Qodana is a SAST platform from JetBrains that brings 3,000+ IDE inspections into CI/CD pipelines. It runs the same analysis engines that power IntelliJ IDEA, PyCharm, WebStorm, and other JetBrains IDEs, supporting 60+ languages.
The platform covers code quality, security vulnerabilities, and technical debt tracking. A free Community tier is available, with paid plans starting at $6 per active contributor per month.
What is Qodana?
Qodana extends JetBrains IDE inspections beyond individual developer workstations into automated CI/CD workflows.
According to NIST’s Secure Software Development Framework (SSDF), organizations should use automated tools consistently across all development environments to maximize vulnerability detection.
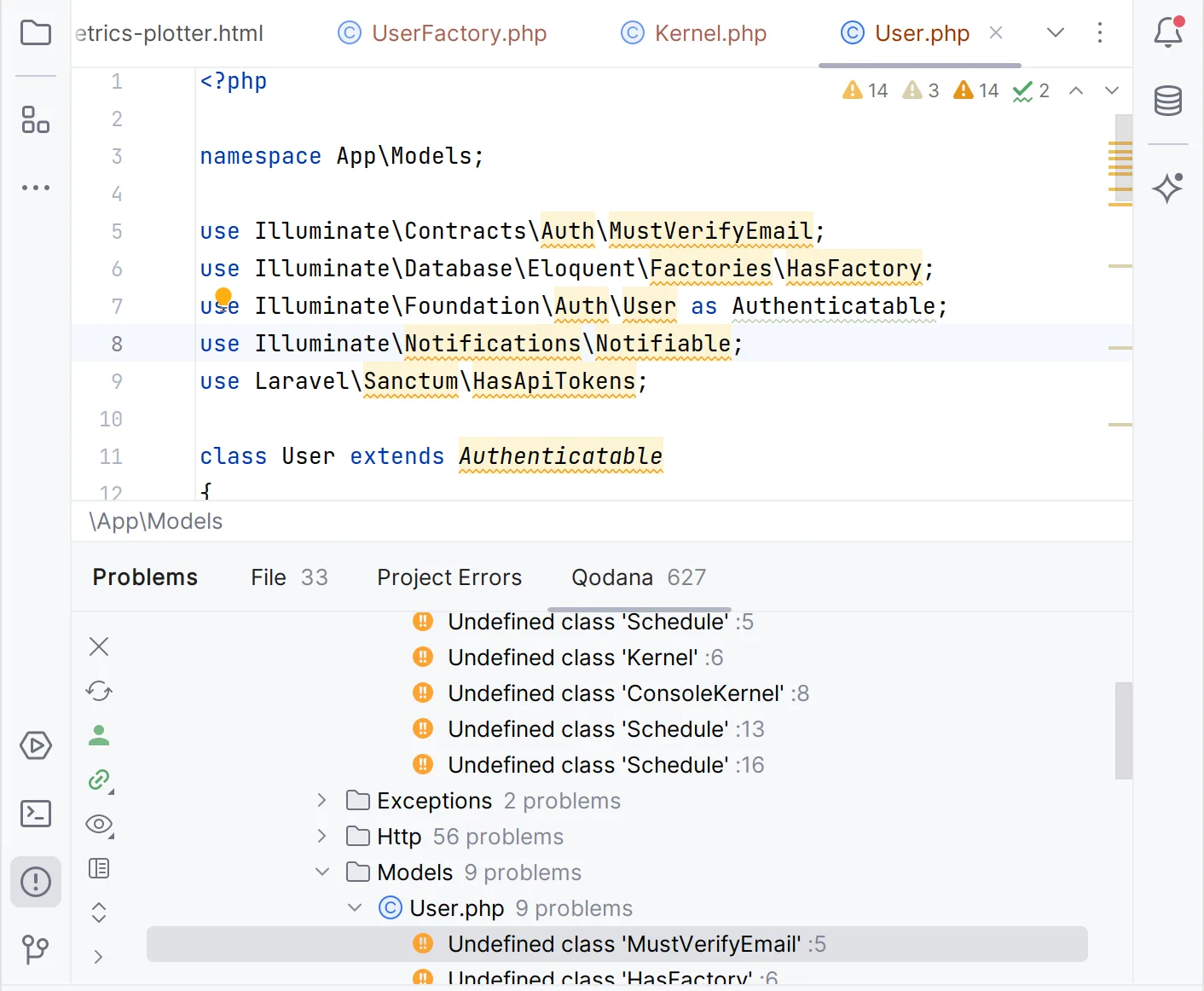
Qodana achieves this by running the same analyses in CI/CD that developers see in their JetBrains IDEs, catching issues that might be missed or ignored during local development.
Each language gets a specialized linter based on the corresponding JetBrains IDE: Qodana for JVM uses IntelliJ’s engine, Qodana for Python uses PyCharm’s, and so on. This means the same rules and the same accuracy in both places.
The current version is 2025.3. There are 15 linters available, including 4 free Community linters (JVM Community, Python Community, .NET Community, Clang).
Pricing
Qodana uses a contributor-based pricing model. An “active contributor” is anyone who committed to a Qodana Cloud project in the past 90 days.
| Tier | Price | Features |
|---|---|---|
| Community | Free | Java, Kotlin, Python, C#, C++, VB.NET. Limited linters and historical data. |
| Ultimate | $6/contributor/month | All languages. Quality gates, baselines, code coverage, FlexInspect, Quick-Fix. 180 days historical data. |
| Ultimate Plus | $15/contributor/month | Everything in Ultimate plus taint analysis, vulnerability checker, license audit, SSO, public API. Unlimited historical data. |
Minimum 3 contributors for paid plans. 60-day free trial available for both paid tiers.
Key features
Taint analysis (Ultimate Plus)
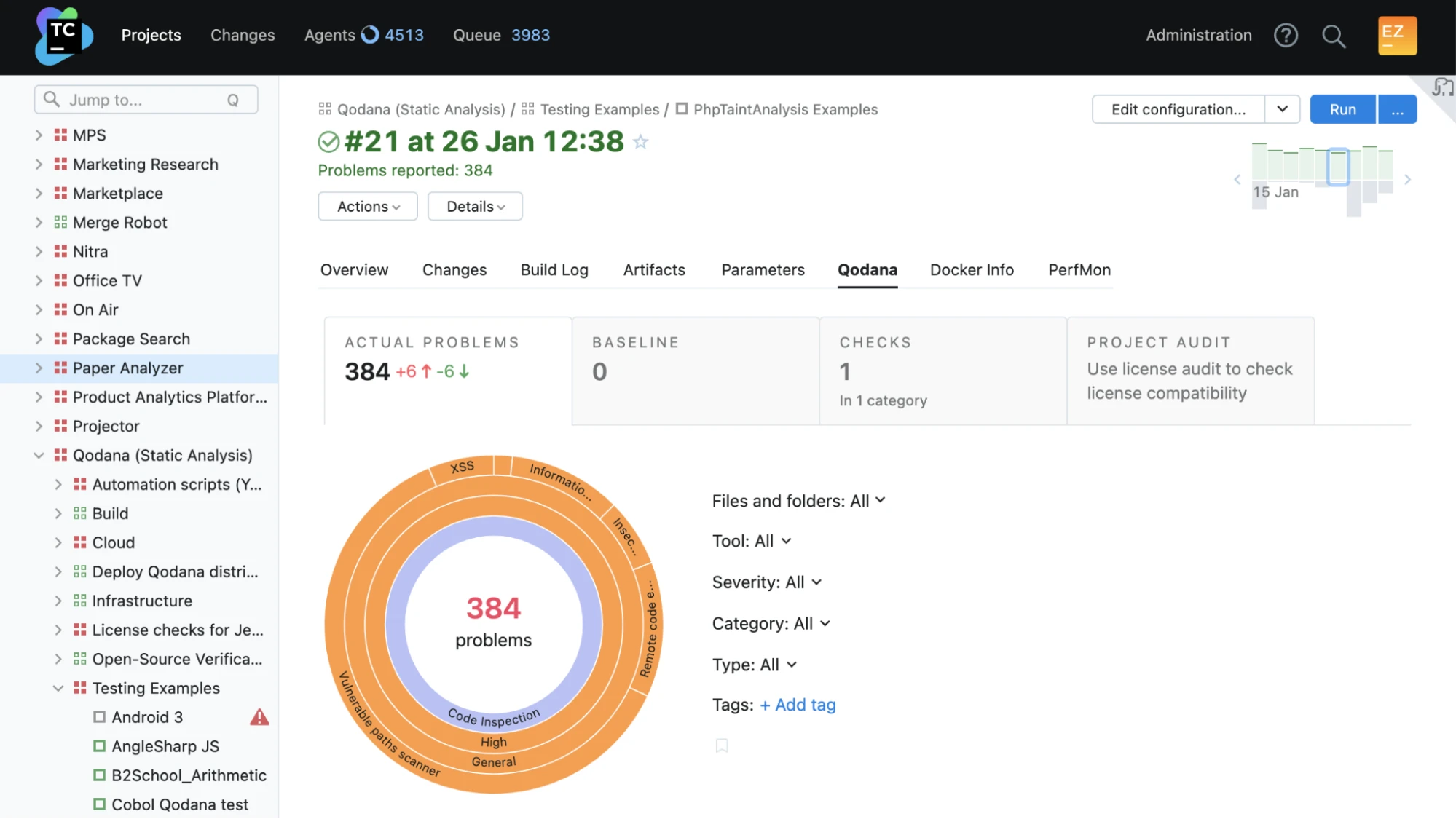
Qodana traces potentially harmful data through your application to identify paths where untrusted input reaches sensitive operations without validation. The engine covers 700+ built-in taint configuration entries for common frameworks and libraries.
Performance benchmark: Qodana can analyze 7 million lines of code in under 30 minutes for taint analysis (as of the 2025.2 release).
Currently supported in the PHP and JVM linters.
Vulnerability checker (Ultimate Plus)
Uses the OSV tool to check Gradle, Maven, npm, and PyPI dependencies for known vulnerabilities. Available in the JVM, .NET, Python, Go, PHP, and JS linters.
Technical debt tracking
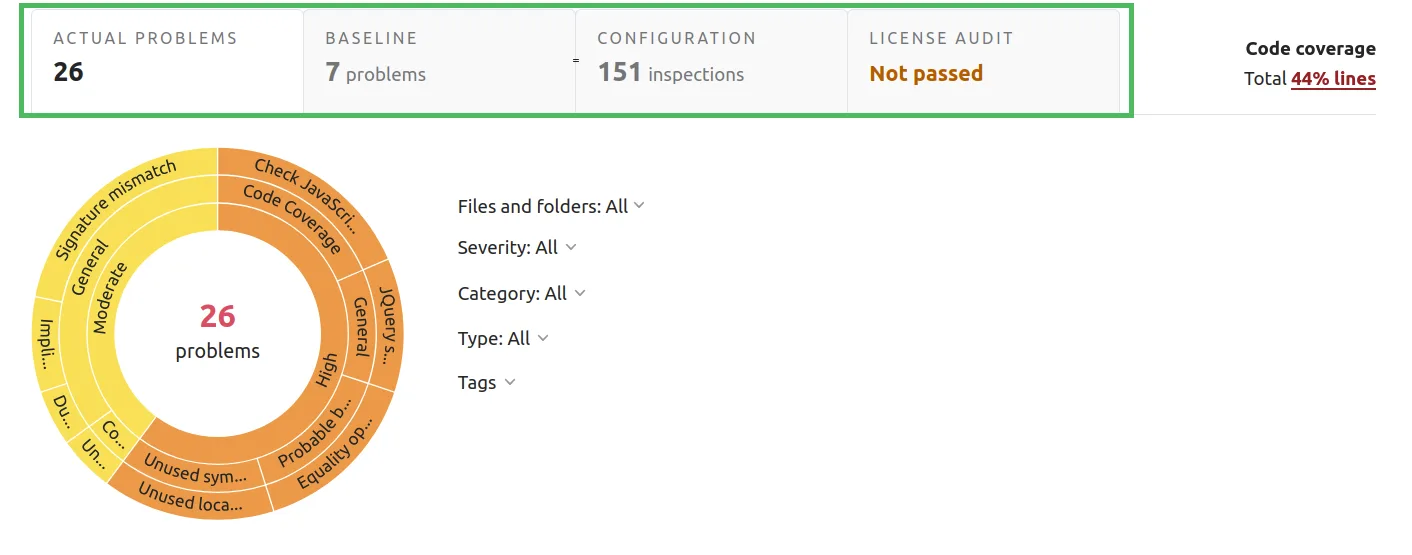
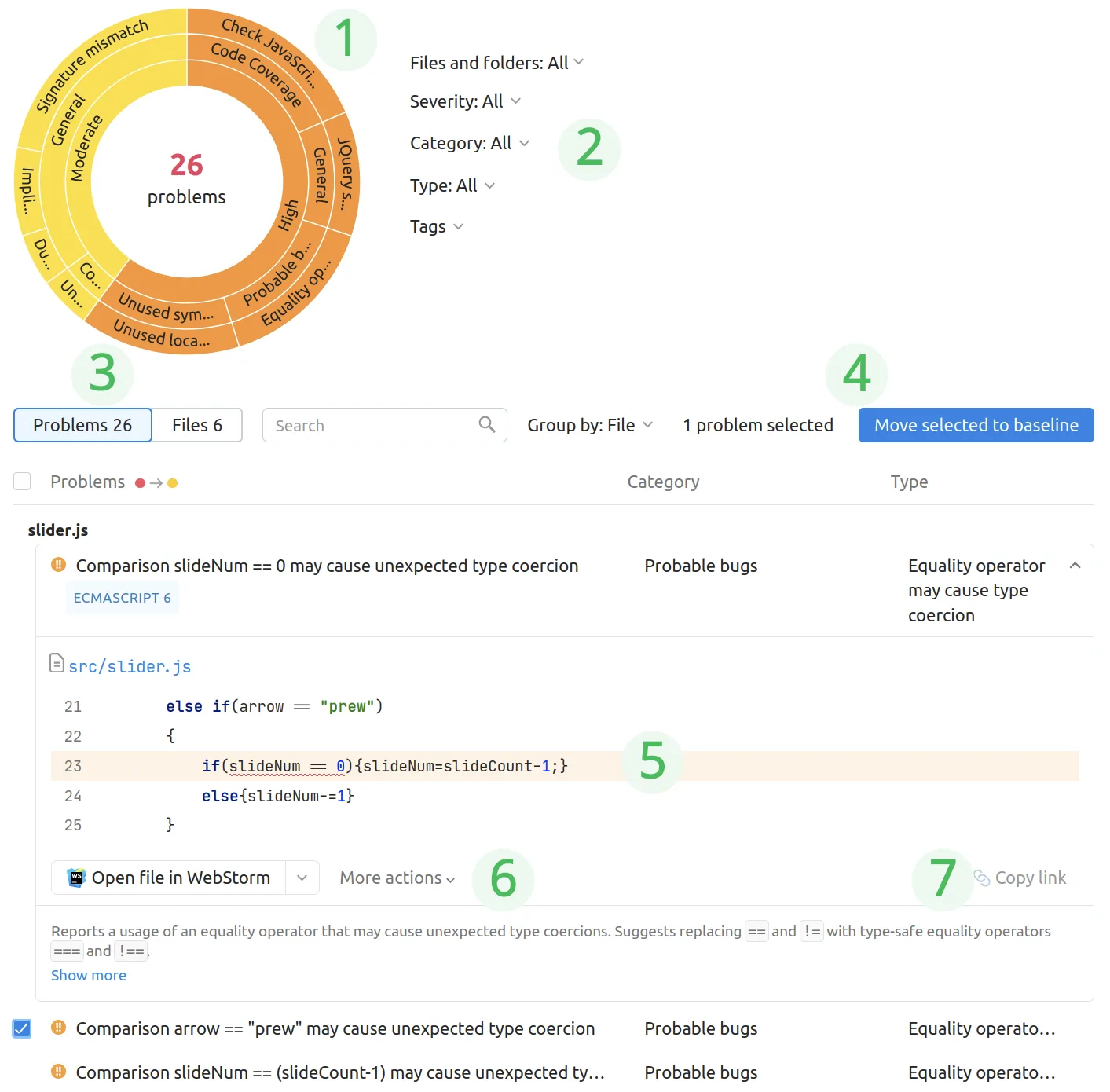
The baseline feature marks a project’s current state as a starting point, then tracks only new problems from that point forward. When combined with quality gates, only new issues count toward the threshold — pre-existing technical debt doesn’t block builds.
Getting started
curl -fsSL https://jb.gg/qodana-cli/install | bash or brew install jetbrains/utils/qodana on macOS. Windows users can use winget install JetBrains.QodanaCLI.qodana scan in your project directory. Qodana auto-detects the language and selects the appropriate linter. Results open in a local HTML report.JetBrains/qodana-action@v2025.3) with a QODANA_TOKEN. Native integrations also exist for GitLab CI, Azure Pipelines, CircleCI, and TeamCity.qodana.yaml to your project root with failThreshold and baseline settings. New problems exceeding the threshold will fail the build.When to use Qodana
Qodana is a natural fit for teams already using JetBrains IDEs. The consistency between editor warnings and CI/CD findings eliminates the “works on my machine” gap for code quality.
For teams not using JetBrains IDEs, SonarQube offers a broader plugin ecosystem. For focused security scanning, Semgrep or Snyk Code may provide deeper vulnerability coverage.
Qodana’s strength is combining code quality, security, and technical debt tracking with the same engine developers already use.
Qodana alternatives
Teams comparing CI-side static analyzers to Qodana usually evaluate:
- SonarQube — multi-language SAST and quality platform with deep CI integration; the most direct competitor to Qodana when you want quality gates plus security findings on the same dashboard.
- Semgrep — rule-driven SAST with a public ruleset and custom-rule support; preferred when security depth matters more than IDE parity and you want consistent rule syntax across languages.
- GitHub CodeQL — query-based SAST bundled with GitHub Advanced Security; a fit when GitHub is already your platform and you want a single vendor for code scanning.
- Snyk Code — developer-first SAST with AI-powered triage; chosen when Snyk’s SCA, container, and IaC products are already in use.
For a feature-by-feature view, the SAST tools hub lists the full active set.
How to use Qodana
A standard Qodana workflow runs in three steps. First, pick the right linter for your stack: Qodana for JVM covers Java and Kotlin, Qodana for Python covers Python, Qodana for .NET covers C# and VB.NET, and so on. Each linter is a separate Docker image, mirroring the matching JetBrains IDE engine, so the inspections you see in IntelliJ or PyCharm match what runs in CI.
Second, run the scan. Locally, qodana scan from the project root pulls the right image and produces an HTML report. In CI, the official Qodana action for GitHub, GitLab, Jenkins, and TeamCity wires the same scan into your pipeline and posts inline annotations on pull requests. Quality gates fail builds when new issues exceed a configured threshold.
Third, manage technical debt with a baseline file. qodana scan --baseline qodana.sarif.json snapshots existing issues and only fails on new ones, which lets legacy projects adopt Qodana without rewriting history. The Qodana Cloud dashboard tracks inspection trends, baseline drift, and per-developer metrics over time.
Qodana vs SonarQube
Qodana and SonarQube are both server-mode static analysis platforms with a quality-gate model, and they end up on the same shortlist often enough that JetBrains positions Qodana directly against SonarQube in their marketing.
The honest split: SonarQube has broader language coverage and a more mature open-source community, with self-hosted Community, Developer, and Enterprise editions plus the SonarCloud SaaS option. Qodana wins for JetBrains IDE shops because every Qodana inspection runs on the same engine the developer sees in IntelliJ, PyCharm, PhpStorm, or Rider — there is no rule-engine drift between local IDE feedback and CI findings, which dramatically reduces the false-positive triage tax on developer time.
If your team is already JetBrains-licensed, Qodana plugs into the workflow with near-zero learning curve. If your stack is polyglot or you need a self-hosted security-first scanner, SonarQube vs Veracode and the SAST tools hub are better starting points.