Top Frida Alternatives
View all 20 alternatives →
Android APK resource decoding & rebuild

No-Code Mobile Defense Automation

Mobile AppSec trusted by 300+ enterprises

ARM-based virtual iOS & Android devices for security research

Full-stack mobile AppSec

Android attack surface assessment framework
- Frida is the default for cross-platform mobile dynamic instrumentation, but Android-only Xposed and Magisk + Zygisk reach deeper into the Zygote and survive app restarts.
- Objection wraps Frida with one-line commands for SSL pinning bypass, root detection bypass, and keystore dumps, so you can use Frida without writing JavaScript.
- QBDI from Quarkslab gives instruction-level instrumentation in C/C++ and Python rather than Frida's JavaScript API, which fits low-level binary analysis better.
- MobSF bundles a Frida workflow inside a static + dynamic platform with reports, so teams that want a UI instead of a CLI rarely need raw Frida.
- Cycript and Cydia Substrate are legacy iOS hooking frameworks largely superseded by Frida on modern iOS, useful only for older jailbreak research.
The best Frida alternatives in 2026 are Objection, Xposed Framework, Magisk + Zygisk, QBDI, Cycript, Cydia Substrate, MobSF, and Ghidra. Each one swaps part of Frida’s role: faster CLI bypasses, deeper Android hooks, lower-level binary instrumentation, or static analysis instead of runtime injection.
Quick answer: Pick Objection for one-line SSL pinning and root detection bypasses, Xposed or Magisk + Zygisk for persistent Android-only hooks, QBDI for instruction-level fuzzing, MobSF for a UI plus reports, and Ghidra for static analysis without runtime injection.
Each option is reviewed below so you can match the tool to your target platform and analysis depth.
Why Look for Frida Alternatives?
Frida is the default choice for mobile dynamic instrumentation. With 20.5k GitHub stars and an active maintainer, it tracks new iOS and Android releases as they ship.
It is free under the wxWindows Library Licence, runs on Android, iOS, Windows, macOS, and Linux, and ships with a JavaScript API for writing custom hooks. Few open-source instrumentation tools cover that platform range.
The friction shows up in three places. Every common task (SSL pinning bypass, root detection bypass, keystore dump) needs JavaScript you either write yourself or copy from gists. Frida hooks are per-process, so they vanish when the app restarts.
On Android, jailbreak-style root detection often spots the frida-server process and kills the app before any hooks land.
That is why most teams either layer Objection on top of Frida or drop into Android-specific frameworks like Xposed or Magisk + Zygisk for persistent hooks.
Top Frida Alternatives
1. Objection
Objection is a runtime mobile exploration toolkit built on top of Frida. It exposes the common bypasses (SSL pinning, root detection, jailbreak detection, keystore dumping, biometric auth) as one-line CLI commands instead of JavaScript.
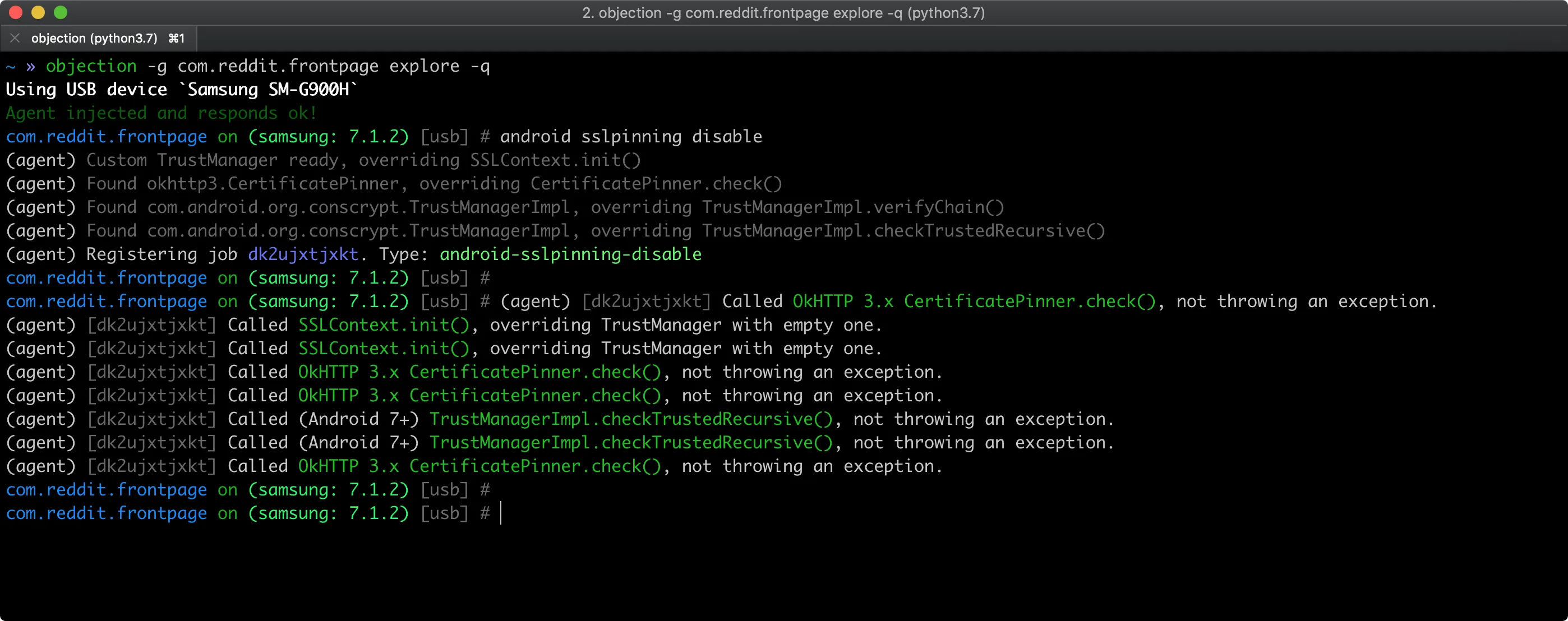 Objection wraps Frida in one-line commands; here
Objection wraps Frida in one-line commands; here android sslpinning disable overrides every TrustManager call without writing any JavaScript.
If you spend most of your Frida time copy-pasting the same hooks, Objection collapses that into objection -g com.example.app explore followed by built-in commands like android sslpinning disable.
It is open source under GPL-3.0 and works anywhere Frida works. The trade-off is reach: for hooks Objection does not ship, you still need raw Frida.
When to choose Objection over Frida: you want SSL pinning, root detection, or keystore dumps in one CLI command without writing JavaScript hooks.
2. Xposed Framework
Xposed is an Android-only modular framework that hooks at the Zygote level, the parent process for every app on the system. Hooks installed via Xposed modules survive app restarts and reach deeper system services than Frida’s per-process injection.
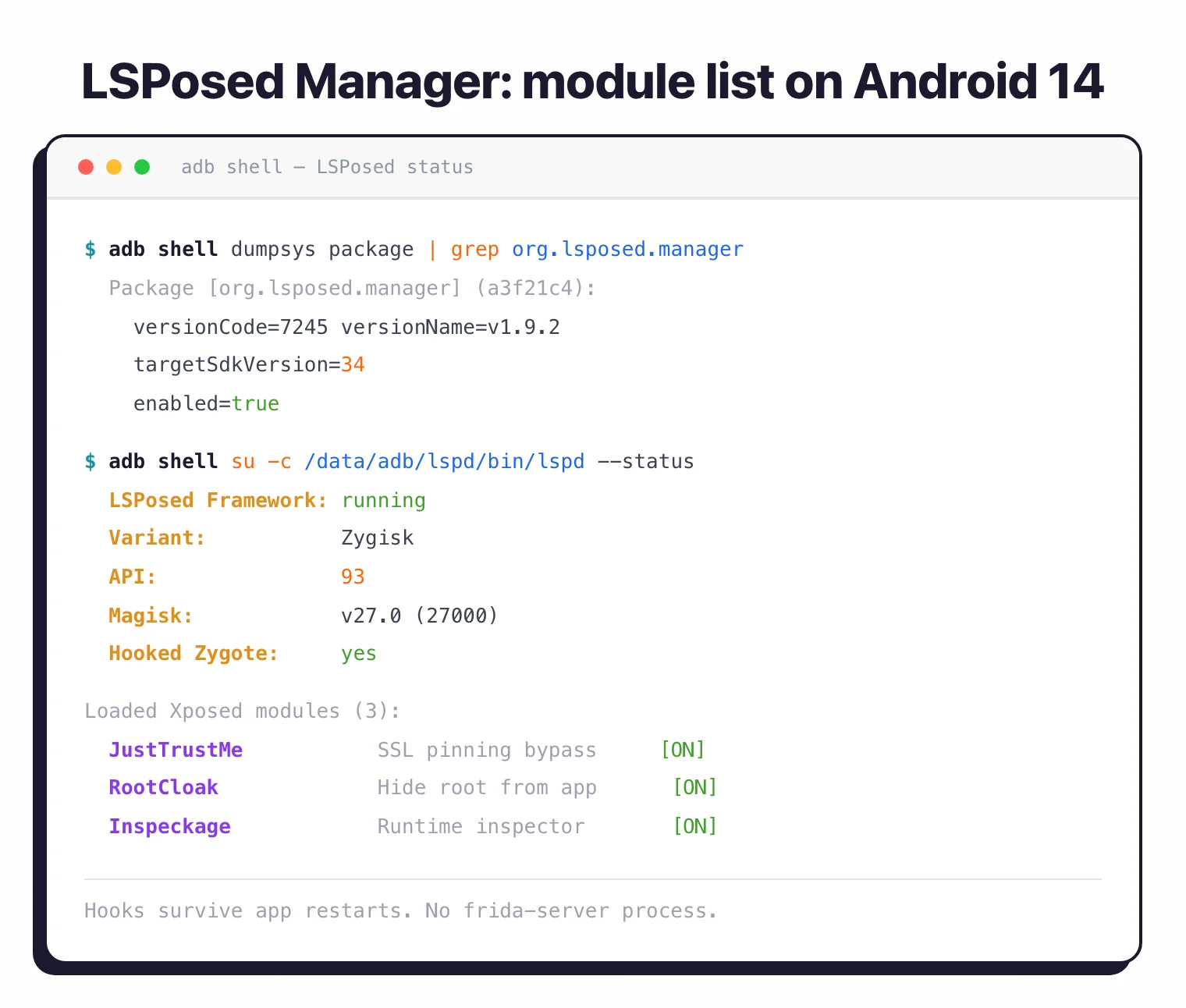 LSPosed’s status check confirms Zygote is hooked and three modules persist across restarts, no frida-server process required.
LSPosed’s status check confirms Zygote is hooked and three modules persist across restarts, no frida-server process required.
The original Xposed project is largely dormant on modern Android. Its successor LSPosed was archived in March 2025 with final support for Android 8.1 through 14. Community forks like LSPosed_mod continue limited development for newer Android releases.
Xposed needs a rooted device or a Magisk module to bootstrap. There is no iOS support and no cross-platform reach. What you get is depth and persistence on Android.
When to choose Xposed over Frida: you only target Android and need Zygote-level hooks that persist across app restarts and reach system services Frida cannot.
3. Magisk + Zygisk
Magisk is the modern Android rooting framework, and Zygisk is its in-process Zygote injection mechanism. Together they offer a Frida-adjacent hook surface that runs without spawning a separate frida-server process, which makes it harder for apps to detect.
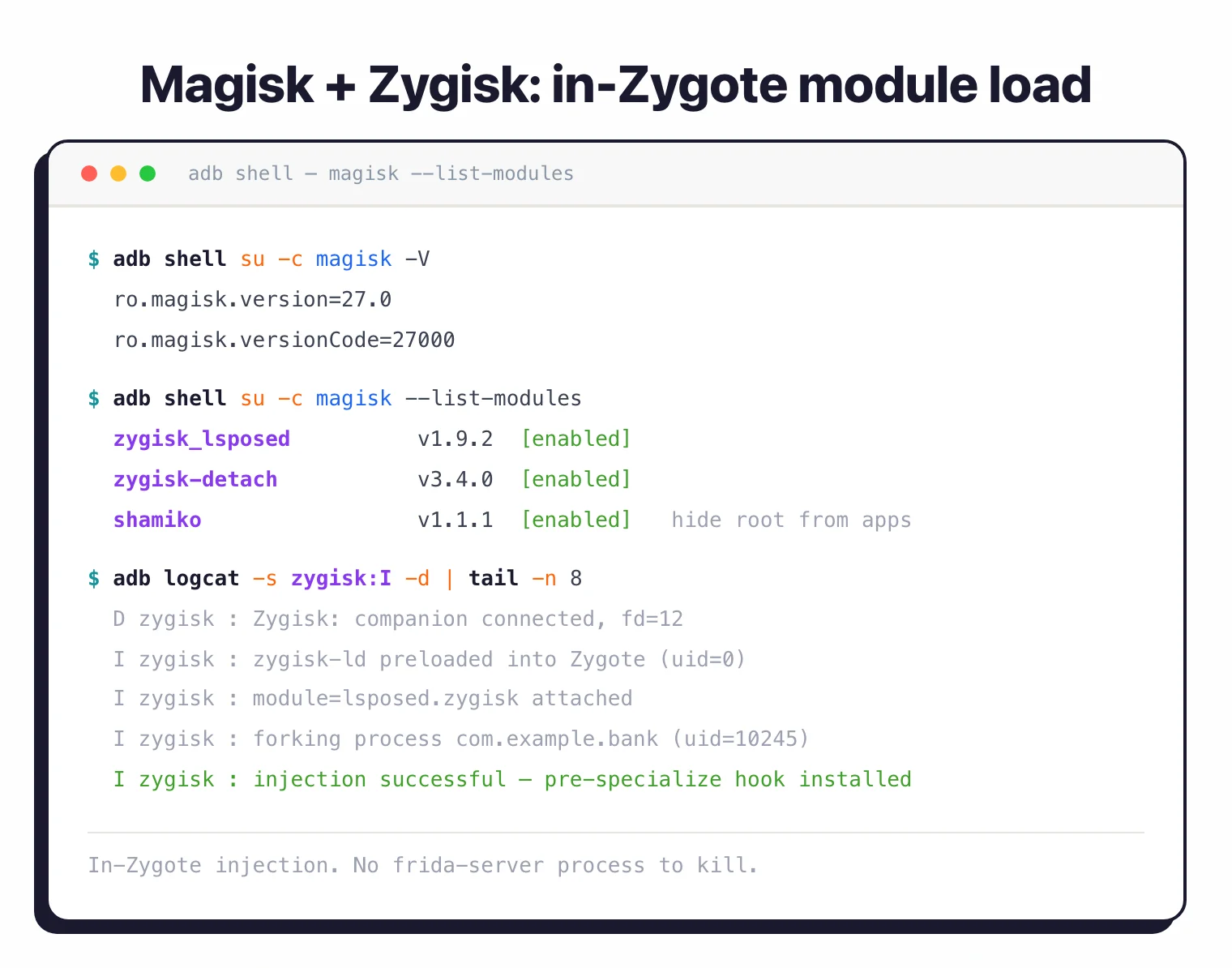 Magisk + Zygisk inject inside Zygote during the app fork, so anti-tamper code that scans for
Magisk + Zygisk inject inside Zygote during the app fork, so anti-tamper code that scans for frida-server finds nothing to kill.
LSPosed itself is built on Zygisk, so for Android instrumentation work where Frida gets killed by anti-tamper code, Magisk + Zygisk modules become the answer.
The cost is a steeper learning curve and the need to write modules in C++ or Java rather than Frida’s JavaScript.
When to choose Magisk + Zygisk over Frida: anti-tamper code is killing the frida-server process and you need in-Zygote injection that the app cannot easily detect.
4. QBDI
QBDI (QuarkslaB Dynamic binary Instrumentation) is a low-level instrumentation library from Quarkslab. It instruments at the instruction level rather than the function level, with bindings for C/C++, Python, and JavaScript.
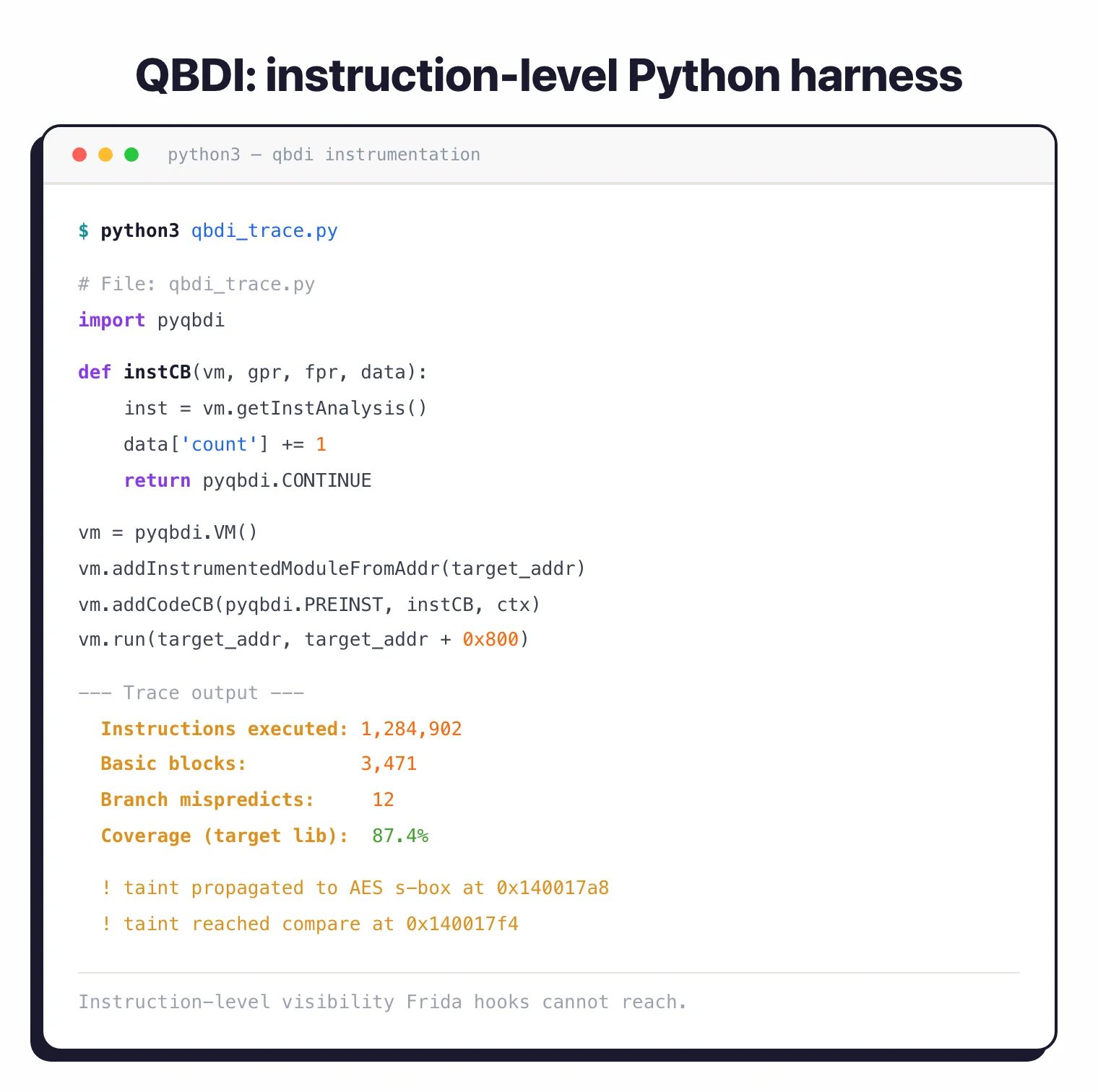 A short pyqbdi harness traces every executed instruction, calculates basic-block coverage, and follows tainted bytes into AES routines that Frida cannot see.
A short pyqbdi harness traces every executed instruction, calculates basic-block coverage, and follows tainted bytes into AES routines that Frida cannot see.
QBDI is the right pick when you need coverage-guided fuzzing, taint analysis, or detailed execution traces, the kind of work where Frida’s function hooking is too coarse-grained.
It supports x86, x86_64, ARM, and AArch64 under Apache 2.0. Documentation skews academic, so the ramp-up is longer than Frida’s, but you get instruction-level visibility Frida cannot reach.
When to choose QBDI over Frida: you need instruction-level instrumentation for fuzzing, taint tracking, or coverage analysis where Frida’s function hooks are too coarse.
5. Cycript
Cycript was the original iOS hooking framework, mixing Objective-C and JavaScript syntax for runtime exploration. It dominated jailbreak research from 2010 through 2017 before Frida overtook it in capability and platform reach.
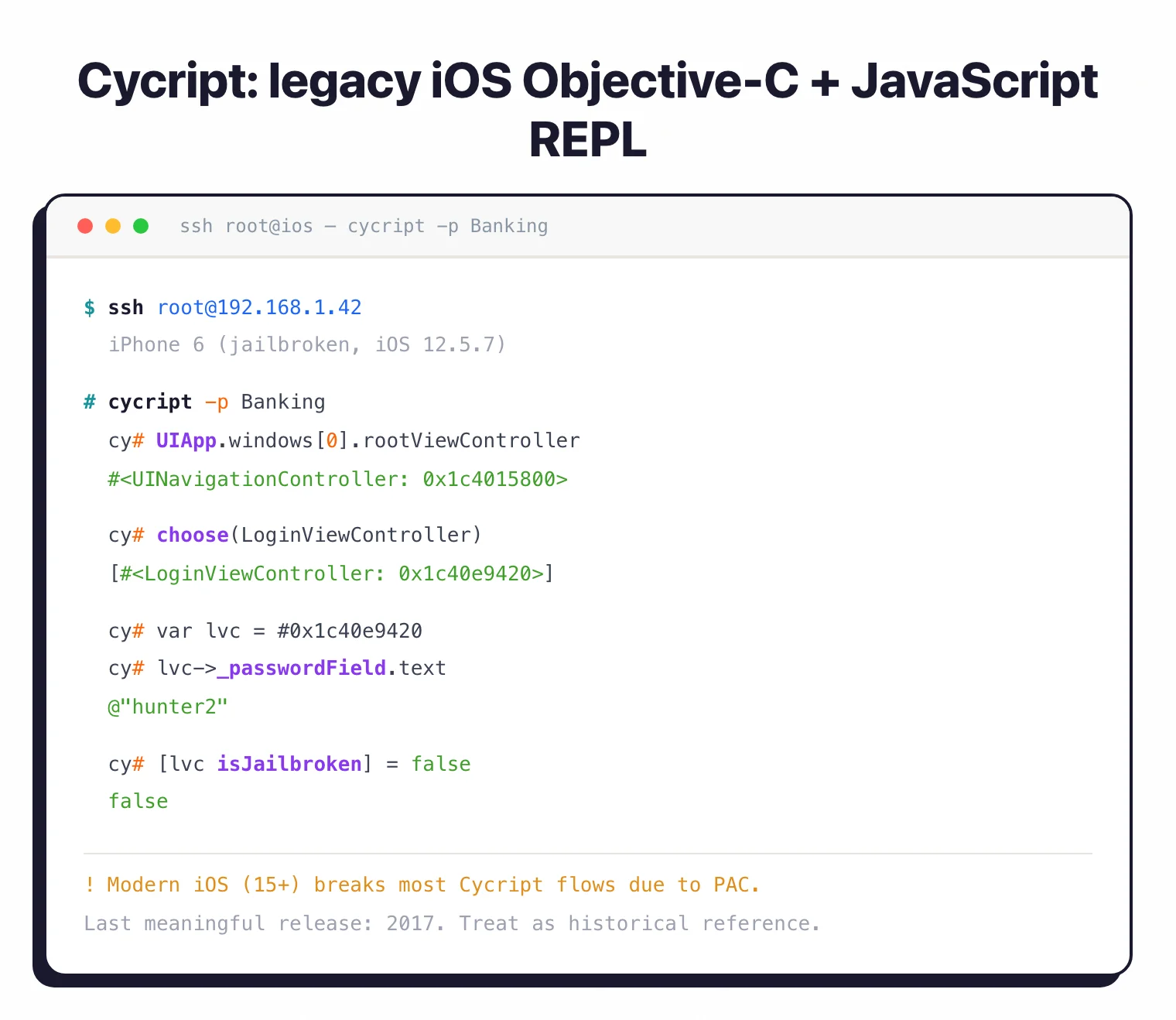 Cycript’s Objective-C plus JavaScript REPL still works on iOS 12 jailbreaks, but PAC and other iOS 15+ mitigations break most modern flows.
Cycript’s Objective-C plus JavaScript REPL still works on iOS 12 jailbreaks, but PAC and other iOS 15+ mitigations break most modern flows.
The project has not seen meaningful releases in years, and modern iOS (15 and later) breaks most Cycript workflows due to PAC and other hardware mitigations.
It still appears in older MASTG-style training material and legacy jailbreak research. For new work, treat Cycript as historical reference rather than a Frida replacement.
When to choose Cycript over Frida: you are reproducing pre-2018 jailbreak research or maintaining legacy iOS tweaks that already depend on its Objective-C plus JavaScript syntax.
6. Cydia Substrate
Cydia Substrate is the iOS code modification platform behind most pre-Frida tweak development. Like Cycript, it was the standard iOS hooking framework before Frida took over the cross-platform niche.
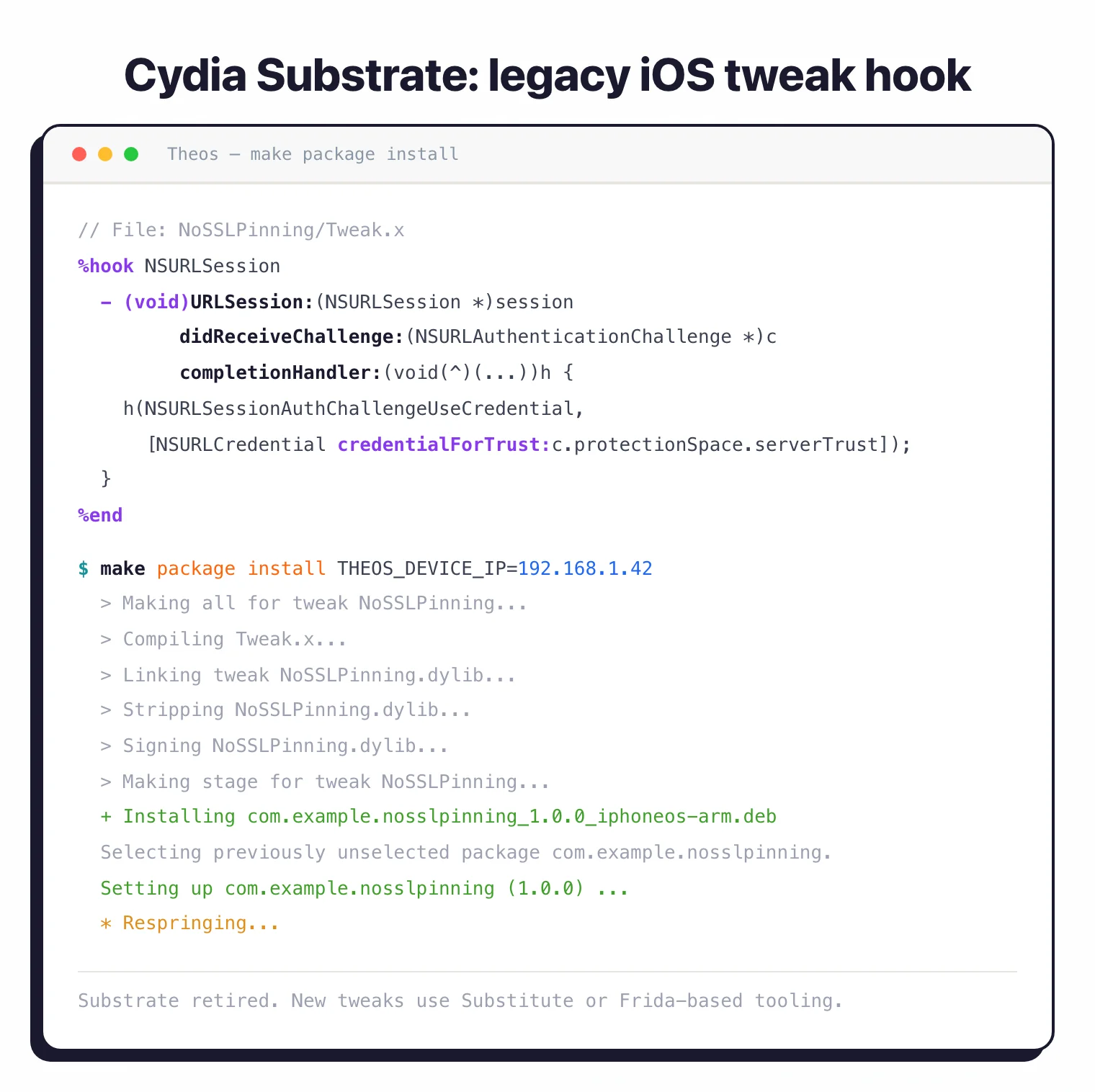 A classic Logos
A classic Logos %hook against NSURLSession plus a Theos build pipeline; Substrate is retired now, with Substitute and Frida tooling carrying new tweaks.
Substrate is still functional on jailbroken iOS but has been retired from active development. Most jailbreak tweaks today either use Substitute (a Substrate-compatible reimplementation) or migrate to Frida-based tooling.
You will mainly encounter Substrate when reading older write-ups or maintaining legacy tweaks. For new iOS analysis, use Frida or Objection.
When to choose Cydia Substrate over Frida: you are maintaining a legacy jailbreak tweak that already targets the Substrate API and porting to Frida is not worth the effort.
7. MobSF
MobSF is the open-source mobile security framework that bundles a Frida-driven dynamic analysis workflow inside a wider static + malware + REST-API platform. With over 21k GitHub stars and 90+ contributors, it is the most-used open-source mobile security scanner.
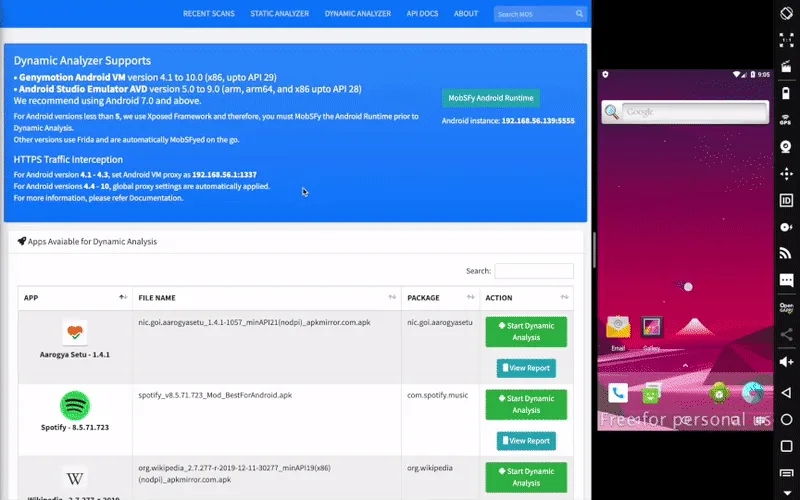 MobSF’s Dynamic Analyzer attaches Frida to a Genymotion or AVD instance, then drives APK scans from a web UI instead of the Frida CLI.
MobSF’s Dynamic Analyzer attaches Frida to a Genymotion or AVD instance, then drives APK scans from a web UI instead of the Frida CLI.
For teams that want HTML reports, CI/CD integration, and a web UI rather than a CLI, MobSF covers most of what they would do with raw Frida, at the cost of less custom hook flexibility.
It runs on Docker, supports Android, iOS, and Windows binaries, and is GPL-3.0 licensed. MobSF will not match Frida script-writers on edge cases, but it stops teams from re-writing the same SSL bypass for every assessment.
When to choose MobSF over Frida: you want a web UI, HTML reports, and CI/CD-integrated scans rather than a CLI plus hand-written JavaScript hooks.
8. Ghidra
Ghidra is the NSA-built static reverse engineering platform. It is not a runtime instrumentation tool, but it is the most-cited Frida-adjacent option when teams want to skip the runtime altogether.
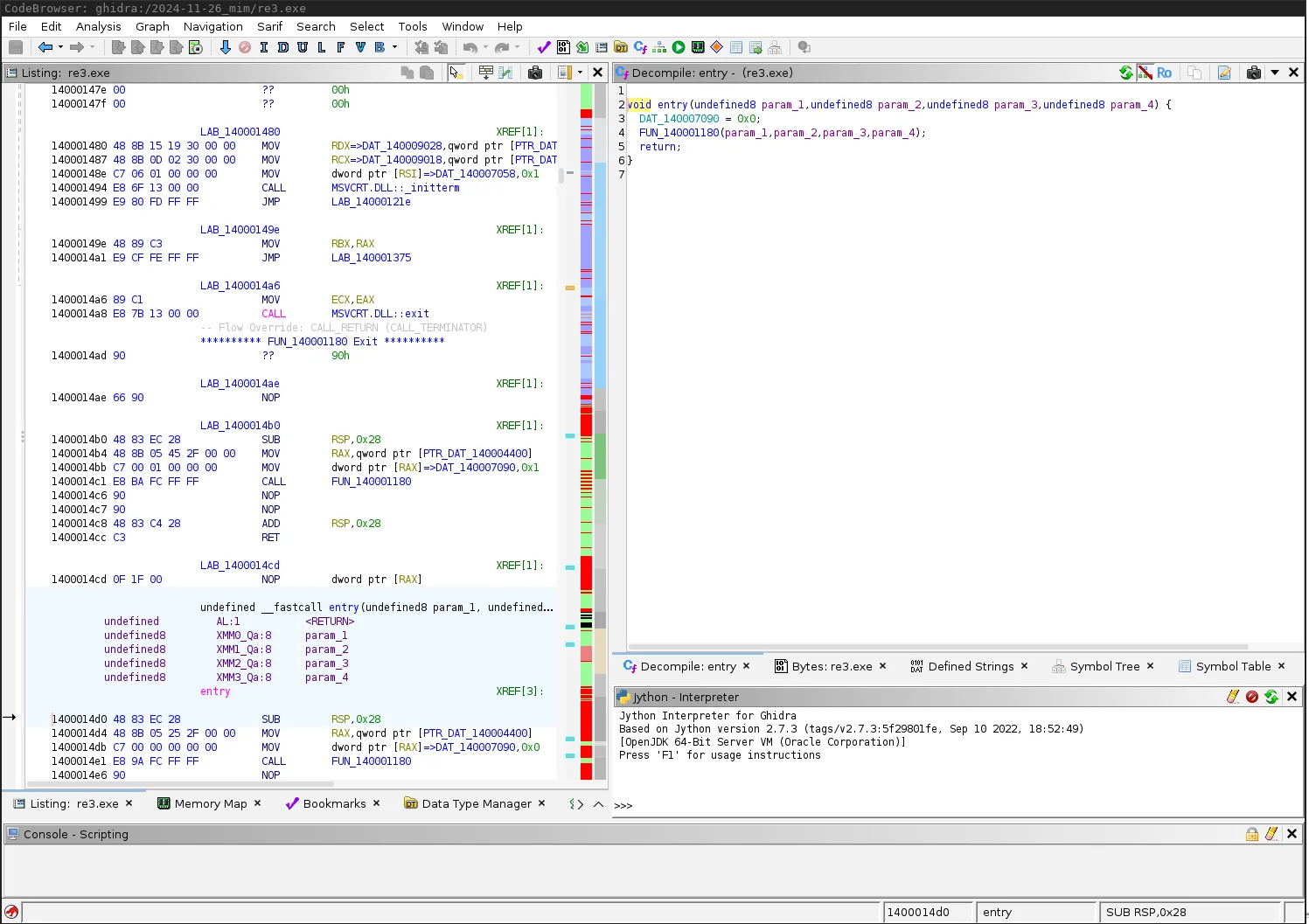 Ghidra’s decompiler renders disassembly and recovered C side by side, so AES constants and crypto call graphs surface without any runtime injection.
Ghidra’s decompiler renders disassembly and recovered C side by side, so AES constants and crypto call graphs surface without any runtime injection.
If your goal is finding hardcoded keys, AES constants, custom crypto routines, or the call graph for an obfuscated function, Ghidra often gets you there faster than wiring Frida hooks. It supports decompiling iOS Mach-O and Android DEX after JADX preprocessing.
It is free under Apache 2.0 and runs on Java. For static-first reverse engineering work, Ghidra is the alternative. For runtime behaviour and live traffic, you still need Frida or Objection.
When to choose Ghidra over Frida: the goal is hardcoded keys, AES constants, or decompiled call graphs that you can extract statically from the binary without runtime injection.
Feature Comparison
| Tool | Platforms | Hook level | License | Best for |
|---|---|---|---|---|
| Frida | Android, iOS, Win, Mac, Linux | Function (JS API) | wxWindows | Custom cross-platform hooks |
| Objection | Android, iOS | Function (Frida CLI) | GPL-3.0 | One-line bypasses (SSL pinning, root detection) |
| Xposed / LSPosed | Android only | Zygote-level Java | GPL-3.0 | Persistent system-wide Android hooks |
| Magisk + Zygisk | Android only | Zygote-level native | GPL-3.0 | Anti-detection, modular Android instrumentation |
| QBDI | Android, Linux, Mac, Win | Instruction-level (C++) | Apache 2.0 | Fuzzing harnesses, coverage tracing |
| Cycript | iOS (legacy) | Function (ObjC + JS) | GPL-3.0 | Historical jailbreak research |
| Cydia Substrate | iOS (legacy) | Function (C/ObjC) | Proprietary | Legacy tweak compatibility |
| MobSF | Android, iOS, Windows | Bundled Frida workflow | GPL-3.0 | Static + dynamic platform with reports |
| Ghidra | Android, iOS, native | Static (no runtime) | Apache 2.0 | Decompilation, crypto-routine discovery |
When to Stay with Frida
Frida is still the right tool when you need cross-platform reach in a single workflow, or when no other tool covers your target. A few cases keep coming up.
Anything that is not Android (iOS, macOS, Windows desktop apps, embedded Linux): the Android-only frameworks like Xposed and Magisk + Zygisk cannot help.
Custom hook scripts that go beyond Objection’s built-in commands: Frida’s JavaScript API is the most expressive runtime instrumentation surface available.
Automated pipelines where you want to script hook injection across many devices or many app versions. Frida’s CLI and Python bindings make this straightforward; Xposed modules and Magisk + Zygisk add deployment friction.
If your work fits any of those, keep Frida and add Objection on top for daily speed.
Related comparisons
- Apktool vs Jadx : Android decompiler comparison for the static-analysis side of the same workflow.
- Radare2 vs Ghidra : Two open-source reverse-engineering platforms for binary analysis.
- NowSecure vs MobSF : Commercial mobile security platform versus the open-source standard.
- iOS vs Android security : Platform security model comparison for context on which alternatives fit which target.
Frequently Asked Questions
What is the best alternative to Frida for Android app hooking?
Is there a Frida alternative for iOS encryption analysis?
Can I run Frida without jailbreaking or rooting?
What is the difference between Frida and QBDI?
Does MobSF replace Frida?

Founder, AppSec Santa
9+ years in application security. Reviews and compares 201 AppSec tools across 12 categories to help teams pick the right solution. More about me →
