MobSF Alternatives: 8 Better Mobile App Security Tools in 2026
Looking to replace or complement MobSF? Compare the top commercial and open-source mobile app security alternatives including NowSecure, Appknox, Ostorlab, and Corellium.
Top MobSF Alternatives
View all 20 alternatives →
Android APK resource decoding & rebuild

No-Code Mobile Defense Automation

Mobile AppSec trusted by 300+ enterprises

ARM-based virtual iOS & Android devices for security research

Full-stack mobile AppSec

Android attack surface assessment framework
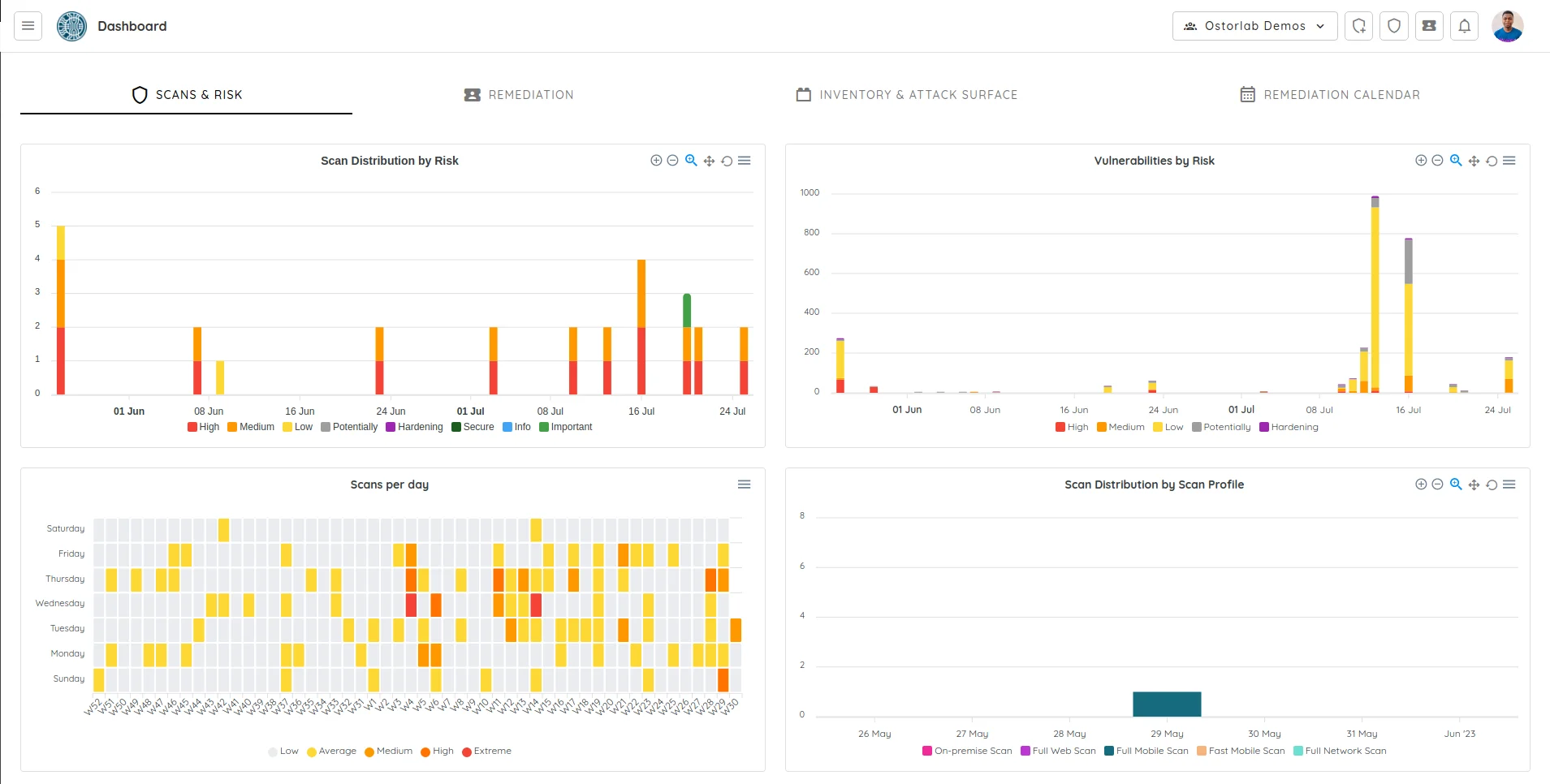
- MobSF is free, open-source, and has 20.7k GitHub stars, but self-hosting means you own the infrastructure, triage, and false-positive tuning yourself.
- NowSecure is trusted by 4 of the top 5 US telecoms and is an authorized lab for Google's App Defense Alliance MASA program — something no OSS tool can offer.
- Corellium runs ARM-native virtual iPhones on its CHARM hypervisor with instant jailbreak, replacing MobSF's dynamic analysis that requires physical devices or emulators.
- Ostorlab offers an open-source scan orchestration engine called OXO (Apache 2.0, 560 GitHub stars) that coordinates Nuclei, Nmap, and custom agents — the closest OSS challenger to MobSF.
- Guardsquare's DexGuard and iXGuard focus on hardening apps against reverse engineering, a use case MobSF does not address at all.
The best MobSF alternatives in 2026 are NowSecure, Appknox, Ostorlab, Corellium, and Data Theorem. Each one adds something MobSF’s open-source model does not cover: enterprise support, manual pentesting, virtual device testing, or SBOM generation.
Each option is reviewed below so you can pick the right fit for your team size and threat model.
Why Look for MobSF Alternatives?
MobSF (Mobile Security Framework) is the most popular open-source mobile security tool around. It has over 20.7k GitHub stars, 104 contributors , and handles static, dynamic, and malware analysis for Android, iOS, and Windows apps.
It is completely free under GPL-3.0, self-hostable via Docker, and exposes a REST API for CI/CD integration.
For individual researchers, students, and small teams, the value is hard to argue with.
The problem is that MobSF is a scanner, not a platform. You host it, you triage findings, you tune false positives, and you answer your own questions when something breaks.
There is no vendor support, no SLA, and no real accountability if a scan misses a critical vulnerability before a release.
Note: MobSF is not a PCI-authorized scanner, is not part of Google's App Defense Alliance MASA program, and carries no third-party attestation that enterprise procurement teams typically require. This lack of support and formal certification is often a blocker for regulated industries.
Dynamic analysis is another friction point. MobSF’s dynamic module needs a rooted Android device, a jailbroken iPhone, or a configured emulator with Frida server running.
Setting this up reliably across a team is non-trivial, and scaling dynamic testing to hundreds of builds per day requires device labs MobSF does not provide.
MobSF also does not perform code hardening or runtime protection. If your threat model includes reverse engineering, IP theft, or tampering with a released app, you need a separate tool like DexGuard, iXGuard, or Zimperium zShield alongside it.
There is no SBOM generation in the formal CycloneDX or SPDX sense, no automated compliance reports for GDPR or HIPAA, and no app store monitoring for clones or repackaged versions of your app.
For small projects these gaps are tolerable. For enterprises shipping mobile apps to millions of users, they stack up into real operational cost.
Top MobSF Alternatives
1. NowSecure
NowSecure is the enterprise standard for mobile AppSec. It combines automated SAST, DAST, and IAST for iOS, Android, and OTT apps with a privacy engine that tracks data flows and third-party SDK sharing.
The platform is trusted by 4 of the top 5 US telecoms and 3 of the top 5 US banks, and reports 4 million+ automated assessments and 8 million+ automatically identified vulnerabilities.
Key Insight
The clearest differentiator is formal attestation. NowSecure is an authorized lab for [Google's App Defense Alliance MASA program](https://appdefensealliance.dev/masa), meaning apps tested through NowSecure can carry the "Independent security review" badge on Google Play. No open-source tool can issue that attestation.
NowSecure also generates dynamic SBOMs, identifies AI libraries and services inside mobile apps, and aligns testing with OWASP MASVS . CI/CD coverage includes GitHub Actions (v5), Jenkins, Azure DevOps, and Bitrise.
Pricing is quote-based, which is the main reason smaller teams stay on MobSF. For a deeper head-to-head, see NowSecure vs MobSF .

Best for: Regulated enterprises that need formal attestation, MASA certification, and vendor support. License: Commercial Key difference: Authorized lab for Google’s App Defense Alliance MASA program. Dedicated privacy engine for GDPR, CCPA, and HIPAA compliance.
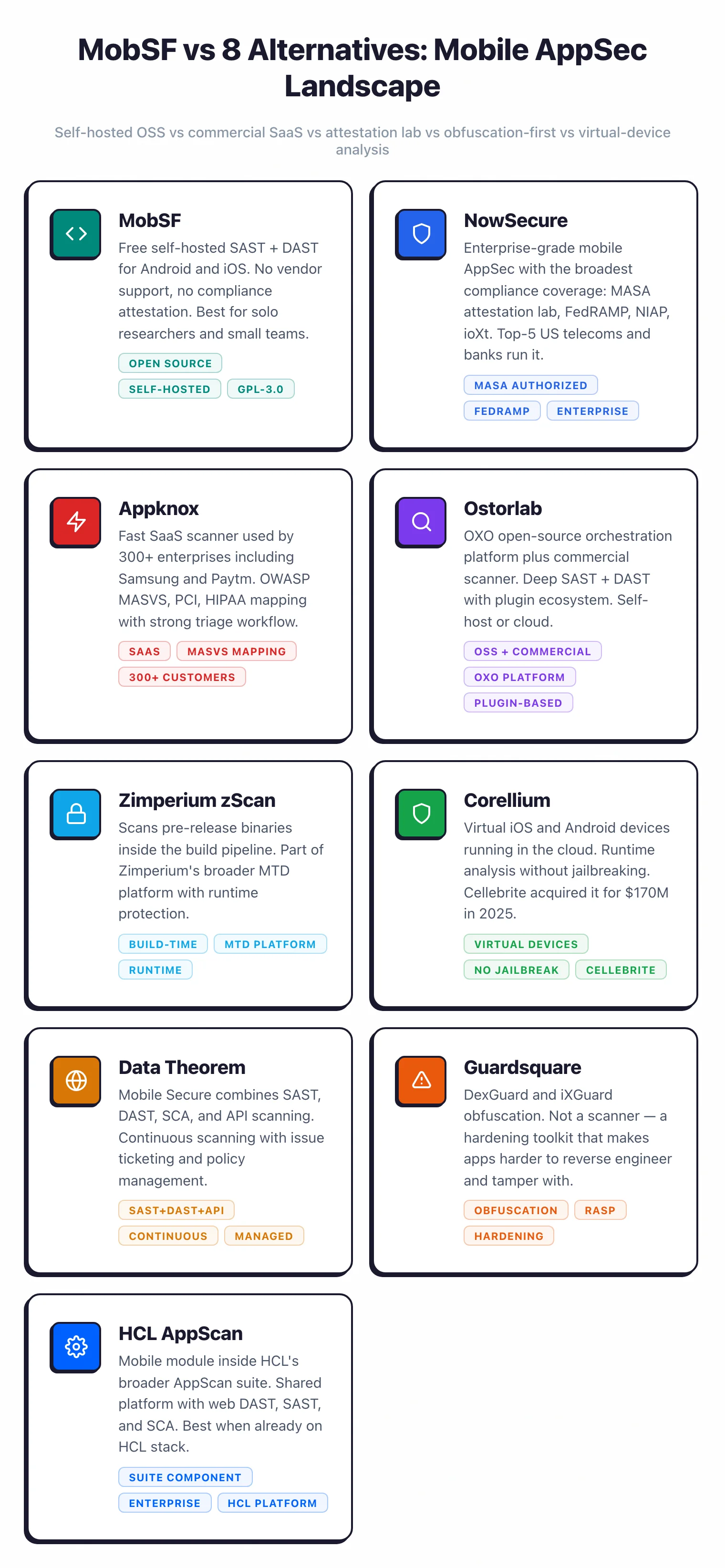
2. Appknox
Appknox is the other enterprise platform that comes up most often in MobSF replacement discussions. It is used by 300+ enterprises including Singapore Airlines and Paytm, with Fortune 500 customers on the roster.
The platform bundles SAST, DAST, and API testing with manual penetration testing by certified security researchers — manual PT reports arrive within 3-5 business days.
Appknox evaluates Android (APK, AAB) and iOS (IPA) apps against 130+ security test cases across Java, Kotlin, Swift, Objective-C, Flutter, and React Native. Compliance coverage spans GDPR, PCI-DSS, HIPAA, NIST, and SAMA.
The Storeknox add-on monitors Google Play and the App Store for unauthorized copies, repackaged apps, and phishing clones — a capability that goes beyond what MobSF addresses.
On-premises deployment is available for teams with data residency requirements, and CI/CD integrations cover Jenkins, GitHub Actions, and Azure DevOps.
For teams that want automated scanning and expert human review from one vendor without stitching tools together, Appknox is the right call.
Best for: Enterprises that want combined automated scanning and manual pentesting from a single vendor. License: Commercial Key difference: Bundles manual PT reports within 3-5 business days. Storeknox app store monitoring for clones and repackaged apps.
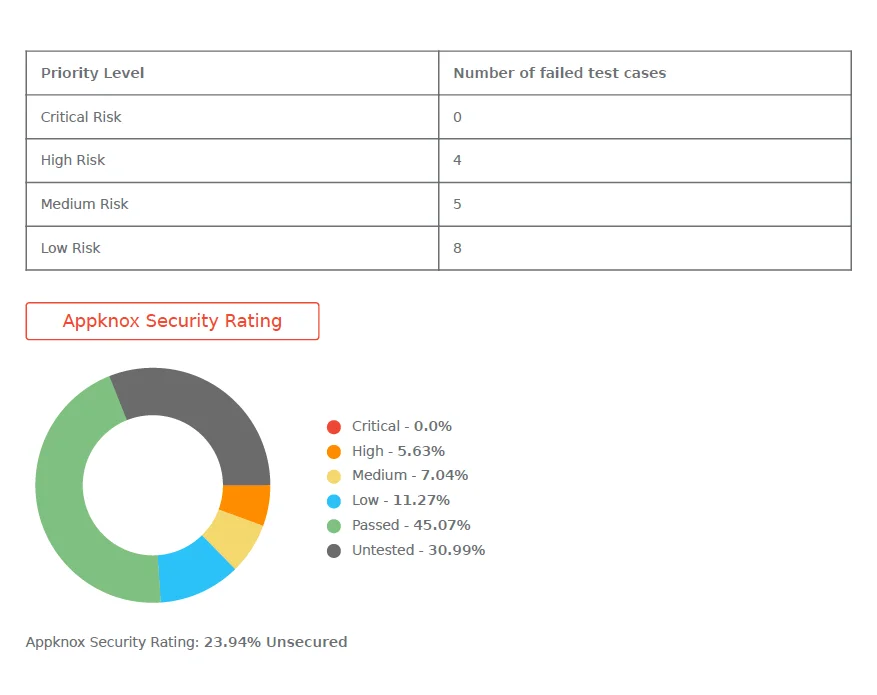
3. Ostorlab
Ostorlab is the closest thing to an open-source MobSF challenger. Its core engine, OXO, is released under Apache 2.0 with 560 GitHub stars and handles scan orchestration across Nmap, Nuclei, ZAP, and custom Docker-containerized agents.
Anyone can self-host OXO for free and extend it through the public agent marketplace.
On top of OXO, Ostorlab offers three mobile scan profiles — Fast Scan (static only), Full Scan (static + dynamic with backend injection testing), and Privacy Scan (data flow tracking and compliance).
The commercial platform adds team collaboration, an AI copilot, attack surface discovery, and integrations for 9 CI/CD platforms including GitHub, GitLab, Jenkins, and Azure DevOps.
Coverage includes Android APK/AAB, iOS IPA, plus web, network, and domain scanning. Detection goes beyond code vulnerabilities to hardcoded secrets and privacy policy compliance gaps.
The freemium model means you can start with OXO for free and move to the commercial tier when you need the collaboration and orchestration features.
For teams that like MobSF philosophically but want a modular, extensible architecture, Ostorlab is the natural upgrade path.
Best for: Teams that want MobSF-style openness with a modular agent architecture. License: Freemium (OXO engine Apache 2.0; platform commercial) Key difference: OXO orchestration engine coordinates Nuclei, Nmap, and custom Docker agents. Public agent marketplace for extension.
4. Zimperium zScan
Zimperium zScan combines SAST, DAST, and IAST with an unusual focus: security control validation. Instead of just finding vulnerabilities, zScan verifies that anti-tampering, SSL pinning, and root detection are actually implemented correctly in the shipped binary.
That is a gap MobSF does not fill — MobSF reports issues but does not validate that hardening controls work.
Zimperium is a Forrester Wave Leader in Mobile Threat Defense and offers a free 30-day trial with unlimited app scans. Scans on APK, IPA, and AAB files return results in 15-30 minutes.
Language coverage spans native (Swift, Kotlin, Java, Objective-C) and cross-platform (Flutter, React Native, Xamarin, Cordova). SBOM generation and supply chain risk detection are built in.
zScan is part of the Zimperium MAPS suite alongside zShield (app hardening), zDefend (in-app RASP), and zKeybox (white-box cryptography).
For teams that need the full defend-and-protect stack from one vendor, MAPS is a single-pane-of-glass option. CI/CD plugins cover GitHub Actions, GitLab CI, Jenkins, Harness, GoCD, and Bitrise with SARIF output.
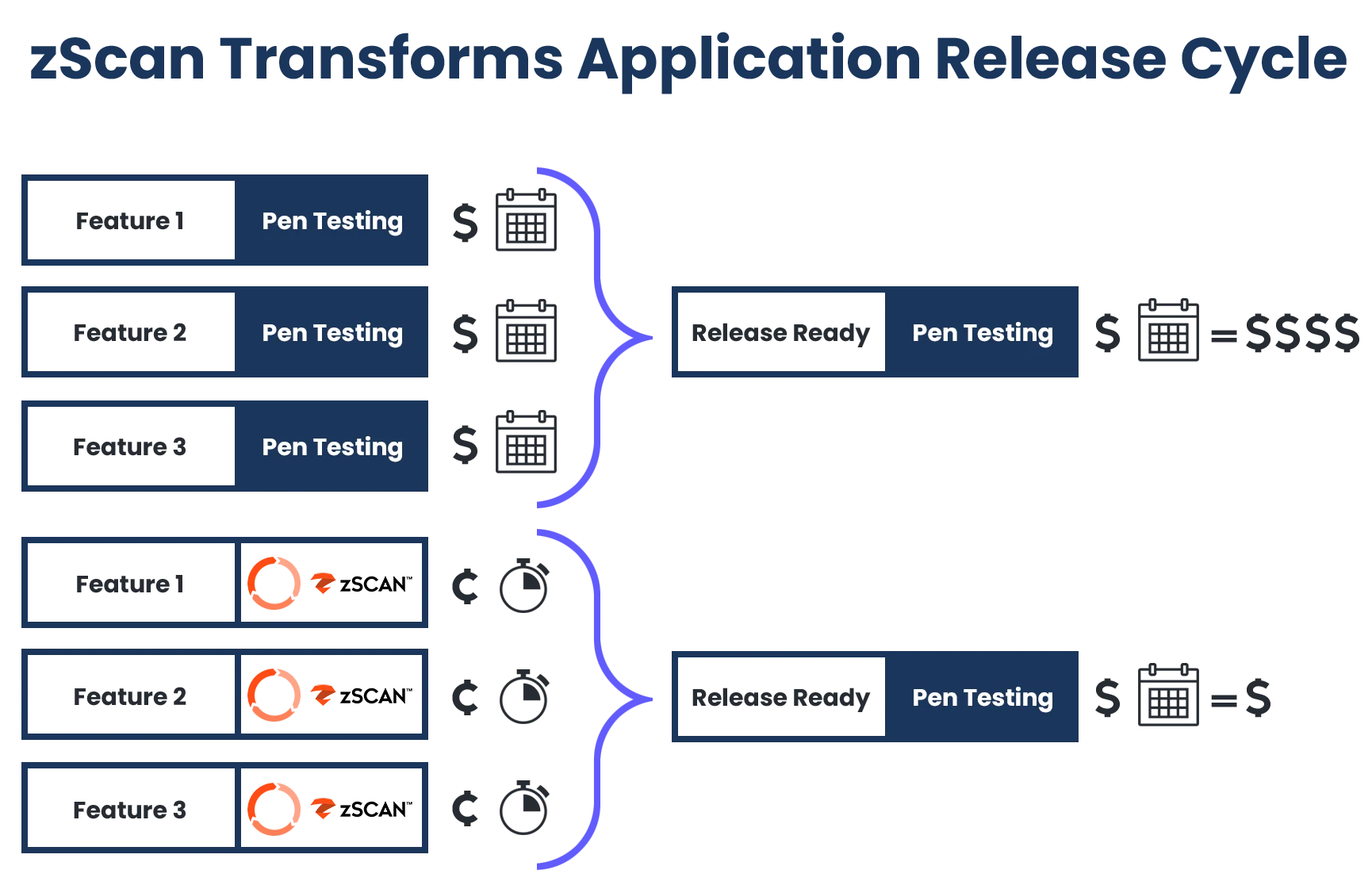
Best for: Teams that need both vulnerability scanning and security control validation in one tool. License: Commercial Key difference: Validates that anti-tampering, SSL pinning, and root detection controls are correctly implemented, not just recommended.
5. Corellium
Corellium solves a completely different problem than MobSF, and that is why it shows up on this list. MobSF’s dynamic analysis needs a rooted device or an emulator with Frida server configured.
Corellium gives you virtualized iOS and Android devices running on ARM-native hardware via its CHARM hypervisor, with instant jailbreak access and no exploits required.
The platform is the only option for virtualized iOS at this fidelity. Corellium won a landmark copyright fair use ruling against Apple in December 2020 (upheld on appeal in May 2023), establishing legal precedent for iOS virtualization in security research.
Cellebrite acquired Corellium for $170M in 2025, and the platform is used by government defense and intelligence agencies, enterprises, and independent researchers worldwide.
For automated testing, the MATRIX engine runs hundreds of OWASP-aligned security checks on mobile apps in minutes — covering authentication, cryptography, storage, network, and platform categories.
Corellium is available as cloud (AWS Graviton), on-premises (air-gappable), or dedicated private servers. Built-in Frida integration, kernel debugging, HyperTrace, and CoreTrace round out the dynamic analysis toolkit.
If your team spends real engineering time maintaining a physical device lab for MobSF dynamic testing, Corellium replaces that operational cost with a cloud API.
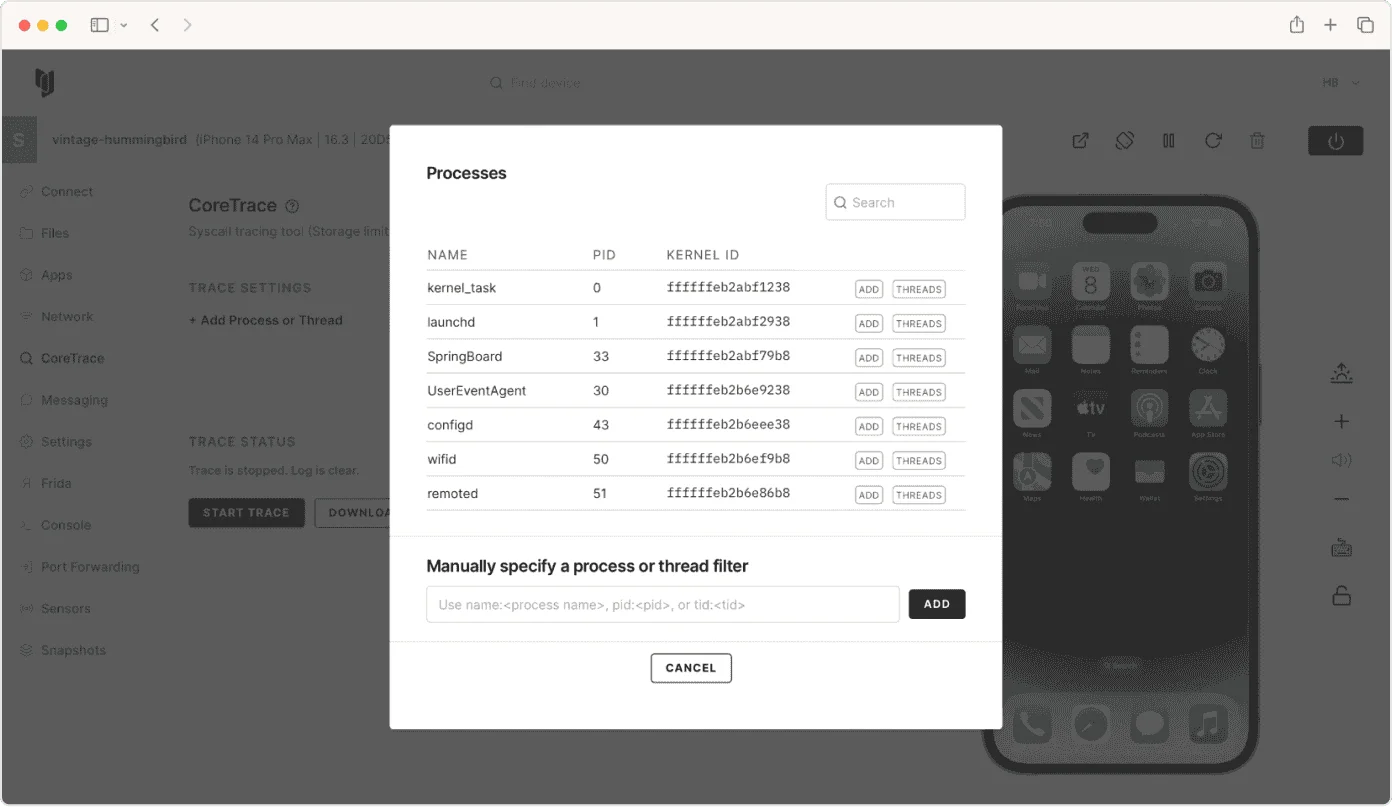
Best for: Mobile security researchers and enterprises doing deep dynamic analysis on iOS and Android. License: Commercial Key difference: ARM-native virtual iPhones and Android devices with instant jailbreak via the CHARM hypervisor. MATRIX automated testing engine.
6. Data Theorem Mobile Secure
Data Theorem protects mobile apps serving 2.8 billion+ users, with customers including Cisco Duo, Zoom, Coinbase, and eBay. The platform unifies SAST, DAST, SCA, and runtime protection specifically for iOS (Swift, Objective-C) and Android (Kotlin, Java).
That four-way combination in a single product is rare — most mobile tools do two or three of those, not all four.
The Analyzer Engine continuously monitors third-party SDKs and app store listings, flagging risky libraries and detecting when an app’s binary appears in unauthorized listings.
Auto-triage with P1 alerts and one-click compliance reports aim to keep AppSec and mobile engineering teams out of manual triage work. Mobile Protect carries kidSAFE certification for apps serving children.
Data Theorem’s pitch over MobSF is full-stack coverage without integration work. You do not assemble a scanner, a runtime protection library, an SCA feed, and app store monitoring from separate sources — it ships as one platform.
The tradeoff is commercial pricing — it is a better fit for teams already running enterprise AppSec procurement than for scrappy mobile shops.
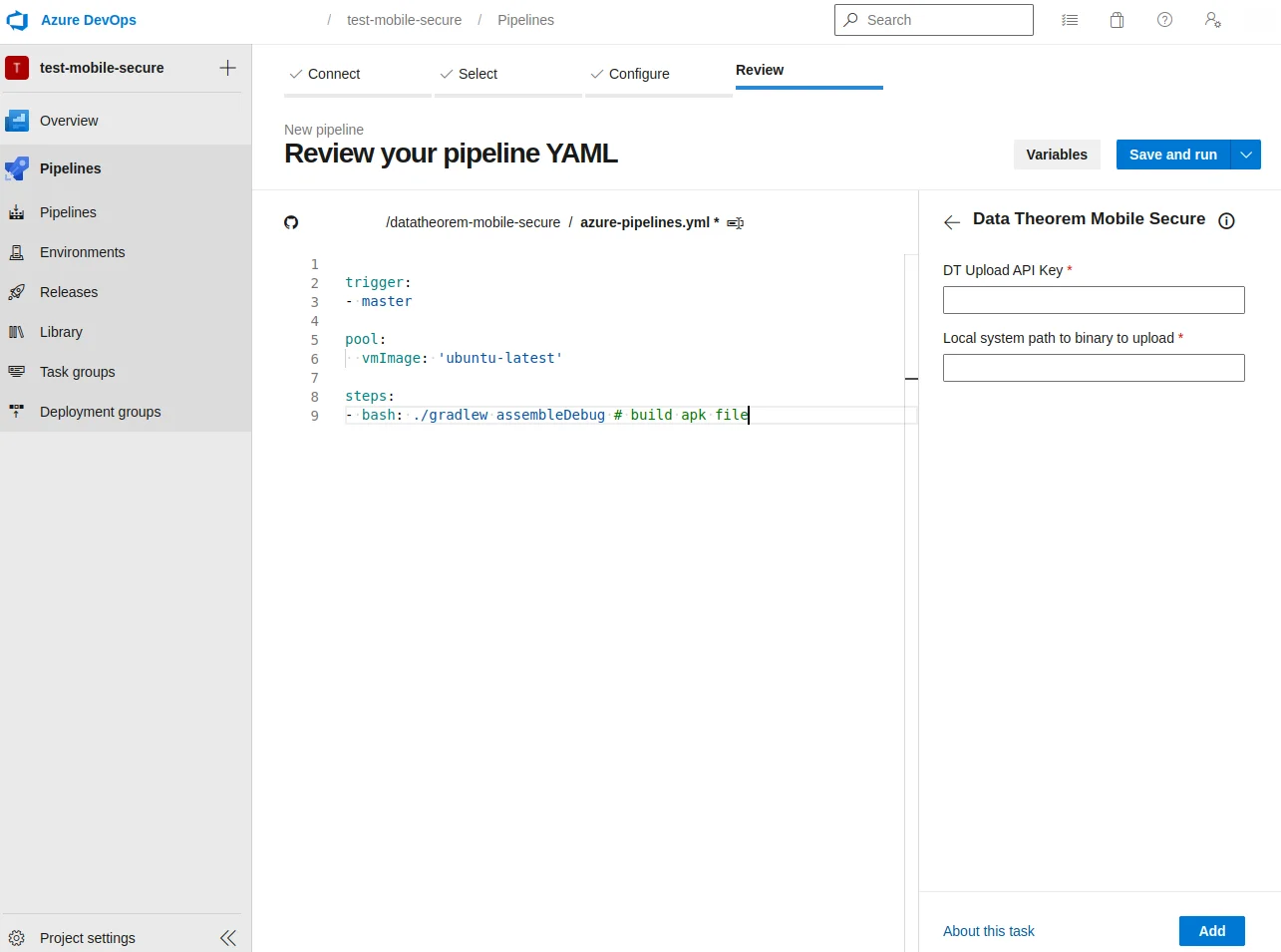
Best for: Mid-market and enterprise teams that want SAST, DAST, SCA, and runtime protection unified in one product. License: Commercial Key difference: Unified SAST, DAST, SCA, and runtime protection for iOS and Android. Continuous monitoring of third-party SDKs and app store listings.
7. Guardsquare
Guardsquare is not a direct MobSF replacement — it solves a problem MobSF does not address. MobSF tests apps; Guardsquare hardens them.
DexGuard (Android) and iXGuard (iOS) apply polymorphic obfuscation, control flow encryption, name mangling, data encryption, and runtime application self-protection (RASP) at build time.
Guardsquare is the creator of ProGuard , the original Android code optimizer that R8 eventually replaced as the Android default. ProGuard is still maintained as open-source.
AppSweep is Guardsquare’s free mobile application security testing tool, positioned as a complement to MobSF-style scanners.
Cross-platform support covers Flutter, React Native, Unity, Cordova, and Ionic. Build integrations plug into Gradle, Xcode, and common CI/CD pipelines.
If you already have MobSF catching vulnerabilities and want a vendor to stop attackers from reverse-engineering your production app, Guardsquare is the standard answer.
Many teams pair MobSF (or one of the commercial scanners above) with Guardsquare rather than replacing one with the other.
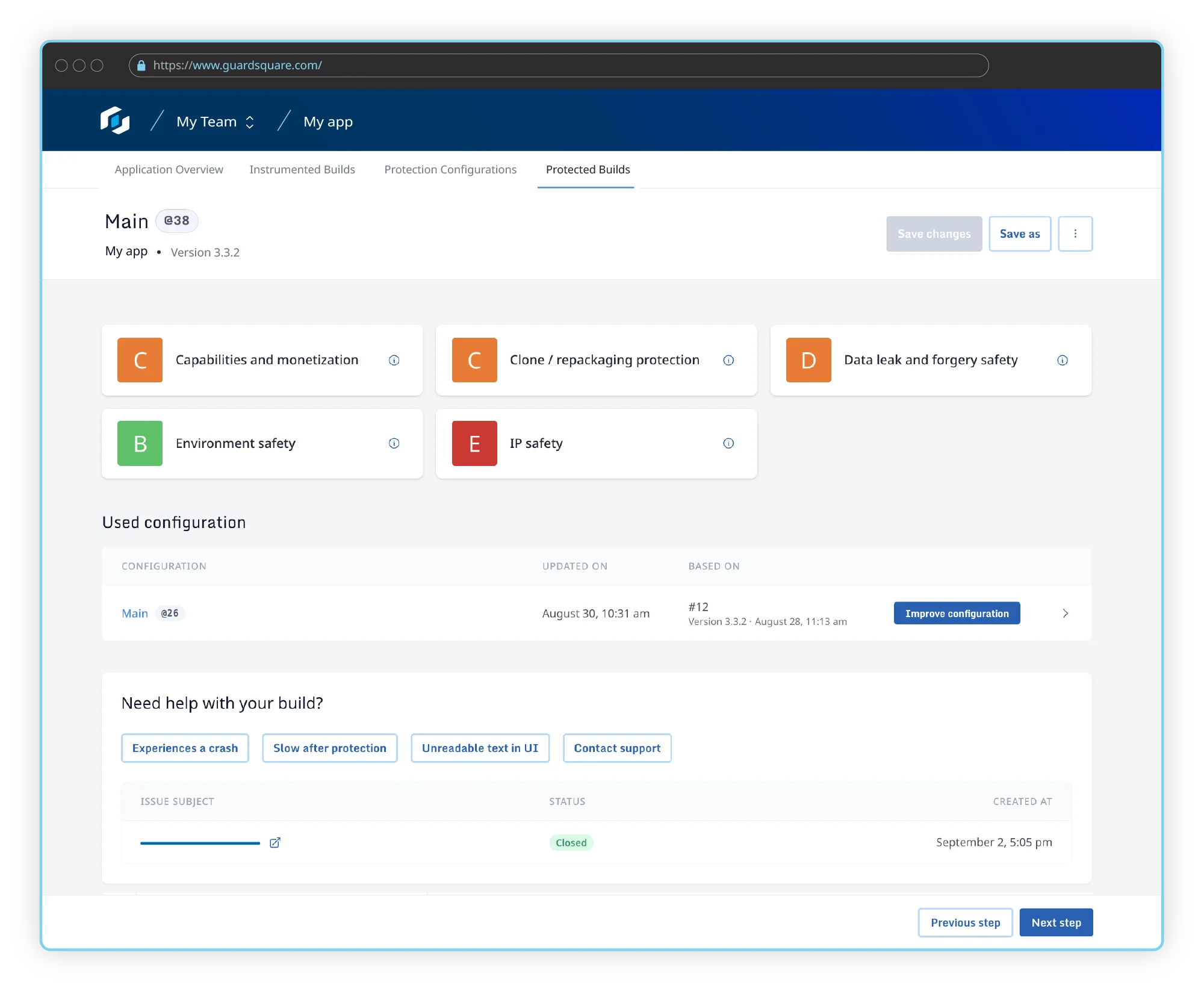
Best for: Teams shipping high-value Android and iOS apps that need strong anti-reversing and RASP protection. License: Commercial (ProGuard is open-source) Key difference: Build-level code obfuscation and RASP for Android (DexGuard) and iOS (iXGuard). Not a scanner — a hardening toolkit.
8. HCL AppScan
HCL AppScan 360° is the enterprise AppSec platform play for teams that want mobile security bundled with SAST, DAST, IAST, and SCA under one license. AppScan SAST alone scans 30+ languages including Java, .NET, C/C++, Python, Go, COBOL, and Swift — one of the broadest language sets in enterprise SAST.
For individual developers, the free CodeSweep VS Code extension provides SAST scanning in the IDE at no cost.
On the AI side, Intelligent Code Analytics (ICA) and Intelligent Finding Analytics (IFA) reduce false positives and prioritize findings.
Mobile testing is part of the unified 360° platform rather than a standalone product, which is where the trade-off lives. If you already run AppScan for web or backend SAST, adding mobile coverage avoids a separate vendor.
If you are mobile-only, a dedicated tool like NowSecure or Appknox is typically a better fit. HCL AppScan is positioned for enterprises consolidating AppSec tooling — the opposite of MobSF’s “one tool, one job” model.
Pricing is quote-based, and the platform is most common in established enterprise environments with existing IBM Rational or HCL software footprints.
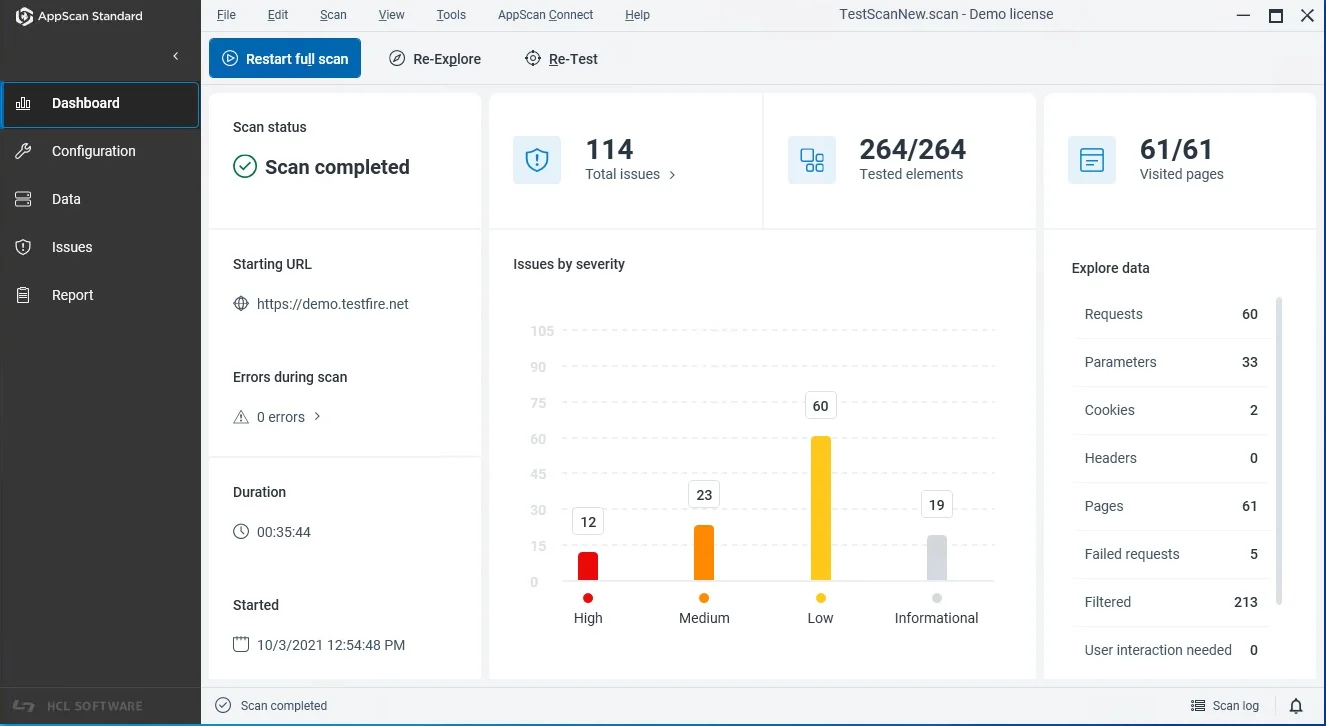
Best for: Enterprises consolidating SAST, DAST, IAST, SCA, and mobile under one AppSec platform. License: Commercial (CodeSweep IDE extension is free) Key difference: Mobile testing bundled inside the broader AppScan 360° platform alongside web and backend AppSec.
Feature Comparison
| Feature | MobSF | NowSecure | Appknox | Ostorlab | Zimperium | Corellium | Data Theorem | Guardsquare | HCL AppScan |
|---|---|---|---|---|---|---|---|---|---|
| License | Open-source | Commercial | Commercial | Freemium | Commercial | Commercial | Commercial | Commercial | Commercial |
| Static analysis | Yes | Yes | Yes | Yes | Yes | MATRIX | Yes | No | Yes |
| Dynamic analysis | Frida-based | Yes | Yes | Yes | Yes | Virtual devices | Yes | No | Yes |
| iOS + Android | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Yes |
| Manual pentesting | No | PTaaS | 3-5 day reports | No | No | No | No | No | Services |
| Virtual devices | No | No | No | No | No | Core feature | No | No | No |
| Code hardening/RASP | No | No | No | No | zShield (sibling) | No | Runtime protection | Core feature | No |
| SBOM | No | Dynamic SBOM | Binary-based | No | Yes | No | Yes | No | Yes |
| App store monitoring | No | No | Storeknox | No | No | No | Yes | No | No |
| MASA authorized lab | No | Yes | No | No | No | No | No | No | No |
| Self-hosted | Yes (Docker) | No | On-prem option | OXO self-host | No | On-prem/air-gap | No | Yes (build-time) | On-prem option |
When to Stay with MobSF
MobSF is still the right choice in plenty of scenarios:
- You are an individual researcher or small team. MobSF is free, Dockerized, and covers static and dynamic analysis for Android and iOS. For solo work or teams of 2-5, the cost of commercial alternatives rarely pays off.
- Budget is zero. Commercial mobile AppSec platforms are quote-based and enterprise-priced. MobSF has no usage limits and no paid tier.
- You need a CI-friendly static scanner. The REST API and mobsfscan CLI make MobSF easy to wire into GitHub Actions, GitLab CI, or any pipeline. For basic “fail the build on hardcoded secrets” workflows, MobSF is sufficient.
- You are fine with self-hosting and self-support. If your team is comfortable running Docker containers, patching CVEs (MobSF v4.4.6 fixed an SQL injection in March 2026), and troubleshooting without vendor support, MobSF works.
- You pair it with a commercial tool. Many teams run MobSF for quick CI scans while using NowSecure, Appknox, or Corellium for deeper analysis and compliance reporting.
Pro tip: MobSF is licensed under GPL-3.0, which permits commercial use of the tool itself. If you modify and redistribute MobSF source code in a closed-source product, copyleft obligations apply — review the license carefully before bundling MobSF into a commercial offering.
For more AppSec Santa mobile security comparisons, see the mobile security tools category.
Frequently Asked Questions
What is the best commercial alternative to MobSF?
Is there an open-source alternative to MobSF?
Does MobSF do everything Corellium does?
Can I use MobSF and a commercial tool together?
Which MobSF alternative supports app hardening?

Founder, AppSec Santa
Years in application security. Reviews and compares 215 AppSec tools across 12 categories to help teams pick the right solution. More about me →
