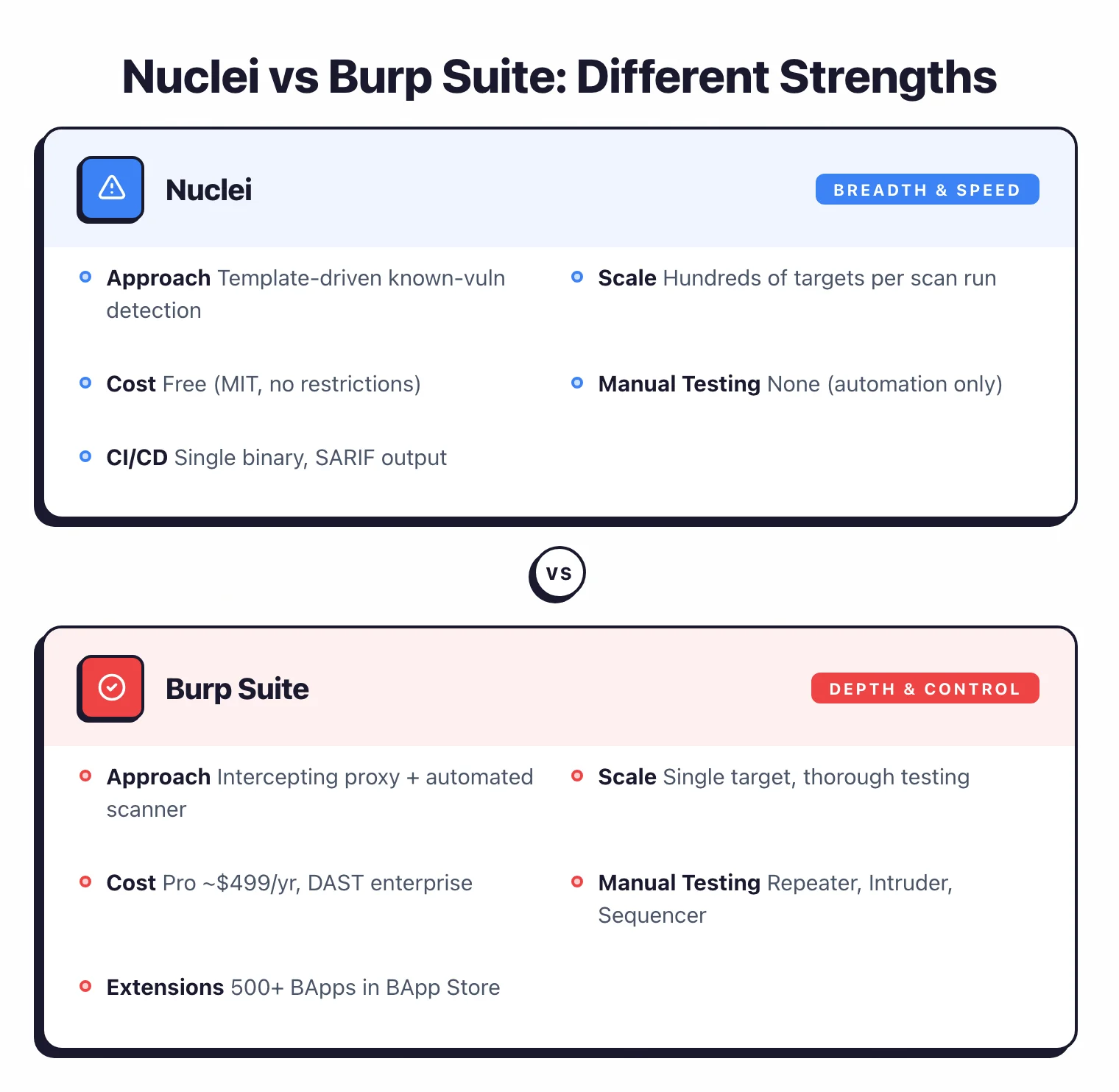
- Nuclei is a free, MIT-licensed scanner with 27,000+ GitHub stars that runs 10,000+ community YAML templates for known vulnerability detection. Burp Suite is PortSwigger's commercial intercepting proxy combining automated scanning with manual pentesting tools.
- Nuclei scans across six protocols (HTTP, DNS, TCP, SSL, WebSocket, headless browser) at a default rate of 150 requests per second. Burp Suite focuses on HTTP/HTTPS/WebSocket traffic through its intercepting proxy for deep, single-application testing.
- Burp Suite Professional costs approximately $499 per year per user (per PortSwigger's website) and unlocks the full automated scanner. Nuclei is completely free with no usage limits or feature restrictions.
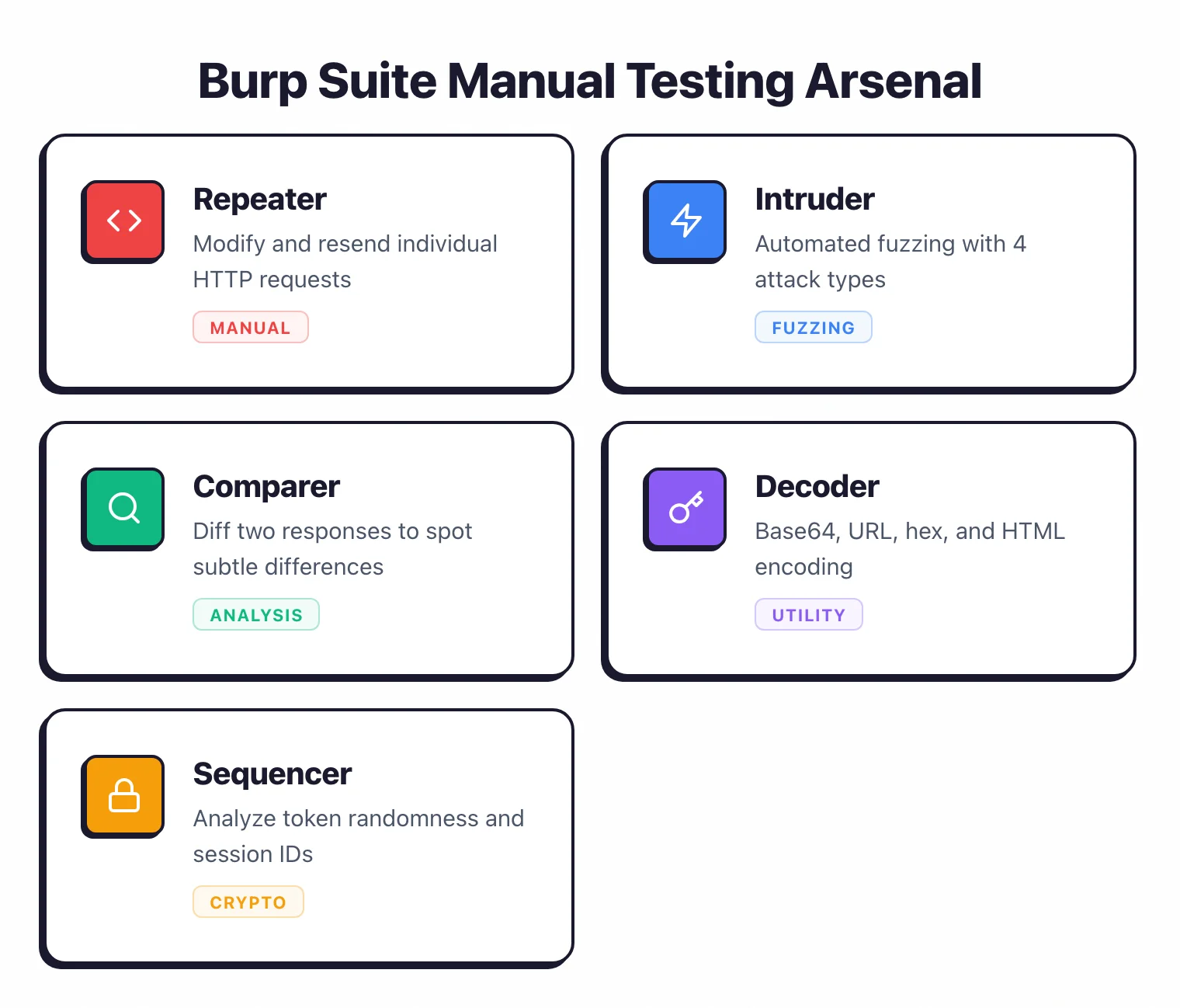
- Burp Suite's five manual tools — Repeater, Intruder, Comparer, Decoder, and Sequencer — have no equivalent in Nuclei. Nuclei is template-driven automation only, with no interactive testing capabilities.
- The nuclei-templates community publishes new CVE templates within hours of disclosure. Burp Suite DAST (formerly Enterprise) runs from Docker for CI/CD integration with Jenkins, GitHub Actions, GitLab CI, and Azure DevOps.
Which Is Better: Nuclei or Burp Suite?
Nuclei is a free, open-source vulnerability scanner that runs 10,000+ community-maintained YAML templates against targets to detect known CVEs, misconfigurations, and exposures.
Burp Suite is PortSwigger’s commercial web application pentesting toolkit built around an intercepting proxy with both automated scanning and manual testing tools. Nuclei excels at breadth — scanning hundreds of hosts across HTTP, DNS, TCP, SSL, and WebSocket protocols at 150 requests per second by default.
Burp Suite excels at depth — crawling a single web application, intercepting live traffic, and giving pentesters hands-on tools like Repeater, Intruder, and a 500+ extension ecosystem.
Pick Nuclei for fast, scalable known-vulnerability detection across infrastructure; pick Burp Suite for thorough, interactive web application security testing.
What Are the Key Differences?
| Feature | Nuclei | Burp Suite |
|---|---|---|
| License | Free (MIT) | Community (free, limited), Professional (~$499/yr), DAST (enterprise) |
| GitHub Stars | 27,000+ | N/A (closed source) |
| Maintained By | ProjectDiscovery | PortSwigger |
| Approach | Template-driven scanning for known vulnerabilities | Intercepting proxy with automated and manual testing |
| Protocols | HTTP, DNS, TCP, SSL, Websocket, Headless browser | HTTP, HTTPS, WebSocket |
| Vulnerability Detection | 10,000+ YAML templates (CVEs, misconfigs, exposures) | Active and passive scanning engine |
| Manual Testing Tools | None | Repeater, Intruder, Comparer, Decoder, Sequencer |
| Intercepting Proxy | No | Yes (core feature) |
| Crawling | No (template-driven, does not crawl) | Yes (automated crawling and content discovery) |
| Extensions | Custom YAML templates | 500+ BApps in BApp Store (Java/Python) |
| AI Features | AI-powered template generation (-ai flag) | Burp AI for scan analysis and attack suggestions |
| CI/CD Integration | CLI binary, SARIF/JSON output, Docker image | DAST edition: Docker-based for Jenkins, GitHub Actions, GitLab CI, Azure DevOps |
| Rate Limiting | Default 150 req/sec, configurable | Configurable (throttled in Community Edition) |
| Output Formats | JSON, JSONL, SARIF, Markdown | HTML, XML (Professional); JUnit, Burp XML (DAST) |
| Multi-Target Scanning | Yes (scan lists of targets in one run) | Single target per scan |
| Written In | Go | Java |
| Issue Tracking | Jira, GitHub Issues, GitLab, Elasticsearch, Splunk | Jira, Trello, GitLab, Slack, Splunk |
Nuclei vs Burp Suite: How Do They Compare?
How does Nuclei scanning differ from Burp Suite?
Nuclei and Burp Suite take fundamentally different approaches to vulnerability detection. Nuclei is template-driven: each of its 10,000+ YAML templates defines a specific HTTP request (or DNS/TCP/SSL query) and a response pattern that indicates a vulnerability.
You select templates by tag, severity, or CVE ID, point Nuclei at a list of targets, and it fires off the matching checks in parallel. If a response matches the template’s conditions, Nuclei reports a finding.
There is no crawling, no traffic interception, no interactive testing — just fast, declarative pattern matching against known issues.
Burp Suite is proxy-based. It sits between your browser and the target application, capturing all HTTP/HTTPS traffic.
From that intercepted traffic, you can manually probe requests with Repeater, fuzz parameters with Intruder, or run the automated scanner against specific endpoints or the entire application.
The scanner crawls the application, discovers content, and actively probes for vulnerabilities using PortSwigger’s proprietary detection engine.
The practical result: Nuclei tells you “this target has CVE-2024-XXXX” or “this server exposes a default admin panel.” Burp Suite helps you discover unknown vulnerabilities in custom application logic — SQL injection in a form, XSS in a parameter, IDOR in an API endpoint.
Which tool is faster for large-scale scanning?
Nuclei is purpose-built for scanning at scale. According to ProjectDiscovery’s documentation , the default configuration processes 150 requests per second across 25 parallel hosts and 25 parallel templates simultaneously.
Request clustering groups similar requests to reduce total traffic, and you can scan hundreds or thousands of targets in a single run from a target list.
The open-source community, which maintains the nuclei-templates repository with 27,000+ GitHub stars on the main project, often publishes new CVE templates within hours of public disclosure — letting teams check entire infrastructure against emerging threats quickly.
Burp Suite is designed for depth on a single target. You scan one application at a time, thoroughly.
The automated scanner crawls every path, probes every parameter, and tests every input.
Community Edition throttles scan speed; Professional (priced at approximately $499 per year per user, per PortSwigger’s website) removes those limits.
The DAST edition runs automated scans in CI/CD via Docker, but still focuses on one application per scan.
For checking 500 hosts against known CVEs: Nuclei. For thoroughly testing one web application for all vulnerability types: Burp Suite.
Does Nuclei support manual penetration testing?
Nuclei does not support manual testing — it is a template-driven automation tool with no interactive capabilities. You cannot intercept traffic, modify requests on the fly, or fuzz parameters interactively with Nuclei.
This is a deliberate design choice: Nuclei automates known-vulnerability checks so security teams do not have to run them manually, freeing pentesters to focus on exploratory testing with other tools.
Burp Suite’s manual tools are what separate it from every other DAST tool. Repeater lets you send individual requests and iterate on payloads.
Intruder automates fuzzing with four attack types: Sniper, Battering Ram, Pitchfork, and Cluster Bomb. Comparer diffs two responses to spot subtle differences.
Decoder handles Base64, URL, hex, and HTML encoding. Sequencer analyzes randomness in tokens and session IDs.
These five tools, combined with the intercepting proxy, give pentesters full control over every request during exploratory testing.
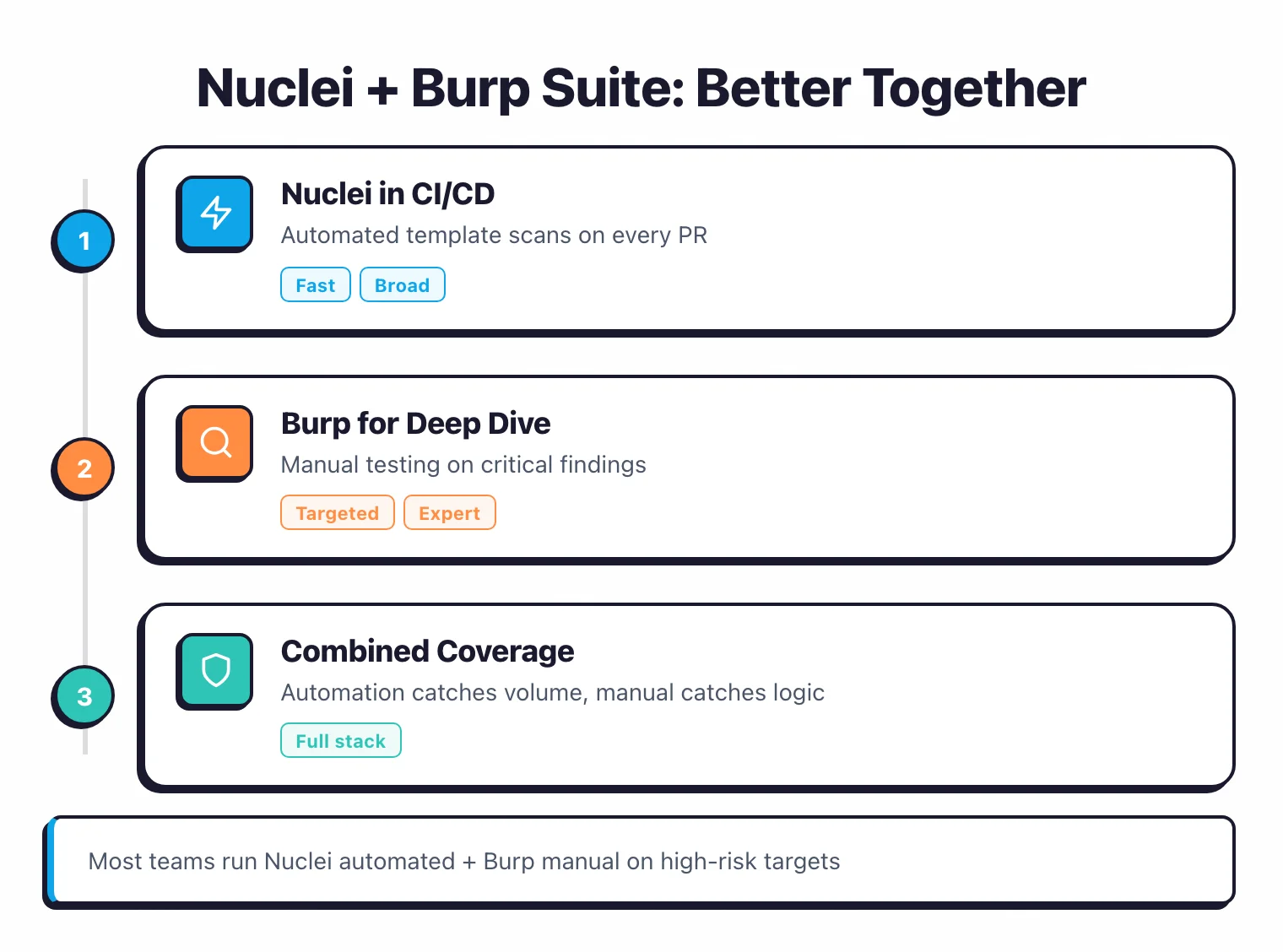
Most professional pentesters use both tools together — Nuclei for automated known-vuln sweeps, Burp Suite for hands-on application testing where human judgment matters.
How do Nuclei templates compare to Burp Suite extensions?
Both tools are highly extensible, but through different mechanisms and for different purposes.
Nuclei extends through YAML templates — each template defines a protocol, request pattern, matchers, and extractors in a declarative format that requires no programming knowledge.
The nuclei-templates repository hosts 10,000+ community-maintained templates covering CVEs, misconfigurations, exposures, default credentials, and technology detection. ProjectDiscovery also added an -ai flag that generates YAML templates from natural language descriptions.
Burp Suite extends through PortSwigger’s BApp Store , which lists 500+ extensions written in Java or Python.
Extensions add capabilities like Active Scan++ for expanded active scanning, Autorize for access control testing, JWT Editor for token manipulation, and Logger++ for advanced request logging.
Custom extensions hook into Burp’s request/response pipeline through the Montoya API, giving developers deep control over the testing workflow.
The key difference: Nuclei templates are simpler (YAML, no code) and focused purely on detection. Burp BApps are more powerful (Java/Python) and can modify the entire testing workflow, add new UI panels, and interact with external services.
When Should You Choose Nuclei vs Burp Suite?
Choose Nuclei when you need to…
- Scan large numbers of targets for known vulnerabilities quickly
- Automate CVE, misconfiguration, and exposure detection across infrastructure
- Test beyond HTTP — DNS, TCP, SSL, and Websocket protocols included
- Avoid license costs entirely (MIT licensed, no feature restrictions)
- Drop a single Go binary into your CI/CD pipeline with SARIF or JSON output
- Get community templates for new CVEs within hours of disclosure
Choose Burp Suite when you need to…
- Perform interactive web application penetration testing
- Manually craft and replay requests with Repeater, Intruder, Comparer, Decoder, Sequencer
- Intercept and modify live HTTP/HTTPS traffic through a proxy
- Crawl and scan individual web applications for unknown vulnerabilities
- Extend your workflow with 500+ BApp Store extensions
- Run automated CI/CD scans via Burp Suite DAST (formerly Enterprise) in Docker
Nuclei and Burp Suite solve different problems. Nuclei checks many targets for known vulnerabilities fast.
Burp Suite digs into a single web application for unknown bugs. Many security teams run both — Nuclei for breadth, Burp Suite for depth.
For more options, browse AppSec Santa’s DAST tools category.
Nuclei + Burp Suite: do they replace each other?
The short answer is no — they solve adjacent problems. Nuclei is best at fast, scalable, known-vulnerability scanning across many targets. Burp Suite is best at hands-on testing of individual web applications where human judgment, request manipulation, and chained-vulnerability discovery matter.
Most pentesters and AppSec teams I have seen run both. A typical workflow looks like this:
- CI/CD pipeline — Nuclei runs on every pull request, filtering by
-tags cve,criticalto fail builds on known vulnerabilities and exposed secrets. Output goes to SARIF for GitHub Code Scanning. - Pre-engagement reconnaissance — Nuclei sweeps the target’s domain list with
-severity high,criticalto surface obvious wins before a manual pentest starts. - Manual testing phase — Burp Suite Professional drives the engagement: intercepting proxy maps the application, Repeater iterates on payloads, Intruder fuzzes parameters, and the active scanner runs against authenticated endpoints.
- Post-engagement validation — Burp Suite confirms findings with proof-of-concept screenshots; Nuclei generates the vulnerability inventory in JSON for client-facing reports.
If you only have time for one, the choice depends on your role. Application pentesters and red-teamers pick Burp Suite because manual testing is the work. Security engineers and CI owners pick Nuclei because automation at scale is the work.
The two tools rarely overlap on the same finding type because Nuclei’s template-driven model and Burp’s interactive proxy model are structurally different.
Frequently Asked Questions
Is Nuclei better than Burp Suite?
Is Nuclei free?
Can Nuclei replace Burp Suite?
Which tool is better for CI/CD?
Can I use Nuclei and Burp Suite together?

Founder, AppSec Santa
Years in application security. Reviews and compares 201 AppSec tools across 12 categories to help teams pick the right solution. More about me →
