OX Security introduced Active ASPM, moving past passive aggregation to autonomous posture management. VibeSec, their AI-driven security agent, continuously enforces security policies within CI/CD pipelines.
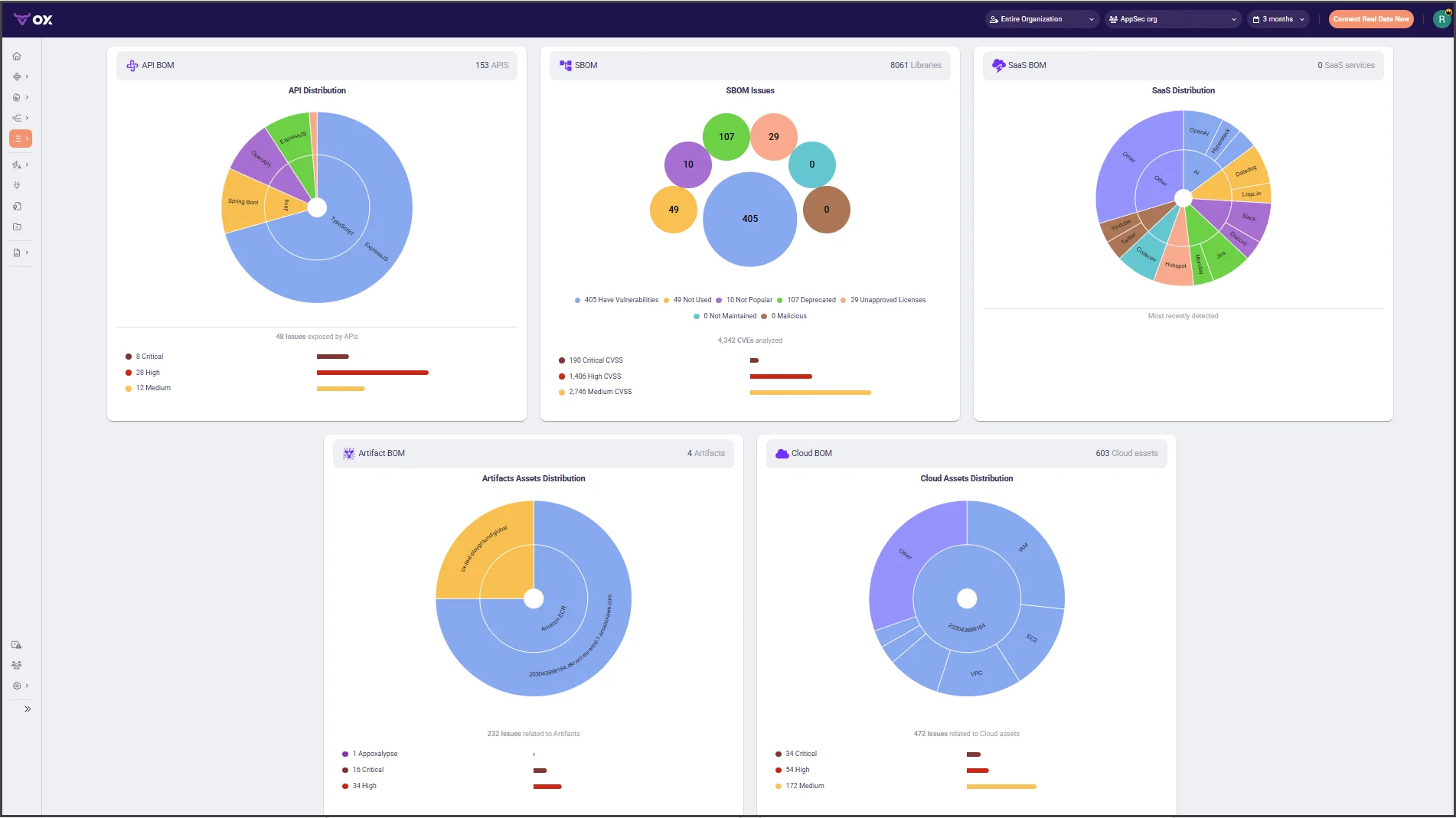
Their Pipeline Bill of Materials (PBOM) tracks full software lineage from code to deployment.
The company also created the OSC&R framework in collaboration with security experts from Google, Microsoft, and GitLab — an ATT&CK-like model for describing software supply chain threats.
What is OX Security?
Most ASPM platforms collect vulnerabilities and display them. OX Security goes further by actively monitoring the development pipeline and blocking risky deployments before they reach production.
OX Security reports up to 97% reduction in security debt for organizations using the platform.
Key features
Active ASPM
The “active” part distinguishes OX Security from most competitors:
| Action | How it works |
|---|---|
| Real-time monitoring | Watches pipeline activity and detects policy violations as they occur |
| Deployment blocking | Prevents risky builds from reaching production based on configurable policies |
| Automated remediation | Triggers fix workflows and routes findings to the right teams |
| Anomaly detection | Alerts on unusual pipeline behavior that could indicate compromise |
Pipeline Bill of Materials
PBOM captures the full software delivery chain:
| What PBOM records | Why it matters |
|---|---|
| Source code components and dependencies | Standard SBOM coverage |
| Build pipeline configurations | Detect pipeline injection risks |
| CI/CD tool versions and plugins | Track build environment integrity |
| Artifact signatures and checksums | Verify artifact provenance |
| Deployment targets and configurations | Map what runs where |
| Developer and approver identities | Audit trail for compliance |
This record supports incident investigation, compliance evidence, and supply chain attack detection.
No-code workflows
OX Security has a visual workflow builder for security automation:
| Feature | Description |
|---|---|
| Drag-and-drop policies | Create security rules without writing code |
| Conditional logic | Build complex decision trees for different scenarios |
| Integration actions | Trigger Jira tickets, Slack alerts, or custom webhooks |
| Approval gates | Require manual sign-off for sensitive operations |
| Audit trails | Full history of every workflow execution and outcome |
OSC&R framework
The Open Software Supply Chain Attack Reference provides structured taxonomy for supply chain threats:
| Category | Examples |
|---|---|
| Compromise vectors | Source code, build systems, dependencies |
| Attack techniques | Typosquatting, dependency confusion, pipeline injection |
| Detection strategies | Behavioral analysis, integrity checking, provenance verification |
| Mitigation controls | Code signing, pipeline hardening, dependency pinning |
Security teams use OSC&R to assess their defenses against known attack patterns.
Compliance support
OX Security maps findings and controls to major frameworks:
| Framework | Coverage |
|---|---|
| EU Cyber Resilience Act | SBOM/PBOM generation, vulnerability tracking |
| CISA SSDF | Secure development lifecycle evidence |
| NIST 800-53 | Security control documentation |
| SOC 2 | Security monitoring and incident response |
| FedRAMP | Continuous monitoring requirements |
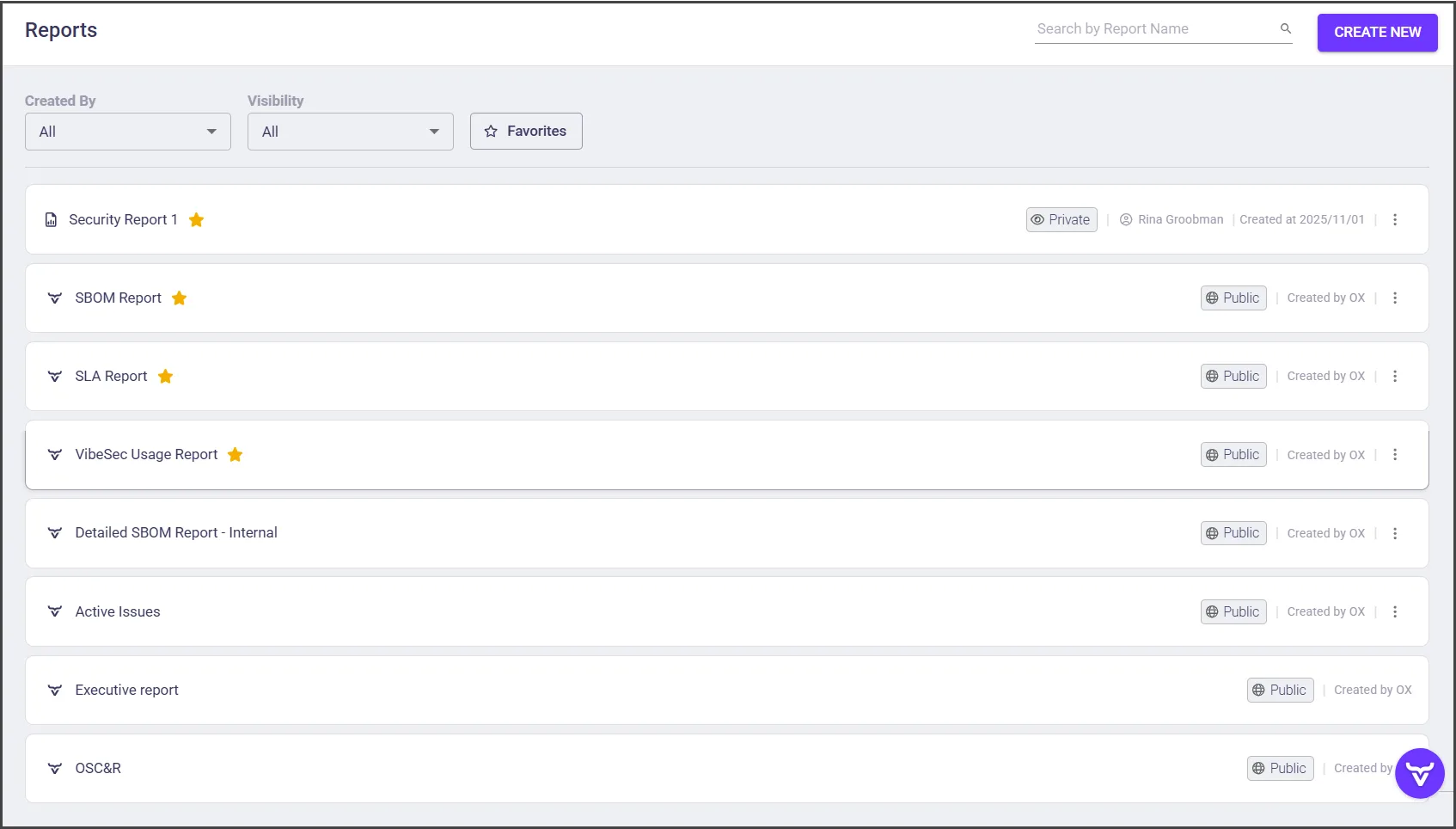
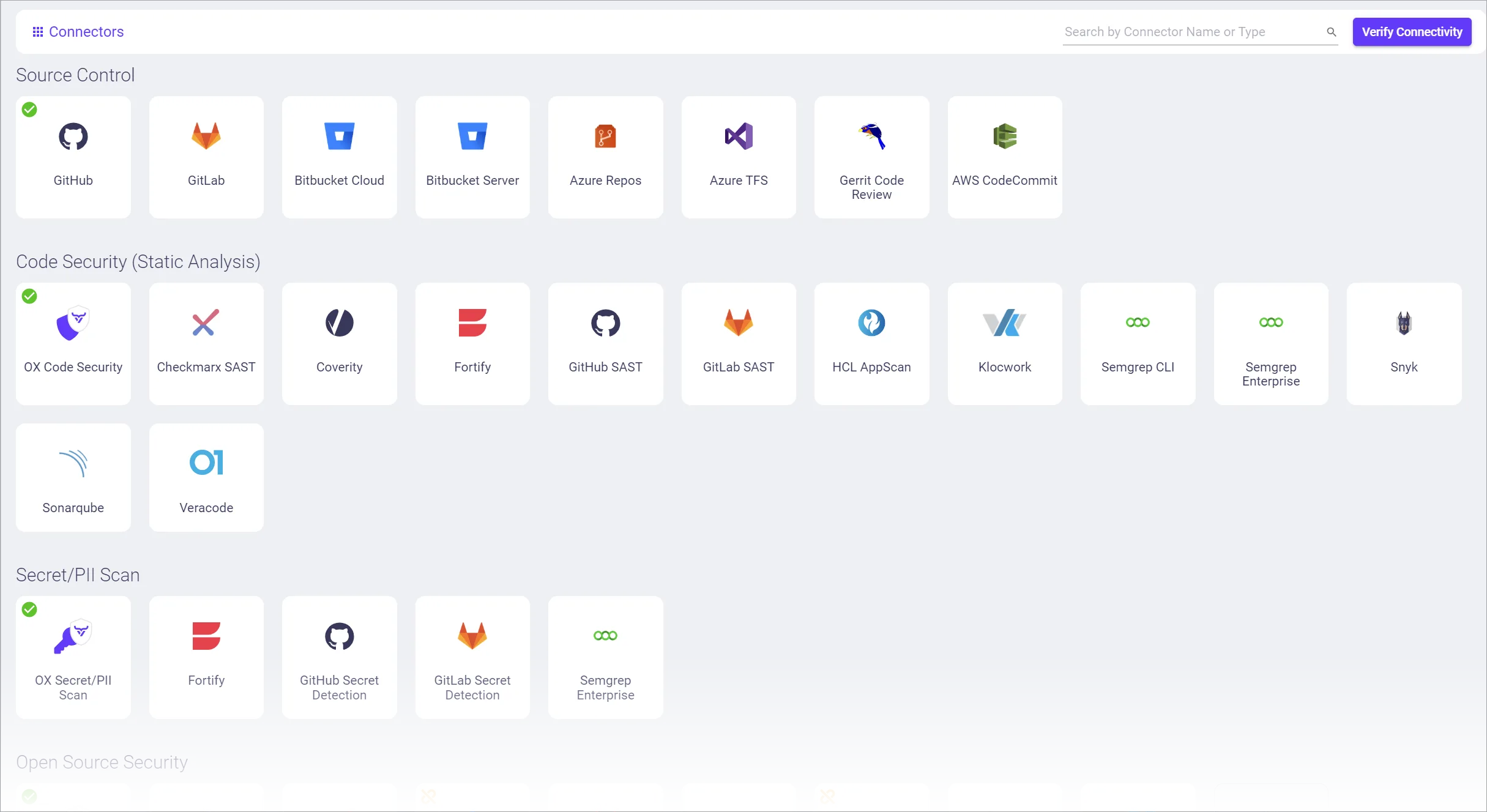
Integrations
Getting started
When to use OX Security
OX Security makes sense when passive ASPM isn’t enough.
If vulnerabilities keep reaching production despite detection, if you need supply chain visibility beyond standard SBOM, or if compliance mandates (EU CRA, CISA guidelines) require build provenance, OX Security’s active approach fills those gaps.
If you mainly need vulnerability aggregation without pipeline enforcement, ArmorCode or DefectDojo are simpler options.
If you want built-in scanning rather than pipeline governance, Aikido or Jit take that approach.