A software supply chain attack targets the components, dependencies, and build processes that make up modern applications rather than the application itself.
Attackers inject malicious code into open source packages, compromise build pipelines, or exploit trust relationships between vendors and customers. With 97% of commercial codebases containing open source components and 9.8 trillion package downloads in 2025 alone, the attack surface is enormous.
I collected data from 14 industry reports and surveys (Sonatype, Black Duck, JFrog, Verizon, Snyk, Checkmarx, and others) published between 2024 and 2026. Every statistic links to its source.
For related data on software vulnerabilities broadly, see my Software Vulnerability Statistics page. For DevSecOps adoption and pipeline security, see DevSecOps Statistics .
Key statistics at a glance#
Malicious packages#
Malicious packages in open source registries are growing faster than most security teams can track.
How many malicious open source packages exist?#
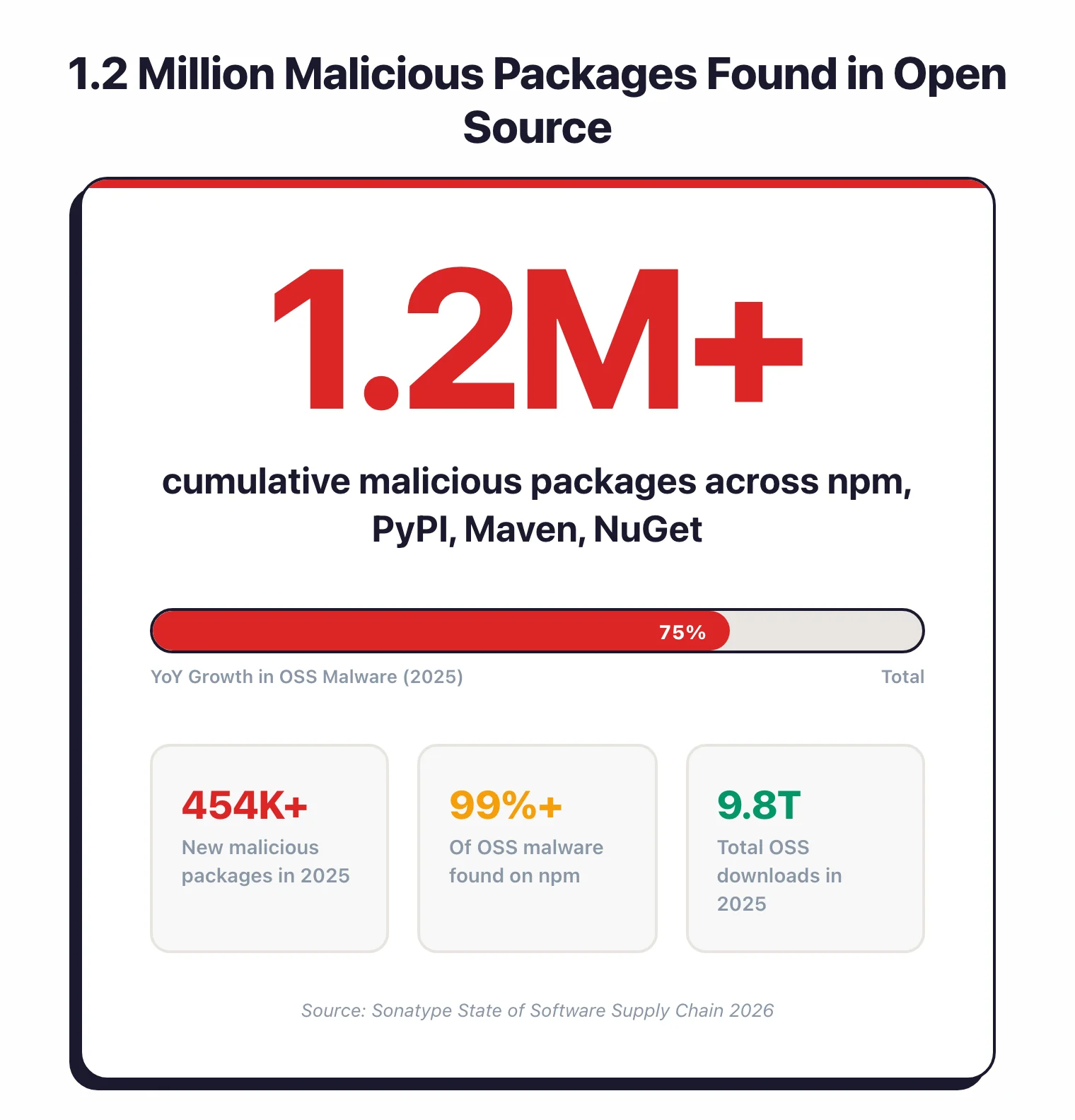
- Sonatype has identified over 1.233 million cumulative malicious packages across npm, PyPI, Maven, NuGet, and Hugging Face as of 2025 — Sonatype 2026
- 454,600+ new malicious packages were discovered in 2025 alone, a 75% year-over-year increase — Sonatype 2026
- The prior year saw 512,847 malicious packages, a 156% YoY increase at the time — Sonatype 2024
- ReversingLabs reported a 1,300% increase in malicious threats in open source repositories between 2020 and 2023 — ReversingLabs 2024
Where does the malware live?#
- Over 99% of open source malware occurs on npm — Sonatype 2026
- Repository abuse (spam, squatting, typosquatting) shows up in 55.9% of all logged malicious packages — Sonatype 2026
- 17% of malicious packages pose critical security risks; nearly half are categorized as “potentially unwanted applications” — Sonatype 2024
- 20% of Docker Hub’s 15 million repositories were used to spread malware in 2024 — Infosecurity Magazine 2024
- JFrog detected 25,229 exposed secrets/tokens in public registries, up 64% YoY, with 27% still active — JFrog 2025
The Log4j problem still isn’t solved#
- 13% of Log4j downloads in 2025 were still vulnerable — roughly 40 million vulnerable downloads out of 300 million total, four years after patches became available — Sonatype/Infosecurity 2026
- 95% of vulnerable component downloads already had a fix available; only 0.5% had no fixed version — Sonatype 2024
Open source dependency risk#
Open source usage keeps growing, and the risk grows with it.
How exposed are commercial codebases?#
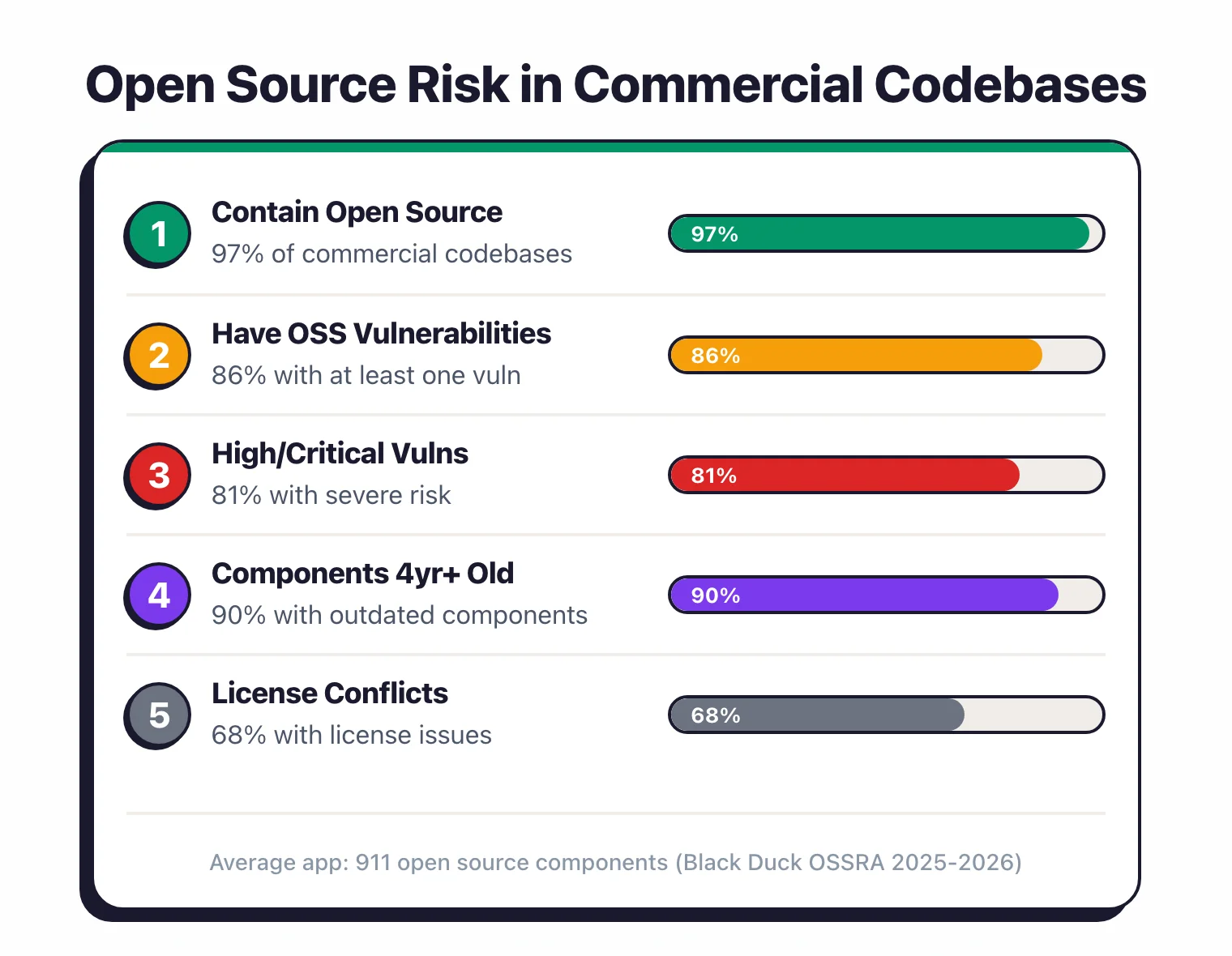
- 97% of commercial codebases contain open source components — Black Duck OSSRA 2025
- 86% of codebases contain open source vulnerabilities; 81% have at least one high- or critical-risk vulnerability — Black Duck OSSRA 2025
- The average application contains 911 open source components; open source files per app tripled from 5,386 (2020) to 16,082 (2024) — Black Duck OSSRA 2025
- Mean vulnerabilities per codebase jumped 107% to 581 in the 2026 OSSRA — Black Duck OSSRA 2026
- 90% of audited codebases had components more than 4 years out of date — Black Duck OSSRA 2025
- 80% of application dependencies remain un-updated for over a year — Sonatype 2024
License and ecosystem risk#
- 68% of codebases contain license conflicts — the highest in OSSRA history, up 12 points from 56% — Black Duck OSSRA 2026
- 95% of vulnerabilities are found in transitive (indirect) dependencies, not the direct ones developers explicitly install — Endor Labs 2025
- Only 77% of dependencies are identifiable via package manager; the remaining ~23% come through other means including AI coding assistants — Black Duck OSSRA 2025
- 70-90% of a typical codebase consists of third-party open source packages — Socket.dev 2025
The ecosystem is massive#
- 9.8 trillion open source downloads in 2025 across the four largest registries, 67% YoY growth — Sonatype 2026
- npm alone: 4.8 million projects, 4.5 trillion annual requests (70% YoY growth); PyPI: 635,000 projects, 530 billion requests (31% growth) — Sonatype 2024
For tools that detect open source risk, see my SCA tools comparison . For background on what SCA does, see What is SCA? .
Attack growth and notable incidents#
Supply chain attacks used to make headlines individually. Now they’re a steady background drumbeat.
How often do supply chain attacks happen?#
- Since April 2025, supply chain attacks average 28+ per month, more than double the 13/month seen from early 2024 to March 2025 — Comparitech 2025
- In 2024, 183,000 customers were affected by supply chain attacks, 33% more than in 2023 — Comparitech/Global Security Mag
- 63% of organizations fell victim to a software supply chain attack in the past two years; 100% of large enterprises reported at least one — Checkmarx 2024
- Gartner predicted 45% of organizations would experience supply chain attacks by 2025; the actual number hit 75% — BlackBerry/Gartner
Notable incidents (2024–2025)#
- XZ Utils backdoor (CVE-2024-3094): CVSS 10.0, a 2-year social engineering campaign compromised a critical Linux compression library. Caught by a developer who noticed a 500ms SSH slowdown — JFrog 2024
- Polyfill.io: over 380,000 hosts embedded the malicious script; 100,000+ websites directly affected, including Warner Bros, Hulu, Mercedes-Benz, and the World Economic Forum — The Hacker News 2024
- tj-actions/changed-files (March 2025): 23,000 repositories affected, exposing CI/CD secrets including AWS keys, GitHub PATs, and npm tokens — Wiz 2025
- CrowdStrike Falcon update (July 2024): not an attack but a supply chain failure — affected 8.5 million systems with estimated losses exceeding $5 billion — CSA 2025
- Shai-Hulud worm: 500+ npm packages infected, 25,000 malicious GitHub repositories created across 350 user accounts — Arctic Wolf 2025
Third-party breaches#
When your vendor gets breached, you inherit the consequences. This is happening more often.
- Third-party involvement in breaches doubled to 30% in 2025, up from 15% the prior year — Verizon DBIR 2025
- Edge device and VPN exploitation surged eightfold (from 3% to 22% of exploit-based breaches); only 54% of affected devices were patched — Verizon DBIR 2025
- Only 24% of organizations feel confident in the security of their direct dependencies — Snyk 2024
- Fewer than 25% of organizations perform regular audits of their software supply chain — Snyk 2024
- 52% of teams fail to meet vulnerability SLA deadlines; 74% set unrealistic SLAs of a week or less — Snyk 2024
Cost of supply chain attacks#
Supply chain breaches take longer to find and cost more to fix than direct attacks.

- Global cost of supply chain attacks: $46 billion (2023) → $60 billion (2025) → projected $138 billion by 2031 at 15% annual growth — Cybersecurity Ventures
- Average data breach cost: $4.44 million globally (down 9% from $4.88M in 2024 — first decline in five years), $10.22 million in the US (record high) — IBM 2025
- Supply chain attacks cost roughly 17x more to remediate than direct (first-party) breaches — SOCRadar 2025
- Average 267 days to detect and contain a supply chain breach — the longest of any attack vector — IBM Cost of Data Breach 2025
SBOM adoption#
Software Bills of Materials are the inventory lists that make supply chain risk visible. Adoption is growing, though the regulatory picture recently got complicated.
- Nearly 50% of organizations were using SBOMs by 2024, with 78% planning to increase usage — Anchore 2024
- Gartner predicted 60% of organizations building critical infrastructure would mandate SBOMs by 2025, up from less than 20% in 2022 — Gartner
- SBOM daily publication rate tripled from ~68/day (March 2022) to ~200/day (June 2024) — Sonatype 2024
- Federal policy shift: OMB M-26-05 made SBOMs discretionary (not mandatory) for US federal agencies, reversing Biden-era mandates — DWT 2026
AI and dependency risk#
AI coding assistants add a new wrinkle to supply chain risk. They suggest dependencies that may not exist, may be outdated, or may contain known vulnerabilities.
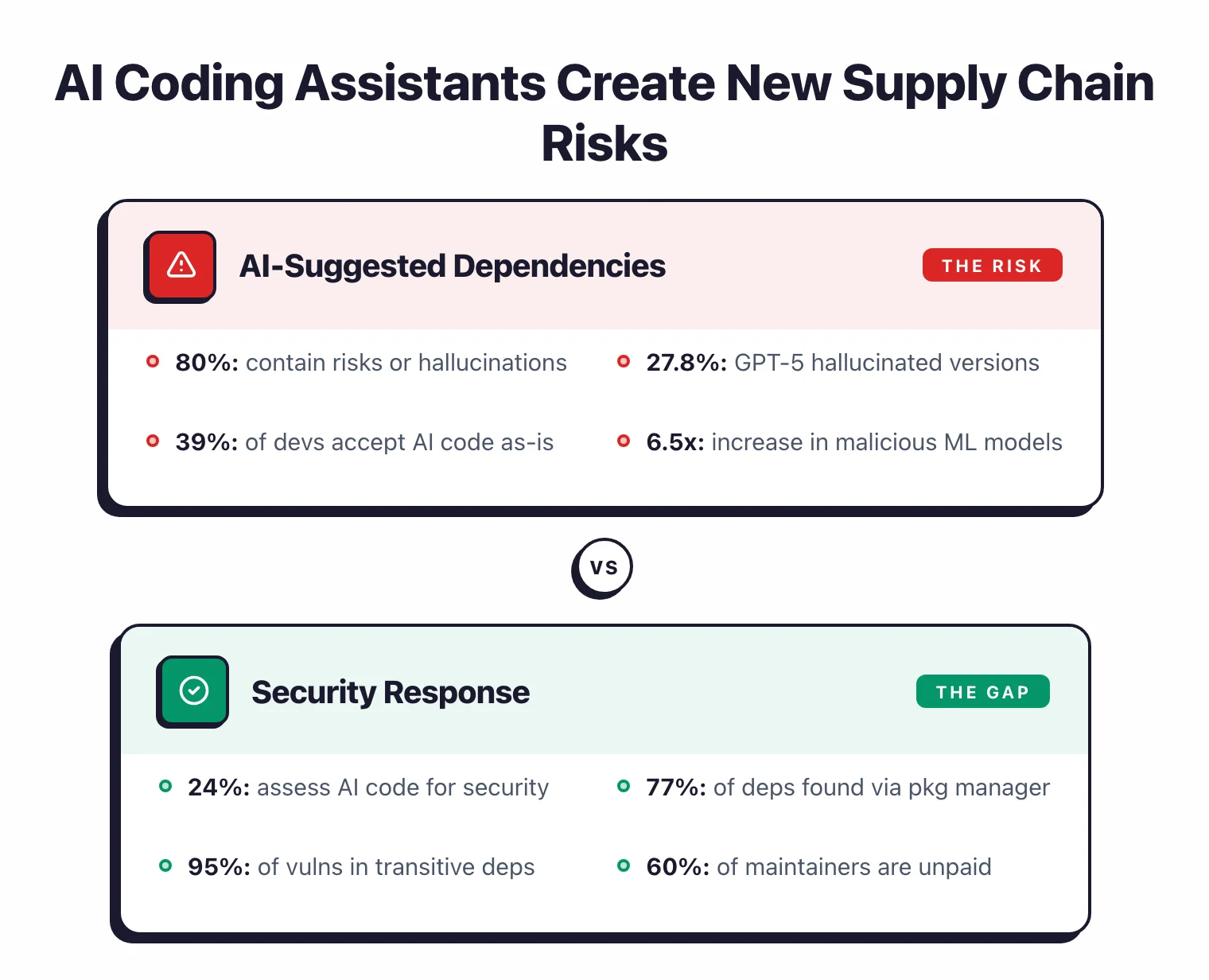
- Only 1 in 5 (20%) AI-suggested dependency versions were safe to use; 80% contained risks from hallucinations or known vulnerabilities — Endor Labs 2025
- GPT-5 hallucinated 27.8% of component version recommendations and suggested actual malware packages — Sonatype 2026
- 39% of developers accept AI-generated code without any revision — IDC/Sonatype 2026
- Only 24% of organizations perform thorough IP, license, security, and quality assessments of AI-generated code — Black Duck OSSRA 2026
- JFrog detected a 6.5x increase in malicious ML models on Hugging Face, where 1 million+ new models/datasets were added in 2024 — JFrog 2025
The maintainer problem#
Open source security depends on the people who maintain packages, and most of them do it for free.
- 60% of open source maintainers are unpaid; 61% of unpaid maintainers work alone — Socket.dev/Tidelift 2025
- 60% of maintainers have quit or considered quitting their projects — Socket.dev/Tidelift 2025
- 70%+ of developers download packages directly from public registries without central control — JFrog 2025
Market and tooling#
The SCA market is growing fast. Everyone wants better visibility into their dependencies.
- The SCA market was valued at $585 million in 2024 and is projected to reach $3.3 billion by 2033 at a 21.2% CAGR — SkyQuest
- The broader software supply chain security market is projected at $2.16 billion in 2025 — Custom Market Insights
- By 2028, 85% of large enterprise software engineering teams will have deployed supply chain security tools, up from 60% in 2025 — Gartner 2025
- Only 43% of IT professionals apply security scans at both code and binary levels, down from 56% in 2023 — a concerning decline — JFrog 2025
- An 11.3% drop in security tool adoption and 17.8% drop in training investment from 2023 — Snyk 2024
My own research#
I evaluated 100+ open-source security tools in early 2026 and found several data points relevant to supply chain security.
Open source AppSec tool health#
I scored tools using a composite health metric (stars, contributors, release frequency, issue response time, downloads). Among SCA tools , Trivy and Grype scored highest for community health, while several niche tools showed signs of abandonment — single maintainer, months between releases, growing issue backlogs. Full findings: State of Open Source AppSec Tools 2026 .
AI-generated code and dependencies#
In my AI-Generated Code Security Study 2026 , I tested 522 code samples from six LLMs. While the study focused on vulnerability rates (25.7% overall), the dependency patterns in AI-generated code deserve scrutiny given Endor Labs’ finding that 80% of AI-suggested dependencies contain risks.
Sources & methodology#
Every number on this page links to a published report, survey, or vendor study. If I cannot trace a statistic to a primary source, I do not include it.
Primary industry reports:
- Sonatype State of the Software Supply Chain 2024 — tracking of 7 million+ open source projects
- Sonatype Open Source Malware Index 2026 — cumulative malicious package tracking
- Black Duck OSSRA Report 2025 — audit of 1,000+ commercial codebases
- Black Duck OSSRA Report 2026 — updated vulnerability and license data
- JFrog Software Supply Chain Report 2025 — CVE trends, secret exposure, ML model risks
- Verizon 2025 DBIR — 22,052 incidents including 12,195 confirmed breaches
- Snyk State of Open Source Security 2024 — developer survey on dependency management
- Checkmarx Supply Chain Security Survey 2024 — 1,504 security professionals surveyed
- Endor Labs State of Dependency Management 2025 — transitive dependency risk analysis
- ReversingLabs Software Supply Chain Report 2024 — malware growth trends
- Anchore 2024 SBOM Survey — SBOM adoption metrics
Cost and market data:
- Cybersecurity Ventures Supply Chain Projections — global cost estimates
- SOCRadar Hidden Cost of Supply Chain Breaches 2025 — remediation costs and detection time
- SkyQuest SCA Market Report — market sizing and growth projections
Original research (AppSec Santa):
- State of Open Source AppSec Tools 2026 — 100+ tools evaluated across 10 categories
- AI-Generated Code Security Study 2026 — 522 code samples, dependency patterns
