Salt Security is an API security tools platform that uses behavioral ML to discover APIs, detect logic-based attacks, and enforce posture governance across cloud environments.
The platform — called Salt Illuminate — works by analyzing live API traffic without adding latency to the request path. I have compared Salt head-to-head with 42Crunch for buyers weighing behavioral runtime against contract-first design, and against Imperva API Security for the WAF-extension comparison.
Founded in 2016 and headquartered in Palo Alto, Salt was one of the first companies focused exclusively on API security. Co-founded by CEO Roey Eliyahu and COO Michael Nicosia.
Enterprise customers include Alaska Airlines, Hyundai, Stryker, SoFi, Kingston Technology, and Standard Bank Group.
What is Salt Security?
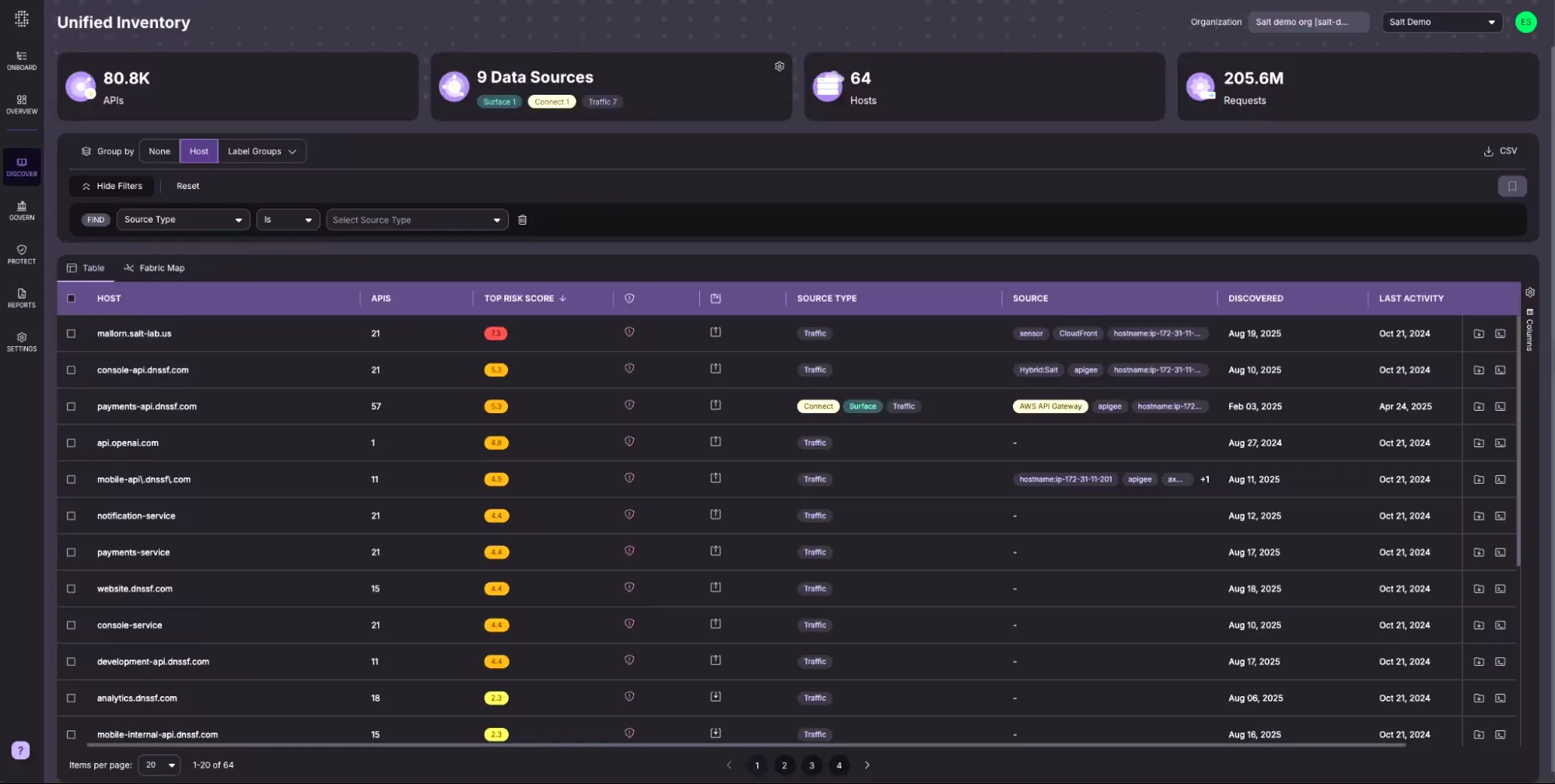
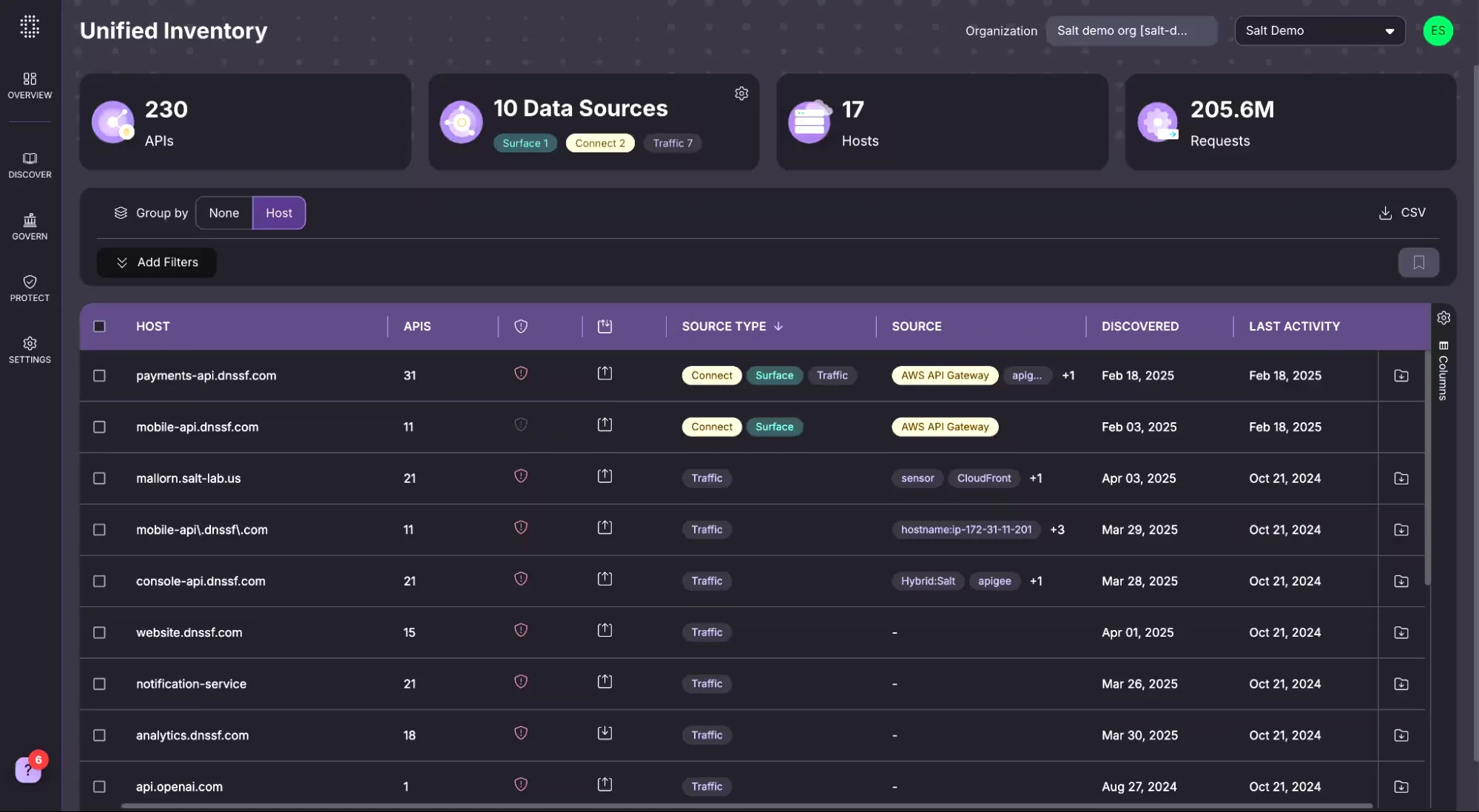
Salt Security addresses a gap most security teams know about but struggle to close: you can’t protect APIs you don’t know exist. The platform combines API discovery, posture governance, and runtime threat detection under one product.
Salt deploys agentlessly. Connect your cloud accounts, API gateways, or traffic mirrors, and the platform starts mapping your API landscape within minutes.
No inline agents, no added request latency, no architecture changes required.
What are Salt Security’s key features?
| Feature | Details |
|---|---|
| API Discovery | Shadow, zombie, internal, external, and third-party APIs via traffic, cloud connectors, and external surface scanning |
| Posture Governance | ~100 pre-loaded policy rules covering PCI DSS, HIPAA, GDPR, SOC 2, NIST, CMMC, FedRAMP |
| Threat Detection | BOLA, credential stuffing, data exfiltration, account takeover, injection, API abuse |
| Data Security | PII, PHI, and payment data tracking across API traffic in motion |
| AI Agent Security | MCP Protect for MCP server monitoring, Agentic AI Governance controls, GitHub Connect for code-level MCP discovery |
| Deployment | Cloud SaaS or on-premises, agentless with traffic mirroring |
API discovery
Salt discovers APIs through multiple data sources simultaneously:
- Salt Connect — Pulls API metadata from AWS, Azure, GCP, and gateways like Kong, Apigee, and MuleSoft. Agentless, cloud-native discovery.
- Salt Surface — Scans your external attack surface from an adversary’s perspective, finding public-facing APIs that internal tools miss.
- Traffic analysis — Monitors live API traffic to identify undocumented endpoints, including shadow APIs and deprecated-but-still-active zombie APIs.
- GitHub Connect — Scans public and private GitHub repositories to identify shadow APIs and MCP servers in source code before they reach production. Launched November 2025.
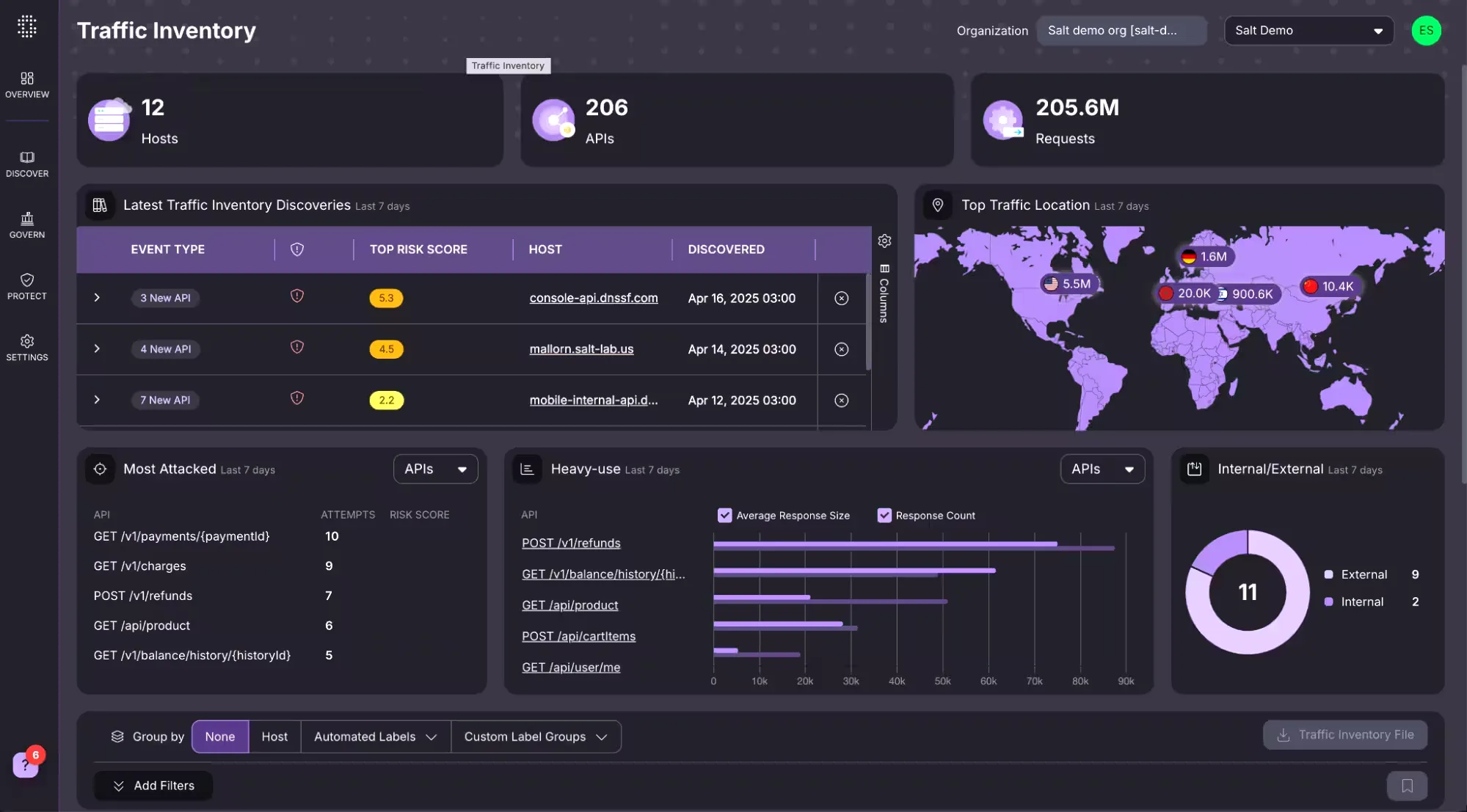
The platform automatically tags each discovered API with metadata: risk score, authentication type, data classification (PII, PHI), environment, and service owner. You can filter and group by any of these in the dashboard.
Posture governance
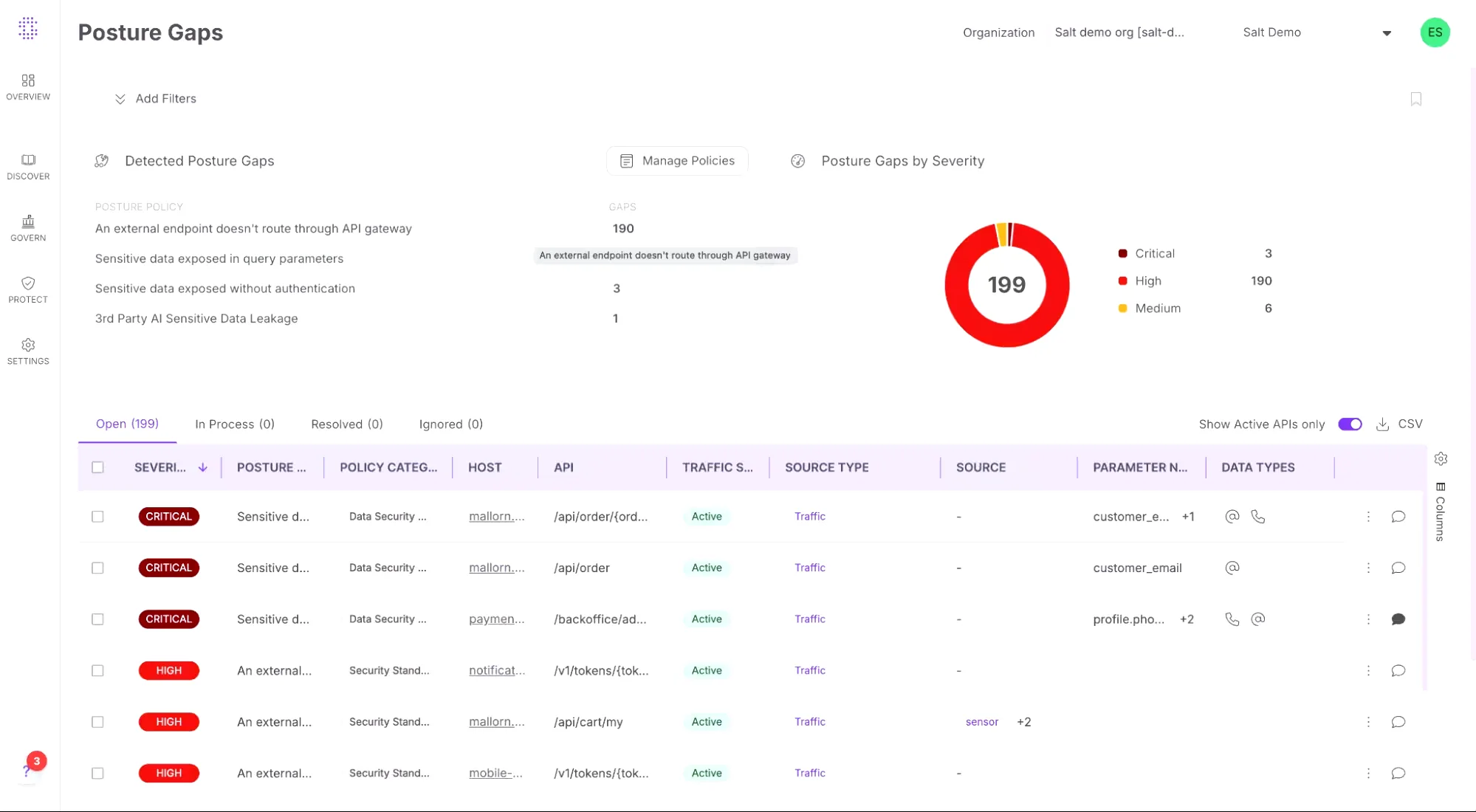
The Policy Hub ships with nearly 100 pre-loaded posture rules. Categories include PCI DSS, HIPAA, GDPR, SOC 2, NIST, CMMC, FedRAMP, OAuth, access control, data security, and API architecture standards.
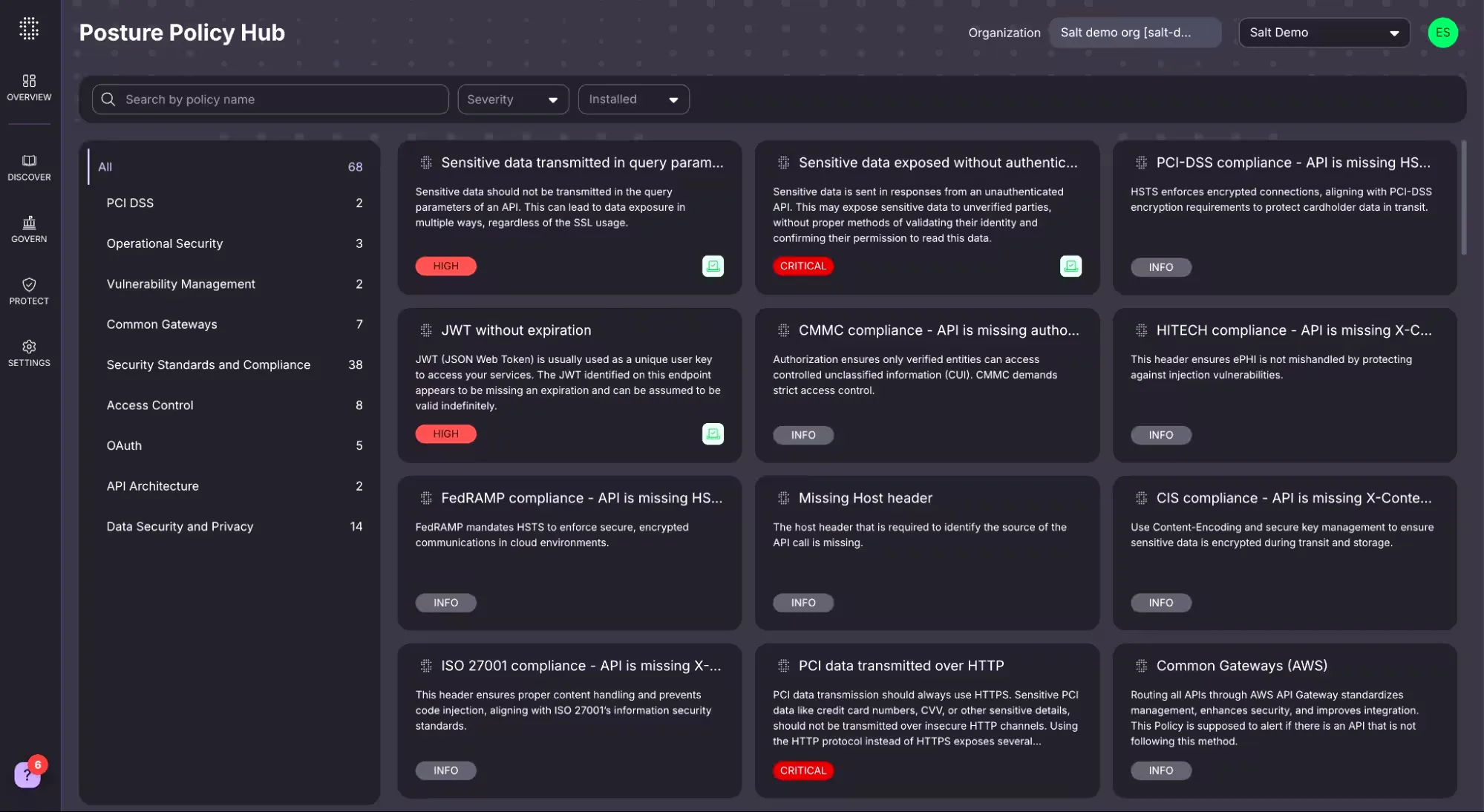
Each rule triggers a posture gap when violated. The dashboard groups gaps by severity (Critical, High, Medium) so you know where to focus first.
You can also create custom posture rules in three clicks and export reports for auditors.
Behavioral threat detection
Salt Protect baselines normal API behavior over days and weeks, then flags deviations that match attacker patterns. This catches logic-based attacks that WAFs and signature tools miss — things like slow credential stuffing, BOLA exploitation, and gradual data scraping.
Attack types Salt detects:
- BOLA/IDOR — Broken Object Level Authorization, the #1 API vulnerability per OWASP
- Credential stuffing — Automated login attempts across API endpoints
- Data exfiltration — Systematic extraction of data through API responses
- Account takeover — Session and token manipulation attacks
- API abuse — Rate limiting bypasses and resource exhaustion
- Injection — SQL, NoSQL, and command injection through API parameters
AI agent and MCP security
Salt added agentic AI security capabilities in 2025, announced at CrowdStrike Fal.Con. Their own research shows only 37% of organizations using agentic AI currently deploy dedicated API security, while 48% operate 6-20 different agent types.
Three components cover the MCP lifecycle:
- MCP Protect — Discovers and monitors all MCP server interactions with AI agents in runtime, maps hidden connections, and assesses data exposure risk
- Agentic AI Governance — Out-of-the-box security controls enforcing safe AI agent behavior in MCP and A2A environments, enabled by default at first login
- GitHub Connect — Identifies risky MCP servers in source code repositories before they deploy to production
As Michael Nicosia, co-founder and COO, put it: “Most organizations’ first AI security gap isn’t model jailbreaks — it’s the invisible API connections powering agents.”
Sensitive data tracking
Salt identifies PII, PHI, payment card data, and custom data patterns flowing through API traffic in real time. The posture engine flags exposed sensitive data in query parameters, unauthenticated responses, and unencrypted channels.
What does Salt Security integrate with?
Salt connects to API gateways, cloud platforms, SIEM/SOAR tools, and developer platforms:
How do I get started with Salt Security?
Salt also offers a free external attack surface scan through their website, giving you an adversary-perspective view of public-facing APIs before committing to the platform.
When to use Salt Security
Salt fits organizations that need to find and protect APIs they don’t fully know about — especially in environments with fast-moving development teams, multiple cloud accounts, or third-party integrations.
It’s a good fit if:
- You suspect your actual API count is larger than what your gateway or documentation shows
- You need compliance mapping across PCI DSS, HIPAA, GDPR, or SOC 2 for API traffic
- You’re adopting agentic AI and need visibility into MCP server interactions
- You want threat detection that catches logic-based attacks (BOLA, credential stuffing) rather than just signature matches
- You need an agentless deployment that doesn’t add latency or require architecture changes
Consider other options if:
- You primarily need pre-production API testing rather than runtime protection — tools like 42Crunch focus on API security testing in CI/CD
- You need a broader platform approach — Imperva API Security combines API protection with WAF, DDoS, and bot management under the Thales umbrella
- You’re looking for a free or open-source solution
- Your API estate is small and fully documented, making discovery less critical
If Salt’s runtime-only model isn’t a fit, see Salt Security alternatives for a deeper comparison across contract-first, WAF-bundled, and platform-extension peers.
How to use Salt Security
Salt’s deployment model assumes that no one wants to retrofit gateways or rewrite traffic paths just to evaluate a new platform. The onboarding sequence I have seen work cleanly looks like this:
- Deploy a passive traffic mirror to the Salt cloud. Salt Connect pulls metadata from AWS, Azure, GCP, Kong, Apigee, and MuleSoft without inline components, and the Sensor accepts mirrored traffic from VPC mirrors, F5, NGINX, or service mesh sidecars. No gateway changes are required.
- Let the Salt Illuminate engine learn the API behavioral baseline. The first inventory shows up within minutes, but the behavioral models that drive logic-attack detection typically need 30 days of representative traffic to stabilize, especially across slow business cycles like end-of-month batch jobs.
- Review the API inventory and risk score. Each discovered endpoint carries auth type, data classification (PII, PHI, payment data), environment, and ownership. This is the working set for the next two steps.
- Configure alerts and SOAR integration. Salt pushes incidents into Splunk, CrowdStrike, Microsoft Sentinel, Slack, Jira, and the wider SIEM/SOAR stack. Detection-only by default — Salt does not block inline — so the integration design has to specify which downstream system enforces.
- Tune behavioral detection thresholds against your traffic baseline. Salt’s models surface BOLA, credential stuffing, account takeover, and data exfiltration without code-level signals; the per-customer tuning step is what keeps false positives from drowning real incidents.
The buyer signal that consistently favors Salt is wanting behavioral runtime detection without re-architecting the request path.
How much does Salt Security cost?
Salt does not publish price lists for the Illuminate platform. The salt.security pricing page directs prospects to a contact-sales flow, and the company offers a free external attack surface scan through Salt Surface as a no-commit entry point ahead of the formal procurement cycle.
Three signals consistently move the quote: API call volume across the monitored estate, the deployment model (cloud SaaS vs hybrid SaaS with on-prem Sensors), and which Illuminate modules are in scope — Discovery and Posture together cover most starter deployments, while Threat Detection, MCP Protect, and Agentic AI Governance layer on for behavioral runtime and AI-agent coverage. Larger enterprise deployments tend to anchor an annual contract on a baseline traffic tier with overage terms negotiated separately. Onboarding usually closes in a 30–60 day procurement cycle for new buyers, and existing Salt customers typically renew at the same module mix unless the AI agent or compliance footprint expands.
What are alternatives to Salt Security?
Salt is the canonical behavioral-runtime API security platform, so the closest alternatives split by which trade-off you want to make against that model.
- 42Crunch takes the contract-first stance. Every check ties back to the OpenAPI spec and a runtime micro API firewall enforces the same contract in production, which makes it the obvious pick when the security model has to live and die with the spec rather than with traffic baselines. See the dedicated Salt Security vs 42Crunch comparison for the head-to-head detail.
- Akamai API Security , formerly Noname Security before the June 2024 acquisition, offers behavioral runtime plus Akamai’s edge integration. Pick it when multi-CDN coverage or an existing Akamai relationship matters more than Salt’s pure-play independence.
- Wallarm bundles WAAP heritage with developer-focused API discovery and runtime detection. It suits product engineering teams who want the same tool to handle the WAF replacement decision and the API security purchase in one cycle.
- Imperva API Security extends an established WAF platform with discovery and runtime checks; the Imperva API vs Salt Security comparison covers the WAF-extension-vs-pure-play trade-off in depth.
- Cequence leads with a unified API protection platform tuned for bot abuse and business-logic attacks, with native inline blocking that Salt’s detection-only model does not provide.
For a deeper-dive comparison across all of Salt’s peers, see Salt Security alternatives .