Java remains the backbone of enterprise software - banking systems, government services, large internal platforms - and its mature ecosystem means Java SAST has deeper tooling than almost any other language.
This guide compares 8 SAST tools with strong Java support: SonarQube , SpotBugs , CodeQL , Semgrep , Snyk Code , Checkmarx , Fortify , and Coverity .
Why Java SAST is different
Java’s static type system and mature compiler make it one of the easier languages to analyze statically. Tools can resolve types, trace method calls, and build accurate call graphs. That means Java SAST detection quality is generally higher than for Python or JavaScript at the same tool tier.
The trade-off is framework complexity. A modern Java service sits on Spring Boot, Struts, or Jakarta EE, with dependency injection, annotation-driven routing, and reflection-heavy serialization. A SAST tool that does not model these frameworks will miss the entry points where user input actually enters the application.
The major Java-specific vulnerability patterns SAST tools target:
- Unsafe deserialization (the class of bugs behind Log4Shell and older Apache Commons issues)
- JNDI injection via lookup strings
- SQL injection through JPA and raw JDBC
- XXE in XML parsers
- Spring Expression Language (SpEL) injection
- Struts action injection
- LDAP injection
- Path traversal through servlet request parameters
- Hardcoded secrets in
application.propertiesorapplication.yml
Java also has a longer tail of legacy code than most languages.
SAST tools that run at the bytecode level (SpotBugs, Coverity) handle code where source may not be available or where the source was generated by a build tool. That matters in large enterprises running decades-old code alongside new services.
Key Insight
For Java SAST, framework modeling is the moat. Any scanner can grep for Statement.executeQuery. Only the scanners that know a Spring @RequestParam is a tainted source, a Jakarta EE @Inject field carries request state, and Apache Commons ObjectInputStream is a dangerous sink will find the actual bugs in real Spring Boot code.
Top SAST tools for Java
1. SonarQube
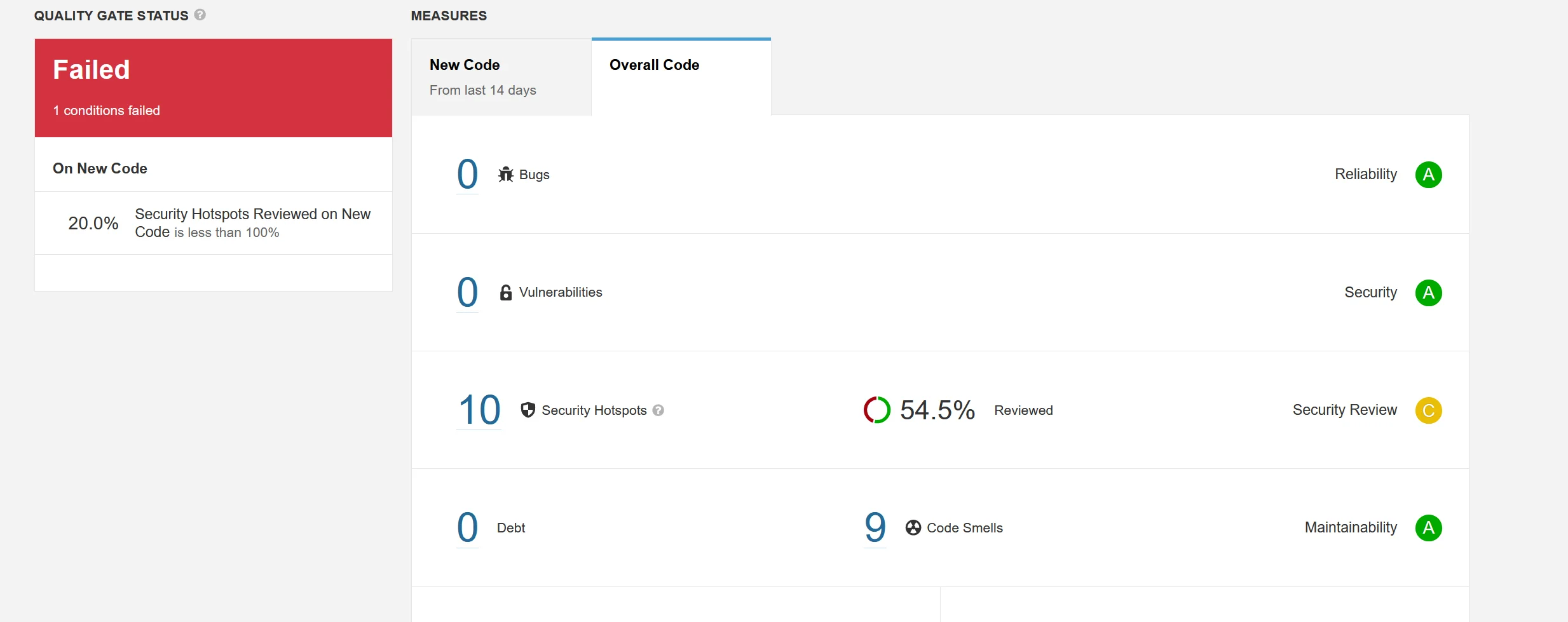
SonarQube is the most widely deployed Java static analysis platform. Its Java rule set covers OWASP Top 10 categories, Spring-specific patterns, servlet vulnerabilities, and a large body of code quality rules that overlap with security concerns (null dereferences, resource leaks, thread safety).
What SonarQube does well: Integration is native with Maven and Gradle via the sonar-scanner plugin. Quality gates block pull requests that introduce new issues. The Community Edition covers pattern-based Java security well and pairs with code coverage and duplication metrics in one dashboard. SonarQube’s Java analyzer understands common frameworks out of the box.
Where SonarQube falls short: Inter-procedural taint analysis - following user input from an HTTP request parameter across method calls to a SQL sink - requires Developer Edition or above. Community Edition misses complex injection patterns that span classes.
Best fit: Java teams that want one platform covering security plus code quality with a low setup cost, and that are willing to pay for Developer Edition when taint coverage becomes a hard requirement.
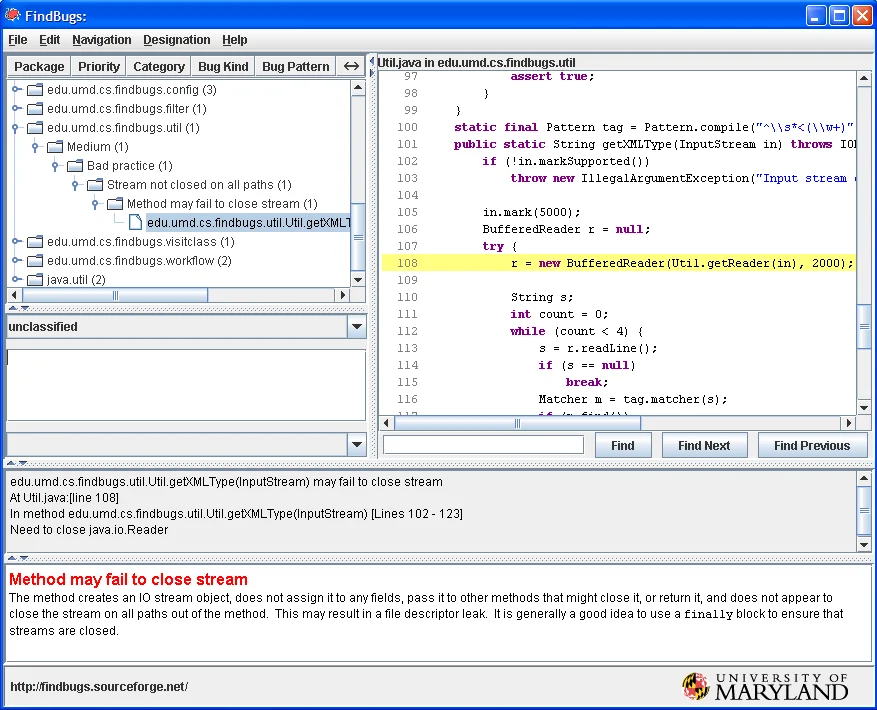
2. SpotBugs
SpotBugs is the actively maintained successor to FindBugs . It analyzes Java bytecode directly, which means it can inspect compiled class files and libraries where source code is not available. The FindSecBugs plugin extends it with 130+ security checks.
What SpotBugs does well: Bytecode analysis catches issues that source-level tools miss, including calls into third-party libraries and generated code. FindSecBugs provides deep Java security coverage: servlet and JSP injection, cryptography misuse, deserialization, JNDI, LDAP, XXE, and more. It is open source (LGPL) and integrates with Maven, Gradle, Ant, and most IDEs.
Where SpotBugs falls short: The UI and integrations feel older than modern SAST platforms. False positives are higher than with commercial tools because SpotBugs errs toward reporting rather than filtering. Results need tuning to be actionable.
Best fit: Any Java project that compiles to class files. SpotBugs with FindSecBugs is the strongest free bytecode-level security scanner for Java and pairs well with SonarQube.
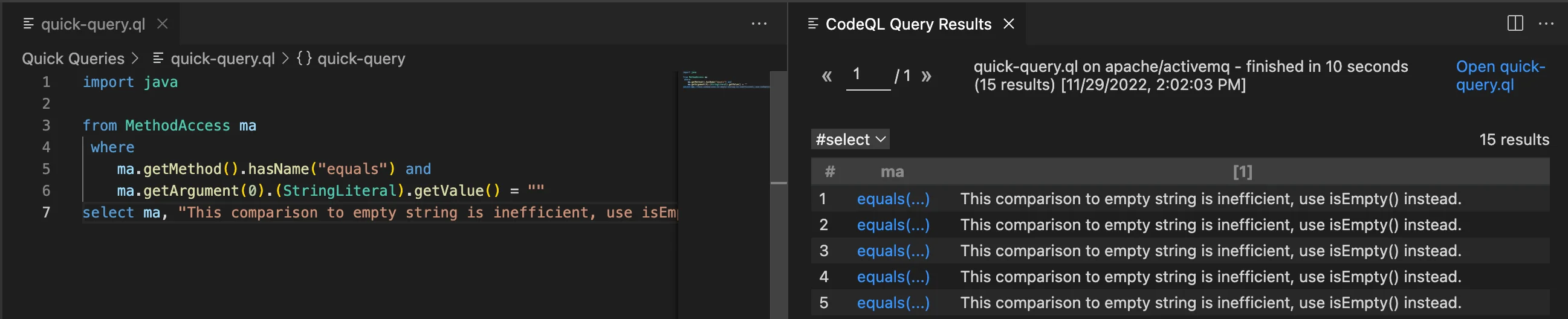
3. CodeQL
CodeQL models Java code as a queryable database and ships a comprehensive library of queries for Java taint tracking . Its Java support includes Spring, Struts, Jakarta EE, JAX-RS, and common ORM frameworks, with data flow tracking that crosses method and class boundaries.
What CodeQL does well: Deep Java inter-procedural data flow analysis that actually understands framework semantics. CodeQL knows that a Spring @RequestParam annotation creates a tainted source, that a Jakarta EE injected @Inject field may carry request state, and that Apache Commons ObjectInputStream is a dangerous sink. Queries for Log4Shell-style JNDI patterns are shipped and maintained by GitHub’s security lab.
Where CodeQL falls short: Analysis time is longer than pattern-based tools - 10 to 30 minutes on medium Java projects is common. Writing custom queries in QL has a learning curve. CodeQL is free for public repositories via GitHub Actions but requires GitHub Advanced Security for private repos.
Best fit: Java services with complex taint flows where detection accuracy is critical. For open-source Java projects, CodeQL via Actions is the best free deep scanner available.
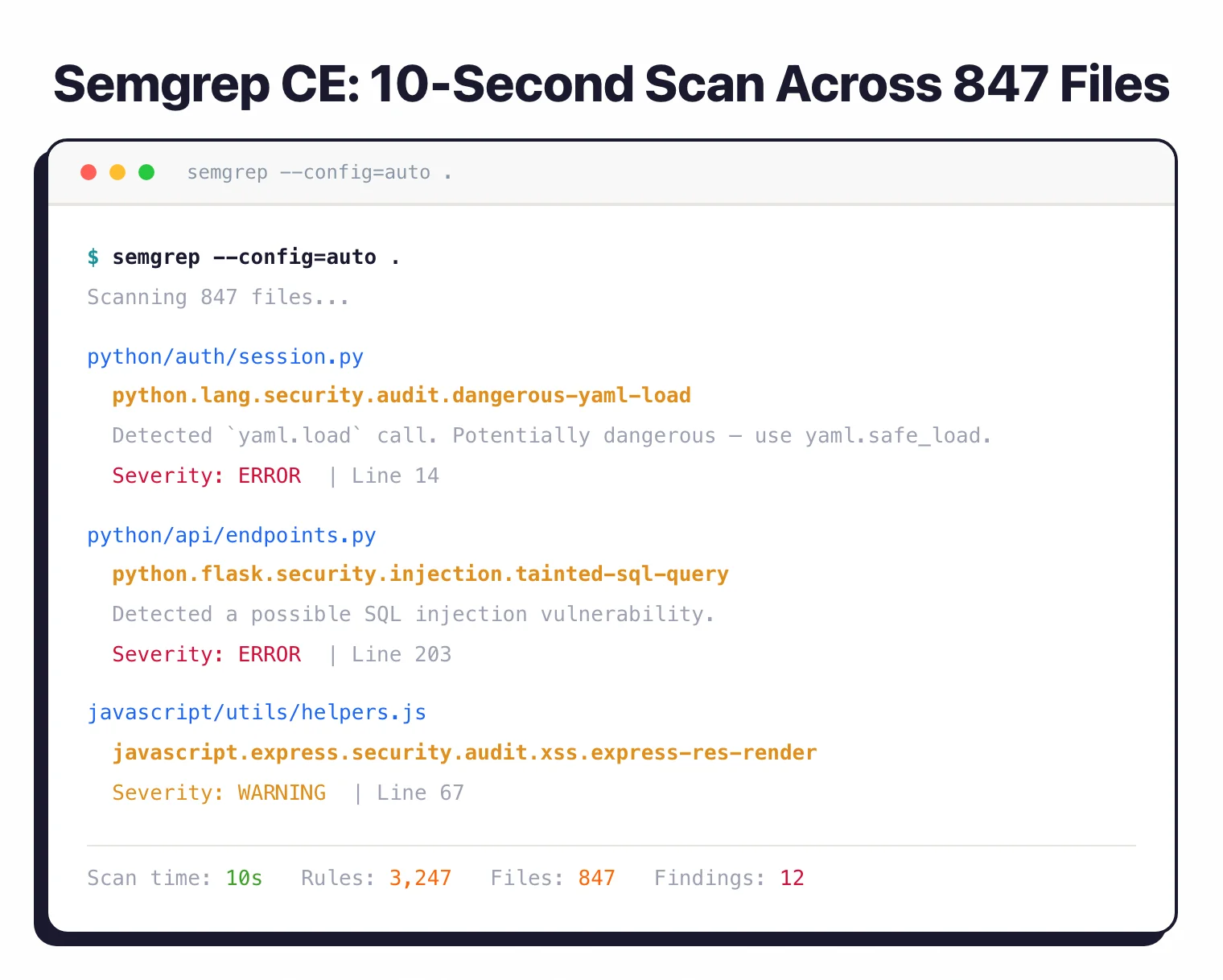
4. Semgrep
Semgrep supports Java through its structural pattern-matching engine. The Semgrep Registry includes Java rulesets for OWASP Top 10, Spring security patterns, Struts, JAX-RS, and common deserialization sinks. Custom rules in YAML make it straightforward to encode rules for proprietary frameworks.
What Semgrep does well: Custom rule authoring is the standout feature. A Java platform team that owns an internal framework can write Semgrep rules against it in minutes. The community registry covers common Java patterns and includes rules equivalent to many FindSecBugs checks. Semgrep’s taint engine tracks tainted values within a file.
Where Semgrep falls short: Deep cross-file taint analysis requires Semgrep Code (the paid platform tier). The community engine is strong for single-file analysis but does not track taint across the codebase the way CodeQL or Snyk Code do.
Best fit: Java platform teams with proprietary frameworks that need custom detection, and multi-language organizations that want a single scanner across Java, Python, and JavaScript.
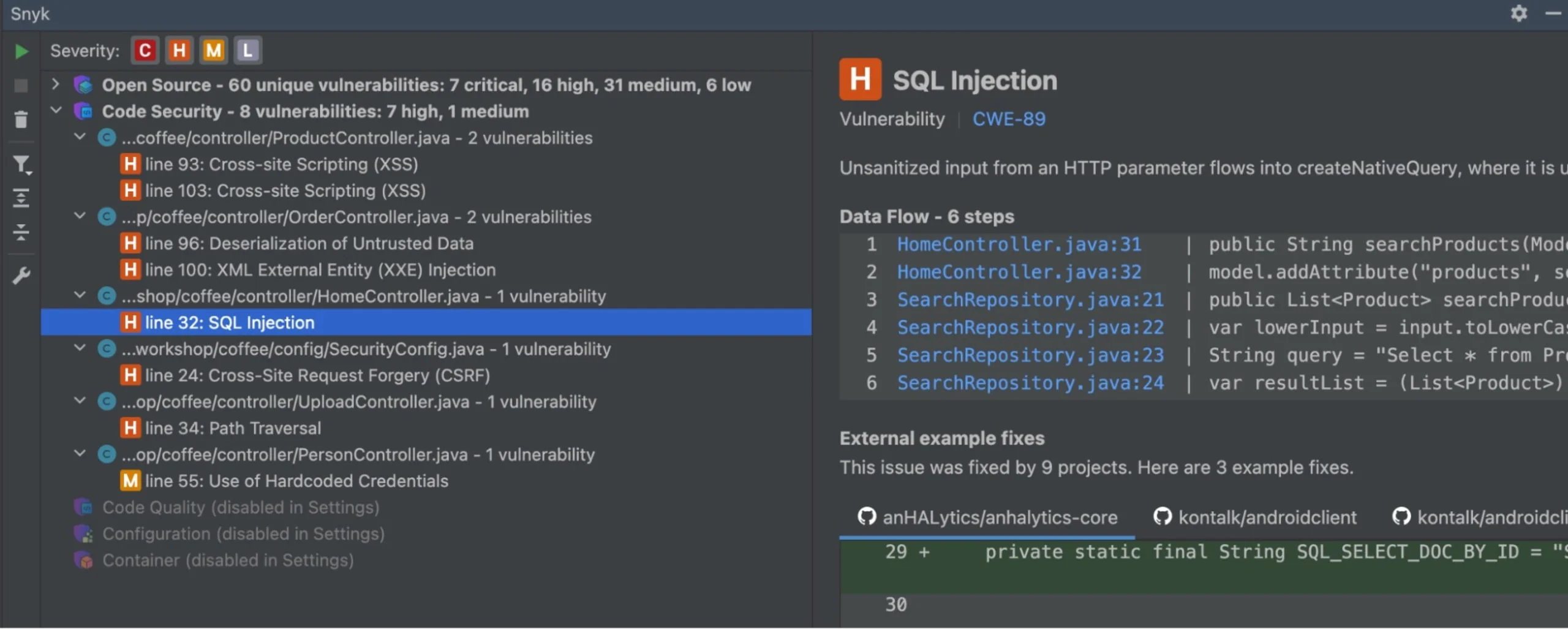
5. Snyk Code
Snyk Code provides commercial Java SAST with real-time IDE feedback and inter-procedural taint analysis . Its engine understands Spring Boot, Struts, JAX-RS, and common ORM patterns, and traces user input across methods and files to dangerous sinks.
What Snyk Code does well: Taint analysis that crosses method and file boundaries with high accuracy. The IDE experience in IntelliJ and VS Code surfaces issues inline as developers type, with fix guidance that includes code suggestions. Results include the data flow path from source to sink, which speeds up triage.
Where Snyk Code falls short: The free tier is limited to the IDE. CI/CD integration with full taint analysis requires a paid plan. Snyk Code is a SaaS tool - source code is sent to Snyk’s cloud for analysis, which matters for some regulated or air-gapped environments.
Best fit: Java development teams that want commercial-quality taint analysis with a developer-first IDE workflow, where cloud-based analysis is acceptable.
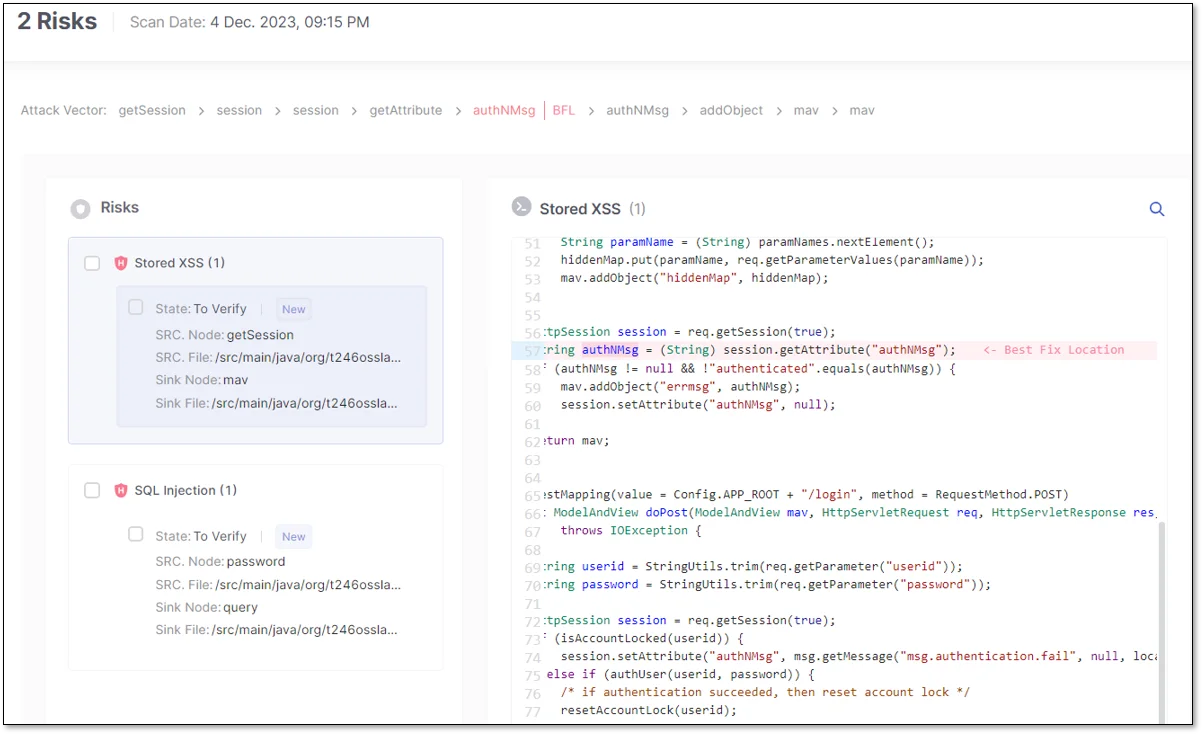
6. Checkmarx
Checkmarx is one of the longest-standing enterprise SAST platforms with strong Java coverage. Its Checkmarx SAST engine supports Spring, Struts, Jakarta EE, and JAX-RS, and its CxQL query language lets security teams write custom queries against the abstract syntax tree.
What Checkmarx does well: CxQL custom queries are the primary advantage for security teams that need tool-level control. Checkmarx’s Java engine includes a comprehensive default ruleset covering injection, deserialization, cryptography, and framework-specific issues. Incremental scanning reduces pipeline time after the initial full scan.
Where Checkmarx falls short: Setup and tuning take time. False positive rates on initial scans are typical of enterprise platforms and require an AppSec team to triage and suppress. Pricing is not publicly listed and requires a sales conversation.
Best fit: Regulated industries (finance, government, healthcare) with dedicated AppSec teams that need customizable query authoring, audit trails, and on-premise deployment options.
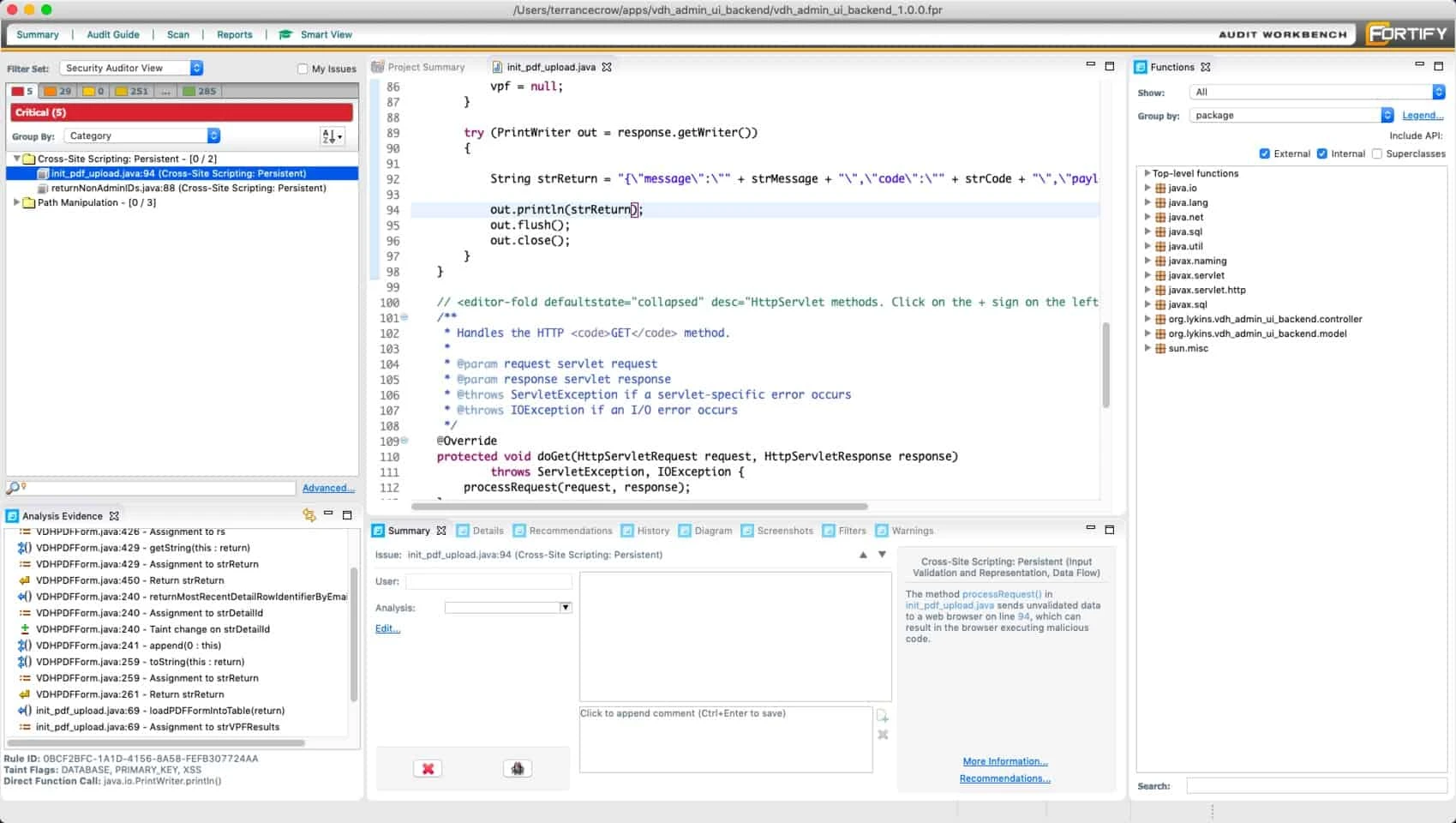
7. Fortify Static Code Analyzer
Fortify Static Code Analyzer (now under OpenText) is the enterprise Java SAST most common in large banks, government contractors, and organizations with legacy codebases. It supports Java alongside COBOL, ABAP, PL/SQL, and other enterprise languages in one engine.
What Fortify does well: Coverage of legacy and mixed-language codebases is Fortify’s signature strength. A bank with Java services calling into COBOL batch jobs can scan the full stack in one tool. Fortify’s Java engine covers Spring, Struts, Jakarta EE, and a long list of enterprise frameworks. Audit workbench features support large AppSec team workflows.
Where Fortify falls short: The user experience reflects its enterprise origins and can feel heavy compared to modern developer-first tools. False positives on default configuration are typical of the enterprise category. Pricing requires direct vendor engagement.
Best fit: Large enterprises with legacy Java codebases and mixed-language requirements, particularly those with compliance or contractual obligations that mandate a named enterprise SAST vendor.
8. Coverity
Coverity (Synopsys, now part of Black Duck) is a defect-density focused SAST platform with strong Java analysis. Its engine is known for low false positive rates on C and C++ and carries a similar philosophy into its Java checks.
What Coverity does well: Accuracy and defect-density reporting. Coverity positions itself as the tool with the lowest false positive rate among enterprise SAST platforms, which makes its results higher signal per finding at the cost of some recall. Its Java coverage includes deserialization, injection, resource leaks, and concurrency issues.
Where Coverity falls short: Framework coverage for modern Java (Spring Boot, microservices patterns) has historically lagged dedicated Java-first tools like Checkmarx. Setup is enterprise-grade and requires a named deployment effort. Pricing is not public.
Best fit: Java shops that already use Coverity for C or C++ analysis and want a single vendor across their stack, or teams that prioritize signal-to-noise ratio over maximum recall.
Comparison table
| Tool | Type | Java Depth | Taint Analysis | License | Best For |
|---|---|---|---|---|---|
| SonarQube | SAST + quality | Strong patterns | Paid tiers only | Open source / Commercial | Quality + security in one platform |
| SpotBugs | SAST (bytecode) | Deep (with FindSecBugs) | Limited | Open source (LGPL) | Bytecode-level Java checks, free |
| CodeQL | SAST (deep analysis) | Very deep | Cross-codebase | Free (public) / Commercial | Deep Spring/Struts/Jakarta EE taint |
| Semgrep | SAST (multi-language) | Strong patterns | Single-file (CE) | Open source / Commercial | Custom rules, multi-language |
| Snyk Code | SAST (commercial) | Deep + frameworks | Cross-file | Commercial (free IDE tier) | Developer-first taint analysis |
| Checkmarx | SAST (enterprise) | Deep + CxQL | Cross-codebase | Commercial | Custom query authoring, compliance |
| Fortify | SAST (enterprise) | Deep + legacy | Cross-codebase | Commercial | Legacy and mixed-language Java |
| Coverity | SAST (enterprise) | Deep, low FP | Cross-codebase | Commercial | Low false positive rate |
How to choose for your use case
Small team or open-source project: Run SonarQube Community plus SpotBugs with FindSecBugs in CI. Add CodeQL via GitHub Actions on the main branch (free for public repos). That covers breadth, bytecode-level security, and deep taint for zero cost.
Growing Java team with Spring Boot services: Same free stack plus Semgrep for custom rules against any internal framework. This gives you 80% of the coverage of a commercial tool with no license spend. Graduate to Snyk Code or SonarQube Developer when cross-file taint becomes a consistent gap.
Regulated enterprise (finance, healthcare, government): Checkmarx or Fortify for the audit trail, on-premise deployment, and compliance features. Checkmarx wins when custom query authoring matters. Fortify wins when you have legacy code or mixed-language requirements. See the enterprise SAST tools guide for the broader landscape.
Legacy Java alongside COBOL, ABAP, or older stacks: Fortify is the most common choice because it covers the full enterprise language list in one engine.
Teams already invested in GitHub Actions: CodeQL integrates natively and is free for public repos. For private repos on GitHub Advanced Security, CodeQL gives you deep Java taint analysis without a separate SAST vendor.
Monorepo with Java plus Python or JavaScript: Semgrep or Snyk Code keeps the scanner count down. Semgrep for custom-rule-heavy teams. Snyk Code for developer-first taint analysis across languages.
Open source vs commercial
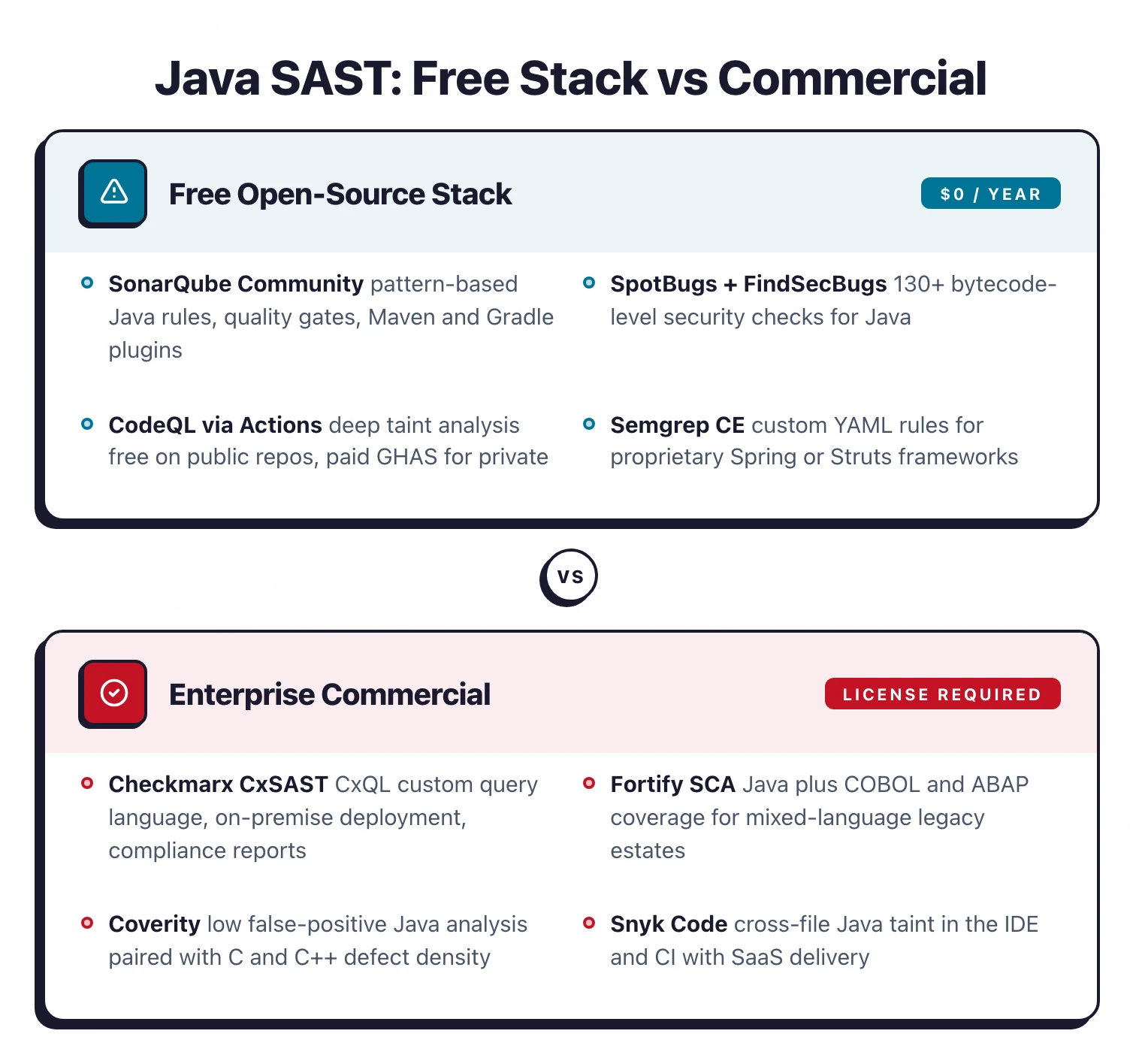
The free Java SAST stack - SonarQube Community, SpotBugs with FindSecBugs, CodeQL (public repos), Semgrep CE - is stronger than the free stack for almost any other language. For many Java projects, the combination covers pattern-based issues, bytecode-level security, and cross-codebase taint analysis without a commercial license.
The gap versus commercial tools is primarily in three areas. First, inter-procedural taint analysis on private repositories at CI speed - CodeQL’s quality is free only for public repos, so private-repo teams either pay for GitHub Advanced Security or switch to Snyk Code, Checkmarx, or Fortify. Second, custom query authoring for proprietary frameworks - Checkmarx CxQL and Semgrep (commercial tier) are the main options. Third, audit trails, RBAC, and on-premise deployment required by regulated industries.
Coverity and Fortify stand out when the Java codebase intersects with other languages - C, C++, COBOL, ABAP - where single-vendor coverage matters more than best-of-breed Java analysis.
For a more detailed look at the free and open-source options, see the open source SAST tools guide . For buying considerations around commercial tools, see SAST vs SCA: which do you need first . For sibling language guides, see SAST tools for Python and SAST tools for JavaScript .