The best open source AppSec tools in 2026 are Semgrep CE for SAST, Trivy and Grype for SCA and containers, ZAP and Nuclei for DAST, Checkov for IaC, Gitleaks and TruffleHog for secrets, Garak for LLM security, and MobSF for mobile.
I track 64 active open source AppSec tools across 10 categories — SAST, SCA, DAST, IaC security, secrets, ASPM, AI security, mobile, container, and policy — and this guide is the umbrella index with first-person reviews of the 12 strongest picks, license clarity, and links to the category-level deep dives.
The shortlist below is curated from tools I have personally used in scans, stress-tested against real codebases, and tracked over time through my State of Open Source AppSec 2026 research . Star counts and license details are current as of April 2026.
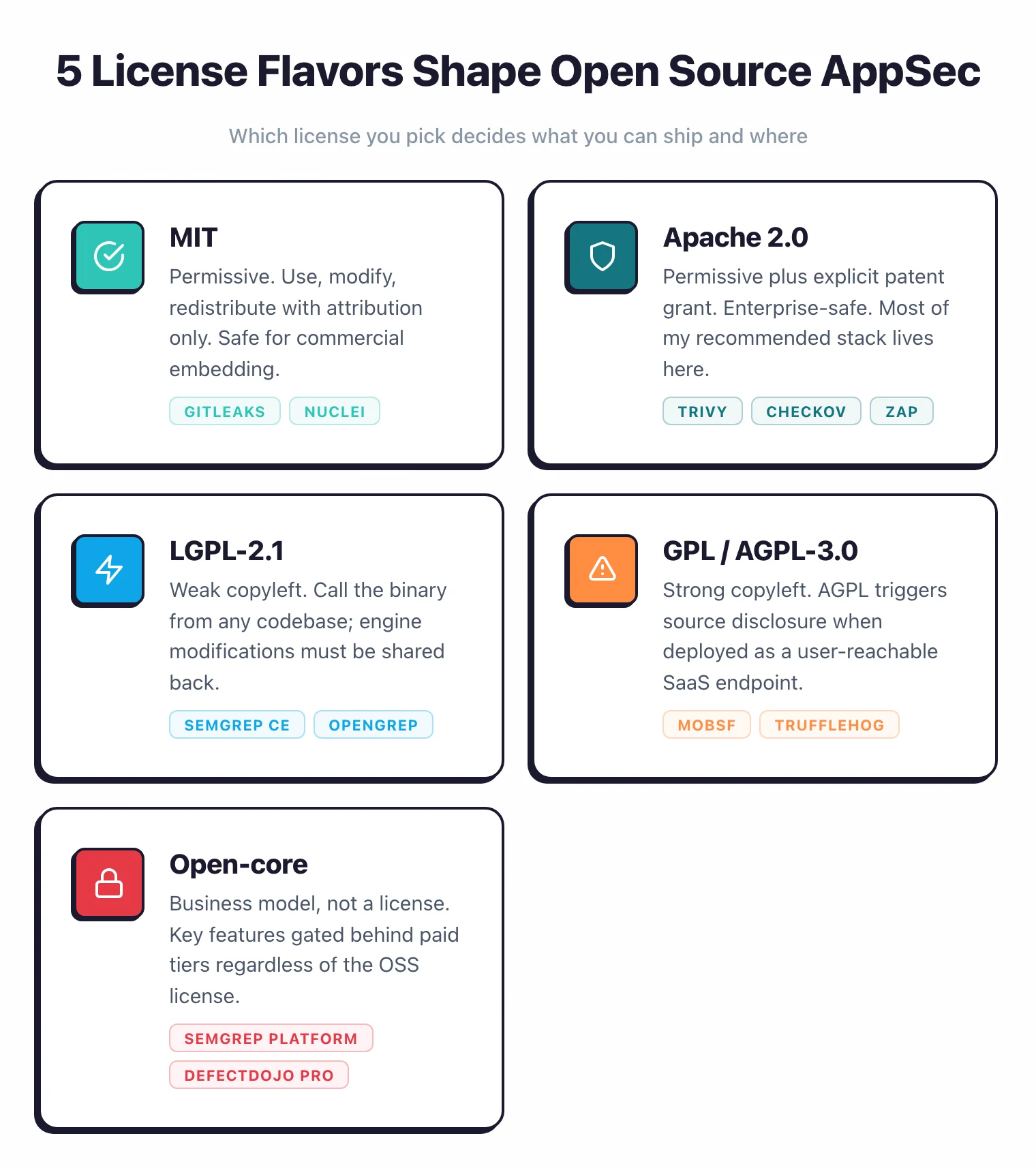
What is an open source AppSec tool? An open source application security tool ships its source code under an OSI-approved license (MIT, Apache 2.0, LGPL, GPL, or AGPL) so you can audit detection logic, self-host scans, write custom rules, and redistribute the binary without paying a vendor. The term excludes “source available” projects with restricted licenses and freemium SaaS with proprietary backends.
Why open source matters for AppSec
Open source AppSec tools removed the license barrier. A startup can now run Semgrep, Trivy, ZAP, and Gitleaks in CI with zero spend and catch the same SQL injection, vulnerable dependency, and leaked AWS key that a six-figure commercial tool would flag.
The three real reasons to choose open source are cost, transparency, and customization. You can audit the detection logic, write your own rules, and self-host sensitive scans without shipping code to a vendor.
Commercial tools still win on depth and polish, and I explain where in the “When not to use OSS” section.
Adoption reflects this shift. According to a Snyk survey I cite in my SAST roundup , 87% of organizations use open source security tools in some capacity.
The OWASP Benchmark Project has shown repeatedly that a well-configured open source stack matches or exceeds a poorly configured commercial one — configuration and rule tuning matter more than sticker price.
Across the 64 open source AppSec projects I analyzed for my State of Open Source AppSec 2026 research, the dataset holds 608,000+ GitHub stars collectively, with Trivy (32,200) and Nuclei (26,900) leading the dedicated vulnerability scanner category.
License quick guide
License flavor decides whether you can ship the tool inside your product or use it in a managed service. I group the 64 tools I track into five license buckets.
What license flavors should enterprises care about? MIT and Apache 2.0 are the safest for commercial embedding because they impose almost no obligations beyond attribution, and LGPL is safe for CI/CD use as long as you do not modify the engine. AGPL-3.0 is the one that trips enterprises up: deploying an AGPL tool as a SaaS endpoint users can reach triggers source disclosure to those users. “Open-core” is a business model, not a license, that gates key features behind paid tiers regardless of the underlying license.
MIT — Permissive. You can use, modify, and redistribute with almost no obligations.
Gitleaks, Nuclei, and LLM Guard ship under MIT. Safe for commercial product embedding.
Apache 2.0 — Permissive with explicit patent grant. Most of my recommended stack lives here: Trivy, Grype, Syft, Checkov, ZAP, OSV-Scanner, Falco, Kubescape, KICS, OWASP Dependency-Check, and Dependency-Track. Enterprise-friendly.
LGPL-2.1 — Weak copyleft. Semgrep CE and OpenGrep use LGPL-2.1.
You can call the binary from any codebase, but modifications to the engine itself must be shared back. Safe for CI/CD use without redistribution concerns.
GPL / AGPL-3.0 — Strong copyleft. MobSF uses GPL v3; TruffleHog uses AGPL-3.0.
AGPL is the one that trips enterprises up — if you deploy the tool as a SaaS endpoint users can reach, you owe source code disclosure to those users. Fine for internal scanning, risky for embedding in hosted products.
Open-core — Not a license, a business model. Semgrep AppSec Platform, Bearer (now Cycode), and DefectDojo Pro keep a free OSS core and gate cross-file dataflow, enterprise reporting, and SSO behind paid tiers. Read the fine print before assuming “open source” means “full-featured.”
Top 12 open source AppSec picks
I picked these 12 based on the health signals from my State of Open Source AppSec 2026 research : stars, commit recency, contributor diversity, and CandyShop benchmark performance, plus hands-on use in my own scanning workflows. Each review is 2-3 sentences in my own voice with a commercial alternative where one maps cleanly.
These 12 open source picks span SAST, SCA, container scanning, SBOM, DAST, IaC, secrets, LLM security, and mobile — and together they cover roughly 70% of what a commercial AppSec platform delivers for teams under 50 developers, at zero license cost.
1. Semgrep CE — Best general-purpose SAST
I run Semgrep CE on every project I test. It scans 30+ languages with 3,000+ community rules, finishes a 500K-line repo in under a minute on my M2 laptop, and lets me write custom rules in pattern syntax that mirrors source code. LGPL-2.1 license, 14,300 GitHub stars, and a healthy community rule registry.
Rule authoring is the killer feature. I can codify a team-specific pattern like “never call eval() on user input” in 5 lines of YAML and ship it to CI the same day. Dropbox, Figma, and Snowflake all use it in production.
When it breaks down: Semgrep CE only does single-file analysis. Cross-file taint tracking lives in the paid AppSec Platform or in OpenGrep , the community fork.
Paid alternative: Semgrep AppSec Platform (free up to 10 contributors, then custom) or Checkmarx One for deeper inter-procedural analysis.
2. OpenGrep — Taint analysis restored
OpenGrep is a community fork of Semgrep CE that brings back taint analysis, Windows support, and inter-procedural scanning that the CE version lost. It stays backward compatible with Semgrep rule format, so existing pipelines work without edits. Backed by a consortium of 10+ AppSec companies including Aikido, Endor Labs, and Orca Security.
I use OpenGrep when I need taint tracking without buying Semgrep AppSec Platform. LGPL-2.1, 2,144 stars, and a full-time OCaml team driving it forward. Visual Basic support is exclusive to OpenGrep — useful for teams still carrying legacy .NET codebases.
3. Trivy — The most-starred OSS scanner
Trivy is the do-everything scanner. One binary covers container images, filesystems, Git repos, Kubernetes clusters, and IaC, finding vulnerabilities, misconfigurations, secrets, and licenses in a single run. 32,200 GitHub stars, 513+ contributors, Apache 2.0.
I run trivy fs . on every repo I audit. Aqua Security absorbed tfsec
in 2023, so all Terraform checks now live in trivy config. If you only install one OSS AppSec tool this year, install Trivy.
Paid alternative: Aqua Platform , Snyk Container , or Prisma Cloud for runtime protection and centralized policy.
4. Grype — Focused container vuln scanner
Grype does one thing: scan container images and SBOMs for CVEs. It runs with lower false positive rates than most competitors and pulls from NVD, GitHub Advisories, and distribution feeds, with EPSS and KEV scoring on top. 11,500 stars, Apache 2.0.
I pair it with Syft: Syft generates the SBOM, Grype scans it. This two-step pipeline matches commercial SCA quality at zero cost.
Paid alternative: Snyk Container , Anchore Enterprise , or JFrog Xray for policy gates and VEX management.
5. Syft — Open source SBOM generation
Syft generates CycloneDX and SPDX SBOMs from container images, filesystems, and archives. It runs offline, auto-detects Alpine, Debian, RPM, npm, pip, Maven, Go, and Rust packages, and supports signed in-toto attestations. 8,400 stars, Apache 2.0.
I treat Syft as infrastructure: every build I push generates an SBOM and stores it alongside the artifact. It pairs naturally with Grype for CVE scanning.
Paid alternative: Anchore Enterprise for SBOM inventory and attestation management across a portfolio.
6. ZAP — The free DAST benchmark
ZAP is still the strongest free DAST scanner in 2026. Checkmarx hired all three project leaders in September 2024 but kept it free under Apache 2.0 with no paid tiers. 14,700 stars, and a YAML automation framework that codifies scan workflows as CI/CD steps.
I run ZAP baseline scans on every PR and full active scans nightly. Detection rates on standard OWASP classes (SQL injection, XSS, SSRF, path traversal) match commercial tools in independent benchmarks. The intercepting proxy is also a solid manual testing workbench when I need to replay a specific request.
Paid alternative: Invicti or Burp Suite Enterprise for proof-based validation, JavaScript SPA crawling, and centralized scan management.
7. Nuclei — Template-driven vulnerability scanning
Nuclei runs 12,000+ community YAML templates against HTTP, DNS, TCP, SSL, and headless browser targets. New CVE templates often appear within hours of public disclosure. 26,900 stars, MIT license, written in Go.
I use Nuclei for known-CVE sweeps across infrastructure. It does not crawl, so it needs targets, but it catches default credentials, misconfigurations, and specific CVE patterns that ZAP’s active scanner sometimes misses.
Paid alternative: ProjectDiscovery Cloud for hosted scanning, or Tenable for broader vulnerability management.
8. Checkov — Policy as code for IaC
Checkov ships 1,000+ built-in policies covering Terraform, CloudFormation, Kubernetes, Helm, ARM, Bicep, Ansible, and more. The 3.0 release added 800+ graph-based policies that check cross-resource relationships (for example, an EC2 instance connected to a VPC-attached subnet) which single-resource scanners miss. 8,500 stars, Apache 2.0, 80M+ downloads.
I run Checkov as a pre-deploy gate on every Terraform change. Custom policies can be written in Python or YAML.
Paid alternative: Prisma Cloud (same vendor, adds centralized management) or Wiz for cloud-native posture management.
9. Gitleaks — Pre-commit secret scanning
Gitleaks is my pre-commit hook of choice. It scans git history, working trees, and staged changes for 150+ secret patterns (AWS keys, API tokens, database credentials) and outputs SARIF for GitHub code scanning. 24,400 stars, MIT license.
Use it as a pre-commit hook, a GitHub Action, or a nightly history sweep. Catches most hardcoded secrets before they land.
Paid alternative: GitGuardian for real-time detection, automatic public-exposure checks, and remediation workflows.
10. TruffleHog — Secrets with live verification
TruffleHog goes a step further than Gitleaks: it detects 800+ secret types and then verifies whether each one is still live by calling the service. 24,500 stars, AGPL-3.0, developed by Truffle Security with 250,000+ daily scans. A comparative study of secret detection tools found wide variance in precision and recall across the OSS landscape, which matches what I see when running multiple scanners side by side (Basak et al., 2023 ).
I run TruffleHog for incident response. When I need to know whether a leaked key was burned or still works, its verification is faster than manual credential rotation audits. Watch the AGPL license if you plan to embed it.
Paid alternative: Truffle Security Enterprise (same vendor, adds SSO, API, and managed detectors) or GitGuardian .
11. Garak — LLM vulnerability scanning
Garak is NVIDIA’s open source LLM vuln scanner with 50+ probe modules for prompt injection, jailbreaks, hallucinations, and data leakage. It supports 23 generator backends including OpenAI, Anthropic, Hugging Face, and local models, and produces JSONL or HTML reports. 7,000 stars, Apache 2.0.
I use Garak when testing LLM-backed features. It is the closest thing to ZAP-for-LLMs in the open source world.
Paid alternative: Lakera Guard , Protect AI Guardian , or HiddenLayer for production runtime protection and policy enforcement.
12. MobSF — Mobile app security framework
MobSF is the only full-featured open source mobile app scanner I recommend. It handles static and dynamic analysis for Android APK, iOS IPA, and Windows APPX, with Frida-based runtime instrumentation and a web dashboard. 20,700 stars, GPL v3.
The GPL v3 license means you cannot embed MobSF in a proprietary product, but for internal security testing it is excellent. Featured at Black Hat Arsenal.
Paid alternative: NowSecure or Guardsquare for on-device hardening and app store monitoring.
My recommended free starter stack
If you are building AppSec from zero on a zero budget, here is the exact stack I recommend for a team under 50 developers. Every tool below is Apache 2.0, MIT, or LGPL — nothing that triggers AGPL copyleft or open-core paywalls.

SAST: Semgrep CE as the primary scanner, plus one language-specific tool (Bandit for Python, Brakeman for Rails, gosec for Go). Run both on every PR.
SCA: Trivy for filesystems and container images, or Grype + Syft if you want separation between SBOM generation and vulnerability scanning. For Java-heavy shops, OWASP Dependency-Check still has the cleanest Maven and Gradle integration.
DAST: ZAP for broad crawling and automated baseline scans on every PR, Nuclei for targeted CVE template sweeps on staging. Both run in under 5 minutes in CI.
IaC: Checkov for Terraform, CloudFormation, and Kubernetes manifests. Trivy handles the same targets if you want one binary for SCA + IaC.
Secrets: Gitleaks as a pre-commit hook plus a CI safety net. Add TruffleHog only when you need live verification during incident response.
Aggregation: DefectDojo to collect findings from all the above tools into a single triage queue. It parses 200+ scanner formats and deduplicates findings across sources.
Total license cost: zero. Setup time: about one engineering week for a team new to AppSec. This stack covers roughly 70% of what a commercial platform delivers at 0% of the cost.
Go deeper by category
Each category-specific OSS guide goes deeper than this umbrella page, with language coverage tables, CI/CD setup, detection benchmarks, and side-by-side comparisons.
- Open source SAST tools — Semgrep, OpenGrep, SonarQube CE, CodeQL, Bandit, Brakeman, gosec, Graudit with language coverage tables and detection quality data.
- Open source SCA tools — Trivy, Grype, Syft, OSV-Scanner, OWASP Dependency-Check, Dependency-Track, Renovate, cdxgen with vulnerability database and CI/CD integration details.
- Free DAST tools — ZAP, Nuclei, Nikto, Wapiti, Wfuzz with scan speed, API support, and SPA crawling benchmarks.
- Secret scanning tools — Gitleaks, TruffleHog, detect-secrets, BetterLeaks with speed benchmarks and pre-commit vs CI setup.
- Open source license compliance — FOSSology, ScanCode Toolkit, and license policy enforcement.
Full list of 64 open source AppSec tools
The filter engine below groups all 64 active open source tools by category and lets you narrow by language, license flavor, and free-vs-open-core status.
The distribution across categories is uneven. SAST, SCA, IaC, and secret scanning have mature open source options I would deploy in production tomorrow. AI security OSS is the fastest-growing slice; tools like Garak, LLM Guard, Agentic Radar, NeMo Guardrails, and Giskard did not exist three years ago.
Mobile, container runtime, and policy-as-code each have one or two strong picks (MobSF, Falco, OPA Gatekeeper, Kyverno). IAST and RASP remain commercial-only.
Which open source AppSec tools have the most GitHub stars?
The 64 open source AppSec projects I analyzed for the State of Open Source AppSec Tools 2026 study hold 608,000+ GitHub stars collectively. Among dedicated vulnerability scanners, Trivy leads with 32,200 stars, followed by Nuclei at 26,900 and TruffleHog at 24,500. The full top 20 also includes Gitleaks, MobSF, ZAP, Semgrep, Grype, Kubescape, and Falco, alongside reverse-engineering staples like Ghidra (64K) and Jadx (47K) that pull the dataset’s biggest star counts.
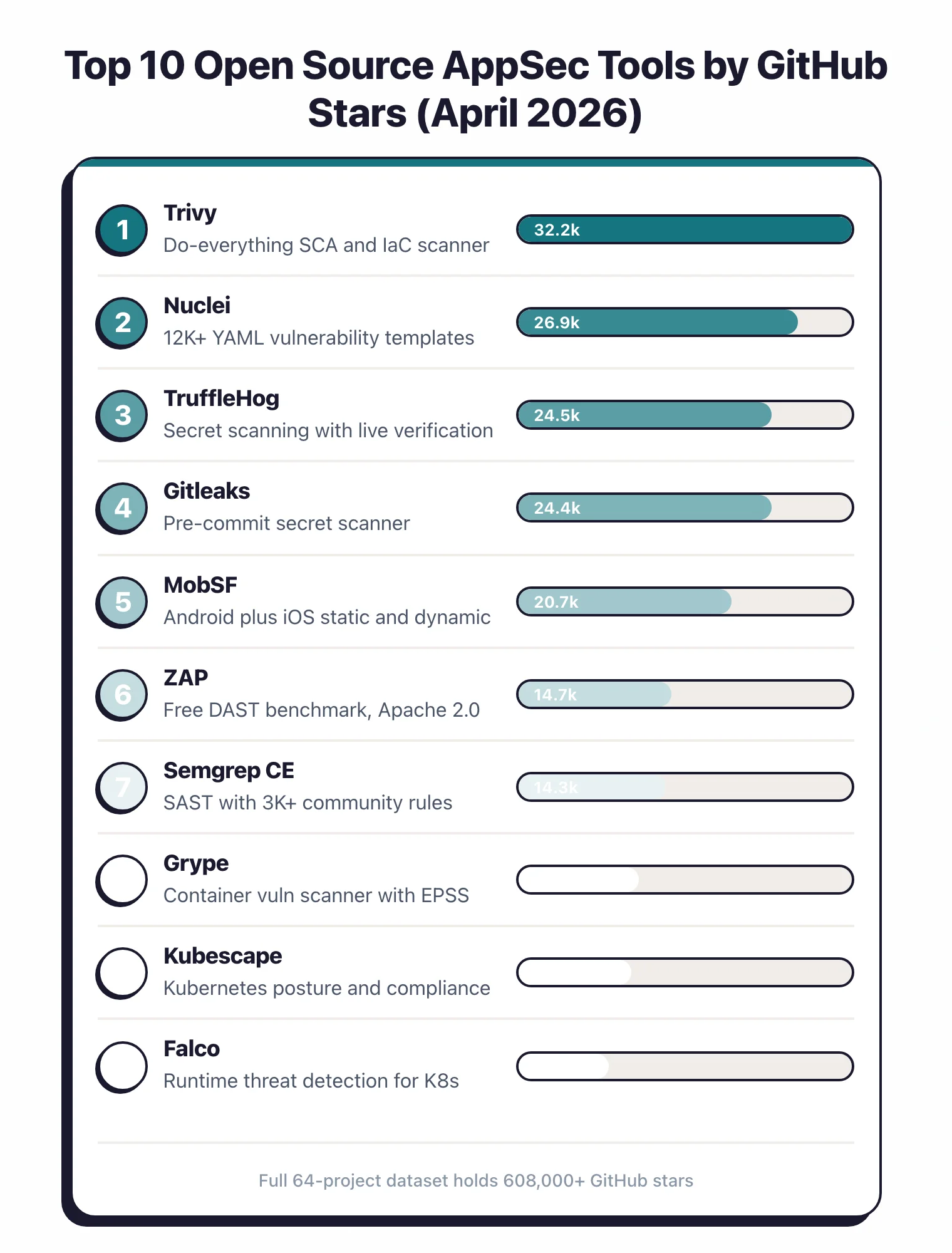
The same study flagged several projects as “at risk”: single-maintainer ownership, irregular commit activity, or no funding model. I reference it in every review because long-term health matters more than star count for AppSec tooling you put in CI. Empirical research on open source sustainability backs this up, showing that institutional support and contributor diversity predict project survival far better than raw popularity metrics (Yin et al., 2022 ).
Health also varies by category. SCA and IaC scanners (Trivy, Grype, Checkov, Kubescape) all have multi-maintainer teams backed by companies like Aqua Security, Anchore, and ARMO. Secret scanners sit between: Gitleaks is run by a small core team, TruffleHog by Truffle Security.
AI security OSS is the youngest, noisiest category: projects like Garak, LLM Guard, and Agentic Radar launched in 2023-2024 and are still finding their shape.
When not to use open source
I run open source in my own workflow, but I am honest about where commercial wins. Here are the cases where I tell teams to pay.
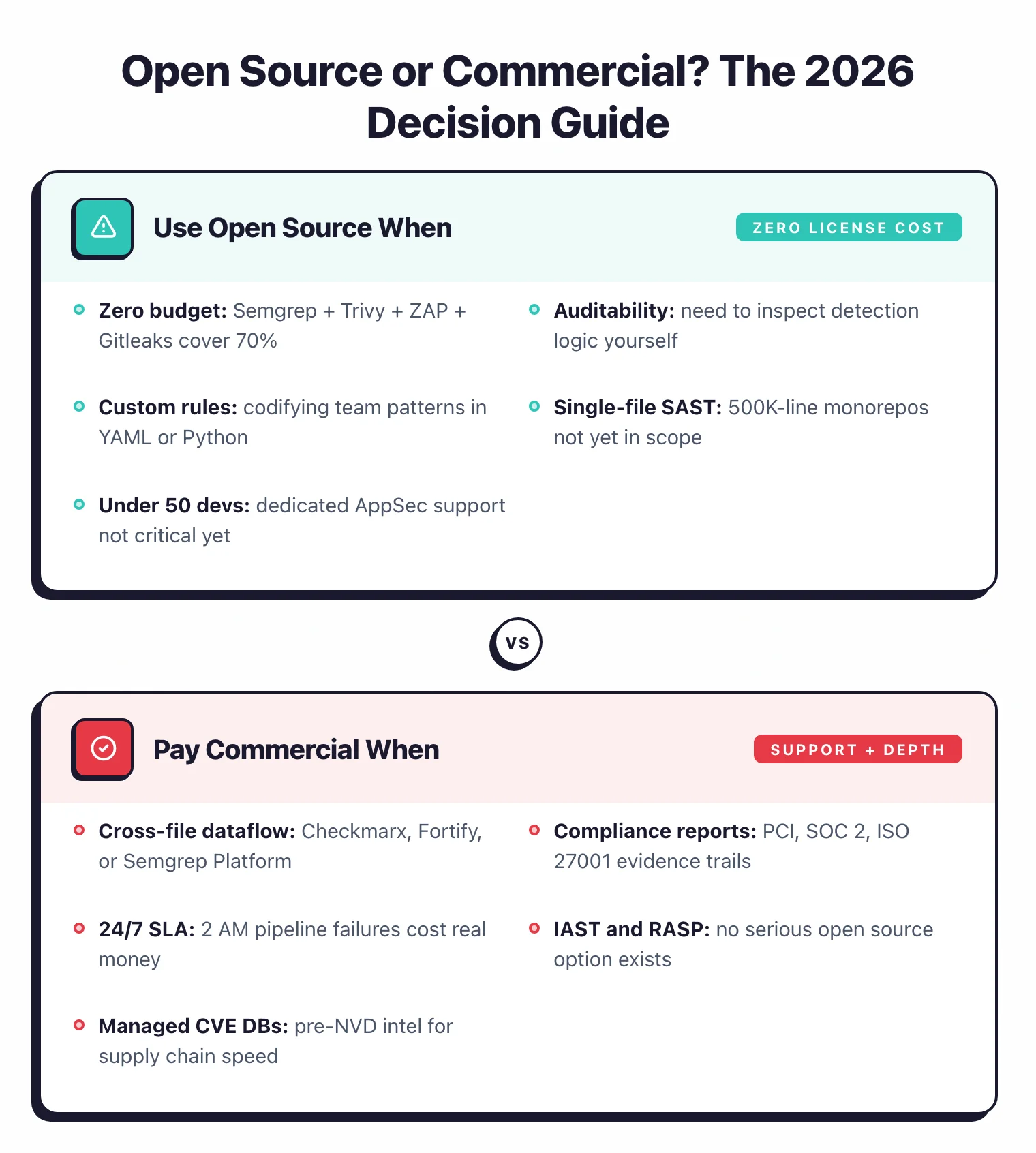
Cross-file dataflow analysis. Semgrep CE, Bandit, and gosec all do single-file analysis. If you need true inter-procedural taint tracking across a 500K-line monorepo, you need OpenGrep, Semgrep AppSec Platform, Checkmarx, or Fortify. The gap is real: Semgrep’s own benchmark shows cross-file analysis raises detection on WebGoat from 48% to 72%.
Enterprise compliance reporting. Auditors expect PCI, SOC 2, or ISO 27001 mapped reports out of the box. Open source tools produce JSON, SARIF, and HTML, which is fine for engineers but painful for compliance teams. Commercial ASPM platforms like Apiiro , Cycode , and Snyk automate this mapping with evidence trails auditors recognize.
Support and SLA. When a scanner crashes on a 2 AM pipeline run, GitHub issues are not a support contract. If downtime costs real money, pay for a vendor with a named account manager and a phone number.
Polished developer experience. IDE plugins, PR decoration, one-click fix suggestions, and a clean web UI cost engineering time that OSS projects rarely have. Snyk , Semgrep AppSec Platform , and GitHub Advanced Security all lead here. The productivity gap on a 100-developer team often justifies the spend.
IAST and full RASP. No serious open source IAST tool exists. Contrast Assess and Checkmarx IAST dominate this category. If you need runtime vulnerability detection with stack traces, commercial is the only option.
Managed vulnerability databases. Commercial SCA vendors like Snyk and Mend curate their own databases with researcher-added findings that appear weeks before NVD. For supply chain incidents where hours matter, that freshness window is worth paying for. Academic work on automated malicious npm package detection has shown the problem is solvable in principle but slow to operationalize without dedicated tooling and curation (Sejfia and Schäfer, 2022 ).
Business logic testing. DAST scanners, free and commercial alike, all struggle with auth flows, multi-step transactions, and CSRF-aware endpoints. Invicti and Bright Security add proof-based validation that eliminates the false positive triage burden ZAP and Nuclei hand back to developers.
Methodology
I evaluate open source AppSec tools against four criteria. First, license clarity: a real OSI-approved license, not a “source available” license pretending to be open source. Second, active maintenance: commits in the last 90 days and a maintainer team larger than one.
Third, real detection value — I run each tool against sample repos and compare findings against known vulnerabilities. Fourth, ecosystem fit — does it integrate with Git, CI/CD, and standard output formats like SARIF, JSON, and CycloneDX.
For detection benchmarking I use my own CandyShop test corpus alongside public benchmarks like the OWASP Benchmark Project . Health signals (stars, commit recency, contributor count, CVE disclosure cadence) come from the State of Open Source AppSec 2026 research I ran earlier this year. Reviews are updated when a tool ships a major release or changes its license model.
I also weight practical signals that benchmarks miss: how quickly new CVE templates or rules ship, how the project handles disputed findings, and whether the maintainers respond to security advisories in their own code. A tool with 20,000 stars but a 6-month issue backlog is less trustworthy than a 3,000-star project with a healthy contribution cadence.