Enterprise SAST tools are static analysis platforms built for organizations scanning hundreds of repositories across multiple languages under compliance pressure. For a primer on the underlying technique, see what is SAST .
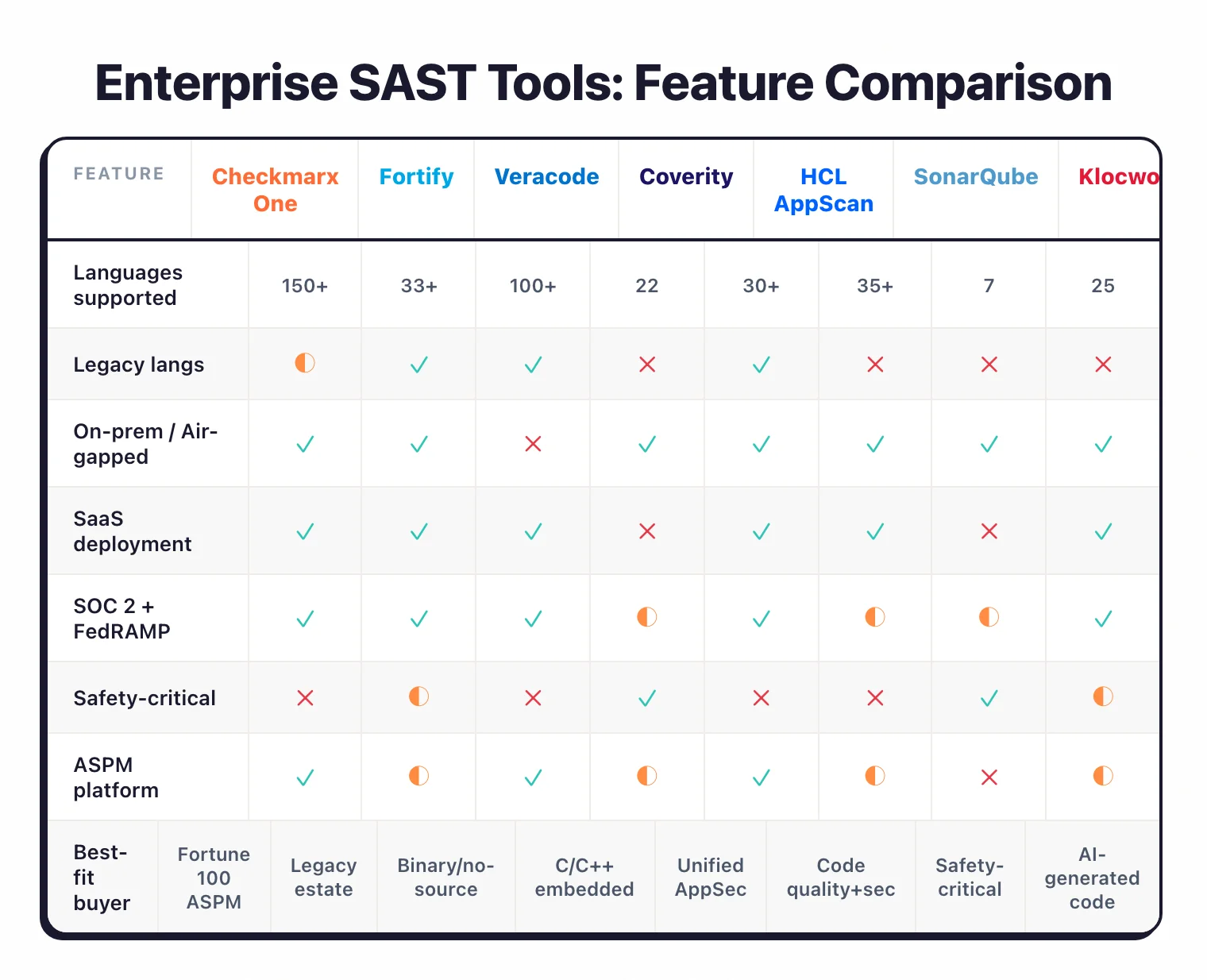
This guide compares 8 enterprise-tier SAST products — Checkmarx One , OpenText Fortify , Veracode Static Analysis , Black Duck Coverity , HCL AppScan , SonarQube Enterprise , Klocwork , and Mend SAST — across language coverage, compliance certifications, deployment models, and best-fit customer profile.
The open-source alternatives and developer-first tools have their own guides; everything here is enterprise-grade and contact-sales only.
Pricing note: All eight vendors on this list are contact-sales only. There are no published list prices for enterprise tiers. I do not publish pricing figures unless a vendor displays them on their own site.
For the full SAST landscape including developer-first and free options, see the complete SAST tools comparison or the open source SAST tools guide .
What makes a SAST tool enterprise-grade?
Enterprise SAST tools are static analysis platforms designed to scan hundreds of repositories across mixed modern and legacy codebases under active compliance pressure. The defining traits are deep inter-procedural taint analysis, support for legacy languages like COBOL or ABAP, on-premises deployment for air-gapped environments, SSO and RBAC, and SLA-backed support — not merely a higher price tier.
“Enterprise SAST” is a buyer’s shorthand for a tool that survives procurement review at a Fortune 2000 company. It is not simply the most expensive tier in a vendor’s pricing table.
Most developer-first tools — Semgrep , Snyk Code , SonarQube Community Build — optimize for fast feedback on a single repository. Enterprise SAST solves a different problem entirely: governance across hundreds of repos, multi-year audit trails, and deep analysis on codebases that mix modern microservices with 20-year-old legacy systems. The moment compliance auditors arrive with a PCI DSS or FedRAMP questionnaire, developer-first tools usually stop being enough.
I use six criteria to decide whether a tool belongs on an enterprise shortlist.
- Language breadth beyond the modern stack. Enterprise estates still contain COBOL, ABAP, RPG, Visual Basic 6, and large C/C++ codebases. A tool that only covers the JVM and JavaScript eliminates itself from the conversation.
- Deep inter-procedural taint analysis. The tool must trace user input across files, modules, and function calls — not just match patterns in a single file. This is the main technical gap between enterprise and developer-first tools.
- On-premises or air-gapped deployment. Many regulated environments cannot send source code to a SaaS vendor. On-prem support is a procurement blocker, not a nice-to-have.
- SSO, SAML, and RBAC. Large orgs need tools that plug into Okta, Azure AD, or similar identity providers and support role-based access across hundreds of teams.
- Compliance certifications and reports. SOC 2 Type II, ISO 27001, FedRAMP, PCI DSS, HIPAA — plus mappings to OWASP Top 10, CWE Top 25, and industry-specific standards like MISRA or AUTOSAR for safety-critical work.
- SLA-backed support. When a scanner flags something unexpected at 2am before a release, open-source means reading source code and searching GitHub issues. Enterprise means calling a support engineer.
Tools that hit five or six of these criteria make the shortlist below. Tools that hit three or four get mentioned in context but do not anchor the guide.
Feature comparison
The table below summarizes the eight enterprise SAST tools across the dimensions that typically drive purchase decisions.
| Tool | Languages | Deployment | Compliance Standards | Best For |
|---|---|---|---|---|
| Checkmarx One | 150+ technologies | SaaS + Self-hosted | OWASP, PCI DSS, HIPAA, SOC 2 | Fortune 100 ASPM consolidation |
| OpenText Fortify | 33+ (COBOL, ABAP) | On-prem + SaaS (Fortify on Demand) + Hybrid | OWASP, PCI DSS, HIPAA, FISMA | Mixed modern + legacy estates |
| Veracode Static Analysis | 100+ (COBOL, VB6, RPG) | SaaS only | OWASP, PCI DSS, HIPAA, FedRAMP | Binary analysis, no-source workflows |
| Black Duck Coverity | 22 (deep C/C++) | Self-hosted | MISRA, AUTOSAR, ISO 26262, CERT, OWASP, CWE Top 25, DISA STIG | C/C++ and embedded safety-critical |
| HCL AppScan | 30+ (COBOL, Swift) | SaaS + Self-hosted | OWASP, PCI DSS, HIPAA | Unified AppScan 360° (SAST+DAST+IAST+SCA) |
| SonarQube Enterprise | 35+ | Self-hosted | OWASP, CWE, PCI DSS | Code quality + security in one platform |
| Klocwork | 7 (1,000+ C/C++ checkers) | Self-hosted | MISRA, AUTOSAR, CERT, DO-178B/C, ISO 26262, IEC 61508 | Safety-critical automotive, aerospace, medical |
| Mend SAST | 25 | SaaS + Self-hosted | OWASP, PCI DSS, HIPAA, MISRA | Agentic AI-generated code workflows |
Language breadth is the second common filter. If your stack includes COBOL, ABAP, RPG, or VB6, only Fortify , Veracode , and HCL AppScan cover it natively.
Top enterprise SAST tools
1. Checkmarx One
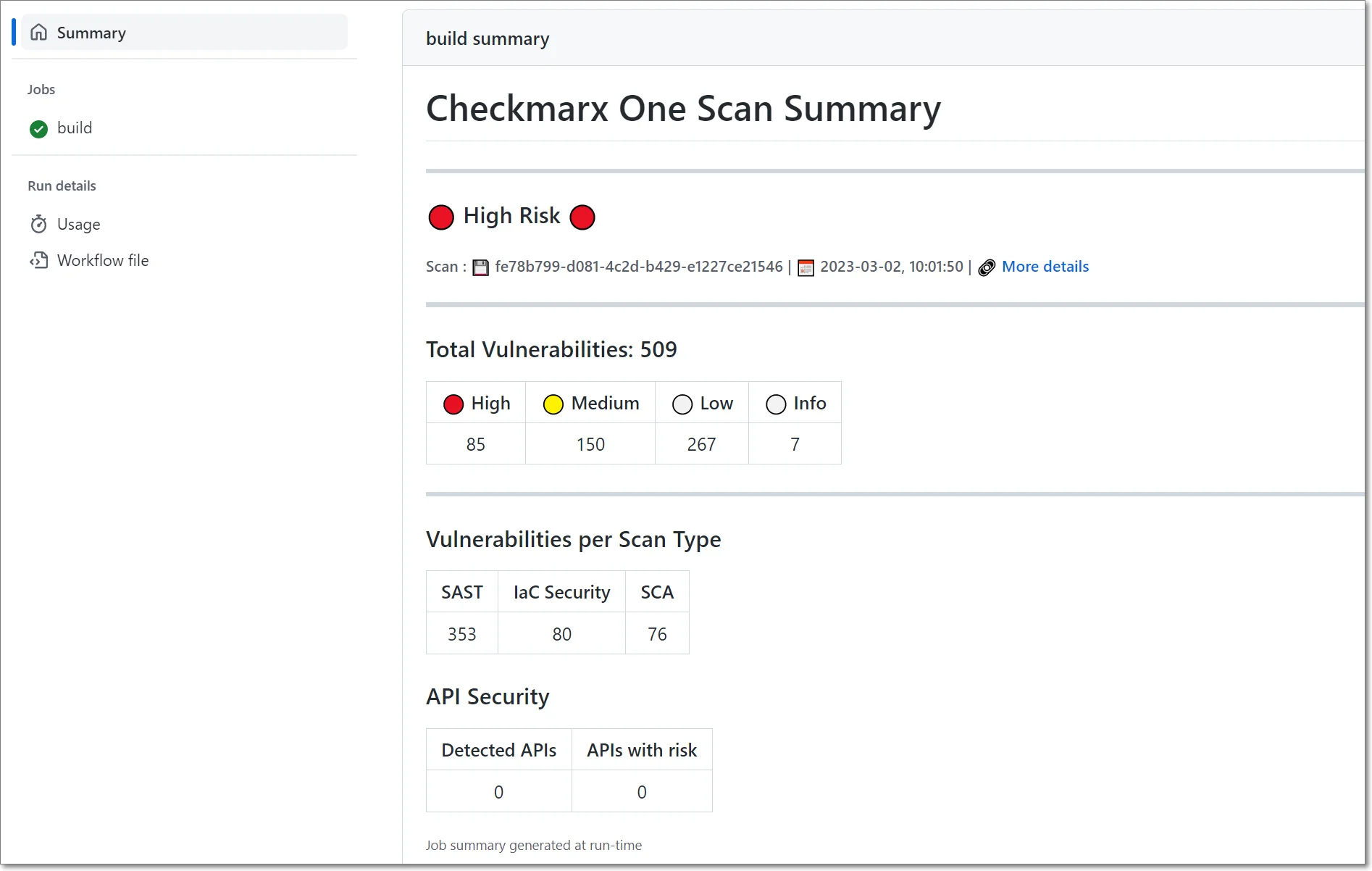
Checkmarx One is a unified application security platform that bundles SAST, SCA, DAST, IaC security, container security, API security, secrets detection, malicious package protection, and repository health scanning under a single ASPM layer. It supports 150+ technologies and, as of October 2025, scans 800 billion+ lines of code per month across its customer base — a scale metric that reflects how deeply the platform is embedded in large engineering organizations.
What it offers: Nine scanning engines correlated by ASPM, Checkmarx One Assist (AI remediation agents), Developer Assist for in-IDE prevention, and IDE plugins for VS Code, IntelliJ, Eclipse, Visual Studio, Cursor, and Windsurf.
Best for: Fortune 100 organizations consolidating multiple point tools into a single ASPM platform. Checkmarx reports that 60% of the Fortune 100 are customers , including Apple, Salesforce, Walmart, Visa, Citigroup, Ford, Siemens, Airbus, Adidas, and SAP.
Deployment: SaaS and self-hosted. On-premises is available for regulated and air-gapped environments.
2. OpenText Fortify
OpenText Fortify is one of the longest-running commercial SAST tools on the market, with two decades of enterprise deployments behind it. It detects 1,700+ categories of vulnerabilities across 33+ programming languages and 350+ frameworks, covering over 1 million individual APIs .
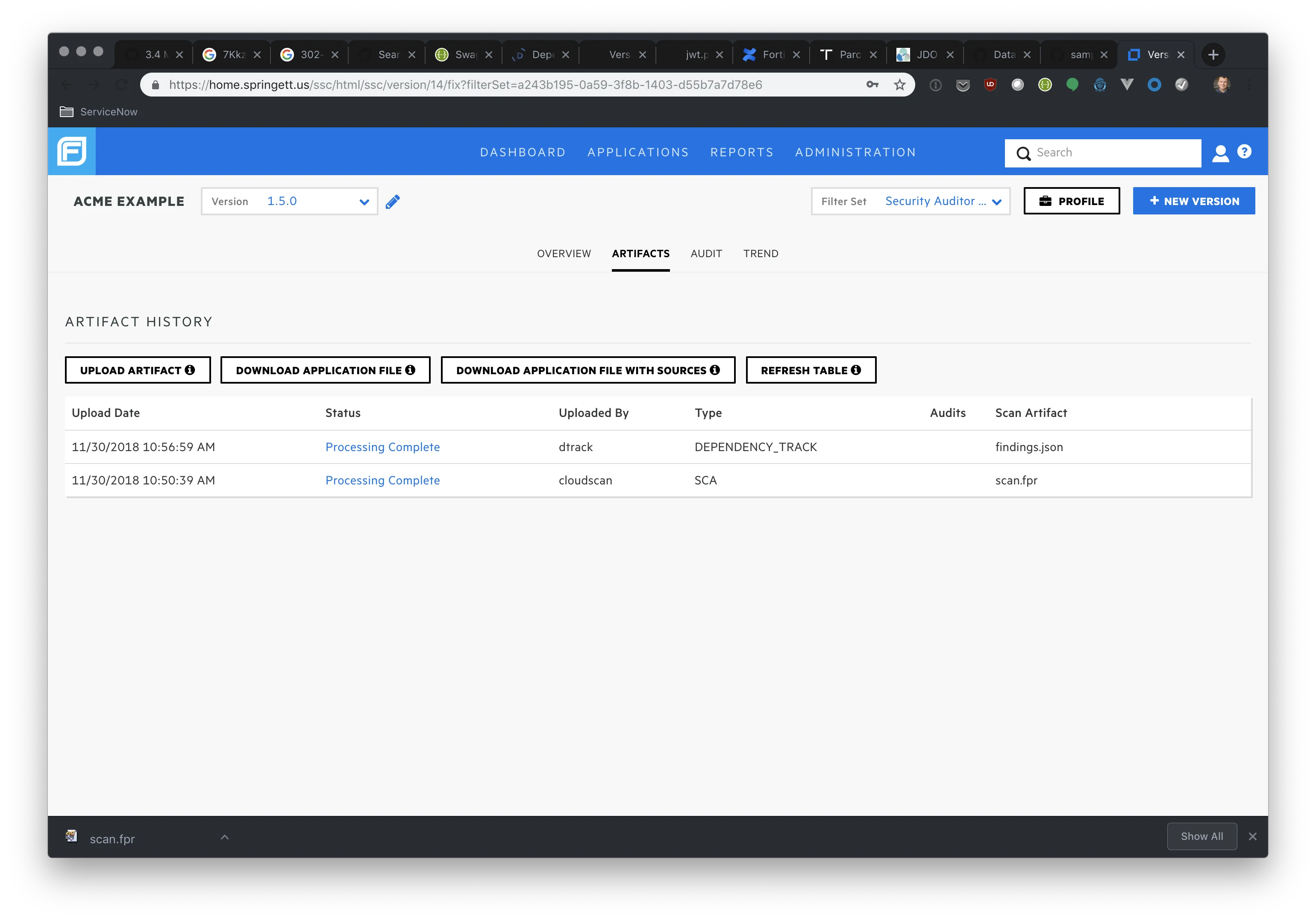
What it offers: Deep inter-procedural analysis, Fortify Aviator AI for automated code fix suggestions, IaC and container scanning, and IDE/CI-CD integrations.
Best for: Organizations with mixed modern and legacy estates. Fortify’s language list includes COBOL, ABAP, Apex, Swift, Kotlin, and most modern languages — few tools cover this range natively.
Deployment: On-premises, SaaS (Fortify on Demand), and hybrid. Now owned by OpenText, which acquired Micro Focus in 2023.
3. Veracode Static Analysis
Veracode Static Analysis takes a different technical approach than its peers. Instead of scanning source code, it analyzes compiled binaries — JAR files, .NET assemblies, native executables — meaning source code never leaves the developer’s environment.
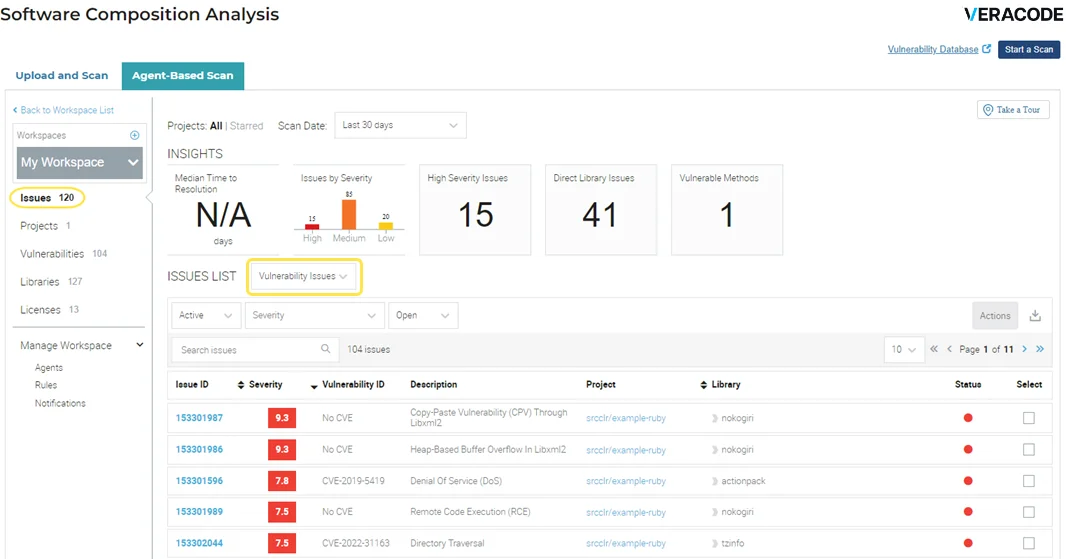
What it offers: Binary analysis across 100+ languages and frameworks , Pipeline Scan for CI/CD (results in under 90 seconds), Platform Scan for deep compliance analysis, and 40+ CI/CD integrations in a unified platform alongside Veracode DAST, SCA, and manual penetration testing.
Best for: Organizations where source code cannot be shared with security teams, contractors, or vendors. The binary model sidesteps that governance problem entirely. Legacy language support includes COBOL, Visual Basic 6, and RPG.
Deployment: SaaS only. There is no on-premises Veracode deployment — the binary is uploaded to Veracode’s cloud for analysis.
4. Black Duck Coverity
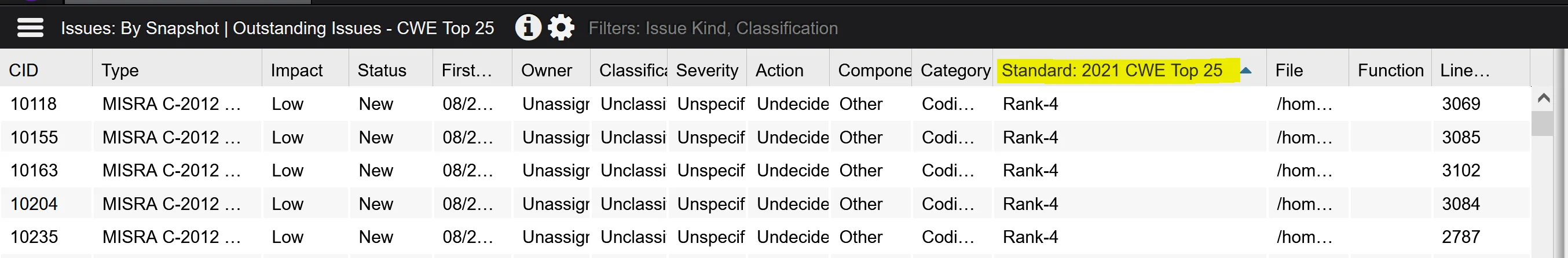
Black Duck Coverity (formerly Synopsys Coverity) is known for deep inter-procedural, path-sensitive, and context-sensitive static analysis. It is particularly strong on C and C++ and is widely deployed in embedded and safety-critical environments.
What it offers: Analysis across 22 languages and 200+ frameworks , 10 supported compliance standards (MISRA, AUTOSAR, ISO 26262, PCI DSS, CERT C/C++/Java, DISA STIG, OWASP Top 10, CWE Top 25), and the Code Sight IDE plugin with real-time SAST and SCA results. Black Duck reports that Code Sight users see a 42% reduction in manual code review time alongside a 66% reduction in vulnerability remediation time — numbers tied specifically to the IDE-side workflow.
Best for: Large regulated enterprises with significant C/C++ and embedded systems work. Black Duck reports Coverity is used by 51% of the Fortune 100 and over 4,000 organizations . Originally developed from Stanford University research before commercialization.
Deployment: Self-hosted. Coverity Scan offers free analysis for open-source projects including the Linux kernel and Firefox.
5. HCL AppScan
HCL AppScan is the security testing suite HCL Software acquired from IBM in 2017 . The AppScan 360° platform combines SAST, DAST, IAST, and SCA into a unified enterprise application security offering.
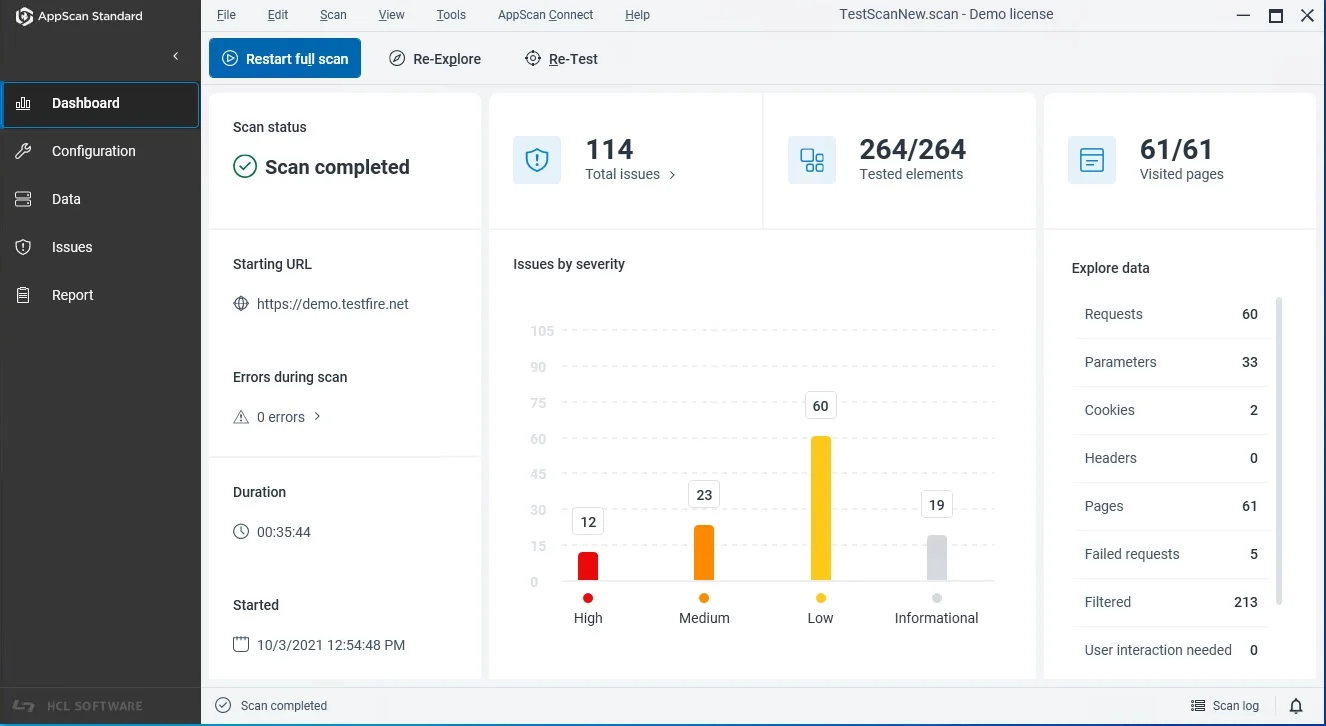
What it offers: SAST across 30+ languages including COBOL, Scala, Swift, Objective-C, Kotlin, and the usual modern set. ICA (Intelligent Code Analytics) and IFA (Intelligent Finding Analytics) use machine learning to reduce false positives and prioritize findings. A free CodeSweep VS Code extension is available for individual developers at no cost.
Best for: Organizations that want SAST, DAST, IAST, and SCA from a single vendor under one platform contract.
Deployment: SaaS and self-hosted. See HCL AppScan alternatives for head-to-head comparisons.
6. SonarQube Enterprise
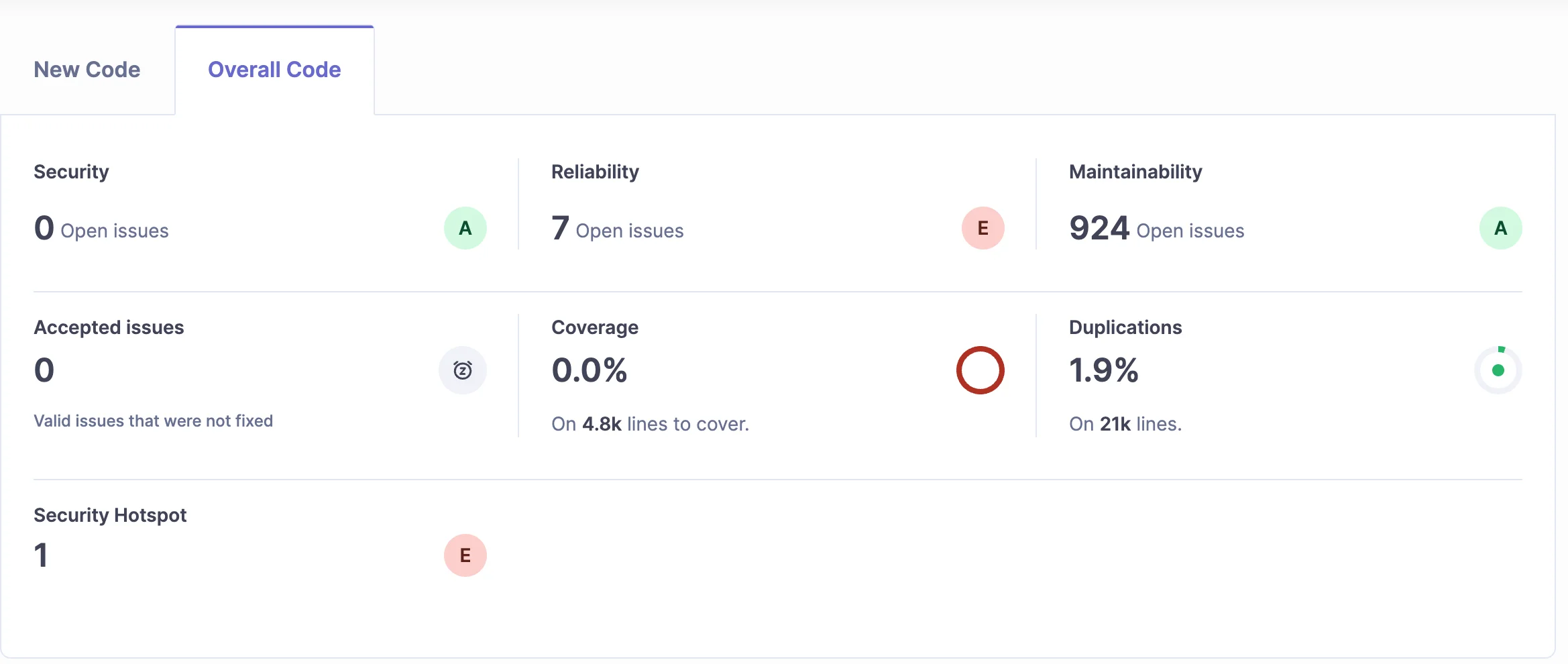
SonarQube Enterprise Edition is the commercial tier of the SonarQube platform , used by 7 million+ developers at organizations including Snowflake, Deutsche Bank, and Ford. Enterprise adds branch analysis, deeper taint tracking, portfolio reporting, and extended language coverage beyond the free Community Build.
What it offers: 6,000+ rules across 35+ languages, calendar-versioned releases (SonarQube Server 2026.2 is the latest, with 2026.1 as the Long-Term Active LTA release), AI CodeFix (model-agnostic — works with multiple LLMs), and an MCP Server that integrates with Claude Code, Cursor, and Windsurf.
Best for: Teams that want code quality and security in a single platform. SonarQube’s quality gates enforce pass/fail build criteria on new code, which is useful for regulated build pipelines.
Deployment: Self-hosted. SonarQube Cloud is a separate SaaS offering with a free tier at 50,000 LOC and 5 users.
7. Klocwork
Klocwork is Perforce’s safety-critical SAST tool , with 2,000+ checkers across C, C++, C#, Java, JavaScript, Python, and Kotlin. For C and C++ alone, Klocwork has 1,000+ checkers — one of the deepest C/C++ rule sets in the industry.
What it offers: TUV SUD certification for ISO 26262 (automotive), IEC 61508 (industrial), EN 50128 (railway), IEC 62304 (medical), and IEC 60880 (nuclear). Coverage for MISRA C (2004, 2012, 2023), MISRA C++, AUTOSAR C++14, CERT C/C++, and DO-178B/C aerospace standards. A differential analysis engine scans only changed files per commit for fast CI/CD feedback.
Best for: Safety-critical software teams in automotive, aerospace, medical devices, rail, and industrial control systems. If you need a TUV SUD certified SAST tool for functional safety compliance, Klocwork and Coverity are the two serious options.
Deployment: Self-hosted. Supports 50+ compiler environments natively.
8. Mend SAST
Mend SAST (formerly WhiteSource, rebranded May 2022) scans 25 languages with a dual-engine approach — Gen 1 covers all languages, Gen 2 adds deeper cross-file taint analysis for Java, C#, Python, JS/TS, and C/C++. In its first-ever appearance in the Forrester Wave for SAST (Q3 2025), Mend was classified as a Strong Performer and also named a “Customer Favorite” — top scores in Innovation and Triage criteria.
What it offers: An agentic SAST capability via MCP server that integrates with Cursor, Claude Code, GitHub Copilot, Windsurf, and Amazon Q — Mend scans AI-generated code before it enters the repository. Three scan profiles (Fast, Balanced, Deep) trade speed for depth. Covers 70+ CWE types with OWASP, PCI DSS, HIPAA, and MISRA compliance mapping.
Best for: Engineering orgs where AI coding assistants generate a meaningful share of new code and the security team needs a native integration with the IDE-side AI workflow. Source code never leaves the local environment — scanning runs locally.
Deployment: SaaS and self-hosted.
When to consider open source instead
Enterprise SAST is the right answer for large regulated orgs. It is the wrong answer for many other teams.
If your engineering org is under 200 developers, your codebase is under 1 million lines, and you do not face SOC 2, PCI DSS, HIPAA, or FedRAMP audits, a well-configured open-source stack will cover most of what you need. I wrote a detailed open source SAST tools guide that walks through Semgrep , SonarQube Community Build , GitHub CodeQL , Bandit , Brakeman , and gosec .
Three specific scenarios where I would start with open source rather than enterprise.
Single-language teams. If you ship only Python, only Ruby on Rails, or only Go, a language-specific tool (Bandit , Brakeman , gosec ) plus Semgrep for cross-language hygiene will catch 60-70% of what an enterprise tool catches — at zero license cost.
Public GitHub repositories. GitHub CodeQL is free for public repos and performs deep semantic analysis comparable to commercial tools. If your code is open source, CodeQL is the obvious starting point.
Early-stage startups. Before Series B, compliance pressure is usually minimal, the codebase is small enough that one security engineer can tune rules directly, and the budget for a $54,000-median enterprise contract does not exist yet.
The trigger for upgrading to enterprise is usually a specific procurement or audit requirement — a customer demanding SOC 2 Type II evidence, a compliance framework adoption (PCI DSS, HIPAA, FedRAMP), or the codebase crossing a complexity threshold where inter-procedural analysis starts catching vulnerabilities that pattern matching misses. For the full SAST landscape across both tiers, see the SAST tools category page .
For head-to-head comparisons between the enterprise tools on this list, see Fortify vs Veracode , Checkmarx vs Veracode , and Snyk Code vs Checkmarx .