Gitleaks Alternatives
Thinking of switching from Gitleaks? Compare top competitors including TruffleHog, GitGuardian, detect-secrets, Bearer, and Aikido for secrets detection across git history and live repositories.
- Gitleaks is fast and free, covering 150+ secret types with a simple TOML config, but it finds secrets — it does not verify them. TruffleHog adds active verification to filter false positives.
- TruffleHog scans S3 buckets, Jira, Confluence, GitHub, GitLab, and 800+ credential types with live API verification so you know which findings are actually valid.
- GitGuardian covers 550+ secret types and offers real-time push protection alongside historical scanning, with a ggshield pre-commit hook that mirrors the Gitleaks workflow.
- detect-secrets from Yelp uses a baseline file to track intentional secrets and block only net-new ones — useful for codebases that already contain legacy secrets you cannot remove immediately.
- Bearer adds a data-flow lens to secret scanning, identifying not just exposed credentials but where sensitive data (PII, tokens) flows through your codebase.
The best Gitleaks alternatives in 2026 are TruffleHog, GitGuardian, and detect-secrets — each adding verification, centralized monitoring, or richer data-flow analysis that Gitleaks does not provide.
Why Look for Gitleaks Alternatives?
Gitleaks is one of the most widely used open-source secret scanners available. It is fast, configurable via TOML, and covers 150+ secret types out of the box. You can drop it into any pre-commit hook or CI pipeline in minutes.
For a tool that costs nothing and requires no external service, it solves the core problem effectively.
The limitation that teams hit first is verification. Gitleaks finds strings that match secret patterns. It does not confirm whether those strings are still valid credentials that would actually authenticate against an API.
In a large repository with years of git history, that gap produces a significant volume of false positives — expired tokens, test credentials, placeholder strings. Engineers learn to tune them out, which creates the same problem as having no scanner.
The second limitation is scope. Gitleaks is a git repository scanner. If your secrets surface in CI/CD logs, cloud storage, Jira tickets, or Slack messages, Gitleaks is not looking there.
GitHub Secret Scanning, GitGuardian, and TruffleHog each extend coverage beyond the repository itself. For organizations where engineering context spreads across multiple systems, that broader coverage matters.
Configuration management is a third friction point. Gitleaks uses a custom TOML format for allowlists and custom rules. Adding patterns for internal secret formats or tuning noisy rules requires editing this config manually.
Tools like detect-secrets use a baseline file approach — scan once, bless the known findings, then only alert on changes — which suits teams inheriting a codebase with pre-existing secrets they cannot immediately rotate.
Top Gitleaks Alternatives
1. TruffleHog
TruffleHog is the most direct upgrade from Gitleaks for teams that need verification. It is open-source under AGPL-3.0 and available as a commercial SaaS through Trufflehog Enterprise.
The defining feature is active verification . When TruffleHog finds a credential that matches a pattern, it sends a probe to the relevant API to confirm whether the credential is still valid.
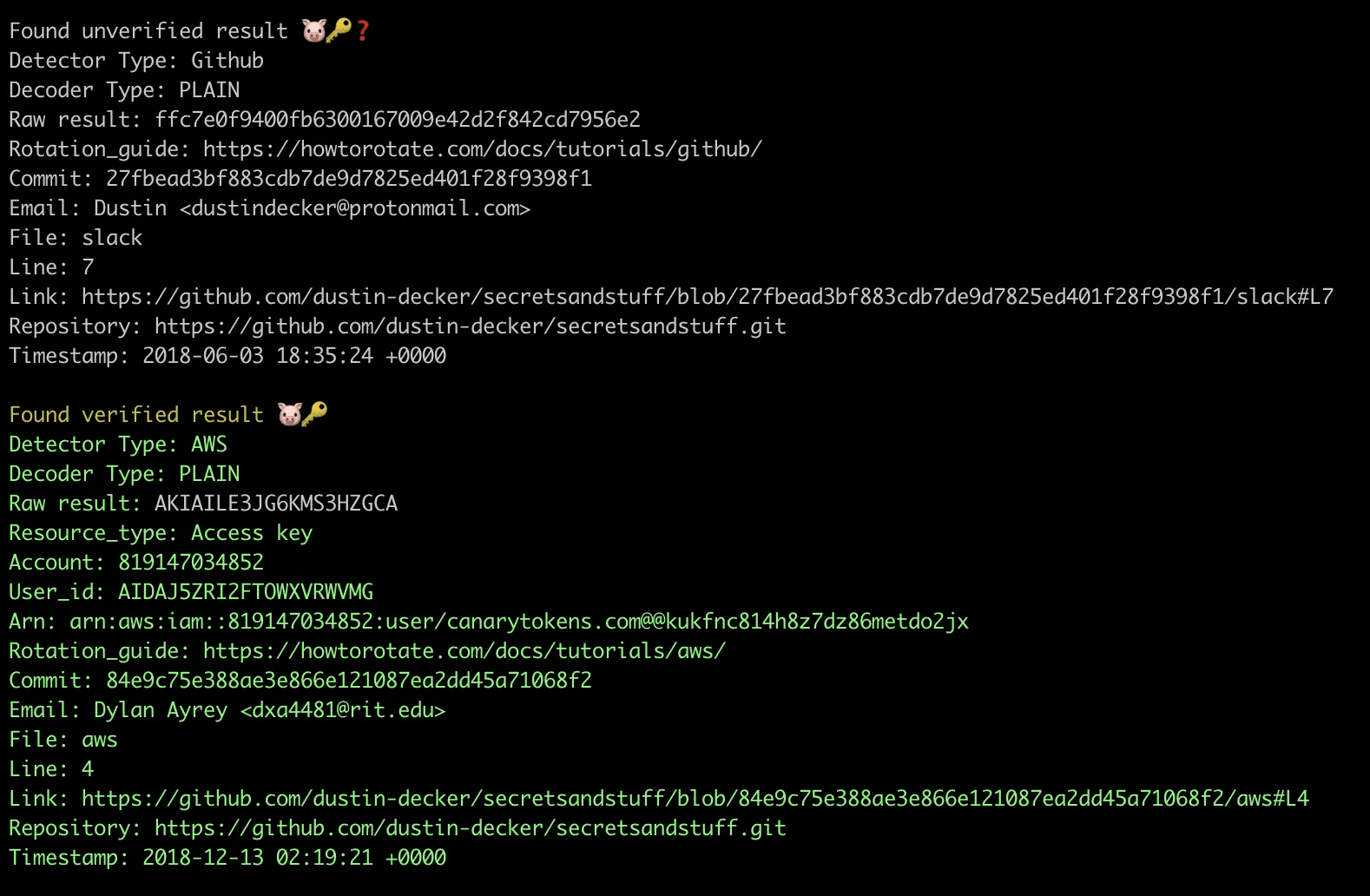
This means your alert queue contains only live secrets that could cause an actual incident — not expired tokens or test strings that have rotated long ago.
TruffleHog covers 800+ credential types versus Gitleaks’ 150+. It scans GitHub, GitLab, S3 buckets, Jira, Confluence, and Slack in addition to git history, giving you broader coverage across the surfaces where secrets tend to leak.
The tradeoff is speed. API verification adds latency compared to Gitleaks’ pure pattern-matching approach. In CI pipelines scanning large repositories, this can be noticeable.
Best for: Teams that need verified findings and broader source coverage beyond git repositories. License: Open-source (AGPL-3.0) Key difference: Active verification against 800+ credential APIs eliminates false positives. Multi-surface scanning beyond git history.
2. GitGuardian
GitGuardian operates as a SaaS platform that monitors pushes in real time across your organization’s repositories. Where Gitleaks is a tool you run, GitGuardian is a service that watches your code.
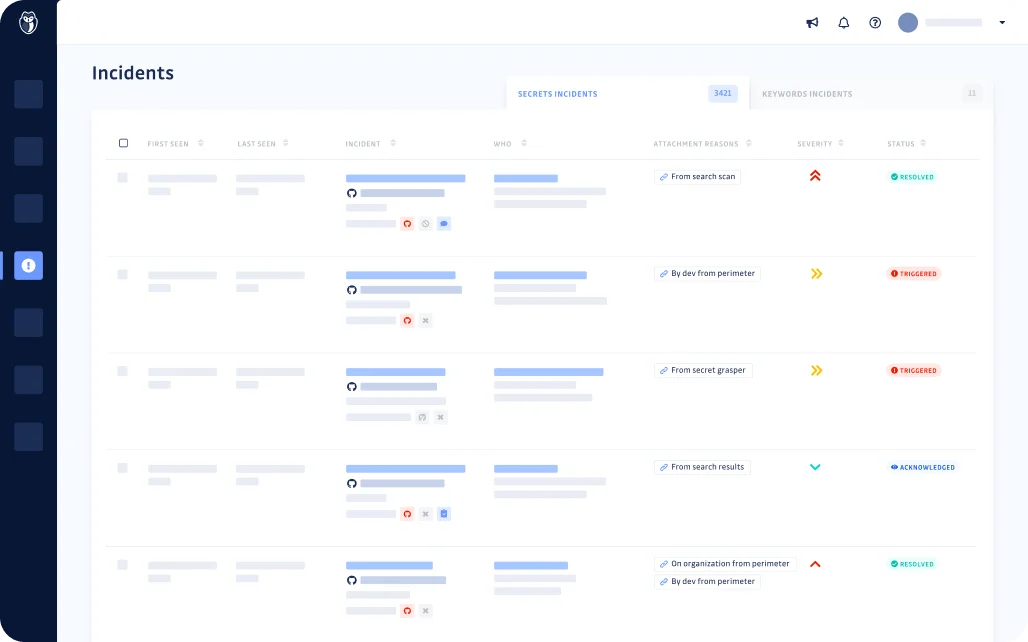
It supports 550+ secret types and provides push protection that can block commits before they merge. The ggshield CLI mirrors the Gitleaks pre-commit hook experience, so the developer workflow feels familiar.
The platform adds centralized incident management that Gitleaks lacks entirely. When a secret is found, GitGuardian creates an incident record, tracks remediation status, assigns it to the responsible developer, and monitors whether the secret has been rotated or revoked.
For security teams managing hundreds of repositories, this workflow context is the difference between a scanner and a program.
GitGuardian includes a free tier for individual developers and small teams. Larger organizations move to paid plans for features like SAML SSO, audit logs, and extended monitoring.
Compared to the gitleaks-vs-trufflehog trade-off , GitGuardian occupies a different position: it is designed for security programs, not individual developer workflows.
Best for: Security teams that need centralized incident management across many repositories. License: Commercial (free tier available) Key difference: Real-time push monitoring with incident management workflow. 550+ secret types with developer attribution and remediation tracking.
3. detect-secrets
detect-secrets from Yelp takes a different philosophical approach to the problem. Rather than scanning to find all secrets and expecting every finding to be actionable, it creates a baseline file of known secrets on first scan.

Future scans only alert on findings that are not in the baseline — net-new secrets that appeared after the baseline was committed.
This design is practical for codebases that already contain legacy secrets you know about but cannot immediately rotate. Gitleaks would report them on every scan, creating noise. detect-secrets tracks them as accepted and stays quiet until something new appears.
The tool integrates with pre-commit and supports custom plugins for detecting internal credential formats. The baseline file is a JSON file committed to the repository, making it easy to audit and review in pull requests.
What detect-secrets does not do is verify credentials, scan git history deeply, or provide a centralized management dashboard. It is a local development tool.
For teams migrating a legacy codebase toward secrets hygiene over time, the baseline approach makes the transition manageable.
Best for: Teams with legacy codebases that need incremental secrets hygiene without overwhelming noise. License: Open-source (Apache 2.0) Key difference: Baseline-diff approach — alerts only on new secrets, not pre-existing ones. Practical for codebases with known legacy credentials.
4. Bearer
Bearer approaches secret scanning as part of a broader data security analysis. Its primary strength is data-flow analysis: it traces where sensitive data — including credentials, PII, and session tokens — travels through your application code.
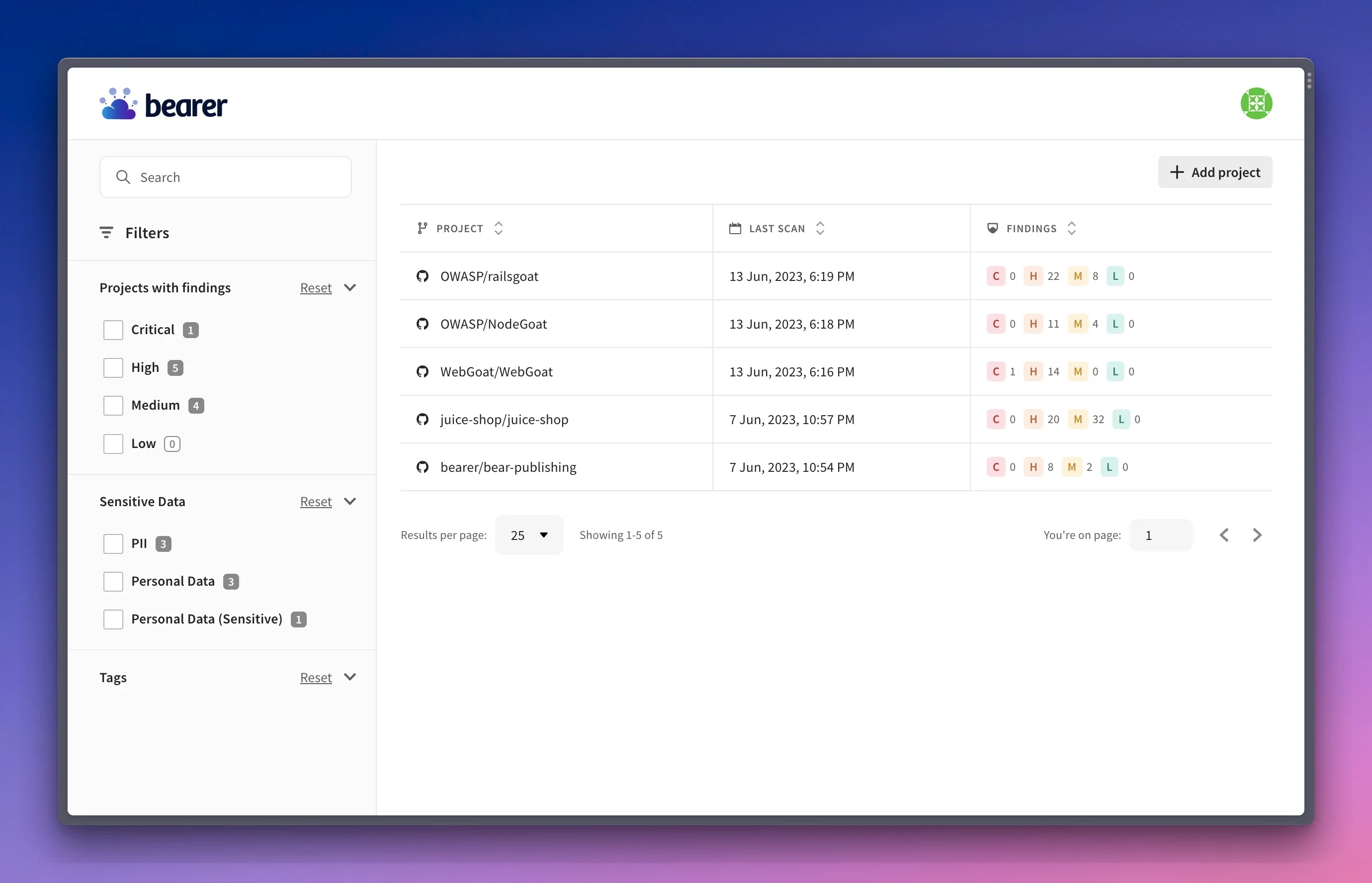
This means Bearer can identify secrets that are not just stored in config files but are passed through function calls, logged, or returned in API responses.
Gitleaks finds static patterns in files. Bearer finds patterns in how data moves.
For SAST tools teams, Bearer’s ability to catch credential exposure in runtime paths is a distinct capability. It supports Ruby, JavaScript, TypeScript, Python, Java, Go, and PHP.
Bearer is open-source under the BUSL-1.1 license. The commercial version adds more rules and integrations.
If your concern is not just committed secrets but exposed credentials in live application code, Bearer adds a dimension that Gitleaks and TruffleHog do not cover.
Best for: Development teams that want data-flow analysis alongside secret pattern detection. License: Open-source (BUSL-1.1) Key difference: Data-flow tracing finds credentials exposed in application logic, not just committed in config files.
5. Aikido Security
Aikido Security is an all-in-one AppSec platform that includes secret scanning as one of its modules alongside SAST, SCA, and container scanning.
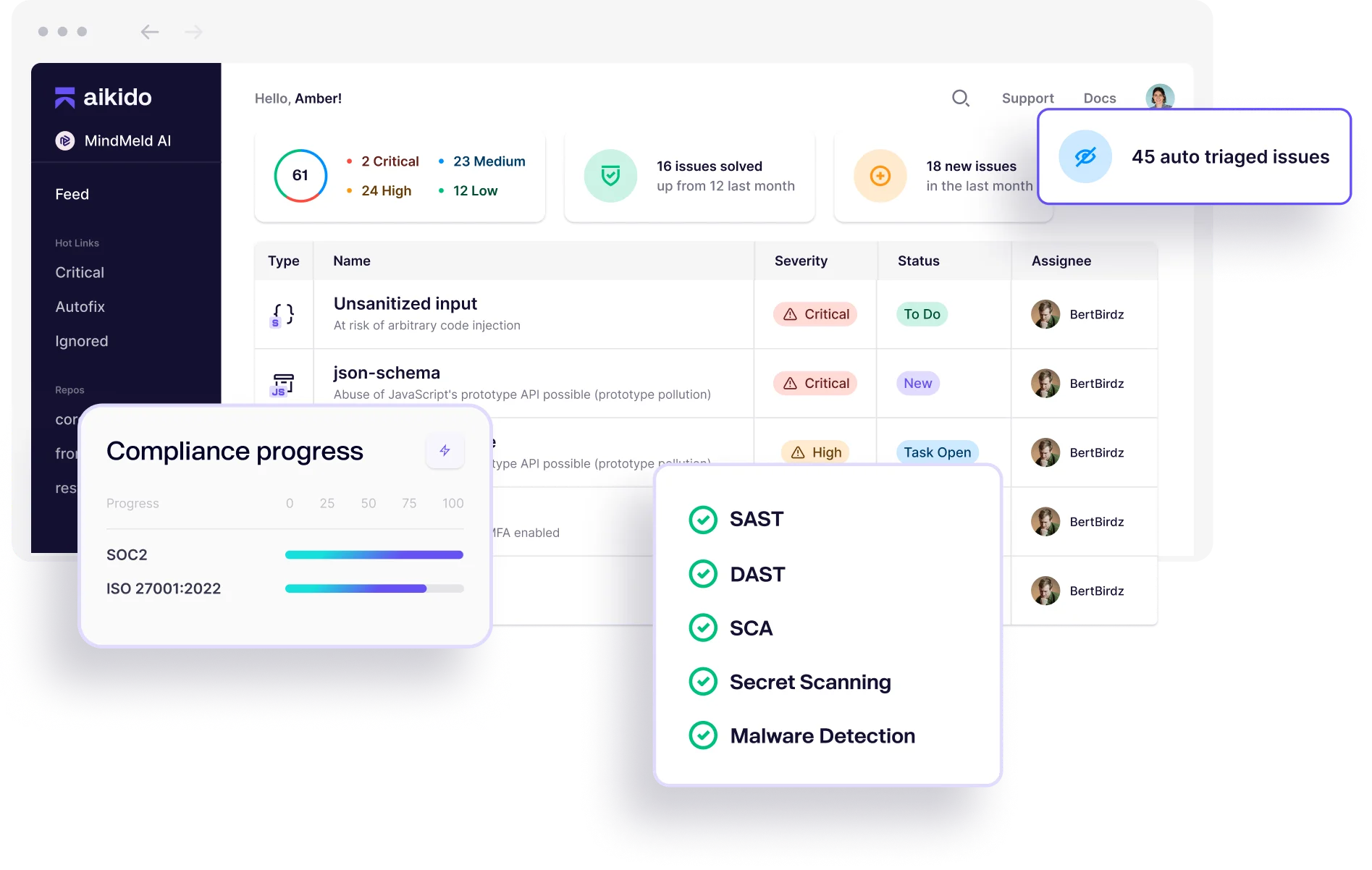
If your team is evaluating Gitleaks alternatives as part of a broader effort to consolidate AppSec tooling rather than just improve secrets detection specifically, Aikido is worth considering.
The secret scanning module covers standard credential patterns and integrates with Aikido’s single-pane interface for triaging and tracking findings across all AppSec categories.
For small to mid-size engineering teams managing multiple AppSec tools separately, Aikido’s consolidation can reduce operational overhead at the cost of depth in any single scanning category.
Best for: Teams consolidating multiple AppSec tools who want secret scanning included in a broader platform. License: Commercial (free tier available) Key difference: Secret scanning as part of an integrated AppSec platform (SAST, SCA, containers, secrets in one tool).
Feature Comparison
| Feature | Gitleaks | TruffleHog | GitGuardian | detect-secrets | Bearer |
|---|---|---|---|---|---|
| License | Open-source (MIT) | Open-source (AGPL-3.0) | Commercial (free tier) | Open-source (Apache 2.0) | Open-source (BUSL-1.1) |
| Secret types | 150+ | 800+ | 550+ | Plugin-based | Data-flow based |
| Verification | No | Yes (active API checks) | Yes | No | No |
| Pre-commit hook | Yes | Yes | Yes (ggshield) | Yes | Yes |
| CI/CD integration | Yes | Yes | Yes | Yes | Yes |
| Centralized dashboard | No | Enterprise only | Yes | No | No |
| Multi-surface scanning | Git only | Git, S3, Jira, Slack | Git + monitoring | Git only | Code analysis |
| Incident management | No | Enterprise only | Yes | No | No |
| Self-hosted | Yes | Yes | Enterprise only | Yes | Yes |
| Data-flow analysis | No | No | No | No | Core feature |
When to Stay with Gitleaks
Gitleaks is still the right choice in several common scenarios:
- Speed is critical. Gitleaks is among the fastest secret scanners available. For large monorepos where CI pipeline time is a constraint, its pure pattern-matching approach outperforms verification-based tools.
- You need a self-hosted, zero-dependency solution. Gitleaks runs as a single binary with no external service calls required. For air-gapped environments or organizations with strict data-residency requirements, this matters.
- Your pre-commit hook needs to be lightweight. The developer experience with Gitleaks is minimal friction. TruffleHog with verification adds latency that some teams find unacceptable in a synchronous pre-commit hook.
- 150+ built-in types cover your stack. If your organization uses standard SaaS credentials and cloud provider tokens, Gitleaks’ built-in rules handle the common cases well.
- Budget is zero and scope is git-only. Gitleaks is MIT-licensed, requires no account, and does exactly what it promises for repositories that live entirely in git.
For a broader look at secret detection tooling beyond Gitleaks alternatives, see the secret scanning tools guide . For more SAST tools comparisons, see the full category overview.
Frequently Asked Questions
What is the best free alternative to Gitleaks?
Does TruffleHog find more secrets than Gitleaks?
Can I use Gitleaks and GitGuardian together?
What is the difference between Gitleaks and GitHub Secret Scanning?
Which secret scanning tool has the best pre-commit integration?

Founder, AppSec Santa
Years in application security. Reviews and compares 215 AppSec tools across 12 categories to help teams pick the right solution. More about me →




