NeuVector is an open-source, Kubernetes-native container security platform that provides full-lifecycle protection from build-phase scanning through runtime threat detection and response.
Maintained by SUSE, it was open-sourced in January 2022 under the Apache 2.0 license, making it the first end-to-end open-source container security platform. 1.3k GitHub stars, 37 contributors, latest release v5.5.0 (March 2026).
What does NeuVector do?
NeuVector provides vulnerability scanning during build and deployment, plus runtime protection in production with network-level threat detection.
The feature that separates it from most container security tools is a patented deep packet inspection (DPI) engine that acts as a Layer 7 firewall between containers and pods.
Unlike tools that only monitor system calls, NeuVector inspects actual network payloads to detect and block attacks like SQL injection, DDoS, and DNS-based threats in real time.
The platform deploys four main components as containers in a Kubernetes cluster:
| Component | Role |
|---|---|
| Controller | Central management, policy engine, REST API |
| Enforcer | Per-node agent for runtime monitoring and DPI |
| Manager | Web UI for visualization and management |
| Scanner | Vulnerability database and image scanning engine |
How does NeuVector’s runtime protection work?
NeuVector’s runtime security operates in three modes, progressively moving from observation to enforcement:
Discovery mode learns normal application behavior — which processes run, what network connections containers make, and what file access patterns are expected. This behavioral baseline becomes the foundation for security policies.
Monitor mode alerts on deviations from learned behavior without blocking traffic, letting teams validate policies before enforcement.
Protect mode blocks threats and policy violations. The DPI engine inspects Layer 7 traffic between container pairs, catching SQL injection, cross-site scripting, DDoS attacks, DNS-based threats, and tunneling attempts inside otherwise allowed flows.
The distinguishing mechanism is process behavior whitelisting plus network policy auto-learning. In Discovery mode the Enforcer watches every process that starts inside a container and every connection it makes. NeuVector then derives an allowlist policy — “this image runs nginx and only talks to the redis service on 6379” — and surfaces it as an editable proposal. Switch to Protect and any process or connection outside the learned allowlist is blocked. This inverts the Falco model: Falco asks “what bad behavior matches a rule?” and NeuVector asks “is this behavior in the allowlist I learned?”. The two approaches are complementary rather than competitive.
Layer 7 DPI is what distinguishes NeuVector from syscall-based tools. The Enforcer parses HTTP, HTTPS (with TLS interception when configured), DNS, and several other protocols, so attacks that ride inside an allowed network connection still get caught. Modern releases also use eBPF for syscall-level visibility, complementing DPI without replacing it.
Built-in WAF and DLP engines add web application firewall protection and data loss prevention directly to container network traffic — both run on the Enforcer, so policy enforcement happens at the same point as L7 inspection.
NeuVector implements a Zero Trust model for container networks. Every connection between containers is inspected and must be explicitly allowed by policy.
The behavioral learning phase automates initial policy creation, reducing the manual effort of defining allowed traffic patterns.
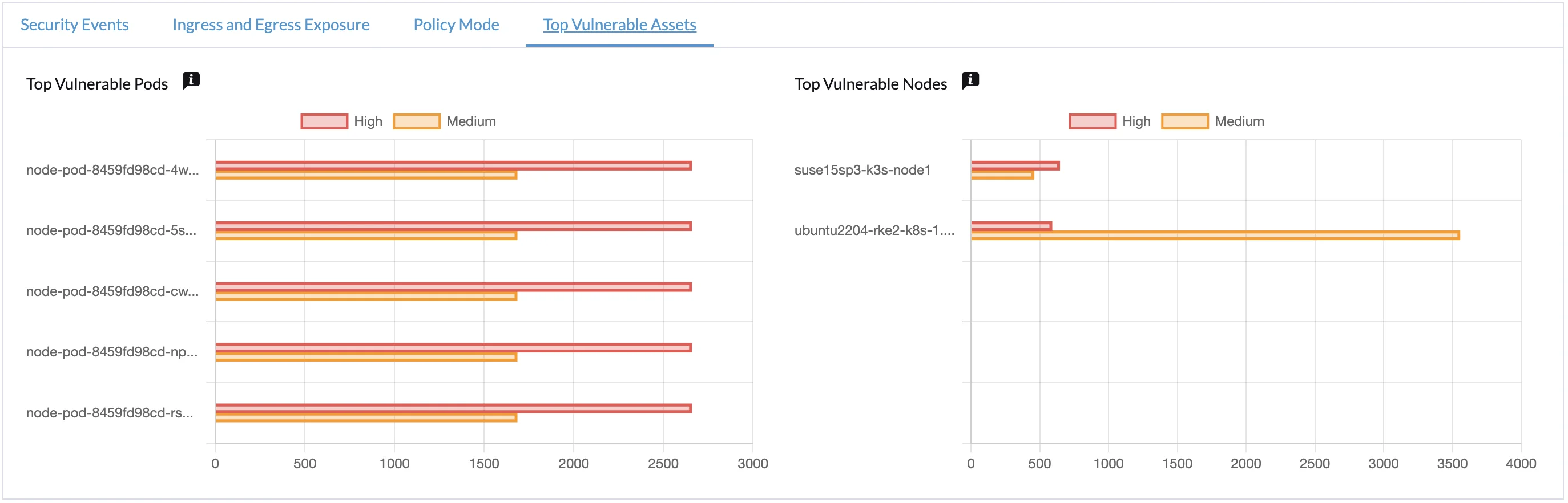
Does NeuVector include vulnerability scanning and compliance?
NeuVector includes built-in vulnerability scanning that covers container images in registries, CI/CD pipelines, and running containers and host nodes. The Scanner component maintains its own CVE database and updates independently of the main platform, so scan results reflect the latest known CVEs without waiting on a full NeuVector upgrade.
NeuVector’s image scanner is self-contained — you do not need Trivy or Clair to scan images, although both can be used in parallel. Many teams keep Trivy in CI for pre-merge speed and rely on NeuVector’s scanner for in-registry and runtime scans.
For compliance, NeuVector runs automated audits against the CIS Kubernetes Benchmark and the CIS Docker Bench. It ships with report templates and control mappings for PCI-DSS, HIPAA, GDPR, and NIST 800-53 — saving real time during audit cycles. Admission control rules can block deployments whose images exceed a CVE severity threshold or fail required compliance checks, turning the scanner into a deploy-time gate.
Results can be exported via the REST API and integrated into Splunk, Elastic, ServiceNow, or any SIEM. SBOM export is supported in current 5.x releases for supply-chain workflows.
How do you deploy NeuVector?
The Helm chart is the recommended path on every Kubernetes distribution — helm install neuvector neuvector/core from the official repository deploys the Controller, Enforcer (as a DaemonSet), Manager, and Scanner pods. NeuVector also ships kubectl manifests and an OpenShift Operator for clusters where Helm is not preferred.
Footprint is small. Each Enforcer pod typically uses well under 200 MB of RAM per node and a few hundred millicores of CPU; Controller and Manager run as a small set of cluster-wide pods. The Scanner is the heaviest component because it pulls and unpacks images, but it scales horizontally.
NeuVector works on EKS, AKS, GKE, OpenShift, and self-managed clusters. Air-gapped installs are supported by mirroring images to an internal registry and pointing the Helm values at it — common in FedRAMP and other regulated environments. SUSE Rancher integrates NeuVector natively, so multi-cluster Rancher fleets get one-click deployment and SSO into the NeuVector Manager UI.
Authentication plugs into LDAP, Active Directory, SAML, and OIDC providers (Okta, Auth0, Azure AD). Security policies live as Kubernetes CRDs, so rules sit in version control alongside the application manifests they protect.
When should you use NeuVector?
NeuVector is the right choice when you need runtime container security with network-level threat detection, not just pre-deployment scanning. The Layer 7 firewall and DPI engine catch attacks like SQL injection, cross-site scripting, and lateral movement that image scanners miss entirely.
It pairs well with image scanners like Trivy or Clair for pre-deployment vulnerability detection, and admission controllers like Kyverno or OPA Gatekeeper for policy enforcement at deploy time.
Limitations: The DPI engine requires privileged access to network namespaces, which some managed Kubernetes services restrict. Behavioral learning needs time to build accurate baselines in dynamic environments.
The community is smaller (1.3k stars, 37 contributors) than Falco or Trivy, though SUSE provides commercial backing.
NeuVector v5.5.0 (March 2026) improves vulnerability reporting and fixes Rancher SSO authentication errors that occurred when the Rancher Helm release name was not “rancher.” If you’re running NeuVector in a SUSE Rancher environment, the SSO fix alone is worth the upgrade.
For a broader view of container security options, see the container security tools category page. e.