MCP-Scan is an open-source security scanner that checks MCP (Model Context Protocol) server configurations for prompt injection, tool poisoning, cross-origin escalation, and rug pull attacks. It is the most widely adopted MCP security scanner, with over 2,000 GitHub stars, and serves as the foundation for Snyk’s enterprise Agent Scan product.
The tool has been rebranded to Snyk Agent Scan following the acquisition, with the latest release being v0.4.13 (April 2026).
Built by Invariant Labs, an ETH Zurich spin-off co-founded in 2024 by professors Martin Vechev and Florian Tramer along with Marc Fischer, Mislav Balunovic, and Luca Beurer-Kellner, the project was one of the first tools built to address MCP security risks.
The Invariant Labs team coined the term “tool poisoning” and documented several novel MCP attack vectors through their security research.
In June 2025, Snyk acquired Invariant Labs to accelerate its agentic AI security strategy. MCP-Scan remains open-source on GitHub and forms the foundation of Snyk’s broader Agent Scan product.
What is MCP-Scan?
MCP-Scan addresses a specific gap in the AI tooling ecosystem: MCP servers connect AI agents to external tools and data sources, but there was no standard way to verify that those connections are safe.
A malicious or compromised MCP server can embed hidden instructions in tool descriptions, inject prompts that hijack agent behavior, or silently change its tools after installation.
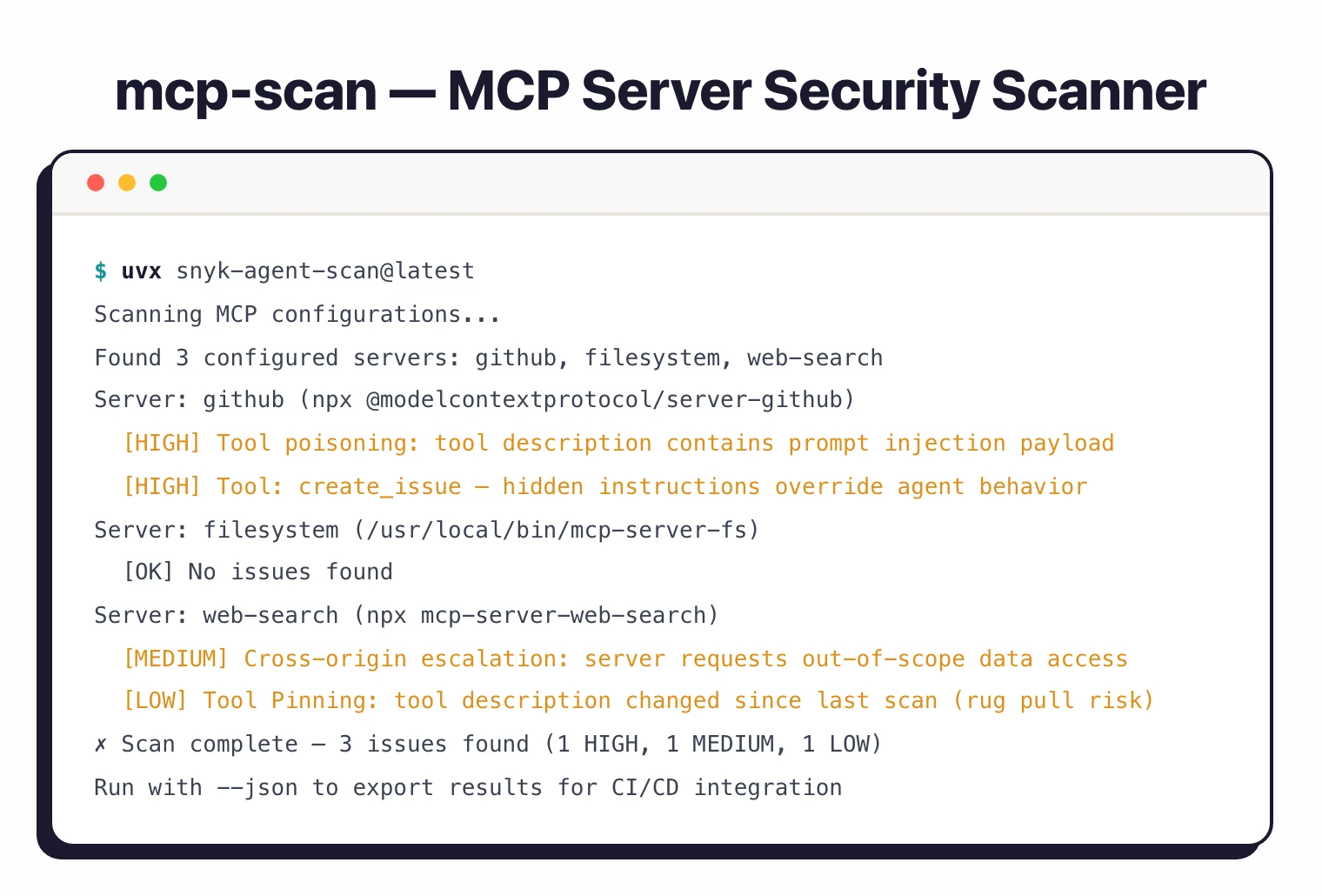
The scanner works by reading local MCP configuration files, connecting to each configured server, retrieving tool descriptions, and analyzing them both locally and through the Invariant Guardrails API. It supports two operating modes for different security needs.
Key Features
| Feature | Details |
|---|---|
| Scan Mode | One-time static vulnerability check of configured MCP servers |
| Proxy Mode | Continuous runtime monitoring and guardrail enforcement |
| Threat Detection | 15+ distinct security risks including prompt injection, tool poisoning, tool shadowing, toxic flows, cross-origin escalation |
| Tool Pinning | Hash-based rug pull detection for installed tools |
| PII Detection | Identifies personally identifiable information in MCP traffic |
| Secrets Detection | Catches exposed API keys, tokens, and credentials |
| Custom Policies | User-defined guardrailing rules for tool calls and responses |
| Client Support | Claude Desktop, Claude Code, Cursor, Windsurf, Gemini CLI, VS Code, OpenClaw, Kiro, Antigravity, Codex, Amazon Q |
| Platform Support | macOS, Linux, Windows |
| Output Formats | Terminal report, JSON (for CI/CD integration) |
Scan mode
The passive scan mode (mcp-scan scan) performs a one-time security audit of your MCP configuration. It reads the configuration files for your MCP client, connects to each server, retrieves tool descriptions, and checks them against known attack patterns.
This is the quickest way to verify new MCP servers before trusting them with your AI agents.
Proxy mode
The active proxy mode (mcp-scan proxy) runs as a background service that intercepts all MCP traffic between your client and servers. Every tool call and response passes through the proxy, which applies guardrailing policies in real time.
This catches dynamic attacks that only appear during actual tool execution — not in static tool descriptions.
Tool Pinning
One of MCP-Scan’s more novel features is Tool Pinning. When you first scan an MCP server, the tool hashes every tool description and stores the result. On subsequent scans, any change to a tool’s description triggers an alert.
This directly addresses the “rug pull” attack vector: a server appears benign at installation time, then modifies its tool behavior later to inject malicious instructions.
CI/CD integration
MCP-Scan supports JSON output via the --json flag, so it fits naturally into automated pipelines. Teams building custom MCP server registries or internal tool catalogs can run MCP-Scan as a validation step before publishing new servers, catching vulnerabilities before they reach developers.
Invariant Labs research background
The team behind MCP-Scan pioneered much of the foundational MCP security research, coining terms like “tool poisoning” and “MCP rug pull” and publishing reproducible attack experiments. This research directly informed the scanner’s detection capabilities — each check maps to a real, demonstrated attack vector rather than theoretical risk.
Getting Started
uvx snyk-agent-scan@latest to install and run the scanner. Requires Python 3.13+ with uv package manager. A free Snyk account provides the API token needed for analysis.snyk-agent-scan to automatically detect your MCP client configurations (Claude, Cursor, Windsurf, Gemini CLI, and more) and scan all configured servers for vulnerabilities. Use --skills to also scan agent skills.mcp-scan proxy as a background service. Configure guardrailing policies for PII detection, secrets scanning, and custom rules to enforce in real time.When to use MCP-Scan
Best for anyone using MCP servers with AI coding assistants or agent frameworks. MCP-Scan is essential as the MCP ecosystem grows rapidly.
The attack surface grows alongside the ecosystem — most MCP servers are community-contributed without formal security review. Running a scan before installing a new MCP server takes seconds and can prevent tool poisoning attacks that would otherwise silently compromise your AI agent’s behavior.
The proxy mode adds the most value for teams that use MCP servers in production workflows, where a one-time scan is not enough and continuous monitoring is needed to catch dynamic or time-delayed attacks.
For a broader overview of AI security tools, see the AI security tools guide. For authorization controls on MCP servers rather than vulnerability scanning, consider Cerbos. For a full agentic AI governance framework including MCP scanning, see Cisco DefenseClaw.