API security is the discipline of protecting application programming interfaces from unauthorized access, data leaks, and abuse. APIs now handle roughly 83% of web traffic and are the primary way applications communicate — which also makes them the primary way attackers get in.
In 2025, 17% of all published security bulletins were API-related, making APIs one of the largest single vulnerability surfaces in modern software.
I collected data from 10 industry reports and surveys (Salt Security, Wallarm, OWASP, Verizon, Akamai, and others) published in 2024–2026. Every statistic links to its source.
For related data on broader vulnerability trends, see my Software Vulnerability Statistics page. For third-party and supply chain risk, see Supply Chain Attack Statistics.
Key statistics at a glance
API attack landscape
APIs have become the preferred attack surface. Most API vulnerabilities are trivial to exploit, and attackers know it.

How common are API security issues?
- 99% of organizations encountered API security problems in the past 12 months — Salt Security Q1 2025
- 34% of these issues involved sensitive data exposure or a privacy incident — Salt Security 2025
- 55% of organizations slowed the rollout of a new application due to API security concerns — Salt Security 2025
- 95% of API attacks in the past 12 months originated from authenticated sources — Salt Security 2025
- 98% of attack attempts targeted external-facing APIs — Salt Security 2025
How exploitable are API vulnerabilities?
- 43% of all additions to CISA’s Known Exploited Vulnerabilities catalog in 2025 were API-related — Wallarm 2025
- 97% of API vulnerabilities can be exploited with a single request — Wallarm 2025
- 98% of API vulnerabilities are classified as either easy or trivial to exploit — Wallarm 2025
- 59% of API vulnerabilities require no authentication at all — Wallarm 2026
- APIs accounted for 11,053 of 67,058 published security bulletins in 2025 (17% of all reported vulnerabilities) — Wallarm 2026
- Akamai reported a 32% uptick in API attacks exploiting OWASP API Security Top 10 risks — Akamai
- Average daily API attacks per organization rose 113% YoY (from 121 to 258 attacks) — Akamai SOTI 2026
- Over 40,000 API incidents recorded in H1 2025, averaging 220+ per day — Imperva/Thales 2025
- Behavior-based attacks (unauthorized workflows) accounted for 61% of API attacks in 2025, up from 30% in 2024 — Akamai SOTI 2026
OWASP API Top 10 in practice
The OWASP API Security Top 10 (2023 edition) lists the most critical API vulnerability categories. Wallarm’s breach analysis shows which ones actually get exploited.
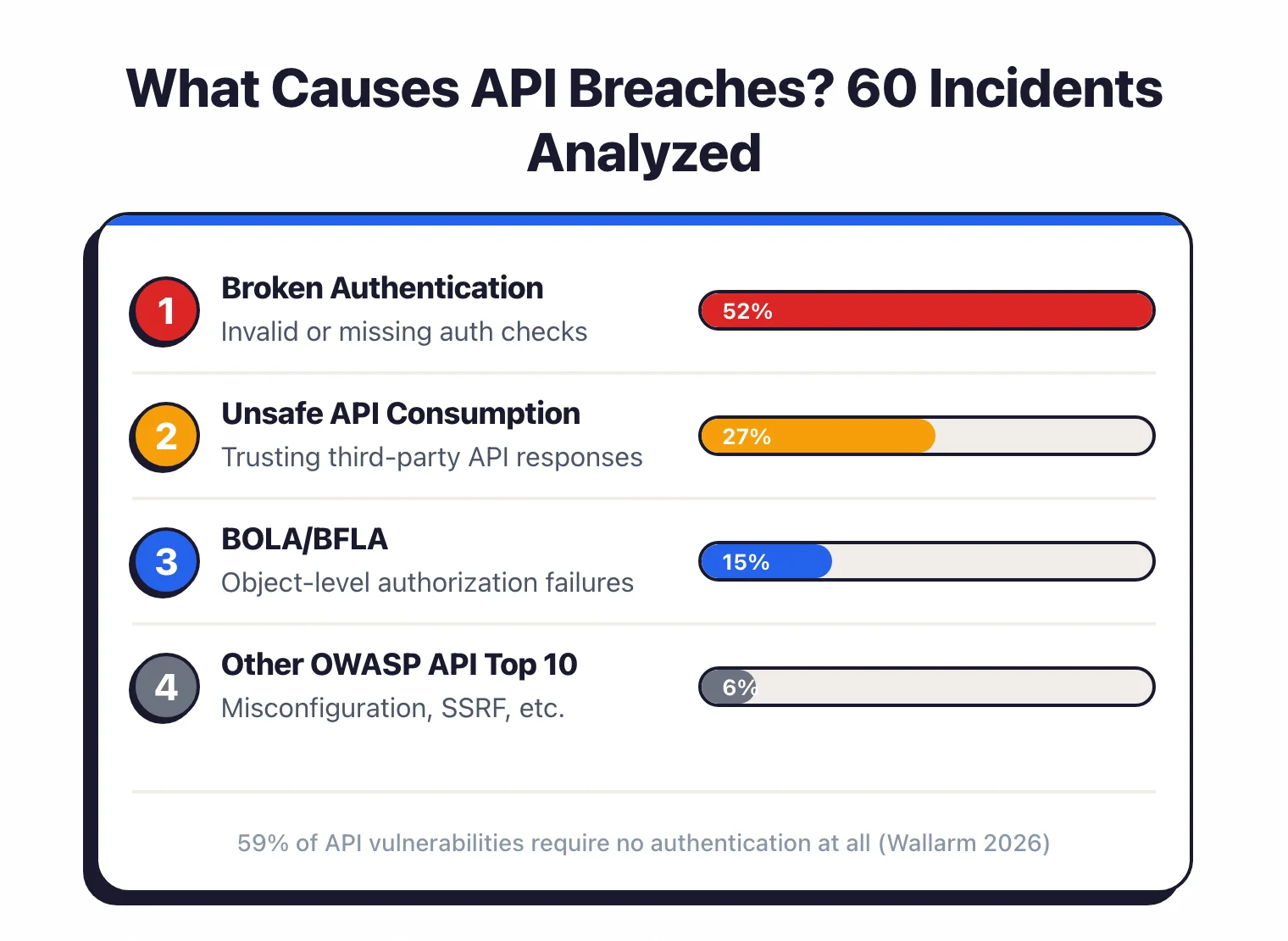
What causes API breaches?
- Broken authentication caused 52% of 60 API breaches analyzed in 2025 — Wallarm 2026
- Unsafe consumption of APIs accounted for 27% of breaches — Wallarm 2026
- BOLA (Broken Object Level Authorization) and BFLA (Broken Function Level Authorization) account for hundreds of API vulnerabilities every quarter — Wallarm 2025
- Breaches clustered by sector: Software (15%), AI platforms (15%), cybersecurity vendors (13%), SaaS (8%), automotive (7%), cloud services (7%) — Wallarm 2026
OWASP API Top 10 (2023 edition)
- API1:2023 — Broken Object Level Authorization (BOLA)
- API2:2023 — Broken Authentication
- API3:2023 — Broken Object Property Level Authorization
- API4:2023 — Unrestricted Resource Consumption
- API5:2023 — Broken Function Level Authorization (BFLA)
- API6:2023 — Unrestricted Access to Sensitive Business Flows
- API7:2023 — Server Side Request Forgery (SSRF)
- API8:2023 — Security Misconfiguration
- API9:2023 — Improper Inventory Management
- API10:2023 — Unsafe Consumption of APIs
Source: OWASP API Security Top 10 2023
Shadow and zombie APIs
You can’t secure what you don’t know about. And most organizations don’t know about a third of their APIs.
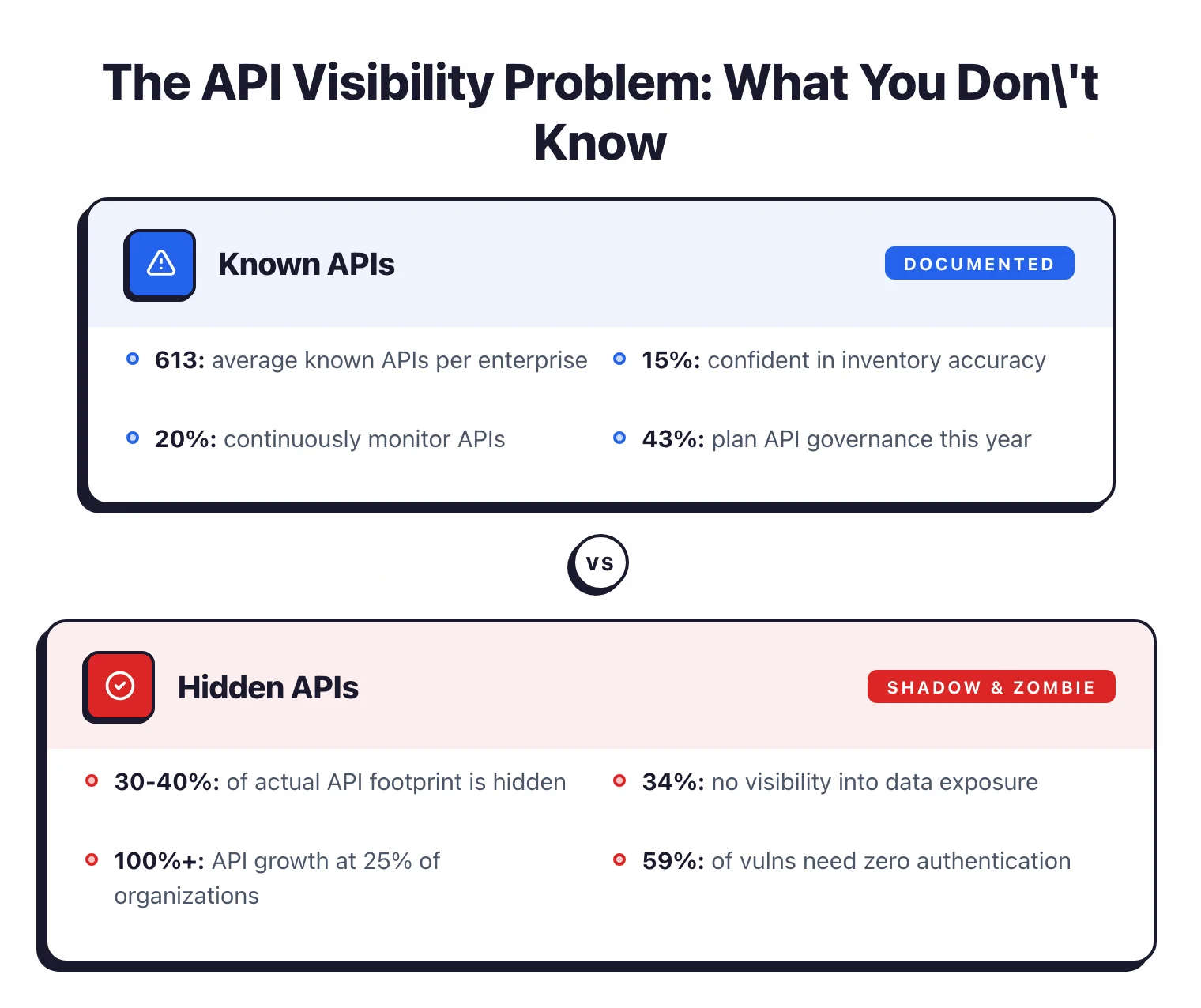
- Security audits show 30-40% of an organization’s actual API footprint consists of shadow APIs (undocumented) or zombie APIs (deprecated but still active) — AppSentinels 2025
- Only 15% of organizations expressed strong confidence in the accuracy of their API inventories — Salt Security 2025
- 34% of organizations lack visibility into sensitive data exposure through APIs — Salt Security 2025
- Only 20% have measures in place to continuously monitor APIs — Salt Security 2025
- 68% of organizations had shadow APIs they did not know about — Enterprise Management Associates/Salt
- Only 6% of organizations have advanced API security programs — Salt Security 2025
- One quarter of organizations experienced API growth exceeding 100% in the past year — Salt Security 2025
API breaches and cost
API breaches hit some of the biggest companies and exposed millions of records. The costs add up fast.
Recent API breaches
- Dell (2024): attackers accessed 49 million customer records through an API vulnerability due to missing authorization checks — CybelAngel 2024
- T-Mobile (2023): API breach impacted 37 million users, with remediation costs estimated around the multi-million-dollar industry average for breaches of that scale — Industry Analysis
- Third-party API exposure at 700Credit exposed millions of records; weak API authentication at Qantas airlines fueled mass unauthorized access — Wallarm 2026
Business impact
- APIs account for approximately 83% of web traffic — Akamai/Industry
- The estimated annual cost of vulnerable API interfaces and bot activity reaches $186 billion — Mordor Intelligence
- 57% of organizations suffered an API-related data breach in the past two years, with 73% of those experiencing three or more incidents — Traceable 2025
- 1 in 5 API security incidents cost over $500,000 — Kong 2025
- Third-party involvement in breaches doubled to 30% in 2025 — Verizon DBIR 2025
AI and API security
The intersection of AI and APIs is creating new attack surfaces. AI agents communicate through APIs, and AI-related vulnerabilities are overwhelmingly API-based.
98.9% of AI-related vulnerabilities are API-related — Wallarm 2025
Salt Security reports 1/3 of respondents lack confidence in detecting AI-driven API threats — Salt Security 2025
47% of respondents expressed concerns about securing AI-generated code that creates APIs — Salt Security 2025
Of 7,000+ MCP servers analyzed, 36.7% were vulnerable to SSRF — an API-level vulnerability — Wallarm 2026
AI vulnerabilities grew 398% YoY (from 439 to 2,185), with 36% involving APIs — Wallarm 2026
62% of organizations adopted GenAI in API development; 65% believe it poses serious API security risk — Salt Security H2 2025, Traceable 2025
For more on AI-specific risks, see my AI Security Statistics page.
API security testing
Most organizations know API security is a problem. Fewer are actually testing.
- 43% of organizations plan to implement API Posture Governance within 12 months — Salt Security 2025
- Only 20% of organizations continuously monitor their APIs for security issues — Salt Security 2025
- Traditional authentication-based defenses are insufficient — 95% of API attacks come from authenticated users — Salt Security 2025
For tools that test API security, see my API Security Tools comparison.
Market and predictions
API security is one of the fastest-growing segments in cybersecurity, driven by both the API explosion and the attack growth that follows it.
- API security market valued at $1.32 billion in 2025, projected to reach $4.60 billion by 2030 at 28.5% CAGR — Mordor Intelligence
- API attacks increased 109% year-over-year — Mordor Intelligence
- The average enterprise manages approximately 613 known APIs, but the real count is 30-40% higher when shadow APIs are included — Industry Audits 2025
My own research
While I haven’t run an API-specific security study, several of my original research projects touch on API security.
Security headers and API endpoints
In my Security Headers Adoption Study 2026, I scanned 10,000 websites and found that many API-serving domains lack basic security headers. Only 27.3% deploy Content-Security-Policy, and CORS misconfigurations remain common — both directly relevant to API security posture.
Open source API security tools
In my State of Open Source AppSec Tools 2026, I evaluated API security tools including ZAP, Nuclei, and others. The API security category showed strong open-source tool health but lower adoption compared to SAST and SCA tools.
Sources & methodology
Every number on this page links to a published report or vendor study. If I cannot trace a statistic to a primary source, I do not include it.
Industry reports:
- Salt Security State of API Security Q1 2025 — survey of API security practitioners across industries
- Salt Security State of API Security 2H 2025 — follow-up report with AI agent security focus
- Wallarm Annual API ThreatStats Report 2025 — analysis of API vulnerabilities and CISA KEV data
- Wallarm API ThreatStats Report 2026 — 60 API breach analysis with OWASP mapping
- OWASP API Security Top 10 2023 — definitive API vulnerability taxonomy
- Verizon 2025 DBIR — 22,052 incidents, third-party breach data
- Akamai State of the Internet — API attack traffic analysis
Market data:
- Mordor Intelligence API Security Market Report — market sizing through 2030
Original research (AppSec Santa):
- Security Headers Adoption Study 2026 — 10,000 websites, header adoption data
- State of Open Source AppSec Tools 2026 — 100+ tools evaluated including API security category
