Go has become a default choice for cloud infrastructure, Kubernetes operators, and network services - and its static typing and explicit error handling make it easier to analyze than dynamic languages.
This guide compares 7 SAST and adjacent static analysis tools with strong Go support: gosec , Semgrep , CodeQL , Snyk Code , SonarQube , staticcheck, and govulncheck.
Why Go SAST is different
Go’s design gives SAST tools several advantages over dynamic languages. Explicit error returns, a static type system, strict package boundaries, and limited runtime reflection mean that pattern-based scanners produce higher-signal results in Go than they do in Python or JavaScript.
The Go-specific concerns that SAST tools target are narrower and more predictable than in frameworks-heavy languages. The most common categories:
- SSRF through
http.Clientcalls without URL validation - SQL injection via string concatenation with
database/sqlinstead of parameterized queries - Hardcoded cryptographic keys and credentials
- Insecure uses of the
unsafepackage that bypass Go’s memory safety - TLS misconfiguration (skipping certificate verification, weak cipher suites)
- Command injection through
os/execwith user-controlled arguments - Path traversal in
os.Openandfilepath.Joincalls
Concurrency is a second layer. Go’s goroutines make race conditions and data races possible in ways that sequential-language SAST tools do not address. Goroutine leaks - where spawned goroutines never exit because a channel is never closed - can lead to denial-of-service conditions.
The Go standard toolchain includes go vet
and the race detector
(go test -race), and static analysis tools like staticcheck catch some of the same issues at build time.
Go’s dependency model is tighter than most languages. go.mod and go.sum pin versions and checksums, and the Go vulnerability database
(golang.org/x/vuln) is actively maintained by the Go team. This is why govulncheck fits naturally alongside a SAST scanner - it covers the CVE side while SAST covers application code.
Key Insight
Go is the first mainstream language where the official toolchain ships a reachability-aware vulnerability scanner. That reframes the buying question: instead of "which SCA tool ranks dependencies?", Go teams can start with govulncheck and only add commercial SCA if they need features it doesn't cover — SBOM generation, license policy, air-gapped scanning.
Top SAST tools for Go
1. gosec
gosec is the Go security scanner most teams reach for first. It is maintained under the securego project, released under Apache 2.0, and ships with more than 30 Go-specific rules targeting injection, insecure crypto, hardcoded credentials, unsafe package usage, and TLS misconfiguration.
What gosec does well: Deep Go AST awareness. gosec understands Go idioms - goroutines, channels, the unsafe package, standard library crypto - and targets them with dedicated rules.
Integration is straightforward: run as a binary, as a GitHub Action, or through the gosec Go module. Results are fast and high signal.
Where gosec falls short: No inter-procedural taint analysis. gosec detects patterns at the function level and does not trace user input across function boundaries to a dangerous sink. Coverage of web framework patterns (Gin, Echo, Chi) is narrower than what CodeQL or Semgrep offer.
Best fit: Any Go project. gosec is the baseline security check for Go code and belongs in every CI pipeline, especially as the first gate before more expensive analysis.
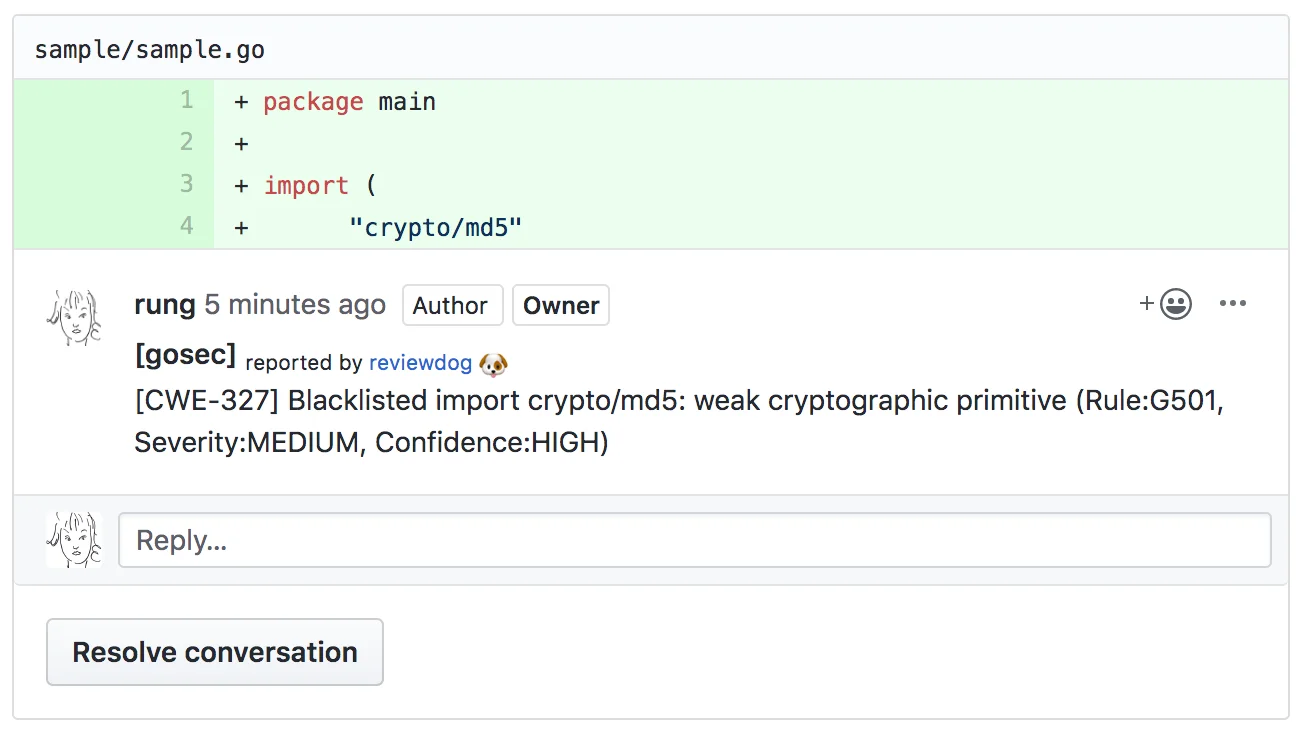
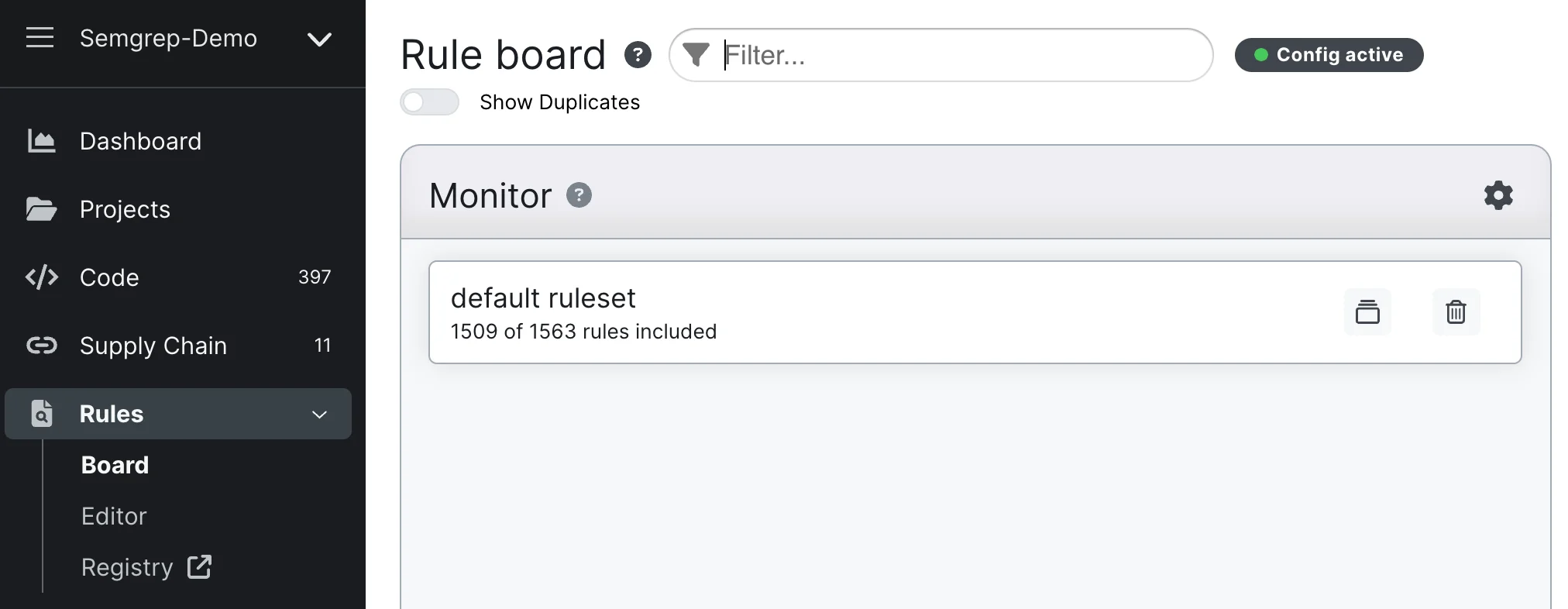
2. Semgrep
Semgrep has had general availability Go support for several years and includes a Go ruleset in the community registry covering OWASP categories, the Gin and Echo web frameworks, database/sql injection, SSRF, and insecure cryptography.
What Semgrep does well: Custom rules in YAML are the standout feature for Go teams with internal frameworks or conventions.
The community registry includes rules equivalent to many gosec checks, and Semgrep’s multi-language support lets one scanner cover Go alongside any other language in the monorepo. Semgrep’s taint engine tracks tainted values within a file.
Where Semgrep falls short: Cross-file inter-procedural taint analysis requires Semgrep Code (the paid tier). The community engine stops at file boundaries for complex Go taint flows. For pure Go projects where gosec already covers the baseline, Semgrep’s added value is primarily custom rule authoring and multi-language coverage.
Best fit: Go teams with proprietary internal frameworks that need custom detection, and multi-language organizations that want a single scanner across Go, Python, and JavaScript.
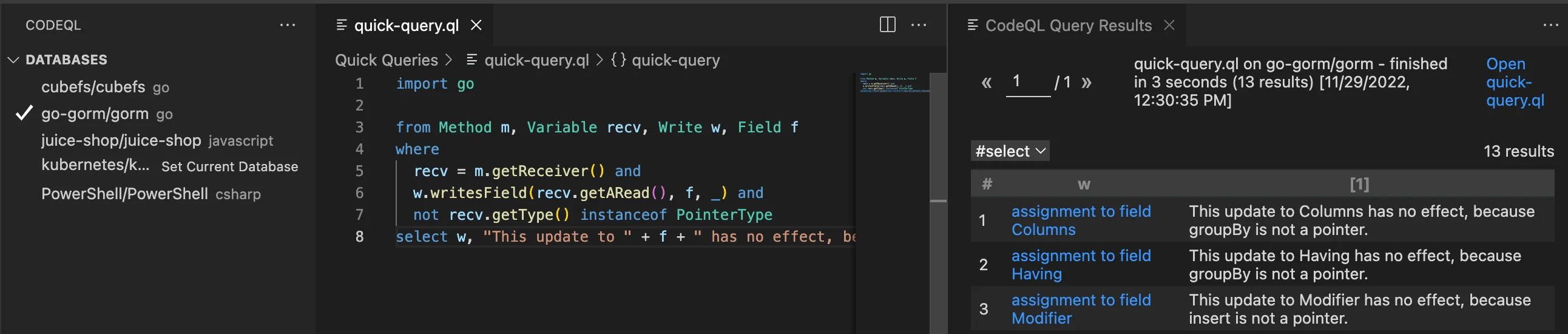
3. CodeQL
CodeQL reached general availability for Go in 2020 and models Go code as a queryable database . Its Go queries cover SSRF, SQL injection, path traversal, command injection, insecure deserialization, and TLS misconfiguration, with taint analysis that follows user input across function and package boundaries.
What CodeQL does well: Deep Go inter-procedural data flow analysis. CodeQL understands Go’s net/http handler patterns, database/sql taint sinks, and common web framework entry points. Results include the full data flow path from source to sink, which makes triage faster and more accurate than pattern-based results.
Where CodeQL falls short: Analysis runs slower than gosec - 5 to 15 minutes is typical for a medium-sized Go codebase. Writing custom Go queries in QL is a learning curve for teams used to YAML rules.
CodeQL is free for public repositories via GitHub Actions but requires GitHub Advanced Security for private repos.
Best fit: Go web services and APIs where complex taint flows through HTTP handlers, middleware, and database calls justify deeper analysis. For open-source Go projects, CodeQL via Actions is the strongest free deep scanner.
go vet and the race detector (go test -race) precisely for this class of issue. Run them alongside gosec and staticcheck, not instead of.4. Snyk Code
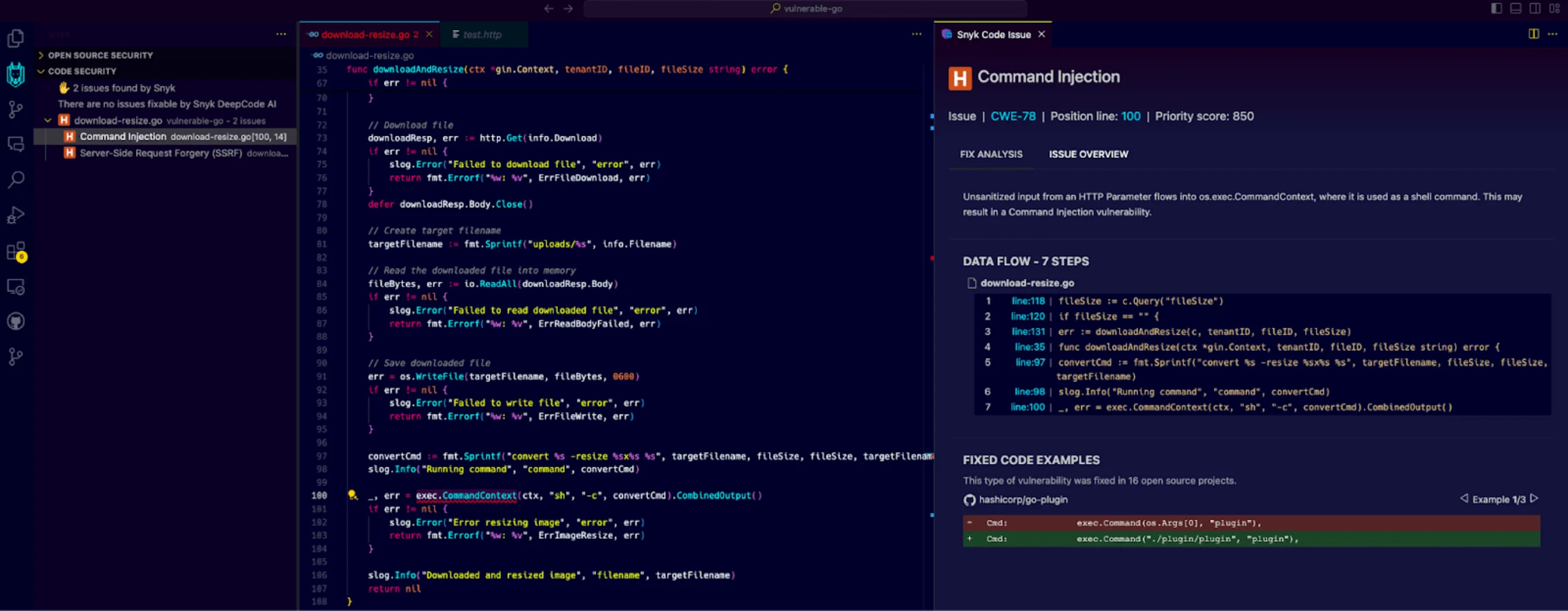
Snyk Code provides commercial Go SAST with real-time IDE feedback and cross-file taint analysis. Its Go engine understands the standard net/http package, common web frameworks, and database/sql patterns.
What Snyk Code does well: Inter-procedural taint analysis across files and packages with IDE integration. Snyk Code surfaces issues inline in VS Code, GoLand, and JetBrains IDEs as developers type, with fix guidance that includes example code. Results include data flow paths from source to sink.
Where Snyk Code falls short: The free tier is limited to the IDE - CI integration with full taint analysis requires a paid plan. Snyk Code is a SaaS tool, which sends source to Snyk’s infrastructure.
Pricing for Go-heavy teams depends on team size and repository count and is not publicly listed.
Best fit: Development teams that want commercial-quality Go taint analysis in a developer-first workflow and are comfortable with cloud-based source analysis.
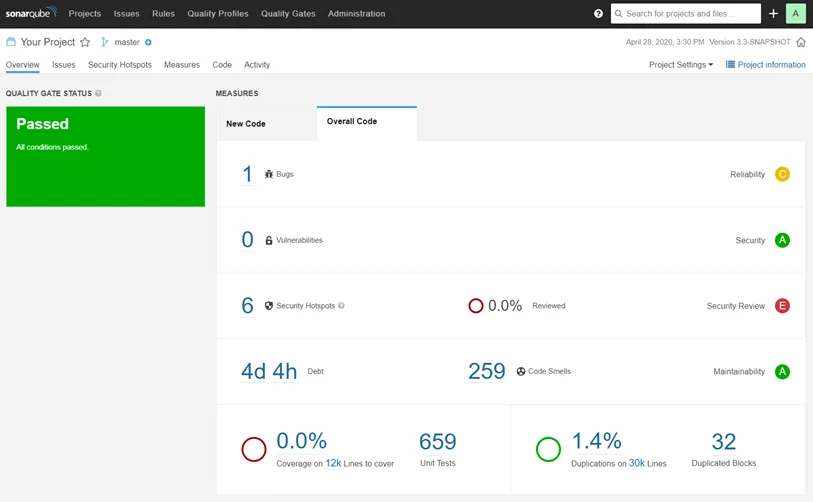
5. SonarQube
SonarQube supports Go in the Community Edition with a rule set covering OWASP Top 10 categories, insecure cryptography, hardcoded credentials, and common Go mistakes that have security implications. SonarQube combines its Go security checks with code quality rules for complexity, duplication, and maintainability.
What SonarQube does well: One platform for Go security plus code quality with pull request quality gates. SonarQube’s Go analyzer runs as part of the standard SonarScanner flow and integrates with GitHub, GitLab, Azure DevOps, and Bitbucket. Quality gates block merges on new issues.
Where SonarQube falls short: Taint analysis for Go requires Developer Edition or higher. The Community Edition catches pattern-based issues but misses complex data flow vulnerabilities. Go coverage has historically lagged SonarQube’s Java support.
Best fit: Teams that already run SonarQube for other languages and want Go in the same dashboard. Teams standardizing on Developer Edition for taint analysis across their stack.
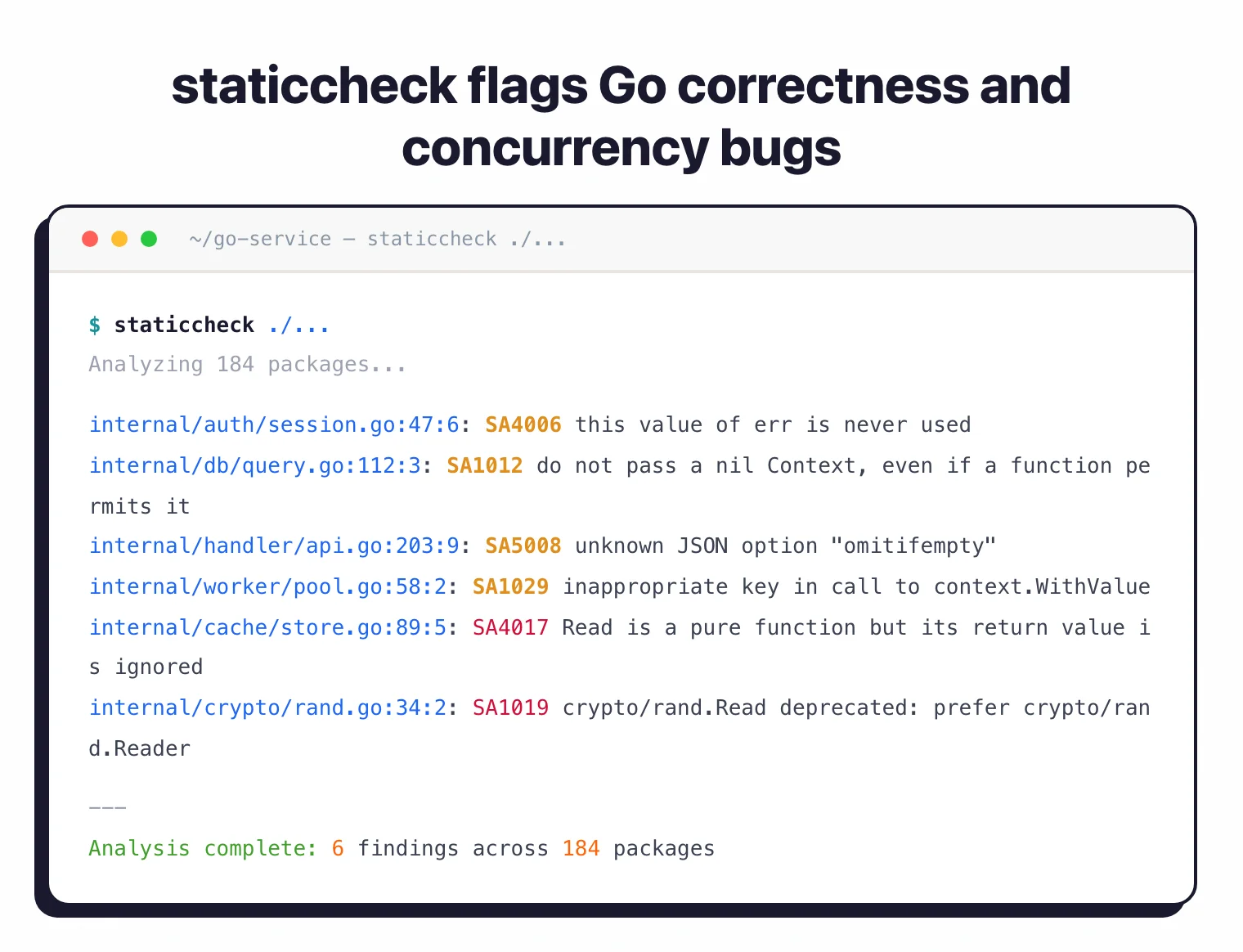
6. staticcheck
staticcheck is Dominik Honnef’s Go static analyzer, widely considered the best-in-class correctness checker for Go. It is not a SAST tool in the traditional sense - its focus is on bug detection, code simplification, and idiomatic Go - but many of its checks catch issues that become security-relevant at runtime.
What staticcheck does well: Deep understanding of Go semantics. staticcheck catches incorrect error handling, nil dereferences, goroutine leaks, misuse of the context package, and concurrency mistakes.
Several of its checks (SA1000 family) flag patterns that can lead to denial-of-service or authentication bypass in production. It is fast, accurate, and low false-positive.
Where staticcheck falls short: No security ruleset. staticcheck does not detect injection, SSRF, or insecure crypto. Its role in a Go security stack is to catch the class of bugs that become vulnerabilities at runtime, not to replace a dedicated security scanner.
Best fit: Every Go project that does not already run it. Pair staticcheck with gosec for a complete coverage of correctness bugs plus security patterns.
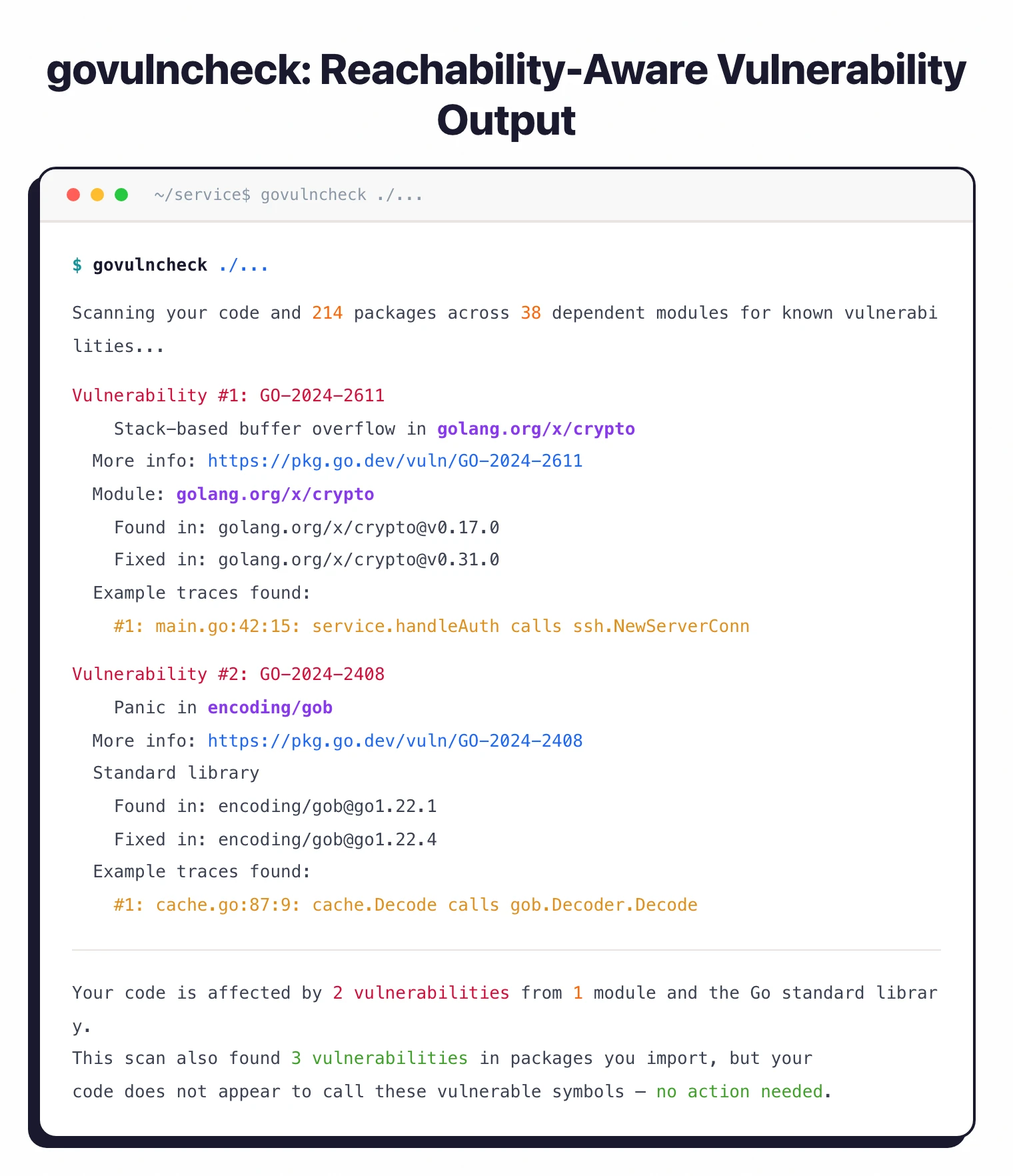
7. govulncheck
govulncheck is Google’s vulnerability scanner for Go, built by the Go team and released in 2022 . It checks your Go module dependencies and standard library against the Go vulnerability database and reports only vulnerabilities that are reachable from your code.
What govulncheck does well: Reachability analysis cuts the noise that plagues generic SCA tools. If a dependency has a CVE but your code never calls the affected function, govulncheck does not report it.
The tool is maintained by the Go team, which means coverage of new Go standard library vulnerabilities is immediate. It integrates with go build workflows and runs in seconds on most projects.
Where govulncheck falls short: It is a vulnerability scanner, not a full SAST tool. It does not detect custom code issues - insecure crypto, SSRF patterns, hardcoded credentials - that gosec and Semgrep cover. It also only reports vulnerabilities in the Go ecosystem, not in C libraries linked via cgo.
Best fit: Every Go project. govulncheck belongs alongside gosec in CI as the dependency-vulnerability layer that pairs with application-code SAST.
Comparison table
| Tool | Type | Go Depth | Taint Analysis | License | Best For |
|---|---|---|---|---|---|
| gosec | SAST (Go-specific) | Deep AST | None | Apache 2.0 | First Go security check in CI |
| Semgrep | SAST (multi-language) | Strong patterns | Limited (single-file) | Open source / Commercial | Custom rules, multi-language |
| CodeQL | SAST (deep analysis) | Very deep | Cross-codebase | Free (public) / Commercial | Deep taint for Go web services |
| Snyk Code | SAST (commercial) | Deep + frameworks | Cross-file | Commercial (free IDE tier) | Developer-first taint analysis |
| SonarQube | SAST + quality | Moderate | Paid tiers only | Open source / Commercial | Quality + security combined |
| staticcheck | Correctness analyzer | Very deep (correctness) | None | Open source (MIT) | Bug detection, idiomatic Go |
| govulncheck | Vulnerability scanner | Reachability-aware | N/A | Open source | Dependency CVEs with reachability |
How to choose for your use case
Open-source Go project: Run gosec, staticcheck, and govulncheck on every commit. Add CodeQL via GitHub Actions on the main branch (free for public repos). That covers code security, correctness, dependency vulnerabilities, and deep taint analysis for zero cost.
Growing Go team with a web service: Same free stack plus Semgrep for custom rules against internal frameworks or conventions. The combination is hard to beat on pattern-based and reachability analysis. Graduate to Snyk Code when cross-file taint at CI speed becomes a consistent gap.
Kubernetes operators, CLI tools, infrastructure code: gosec plus staticcheck plus govulncheck. Taint analysis matters less here than correctness and dependency hygiene - most security bugs in infrastructure Go are about credentials, TLS configuration, and dependency CVEs rather than complex injection flows.
Go microservices handling untrusted HTTP input: Add CodeQL on the main branch and consider Snyk Code for cross-file taint analysis. These services are where SSRF, SQL injection, and path traversal actually appear, and pattern-based scanners miss the cross-function flows.
Teams already on SonarQube: Run it for Go alongside your other languages. Budget for Developer Edition if you need taint analysis. Keep gosec and govulncheck in parallel - SonarQube’s Go coverage is solid but not as Go-native as gosec.
Enterprise with compliance requirements: Snyk Code or SonarQube Developer Edition give you the audit trails, RBAC, and reporting that compliance teams expect. See the enterprise SAST tools guide for the broader landscape.
go vet ./..., staticcheck ./..., gosec ./..., govulncheck ./.... It runs in under a minute on most services, covers correctness, security, and CVEs, and fails the build on any new issue. Add CodeQL via GitHub Actions on main for the deeper taint pass. Budget for Snyk Code only when cross-file taint in every PR becomes a consistent gap.Open source vs commercial
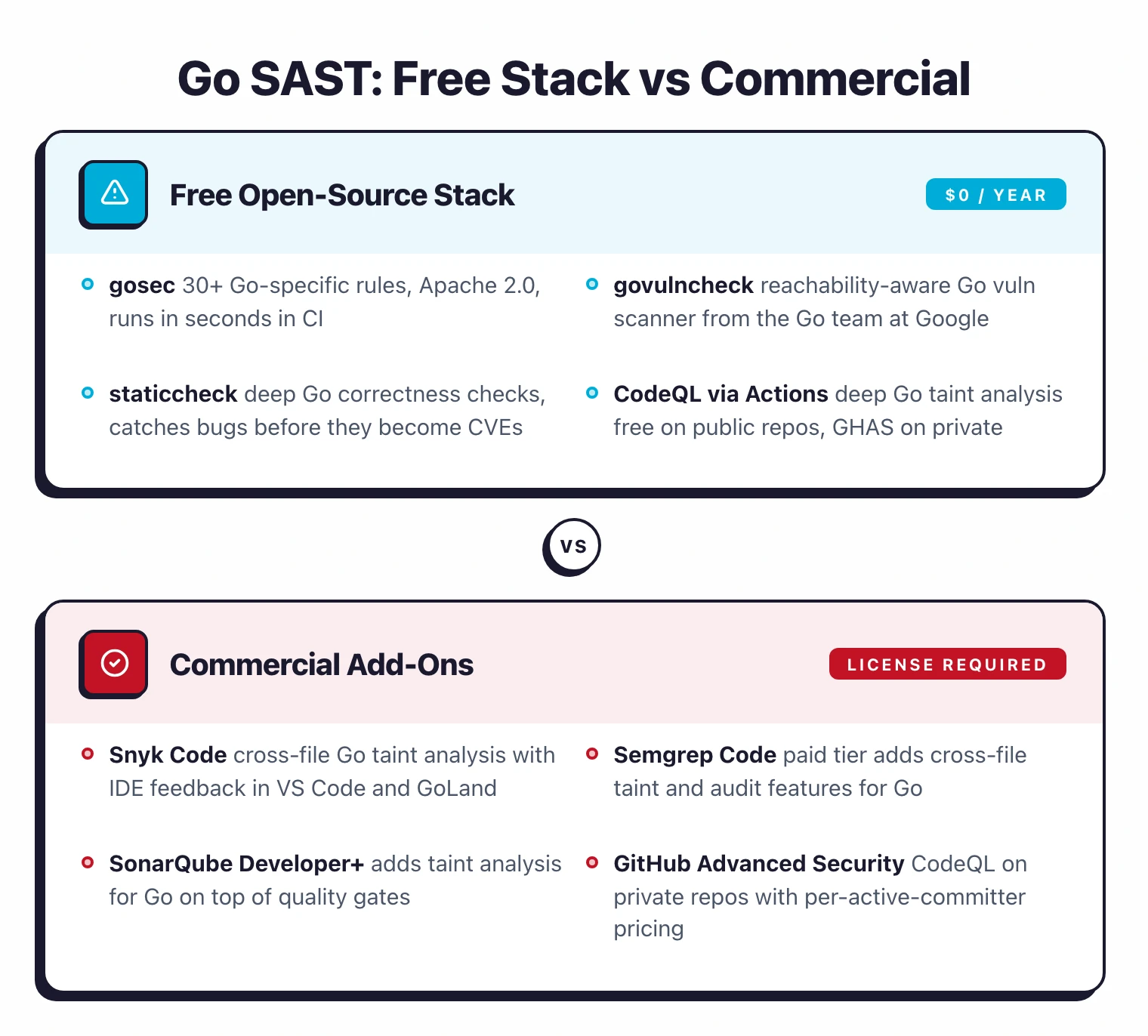
The free Go static analysis stack is one of the strongest across languages. gosec, staticcheck, govulncheck, Semgrep CE, and CodeQL (public repos) together cover code security, correctness, dependency vulnerabilities, and deep taint analysis.
For many Go projects - especially open-source projects, CLI tools, and infrastructure code - this free stack is the complete answer.
The gap versus commercial tools is concentrated in two areas.
First, inter-procedural taint analysis on private repositories at CI speed - CodeQL is free only for public repos, so private-repo teams either pay for GitHub Advanced Security or switch to Snyk Code or SonarQube Developer Edition.
Second, the audit trail, RBAC, and on-premise deployment features required by regulated industries.
Snyk Code is the most common commercial choice for Go teams that want developer-first taint analysis without the weight of an enterprise platform. SonarQube Developer Edition fits teams that already use SonarQube for other languages.
For a more detailed look at the free and open-source options, see the open source SAST tools guide . For buying considerations around commercial tools, see SAST vs SCA: which do you need first .
For sibling language guides, see SAST tools for Python , SAST tools for JavaScript , and SAST tools for Java .