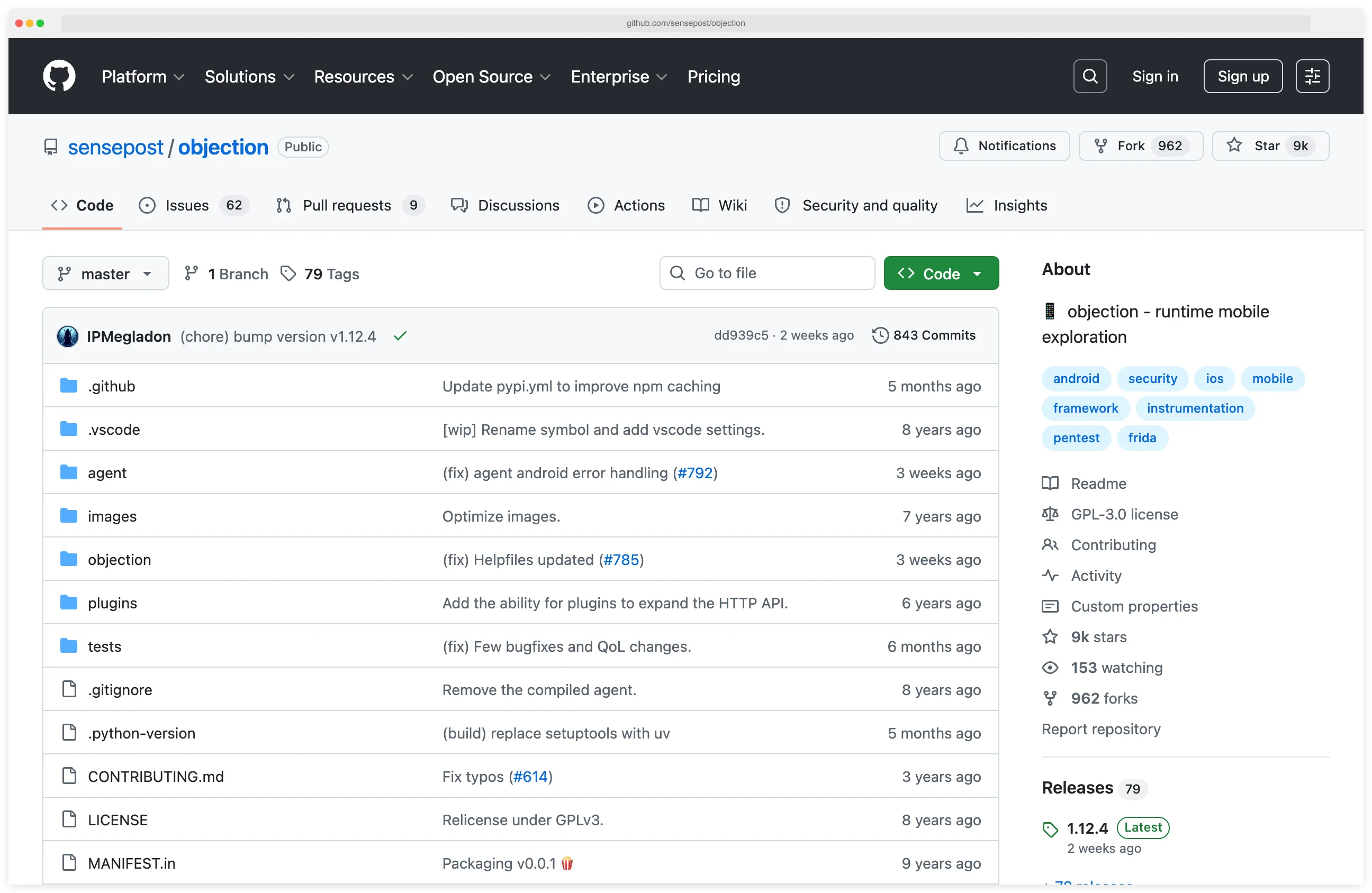
Objection is a runtime mobile security exploration toolkit built on Frida that lets pentesters hook live iOS and Android apps from an interactive command line, without writing custom JavaScript instrumentation. SensePost released it in 2016 under GPL-3.0.
With over 8,900 GitHub stars and v1.12.4 shipping in March 2026, it has become the default choice for pentesters who need quick assessment capabilities without the complexity of writing Frida scripts from scratch.
The short version
- What it is: A Python CLI that wraps Frida with pre-built commands for mobile pentesting — the 80/20 instrumentation tool for iOS and Android.
- How it works: Connects to a running app via an interactive REPL; commands like
ios sslpinning disablehook the target at runtime without modifying its binary on disk. - Runs on: Jailbroken/rooted devices via frida-server, OR non-jailbroken/non-rooted devices via
objection patchipa/patchapk(embeds frida-gadget into the app). - Best for: Quick mobile assessments — SSL pinning bypass, keychain extraction, file system inspection, memory dumps — without writing custom JavaScript hooks.
- Install:
pip3 install objection— current release v1.12.4 (March 2026), GPL-3.0, maintained by SensePost.
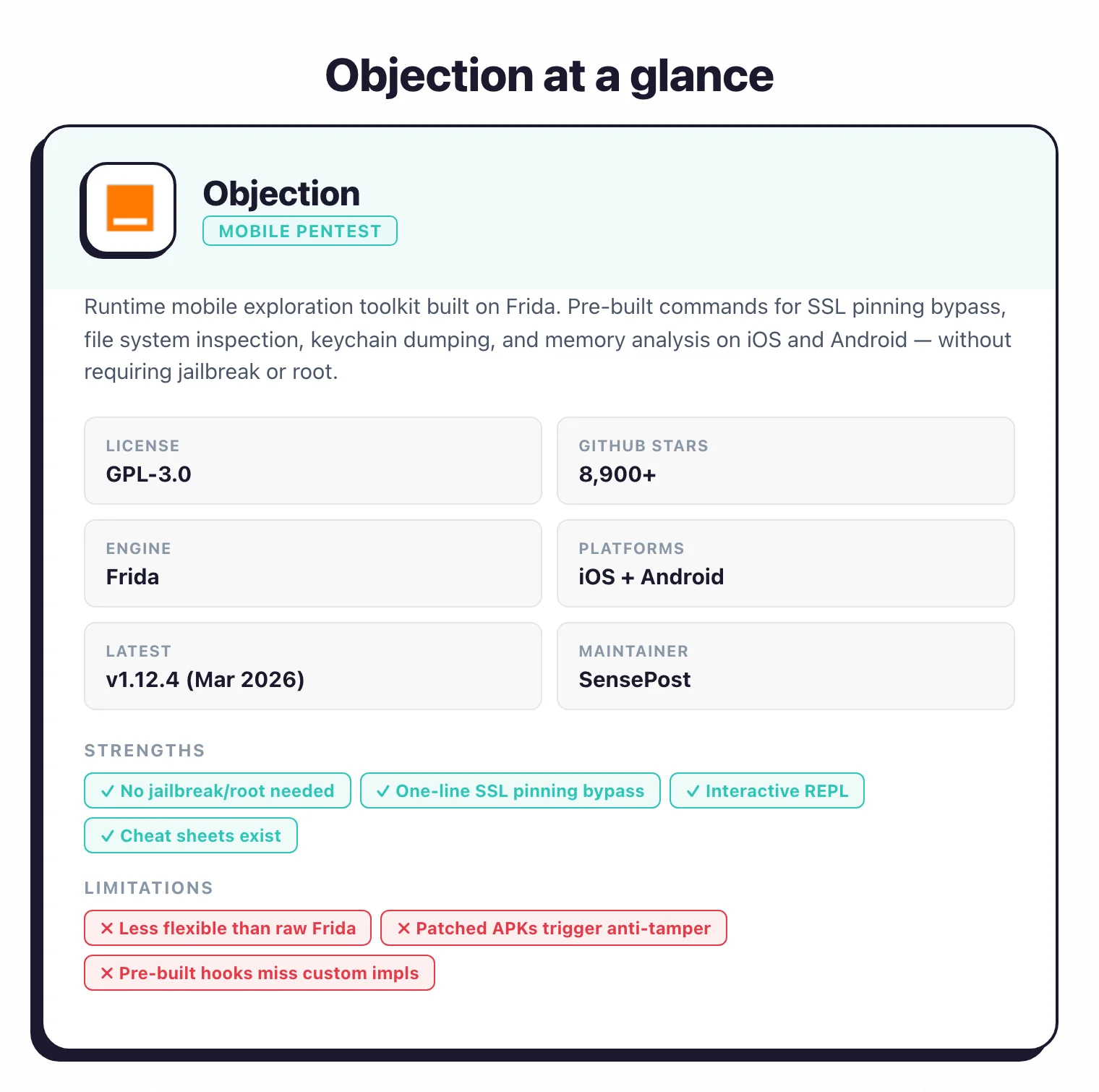
First released by SensePost in 2016 and featured at Black Hat Arsenal Europe 2017 and USA 2019, Objection is actively maintained as an instrumented mobile pentest framework. The latest release, v1.12.4 (March 2026), added a reconnect command and reconnect_spawn functionality for reattaching to targets after process restarts — a useful addition for long testing sessions where the target app may crash or be relaunched.
The main draw is accessibility. Frida expects you to write JavaScript hooks; Objection ships a command-line interface with the hooks already written for you.
That shortens the ramp-up for testers who want to work at the instrumentation layer without reading a Frida tutorial first.
Key Insight
Objection is Frida for people who don't want to write Frida scripts. It is the 80/20 mobile instrumentation tool — pre-built hooks for the tasks that show up on every mobile pentest, with a clean exit hatch to raw Frida scripting when the built-ins don't fit.
I lean on Objection for runtime mobile testing because it wraps Frida with a REPL I can drive without writing scripts first. Commands like android keystore list and ios sslpinning disable cover the first ninety percent of what I need during a pentest — dumping keychains, bypassing cert pinning, tracing class methods. For anything deeper, I drop down to the underlying Frida API.
What is Objection?
Objection is a Python command-line toolkit that wraps Frida’s dynamic instrumentation to perform runtime analysis of iOS and Android apps. It injects scripts into running processes to bypass security controls, inspect app internals, and change behavior — the original APK or IPA on disk stays untouched.
The framework runs as a command-line REPL (Read-Eval-Print Loop) where you issue commands against a live app. The interactive loop lets you react to what you find instead of scripting every check ahead of time.
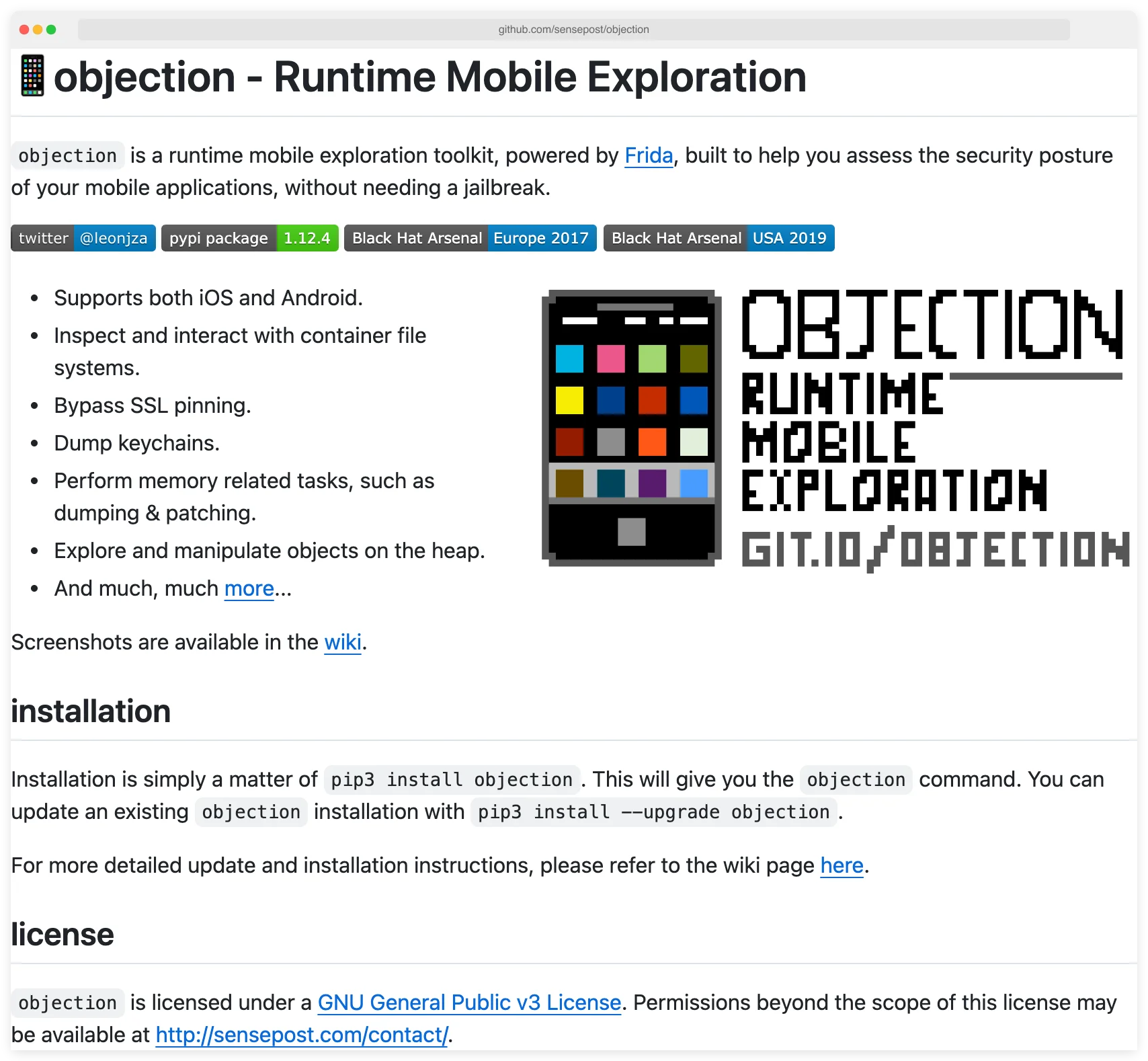
Installation is straightforward via pip (pip3 install objection), and the tool handles the complexity of Frida setup behind the scenes. For apps on non-jailbroken or non-rooted devices, Objection can patch APKs and IPAs to embed frida-gadget, enabling testing without system-level access.
Note: Objection needs a jailbroken/rooted device with frida-server, or a Frida-patched APK/IPA. It does not work on production-signed apps you can't repackage — App Store and Play Store builds pulled directly from a non-jailbroken phone are off-limits unless you can re-sign them.
Pick your next step
Drop down to Frida
When Objection's pre-built hooks miss a custom pinning routine, raw Frida is the escape hatch.
→Pair with mitmproxy
Once SSL pinning is disabled, mitmproxy is the proxy I use to inspect and rewrite the app's HTTPS traffic.
→Browse the category
All mobile pentesting and reverse-engineering tools I've reviewed, grouped by static, runtime, and proxy roles.
→Key features
SSL Pinning Bypass
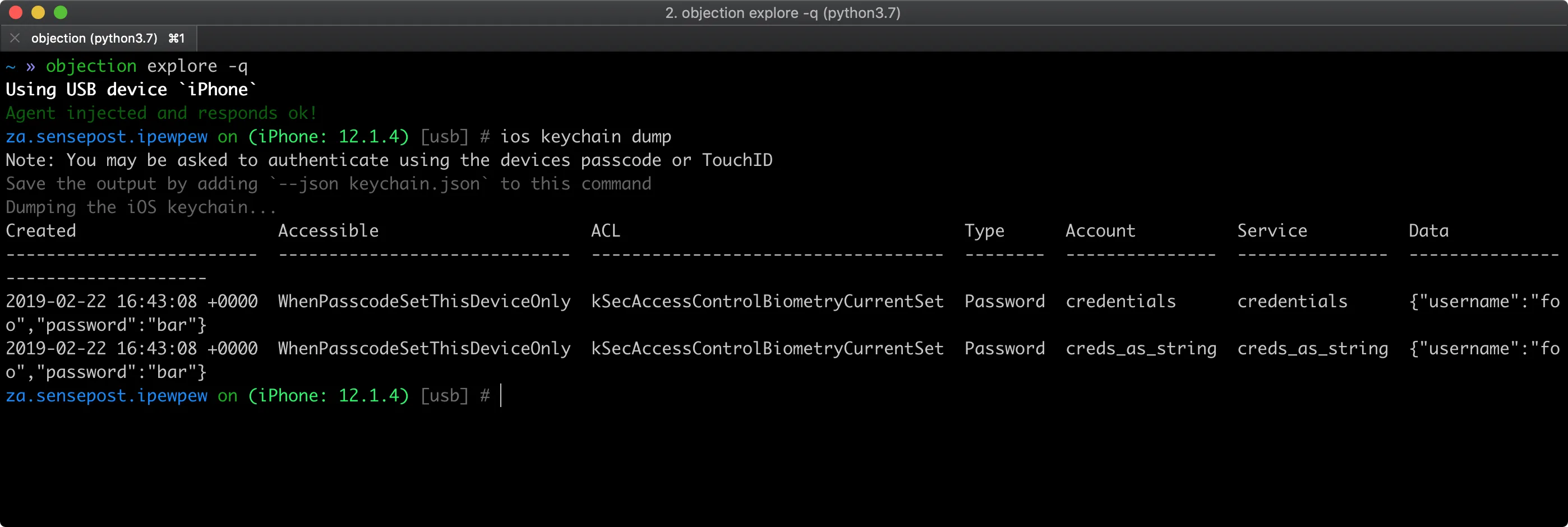
SSL pinning bypass is a runtime patch that disables an app’s certificate-pinning checks so a proxy like Burp or mitmproxy can intercept its HTTPS traffic. It is Objection’s most-used feature.
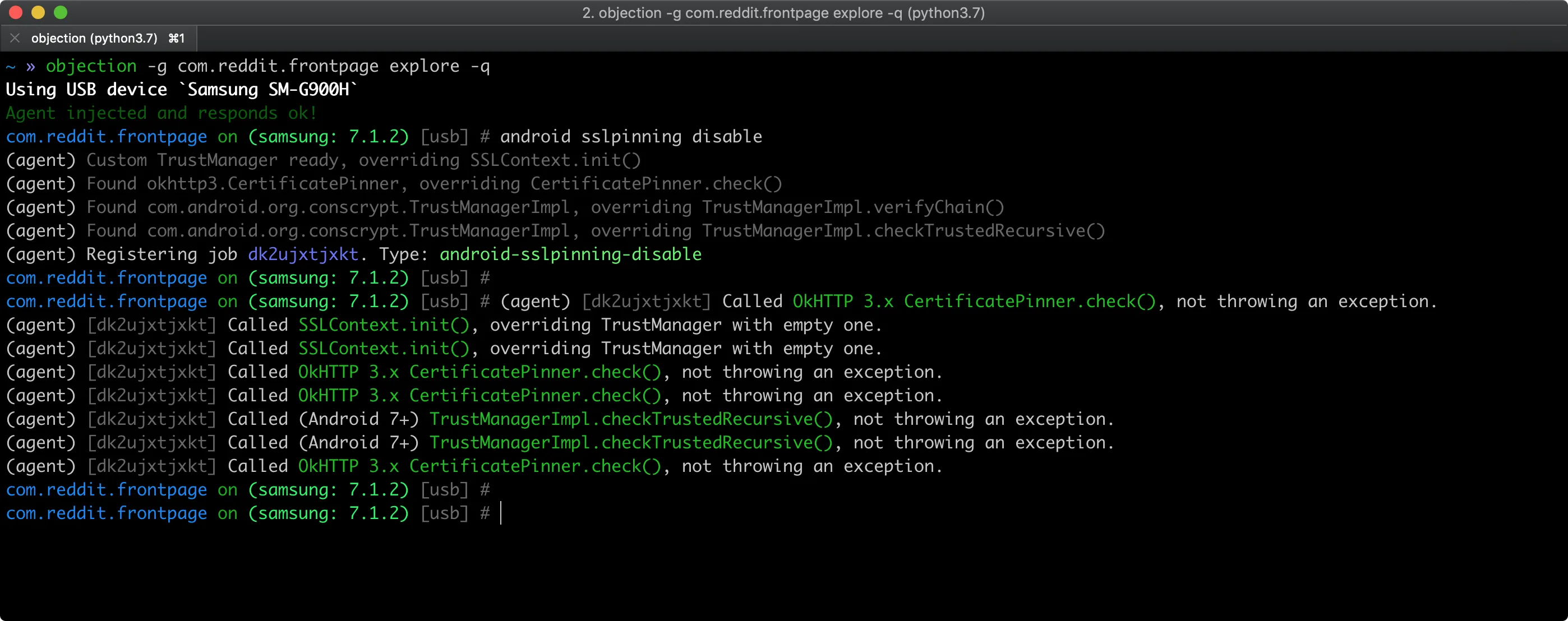
A single command — ios sslpinning disable or android sslpinning disable — defeats most pinning implementations and lets you intercept HTTPS traffic with mitmproxy or Burp Suite.
That replaces hours of manual hook writing for a task that lands on almost every mobile pentest.
Pro tip: Once you're in the REPL with objection --gadget com.target.app explore, the one command that pays for itself before lunch is ios sslpinning disable (or android sslpinning disable). Run it before pointing your phone at mitmproxy or Burp — most apps surrender their TLS traffic immediately, no custom hook required.
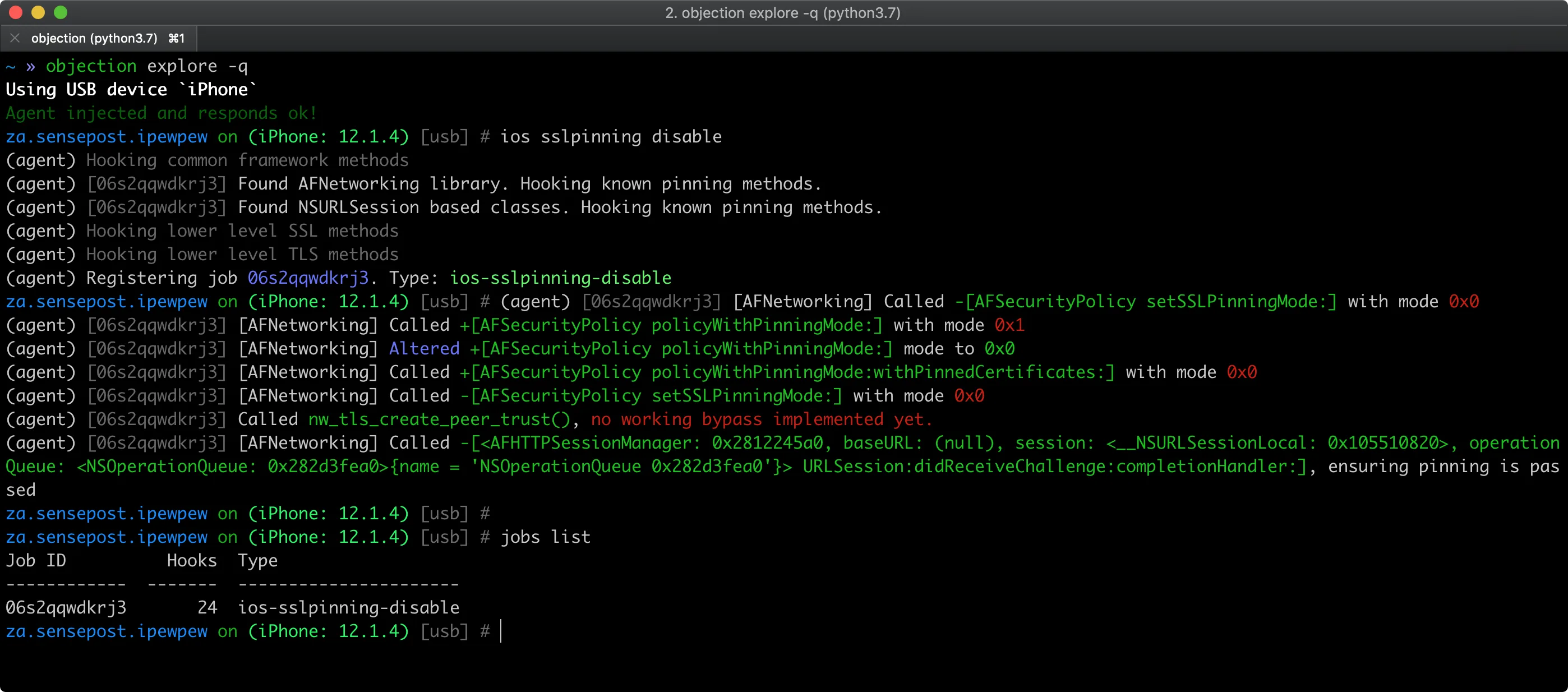
The SSL pinning bypass works by hooking common pinning libraries and custom implementations at runtime. It covers frameworks like AFNetworking on iOS and OkHttp on Android, as well as many custom validation routines.
File System and Container Exploration
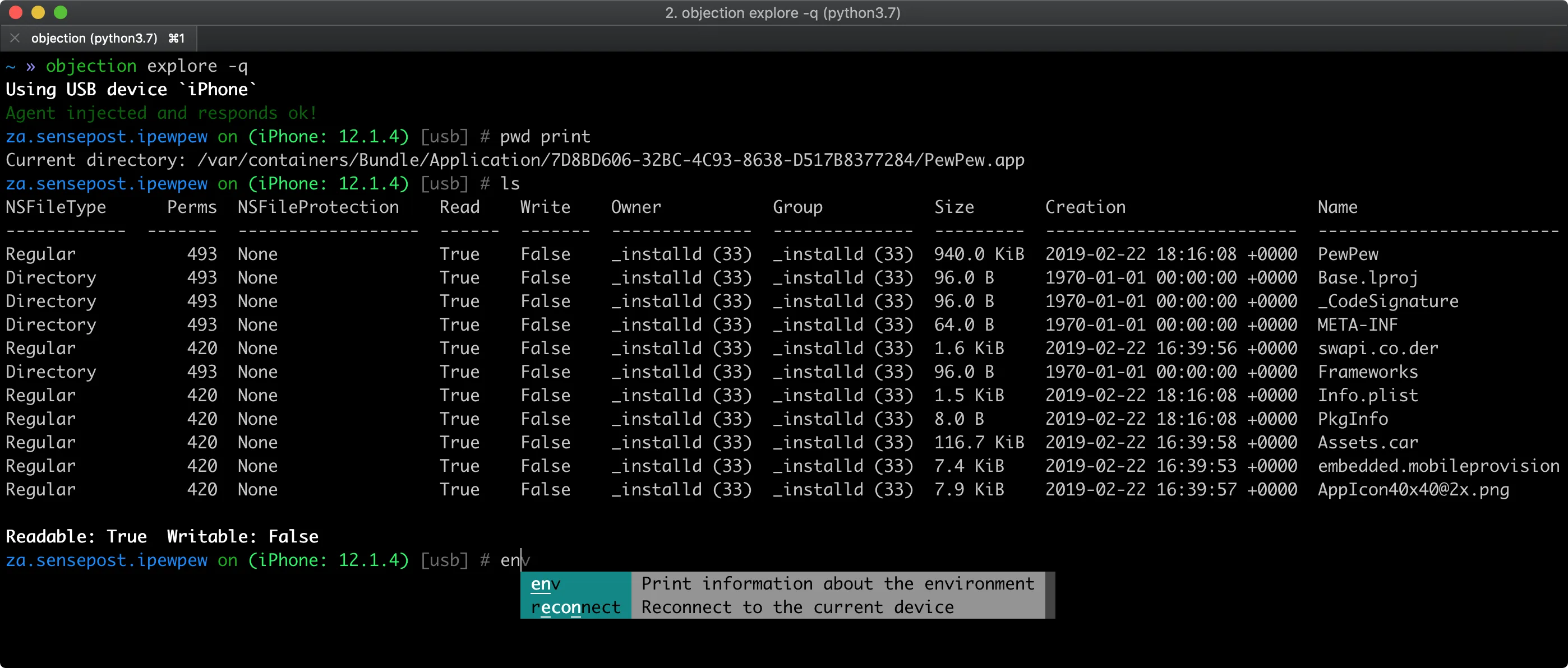
Objection provides commands to browse the app’s file system, download databases and configuration files, and upload modified versions for testing.
On iOS, you can navigate the app’s Documents, Library, and tmp directories. On Android, you can explore /data/data/
That access is where hardcoded credentials, SQLite secrets, and sloppy local encryption usually turn up. You can dump binary cookies, read plist files, and poke at the app’s own encryption routines.
Memory and Heap Analysis
Objection ships commands for memory dumps and heap walks. You can grep process memory for API keys or tokens, pull objects off the heap to inspect runtime state, and pinpoint where sensitive data sits in RAM.
That is how insecure storage bugs surface — apps that hold credentials in memory long after they are needed, or never zero out buffers after use.
Integration with Mobile Security Workflows
Objection slots into a normal mobile testing loop. Start by decompiling the APK with Jadx to map the app’s classes and pick out the methods worth poking at. Then use Objection to hook those methods at runtime, change their behavior, and watch what happens.
For apps with native libraries, reverse the compiled code with Ghidra, then drive Objection’s hook commands against whatever you find. Raw Frida scripts load straight into Objection via the import command when you need something the built-ins don’t cover.
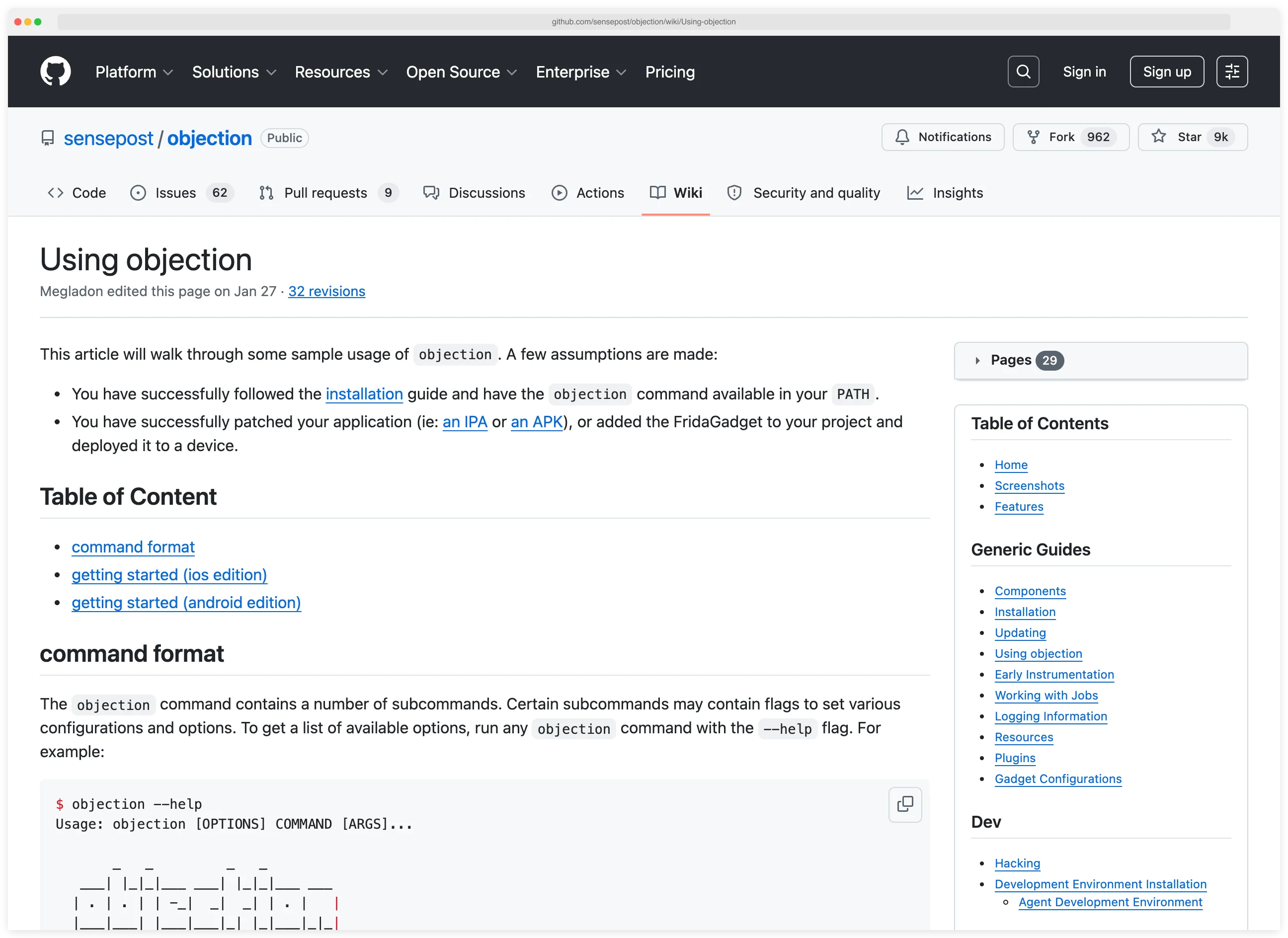
The official wiki documents every command, the patching workflow, and the gadget configuration knobs you’ll need for non-rooted testing.
App Patching for Non-Rooted Testing
A Frida gadget is a shared library (.so on Android, .dylib on iOS) that embeds the Frida runtime into an app so Objection can instrument it without frida-server or device-level privileges.
The objection patchapk (Android) and objection patchipa (iOS) commands handle the embedding for you. That opens up testing on stock, non-rooted Android phones and non-jailbroken iPhones — the same hardware most end users carry.
The patched app behaves like the original but loads the Frida runtime at launch, which gives Objection full access without needing system-level privileges.

Objection is registered in the OWASP Mobile Application Security Testing Guide tool catalog as MASTG-TOOL-0038. It is the canonical runtime tool for several MASTG dynamic-analysis tests: MASTG-TEST-0050 (testing client-side anti-tampering and SSL pinning), MASTG-TEST-0023 (testing key management with hardware-backed keystores), and MASTG-TEST-0026 (testing for sensitive data exposed in process memory). When I write up findings against MASVS-Resilience or MASVS-Crypto, citing the relevant Objection command alongside the MASTG test ID gives the report a direct mapping back to the OWASP standard.
When to use Objection
Strengths:
- Much faster than writing Frida scripts from scratch
- Beginner-friendly CLI with a well-documented wiki
- Covers the mobile pentest tasks that show up on every assessment
- Active development with regular releases
- Strong community and plenty of public cheat sheets
- Works without jailbreak or root via app patching
- Free and open source under GPL-3.0
- Cross-platform support for iOS and Android
Limitations:
- Less flexible than hand-written Frida scripts for unusual targets
- Pre-built hooks can miss heavily customized pinning or auth code
- You still need to learn the command syntax and flags
- Patched APKs may trip anti-tamper checks
- Running many hooks at once adds performance overhead
- Edge cases still mean dropping back to raw Frida
Objection alternatives
A few tools cover overlapping ground when Objection’s pre-built hooks aren’t the right fit:
- Frida — the runtime engine Objection wraps. Drop down to raw Frida when I need a custom hook, a deep call-graph tracer, or anything outside Objection’s command catalog. Slower to write, much more flexible.
- Drozer — Android-only, but built around IPC and content-provider exploitation rather than runtime instrumentation. Use Drozer when the threat model is exported components and intent-filter abuse, not network or memory.
- Magisk + adb — root-based Android workflow with no instrumentation layer. I reach for it when the app I’m testing requires real root and Objection’s patchapk path triggers anti-tamper.
- Brida + Burp Suite — pairs Burp’s proxy with a Frida bridge. Useful when the testing focus is the HTTPS request/response pair and the app’s instrumentation is secondary.
- otool, lldb, class-dump (iOS) — low-level static and runtime inspection on iOS without Frida. Slower for routine pentest tasks but invaluable when the target hardens itself against Frida specifically.
For the most-asked head-to-head, see the mobile pentesting workflow guide, which sketches when Objection wins and when raw Frida is the better answer.
Getting started
pip3 install objection to install the toolkit and its dependencies including Frida.objection -g com.example.app explore to launch the interactive REPL.objection patchapk -s app.apk, install the patched app, run it, then connect with objection explore.ios sslpinning disable to bypass pinning, android hooking list activities to enumerate components, or env to inspect the app’s file system paths.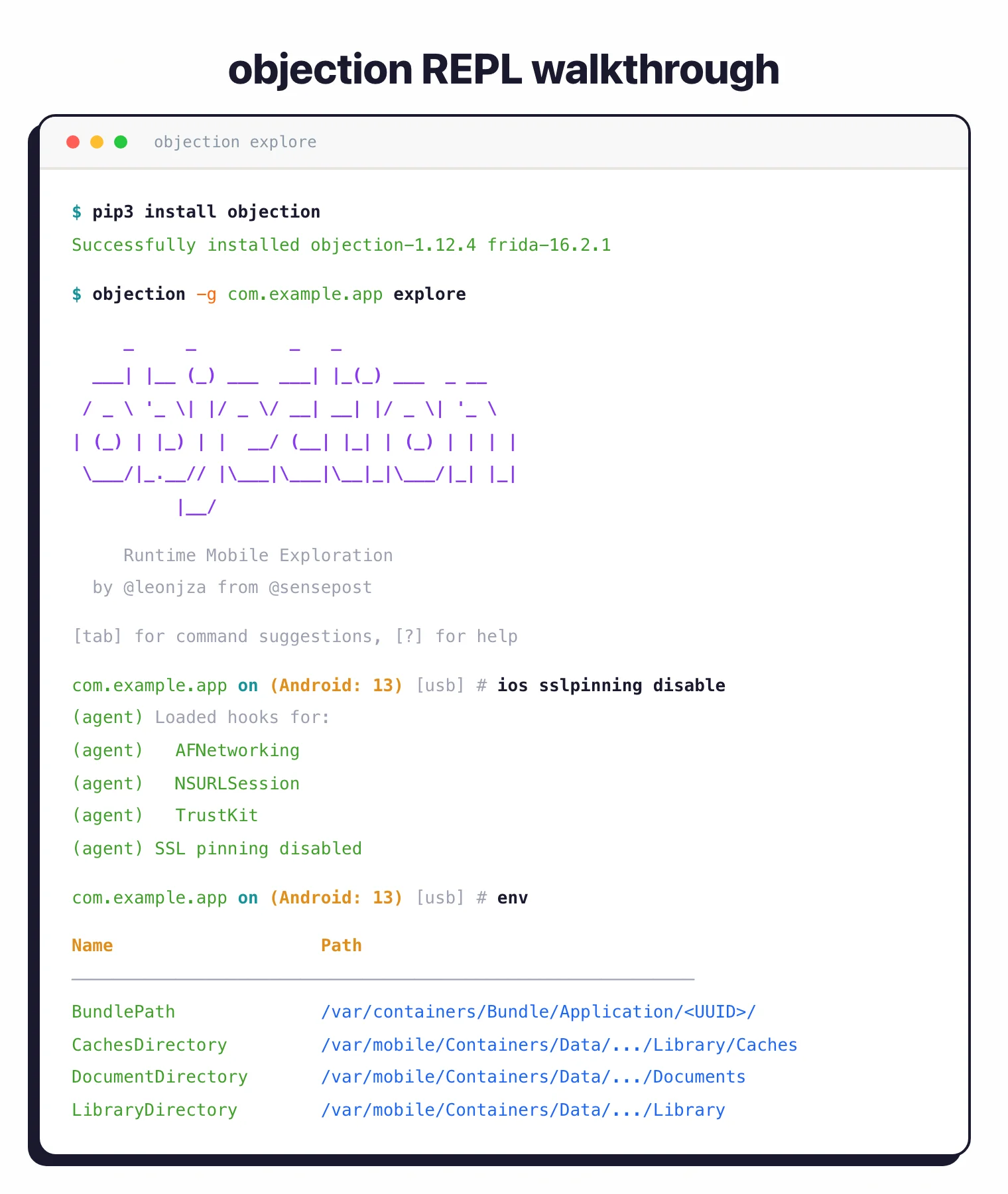
Combine Objection with mitmproxy for traffic interception, Jadx for static analysis, and Frida scripts when you need custom capabilities beyond Objection’s built-in commands.
Objection pricing and licensing
Objection is fully free and open source under GPL-3.0. There is no commercial edition, no paid hosted service, and no per-seat fee — the toolkit ships from a single repository maintained by SensePost. I install it with pip3 install objection and run it inside commercial penetration tests without any licensing dance.
Note: this page is about the SensePost mobile-pentesting toolkit, not about sales or legal objection-handling tools. The two share a name but solve different problems.
Frequently Asked Questions
What is Objection?
How does Objection differ from Frida?
Can Objection work on non-jailbroken devices?
Is Objection suitable for beginners?
How do I bypass SSL pinning with Objection?
objection --gadget com.example.app explore, run ios sslpinning disable on iOS or android sslpinning disable on Android. Objection hooks common pinning libraries (AFNetworking, OkHttp, NSURLSession) at runtime, letting Burp Suite or mitmproxy intercept the app’s HTTPS traffic immediately. For custom pinning implementations that the built-in hooks miss, you can drop to a raw Frida script and load it through Objection’s import command.