Oversecured is an automated mobile application security scanner built specifically for Android and iOS. It runs both static (SAST) and dynamic (DAST) analysis against uploaded app binaries, covering over 260 vulnerability categories combined.
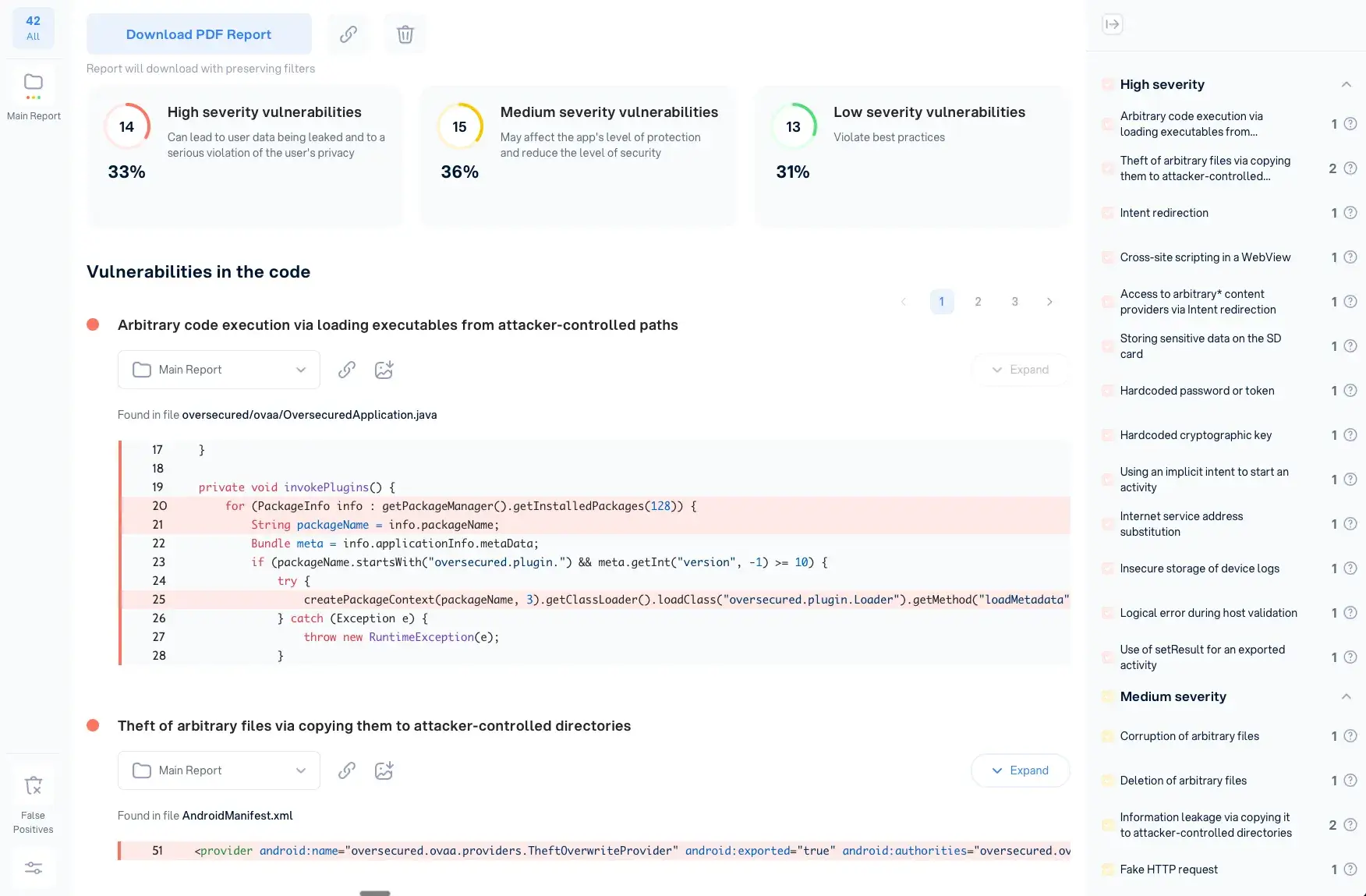
The scanner reports 99.8% detection accuracy with a 3% false positive rate in independent testing. No source code is required — you upload the compiled binary (APK, IPA, or AAB) and get results back with highlighted code, exact file paths, and remediation guidance.
Oversecured ranked #1 in Samsung’s mobile vulnerability detection program and was featured in a CNN investigation about Android app security. Clients include Mercari (Japan’s largest marketplace app), Google, VMware, and Kavak.com.
What is Oversecured?
Oversecured was built from scratch for mobile security testing, not adapted from web or general-purpose scanners. That matters because mobile apps have platform-specific attack surfaces — broadcast receivers on Android, URL schemes on iOS, WebView bridge interactions — that general tools tend to miss or misclassify.
The scanner works without source code access. Upload an APK, AAB, or IPA file through the web portal or API, and Oversecured decompiles the binary and runs both static and dynamic analysis against it.
Results come back with the affected code highlighted, exact file paths, and working proof-of-concept exploits where applicable.
Key Features
| Feature | Details |
|---|---|
| Analysis Type | SAST + DAST dual engine |
| Android Categories | 175+ vulnerability types |
| iOS Categories | 85+ vulnerability types |
| Detection Accuracy | 99.8% in independent testing |
| False Positive Rate | ~3% |
| Scan Speed | Under 5 minutes average |
| Source Code Required | No (binary upload) |
| Supported Formats | APK, AAB, IPA |
| Cross-Platform | React Native, Flutter, Xamarin, Cordova |
| Detection Updates | Weekly |
Vulnerability Coverage
Android (175+ categories):
- Insecure broadcast receivers
- Content provider SQL injection
- Path traversal via content providers
- Deep link hijacking
- WebView JavaScript injection
- Insecure file providers
- Task hijacking vulnerabilities
iOS (85+ categories):
- Keychain access control bypasses
- URL scheme hijacking
- Insecure data storage (UserDefaults)
- Pasteboard data leaks
- ATS configuration issues
- Jailbreak detection bypasses
Cross-Platform Framework Support
Oversecured understands how cross-platform frameworks translate to native code:
- React Native: Analyzes JavaScript bridge interactions
- Flutter: Examines Dart compilation artifacts
- Xamarin: Scans .NET assemblies and native bindings
- Cordova: Reviews plugin security and WebView configuration
Working Proof-of-Concepts
When Oversecured finds a vulnerability, it generates a working proof-of-concept where possible. In Mercari’s case, the scanner identified a WebView vulnerability that “had been missed by all previous tooling” — one that could have allowed arbitrary JavaScript execution within the app context, putting user sessions and payment credentials at risk.
CI/CD Integration
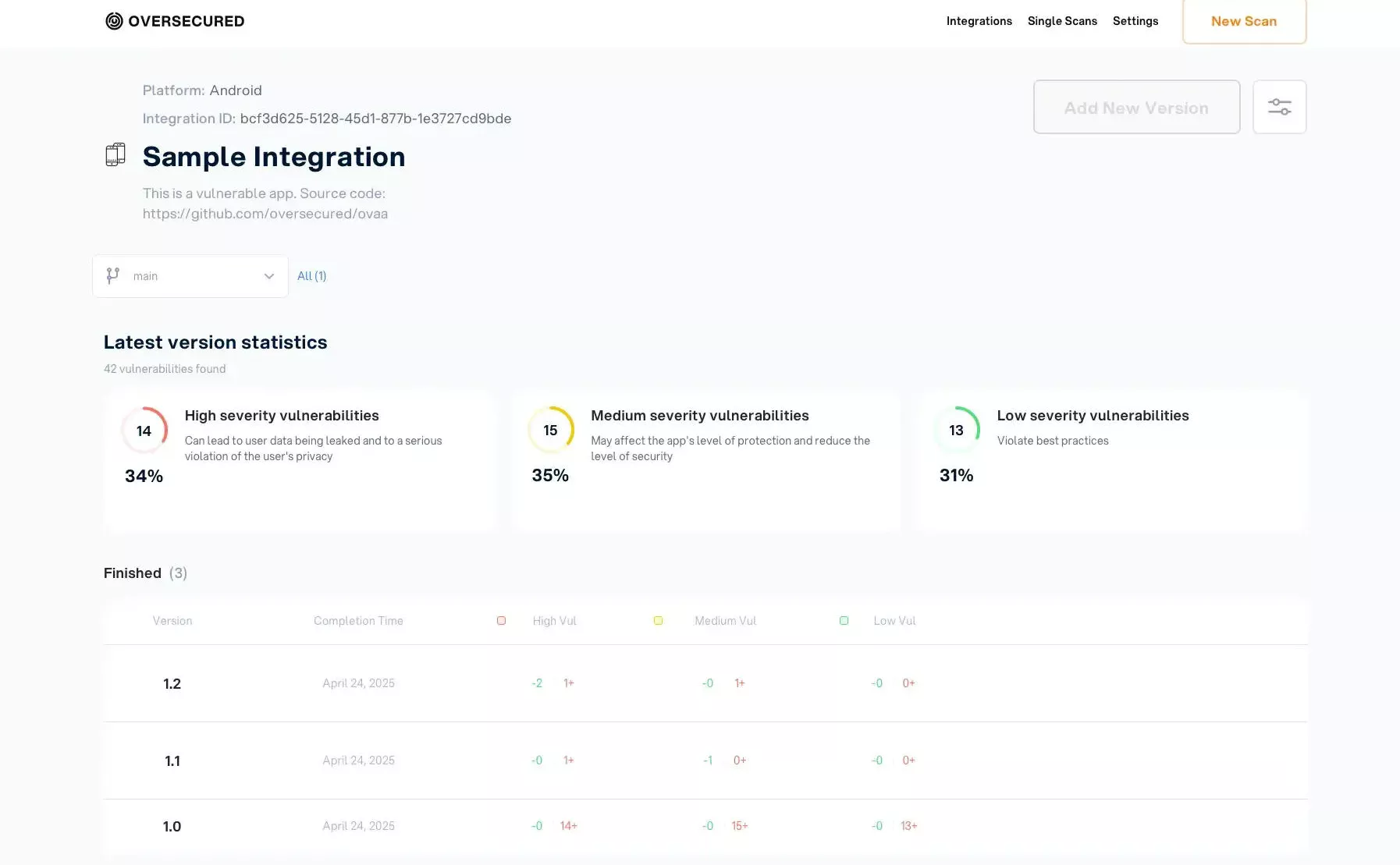
Oversecured provides a REST API for automation. You can configure builds to fail when new vulnerabilities appear, scan on every release build, or run non-blocking scans that report results without stopping deploys.
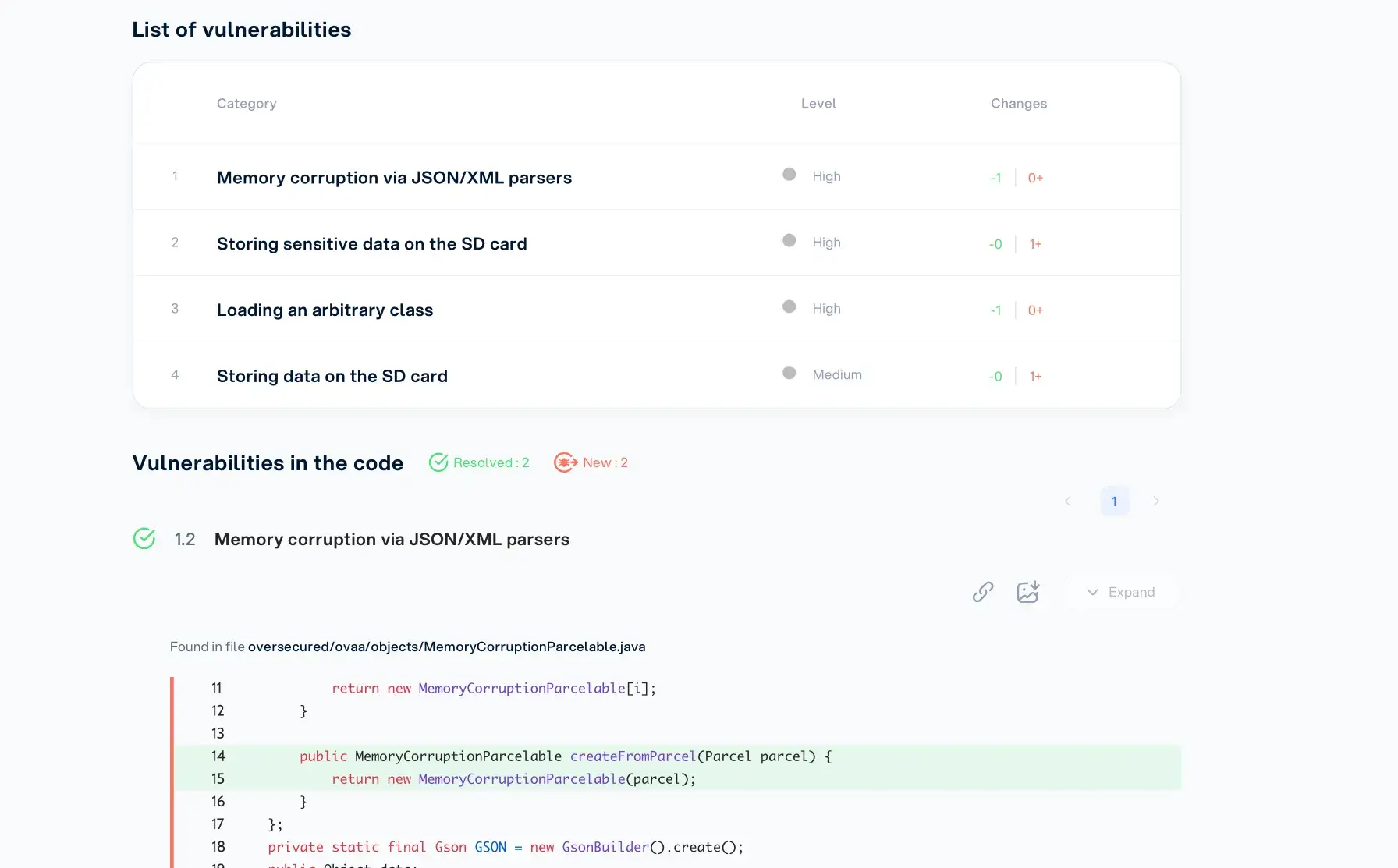
The dashboard also supports diff comparison between scan reports, so teams can track whether vulnerability counts are trending down over time.
Integrations
Getting Started
Compliance
Oversecured helps organizations meet mobile security compliance requirements:
- OWASP MASVS: Mobile application security verification
- GDPR: Data protection and privacy analysis
- PCI-DSS: Payment security controls
- HIPAA: Healthcare data protection
Reports can be customized to map findings to specific compliance frameworks for audit documentation.
When to Use Oversecured
Oversecured is a strong fit when detection accuracy matters more than anything else. The 3% false positive rate means findings can go straight to developers without security teams spending hours triaging noise.
Consider Oversecured when:
- False positives from other mobile security tools have worn down developer trust
- Fast scan times are a requirement for CI/CD integration
- Mobile-specific vulnerabilities (not generic web issues) are your primary concern
- You work with cross-platform frameworks like React Native or Flutter
- You need proof-of-concept exploits to demonstrate risk to stakeholders
The unlimited scan model encourages testing on every commit rather than only before releases. Organizations with multiple mobile apps benefit from consistent, reliable scanning across their entire portfolio.