GitHub Advanced Security Alternatives
Thinking of switching from GitHub Advanced Security? Compare top alternatives including Semgrep, Snyk Code, SonarQube, Checkmarx, Socket, and GitGuardian for code scanning, secrets detection, and dependency review.
Top GitHub CodeQL Alternatives
View all 32 alternatives →- GitHub Advanced Security bundles CodeQL (SAST), secret scanning, and dependency review — alternatives rarely replace all three in one product, so evaluate by which layer matters most for your team.
- Semgrep is the fastest and most customizable open-source SAST alternative — scans run in seconds with 2,000+ community rules and YAML-syntax custom rules that non-security engineers can write.
- Snyk Code adds AI-assisted fix suggestions and a free tier (100 scans/month) to SAST — stronger for teams already using Snyk for SCA who want unified code and dependency security.
- GitGuardian and Gitleaks are the strongest alternatives to GHAS secret scanning for non-GitHub platforms — GitGuardian detects 350+ secret types with incident management; Gitleaks is open-source with no API dependency.
- Socket is the best alternative for the supply chain security gap in GHAS — it detects malicious packages through behavioral analysis, not just CVE matching, catching threats before they reach the advisory database.
GitHub Advanced Security (GHAS) is GitHub’s built-in application security suite for Enterprise plans, combining CodeQL-powered code scanning , secret scanning with push protection, and dependency review. For teams on GitHub Enterprise, it is the lowest-friction way to get SAST, secrets detection, and SCA coverage without deploying separate tools.
GHAS has real constraints. It works only on GitHub, CodeQL scans slow down on large monorepos, custom queries require learning the QL language, and per-active-committer pricing compounds quickly at scale.
Why look for GitHub Advanced Security alternatives?
**GitHub lock-in. ** GHAS only works on GitHub. Teams on GitLab, Bitbucket, Azure DevOps, or self-hosted Git servers cannot use it at all.
For organizations with mixed Git platforms — common in enterprises after acquisitions or mergers — GHAS creates coverage gaps wherever code lives outside GitHub. Tools like Semgrep and SonarQube integrate with all major Git platforms.
**Scan speed at scale. ** CodeQL builds a semantic database of your codebase before analysis. On large monorepos, this can take 10–30+ minutes per scan, which slows pull request feedback loops.
Semgrep and Snyk Code complete equivalent scans in seconds to minutes by using different analysis approaches. For a direct comparison, see Snyk Code vs GitHub CodeQL .
**Rule customization. ** GHAS ships a fixed set of CodeQL query packs. Writing custom CodeQL queries requires learning the QL query language — a non-trivial investment for most development teams.
Semgrep custom rules use YAML syntax that any developer can write in minutes. For a direct comparison of the two, see Semgrep vs CodeQL .
**Cost at scale. ** GHAS pricing is per active committer per month. For large engineering organizations with hundreds of active contributors, the cost compounds.
Some teams find that open-source alternatives (Semgrep , Gitleaks ) combined with targeted commercial tools cost less than GHAS at scale.
Secret scanning breadth. GHAS secret scanning covers 200+ token patterns . GitGuardian covers 350+ and includes real-time monitoring of public repositories — catching secrets even when they’re committed to repositories outside your organization.
Top GitHub Advanced Security alternatives
1. Semgrep
Semgrep is the most widely adopted open-source SAST alternative to CodeQL. It covers 30+ languages with pattern-matching rules and a community ruleset of 2,000+ checks. Semgrep scans complete in seconds to minutes rather than CodeQL’s minutes to tens of minutes.
What Semgrep does well: Custom rule writing is the key differentiator. Semgrep rules are YAML files that use code patterns — not a specialized query language. A developer can write a custom rule to catch a project-specific vulnerability pattern in 15 minutes. Semgrep Community Edition is fully open-source and integrates with GitHub Actions, GitLab CI, Bitbucket Pipelines, and Azure DevOps without platform lock-in.
Semgrep Code (the commercial tier) adds AI-generated fix recommendations, taint analysis rules, and centralized finding management. Semgrep Secrets is a separate product covering secret detection with 750+ validators.
Where Semgrep falls short: Semgrep’s pattern-matching does not perform the deep inter-procedural taint tracking that CodeQL achieves. A vulnerability that requires tracing data flow through multiple function calls across files is more reliably caught by CodeQL. Semgrep compensates with a broader community ruleset and faster iteration.
Best fit: Teams on any Git platform (GitHub, GitLab, Bitbucket, Azure DevOps) that want fast SAST with customizable rules and no platform lock-in.
2. Snyk Code
Snyk Code is a commercial AI-assisted SAST tool that combines dataflow analysis with an AI fix engine. It scans in seconds, supports 20+ languages, and integrates with Snyk Open Source for unified SAST + SCA on a single platform.
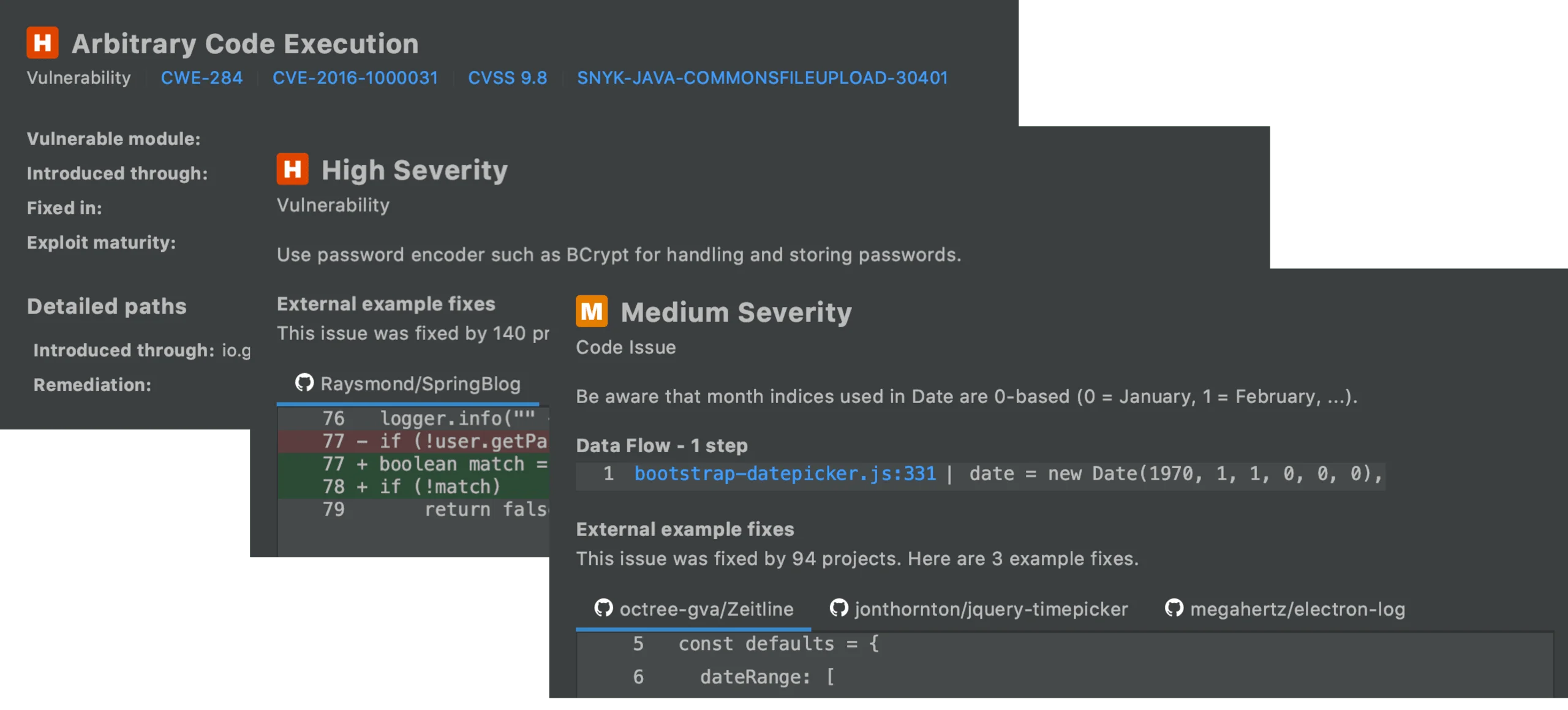
What Snyk Code does well: AI fix suggestions are Snyk Code’s most distinctive feature — for common vulnerability patterns (SQL injection, XSS, path traversal), Snyk Code generates a fix diff that developers can apply directly. The free tier allows 100 tests per month . For teams already using Snyk for SCA, adding Snyk Code unifies code and dependency security findings in one interface.
Snyk Code’s analysis is fast because it uses a proprietary semantic analysis engine rather than CodeQL’s database-build approach. IDE plugins for VS Code, IntelliJ, and Eclipse provide real-time SAST feedback without leaving the editor.
Where Snyk Code falls short: Snyk Code covers more languages than CodeQL, but CodeQL’s analysis goes deeper on the languages it does support — inter-procedural taint tracking across complex call graphs. Custom rules are available in the enterprise tier but require Snyk’s rule format, not the open rule ecosystem that Semgrep provides.
Best fit: Teams already using Snyk for dependency security that want to extend to code scanning on a unified platform, or teams that prioritize AI fix suggestions to reduce developer friction.
3. SonarQube
SonarQube combines code quality analysis with security vulnerability detection across 30+ languages. Its Community Edition is open-source and free; Developer, Enterprise, and Data Center editions add branch analysis, taint analysis, security hotspot review, and integration features.
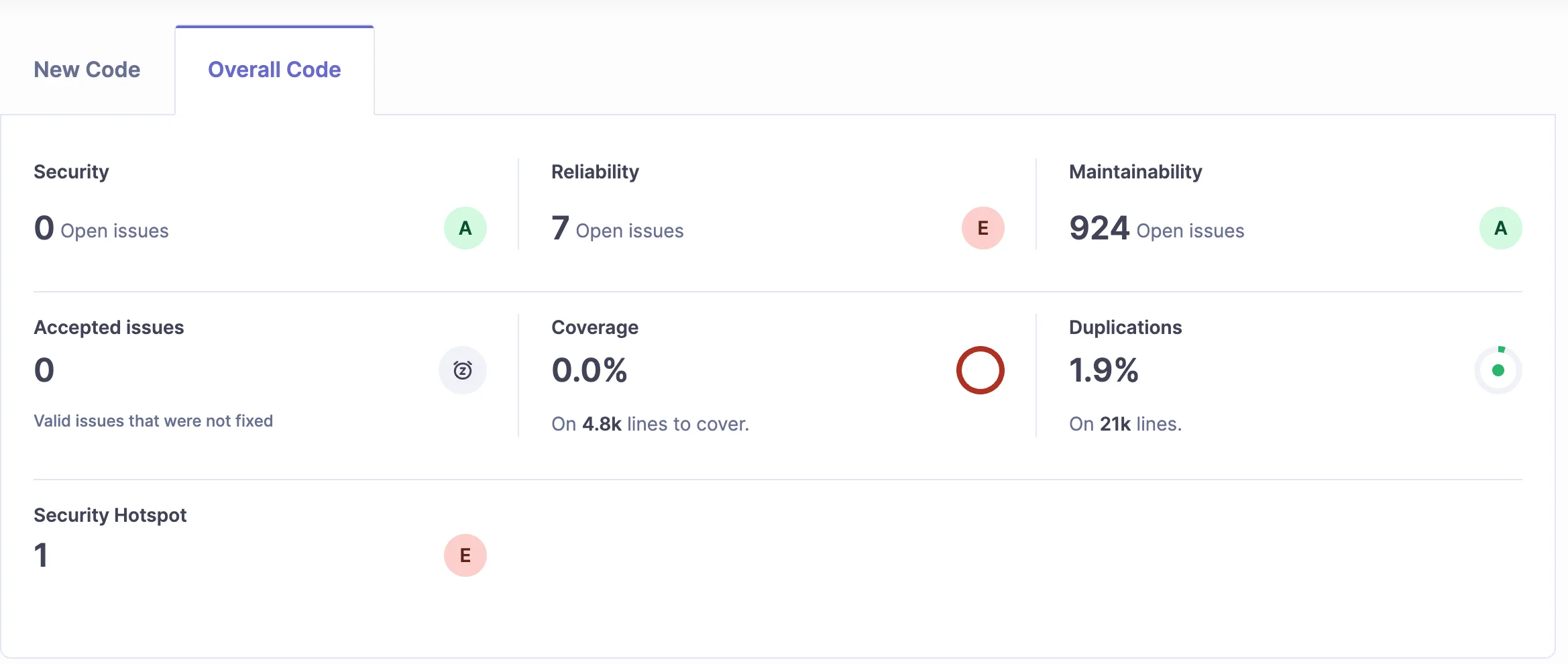
What SonarQube does well: Code quality integration is SonarQube’s unique position. It covers not just security vulnerabilities but also code smells, duplication, complexity, and technical debt — making it appealing to teams that want security and quality in a single gate. The Quality Gate concept lets teams define passing conditions for pull requests: zero new critical security issues, code coverage above 80%, and duplication below 3%. For alternatives to SonarQube itself, see SonarQube alternatives .
SonarQube’s taint analysis (available in the Developer Edition and above) tracks data flow through method calls to catch injection vulnerabilities — comparable in approach to CodeQL but with a different trade-off on speed vs depth.
Where SonarQube falls short: The open-source Community Edition lacks taint analysis and branch analysis. Teams on the free tier get basic security pattern matching, not deep dataflow. The commercial editions require self-hosted deployment (or SonarCloud, the SaaS version) and per-developer licensing.
Best fit: Teams that want code quality and security in a single platform, especially those with existing SonarQube deployments for code quality that want to extend to security coverage.
4. Checkmarx
Checkmarx is a commercial enterprise SAST platform with deep inter-procedural taint analysis comparable to CodeQL. Checkmarx One bundles SAST, SCA, IaC scanning, container security, API security, and ASPM in a single platform.
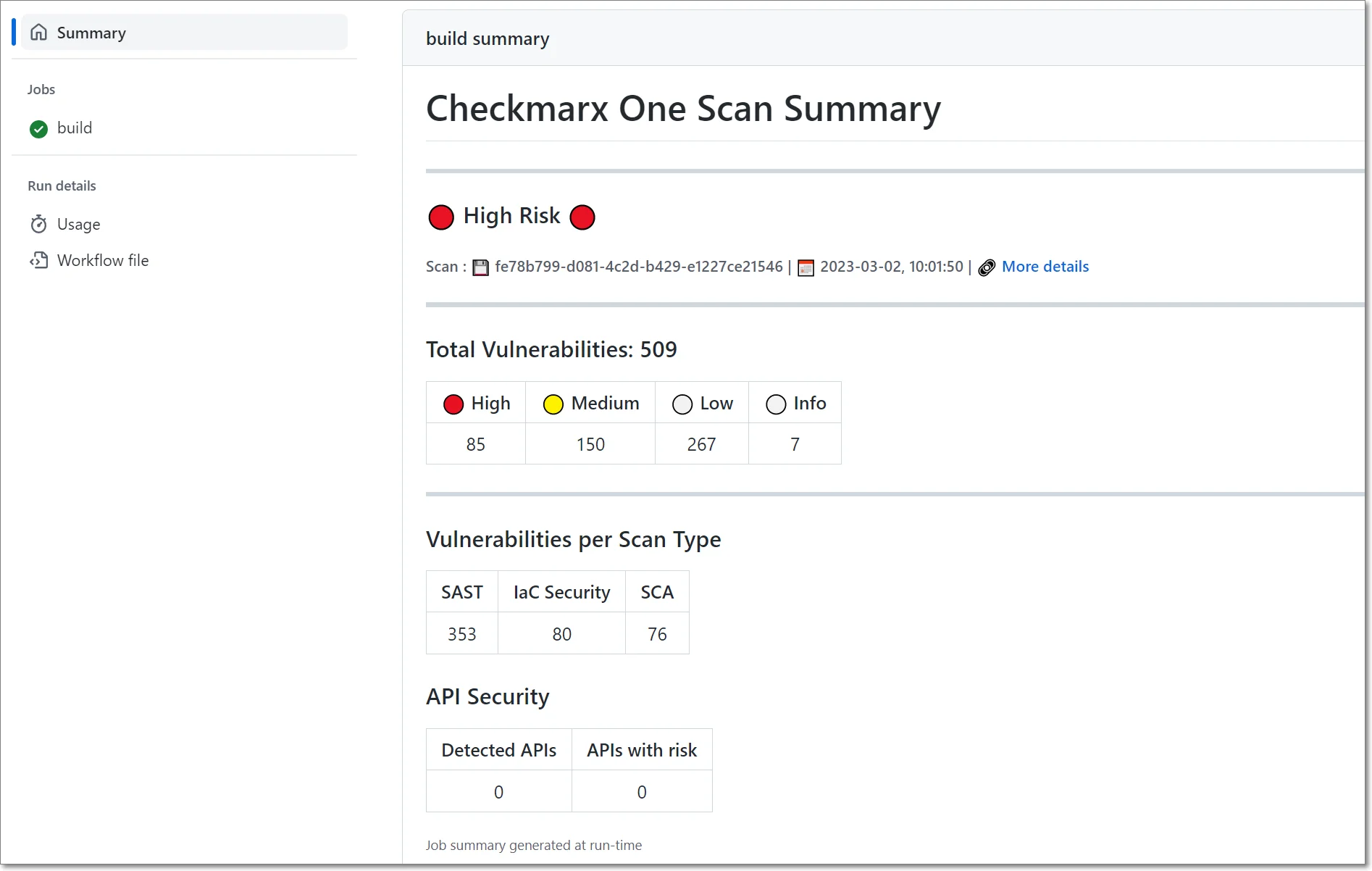
What Checkmarx does well: Enterprise breadth — for organizations that want a single vendor covering the full AppSec lifecycle. Checkmarx SAST performs deep inter-procedural analysis with configurable query customization through its proprietary CxQL language. It integrates with GitHub, GitLab, Bitbucket, Azure DevOps, Jenkins, and most CI/CD platforms. For a deeper comparison, see Checkmarx alternatives .
Checkmarx also provides compliance-oriented reporting for SOC 2, PCI DSS, HIPAA, and OWASP Top 10 that GHAS does not produce.
Where Checkmarx falls short: Cost and complexity. Checkmarx One is priced for enterprise contracts with no public pricing. Scan times on large codebases can be significant. For small or mid-sized teams that do not need the full platform breadth, the investment is hard to justify.
Best fit: Large enterprises needing full-lifecycle AppSec coverage from a single vendor with compliance reporting requirements.
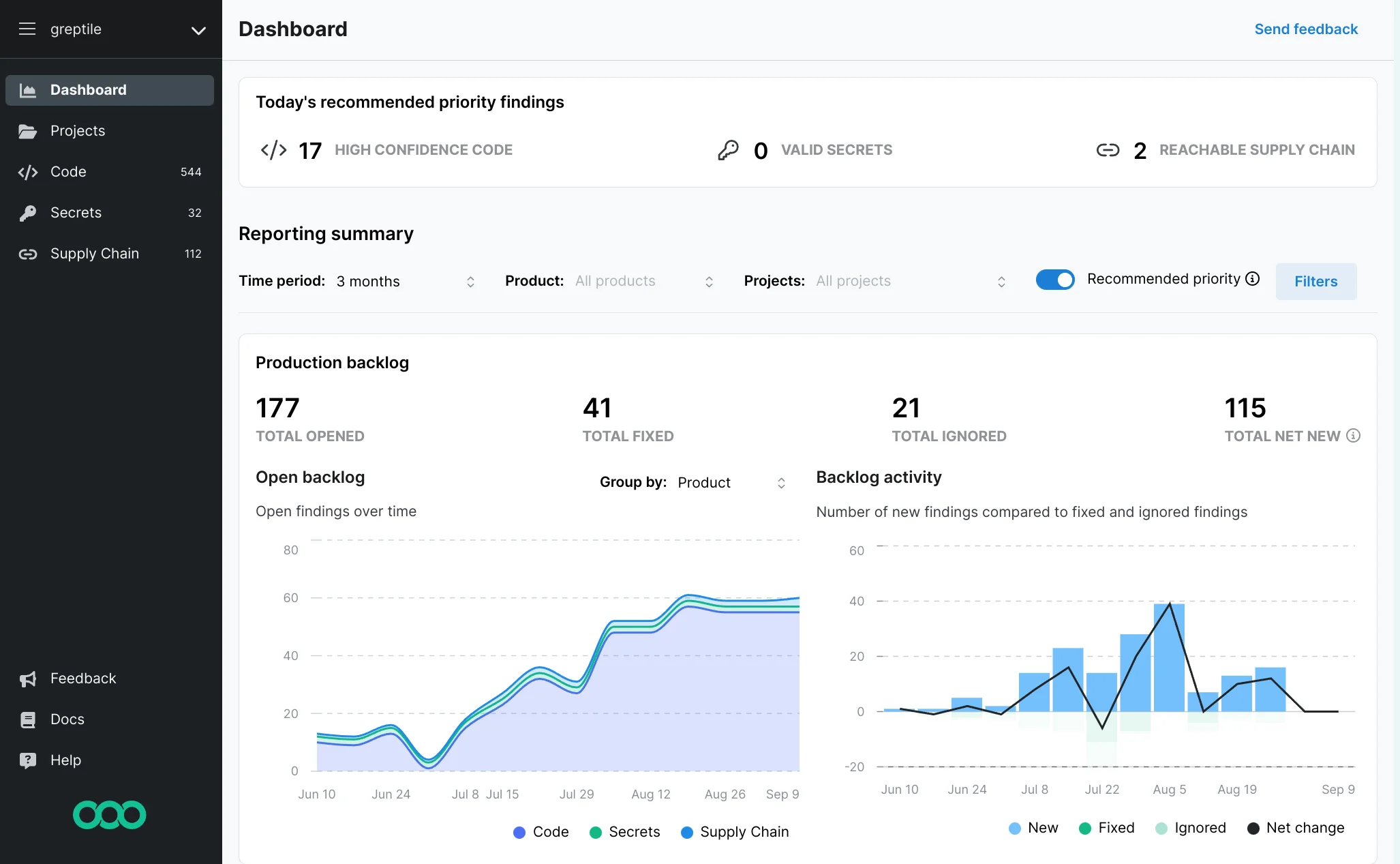
5. Socket
Socket is a supply chain security tool that addresses the gap GHAS dependency review does not close: malicious package detection. GHAS dependency review checks for known CVEs in dependencies. Socket analyzes the actual behavior of npm, PyPI, Maven, and other packages — install scripts that phone home, packages that access the filesystem unexpectedly, or typosquatted packages mimicking legitimate names.
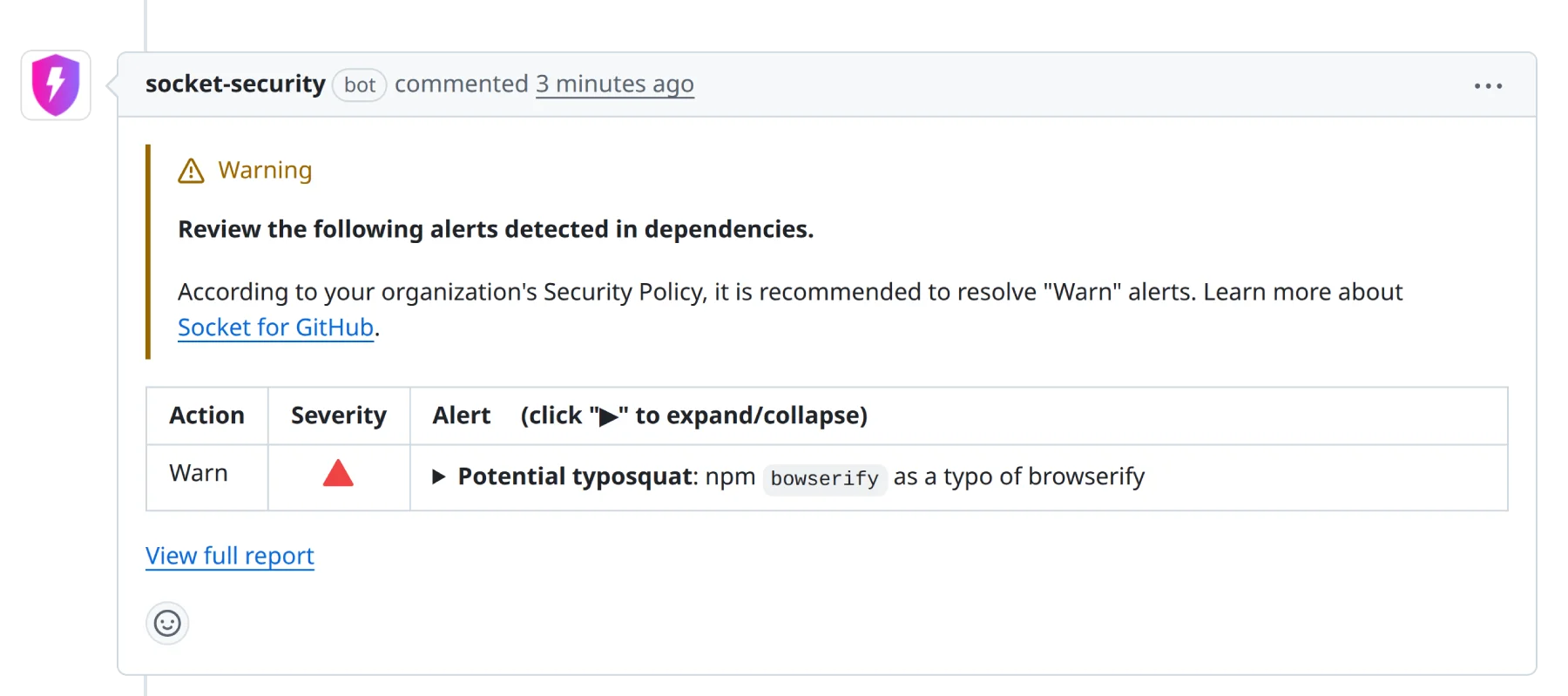
What Socket does well: Behavioral analysis catches supply chain attacks that have no CVE entry — malicious packages added to open-source projects before the advisory databases are updated. Socket’s threat detection monitors the npm registry in real-time and alerts within hours of a new malicious package being published. A GitHub App integration blocks pull requests that introduce suspicious packages before they’re merged.
Where Socket falls short: Socket is a supply chain security tool, not a SAST tool. It does not scan application code for vulnerabilities — it analyzes package behavior. Teams replacing GHAS need Socket plus a SAST tool (Semgrep or SonarQube) for full coverage.
Best fit: Teams with significant open-source dependency usage (especially npm/Node.js) who need supply chain attack detection that CVE-based tools cannot provide.
6. GitGuardian
GitGuardian is the leading alternative to GHAS secret scanning. It monitors commits across GitHub, GitLab, Bitbucket, Azure DevOps, and self-hosted Git servers for 350+ secret types — including AWS keys, GCP service account credentials, database connection strings, Slack tokens, and custom regex patterns.
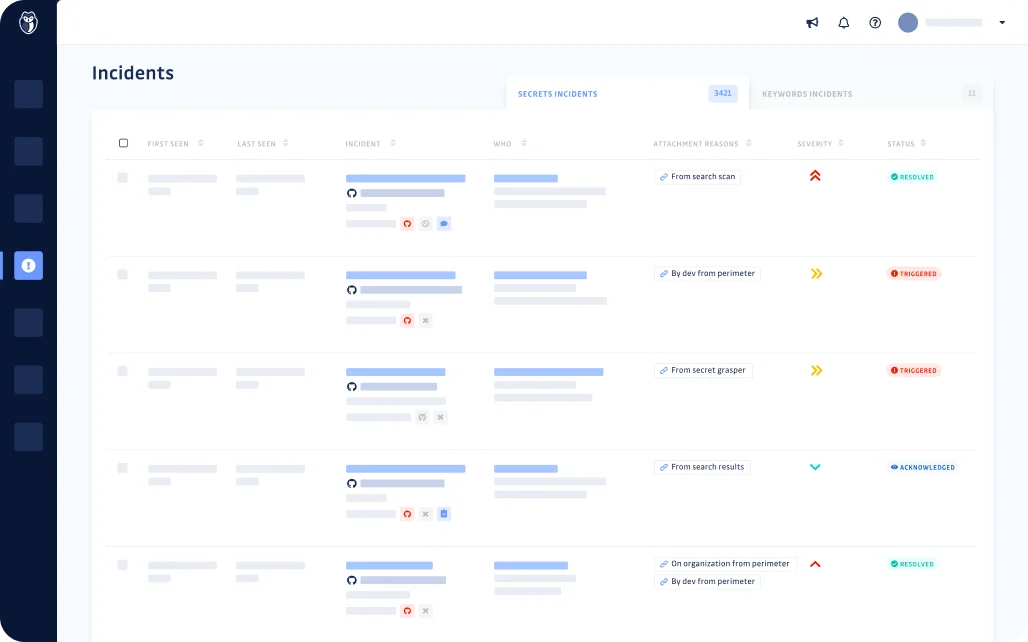
What GitGuardian does well: Platform breadth and detection volume. GitGuardian monitors all branches and historical commits, not just the default branch. It provides real-time alerts when a secret is detected, a remediation workflow for developers to rotate and remediate, and a centralized security team dashboard for incident tracking. GitGuardian also monitors public GitHub repositories — catching secrets accidentally committed to public repos from your organization’s email domains.
The free tier for public repositories and a developer plan are available, making it accessible for smaller teams.
Where GitGuardian falls short: GitGuardian is a secrets detection tool — it does not cover SAST, SCA, or dependency review. Teams replacing all of GHAS need GitGuardian alongside a SAST tool.
Best fit: Teams on GitLab, Bitbucket, or Azure DevOps who need secret scanning with coverage equivalent to GHAS, or GitHub teams that want broader secret detection patterns and historical commit scanning.
Comparison table
| Tool | Code Scanning | Secrets | Dependency Review | Platform Support | Cost |
|---|---|---|---|---|---|
| GHAS (CodeQL) | Yes (deep taint) | Yes (200+ types) | Yes | GitHub only | Per committer |
| Semgrep | Yes (pattern + taint) | Yes (Semgrep Secrets) | No | Any Git platform | Free / Commercial |
| Snyk Code | Yes (AI-assisted) | No | Via Snyk SCA | Any Git platform | Free tier |
| SonarQube | Yes (quality + security) | No | No | Any Git platform | Free / Commercial |
| Checkmarx | Yes (deep taint) | No | Yes (SCA) | Any Git platform | Enterprise |
| Socket | No | No | Yes (behavioral) | GitHub, GitLab | Free / Commercial |
| GitGuardian | No | Yes (350+ types) | No | Any Git platform | Free / Commercial |
When to stay with GHAS
GHAS is the right choice for GitHub-native organizations that want security built into their existing developer workflow with minimal operational overhead. If your entire engineering organization is on GitHub Enterprise and you want SAST, secrets, and dependency review without deploying additional tooling, GHAS delivers this at lower operational cost than assembling a multi-tool stack.
CodeQL’s semantic analysis depth is also genuinely hard to match with open-source alternatives for complex dataflow vulnerabilities. For security-critical codebases (financial services, healthcare) where catching inter-procedural taint vulnerabilities matters, CodeQL remains technically strong.
The cases where alternatives win: multi-platform Git environments, faster feedback loops needed, custom rule requirements, secrets detection breadth, or supply chain attack protection that CVE databases miss. For a broader view of the SAST landscape, see the SAST tools comparison and the SAST tools for JavaScript and Python guides for language-specific recommendations.
FAQ
Frequently Asked Questions
What is GitHub Advanced Security?
Is Semgrep better than GitHub Advanced Security?
Does GitHub Advanced Security work outside GitHub?
What is the best alternative to GHAS secret scanning?
How much does GitHub Advanced Security cost?

Founder, AppSec Santa
Years in application security. Reviews and compares 215 AppSec tools across 12 categories to help teams pick the right solution. More about me →