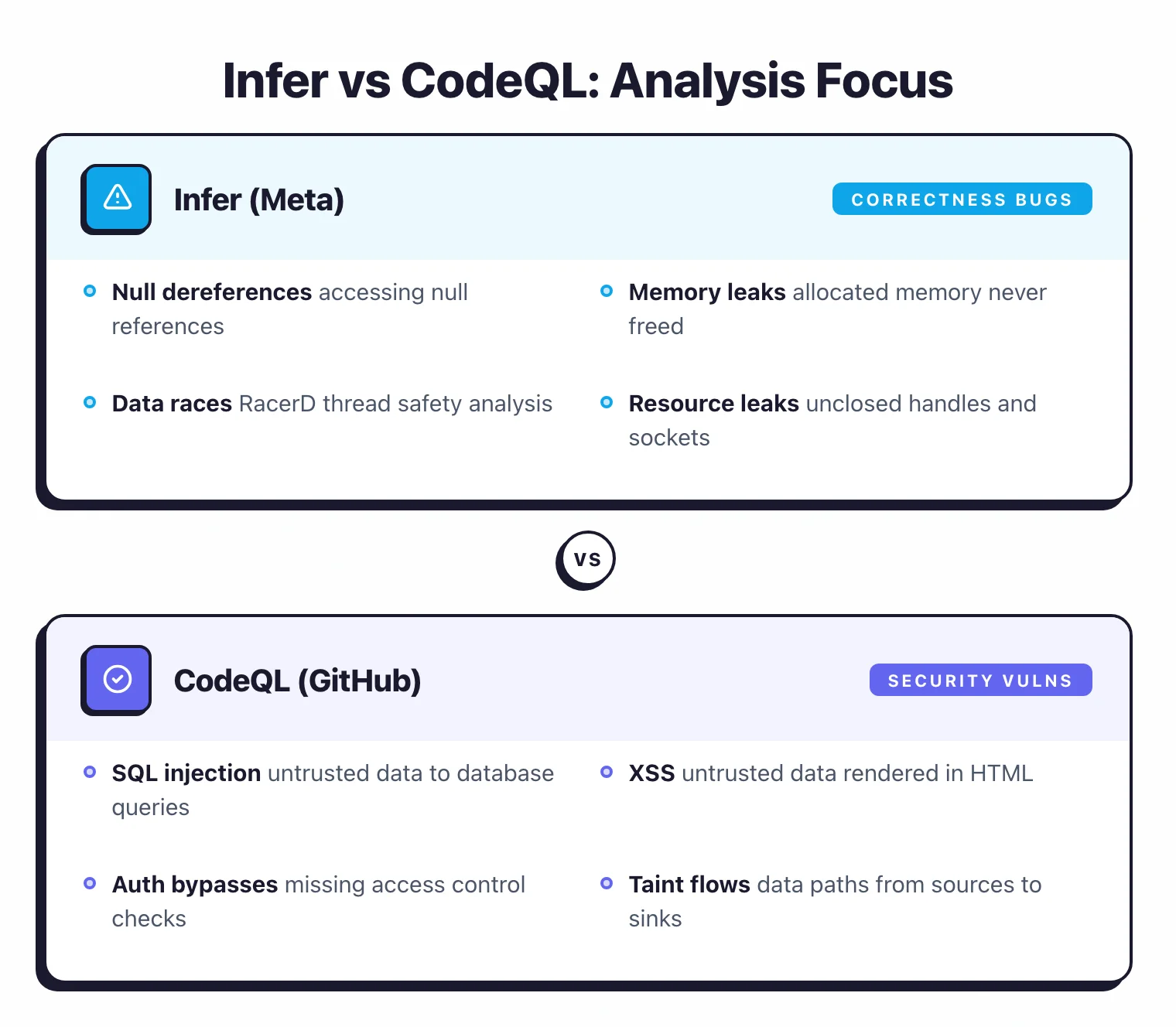
- Infer uses separation logic to find memory safety and concurrency bugs (null dereferences, leaks, data races); CodeQL uses semantic database queries to find security vulnerabilities (injections, auth bypasses, taint flows).
- CodeQL supports 12 languages including Java, Python, JavaScript, Go, Ruby, and Rust; Infer supports 6 languages focused on compiled/mobile: Java, C, C++, Objective-C, Erlang, and Hack.
- Both are free for open-source projects. CodeQL requires GitHub Code Security ($30/committer/month) for private repos; Infer is MIT-licensed with no restrictions.
- Infer's differential analysis reports only new issues per code change — purpose-built for CI. CodeQL's incremental analysis (2025) speeds up PR scans by 5-40% across supported languages.
- The tools complement each other well: Infer catches correctness bugs that CodeQL misses (memory leaks, races), while CodeQL catches security patterns that Infer does not target (SQLi, XSS, auth flaws).
Which Is Better: Infer or CodeQL?
The main difference between Infer and CodeQL is what they detect: Infer finds memory safety and concurrency bugs using separation logic, while CodeQL finds security vulnerabilities using semantic database queries.
Infer is Meta’s open-source analyzer built on separation logic — a formal verification framework for reasoning about memory and concurrency. Infer excels at finding null pointer dereferences, memory leaks, resource leaks, use-after-free bugs, and data races.
Its differential analysis mode reports only new issues introduced by a code change, making it practical for CI workflows at any scale. Meta runs Infer on every code change across Facebook, Instagram, WhatsApp, and Messenger.
CodeQL is GitHub’s semantic analysis engine that compiles source code into a queryable relational database. CodeQL excels at finding security vulnerabilities — SQL injection, cross-site scripting, command injection, authentication bypasses, and other patterns where untrusted data flows to dangerous operations.
It supports 12 languages and integrates natively into GitHub pull requests.
These tools are not competitors — they complement each other. Infer is better for catching correctness bugs (null dereferences, memory leaks, data races), while CodeQL is better for catching security vulnerabilities (SQL injection, XSS, auth bypasses).
For Java or C/C++ projects, running both gives you coverage across both bug categories.
What Are the Key Differences?
| Feature | Infer | CodeQL |
|---|---|---|
| Developer | Meta (Facebook) | GitHub (Microsoft) |
| License | MIT (fully open-source) | Free for OSS; GitHub Code Security for private repos |
| GitHub Stars | 15,500+ | N/A (GitHub-maintained) |
| Languages | Java, C, C++, Objective-C, Erlang, Hack | C, C++, C#, Go, Java, Kotlin, JS, TS, Python, Ruby, Swift, Rust |
| Analysis Foundation | Separation logic + bi-abduction | Semantic database + QL query language |
| Primary Focus | Memory safety, null safety, concurrency | Security vulnerabilities, taint flows |
| Bug Types | Null deref, memory/resource leaks, data races, use-after-free | SQLi, XSS, command injection, auth bypasses, taint flows |
| Custom Rules | Topl (state machine DSL) | QL (SQL-like query language) |
| Taint Analysis | Configurable (Pulse engine) | Built-in with source/sink/sanitizer model |
| Differential/Incremental | Yes (reports only new issues per diff) | Yes (incremental analysis since 2025, 5-40% faster) |
| Requires Compilation | Yes (hooks into build system) | Yes for compiled languages; extraction for interpreted |
| CI Integration | Any CI (CLI-based) | GitHub Actions (primary), CLI for others |
| Pull Request Integration | Manual (JSON/SARIF output) | Native GitHub PR annotations |
| Web Dashboard | No | GitHub Security tab |
| IDE Support | No official IDE plugin | VS Code (CodeQL extension) |
| Concurrency Analysis | Yes (RacerD for thread safety) | Limited |
Infer vs CodeQL: How Do They Compare?
Analysis Philosophy
The core difference between Infer and CodeQL is how they understand code and what they look for.
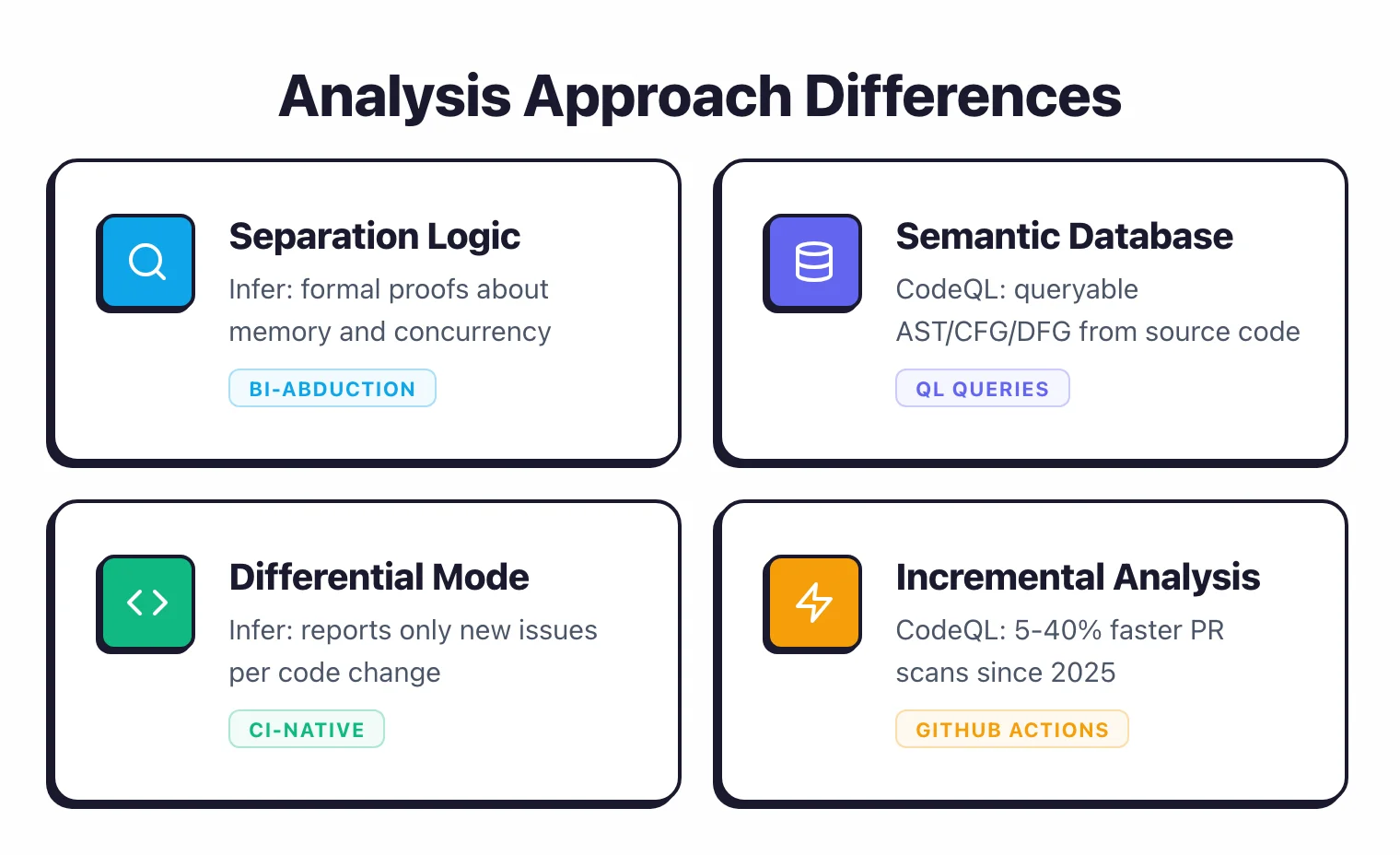
Infer is rooted in formal verification. Its core engine uses separation logic — a mathematical framework for reasoning about programs that manipulate heap memory.
The bi-abduction technique automatically discovers function pre-conditions and post-conditions without developer annotations. This lets Infer prove (or disprove) properties about memory safety and resource management across function boundaries.
When Infer analyzes a function, it does not need to see the whole program. It infers what the function assumes about its inputs and what it guarantees about its outputs, then composes these summaries across the call graph.
This compositional approach is what makes Infer scale to millions of lines of code at Meta.
CodeQL takes a database-driven approach. It compiles source code into a relational database that captures the full semantic structure: abstract syntax trees, control flow graphs, data flow graphs, type hierarchies, and call graphs.
Security researchers write queries in the QL language to search this database for vulnerability patterns.
A CodeQL query might say: “find all paths where data from an HTTP request parameter reaches a SQL query without passing through a parameterized query or escaping function.” The database contains enough structural information to trace these paths across files and functions.
Infer is better at answering questions like “will this pointer ever be null when dereferenced?” while CodeQL is better at answering “can user input reach this database query unsanitized?” This fundamental difference in analysis approach explains why they catch different bug categories.
Bug Detection Focus
Infer’s Pulse engine detects:
- Null pointer dereferences — accessing a null reference in Java, C, C++, or Objective-C
- Memory leaks — allocated memory that is never freed (C/C++/Objective-C)
- Resource leaks — unclosed file handles, database connections, network sockets
- Use-after-free — accessing memory after deallocation
- Uninitialized values — reading variables before assignment
- Data races — via RacerD, detecting unsynchronized access to shared mutable state across threads
- Unnecessary copies — C++ objects copied when a reference would suffice
- Configurable taint flows — user-defined source-sink tracking via the Pulse engine
CodeQL’s query packs detect:
- SQL injection — untrusted data reaching database queries
- Cross-site scripting (XSS) — untrusted data rendered in HTML output
- Command injection — untrusted data passed to shell commands
- Path traversal — untrusted data used in file system operations
- Authentication and authorization flaws — missing access checks, insecure session handling
- Insecure deserialization — untrusted data passed to deserialization functions
- SSRF — untrusted data used in server-side HTTP requests
- Cryptographic weaknesses — weak algorithms, hardcoded secrets
The overlap between these two lists is minimal. Infer finds correctness bugs that cause crashes, memory corruption, and undefined behavior, while CodeQL finds security vulnerabilities that attackers can exploit.
For Java and C/C++ projects, running Infer and CodeQL together covers both categories — correctness and security — that no single tool addresses fully on its own.
Language Support
CodeQL supports far more languages: 12 in total (C, C++, C#, Go, Java, Kotlin, JavaScript, TypeScript, Python, Ruby, Swift, and Rust).
Each language has a dedicated extractor that builds the semantic database, and the standard query packs include security rules tuned for each language’s idioms.
Infer supports 6 languages: Java, C, C++, Objective-C, Erlang, and Hack. The focus is on compiled and mobile languages where memory safety and concurrency issues are most critical.
Infer does not support JavaScript, Python, Go, Ruby, or other interpreted languages where memory management is handled by the runtime.

For teams working in Java or C/C++, both tools are applicable and complementary. For teams working in Python, JavaScript, Go, Ruby, or C#, CodeQL is the only option of the two.
CI/CD Integration and Developer Workflow
Infer was designed for CI from the start. Its differential analysis mode compares the current analysis results against a previous baseline and reports only regressions — new issues introduced by the current code change.
At Meta, every diff submitted for code review triggers an Infer run that comments only on new findings. Developers get focused feedback without being buried in pre-existing issues.
The workflow is build-system-native: infer run -- ./gradlew build hooks into Gradle, Maven, make, clang, or Xcode. Results are saved as JSON and SARIF, which can be uploaded to any code review system.
CodeQL’s CI story centers on GitHub. The standard setup is a GitHub Actions workflow that runs CodeQL on push and pull request events, with results appearing as inline annotations in pull requests and in the GitHub Security tab.
Since late 2025, CodeQL supports incremental analysis across all languages, speeding up PR scans by 5-40% by only re-analyzing new or changed code.
For teams on GitHub, CodeQL’s integration requires almost no setup beyond enabling the workflow. For teams on GitLab, Bitbucket, or other platforms, the CodeQL CLI works but you lose the native PR annotation and security dashboard features.
Infer is platform-agnostic. It runs the same way regardless of where your code is hosted.
Custom Rules and Extensibility
CodeQL’s QL language is its extensibility mechanism. Security engineers write queries that describe vulnerability patterns using a SQL-like syntax with object-oriented extensions. The language is expressive enough to model complex multi-step vulnerabilities, but it has a learning curve — expect a few days to a week of study before writing useful custom queries.
The VS Code CodeQL extension provides autocompletion, inline documentation, and query testing. GitHub also hosts a community of security researchers who share queries.
Infer’s extensibility comes through the Topl checker — an experimental framework where you define state machines representing temporal properties over memory objects. This is more specialized than CodeQL’s general-purpose query language. For most teams, Infer’s built-in checkers cover the relevant bug categories without needing custom rules.
Infer’s Pulse engine also supports configurable taint tracking: you define sources, sinks, and sanitizers in a configuration file. This is less flexible than CodeQL’s QL queries but sufficient for common data flow patterns.
Cost and Licensing
Infer is fully open-source under the MIT license. There are no restrictions on usage — commercial, private, or otherwise. There is no paid tier or commercial edition.
CodeQL is free for public repositories on GitHub and for academic research. For private repositories, it requires GitHub Code Security, which costs $30 per active committer per month.
Since April 2025, GitHub unbundled the former GHAS bundle into two standalone products: GitHub Secret Protection ($19/committer/month) and GitHub Code Security ($30/committer/month), both available to GitHub Team plan customers without requiring Enterprise.
For open-source projects, both Infer and CodeQL are free. For private codebases, Infer remains free under MIT with no restrictions, while CodeQL requires a GitHub Code Security subscription at $30 per active committer per month.
Performance and Scalability
Infer’s compositional analysis is designed to scale. Because it analyzes each function independently and caches summaries, it can handle codebases with millions of lines of code.
The differential mode further limits analysis to changed files and their dependents, keeping CI times manageable even on very large projects.
CodeQL requires building a database before running queries. For compiled languages (Java, C++, C#), this means a full compilation, while for interpreted languages (Python, JavaScript), extraction is faster.
Database creation ranges from minutes for small projects to 30+ minutes for large codebases, and query execution time adds on top.
Since 2025, CodeQL’s incremental analysis has reduced PR scan times by 5-40% across languages by only re-analyzing changed code during the evaluation step. This helps, but CodeQL still requires more time and memory than Infer’s incremental approach for large Java or C++ projects.
When Should You Choose Infer?
Choose Infer if:
- Your primary concern is memory safety — null dereferences, memory leaks, resource leaks, and use-after-free bugs
- You need concurrency analysis — RacerD catches data races and thread safety violations that most SAST tools miss
- Your codebase is Java, C, C++, or Objective-C (especially mobile apps for Android or iOS)
- Differential analysis that reports only new issues per code change is important for your CI workflow
- You need a fully open-source tool with no licensing restrictions on private codebases
- You work at scale and need compositional analysis that handles millions of lines of code efficiently
When Should You Choose CodeQL?
Choose CodeQL if:
- Your primary concern is security vulnerabilities — SQL injection, XSS, command injection, auth bypasses, and taint flows
- Your codebase uses languages Infer does not support — Python, JavaScript, TypeScript, Go, Ruby, C#, Kotlin, Swift, or Rust
- Your repositories are on GitHub and you want native pull request integration with security alerts
- You need a flexible query language to write custom security rules specific to your organization
- Deep data flow and taint tracking across your full codebase is a priority
- Free SAST for open-source repositories is a deciding factor
For Java and C/C++ projects, the strongest approach is running both tools. Infer finds the correctness bugs — null dereferences, memory leaks, and data races — that CodeQL’s security-focused queries do not target.
CodeQL finds the security vulnerabilities — injection flaws, authentication issues, and taint paths — that Infer’s memory-safety focus does not cover. Together, they provide coverage across both bug categories.
For the full list of static analysis options, see the SAST tools comparison on AppSec Santa.
Frequently Asked Questions
What is the main difference between Infer and CodeQL?
Is Infer better than CodeQL for finding memory bugs?
Can I use both Infer and CodeQL together?
Is CodeQL free to use?
Does Infer support JavaScript or Python?

Founder, AppSec Santa
Years in application security. Reviews and compares 210 AppSec tools across 11 categories to help teams pick the right solution. More about me →
