Top Ghidra Alternatives
View all 20 alternatives →
Android APK resource decoding & rebuild

No-Code Mobile Defense Automation

Mobile AppSec trusted by 300+ enterprises

ARM-based virtual iOS & Android devices for security research

Full-stack mobile AppSec

Android attack surface assessment framework
- Ghidra is the de-facto open-source RE platform with 68k+ GitHub stars and a strong decompiler. The closest commercial alternative is IDA Pro from Hex-Rays, the historical industry standard for x86 / x64 disassembly and decompilation.
- Binary Ninja from Vector 35 has surged in popularity for its modern UI, scriptable API, and strong decompiler at a perpetual one-time licence price below IDA Pro's annual subscription.
- radare2 plus its modern fork Rizin (with Cutter as the GUI) cover most of Ghidra's open-source ground with a different command-line-first design philosophy.
- Hopper Disassembler is the macOS-native alternative for Mach-O and iOS work, with a one-time licence rather than IDA's subscription.
- JEB Decompiler from PNF Software specialises in Android DEX, native ARM, MIPS, and Ethereum smart contracts. angr is the symbolic-execution framework when you need automated analysis rather than manual exploration.
The best Ghidra alternatives in 2026 are IDA Pro, Binary Ninja, Hopper Disassembler, radare2, Cutter + Rizin, JEB Decompiler, angr, and IDA Free. Each one swaps part of Ghidra’s role: commercial polish, modern UI, macOS-native UX, CLI workflow, or symbolic execution.
The strongest paid alternative is IDA Pro. The strongest open-source alternative is Rizin + Cutter. The best value commercial pick is Binary Ninja at a one-time licence below IDA Pro’s annual cost.
Each option is reviewed below so you can pick the right fit for your target platform and workflow.
Why Look for Ghidra Alternatives?
Ghidra is the NSA-built open-source reverse engineering framework with 68k+ GitHub stars . Since its 2019 release, it has become the default open-source RE platform.
It is fully free under the Apache 2.0 licence, supports a long list of processor architectures, and ships with a production-quality decompiler. The Ghidra ecosystem includes scripts, plugins, and a Python (Jython) and Java extension API.
For independent researchers and academic work, Ghidra is the default starting point.
Friction shows up in a few places. Ghidra is a Java application, so startup time, memory use, and UI responsiveness lag behind native commercial alternatives. The workflow is dense, and the learning curve is steeper than Binary Ninja’s modern UX.
Debugger integration is also weaker than IDA Pro’s, particularly for live debugging and dynamic analysis sessions.
For teams that hit those friction points often, the commercial alternatives offer better polish at a price.
Top Ghidra Alternatives
1. IDA Pro
IDA Pro from Hex-Rays is the long-standing commercial reference for reverse engineering. The Hex-Rays decompiler is the most mature option for x86 and x64, with separate decompilers available for ARM, ARM64, MIPS, PowerPC, and other architectures.
The plugin ecosystem is the largest in the RE world. Scripts and plugins exist for malware analysis, vulnerability research, firmware analysis, and smart contract review.
IDA Pro is subscription-based. Hex-Rays’ pricing page lists tiers from IDA Pro Essential at $1,099/year up to IDA Pro Ultimate at $8,599/year. For institutions and professional teams it remains the default; for solo work, the cost often pushes people to Ghidra or Binary Ninja.
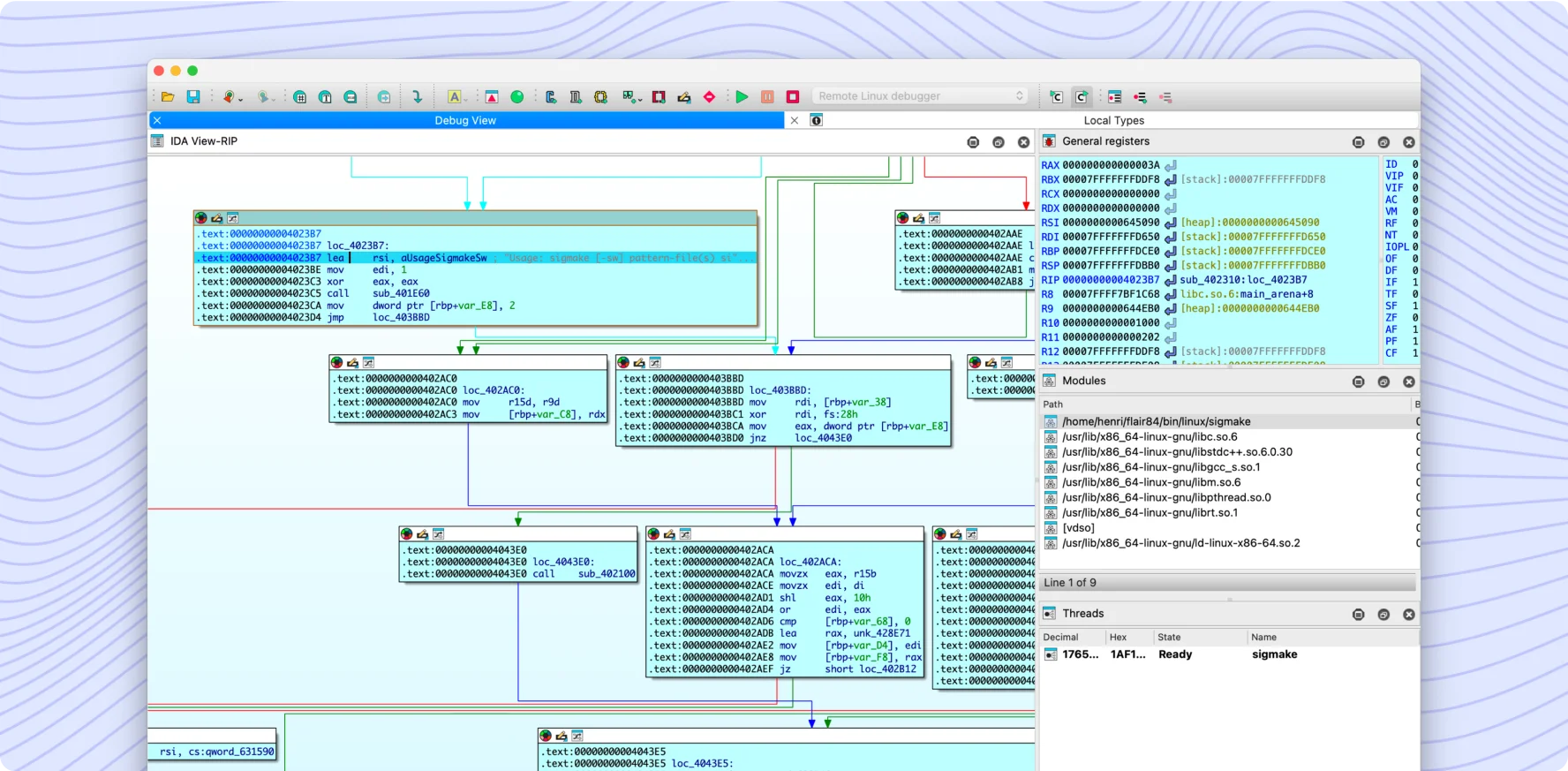 IDA Pro’s graph view connects basic blocks of x86 disassembly while the side panes track types, modules, and threads in the same workspace.
IDA Pro’s graph view connects basic blocks of x86 disassembly while the side panes track types, modules, and threads in the same workspace.
When to choose IDA Pro over Ghidra: when budget allows and decompiler maturity for x86 / x64 plus the largest plugin ecosystem matter more than open-source licensing.
2. Binary Ninja
Binary Ninja from Vector 35 has gained traction as a commercial alternative since 2020. The product positions itself as a modern RE platform with a clean UI, scriptable Python API, strong decompiler, and a perpetual one-time licence rather than IDA Pro’s annual subscription.
Personal licences are $299, Commercial $1,499, and Ultimate $2,999 (each with one year of updates). The pricing sits closer to a developer-tool tier than IDA Pro’s enterprise tiers.
The decompiler is strong for x86, x64, and ARM. Architecture breadth is narrower than Ghidra or IDA Pro but covers what most users need. The plugin ecosystem is smaller than IDA’s, though growing.
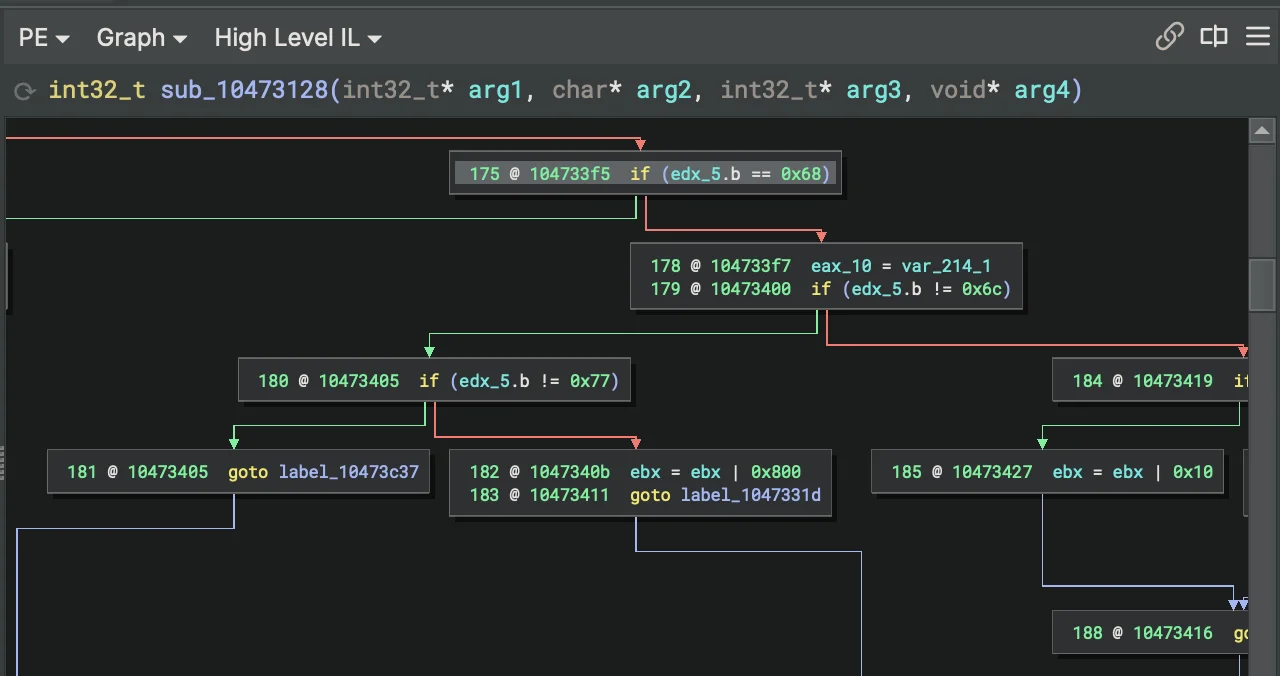 Binary Ninja’s High Level IL renders the function as readable conditionals between basic blocks, closer to source than raw assembly.
Binary Ninja’s High Level IL renders the function as readable conditionals between basic blocks, closer to source than raw assembly.
When to choose Binary Ninja over Ghidra: when a modern UI and Python-scriptable workflow matter more than Ghidra’s wider architecture support, and a one-time licence is acceptable.
3. Hopper Disassembler
Hopper Disassembler is a macOS-native disassembler used for iOS reverse engineering and Mach-O analysis. It supports x86, x64, ARM, and ARM64.
Pricing is a one-time licence: €99 for the personal licence and €129 for the per-computer licence (Hopper webstore). The one-time model is unusual in the RE space and attractive for solo practitioners.
Hopper does not match IDA Pro or Ghidra on architecture breadth. For macOS and iOS work it is a focused fit. For Linux or Windows analysis, the alternatives above are more capable.
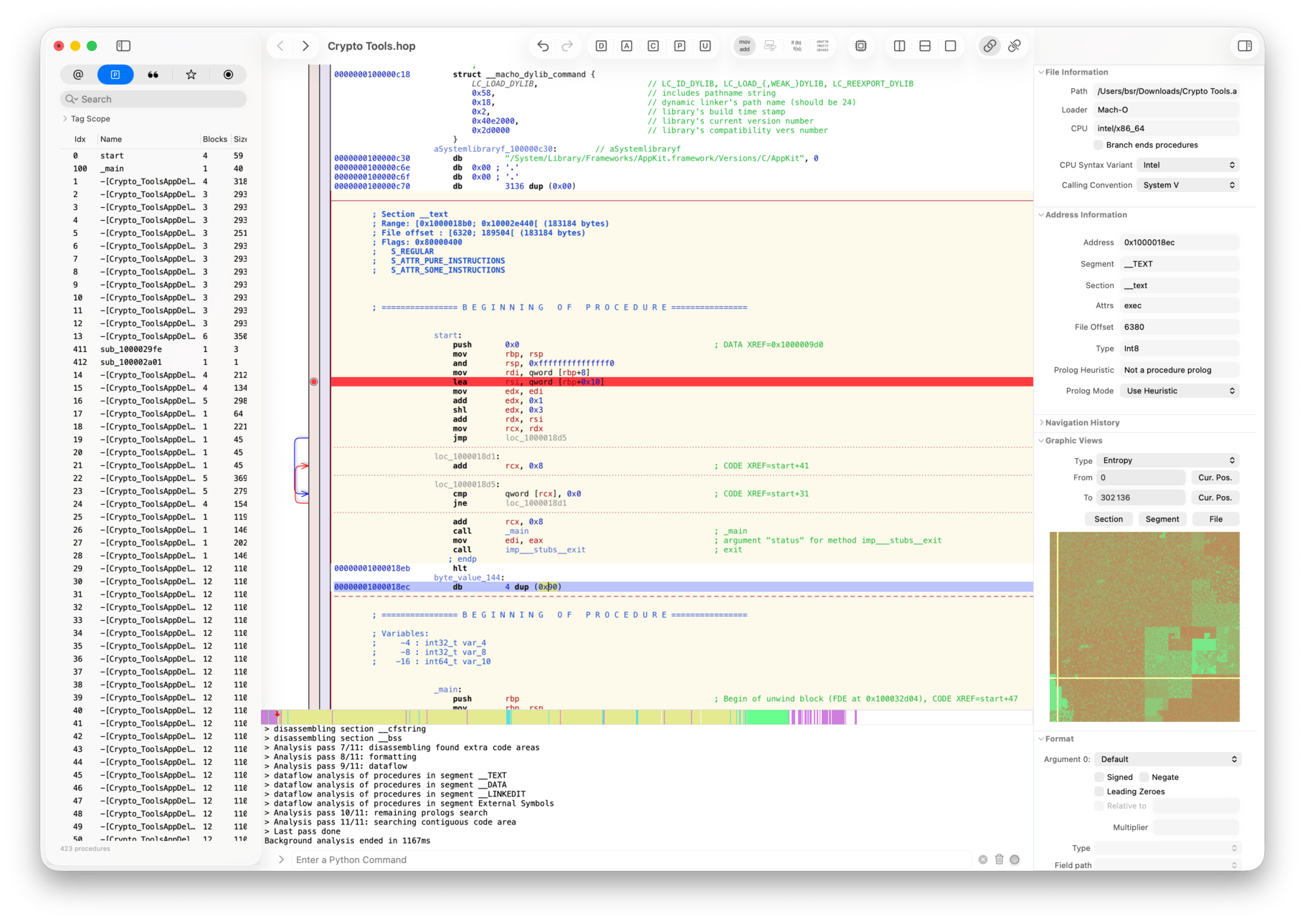 Hopper feels native on macOS: the procedure list, disassembly, and inspector ride the same toolbar as any other Mac app, with no JVM in the way.
Hopper feels native on macOS: the procedure list, disassembly, and inspector ride the same toolbar as any other Mac app, with no JVM in the way.
When to choose Hopper over Ghidra: when macOS / iOS Mach-O analysis is the main workload and a native-feel macOS app outweighs Ghidra’s broader architecture list.
4. radare2
radare2 is the long-running open-source command-line reverse engineering framework. It covers disassembly, debugging, binary analysis, and scripting across most architectures.
The defining trait is the CLI-first workflow. Most operations are radare2 commands typed at a prompt rather than menu clicks. The learning curve is steeper than Ghidra’s GUI but rewards investment with a powerful, scriptable workflow.
A web UI (Iaito), a GUI (Cutter), and active community plugins extend the toolset. For reverse engineers comfortable with CLI workflows, radare2 is the most flexible OSS alternative.
 radare2 visual mode tiles disassembly, calls, registers, and an ASCII function graph into a single terminal window driven entirely by keystrokes.
radare2 visual mode tiles disassembly, calls, registers, and an ASCII function graph into a single terminal window driven entirely by keystrokes.
When to choose radare2 over Ghidra: when scripting and CLI automation drive most of the workflow, and Ghidra’s Java GUI feels too heavy for batch or pipeline analysis.
5. Cutter (with Rizin)
Cutter is the Qt-based GUI for Rizin, a modern fork of radare2 maintained as a more stable, refactored codebase. The Cutter + Rizin pair is the closest open-source match to Ghidra’s free-and-capable positioning.
Cutter ships with a decompiler (rz-ghidra, which embeds the Ghidra decompiler), debugger integration, and a plugin SDK. The UX is closer to a modern desktop application than radare2’s CLI roots.
For users who want radare2’s power with a GUI workflow, Cutter is a good fit. For users who want Ghidra’s GUI feel without Java startup cost, Cutter is a strong alternative.
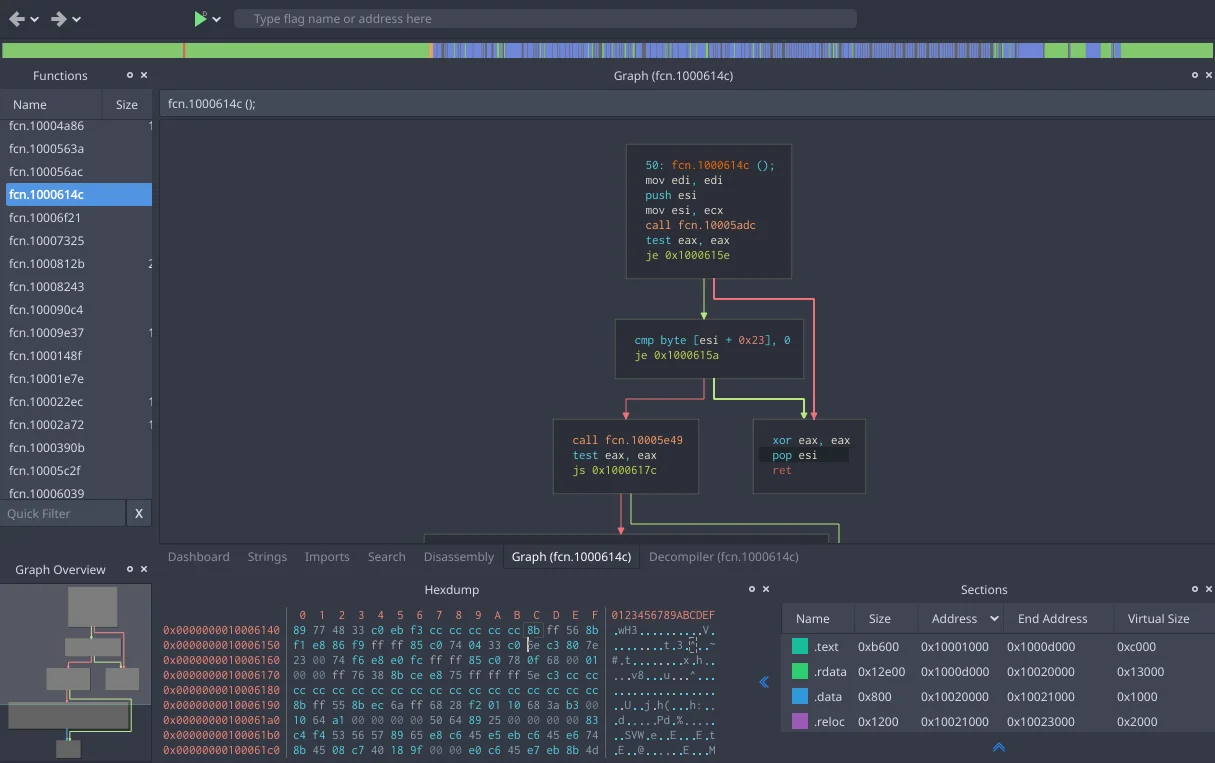 Cutter wraps Rizin in a Qt desktop UI: the Functions list, control-flow graph, hex dump, and section map dock into one workspace driven by Rizin commands underneath.
Cutter wraps Rizin in a Qt desktop UI: the Functions list, control-flow graph, hex dump, and section map dock into one workspace driven by Rizin commands underneath.
When to choose Cutter + Rizin over Ghidra: when a native Qt GUI with the Ghidra decompiler, faster startup, and a refactored radare2 codebase matter more than Ghidra’s plugin ecosystem.
6. JEB Decompiler
JEB Decompiler from PNF Software is a commercial RE platform with broad target support: Android DEX, x86, x86-64, ARM, ARM64, MIPS, RISC-V, WebAssembly, Ethereum smart contracts, Flutter/Dart AOT, and a few niche formats (Simatic S7 PLC, Nvidia GPU SASS, PDF).
The Android DEX decompiler is one of the strongest on the market. Teams that use Ghidra or IDA Pro for x86 work often switch to JEB for Android.
Pricing is per-product (separate licences gate the various decompilers), and total cost can rival IDA Pro for full coverage. For Android-heavy work specifically, JEB is the standard alongside Ghidra.
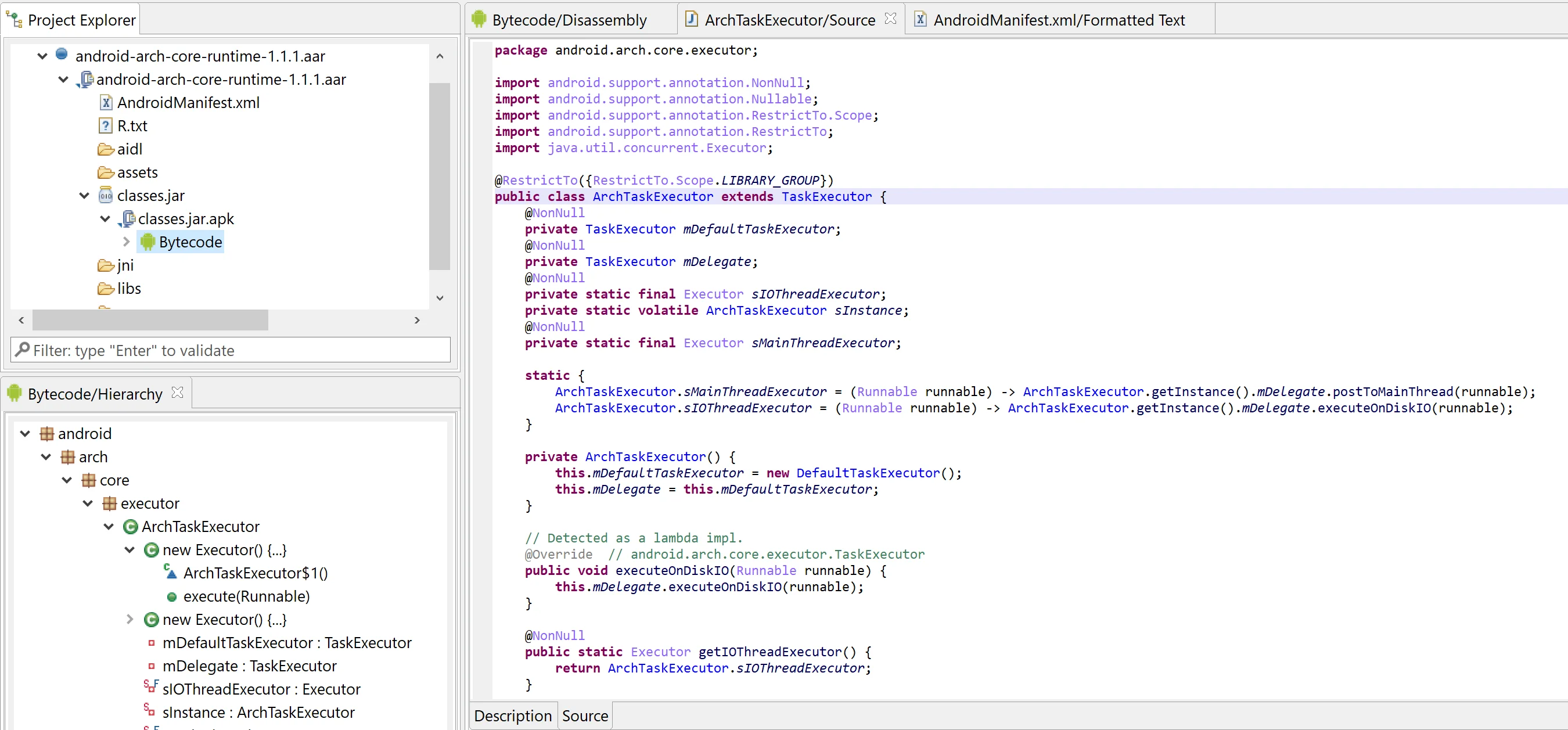 JEB lifts Android
JEB lifts Android .aar bytecode straight to Java source — here ArchTaskExecutor is read as readable Java with annotations preserved, not as DEX opcodes.
When to choose JEB over Ghidra: when Android DEX, smart contracts, or niche embedded targets (Simatic S7, Nvidia SASS, Flutter AOT) need a stronger decompiler than Ghidra’s stock output.
7. angr
angr is a Python-based binary analysis framework for symbolic execution, control-flow analysis, and automated vulnerability discovery. It is not a GUI tool; angr is a library for writing analysis scripts.
For automated analysis tasks (CTF challenges, automated exploit generation, fuzzing harness setup, taint analysis), angr is the strongest open-source option. The trade-off is that angr requires writing Python; there is no out-of-the-box “open binary, browse decompilation” workflow.
angr complements Ghidra rather than replacing it. Use Ghidra for manual exploration; use angr for automated analysis.
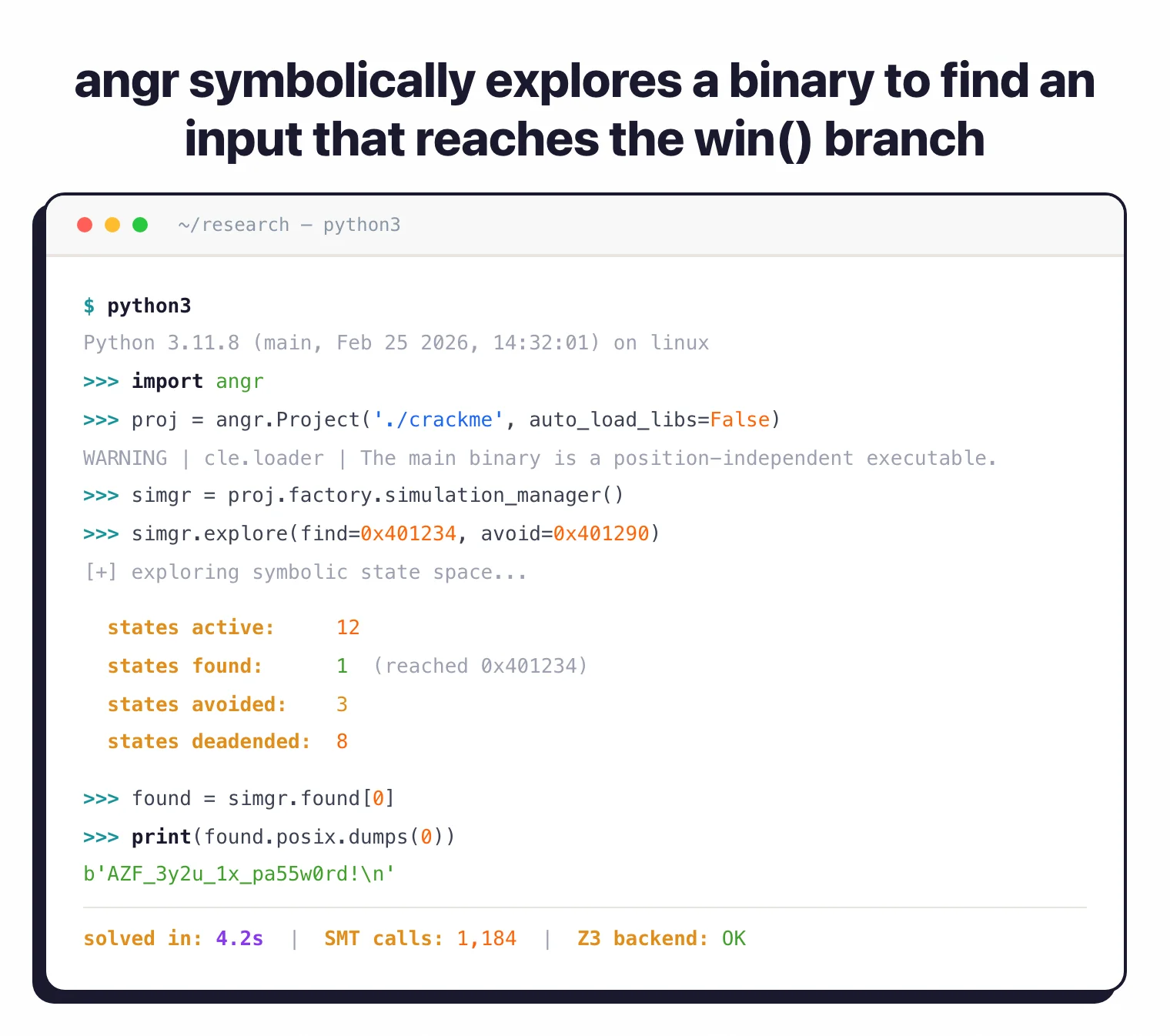 angr is a library, not a GUI: a few lines of Python set up a Project, ask the simulation manager to reach
angr is a library, not a GUI: a few lines of Python set up a Project, ask the simulation manager to reach 0x401234, and recover the input that satisfies the path constraints.
When to choose angr over Ghidra: when the task is automated reasoning over a binary (symbolic execution, taint analysis, exploit-gen) rather than interactive disassembly and decompilation.
8. IDA Free
IDA Free from Hex-Rays is the no-cost edition of IDA. It is restricted to x86 and x86-64 disassembly, ships a cloud-based decompiler limited to those same two targets, and is licensed for non-commercial use only.
For students and curious users who want to know what IDA looks like before paying for IDA Pro, IDA Free is the gateway. For production work, the architecture limits and absence of the IDA C++ SDK or IDAPython API make it less useful than Ghidra or radare2.
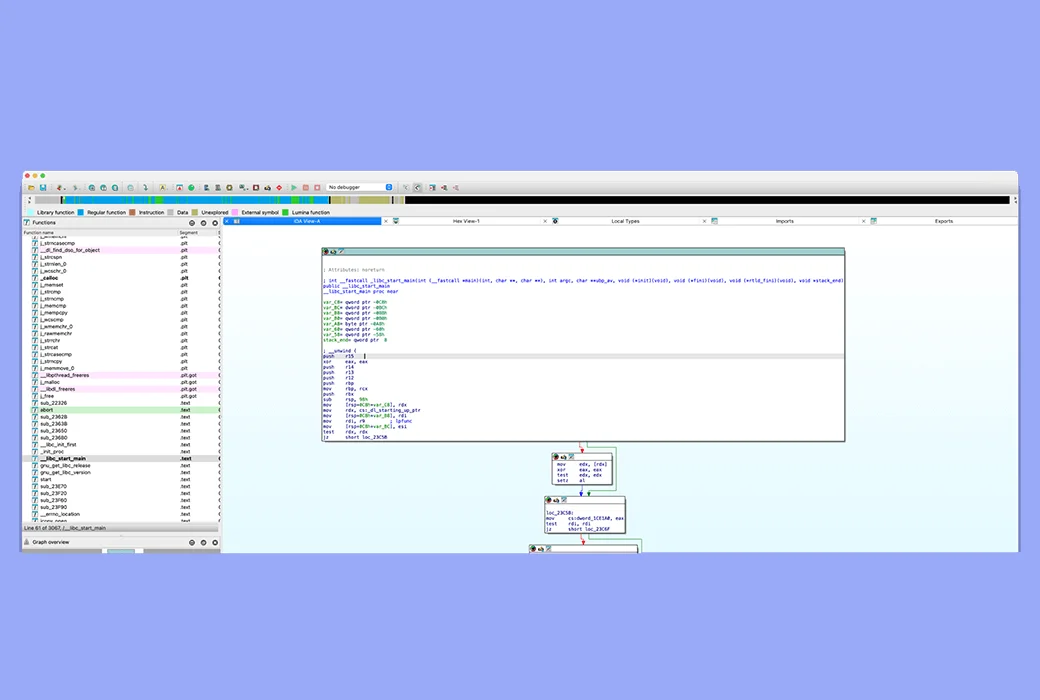 IDA Free shows the same Functions panel, IDA-View disassembly, and graph layout as IDA Pro, but disassembly is locked to x86 / x64 and no IDAPython is available.
IDA Free shows the same Functions panel, IDA-View disassembly, and graph layout as IDA Pro, but disassembly is locked to x86 / x64 and no IDAPython is available.
When to choose IDA Free over Ghidra: essentially never for production work; only as a free taste of IDA’s UI before deciding on IDA Pro, since Ghidra is broader and fully scriptable.
Feature Comparison
| Tool | License | Pricing model | Decompiler | Best for |
|---|---|---|---|---|
| Ghidra | Apache 2.0 | Free | Strong | All-purpose open-source RE |
| IDA Pro | Commercial | Subscription ($1,099–$8,599/yr) | Best-in-class (Hex-Rays) | Professional teams with budget |
| Binary Ninja | Commercial | One-time + 1yr updates ($299–$2,999) | Strong | Modern UI + scriptable workflow |
| Hopper | Commercial | One-time (€99–€129) | Solid for Mach-O | macOS / iOS reverse engineering |
| radare2 | LGPL-3 | Free | Via r2ghidra | CLI-first workflow, scripting |
| Cutter + Rizin | GPL-3 | Free | Strong (rz-ghidra) | GUI for radare2 / Rizin lineage |
| JEB Decompiler | Commercial | Per-product licence | Class-leading Android DEX | Android, ARM, MIPS, smart contracts |
| angr | BSD-2 | Free | N/A (Python framework) | Symbolic execution, automated analysis |
| IDA Free | Free / personal | Free | Cloud x86/x64 only | Trying IDA’s workflow before paying |
When to Stay with Ghidra
Ghidra is still the right tool for several scenarios.
When budget is zero and you need a full-featured GUI RE platform: Ghidra’s combination of free price, strong decompiler, and broad architecture support is difficult to match for solo and academic work.
When you work with uncommon architectures: Ghidra supports a wide list of exotic embedded processors, microcontrollers, and legacy chips that IDA Pro charges separately for or does not cover.
When sharing and collaborating with peers in security research: Ghidra projects export cleanly, analysis scripts are Java / Python (Jython), and the open licence makes sharing trivial.
If your work fits any of those, the right move is to keep Ghidra and add a commercial tool only when specific friction points (decompiler quality on a target, debugger integration, UI responsiveness) become recurring blockers.
Related comparisons
- Ghidra vs Radare2 : two open-source RE platforms head-to-head.
- Apktool vs Jadx : Android decompiler comparison.
- Frida alternatives : dynamic instrumentation tools that complement static RE.
- Mobile security tools : wider category overview.
Frequently Asked Questions
What is the best alternative to Ghidra?
Is IDA Pro better than Ghidra?
Is Binary Ninja a good Ghidra alternative?
Can radare2 or Rizin replace Ghidra?
What about Hopper Disassembler?

Founder, AppSec Santa
9+ years in application security. Reviews and compares 201 AppSec tools across 12 categories to help teams pick the right solution. More about me →
