radare2 (r2) is a free, open-source reverse engineering framework for disassembling, debugging, and analyzing binaries across 60+ CPU architectures. With 23,300+ GitHub stars, it is the most architecturally versatile open-source binary analysis tool available.
Created by pancake (Sergi Alvarez) in 2006, radare2 follows a UNIX philosophy: small, composable command-line tools instead of a monolithic application. This design makes r2 particularly good for scripting, automation, and fitting into analysis workflows where GUI tools like Ghidra add unnecessary overhead.
GitHub: radareorg/radare2 | Stars: 23.2k | Latest Release: v6.1.0 (February 2026) | License: LGPL-3.0
The main difference between radare2 and Ghidra is the interface philosophy. Ghidra is the go-to for GUI-based reverse engineering with its built-in decompiler. radare2 lives in the terminal: quick analysis, scriptable automation via r2pipe, native debugging, and lightweight enough to run on constrained environments including Android and iOS devices themselves.
In mobile security, radare2 fills an important gap: it analyzes native libraries (.so and Mach-O files) that Java/Kotlin decompilers like Jadx and resource tools like Apktool cannot touch.
| Feature | Details |
|---|---|
| Architectures | 60+ ISAs (x86, ARM, MIPS, RISC-V, PowerPC, SPARC, AVR, 6502, Z80, and more) |
| Binary formats | ELF, PE, Mach-O, DEX, COFF, raw blobs, firmware images, disk dumps |
| Scripting | r2pipe bindings for Python, JavaScript, Go, Rust, Ruby |
| Debugging | Local and remote via GDB, WinDbg, QNX, Frida (r2frida plugin) |
| Emulation | ESIL intermediate language for safe code analysis without execution |
| GUI | iaito (Qt-based, optional) with graph views, hex editor, decompiler panels |
| Toolsuite | r2, rabin2, rasm2, radiff2, rahash2, rafind2 |
| Latest release | v6.1.0 (February 2026), 346 commits from 24 contributors |
| Platforms | Linux, macOS, Windows, Android, iOS, FreeBSD, WebAssembly |
| License | LGPL-3.0 (fully open source, no commercial tiers) |
Overview
radare2 is not a single tool but a suite of utilities built around a shared library (libr):
- r2 — The main binary analysis shell. Opens files, runs analysis, disassembles, debugs, and patches.
- rabin2 — Binary format inspector. Extracts metadata, imports, exports, strings, and sections from ELF, PE, Mach-O, DEX, and other formats.
- rasm2 — Assembler and disassembler. Converts between assembly and machine code for any supported architecture.
- radiff2 — Binary diffing tool. Compares two binaries at the byte, function, or graph level.
- rahash2 — Hashing utility. Computes checksums and cryptographic hashes of files or memory regions.
- rafind2 — Pattern search tool. Finds byte sequences, strings, and patterns across binaries.
Each tool works independently or in combination. This modularity means you can use rabin2 to extract strings from 500 APK native libraries in a batch script without loading the full analysis engine, or pipe rasm2 output into other tools in a forensics pipeline.
The analysis engine performs automatic function detection, cross-reference tracking, type propagation, and control flow graph construction. The ESIL (Evaluable Strings Intermediate Language) virtual machine enables code emulation without executing the actual binary, which is valuable for analyzing malware or obfuscated code safely.
Key Features
Multi-Architecture Support
radare2 supports over 60 instruction set architectures — more than any other open-source reverse engineering tool. This coverage comes through built-in plugins and the Capstone disassembly framework:
- x86/x86-64 — Intel and AMD processors
- ARM/ARM64 — Including Thumb mode for mobile processors
- MIPS — 32-bit and 64-bit variants with DSP extension handling
- RISC-V — Modern open-source ISA designs
- PowerPC — Embedded and server systems
- SPARC — Legacy Unix workstations
- AVR — Microcontrollers and IoT devices
- 6502, Z80, 8051 — Retro and embedded platforms
This breadth is why r2 shows up in firmware analysis, IoT security research, and cross-architecture vulnerability hunting. One tool handles ARM Android libraries, MIPS router firmware, and x86 desktop binaries.
Architecture Coverage: radare2's 60+ ISA support comes from a combination of built-in plugins and the Capstone disassembly framework. No other open-source tool matches this breadth — Ghidra supports around 20 processors out of the box.
Command-Line Interface
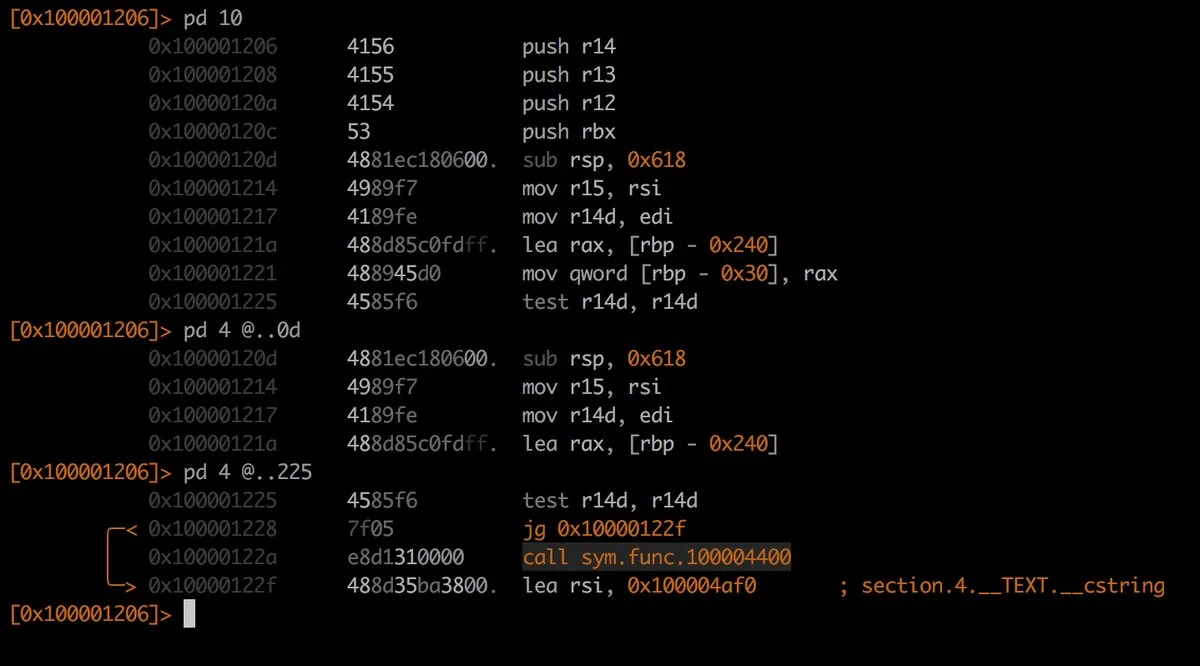
The r2 shell is capable but famously has a steep learning curve. Commands are terse — pd 20 disassembles 20 instructions, afl lists functions, s main seeks to the main function, VV enters visual graph mode.
Once internalized, this terseness becomes efficiency. Experienced analysts navigate binaries faster in r2 than clicking through GUI menus. The ? suffix on any command prints help (pd? shows disassembly options), and the ~ operator pipes output through an internal grep.
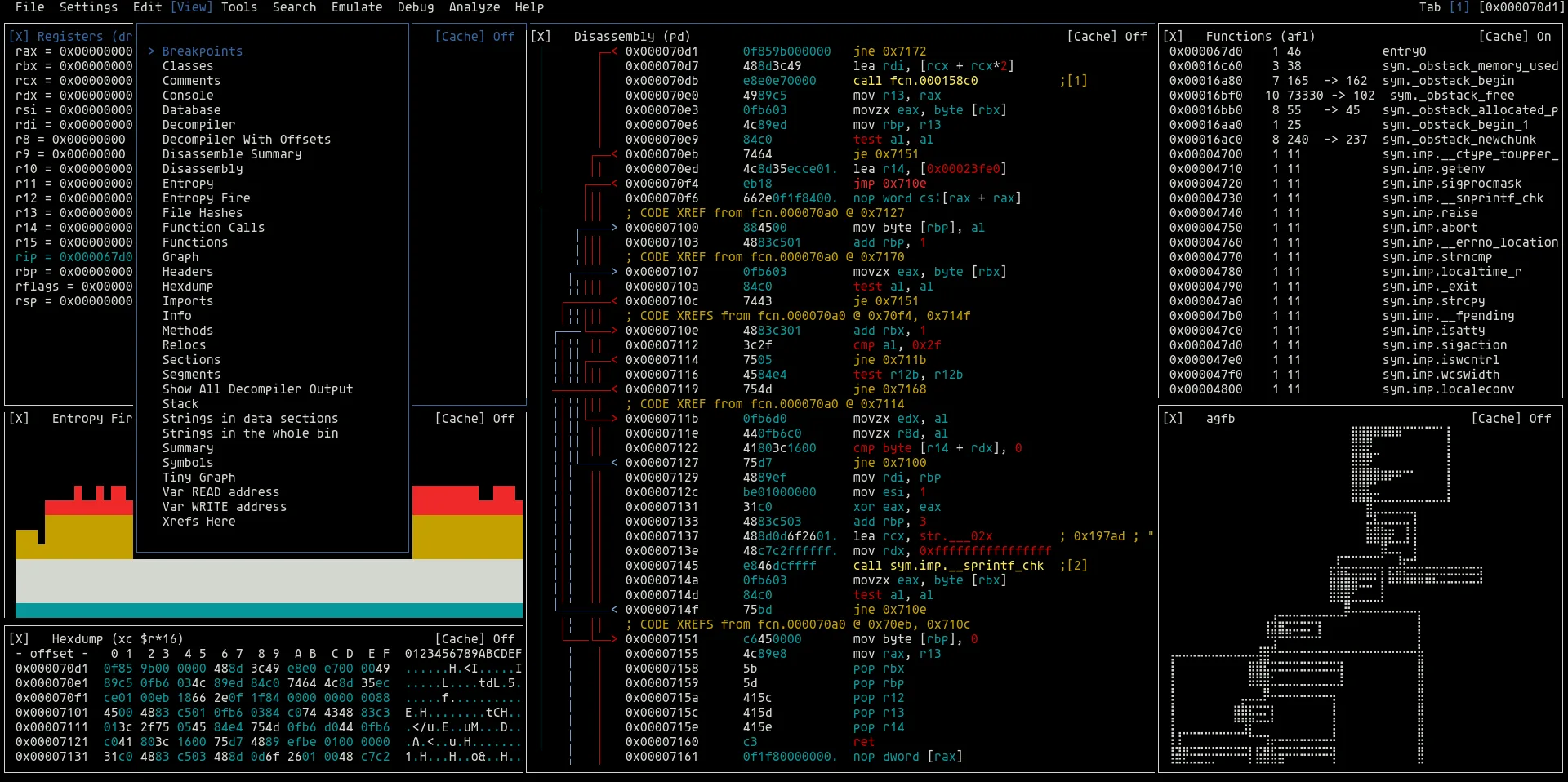
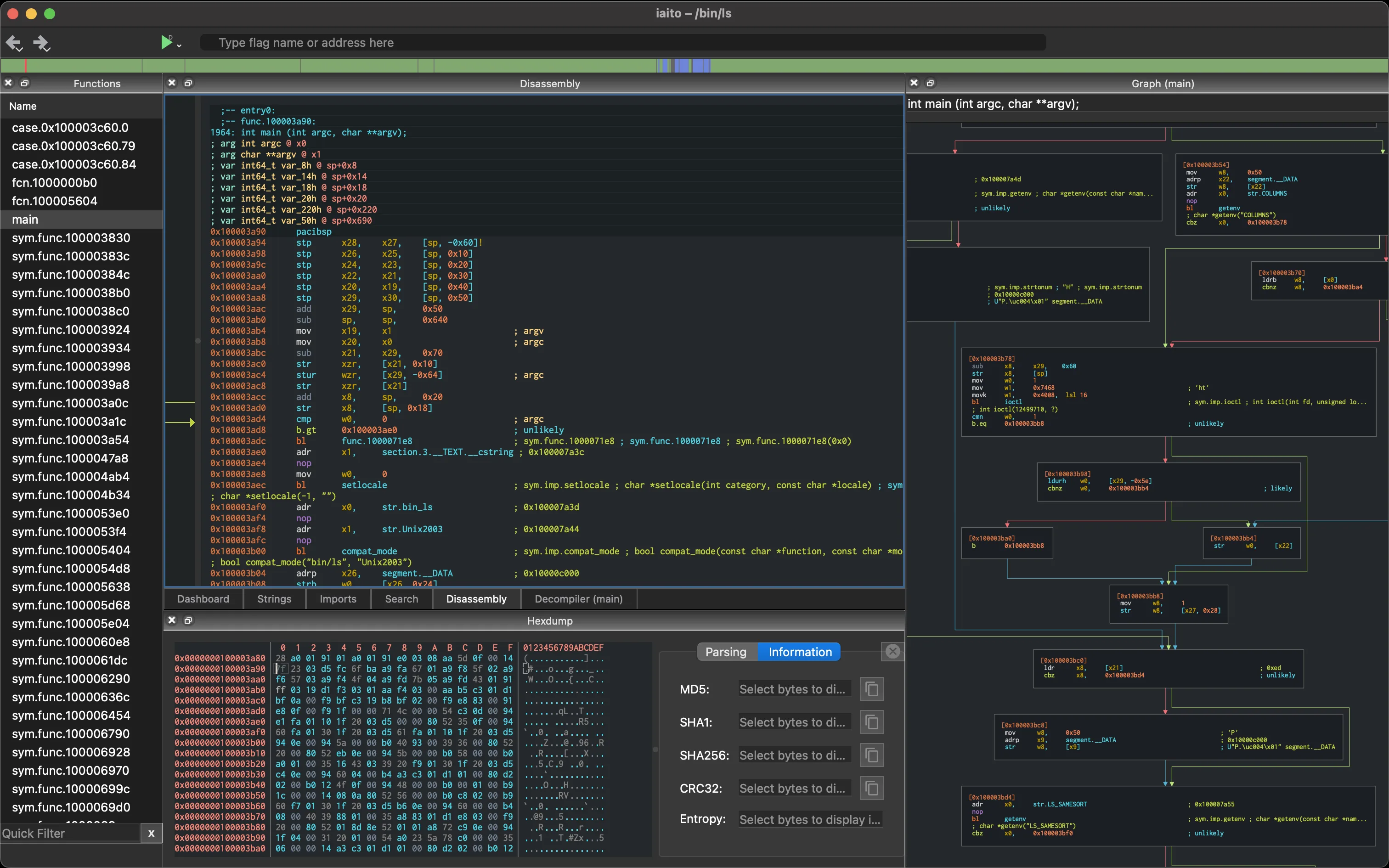
For those who prefer a graphical interface, iaito (the continuation of Cutter for radare2 after the Rizin fork in 2020) provides a Qt-based GUI with graph views, hex editor, decompiler panels, and an integrated r2 console. It delivers r2’s analysis engine through a visual interface without sacrificing access to the command line.
Scripting and Automation
r2pipe is what sets radare2 apart for automated analysis. Available for Python, JavaScript, Go, Rust, Ruby, and other languages, it opens a session to r2 and lets you run any command programmatically:
import r2pipe
r2 = r2pipe.open("target.so")
r2.cmd("aaa") # Full analysis
# List all functions
functions = r2.cmdj("aflj")
for func in functions:
print(f"{func['name']}: {func['size']} bytes at {hex(func['offset'])}")
# Find crypto-related strings
strings = r2.cmdj("izj")
crypto_strings = [s for s in strings if "AES" in s.get("string", "") or "RSA" in s.get("string", "")]
radare2’s r2pipe scriptability is why it keeps showing up in CTF competitions, automated vulnerability scanning pipelines, and binary analysis research where you need to process hundreds of samples programmatically.
Debugging
radare2 includes a native debugger that works locally and remotely. It supports breakpoints, watchpoints, register inspection, memory mapping, and step-by-step execution. Remote debugging works over GDB protocol, WinDbg, and QNX — and notably through Frida via the r2frida plugin.
The r2frida integration is especially useful for mobile security: connect r2 to a running Android or iOS process through Frida, then use r2’s analysis commands on live memory. You get Frida’s dynamic instrumentation plus r2’s disassembly in one session.
Binary Patching and Forensics
r2 can modify binaries directly — patch instructions, change jump targets, NOP out function calls, or modify data sections. Combined with its hex editor mode, this makes it a practical tool for binary patching during security research.
For forensics work, r2 handles disk images, memory dumps, and raw binary blobs. The rahash2 utility computes checksums for integrity verification, and rafind2 searches for byte patterns, strings, and file signatures across large datasets.
Use Cases
Mobile Native Library Analysis
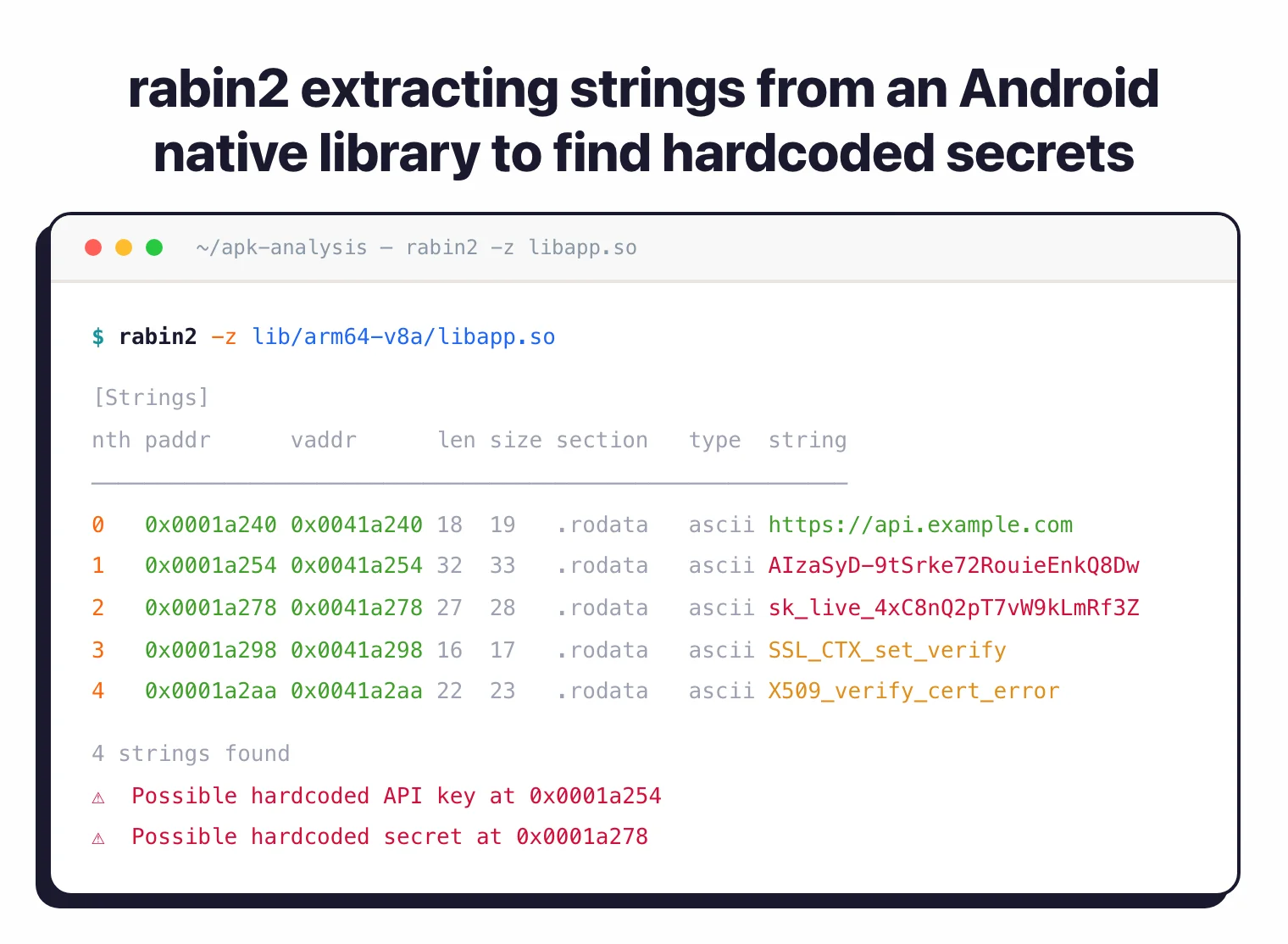
When a mobile app’s security-critical logic lives in native code (JNI libraries on Android, C/C++ code on iOS), Java-level tools are useless. I use r2 to analyze .so files extracted from APKs, looking at encryption implementations, certificate validation routines, anti-tampering checks, and hardcoded secrets in compiled native code.
The workflow typically pairs Jadx or Apktool for Java-layer analysis with r2 for native library deep-dives. The rabin2 -z command quickly extracts all strings from a native library, often revealing API endpoints, encryption keys, and debug messages.
CTF Competitions
radare2 is a staple in capture-the-flag competitions. Its disassembly, debugging, emulation, and scripting cover the range of challenges you hit in reverse engineering and binary exploitation categories. The ESIL emulator can solve simple crackme challenges automatically, and r2pipe scripts automate repetitive analysis across challenge variants.
Firmware and IoT Security
For embedded device security assessments, r2’s multi-architecture support matters. MIPS-based router firmware, ARM Cortex-M microcontroller code, even exotic architectures found in industrial control systems — they all disassemble in r2. The tool can open raw binary blobs, firmware images, and flash dumps without needing specific file format support.
Vulnerability Research
Binary diffing with radiff2 helps identify what changed between software versions — useful for analyzing security patches and finding the specific code changes that fix vulnerabilities. Combined with ESIL emulation for path exploration, r2 supports both patch analysis and independent vulnerability discovery.
Pricing
radare2 is completely free and open source under LGPL-3.0. The iaito GUI is also free under GPL. There are no commercial editions, paid features, or usage restrictions.
Strengths & Limitations
Strengths:
- Widest architecture support of any open-source RE framework (60+ ISAs)
- Best-in-class scriptability via r2pipe across multiple programming languages
- Lightweight — runs on everything from servers to Android phones and Raspberry Pis
- Integrated debugger with local, remote, and Frida-based debugging modes
- Active development — v6.1.0 released February 2026 with 346 commits
- ESIL emulation enables safe analysis of malicious or protected binaries
- Composable UNIX tools for batch processing and pipeline integration
- Strong CTF community with extensive tutorials and write-ups
Limitations:
- Steep learning curve — the command syntax is terse and takes time to internalize
- No built-in decompiler comparable to Ghidra’s built-in C decompiler — requires plugins like r2ghidra or r2dec
- Documentation can be inconsistent across features and versions
- iaito GUI is functional but less polished than Ghidra’s interface
- Single-developer origin means some subsystems are architecturally complex
- Initial analysis can be slower than Ghidra on very large binaries
Best for: radare2 is the right choice when you need scriptable, multi-architecture binary analysis from the command line — especially for mobile native libraries, firmware, CTF challenges, and automated analysis pipelines where GUI tools add unnecessary overhead.
Getting Started
git clone https://github.com/radareorg/radare2 && cd radare2 && sys/install.sh. On macOS: brew install radare2. On Kali Linux, it comes pre-installed. For the GUI, install iaito separately from github.com/radareorg/iaito.r2 -A target.so to open a binary with automatic analysis. The -A flag runs aaa (analyze all) on load. You will land in the r2 shell at the binary’s entry point.afl to list detected functions, s main to seek to main, pdf to print the disassembly of the current function, and VV to enter visual graph mode. Append ? to any command for help (e.g., pd?).pip install r2pipe. Write scripts that open binaries, run analysis commands, and parse JSON output for batch processing or integration into security testing pipelines.For mobile security workflows, combine radare2 with Jadx for Java decompilation, Apktool for resource analysis, Frida for runtime instrumentation (or use r2frida for direct integration), and Ghidra when you need a graphical decompiler view of complex native code.