AppSec Santa Weekly tracks new AppSec tools and the latest releases from 290+ existing ones. Each issue covers what shipped, what changed, and why it matters.
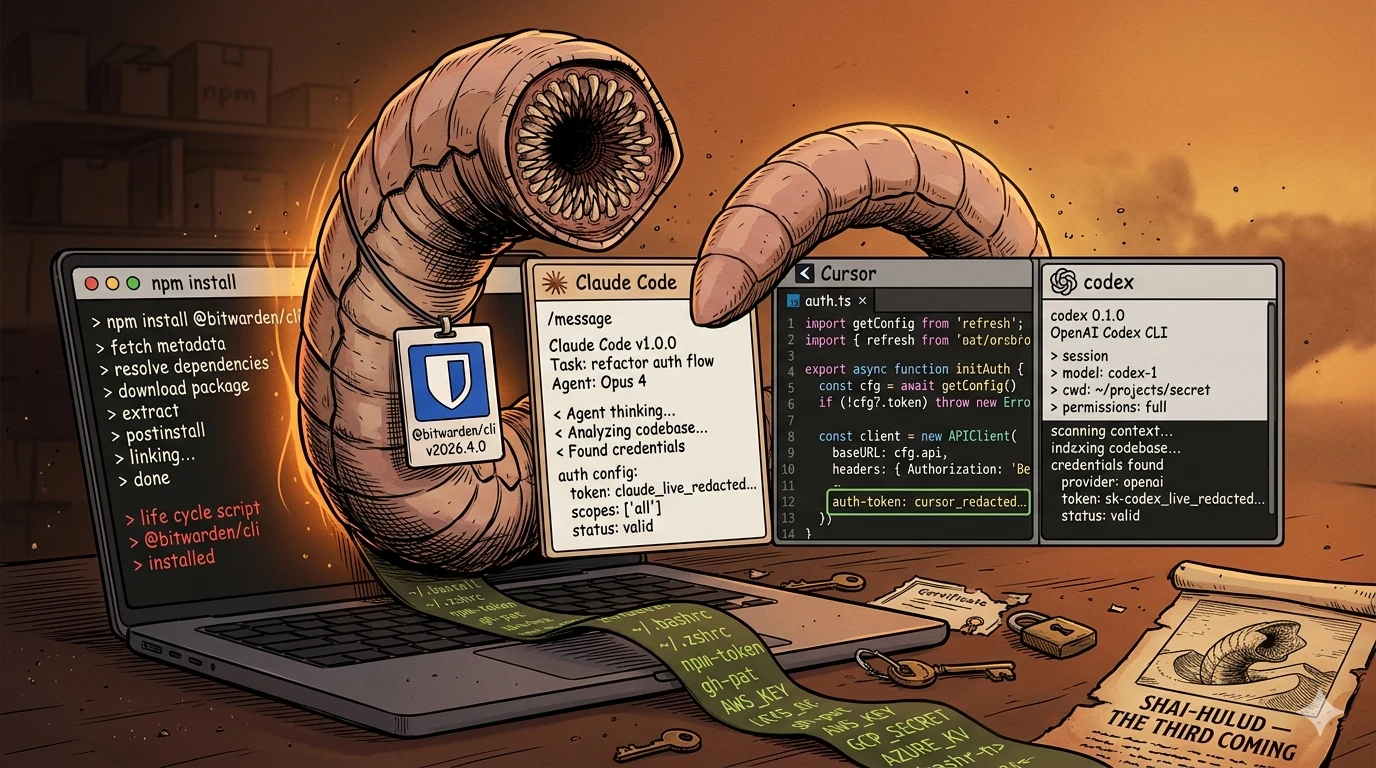
This week, the supply-chain attackers stopped pretending. The Bitwarden CLI got backdoored for 90 minutes with a worm that specifically hunts Claude Code, Gemini CLI, and OpenAI Codex sessions.
Endor’s Agent Security League jumped six points week-over-week — Cursor with GPT-5.5 now sits at 23.5% security correctness. And LAPSUS$ posted Checkmarx’s source code on the dark web, fingering the same campaign that hit Bitwarden.
Busy week on the vendor side too: Kyverno ships two CVE-fix backports, Semgrep tightens its HTTP debug logging, TruffleHog cuts three releases in a single day, and Socket extends reachability to PHP.
This Week at a Glance
49 releases across 7 active categories — the headline pattern is everywhere.
- AI Security (15) — every model-coverage tool is racing GPT-5.5 and Claude Opus 4.7 into their providers; Promptfoo shipped support for both in 4 days.
- SCA (15) — the category absorbing the Bitwarden fallout. Reachability quietly extends to PHP via Socket; PEP 751
pylock.tomladoption now visible in Dependabot too. - SAST (9) — parser quality week. OpenGrep touched six languages in one cut, Semgrep fixed Scala 3.4+, TruffleHog shipped three releases on April 21 — including a same-day revert.
- IaC Security (6) — Kyverno v1.16.4 backports two CVE fixes; the rest is housekeeping.
- Container Security (2) — quiet, two patch releases (NeuVector, StackRox).
- ASPM (1) — DefectDojo parser bug fix.
- Mobile (1) — Ostorlab/oxo ships its first feature release after last week’s rename.
Zero releases this week from DAST, IAST, RASP, API Security.
New on the Radar
Bitwarden CLI gets backdoored to hunt AI coding assistants. On April 22, an attacker pushed a malicious @bitwarden/cli@2026.4.0 to npm and held it there for 1 hour 33 minutes — 5:57 PM to 7:30 PM Eastern. Bitwarden caught it, pulled the package, and shipped 2026.4.1 as a clean re-release of the prior version. About 334 installs went out during the window.
The novelty is in the payload, not the package. Shai-Hulud is the npm-worm campaign first observed in late 2025 that abuses publisher tokens to self-replicate across the registry. This is its third confirmed variant, and it adds a module that nothing else I’ve seen in the wild has shipped:
- AI assistant hijacking — probes
$PATHfor Claude Code, Gemini CLI, OpenAI Codex, Kiro, Aider, and OpenCode; sends each one a “Hello” prompt; if any responds (proof of an active auth token), injects a persistent shell hook into~/.bashrcand~/.zshrc - Self-propagating worm — when it finds an npm token with
bypass_2faandpackage:write, it republishes every package the victim can publish, with a malicious preinstall hook - Seven-surface secret harvest — SSH keys, GitHub and npm tokens, AWS Secrets Manager and SSM Parameter Store, GCP Secret Manager, Azure Key Vault, shell history, and a
sudo python3GitHub Actions runner-memory scraper
Endor Labs, JFrog Research, and Socket all traced the exfil to audit.checkmarx.cx — the same Checkmarx infrastructure that the March 23 supply-chain incident touched. The CI/CD pipeline that rebuilds Checkmarx’s open-source extensions appears to be the staging point.
The C2 channel is unusual too: GitHub commit dead-drops with RSA-signed command delivery, so seizing one repo doesn’t kill the campaign.
My take: Two things are different about this one. The malware reads your
$PATHfor AI assistants — an authenticated Claude Code or Codex session is now treated as a higher-value persistence target than~/.aws/credentials. The worm pattern then compounds a single dev’s npm token into the entire publish surface they touch. If you rannpm installin the affected window, rotate GitHub PATs, npm tokens, cloud secrets, and AI-assistant API keys on disk. Then audit your shell rc files for injected blocks before you trust the laptop again.
Cursor + GPT-5.5 jumps six points on Endor’s Agent Security League — in one week. Last issue I covered the launch numbers: Codex with GPT-5.4 led security at 17.3%. On April 27, Endor updated the leaderboard with new top-three results:
- #1 — Cursor + GPT-5.5: 87.2% functional, 23.5% security
- #2 — Cursor + Claude Opus 4.7: 91.1% functional, 22.9% security
- #3 — Claude Code + Claude Opus 4.7: 87.2% functional, 20.1% security
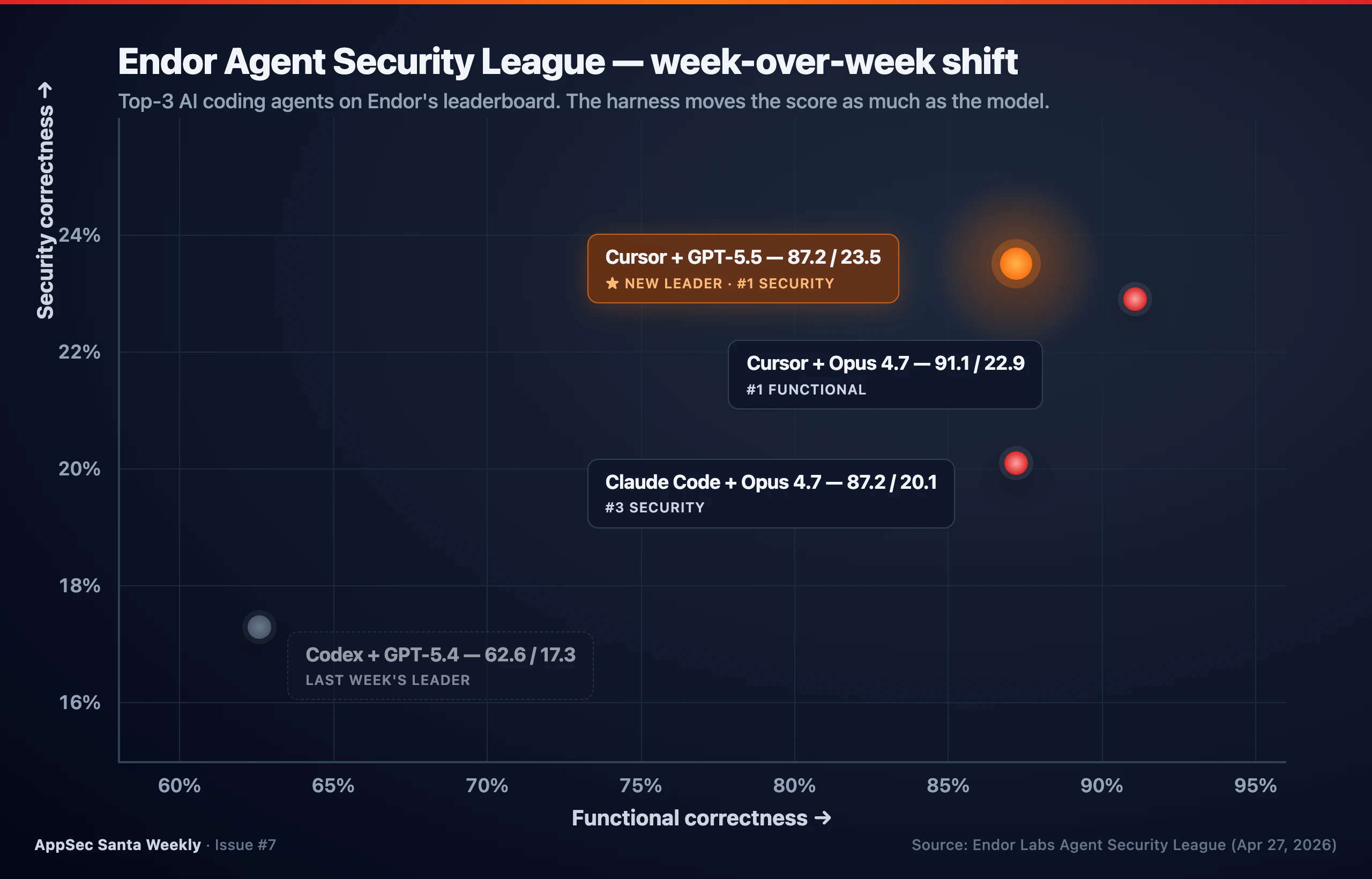
That’s a +6.2-point jump on the security ceiling in seven days. Through Cursor, GPT-5.5 hits a new high. Through the Codex harness, the same model ties for third on security and trails on functional correctness.
Same model, different harness, different security posture.
My take: The split between Cursor-GPT-5.5 and Codex-GPT-5.5 is the story. The model is one input; the harness — system prompts, tool injection rules, code-review loops — is the other. AppSec teams cannot evaluate “AI coding security” by picking a model. The harness is half the answer. Expect this leaderboard to move every few weeks, so treat the snapshot you ship with as decaying.
Checkmarx data appears on the dark web — five weeks after the breach. On April 27, Checkmarx confirmed that data posted by extortionists came from the GitHub repository touched in the March 23 supply-chain incident. The leaked dump reportedly contains source code, API keys, MongoDB and MySQL credentials, and employee details. LAPSUS$ has claimed responsibility; threat-intel circles tag the operating cluster as TeamPCP.
The Checkmarx blog confirmed that customer production environments were not impacted. That distinction matters less than it sounds — the same infrastructure was the staging point for the Bitwarden CLI compromise four weeks later.
My take: This is the second campaign in two months where stolen developer-tooling credentials become a launch pad for npm worms targeting other vendors. Snyk in early March, now Bitwarden via Checkmarx. The pattern: compromise a security vendor’s CI, use their trusted publishing path to drop malware into a downstream package that thousands of developers run on
npm install. If you sell developer-side security tools, your CI pipeline is now the most valuable asset you operate.
LMDeploy SSRF goes from disclosure to in-the-wild exploitation in 12 hours, 31 minutes. On April 21, GitHub Security published GHSA-6w67-hwm5-92mq, later assigned CVE-2026-33626. By 03:35 UTC on April 22, Sysdig had exploitation hits in their honeypot fleet.
The vulnerability is in LMDeploy’s vision-LLM image loader. The attacker passes the model a URL, the model fetches it server-side, and the loader becomes a generic SSRF primitive.
In an eight-minute session, the attacker port-scanned the internal network — AWS IMDS, Redis, MySQL, an admin HTTP service, plus DNS exfiltration over an OOB channel. They rotated between InternLM-XComposer2 and InternVL2-8B endpoints to blend in.
Separately on April 27, OX Security disclosed two more LLM-stack CVEs: Flowise (CVE-2026-40933, authenticated RCE via MCP stdio adapters) and Upsonic (CVE-2026-30625, allowlist bypass). Both tools had hardened against command injection by allowing only python, npm, and npx — OX bypassed the allowlist by injecting the malicious command as an argument (npx -c <command>).
LiteLLM picked up CVE-2026-42208 in the same window — a pre-auth SQL injection where the Authorization: Bearer header value was concatenated unsafely into a PostgreSQL query. Sysdig observed it in the wild 36 hours after disclosure.
My take: AI inference servers are the new Apache Tomcat. Every model endpoint is a server-side fetch primitive that takes URLs from clients. Every prompt-templating layer is one bad regex away from SQL injection. The 12-hour exploitation timeline isn’t the attacker getting faster — it’s the defender having no patch process for self-hosted AI infra. If you run LMDeploy, Flowise, Upsonic, or LiteLLM, this is the week to bake patch SLAs into your AI runbook.
GlassWorm wakes up: 73 OpenVSX sleeper extensions go live. Socket tracked a fresh batch of 73 impersonation extensions on Open VSX, the alternate marketplace VS Code, Cursor, and Windsurf use when Microsoft’s marketplace is gated. Six extensions have already been weaponized; the remaining 67 are confirmed sleepers — published clean, still benign, still updateable.
The technique is older than this campaign: build trust under a typo’d name, then ship malware via a normal update. GlassWorm runs invisible-Unicode obfuscation and chain-loads platform-specific .node modules from GitHub.
My take: Open VSX is the supply-chain underbelly of the AI coding stack. If your team uses Cursor or Windsurf, they’re pulling extensions from a marketplace that has 73 known dormant malware artifacts on it right now. There is no LSP-equivalent answer for “is this extension safe to install.” The gap is real, and a tooling category will fill it.
Notable Updates
- Kyverno v1.16.4 — Backports two security fixes to the 1.16 line: CVE-2026-24051 and CVE-2025-68121. If you’re on 1.16.x, this is a same-day upgrade. The 1.17.2 release on the same day is a routine cherry-pick batch.
- Semgrep v1.161.0 — Scala 3.4+ trait parameters now parse correctly (last week’s tree-sitter Scala move continues to harden). Privacy fix: HTTP request URLs are no longer logged above debug level — useful if you’ve been redacting CI logs by hand.
- OpenGrep v1.20.0 — Six parser improvements in one release: Elixir field-access vs zero-arity remote calls, Python PEP 634 match/case statements (in both menhir and tree-sitter parsers), Clojure string-key map destructuring, plus a lambda taint-tracking fix in intrafile mode.
- TruffleHog v3.95.0 → v3.95.1 → v3.95.2 — Three releases on April 21. v3.95.0 deprecated the SquareUp detector and fixed a git version-parser panic on non-numeric patch versions. v3.95.1 fixed a Mesibo verification bug. v3.95.2 reverted the v3.95.0 git parser fix — bisect-style rollback, which is fast incident response but a bad signal if it lands in your CI.
- Snyk CLI v1.1304.1 — Stability-channel rollout matures: error handling now surfaces the most relevant error and derives the correct exit code when multiple failures stack up in one run. Useful for pipelines that branch on exit code.
- Anchore Grype v0.111.1 — Overlap-by-ownership relationship handling and mismatched package/db version comparison fixes. Also fixed a SARIF output regression where HelpURI was missing.
- Anchore Syft v1.43.0 — Adds Deno binary classifiers, Erlang/Haskell legacy version detection, and OpenLDAP binary detection. If your SBOMs miss container binaries, this closes three more gaps.
- Cerbos v0.52.0 — Adds TraceBatch — a compact trace format that cuts the per-decision overhead in policy debugging. Build constraints land too, so binary slimming is now first-class.
- Promptfoo 0.121.6 → 0.121.9 — Four releases adding GPT-5.5 and Claude Opus 4.7 model support, harmbench plugin filtering, and a Promptfoo Codex skills plugin. AI red-teaming continues to ship faster than the models do.
- DefectDojo 2.57.3 — Fixes the Dependency Track parser dropping vulnerability IDs when the aliases array is empty — a quiet but real false-negative bug for anyone routing DT findings through DefectDojo.
- NeuVector v5.5.1 — Exposes OS scan support status in scanner results and fixes registry scanning through HTTP proxies. Container scanners that lose registry visibility behind corporate proxies will recognize this one.
AI Security
15 releases. The same three vendors carry the category every week and ship faster than most product orgs ship in a quarter.
Arize Phoenix shipped four releases (v14.13 → v14.15.0 plus client v2.5 and otel v0.16) — trace notes via the CLI, a sessions UX flag with a Turns/Traces toggle, and a phoenix-skills-audit GHA.
Stars at 9,458 (+89 week-over-week). Phoenix is the AI-observability tool to track now that Galileo is being absorbed into Splunk.
Akto shipped four (v1.99.4 / v1.99.5 plus two guardrails-service patches). Empty changelogs again — same publish-fast-document-later pattern as the prior two weeks.
Promptfoo shipped four (0.121.6 → 0.121.9). Model coverage was the visible work — Claude Opus 4.7 lands in 0.121.6, GPT-5.5 in 0.121.8 and 0.121.9. Stars at 20,653 (+289 week-over-week, still the steepest absolute climb in my tracked set).
Cerbos v0.52.0 puts an authorization tool in the AI-security column for me this week. The TraceBatch format reads like a feature designed for high-volume agent decision flows where every tool call is a policy check.
SCA
15 releases. The category is doing two things at once — quietly shipping ecosystem coverage, and absorbing fallout from the third Shai-Hulud campaign.
Snyk CLI v1.1304.1 is a maintenance step on the channel-rollout work, but Snyk also published a Snyk Code Early May 2026 Update that previews a near-term Snyk Secrets future I’m watching. Their Hardcoding Security into Every Commit post is the clearest mapping of where Snyk Secrets is going next.
Dependabot v0.371.0 / v0.372.0 added Poetry non-package-mode test coverage and uv env-var index auth handling. PEP 751 pylock.toml adoption is showing up across SCA scanners — Trivy parsed it last week, Dependabot is making uv first-class now. The Python lockfile landscape is shifting.
Renovate shipped five releases (43.143.0 → 43.146.0). Routine cadence; the only notable item is manager/mise adding clang-format support.
Grype v0.111.1 and Syft v1.43.0 land together — the Anchore stack continues to widen its language-runtime coverage. Deno joins the binary-classifier list in Syft this week. If you ship Deno workers in containers, your SBOMs were missing them until now.
FOSSA v3.17.2 adds PEP 621 project.dependencies support in Poetry 2.x, NuGet Central Package Management, and Swift Package.swift parser improvements. Cross-ecosystem coverage is FOSSA’s product line, and three at once is unusually concentrated.
Chainguard apko v1.2.5 → v1.2.8 — four releases, mostly hardening: scope all DirFS operations through os.Root, strip special mode bits in OpenFile/WriteFile, and verify package control hashes against the signed APKINDEX. Defense-in-depth for the apk format.
Worth flagging: Socket introduced Reachability for PHP in experimental on April 24. PHP joins the list of languages where SCA tools can ask “is this vulnerable function actually called from your code.”
Reachability is now the default ask in SCA evals. Vendors that don’t have it across the JVM, Python, JS, and PHP tier will lose head-to-heads in 2026.
SAST
Nine releases. A heavy week for parser quality and a notable bisect-and-revert from TruffleHog.
Semgrep v1.161.0 lands the Scala 3.4+ parameter parsing follow-up plus the URL-redaction debug log change. The HTTP-logging change is small but matters: any team that pipes Semgrep CI logs into a SIEM was leaking scan target URLs above debug level.
OpenGrep v1.20.0 is the busiest parser-improvement release I’ve seen from them. Six languages touched in one cut — Elixir, Python, Clojure, plus the lambda taint-tracking fix in intrafile mode that cleans up a real false-negative class.
TruffleHog shipped three patches in one day: v3.95.0 with the SquareUp detector deprecation and a git parser panic fix, v3.95.1 with a Mesibo verification fix, v3.95.2 reverting the v3.95.0 git parser fix.
Same-day-revert is a fast incident response, but if you pin a specific patch version in CI, this is the week to widen your range or pin to .2.
PHPStan 2.1.51 continues the bisect-driven regression-fix cadence — argument-index in dumpType, ReflectionGetAttributes for UnionTypes, ErrorType from array_key_exists with union key types in loops. Maintenance-class, but useful in big codebases.
Qodana v2026.1.0 is the first 2026.x release. Two reverts in the changelog (a dependency bump revert and a devcontainer image revert) suggest the team is consolidating before adding new analyzers.
SonarLint IntelliJ 12.2.0.84584 is a quiet IDE-side update. PMD 7.24.0 adds a new Apex rule (AvoidInterfaceAsMapKey). Niche but real for Salesforce shops.
IaC Security
Six releases. Kyverno is the security release this week — backporting two CVE fixes to the 1.16 line on the same day as a routine 1.17.2 patch.
Kyverno v1.16.4 + v1.17.2 — same-day backport pattern that lets long-tail clusters stay on 1.16 while pulling the security fixes (CVE-2026-24051, CVE-2025-68121). Verify which line you’re on.
Mondoo cnspec v13.5.1 + v13.6.0 — parallel scanning, an auditd MAC policy bare-keyname null-propagation fix, and a DynamoDB KMS-encryption check that handled null sseDescription poorly. The DynamoDB fix is the kind of false-positive class that quietly inflates IaC dashboards for AWS-heavy shops.
Checkov 3.2.525 is a one-line Terraform Windows-path fix.
OPA Gatekeeper v3.22.2 fixes gh CLI compatibility with immutable releases — release-tooling housekeeping.
Container Security
Two releases. NeuVector v5.5.1 exposes OS scan support status from scanner results and fixes a registry-via-proxy scan failure. StackRox 4.8.11 is a Red Hat ACS patch — release notes route through the Red Hat documentation portal.
ASPM
DefectDojo 2.57.3 is the parser-bug fix release: Dependency Track parser dropping vulnerability IDs when aliases is empty. If you route DT findings through DefectDojo, this is a same-week upgrade.
Mobile
Ostorlab/oxo v2.1.0 — first feature release after last week’s oxo rename. Adds a ticket selector, a phone-number asset type, and a CLI command for ticket workflows.
The asset-type expansion is interesting: phone numbers as a scannable asset surface aligns with the SMS-blaster and IRSF-fraud reporting trend showing up in CISA advisories this month.
Quiet This Week
No GitHub releases from DAST, IAST, RASP, or API Security.
Star Watch
- TruffleHog 25,948 — joined my front-of-mind set after the three-release April 21 burst.
- Renovate 21,395 — five releases this week, slow and steady.
- Promptfoo 20,653 — +289 WoW, the biggest absolute add in my AI-security tracked set for the third week running.
- Semgrep 14,951 — +81. Steady drip.
- PHPStan 13,924 — solid baseline despite no new features in the 2.1.x line.
- Anchore Grype 12,097 — +36.
- Arize Phoenix 9,458 — +89, holding the trajectory toward 10K.
- Anchore Syft 8,827 — companion to Grype, ships in lockstep.
- Checkov 8,671 — quiet release week, stars steady.
- Kyverno 7,683 — security-release week.
- Snyk CLI 5,513 — channel-rollout maturity.
- OpenGrep 2,449 — +39. Same trajectory as last week.
Quick Hits
Things not big enough for their own paragraph but worth knowing:
- Phoenix v14.13 → v14.15.0 plus client v2.5 and otel v0.16 — sessions UX flag, trace notes, phoenix-skills-audit GHA.
- Akto v1.99.4 / v1.99.5 plus two guardrails-service patches. Empty changelogs.
- Renovate 43.143.0 → 43.146.0 — base-image bumps and
manager/miseclang-format. - Chainguard apko v1.2.5 → v1.2.8 — DirFS through
os.Root, mode-bit stripping, signed APKINDEX hash verify. - Dependabot v0.371 / v0.372 — Poetry non-package mode,
uvenv-var index auth, PR-update commit messages. - FOSSA v3.17.2 — PEP 621 in Poetry 2.x, Swift parser improvements, NuGet CPM support.
- PHPStan 2.1.51 — argument-index in
dumpType, ReflectionGetAttributes for UnionTypes. - Qodana v2026.1.0 — first 2026.x release with internal reverts.
- SonarLint IntelliJ 12.2.0.84584 — IDE-side update.
- PMD 7.24.0 — new Apex
AvoidInterfaceAsMapKeyrule. - Kyverno v1.17.2 — cherry-pick patch batch alongside the v1.16.4 security backport.
- Mondoo cnspec v13.5.1 / v13.6.0 — parallel scanning + DynamoDB KMS check fix.
- Checkov 3.2.525 — Terraform Windows-path fix.
- OPA Gatekeeper v3.22.2 — gh CLI immutable-release support.
- StackRox 4.8.11 — Red Hat ACS patch.
- Ostorlab/oxo v2.1.0 — first post-rename feature release.
On AppSec Santa This Week
Updated this week:
- Endor Labs — added the Cursor + GPT-5.5 #1 placement on the Agent Security League (23.5% security correctness).
- Snyk — added v1.1304.1 stability-channel rollout note.
- Kyverno — added v1.16.4 CVE-2026-24051 + CVE-2025-68121 backports.
- Semgrep — added v1.161.0 Scala 3.4+ parser fix and HTTP debug-log redaction.
- TruffleHog — added v3.95.0/.1/.2 three-release sequence and the same-day revert.
Most read this week: Semgrep, Snyk, Trivy, SonarQube, Endor Labs
If you spot anything outdated or wrong on a tool page, reply to this email — I update pages based on reader feedback.
Worth Reading
Endor Labs — Inside the Bitwarden CLI 2026.4.0 Supply Chain Attack — The technical anchor for this week. Read it with your
~/.bashrcopen. The seven secret surfaces and the AI-assistant probe section are the parts that change how you write your incident playbook.JFrog Research — TeamPCP Campaign Spreads to npm via Hijacked Bitwarden CLI — JFrog’s deobfuscation of the Bun runtime loader and the GitHub Actions secret-harvesting workflow. The “create branch, run workflow, exfiltrate, clean up” pattern is reusable knowledge for SOC playbooks.
Endor Labs — GPT-5.5 Sets a New Code Security Record with Cursor, Not Codex — The leaderboard update with full week-over-week numbers. Cite this when someone tells you “we picked GPT-5 — we’re secure” — the harness, not the model, is where the variance lives.
Sysdig — How Attackers Exploited LMDeploy LLM Inference Engines in 12 Hours — The first end-to-end public timeline of an AI-infra CVE going from disclosure to honeypot exploitation. The eight-minute SSRF port-scan-and-exfil session reads like a 2010 web app pen-test, except the loader is a vision-LLM.
Socket — 73 OpenVSX Sleeper Extensions Linked to GlassWorm — The sleeper-extension pattern explained with worked examples. If your team uses Cursor or Windsurf, the IOC list at the bottom is what your EDR rules need this week.
Sysdig — 2026 Cloud-Native Security Report — Headline: 25× growth in AI-specific package adoption, 70% of orgs run behavior-based detection, 140% YoY rise in auto-killing suspicious processes. Useful baseline for board decks.
OX Security — Flowise and Upsonic: When Best Practice Isn’t Enough — Two more LLM-stack CVEs from the OX team that disclosed the MCP protocol RCE two weeks ago. Their argument: even the AI tools that hardened against command injection got bypassed because allowlists for
python,npm,npxstill let attackers smuggle commands through arguments.The Register — Ongoing Supply-Chain Attack Targets Security and Dev Tools — The clearest journalist-side connect-the-dots writeup linking Snyk early-March, Checkmarx March 23, Bitwarden CLI April 22, and the LAPSUS$ dark-web post on April 27.
Wrapping Up
That’s issue #7. 49 releases tracked, one supply-chain worm that now hunts your AI assistants, one leaderboard that shifted six points in seven days, and a five-week-old breach that finally surfaced as a downstream attack.
The through-line is the developer machine. Last month the attacker target was your CI runner. This week it’s your laptop — your $PATH, your ~/.bashrc, your Claude Code token, your npm publish permission.
The pivot is faster than the policy.
I track 114 GitHub repos and 97 RSS feeds every week. If a tool ships a release, it shows up here, with context on what it means.
If you found this useful, forward it to a colleague who’d benefit.
And if I missed something or got something wrong, just reply — I read every response.
See you next Tuesday.
AppSec Santa Weekly — changelog analysis and category trends from 290+ AppSec tools. Browse all tools or subscribe for weekly updates.