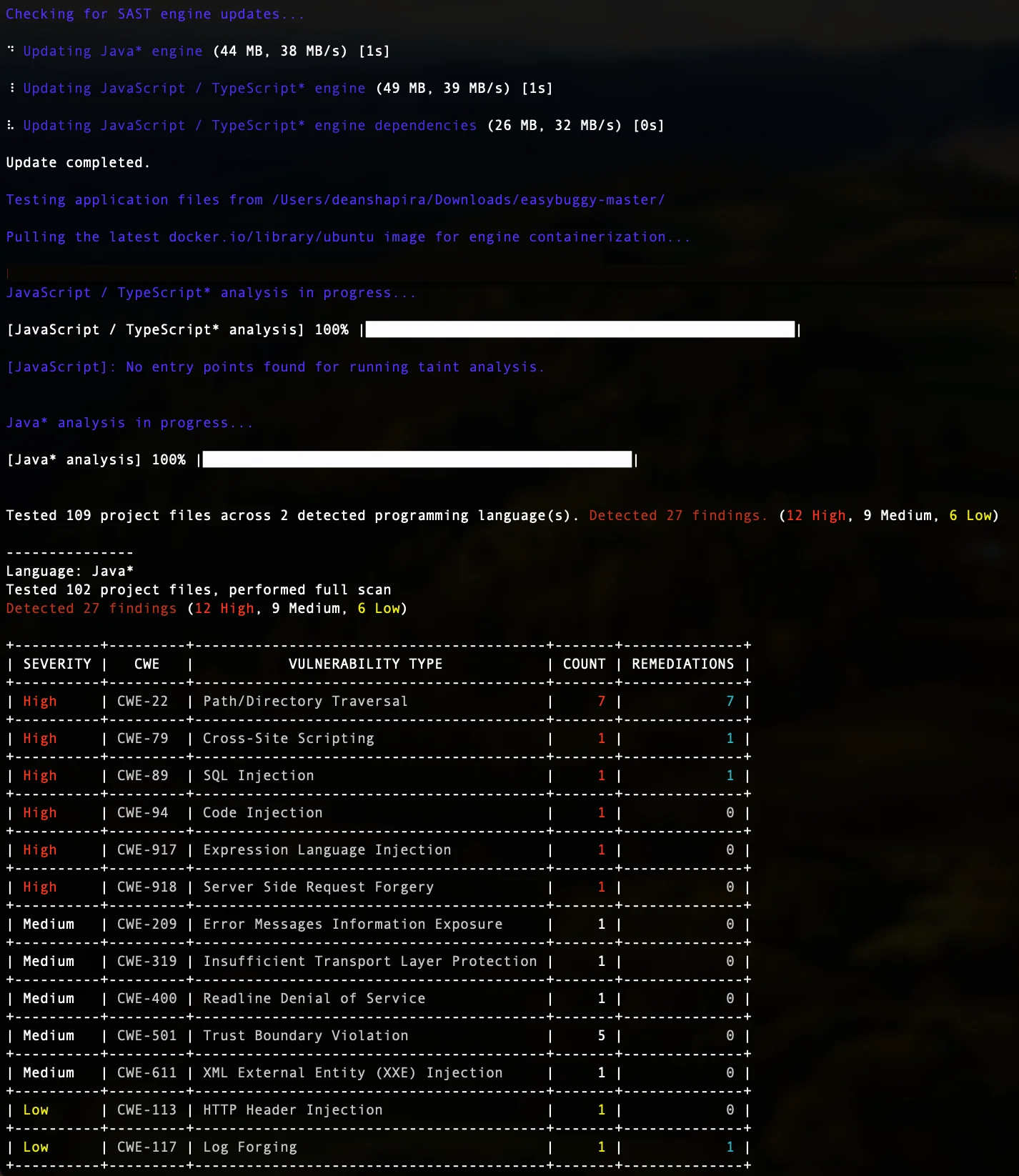
8. Mend SAST
Mend SAST is a commercial SAST platform with JavaScript and TypeScript support covering taint analysis, XSS, injection, and insecure cryptography. Mend is often used by teams already using Mend SCA for dependency scanning who want to consolidate SAST and SCA in one vendor.
What Mend SAST does well: Commercial-grade JavaScript taint analysis with a consistent interface across SAST, SCA, and secrets detection. The platform supports GitHub, GitLab, Bitbucket, and Azure DevOps integration.
Where Mend SAST falls short: Contact-sales pricing and commercial-only product. No free tier for SAST beyond a trial.
Best fit: Organizations using Mend SCA who want unified SAST and SCA coverage from a single vendor without managing multiple tool integrations.
Comparison table
| Tool | Type | JS/TS Depth | Taint Analysis | License | Best For |
|---|---|---|---|---|---|
| Semgrep | SAST (multi-language) | Strong patterns | Limited (per-file) | Open source / Commercial | Custom rules, multi-language repos |
| ESLint + plugins | Linter + basic SAST | Syntactic only | None | Open source | IDE/pre-commit first layer |
| Snyk Code | SAST (commercial) | Deep + frameworks | Cross-file | Commercial (free IDE) | Developer-first taint analysis |
| SonarQube | SAST + quality | Moderate | Paid tiers | Open source / Commercial | Quality + security in one platform |
| CodeQL | SAST (deep) | Very deep + TS types | Cross-project | Free (public) / Commercial | Complex Node.js API taint |
| NodeJSScan | SAST (Node-specific) | Node.js patterns | None | Open source | Node.js secondary scanner |
| Gitleaks | Secret detection | N/A | N/A | Open source | Secrets in JS repos |
| Mend SAST | SAST (commercial) | Deep + frameworks | Cross-file | Commercial | Mend SCA + SAST consolidation |
How to choose for your use case
React frontend only: ESLint with eslint-plugin-security and eslint-plugin-no-unsanitized in the IDE, Semgrep in CI targeting React XSS rules, and Gitleaks on the git history. That is a complete free stack for a frontend repo.
Node.js API service: ESLint security plugins for the dev loop, Semgrep in CI, CodeQL on the main branch via GitHub Actions (free for public repos). Add NodeJSScan as a secondary scanner for Node.js-specific patterns. Snyk Code or SonarQube Developer Edition if the team needs commercial support and deeper taint tracking.
TypeScript full-stack: CodeQL benefits most from TypeScript — it uses the type information to reduce false positives and improve taint tracking. Run CodeQL alongside Semgrep for complementary coverage.
Enterprise team with compliance requirements: Snyk Code or Mend SAST provide audit trails, RBAC, and OWASP/CWE report mappings. See the enterprise SAST tools guide for larger-scale options including Checkmarx and Veracode .
Monorepo with Python + JavaScript: Semgrep as the anchor — it handles both languages in one scanner with a unified rule format.
Open source vs commercial
The free JavaScript SAST stack — ESLint plugins, Semgrep CE, NodeJSScan, Gitleaks, CodeQL (public repos) — covers syntactic vulnerability patterns and basic data flow well. The primary gap versus commercial tools is cross-file inter-procedural taint analysis.
For a Node.js API service where req.body data flows through five middleware layers to a MongoDB query, the free tools will miss the vulnerability unless it is in a pattern-based rule. Snyk Code
and SonarQube
Developer Edition both model that kind of flow explicitly.
CodeQL bridges the gap for projects hosted publicly on GitHub — it provides commercial-depth taint analysis free of charge via GitHub Actions. For private repos, the GitHub Advanced Security cost is the decision point.
For the broader open-source landscape, see the open source SAST tools guide . For SAST vs SCA trade-offs, see SAST vs SCA .